Professional Documents
Culture Documents
Border Security Using Iot IJERTCONV6IS13123
Uploaded by
Nagaraj HCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Border Security Using Iot IJERTCONV6IS13123
Uploaded by
Nagaraj HCopyright:
Available Formats
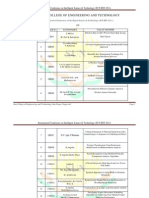
Special Issue - 2018 International Journal of Engineering Research & Technology (IJERT)
ISSN: 2278-0181
NCESC - 2018 Conference Proceedings
Border Security using IoT
Pooja S N Spurthi T M
U G Student U G Student
Department Of Electronics And Communication Department Of Electronics And Communication
Rajarajeswari College Of Engineering Rajarajeswari College Of Engineering
Bangalore , India Bangalore, India
Rashmi R K Samreen Unnisa
U G Student U G Student
Department Of Electronics And Communication Department Of Electronics And Communication
Rajarajeswari College Of Engineering Rajarajeswari College Of Engineering
Bangalore ,India Bangalore , India
Deepika J
Assistant Professor
Department Of Electronics And Communication
Rajarajeswari College Of Engineering
Bangalore, India
Abstract-Terrorists cross our borders unknowingly. It is not task: (a). Patrolling mode: Here reconnaissance robot
possible for our soldiers to watch the borders at each and roams in the environment and tracks predefined routes
every moment. An essential requirement in security is the unconventionally. It will send key information related to
capability to automatically detect terrorist in borders . In this security to the server for further analysis. (b). First
paper we propose an robot which identifies terrorist using IR
Responder mode: The reconnaissance robot will work in
sensor and capture image of terrorist using pi camera and
sends notification to respective admin. If admin accept to collaboration with fixed monitoring devices and it is
shootout that terrorist then that notification is sent back to programmed. It will be directed to target location in order
robot through server to kill that person, if admin decline to to perform on-site inspection when a security related event
shootout then the process will stop their itself. This is reported by one of the monitoring device. Obstacles in
development enables security personnel to effectively detect its path can be avoided by creating a deviation or
terrorist at low cost. unswervingly jumping over them. (c). Remote Control
mode: In this mode remote user will navigate the
Keywords – IR sensor, Raspberry pi, Robot, Pi Camera, surveillance robot to the target region. Security system can
be accessed by the users through PCs, mobile phones and
I. INTRODUCTION
PDAs.
II. LITERATURE SURVEY
An autonomous robot system is an innovation of modern
technology. It has been able to provide significant support
1.“Human Motion Detection Using Passive Infrared
to mankind by accomplishing task that is impossible for
Sensor” K Sravani, Md Parvez Ahmed, N Chandra
human beings. These robots can be used to accomplish
Sekhar, G Sirisha,V Prasad.International journal of
tasks like rescue, security, surveillance in unstructured and
research in computer application and information vol-
natural environments. An Internet-based intelligent robot
2,issue-2,march-april,2014.The objective of this project is
security system, “iBotGuard” in [2] detects trespassers
to develop a motion sensor alarm based on a Passive Infra-
using face recognition algorithm. System can detect a
Red (PIR) sensor module. In this project, microcontroller
trespasser using intruder detection subsystem which relies
continuously monitors the output from the sensor module
on invariant face recognition and it tracks the trespasser
and turns a buzzer on when it goes active. The application
using intruder tracking subsystem based on streaming
areas of this project are: All outdoor lights, Lift lobby,
technology. Intruder detection subsystem captures images
Multi apartment complexes, common staircases, for
periodically when it detects trespasser in a secure area and
basement or covered parking area, shopping malls, for
verifies whether the object detected is human using
garden lights.
