Professional Documents
Culture Documents
Cloud Computing
Uploaded by
vibhor1990Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Cloud Computing
Uploaded by
vibhor1990Copyright:
Available Formats
CLOUD COMPUTING
Congruent and Converging Forces
that compete
If you accept
There is an unquenchable thirst for
collaboration and sharing
We can work anywhere at any time highly
mobile workforce
You can work wherever you are at home,
traveling, etc.
Then
How do we achieve mission assurance on the same
network?
How do we ensure the network is there when we
need it?
What approach should we take?
Mission
Assurance
Work
Anywhere
at any
time
Sharing
Collaboration
Work
wherever
you are
Cloud Computing
Cloud means Internet. The computing takes place on the Internet
in place of the software you use executing on your desktop pc, its
hosted on the Internet on a server installed in a data centre usually
staffed by people who are experts in managing technology.
Gartner definition
a style of computing where massively scalable IT-enabled
capabilities are delivered as a service to external customers using
Internet technologies
Characteristics
It is sold on demand, typically by the minute or the hour;
it is elastic -- a user can have as much or as little of a service as they
want at any given time
the service is fully managed by the provider (the consumer needs
nothing but a personal computer and Internet access).
Significant innovations in virtualization and distributed computing,
as well as improved access to high-speed Internet and a weak
economy, have accelerated interest in cloud computing.
Private or Public?
A public cloud sells services to anyone on the Internet. (Currently,
Amazon Web Services is the largest public cloud provider.)
A private cloud is a proprietary network or a data center that
supplies hosted services to a limited number of people.
When a service provider uses public cloud resources to create their
private cloud, the result is called a virtual private cloud.
Private or public, the goal of cloud computing is to provide easy,
scalable access to computing resources and IT services.
Infrastructure-as-a-Service
Infrastructure-as-a-Service like Amazon Web Services provides
virtual server instance) to start, stop, access and configure their
virtual servers and storage.
In the enterprise, cloud computing allows a company to pay for
only as much capacity as is needed, and bring more online as soon
as required.
Because this pay-for-what-you-use model resembles the way
electricity, fuel and water are consumed, it's sometimes referred to
as utility computing.
Platform-as-a-service
Platform-as-a-service in the cloud is defined as a set of software and
product development tools hosted on the provider's infrastructure.
Developers create applications on the provider's platform over the
Internet.
PaaS providers may use APIs, website portals or gateway software
installed on the customer's computer. GoogleApps is an example.
Developers need to know that currently, there are not standards for
interoperability or data portability in the cloud. Some providers will
not allow software created by their customers to be moved off the
provider's platform.
Software-as-a-service
In the software-as-a-service cloud model, the vendor supplies the
hardware infrastructure, the software product and interacts with the
user through a front-end portal.
SaaS is a very broad market.
Services can be anything from Web-based email to inventory
control and database processing.
Because the service provider hosts both the application and the data,
the end user is free to use the service from anywhere.
Benefits
Reduced costs: You pay for what you use.
Scalability: You can scale your business storage needs seamlessly
rather than having to go out and purchase expensive programs or
hardware.
Automatic Updates: There is no need for IT to worry about paying
for your future updates in terms of software and hardware.
Remote Access: employees, partners and clients can access, and
update information wherever they are, rather than having to run
back the office.
Contd.
Disaster Relief: With your companys data safely stored on secure
data centers instead of your server room (previously known as your
storage closet), losing power due to hurricanes, earthquakes or a
construction worker cutting the power lines, you are back at work
as long as you have an internet connection.
Ease of Implementation: Your IT team (hopefully older than a 10
year old) may not like this, but implementing cloud services is as
easy as, well, setting up a LinkedIn page.
Skilled Vendors: Who would you rather manage and protect your
data? A company such as InfoStreet (with over 16 years experience
serving enterprise clients), IBM or Amazon or your IT staff.
Contd.
Response Time: Cloud computing accomplishes a better response
time in most cases than your standard server and hardware.
