Professional Documents
Culture Documents
ISO27k Preventive Action Procedure PDF
Uploaded by
TahirOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
ISO27k Preventive Action Procedure PDF
Uploaded by
TahirCopyright:
Available Formats
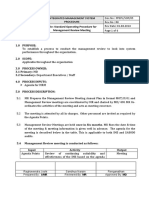
Document Title
Document Ref No
PREVENTIVE ACTION PROCEDURE
Original Author:
I27KIForum-ROR-PA
Approved by
Revision Stat
Richard O. Regalado
Purpose
Scope
Page/Total
1/2
The purpose of this procedure is to have a defined method in applying preventive actions to eliminate the
cause of potential non-conformities on the established information security management system (ISMS).
This procedure covers the collection of data on potential non-conformities, analysis of the potential root
causes of nonconformities and action planning to prevent occurrence of non-conformities.
RESPONSIBILITY
PROCESS FLOW
Auditor
Observer
Determine the extent or gravity of the
potential non-conformity
Issue Non-conformance Corrective Action/
Preventive Action report (NCPAR) to
concerned person or auditee
Auditor
Observer
Auditee
Auditees management
Lead Auditor
Auditor
Potential non-conformities maybe in the
form of findings during internal audits
(improvement potentials), suspected
information security weaknesses and
suggestions by [company] staff.
Identify potential non-conformities
Auditor
Observer
Auditee
Auditees management
DETAILS
Refer to instructions on page 2 of NCPAR
for proper usage
Apply immediate or containment action to
arrest the non-conformity
Determine potential root cause of the nonconformity
Root cause analysis tools such as the
why-why analysis and Ishikawa diagram
shall be used to identify potential root
causes of the non-conformity.
Establish preventive action based on rootcause analysis
Preventive actions shall be applied in a
holistic manner with efforts done to
ensure applicability on other areas or
processes.
Preventive action
is valid?
No
For preventive action to be valid, it
shall ensure non-occurrence of the
non-conformity.
Yes
Lead Auditor
Enter details in the NCPAR Log
Lead Auditor
Perform follow-up audit within 3 days after
the committed date of implementation.
Lead Auditor shall monitor NCPAR Log
on a weekly basis to verify open
potential non-conformities and ensure
timeliness of follow-up audits.
Follow-up shall be performed to ensure
implementation of preventive action.
REVISION HISTORY
No
0
Revision Details
Initial issue
Effectivity Date
2009 06 03
1
2
This work is copyright 2007, Richard O. Regalado and ISO27k implementers' forum, some rights reserved. It is licensed under the Creative Commons
Attribution-Noncommercial-Share Alike 3.0 License. You are welcome to reproduce, circulate, use and create derivative works from this provided that (a) it
is not sold or incorporated into a commercial product, (b) it is properly attributed to the ISO27k implementers' forum www.ISO27001security.com), and (c)
derivative works are shared under the same terms as this.).
Document Title
Document Ref No
PREVENTIVE ACTION PROCEDURE
RESPONSIBILITY
Revision Stat Page/Total
I27KIForum-ROR-PA
PROCESS FLOW
2/2
DETAILS
Lead Auditor
Preventive action
is implemented?
Issue new NCPAR
Yes
Lead Auditor
No
2
Perform 2nd follow-up 3 months after
committed implementation date
Follow-up shall be performed to ensure
implementation of corrective action.
Lead Auditor
Preventive action
is effective?
Yes
No
Issue new NCPAR
Lead Auditor
Close out non-conformity by making proper
notations on the NCPAR Log.
Lead Auditor
File and maintain all records in
accordance with Control of records
procedure
Instances where potential non-conformities may be identified
SITUATIONS
DESCRIPTION
As a result of internal
audits
Observed improvement potentials are possible sources of preventive actions.
Identification of
information security
weaknesses
Weaknesses shall be issued appropriate preventive actions lest they become fullblown information security incidents.
Near-misses
Environmental and health and safety near-misses shall be issue corresponding
preventive actions before they become accidents.
This work is copyright 2007, Richard O. Regalado and ISO27k implementers' forum, some rights reserved. It is licensed under the Creative Commons
Attribution-Noncommercial-Share Alike 3.0 License. You are welcome to reproduce, circulate, use and create derivative works from this provided that (a) it
is not sold or incorporated into a commercial product, (b) it is properly attributed to the ISO27k implementers' forum www.ISO27001security.com), and (c)
derivative works are shared under the same terms as this.).