invariant face recognition algorithm then robot will alert
2.“Border Surveillance using sensor based thick-lines”
the security guards through alert signal using internet. The
Ramzi Bellazreg , Noureddine Boudriga, Sunshine28-
security guards use the images in robot camera to control
30,Jan,2013,information networking(ICOIN). The primary
robot motion and to recognize trespasser. The
objective of the deployment research is to find the
reconnaissance robot [3] can be operated in three different
deployment strategy using the minimum number of each
ways in accordance with user requests and possessions of
Volume 6, Issue 13 Published by, www.ijert.org 1
Special Issue - 2018 International Journal of Engineering Research & Technology (IJERT)
ISSN: 2278-0181
NCESC - 2018 Conference Proceedings
type of sensors to cover the whole surveillance area and to there are numerous circumstances that happen, so every
achieve a desired intrusion detection probability when movement our soldiers can’t watch the borders then
intruders near the border. minimum number of each type intruders can enter our border by unknowingly and they
of sensors to cover the whole surveillance area and to may attack. At the point when an unknown person is
achieve a desired intrusion detection probability when recognized in the scope of that IR sensor at that point it
intruders near the border. minimum number of each type sends the flag to the raspberry pi and pi camera starts
of sensors to cover the whole surveillance area and to capturing the images. After capturing images, it will
achieve a desired intrusion detection probability when compare with database stored in the server, if image is
intruders near the border. does not match with any image then robot will shootout
3.“Advanced Border Intrusion Detection and Surveillance that person . At that point the protect operation will be
Using Wireless Sensor Network Technology”. IJCNS 251- quick in identifying the people who are enter
259,2013.This paper surveys the literature for unknowingly. Robot will kill the opponents’ life.
experimenting work done in border surveillance and
intrusion detection using the technology of WSN. The role
of WSN in border surveillance, as in most WSN
applications, focuses on information gathering from
various types of sensors, such as seismic, camera, and
motion detectors. Some advanced WSN process these raw
data and send an abstracted alarm or aggregated data to the
command center, which, in turn, takes the appropriate
defence action
4.“Defence Security Systems”.IEEE , Harry J. woodroof,
Ase k jakobsson , 8 sep 2014.The main purpose of the
project is to enhance the border security electronically
with automation and with that to reduce the work load and
responsibility of the soldiers that continuously take a look
on border 24x7. This project will not fully remove the
responsibility of soldiers but shares the maximum
responsibility and will reduce human efforts on the border.
5.“Wireless sensor networks to prevent unauthorized entry Fig 1. Proposed system
into critical military borders” .IEEE 20 jan 2011,Yan-Xio
Li, Lian Qin, Qian Liang. Human activity at border is IV. SYSTEM IMPLEMENTATION
performed by the system with the help of PIR Sensor. This
will alert if someone enter at border. In second stage the The System implemented using following hardware
system is going to detect whether the person is carrying a components:
weapon or not. If a person is carrying a weapon then it A. Raspberry pi
will alert at monitoring area about the weapon by using Raspberry Pi is a credit-card sized computer manufactured and
metal detector sensor. Then at the final stage capturing the designed in the united kingdom by the raspberry pi
image of the person entering at military border is foundation with the intension of teaching basic computer
performed. For this the system uses a camera which is science to school student s and every other person interested
capable of capturing the image clearly when the person is in computer, programming and DIY-DO-IT yourself projects.
near to it. After capturing the image ofthe unauthorized
person, image processing is used to process the image. By
the use of MATLAB the image is processed and transmits
to the required destination i.e. monitoring section. The
transmission is possible through ZIGBEE. Thus the
human activities and penetration of terrorist are easily
monitored and can be prevented at high dense fog and
critical military borders.
III. PROPOSED SYSTEM
The point of this project is to build up an implanted .
Fig 2 raspberry pi
intruders identification framework in border by utilizing
IR sensor. There are numerous IR sensors being used
today however the sensor that is utilized will identify the
Infrared beams that are transmitted from the human body.
There is a need to use PI camera because, we are using PI
Camera for detecting intruders. We realize that in border
Volume 6, Issue 13 Published by, www.ijert.org 2
Special Issue - 2018 International Journal of Engineering Research & Technology (IJERT)
ISSN: 2278-0181
NCESC - 2018 Conference Proceedings
B. Pi- Camera through which the integral rotor or armature shaft pinion
passes.