Even playing field for small firms: This allows small companies
to complete more effectively with some of the larger businesses,
balancing the playing field. Your small business can utilize the same
tools that Fortune 100 companies use and can do this because with
cloud computing, your business will only pay for what you need
Cloud Computing Challenges: Dealing with too many
issues
Scalability
Reliability
Billing
Utility & Risk
Management
Programming Env.
& Application Dev.
Software Eng.
Complexity
Uhm, I am not quite
clearYet another
complex IT paradigm?
Reasons to Consider Avoiding Cloud Computing
Security
Data Location & Privacy
Internet Dependency, Performance & Latency
Current Enterprise Applications Can't Be Migrated Easily
Many Cloud Offerings: Good, but new issues-vendor lock in,
scaling across clouds
IBM Cloud
Manjrasoft Aneka
Complex decisions
to make?
Threats, vulnerabilities, and enemies
Goal
Learn the cloud computing threat model by examining the assets,
vulnerabilities, entry points, and actors in a cloud
Technique
Apply different threat modeling schemes
Basic components
Attacker modeling
Choose what attacker to consider
Attacker motivation and capabilities
Assets / Attacker Goals
Vulnerabilities / threats
Who is the attacker?
Insider?
Malicious employees at client
Malicious employees at Cloud provider
Cloud provider itself
Outsider?
Intruders
Network attackers?
Attacker Capability: Malicious Insiders
At client
Learn passwords/authentication information
Gain control of the VMs
At cloud provider
Log client communication
Attacker Capability: Cloud Provider
What?
Can read unencrypted data
Can possibly peek into VMs, or make copies of VMs
Can monitor network communication, application patterns
Attacker motivation: Cloud Provider
Why?
Gain information about client data
Gain information on client behavior
Sell the information or use itself
Why not?
Cheaper to be honest?
Why? (again)
Third party clouds?
Attacker Capability: Outside attacker
What?
Listen to network traffic (passive)
Insert malicious traffic (active)
Probe cloud structure (active)
Launch DoS
Attacker goals: Outside attackers
Intrusion
Network analysis
Man in the middle
Cartography
Assets (Attacker goals)
Confidentiality
Data stored in the cloud
Configuration of VMs running on the cloud
Identity of the cloud users
Location of the VMs running client code
Assets (Attacker goals)
Integrity
Data stored in the cloud
Computations performed on the cloud
Assets (Attacker goals)
Availability
Cloud infrastructure
SaaS/ PaaS
Organizing the threats using STRIDE
Spoofing identity
Tampering with data
Repudiation
Information disclosure
Denial of service
Elevation of privilege
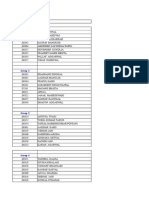
You might also like
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Cloud ComputingDocument27 pagesCloud Computingvibhor1990100% (1)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- IbsDocument4 pagesIbsvibhor1990No ratings yet
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- Group 1: Group / Roll No. NameDocument8 pagesGroup 1: Group / Roll No. Namevibhor1990No ratings yet
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Ratings Terms You Need To Know FINAL 030509Document6 pagesRatings Terms You Need To Know FINAL 030509vibhor1990No ratings yet
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (894)
- TL End Term CaseDocument1 pageTL End Term Casevibhor1990No ratings yet
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- Gender Inequality at WorkplacesDocument27 pagesGender Inequality at Workplacesvibhor1990No ratings yet
- Blue Ocean Red OceanDocument8 pagesBlue Ocean Red Oceanvibhor1990No ratings yet
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Voda India DistributionDocument19 pagesVoda India Distributionvibhor1990No ratings yet
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- IPL - A Group 9 - FinalDocument8 pagesIPL - A Group 9 - Finalvibhor1990No ratings yet
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (587)
