Professional Documents
Culture Documents
Tokenization Best Practices
Tokenization Best Practices
Uploaded by
mail4290Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Tokenization Best Practices
Tokenization Best Practices
Uploaded by
mail4290Copyright:
Available Formats
VISA BEST PRACTICES
14 July 2010
Visa Best Practices for Tokenization Version 1.0
Introduction
In October 2009, Visa published the Visa Best Practices for Data Field Encryption to promote the proper encryption of
sensitive card data that is transmitted, processed or stored by stakeholders throughout the payment system. As part of
these best practices, Visa recommended that entities use tokens (such as a transaction ID or a surrogate value) to
replace the Primary Account Number (PAN) for use in payment-related and ancillary business functions.
Tokenization can be implemented in isolation or in concert with data field encryption to help merchants eliminate the
need to store sensitive cardholder data after authorization. Entities that properly implement and execute a tokenization
process to support their payment functions may be able to reduce the scope, risks and costs associated with ongoing
compliance with the Payment Card Industry Data Security Standards (PCI DSS).
How Tokenization Works
Tokenization defines a process through which PAN data is replaced with a surrogate value known as a token. The
security of an individual token relies on properties of uniqueness and the infeasibility to determine the original PAN knowing
only the surrogate value. As a reference or surrogate value for the original PAN, a token can be used freely by systems
and applications within a merchant environment.
Where properly implemented, tokenization allows merchants to limit the storage of cardholder data to within the
tokenization system, potentially simplifying an entitys assessment against the PCI DSS. As a reference or surrogate value
for the original PAN, a token can be used by systems and applications within a merchant environment without having to
consider the security implications associated with the use of cardholder data.
The security and robustness of a tokenization system is dependent upon the secure implementation of four critical
components, and the overall management of the system and any historical data:
Token Generation: Defines the process through which a token is generated.
Token Mapping: Defines the process for associating a token to its original PAN value.
Card Data Vault: Defines the central repository of cardholder data used by the token mapping process.
Cryptographic Key Management: Defines the process through which cryptographic keys are managed and how
they are used to protect cardholder and account data.
Visa Public
1
Visa Best Practices for Tokenization, Version 1.0
The following are best practices for use of tokenization technology to protect cardholder data:
Domain
Best Practice
1. Network Segmentation: The tokenization system must be adequately
segmented from the rest of the network. The tokenization system must be
deployed within a fully PCI DSS compliant environment and be subject to
a full PCI DSS assessment.
2. Authentication: Only authenticated entities shall be allowed access to
the tokenization system.
3. Monitoring: The tokenization system must implement monitoring to
detect malfunctions or anomalies and suspicious activities in token-to-PAN
mapping requests. Upon detection, the monitoring system should alert
Tokenization
System
administrators and actively block token-to requests or implement a rate
limiting function to limit PAN data disclosure.
4. Token Distinguishability: The tokenization system must be able to
identify and distinguish between tokenized and cleartext cardholder data and
avoid the propagation of tokens to
systems expecting cleartext cardholder data.
Note: In accordance with the Visa Best Practices for Data Field
Encryption, cardholder data must remain encrypted from the point where it
enters an entitys system up to the point it is tokenized to achieve the
full benefits of a tokenization solution.
5. Token Generation: Knowing only the token, the recovery of the original
PAN must not be computationally feasible. Token generation can be
conducted utilizing either:
Token Generation
A known strong cryptographic algorithm (with a secure mode of
operation and padding mechanism), or
A one-way irreversible function (e.g., as a sequence number, using a
hash function with salt or as a randomly generated number)
Visa Public
2
6. Single-use vs. Multi-use Tokens: Tokens can be generated as a
single- or multi-use surrogate value, the choice of which depends largely
on business processes:
A single-use token should be used when there is no business need to
track an individual PAN for multiple transactions. Acceptable methods
for producing a single-use token include, but are not limited to, hashing
of the PAN with a transaction-unique salt
value, using a unique sequence number, or encrypting the PAN with an
ISO- or ANSI-approved encryption algorithm using a transaction-unique
key.
A multi-use token should be used when there is a business need to
track an individual PAN for multiple transactions. A multi-use token will
always map the same input PAN to the same token. An acceptable
method for producing a multi-use token includes, but is not limited to,
hashing of the cardholder data using a fixed but unique salt value per
merchant.
Notes: If a salt value is used, the salt must be kept secret and appropriately
protected. A salt should have a minimum length of 64-bits.
If a token is generated as a result of using a hash function, truncated PAN
data must not be stored or transmitted in conjunction with the tokenized
data.
7. PAN Processing: In order to limit / eliminate storage of PAN data, the
tokenization system should not provide PAN data to a token recipient (e.g., a
merchant). If PAN data is returned, the receiving system will be in the scope
of the PCI DSS. The token mapping should perform the following:
Processes should not return the PAN as part of any response to the
merchant.