Fig 3. Pi camera
In order to meet the increasing need of Raspberry Pi
compatible camera modules. The ArduCAM team now
released a revision C add-on camera module for Raspberry Fig 6. Gear Motor
Pi which is fully compatible with official one. It optimizes
the optical performance than the previous Pi cameras, and V. RESULT
give user a much clear and sharp image .
C. IR Sensor
This device emits and/or detects infrared radiation to sense a
particular phase in the environment. Generally, thermal radiation
is emitted by all the objects in the infrared spectrum. The infrared
sensor detects this type of radiation which is not visible to human
eye.
Fig 7. system representation
Fig 4. IR Sensor
D. Motor Driver
It is a little current amplifier , the function of motor drivers
is to take a low-current signal and then turn it into a
higher-current signal that can drive motor.
Fig 8. screenshot represents phase one detection
Fig 5. Motor Driver
E. Gear Motor VI. CONCLUSION
A small motor (ac induction, permanent magnet dc, or The purpose of the proposed system is to provide a cost
brushless dc) designed specifically with an integral (not effective system for rescue of human in border. The
separable) gear reducer (gear head). The end shield on the proposed system uses a low cost sensor which is easily
drive end of the motor is designed to provide a dual available. It is impossible for an individual to visit the
function. The side facing the motor provides the border. So, in such situations, the proposed system can be
armature/rotor bearing support and a sealing provision useful.
Volume 6, Issue 13 Published by, www.ijert.org 3
Special Issue - 2018 International Journal of Engineering Research & Technology (IJERT)
ISSN: 2278-0181
NCESC - 2018 Conference Proceedings
VII. FUTURE SCOPE
In the future enhancement can be done by incorporating an
IR camera that can exactly capture IR pattern emitted by
human body. Furthermore, metal and bomb detector can
be used to protect from possible damage.
VIII. REFERENCES
[1] Defence Security System: Border Security International Journal
of Innovative Research in Science, Engineering and Technology,
2016
[2] Modeling of IoT-based border protection syste, Hamra
Afzaal, Electrical Engineering and Computing Technologies
(INTELLECT), 2017
[3] Border Security System, International Journal of engineering
and research, 2017 ,KarthiKayan A,
[4] James N. K. Liu, M, Meng Wang, “ iBotGuard: An Internet-
Based Intelligent Robot Security System Using Invariant Face
Recognition Against Intruder”, IEEE Transactions on Systems,
Man, & Cybernetics Part C: Applications and Reviews, Vol. 35,
No.1 February,2005.
[5] Guangming Song et. al., “A Surveillance Robot with Hopping
Capabilities for Home Security”, IEEE Transactions on
Consumer Electronics, Vol. 55,No.4,NOVEMBER,2009.
[6] Mohd.Mazidi, AT89S52 the 8051 micro controller and
embedded systems.
[7] Embedded systems with 8051 by kenith j ayala
[8] Human Motion Detection Using Passive Infra Red Sensor K
Sravani, Md Parvez Ahmed, N Chandra Sekhar, G Sirisha,V
Prasad.
[9] Kenneth G, Eskildsen, Great Neak,”Method and apparatus for
large signal detection in PIR application(2007)
[10] Larry Hurwitz,Alpine,”Apparatus and methods for generating
alerts.(2010).
[11] Wouter dekort (2013) programming in C
[online:www.junglee.com]
[12] Stevenf Barrett,Daniel J.Packand Mitchell a.Thornton(2007)
Atmel AVR microcontroller primer; programming and
interfacing online: www.amazone.in.
