Professional Documents
Culture Documents
Ch#6 Computer
Ch#6 Computer
Uploaded by
Qaisar RiazCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Ch#6 Computer
Ch#6 Computer
Uploaded by
Qaisar RiazCopyright:
Available Formats
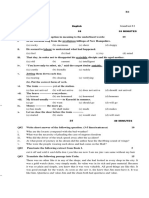
R6
F.Sc - XI COMPUTER Ch # 6
13-02-2016 12 10 MINUTES
Q#1 Encircle the best option. 1x12=12
i. ______ is cause of virus.
(a) e-mail (b) network (c) pirated software (d) all
ii. Types of software that can be freely distributed without violating copyright laws are called:
(a) shareware (b) public domain (c) copy protected (d) both a & b
iii. Another name for antivirus is:
(a) Vaccine (b) Worn (c) Trojan horse (d) DES
iv. Security protection for personal computer include:
(a) internal components (b) lock and cables
(c) software (d) all of these
v. A secret word or number to be typed by a keyboard by a keyboard before an activity can
take place are called:
(a) biometric data (b) data encryption (c) password (d) private word
vi. Which is not an antivirus program?
(a) Redlof (b) Norton (c) McAfee (d) Dr. Solomon
vii. Format C is an example of:
(a) logic bomb (b) Trojan Horse (c) boot sector (d) Chernobal
viii. What is most common computer crime of these listed below?
(a) extortion of bank funds (b) IRS database sabotage
(c) putting people on junk mailing lists (d) software piracy
ix. ______ media is used for backup:
(a) floppy diskette (b) zip disk (c) tape drive (d) all
x. Which virus is activated on the basis of a logical condition?
(a) logic bomb (b) Trojan Horse (c) Boot sector (d) chernobal
xi. ______ is not an anti-virus program:
(a) Red-lof (b) Norton (c) Trojan Horse (d) Virus
xii. _______ is an anti-virus program:
(a) Red-lof (b) Horse Trojan (c) Dr. Solomon (d) Logic bomb
SUBJECTIVE TYPE Total Marks 28 Time 50 MINUTES
Allowed
Q#2 Write short answer of the following questions. 10x2=20
i. What is security?
ii. What is a virus?
iii. What is computer misuse act?
iv. What are the causes of viruses?
v. What are pirated software?
vi. What is copyright act?
vii. What is the function of boot sector virus?
viii. What is a chernobal virus?
ix. What is denial of service situation?
x. What is a Trojan Horse?
Q#3 a) What is a virus? What are the causes of virus? 04
b) What is an antivirus? How to safeguard against virus? 04
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5813)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1092)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (844)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (590)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (897)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (540)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (348)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (822)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (122)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (401)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- Checklist For Painting WorksDocument4 pagesChecklist For Painting WorksBang JoyNo ratings yet
- F7 BPP - Kit (June 2020) PDFDocument336 pagesF7 BPP - Kit (June 2020) PDFTrung Phương Đỗ0% (1)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Type of Compound Structure of Functional Group General Formula /suffix or Prefix ExampleDocument3 pagesType of Compound Structure of Functional Group General Formula /suffix or Prefix ExampleQaisar RiazNo ratings yet
- CH#5 F.SC I Physics Total Marks 40: Q#1 Encircle The Best OptionDocument1 pageCH#5 F.SC I Physics Total Marks 40: Q#1 Encircle The Best OptionQaisar RiazNo ratings yet
- Ch#1,6 R#3 (19-01-2016)Document1 pageCh#1,6 R#3 (19-01-2016)Qaisar RiazNo ratings yet
- CH# 2 (Test 6)Document1 pageCH# 2 (Test 6)Qaisar RiazNo ratings yet
- Q.1. Choose The Correct Option.: D C B ADocument1 pageQ.1. Choose The Correct Option.: D C B AQaisar RiazNo ratings yet
- F.SC - XI 11-03-2016 10 10 Minutes: IslamiatDocument1 pageF.SC - XI 11-03-2016 10 10 Minutes: IslamiatQaisar RiazNo ratings yet
- Mathematics: N R n+1 R N r+1 N RDocument1 pageMathematics: N R n+1 R N r+1 N RQaisar RiazNo ratings yet
- R#4 21.1.16Document1 pageR#4 21.1.16Qaisar RiazNo ratings yet
- R#5 09.02.16Document1 pageR#5 09.02.16Qaisar RiazNo ratings yet
- English: Book-I 13 - 15, Punctuation, CorrectionDocument1 pageEnglish: Book-I 13 - 15, Punctuation, CorrectionQaisar RiazNo ratings yet
- 1 Year English 07-01-2016: Book:1,2: Pair of Words 1-85Document1 page1 Year English 07-01-2016: Book:1,2: Pair of Words 1-85Qaisar RiazNo ratings yet