Token Mapping
The tokenization platform should allow for chargeback and refund
processing without the need for the merchant to retain or have access
to full PAN.
8. PAN data must be encrypted in storage.
Card Data Vault
9. The card data vault must be managed and protected per PCI DSS
requirements.
Cryptographic Key
10. Encryption keys shall use a minimum bit strength of 112 bits.
Visa Public
3
Management
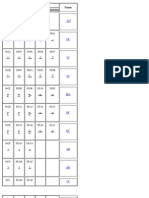
The following table summarizes equivalent bit strengths for commonly
used approved algorithms:
Algorithms
Bit Length
TDES
1121
AES
1282
RSA
2048
ECC
224
SHA
224
11. Any cryptographic keys used by the tokenization system must be
managed in accordance with PCI DSS.
Management of
Historical Data
12. Any retained historical or existing repositories of cardholder data must
be protected (per PCI DSS requirements), tokenized
or eliminated as part of the implementation.
Conclusion
Visa supports tokenization as a means of replacing Primary Account Numbers (PANs) with non-sensitive surrogate values
(known as tokens) to eliminate or reduce storage of cardholder data. Tokenization can be implemented independently or
in concert with data field encryption for the protection of cardholder information. To support marketplace adoption of
tokenization, Visa has developed best practices to assist merchants and other stakeholders in evaluating and adopting
tokenization solutions. These best practices should be viewed as high level guidance to be considered for any such solution
to assist stakeholders in the Visa payment system.
Respond With Comments by August 31, 2010
Visa would appreciate stakeholder feedback on these best practices by August 31, 2010. Please submit any comments via
e-mail to inforisk@visa.com with "Best Practices for Tokenization" in the subject line.
Related Documents
Visa Best Practices for Data Field Encryption October 2009
Visa Best Practices for Primary Account Number Storage and Truncation July 2010
For the purpose of these best practices, two key TDES (112-bits) should not process more than 1 million transactions. In cases where
the number of transactions potentially processed through the system using a single 112-bits TDES key greatly exceeds 1 million, three
key TDES (168-bits) or AES should be used. Key management schemes that greatly limit the number of transactions processed by a
single key, such as Derived Unique Key Per Transaction (DUKPT), can be used to ensure that any individual key is used only a limited
number of times..
2
The smallest key size usable with AES is 128 bits. This key size is stronger than needed, but if AES is to be used, it is
the smallest available. Longer keys may be used if so desired.
Visa Public
4
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5810)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1092)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (843)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (590)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (897)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (540)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (346)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (822)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (122)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (401)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- CISSP Study Guide PDFDocument100 pagesCISSP Study Guide PDFSK TuNo ratings yet
- EMV CPS v1.1Document104 pagesEMV CPS v1.1Hafedh Trimeche67% (3)
- OpenVAS ManualDocument347 pagesOpenVAS ManualwetcomNo ratings yet
- Amex Global Credit Auth Guide ISO Apr2011Document350 pagesAmex Global Credit Auth Guide ISO Apr2011Hafedh Trimeche100% (2)
- PCI HSM Security Requirements v3 2016 FinalDocument47 pagesPCI HSM Security Requirements v3 2016 FinalRifat Hasif Putrafebrian100% (1)
- Complete Hacking Crash CourseDocument60 pagesComplete Hacking Crash CourseRahul Kumar100% (1)
- User Manual: 4-4-2 Enrollment ScannerDocument11 pagesUser Manual: 4-4-2 Enrollment ScannerHafedh TrimecheNo ratings yet
- Essentials API - v1.1 - ENDocument24 pagesEssentials API - v1.1 - ENHafedh TrimecheNo ratings yet
- Passport Reader SDK User ManualDocument6 pagesPassport Reader SDK User ManualHafedh TrimecheNo ratings yet
- Intelligent Portable Control System: Project PresentationDocument14 pagesIntelligent Portable Control System: Project PresentationHafedh TrimecheNo ratings yet