Volume 6, Issue 13 Published by, www.ijert.org 4
You might also like
- Military Surveillance Robot: Keywords:-Robot, Arduino Uno, Raspberry Pi, CameraDocument4 pagesMilitary Surveillance Robot: Keywords:-Robot, Arduino Uno, Raspberry Pi, CameraInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Security in IoT Social NetworksFrom EverandSecurity in IoT Social NetworksFadi Al-TurjmanNo ratings yet
- +martin Marinov - Remote Video Eavesdropping Using A Software-De - Ned Radio PlatformDocument78 pages+martin Marinov - Remote Video Eavesdropping Using A Software-De - Ned Radio Platformalex logNo ratings yet
- Theft-Detection Using Motion Sensing Camera: IJISRT17NV31Document8 pagesTheft-Detection Using Motion Sensing Camera: IJISRT17NV31International Journal of Innovative Science and Research TechnologyNo ratings yet
- Body Area Networks using IEEE 802.15.6: Implementing the ultra wide band physical layerFrom EverandBody Area Networks using IEEE 802.15.6: Implementing the ultra wide band physical layerNo ratings yet
- Border Security Using Wireless Integrated Network Sensors (WINS)Document18 pagesBorder Security Using Wireless Integrated Network Sensors (WINS)Pradeep CheekatlaNo ratings yet
- 716camouflage Technology PDFDocument4 pages716camouflage Technology PDFrenatotorresa2803No ratings yet
- Infrared Sensors Hand HeldDocument5 pagesInfrared Sensors Hand HeldEliasNo ratings yet
- Penetration Testing in Wireless Networks: Shree Krishna LamichhaneDocument51 pagesPenetration Testing in Wireless Networks: Shree Krishna LamichhanedondegNo ratings yet
- DATA MINING and MACHINE LEARNING. CLASSIFICATION PREDICTIVE TECHNIQUES: SUPPORT VECTOR MACHINE, LOGISTIC REGRESSION, DISCRIMINANT ANALYSIS and DECISION TREES: Examples with MATLABFrom EverandDATA MINING and MACHINE LEARNING. CLASSIFICATION PREDICTIVE TECHNIQUES: SUPPORT VECTOR MACHINE, LOGISTIC REGRESSION, DISCRIMINANT ANALYSIS and DECISION TREES: Examples with MATLABNo ratings yet
- FPGA - Based Accelerators of Deep LearningNetworks For Learning and ClassificationDocument37 pagesFPGA - Based Accelerators of Deep LearningNetworks For Learning and ClassificationAvinash Baldi100% (1)
- International Journal of Computer Science & Information SecurityDocument92 pagesInternational Journal of Computer Science & Information SecurityDhinaNo ratings yet
- Fundamentals of Biometric AnalysisDocument19 pagesFundamentals of Biometric AnalysisReema MitraNo ratings yet
- Bluetooth Technology: Mobile ComputingDocument12 pagesBluetooth Technology: Mobile Computingrws1000No ratings yet
- Adaptive Biometric Systems A Complete Guide - 2020 EditionFrom EverandAdaptive Biometric Systems A Complete Guide - 2020 EditionNo ratings yet
- Bluetooth Based Smart Sensor NetworksDocument10 pagesBluetooth Based Smart Sensor NetworksSaugat PradhanNo ratings yet
- Analytical Study On Object Detection Using Yolo AlgorithmDocument3 pagesAnalytical Study On Object Detection Using Yolo AlgorithmInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- DSc Research in Digital ForensicsDocument15 pagesDSc Research in Digital ForensicsRajiv Dharaskar100% (1)
- BiometricsDocument12 pagesBiometricssubinjose100% (3)
- Developing Practical Wireless ApplicationsFrom EverandDeveloping Practical Wireless ApplicationsRating: 5 out of 5 stars5/5 (2)
- A Deep Learning Gated Architecture For UGV Navigation Robust To SensorDocument18 pagesA Deep Learning Gated Architecture For UGV Navigation Robust To SensorOscar Ramos SotoNo ratings yet
- Computer Forensics GuideDocument20 pagesComputer Forensics GuideShilpa KanhurkarNo ratings yet