You might also like
- HSE DocumentationDocument99 pagesHSE DocumentationTozmanNo ratings yet
- ISO 28000 A Complete Guide - 2019 EditionFrom EverandISO 28000 A Complete Guide - 2019 EditionRating: 4 out of 5 stars4/5 (1)
- Cairo HSEQ P 11 PDFDocument11 pagesCairo HSEQ P 11 PDFzakalyNo ratings yet
- Accident Reporting ProcedureDocument7 pagesAccident Reporting ProcedureDavid J CRNo ratings yet
- Business Continuity Management Program A Complete Guide - 2021 EditionFrom EverandBusiness Continuity Management Program A Complete Guide - 2021 EditionNo ratings yet
- Environmental Objectives & Targets Ver1407Document8 pagesEnvironmental Objectives & Targets Ver1407Veera RagavanNo ratings yet
- BM Waste Color CodingDocument23 pagesBM Waste Color Codingpriyankamote100% (1)
- 85-04, The BW Preventive Action Register.: Purpose and ScopeDocument2 pages85-04, The BW Preventive Action Register.: Purpose and Scopedanaka007No ratings yet
- Health Certificate To Work in Confined SpaceDocument6 pagesHealth Certificate To Work in Confined SpacenmmarhelNo ratings yet
- Risk Assessment and Treatment ProcessDocument3 pagesRisk Assessment and Treatment ProcessManojNo ratings yet
- Threat And Risk Assessment A Complete Guide - 2020 EditionFrom EverandThreat And Risk Assessment A Complete Guide - 2020 EditionNo ratings yet
- HSE Advice For Plant Operators FTGRG PDFDocument144 pagesHSE Advice For Plant Operators FTGRG PDFMuhammad Fiqih AgusfianNo ratings yet
- Crisis ManagementDocument19 pagesCrisis Managementsssr3103No ratings yet
- Appendix 7 To Chapter 5 Sms Gap Analysis Checklist and Implementation PlanDocument8 pagesAppendix 7 To Chapter 5 Sms Gap Analysis Checklist and Implementation PlanCahaya Yg TerpujiNo ratings yet
- ISO DIS 9001 2015 Risk Based Thinking 2 UpsDocument9 pagesISO DIS 9001 2015 Risk Based Thinking 2 Upsabdelmutalab100% (1)
- Autoclaves - Generic Assessment - L Use of AutoclavesDocument1 pageAutoclaves - Generic Assessment - L Use of AutoclavesaKureishiNo ratings yet
- PR09 Non-Conformity Procedure VersionDocument3 pagesPR09 Non-Conformity Procedure VersionAli KayaNo ratings yet
- Use of Certification Mark 2010 Eng - 2013-05-27 PDFDocument25 pagesUse of Certification Mark 2010 Eng - 2013-05-27 PDFAnonymous nhrbzyBNo ratings yet
- 00 - Petrobel IMS Overview FinalDocument52 pages00 - Petrobel IMS Overview FinalAhmed El AmraniNo ratings yet
- ENV18 Aspects Register Procedure 2014 - UpdatedDocument5 pagesENV18 Aspects Register Procedure 2014 - UpdatedsametggtNo ratings yet
- Warehouse Man StorekeeperDocument3 pagesWarehouse Man Storekeeperjay jayNo ratings yet
- Initial Ergonomics Risk Assessment ChecklistDocument8 pagesInitial Ergonomics Risk Assessment ChecklistIma HishamNo ratings yet
- HBB Business Continuity Plan - Major Incident Response PDFDocument55 pagesHBB Business Continuity Plan - Major Incident Response PDFNishimaNo ratings yet
- Cyprus Work Permit Procedure EnglishDocument17 pagesCyprus Work Permit Procedure EnglishAbdullah ElNaser Helmy عبدالله الناصر حلمىNo ratings yet
- RISK Mba 17Document22 pagesRISK Mba 17Cecily Sandra100% (1)
- Fire Protection Plan 1Document11 pagesFire Protection Plan 1Muhammad TariqNo ratings yet
- Business Continuity ManagementDocument3 pagesBusiness Continuity ManagementChandra RaoNo ratings yet
- MNO-PR-HSE 0009 Monitoring and Measurement ProcedureDocument9 pagesMNO-PR-HSE 0009 Monitoring and Measurement Procedurebubbles82No ratings yet
- SWP Coshh v5.02 Dec 2015Document8 pagesSWP Coshh v5.02 Dec 2015marvinNo ratings yet
- ISO27k Model Security Policy On MalwareDocument3 pagesISO27k Model Security Policy On Malwarepenumudi233No ratings yet