- Mightygps Itrack Gold: Gps Tracking For Fleet & SecurityDocument32 pagesMightygps Itrack Gold: Gps Tracking For Fleet & SecurityHafedh TrimecheNo ratings yet
- Kelio V14Document36 pagesKelio V14Hafedh TrimecheNo ratings yet
- Writing ActiveX ControlsDocument6 pagesWriting ActiveX ControlsHafedh TrimecheNo ratings yet
- Arabic GlyphsDocument4 pagesArabic GlyphsHafedh TrimecheNo ratings yet
- TimestampDocument5 pagesTimestampHafedh TrimecheNo ratings yet
- Anexo 5 Major US Bank Replaces Base24 With OmniPayments - 1335820935474Document4 pagesAnexo 5 Major US Bank Replaces Base24 With OmniPayments - 1335820935474Hafedh TrimecheNo ratings yet
- OFXDocument665 pagesOFXHafedh TrimecheNo ratings yet
- Remote Key LoadDocument8 pagesRemote Key LoadHafedh TrimecheNo ratings yet
- SGWDocument42 pagesSGWHafedh TrimecheNo ratings yet
- ICC AdminDocument182 pagesICC Admincvlucian50% (2)
- EMV (Chip and PIN) ProjectDocument166 pagesEMV (Chip and PIN) ProjectSali Lala100% (1)
- PayPass - MChip (V1.3)Document125 pagesPayPass - MChip (V1.3)vijayasimhasNo ratings yet
- World-Text API SMPP Intergration SpecificationDocument8 pagesWorld-Text API SMPP Intergration SpecificationHafedh TrimecheNo ratings yet
- ActivexDocument2 pagesActivexHafedh Trimeche100% (1)
- Assignment On E-Commerce: Hailey College of Commerce University of The Punjab LahoreDocument7 pagesAssignment On E-Commerce: Hailey College of Commerce University of The Punjab LahoreSabir RazaNo ratings yet
- Iam UgDocument475 pagesIam Ugprasadpra17100% (1)
- AWS IAM-Cheet-SheetDocument11 pagesAWS IAM-Cheet-SheetamarmudirajNo ratings yet
- Security Breach: The Case of TJX Companies, IncDocument18 pagesSecurity Breach: The Case of TJX Companies, Inchammad78No ratings yet
- Enterprise Analytics in The CloudDocument12 pagesEnterprise Analytics in The CloudAnonymous gUySMcpSqNo ratings yet
- Cloud Advocate - 3 - Fundamentals of IBM CloudDocument42 pagesCloud Advocate - 3 - Fundamentals of IBM CloudGabriel PessineNo ratings yet
- Data PrivacyDocument9 pagesData PrivacyRodrick Sonajo RamosNo ratings yet
- VMware 3V0-21.21 Updated Questions and AnswersDocument8 pagesVMware 3V0-21.21 Updated Questions and AnswersJasmine DengNo ratings yet
- Isaca Cisa CismDocument49 pagesIsaca Cisa CismKavithaRamchandranNo ratings yet
- The Protection of Consumers' Personal Data in The Era of E-Commerce in NigeriaDocument41 pagesThe Protection of Consumers' Personal Data in The Era of E-Commerce in NigeriaOmoruyi RachealNo ratings yet
- Activeserver: Frictionless Fraud Prevention With 3D Secure 2Document9 pagesActiveserver: Frictionless Fraud Prevention With 3D Secure 2karlosm84No ratings yet
- Coalfire PCI 3 On AWS With Vormetric White Paper 2014 0312PCIDSSDocument22 pagesCoalfire PCI 3 On AWS With Vormetric White Paper 2014 0312PCIDSSval shaNo ratings yet
- Security Chaos Engineering VericaDocument92 pagesSecurity Chaos Engineering VericaAli DayaniNo ratings yet
- Ebook The Definitive Guide To Cloud Acceleration - HTMDocument119 pagesEbook The Definitive Guide To Cloud Acceleration - HTMaustinfru7No ratings yet
- OmniToken Product SheetDocument1 pageOmniToken Product SheetRishi SrivastavaNo ratings yet
- UL White Paper - Tokenization ExplainedDocument16 pagesUL White Paper - Tokenization ExplainedacpereraNo ratings yet
- Delivery TermsDocument60 pagesDelivery TermsTarush GoelNo ratings yet
- Restaurants Risk Management Guide UKDocument9 pagesRestaurants Risk Management Guide UKSarika JindalNo ratings yet
- Self-Assessment Questionnaire A: and Attestation of ComplianceDocument19 pagesSelf-Assessment Questionnaire A: and Attestation of ComplianceMinh Nhat TranNo ratings yet
- Cyber Breach at TargetDocument12 pagesCyber Breach at TargetVarun LalaNo ratings yet
- Implementing ISO Format 4 PIN Blocks Information SupplementDocument23 pagesImplementing ISO Format 4 PIN Blocks Information SupplementallNo ratings yet
- File ListDocument7 pagesFile Listnatan petraNo ratings yet
- Data MaskingDocument2 pagesData Maskingpavan79No ratings yet
- Welcome To Clearent Mobile Payment Solution With Restaurant Operation SystemDocument14 pagesWelcome To Clearent Mobile Payment Solution With Restaurant Operation SystemJames LeeNo ratings yet
- Change Opera Supervisor Password: BackgroundDocument5 pagesChange Opera Supervisor Password: BackgroundEliecer Francisco Marenco UrbinaNo ratings yet
- Navigating PCI DSS v4.0Document24 pagesNavigating PCI DSS v4.0Ivan DoriNo ratings yet