- Artificial Vision For RobotsDocument228 pagesArtificial Vision For RobotsefrainNo ratings yet
- The Little Book of Deep LearningDocument155 pagesThe Little Book of Deep LearningReza SafaiNo ratings yet
- Wireless and Satellite Systems: Qihui Wu Kanglian Zhao Xiaojin DingDocument516 pagesWireless and Satellite Systems: Qihui Wu Kanglian Zhao Xiaojin DingYounis AhmedNo ratings yet
- Different Approaches To Crack Monitoring of Buildings Using IOTDocument11 pagesDifferent Approaches To Crack Monitoring of Buildings Using IOTIJRASETPublicationsNo ratings yet
- Computer VisionDocument4 pagesComputer VisionSurya Mani SharmaNo ratings yet
- MultiAgent SystemsDocument394 pagesMultiAgent SystemsYAHIA MENASSELNo ratings yet
- Fingerprint Recognition Using MATLAB PDFDocument74 pagesFingerprint Recognition Using MATLAB PDFshakil0% (1)
- A Practical Approach To Spectrum Analyzing Unit Using RTL-SDRDocument10 pagesA Practical Approach To Spectrum Analyzing Unit Using RTL-SDRstanpjames2309No ratings yet
- Privacy and Data Security in Internet of Things: Arun Nagaraja and N. RajasekharDocument13 pagesPrivacy and Data Security in Internet of Things: Arun Nagaraja and N. RajasekharrajeshNo ratings yet
- A Review On Unimodal and Multimodal Biometric SystemsDocument8 pagesA Review On Unimodal and Multimodal Biometric SystemsInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Wireless Sensor Networks Application Centric DesignDocument504 pagesWireless Sensor Networks Application Centric Designaminkhan830% (1)
- Healthcare Ecg Using IotDocument5 pagesHealthcare Ecg Using Iotrohitha jpNo ratings yet
- Routing Protocols For Wireless Sensor Networks (WSNS)Document19 pagesRouting Protocols For Wireless Sensor Networks (WSNS)Anonymous uVZ8dZgNo ratings yet
- Hyperspectral ImagingDocument24 pagesHyperspectral Imagingjwt9478No ratings yet
- IOT Communication ModelsDocument20 pagesIOT Communication Modelskhadijaamir435No ratings yet
- MASINT-CommonSensorCOI To M-CS COIDocument25 pagesMASINT-CommonSensorCOI To M-CS COIZainuddin Bin MohamadNo ratings yet
- An Autonomous Wireless Sensor Network Deployment System Using Mobile Robots For Human Existence Detection in Case of DisastersDocument15 pagesAn Autonomous Wireless Sensor Network Deployment System Using Mobile Robots For Human Existence Detection in Case of DisastersAli MaaroufNo ratings yet
- Deep LearningDocument10 pagesDeep LearningKanishka Singh RaghuvanshiNo ratings yet
- Ufc 4-020-04a Electronic Security Systems - Security Engineering, With Change 2 (22 September 2009)Document155 pagesUfc 4-020-04a Electronic Security Systems - Security Engineering, With Change 2 (22 September 2009)Bob VinesNo ratings yet
- AUTOSAR TR ClassicPlatformReleaseOverviewDocument42 pagesAUTOSAR TR ClassicPlatformReleaseOverviewWolfgang StarkmannNo ratings yet
- Information Technology: Submitted To Devendra KohliDocument15 pagesInformation Technology: Submitted To Devendra KohliAbhirup UbaleNo ratings yet
- DeepLearning NetworkingDocument64 pagesDeepLearning NetworkingAnirudh M KNo ratings yet
- Semtech UseCase SmartAgriculture Chipsafer - 101019 (WEB) PDFDocument4 pagesSemtech UseCase SmartAgriculture Chipsafer - 101019 (WEB) PDFmichael007fierroNo ratings yet
- SeminarDocument12 pagesSeminarNAVEEN KUMAR100% (1)
- Ultra Wide Band Radio Technology (UWB) (B-TECH SEMINAR REPORT)Document93 pagesUltra Wide Band Radio Technology (UWB) (B-TECH SEMINAR REPORT)v2brotherNo ratings yet