- F.SC - XI 25-02-2016 10 10 Minutes: English Grand Test # 2Document1 pageF.SC - XI 25-02-2016 10 10 Minutes: English Grand Test # 2Qaisar RiazNo ratings yet
- English: Book III 1 Play, Poem 1-6, ApplicationDocument1 pageEnglish: Book III 1 Play, Poem 1-6, ApplicationQaisar RiazNo ratings yet
- English: Book-I 6 - 9, CorrectionDocument1 pageEnglish: Book-I 6 - 9, CorrectionQaisar RiazNo ratings yet
- English: Book-I 1-9, Pair of Words, CorrectionDocument1 pageEnglish: Book-I 1-9, Pair of Words, CorrectionQaisar RiazNo ratings yet
- Ch#5 1st HalfR#4 1st Year, 23-01-2016Document1 pageCh#5 1st HalfR#4 1st Year, 23-01-2016Qaisar RiazNo ratings yet
- Ch#5, R#5 1st Year, 08-02-2016Document1 pageCh#5, R#5 1st Year, 08-02-2016Qaisar RiazNo ratings yet
- Computer: CH # 1, 2, 3, 4 1 HalfDocument1 pageComputer: CH # 1, 2, 3, 4 1 HalfQaisar RiazNo ratings yet
- F.SC - XI 08-02-2016 12 10 Minutes: ComputerDocument1 pageF.SC - XI 08-02-2016 12 10 Minutes: ComputerQaisar RiazNo ratings yet
- Maharashtra Jeevan PradhikaranDocument253 pagesMaharashtra Jeevan PradhikaranRupesh Kumar100% (1)
- Brilliant Study Centre, Pala: 21423 296859 S.A.PRAGADEESHDocument1 pageBrilliant Study Centre, Pala: 21423 296859 S.A.PRAGADEESHArthi's RainbowNo ratings yet
- Nineteenth Century Philippines GEC109Document7 pagesNineteenth Century Philippines GEC109Nashebah A. BatuganNo ratings yet
- BIR Ruling DA-648-04Document2 pagesBIR Ruling DA-648-04Phoebe SpaurekNo ratings yet
- AntioxidantsDocument37 pagesAntioxidantsirem emine demirNo ratings yet
- EmulsionsDocument14 pagesEmulsionsام عبدالرحمن الشيخ100% (3)
- On The Practical (In-) Security of 64-Bit Block Ciphers: Collision Attacks On HTTP Over Tls and OpenvpnDocument13 pagesOn The Practical (In-) Security of 64-Bit Block Ciphers: Collision Attacks On HTTP Over Tls and OpenvpnshubhamNo ratings yet
- Data Sheet WD Blue PC Hard DrivesDocument2 pagesData Sheet WD Blue PC Hard DrivesRodrigo TorresNo ratings yet
- St. Croix County Property Transfers For Jan. 4-10, 2021Document39 pagesSt. Croix County Property Transfers For Jan. 4-10, 2021Michael BrunNo ratings yet
- Procedural Rules Volume 1 Amendment of Section 200Document1 pageProcedural Rules Volume 1 Amendment of Section 200PGIndikaNo ratings yet
- Entrepreneurship LAS Lesson-1 Week1Document7 pagesEntrepreneurship LAS Lesson-1 Week1Shanna kaye rallosNo ratings yet
- Ved Prakash: Work ExperienceDocument2 pagesVed Prakash: Work Experiencepallavimehrotra22No ratings yet
- English Core Term 2 3Document3 pagesEnglish Core Term 2 3Divyajyoti KumarNo ratings yet
- Module 3 - GOVERNMENTS AND CITIZENS IN A GLOBALLY INTERCONNECTED WORLD OF STATESDocument8 pagesModule 3 - GOVERNMENTS AND CITIZENS IN A GLOBALLY INTERCONNECTED WORLD OF STATESMark Alvin S. BaterinaNo ratings yet
- Licensing Requirements For Nurses in HAAD CompleteDocument8 pagesLicensing Requirements For Nurses in HAAD CompleteBobby Noel Cerro JrNo ratings yet
- New Microsoft Office Word DocumentDocument7 pagesNew Microsoft Office Word Documentspeak2dasNo ratings yet
- Notes On Agency and TrustsDocument4 pagesNotes On Agency and TrustsArlene CañonesNo ratings yet
- Petition U/s 28 of Special Marriage ActDocument3 pagesPetition U/s 28 of Special Marriage ActVijay Vardhan KudariNo ratings yet
- SDSF Operatinal and Customisation - Isf4cs80Document514 pagesSDSF Operatinal and Customisation - Isf4cs80Sathish KumarNo ratings yet
- Thermistor Temperature Sensing AlarmDocument2 pagesThermistor Temperature Sensing AlarmDark RiderNo ratings yet
- Hiab XS-144Document12 pagesHiab XS-144jairomarcano100% (1)
- TECHNOLOGY3 AnswerDocument7 pagesTECHNOLOGY3 AnswerNashaat DhyaaNo ratings yet
- Metric DIN 609 SpecDocument4 pagesMetric DIN 609 SpecCAT MINING SHOVELNo ratings yet
- Material Characteristics: Ferrite Cores For EMI SuppressionDocument8 pagesMaterial Characteristics: Ferrite Cores For EMI SuppressionMuhammad ImranNo ratings yet
- Ubiquiti PBE-5AC-500 Data SheetDocument11 pagesUbiquiti PBE-5AC-500 Data SheetJMAC SupplyNo ratings yet
- Performance Assessment Matrix: (F2F Face To Face DL Distance Learning)Document4 pagesPerformance Assessment Matrix: (F2F Face To Face DL Distance Learning)Priya NairNo ratings yet
- Toward Uniform CompetencyDocument12 pagesToward Uniform CompetencyDiana Constanza Guzmán SantosNo ratings yet
- C1 3 - Development of An Arduino Based Identification Diagnostic and Monitoring System - ADocument51 pagesC1 3 - Development of An Arduino Based Identification Diagnostic and Monitoring System - ALeigh NavalesNo ratings yet