Professional Documents
Culture Documents
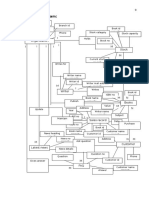
Title System Config Table Design Form Design DFD
Title System Config Table Design Form Design DFD
Uploaded by
Manoj Kumar Mohan0 ratings0% found this document useful (0 votes)
7 views1 pageAttribute-based encryption (ABE) is a relatively recent approach that reconsiders the concept of public-key cryptography. In traditional public-key cryptography, a message is encrypted for a specific receiver using the receiver’s public-key. Identity-based cryptography and in particular identity-based encryption (IBE) changed the traditional understanding of public-key cryptography by allowing the public-key to be an arbitrary string, e.g., the email address of the receiver. ABE goes one step further and defines the identity not atomic but as a set of attributes, e.g., roles, and messages can be encrypted with respect to subsets of attributes (key-policy ABE - KP-ABE) or policies defined over a set of attributes (ciphertext-policy ABE - CP-ABE). The key issue is, that someone should only be able to decrypt a ciphertext if the person holds a key for "matching attributes" (more below) where user keys are always issued by some trusted party.
Original Title
7th dec 2015
Copyright
© © All Rights Reserved
Available Formats
TXT, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentAttribute-based encryption (ABE) is a relatively recent approach that reconsiders the concept of public-key cryptography. In traditional public-key cryptography, a message is encrypted for a specific receiver using the receiver’s public-key. Identity-based cryptography and in particular identity-based encryption (IBE) changed the traditional understanding of public-key cryptography by allowing the public-key to be an arbitrary string, e.g., the email address of the receiver. ABE goes one step further and defines the identity not atomic but as a set of attributes, e.g., roles, and messages can be encrypted with respect to subsets of attributes (key-policy ABE - KP-ABE) or policies defined over a set of attributes (ciphertext-policy ABE - CP-ABE). The key issue is, that someone should only be able to decrypt a ciphertext if the person holds a key for "matching attributes" (more below) where user keys are always issued by some trusted party.
Copyright:
© All Rights Reserved
Available Formats
Download as TXT, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
7 views1 pageTitle System Config Table Design Form Design DFD
Title System Config Table Design Form Design DFD
Uploaded by
Manoj Kumar MohanAttribute-based encryption (ABE) is a relatively recent approach that reconsiders the concept of public-key cryptography. In traditional public-key cryptography, a message is encrypted for a specific receiver using the receiver’s public-key. Identity-based cryptography and in particular identity-based encryption (IBE) changed the traditional understanding of public-key cryptography by allowing the public-key to be an arbitrary string, e.g., the email address of the receiver. ABE goes one step further and defines the identity not atomic but as a set of attributes, e.g., roles, and messages can be encrypted with respect to subsets of attributes (key-policy ABE - KP-ABE) or policies defined over a set of attributes (ciphertext-policy ABE - CP-ABE). The key issue is, that someone should only be able to decrypt a ciphertext if the person holds a key for "matching attributes" (more below) where user keys are always issued by some trusted party.
Copyright:
© All Rights Reserved
Available Formats
Download as TXT, PDF, TXT or read online from Scribd
You are on page 1of 1
title
abstract
system config
module
table design
form design
dfd
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5813)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1092)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (844)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (590)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (897)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (540)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (348)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (822)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (122)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (401)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- Call Center Management System Project ReportDocument126 pagesCall Center Management System Project ReportManoj Kumar MohanNo ratings yet
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Abstract - Electronic Shop Management SystemDocument6 pagesAbstract - Electronic Shop Management SystemManoj Kumar Mohan100% (1)
- Abstract - College Alumni Management SystemDocument45 pagesAbstract - College Alumni Management SystemManoj Kumar Mohan66% (35)
- Unit 3 Visual Realism: ObjectivesDocument37 pagesUnit 3 Visual Realism: ObjectivesManoj Kumar MohanNo ratings yet
- Data Flow Diagram Level 0: Add/edit MediaDocument4 pagesData Flow Diagram Level 0: Add/edit MediaManoj Kumar MohanNo ratings yet
- Online Advertising AgencyDocument36 pagesOnline Advertising AgencyManoj Kumar MohanNo ratings yet
- The Three Tier AbstractDocument5 pagesThe Three Tier AbstractManoj Kumar MohanNo ratings yet
- DFD2Document2 pagesDFD2Manoj Kumar MohanNo ratings yet
- Phish Tester: Automatic Testing of Phishing Attacks AbstractDocument5 pagesPhish Tester: Automatic Testing of Phishing Attacks AbstractManoj Kumar MohanNo ratings yet
- b939 PDFDocument10 pagesb939 PDFManoj Kumar MohanNo ratings yet
- Hospital Management System AbstractDocument5 pagesHospital Management System AbstractManoj Kumar Mohan67% (3)
- Hospital Management System AbstractDocument5 pagesHospital Management System AbstractManoj Kumar MohanNo ratings yet
- Soft W A RE ENG I Neer I NGDocument5 pagesSoft W A RE ENG I Neer I NGManoj Kumar MohanNo ratings yet
- Director 1Document64 pagesDirector 1Manoj Kumar MohanNo ratings yet
- Inter Group Communication of Cued Click Points Using Graphical Password and Image SpectrographDocument4 pagesInter Group Communication of Cued Click Points Using Graphical Password and Image SpectrographManoj Kumar MohanNo ratings yet
- Chapter-I: 1.1 Director An IntroductionDocument71 pagesChapter-I: 1.1 Director An IntroductionManoj Kumar MohanNo ratings yet
- Chapter-I: 1.1 Director An IntroductionDocument71 pagesChapter-I: 1.1 Director An IntroductionManoj Kumar MohanNo ratings yet
- Big BazaarDocument22 pagesBig BazaarManoj Kumar MohanNo ratings yet
- Abstract - Online SupermarketDocument38 pagesAbstract - Online SupermarketManoj Kumar MohanNo ratings yet
- Dharani MotorsDocument29 pagesDharani MotorsManoj Kumar MohanNo ratings yet
- Acknowledgement About The Industry Company Profile Certificate of Training Technology Used ConclusionDocument25 pagesAcknowledgement About The Industry Company Profile Certificate of Training Technology Used ConclusionManoj Kumar MohanNo ratings yet
- Er Page 9 YtytyDocument1 pageEr Page 9 YtytyManoj Kumar MohanNo ratings yet