- Wearable Movement Sensors For Rehabilitation A Focused Reviewof Technological and Clinical AdvancesDocument13 pagesWearable Movement Sensors For Rehabilitation A Focused Reviewof Technological and Clinical AdvancesJenner FeijoóNo ratings yet
- Security Issues and Vulnerability ofDocument16 pagesSecurity Issues and Vulnerability ofMuthuKumar RajendranNo ratings yet
- Phased Array System Toolbox™ ReferenceDocument1,698 pagesPhased Array System Toolbox™ ReferenceVictor Colpo NavarreteNo ratings yet
- Wireless Sensor NetworksDocument24 pagesWireless Sensor NetworksTanvi SharmaNo ratings yet
- Image Processing Techniques For Object Tracking in Video Surveillance - A Survey 2015-2Document6 pagesImage Processing Techniques For Object Tracking in Video Surveillance - A Survey 2015-2musalmanmusalmanNo ratings yet
- Brain Finger Printing TechnologyDocument12 pagesBrain Finger Printing Technologypinks_dollsNo ratings yet
- Lecture02 PDFDocument3 pagesLecture02 PDFNagaraj HNo ratings yet
- Border Security RobotDocument9 pagesBorder Security RobotJames MorenoNo ratings yet
- RV 2nd SlotDocument2 pagesRV 2nd SlotMohana H SNo ratings yet
- Intrusion Detection Using Iot: Nilamadhab Mishra, Sarojananda MishraDocument6 pagesIntrusion Detection Using Iot: Nilamadhab Mishra, Sarojananda MishraNagaraj HNo ratings yet
- Automatic Enemy Detecting Defense Robot by Using Face Detection TechniqueDocument7 pagesAutomatic Enemy Detecting Defense Robot by Using Face Detection TechniqueNagaraj HNo ratings yet
- Automatic Enemy Detecting Defense Robot by Using Face Detection TechniqueDocument7 pagesAutomatic Enemy Detecting Defense Robot by Using Face Detection TechniqueNagaraj HNo ratings yet
- Border Security RobotDocument9 pagesBorder Security RobotJames MorenoNo ratings yet
- Real Time Systems 7th Sem ECE VTU Unit 1 Introduction To Real Time Systems Ramisuniverse PDFDocument10 pagesReal Time Systems 7th Sem ECE VTU Unit 1 Introduction To Real Time Systems Ramisuniverse PDFharshithaysNo ratings yet
- Vehicle Speed Limiter Project: Block DiagramDocument4 pagesVehicle Speed Limiter Project: Block DiagramSai Santosh KumarNo ratings yet
- RV 2nd SlotDocument2 pagesRV 2nd SlotMohana H SNo ratings yet
- .Design and Implementation of Web Surveillance Robot For Video Monitoring and Motion DetectionDocument5 pages.Design and Implementation of Web Surveillance Robot For Video Monitoring and Motion DetectionNagaraj HNo ratings yet
- Fundamentals of Pervasive Computing SyllabusDocument3 pagesFundamentals of Pervasive Computing SyllabusFarha Shah100% (1)
- iMouse Integrated Mobile Surveillance & Wireless Sensor SystemDocument20 pagesiMouse Integrated Mobile Surveillance & Wireless Sensor Systemb.sreevatsavaNo ratings yet
- Iot and Wireless Sensor Network Based Autonomous Farming RobotDocument5 pagesIot and Wireless Sensor Network Based Autonomous Farming RobotAli WaqasNo ratings yet
- Energy-Efficient Routing Protocols For WSN: A Systematic Literature ReviewDocument11 pagesEnergy-Efficient Routing Protocols For WSN: A Systematic Literature ReviewWARSE JournalsNo ratings yet
- IAT-II Question Paper With Solution of 15EC752 IoT and Wireless Sensor Networks Oct-2018-Richa, EishaDocument21 pagesIAT-II Question Paper With Solution of 15EC752 IoT and Wireless Sensor Networks Oct-2018-Richa, Eishasrujana hulkoduNo ratings yet
- IoT Patient Monitoring System for COVID-19 Patients in Home Based CareDocument74 pagesIoT Patient Monitoring System for COVID-19 Patients in Home Based CareGrace JosephNo ratings yet
- BiTs ElectronicsDocument3 pagesBiTs ElectronicselectronicartNo ratings yet