- How Maruti Identified A Smart Supply Chain SystemDocument2 pagesHow Maruti Identified A Smart Supply Chain Systemvibhor1990No ratings yet
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (265)
- Marketing Google Case StudyDocument14 pagesMarketing Google Case Studyvibhor1990No ratings yet
- MiVideoView Debug Logs Analyze Video PlaybackDocument13 pagesMiVideoView Debug Logs Analyze Video PlaybackAniReedNo ratings yet
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- DEVOPS-QUICKDocument2 pagesDEVOPS-QUICKKeerthi KeerthanaNo ratings yet
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- Object Oriented System Design Question BankDocument5 pagesObject Oriented System Design Question BankManikandan KalimuthuNo ratings yet
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- Kanna Technologies - DBA ContentDocument3 pagesKanna Technologies - DBA ContentJ.B.BABUNo ratings yet
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Chapter 3 OoadDocument22 pagesChapter 3 Ooadsujitha14No ratings yet
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- Eduroam Installation in ZambiaDocument11 pagesEduroam Installation in ZambiaThomas YobeNo ratings yet
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2219)
- Normalization AirlinesDocument5 pagesNormalization AirlinesRishab RameshNo ratings yet
- Online Job SystemDocument53 pagesOnline Job Systemrsivapradeep54271% (7)
- 5 Best Portfolio-Ready Data Analytics Projects For Beginners by Learnbay Blogs May, 2023 MediumDocument17 pages5 Best Portfolio-Ready Data Analytics Projects For Beginners by Learnbay Blogs May, 2023 Mediumshmasood55No ratings yet
- Install Apache Dan PHP Pada Windows x64Document8 pagesInstall Apache Dan PHP Pada Windows x64Muh. HattaNo ratings yet
- Kabul University Lecture on ETL ProcessDocument27 pagesKabul University Lecture on ETL ProcessSohail AzizofNo ratings yet
- DEA-1TT4 V14.02 (Updated Dump)Document38 pagesDEA-1TT4 V14.02 (Updated Dump)mani deepNo ratings yet
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- Ansible Automation Saves TimeDocument116 pagesAnsible Automation Saves TimeLAngel ReyesNo ratings yet
- TLE ICT CS9 w1Document4 pagesTLE ICT CS9 w1Erlyn AlcantaraNo ratings yet
- IhigyjgbkjbkjDocument65 pagesIhigyjgbkjbkjtochi efienokwuNo ratings yet
- REST API For Oracle Fusion Cloud HCMDocument19 pagesREST API For Oracle Fusion Cloud HCMerick landaverdeNo ratings yet
- Proposal For A Document Management System in The Modern UniversityDocument12 pagesProposal For A Document Management System in The Modern UniversityBHG GlobaltechNo ratings yet
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (119)
- SDK Developer GuidDocument291 pagesSDK Developer Guidtoteu.comNo ratings yet
- The LFM FamilyDocument1 pageThe LFM FamilyJose Luis Velasco CadavidNo ratings yet
- Interprocess CommunicationDocument30 pagesInterprocess CommunicationSanjay ShahNo ratings yet
- SAP BW 7.5 SP4 Powered by SAP HANA Overview & RoadmapDocument31 pagesSAP BW 7.5 SP4 Powered by SAP HANA Overview & RoadmapVivek KhareNo ratings yet
- Minecraft Activity Slow Operation and Crash LogsDocument18 pagesMinecraft Activity Slow Operation and Crash LogsRe MasteredNo ratings yet
- Republic of the Philippines Commission on Elections List of Regular Voters (Precinct LevelDocument46 pagesRepublic of the Philippines Commission on Elections List of Regular Voters (Precinct LevelAngelika CalingasanNo ratings yet
- Tool of The Week: THC HydraDocument17 pagesTool of The Week: THC Hydrabebi koniNo ratings yet
- Upgrading ODI 11g To 12cDocument50 pagesUpgrading ODI 11g To 12cUsha RamanathanNo ratings yet
- ReportDocument41 pagesReportHimelNo ratings yet
- 22 PLC15 Bset 1Document2 pages22 PLC15 Bset 1Himanshu ChouhanNo ratings yet
- MIS 310 TutorialDocument31 pagesMIS 310 TutorialShàhríàrõ Dã RàkínskìNo ratings yet
- 002.SLA Custom - Source - PrintDocument8 pages002.SLA Custom - Source - PrintFco Jav RamNo ratings yet
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- E-Commerce: Satheesh Kumar.P 10CESF27Document23 pagesE-Commerce: Satheesh Kumar.P 10CESF27simbukumar87No ratings yet