- 10 Controlled Equipment LogDocument1 page10 Controlled Equipment LogRina AnitaNo ratings yet
- Ineco Hse Manual-SignedDocument27 pagesIneco Hse Manual-SignedTantely RazafimahatratraNo ratings yet
- EM01Document20 pagesEM01Anonymous B7pghh100% (1)
- Ergonomics Hazard Zone ChecklistDocument7 pagesErgonomics Hazard Zone ChecklistJoshua RobbinsNo ratings yet
- Revised CERT Audit ChecklistDocument15 pagesRevised CERT Audit ChecklistSBNo ratings yet
- Compressed Fire Risk Assessment TemplateDocument9 pagesCompressed Fire Risk Assessment TemplateReaz UddinNo ratings yet
- Attachment 1 Aibel AS GHG Emissions 2017-2022Document10 pagesAttachment 1 Aibel AS GHG Emissions 2017-2022DavidNo ratings yet
- Emergency Preparedness and Response ProcedureDocument4 pagesEmergency Preparedness and Response ProcedureMUHAMMAD FAIZ BIN RAHAMAT STUDENTNo ratings yet
- Health and Safety Management Manual With Procedures ExampleDocument13 pagesHealth and Safety Management Manual With Procedures ExampleVepxvia NadiradzeNo ratings yet
- Curricular Activity Risks Analysis & Evaluation FormDocument4 pagesCurricular Activity Risks Analysis & Evaluation Formdianna tercinoNo ratings yet
- Isms-C Doc 16.1.5 PDFDocument2 pagesIsms-C Doc 16.1.5 PDFdhir.ankurNo ratings yet
- IT Operations - Document Operating ProceduresDocument10 pagesIT Operations - Document Operating ProcedurespinghooNo ratings yet
- SLCP Verification ProtocolDocument62 pagesSLCP Verification ProtocolWILFREDO SSOCONSULTORESNo ratings yet
- SOP - TWM - Problem Management - v1.1Document12 pagesSOP - TWM - Problem Management - v1.1Abdul HafizNo ratings yet
- 2-Procedure For Control of DocumentsDocument3 pages2-Procedure For Control of DocumentsRichu PaliNo ratings yet
- KOC HE 027 - Heat Stress Management ProcedureDocument44 pagesKOC HE 027 - Heat Stress Management ProcedureGeorge LameyNo ratings yet
- Nesrea ActDocument24 pagesNesrea Actkirandevi1981100% (1)
- ISMS-DeS-L2 28 Information Security Aspects of Business Continuity Management ProcedureDocument6 pagesISMS-DeS-L2 28 Information Security Aspects of Business Continuity Management Procedurepooja07061990No ratings yet
- PPEPL-SOP-05 Procedure For Management ReviewDocument6 pagesPPEPL-SOP-05 Procedure For Management ReviewRaja RehaNo ratings yet
- How Do I Configure Device-Mapper-Multipath For EMC CLARiion or VNX With ALUA Mode in RHEL 6, 7 - Red Hat Customer PortalDocument7 pagesHow Do I Configure Device-Mapper-Multipath For EMC CLARiion or VNX With ALUA Mode in RHEL 6, 7 - Red Hat Customer Portalomid omidanNo ratings yet
- Fumigation Practices For Quarantine PurposesDocument4 pagesFumigation Practices For Quarantine PurposesNor Hisham BadriNo ratings yet
- Enc K Corporate Risk Register PDFDocument7 pagesEnc K Corporate Risk Register PDFrioNo ratings yet
- eSWIS User Manual WACDocument25 pageseSWIS User Manual WACZafani Yaacob100% (1)
- HousekeepingDocument3 pagesHousekeepingFauziah YusoffNo ratings yet
- PMSDailyReport - 140610171657Document21 pagesPMSDailyReport - 140610171657kittisakddNo ratings yet
- GSM InfrastructureDocument19 pagesGSM InfrastructurekittisakddNo ratings yet
- PMS 3G Weekly ReportDocument21 pagesPMS 3G Weekly ReportkittisakddNo ratings yet
- TTS Usage Report 1-6-2014Document35 pagesTTS Usage Report 1-6-2014kittisakddNo ratings yet
- Best Practices of IT Organization Design enDocument35 pagesBest Practices of IT Organization Design enkittisakdd100% (1)
- Introduction To PHP: Server-Side Web LanguagesDocument20 pagesIntroduction To PHP: Server-Side Web LanguageskittisakddNo ratings yet