- Personal Health Monitoring System Using Arduino and Android IJERTCONV4IS22014Document5 pagesPersonal Health Monitoring System Using Arduino and Android IJERTCONV4IS22014Yasir Yasir KovanNo ratings yet
- Identification of Digital Technologies and Digitalisation Trends in Themining Industrylars Barnewold, Bernd G. Lottermoser PDFDocument11 pagesIdentification of Digital Technologies and Digitalisation Trends in Themining Industrylars Barnewold, Bernd G. Lottermoser PDFFlavianRSNo ratings yet
- Ieee Wireless Sensor4Document11 pagesIeee Wireless Sensor4Dr-Raghad Al-FahamNo ratings yet
- BMF AngelaDocument100 pagesBMF Angelacoco_euNo ratings yet
- CSE IndexDocument13 pagesCSE IndexVenkatesh ThirugnanasambandamNo ratings yet
- Smart Sensors For Smart AgricultureDocument426 pagesSmart Sensors For Smart AgricultureAziza GarouachiNo ratings yet
- IoT and WSN Based Smart Home Health and Wellness SeminarDocument48 pagesIoT and WSN Based Smart Home Health and Wellness SeminarNisumba SoodhaniNo ratings yet
- 2021emb Projects ListDocument49 pages2021emb Projects ListSai PraneethNo ratings yet
- An Extended K-Means Cluster Head Selection Algorithm For Efficient Energy Consumption in Wireless Sensor NetworksDocument19 pagesAn Extended K-Means Cluster Head Selection Algorithm For Efficient Energy Consumption in Wireless Sensor NetworksAIRCC - IJNSANo ratings yet
- Iot With pythonDocument68 pagesIot With pythonPriyanshuNo ratings yet
- Sabrina Wallace - Where Do The MAC IDs Come FromDocument5 pagesSabrina Wallace - Where Do The MAC IDs Come FromGeneration GenerationNo ratings yet
- 1 - R000 Redwood Solutions Brochure 107696Document8 pages1 - R000 Redwood Solutions Brochure 107696Asdrubal KakakianNo ratings yet
- Sensors: Low-Cost Air Quality Monitoring Tools: From Research To Practice (A Workshop Summary)Document20 pagesSensors: Low-Cost Air Quality Monitoring Tools: From Research To Practice (A Workshop Summary)SATRIONo ratings yet
- Research On Channel ModelingDocument16 pagesResearch On Channel ModelingSajal SouravNo ratings yet
- WSN Protocol Layers and MAC ProtocolsDocument12 pagesWSN Protocol Layers and MAC ProtocolsUk'xRoXzNo ratings yet
- Hawassa University Institute of TechnologyDocument14 pagesHawassa University Institute of TechnologybinyamNo ratings yet
- Industry 4.0 Architecture and Cyber-Physical SystemsDocument41 pagesIndustry 4.0 Architecture and Cyber-Physical SystemsRaul Gonzales RuizNo ratings yet
- Design and Implementation of A Prototype Smart Parking (Spark) System Using Wireless Sensor NetworksDocument6 pagesDesign and Implementation of A Prototype Smart Parking (Spark) System Using Wireless Sensor NetworksDr-Surendra Kumar ShuklaNo ratings yet
- IOT Fire Detection System Using Sensor With Arduino: Cite This PaperDocument6 pagesIOT Fire Detection System Using Sensor With Arduino: Cite This Papersteven borollaNo ratings yet
- A Mini Project Report ON: Air Pollution Monitoring System Using LabviewDocument47 pagesA Mini Project Report ON: Air Pollution Monitoring System Using LabviewSaarika VedanshiNo ratings yet
- Impact of E-Learning Student Portal For The Department: ArticleDocument19 pagesImpact of E-Learning Student Portal For The Department: ArticleLuise MauieNo ratings yet
- A Novel Approach For Finding Optimal Number of Cluster Head in Wireless Sensor NetworkDocument5 pagesA Novel Approach For Finding Optimal Number of Cluster Head in Wireless Sensor NetworkbhanupartapsharmaNo ratings yet
- Classification Techniques for Detecting DoS Attacks in WSNsDocument6 pagesClassification Techniques for Detecting DoS Attacks in WSNsIshmael OkineNo ratings yet