Professional Documents
Culture Documents
Diffie Hellman PDF
Uploaded by
sushma0 ratings0% found this document useful (0 votes)
23 views6 pagesOriginal Title
diffie hellman.pdf
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
23 views6 pagesDiffie Hellman PDF
Uploaded by
sushmaCopyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 6
Foundations of Computer Security
Lecture 52: Diffie-Hellman Key Exchange
Dr. Bill Young
Department of Computer Sciences
University of Texas at Austin
Lecture 52: 1 Diffie-Hellman Key Exchange
Diffie-Hellman Key Exchange
The question of key exchange was one of the first problems
addressed by a cryptographic protocol. This was prior to the
invention of public key cryptography.
The Diffie-Hellman key agreement protocol (1976) was the first
practical method for establishing a shared secret over an unsecured
communication channel.
The point is to agree on a key that two parties can use for a
symmetric encryption, in such a way that an eavesdropper cannot
obtain the key.
Lecture 52: 2 Diffie-Hellman Key Exchange
Diffie-Hellman Algorithm
(g A mod p)
Alice Bob
(knows p, g, A) (knows p, g, B)
(g B mod p)
Steps in the algorithm:
1 Alice and Bob agree on a prime number p and a base g .
2 Alice chooses a secret number a, and sends Bob (g a mod p).
3 Bob chooses a secret number b, and sends Alice (g b mod p).
4 Alice computes ((g b mod p)a mod p).
5 Bob computes ((g a mod p)b mod p).
Both Alice and Bob can use this number as their key. Notice that
p and g need not be protected.
Lecture 52: 3 Diffie-Hellman Key Exchange
Diffie-Hellman Example
1 Alice and Bob agree on p = 23 and g = 5.
2 Alice chooses a = 6 and sends 56 mod 23 = 8.
3 Bob chooses b = 15 and sends 515 mod 23 = 19.
4 Alice computes 196 mod 23 = 2.
5 Bob computes 815 mod 23 = 2.
Then 2 is the shared secret.
Clearly, much larger values of a, b, and p are required. An
eavesdropper cannot discover this value even if she knows p and g
and can obtain each of the messages.
Lecture 52: 4 Diffie-Hellman Key Exchange
Diffie-Hellman Security
Suppose p is a prime of around 300 digits, and a and b at least
100 digits each.
Discovering the shared secret given g , p, g a mod p and g b
mod p would take longer than the lifetime of the universe, using
the best known algorithm. This is called the discrete logarithm
problem.
Lecture 52: 5 Diffie-Hellman Key Exchange
Lessons
How can two parties agree on a secret value when all of their
messages might be overheard by an eavesdropper?
The Diffie-Hellman algorithm accomplishes this, and is still
widely used.
With sufficiently large inputs, Diffie-Hellman is very secure.
Next lecture: Digital Signatures
Lecture 52: 6 Diffie-Hellman Key Exchange
You might also like
- Diffie-Hellman Key ExchangeDocument5 pagesDiffie-Hellman Key ExchangeNikitaNo ratings yet
- Foundations of Computer Security: Lecture 52: Diffie-Hellman Key ExchangeDocument6 pagesFoundations of Computer Security: Lecture 52: Diffie-Hellman Key ExchangegingeevimalNo ratings yet
- Cryptography 3Document25 pagesCryptography 3Venera MakhambayevaNo ratings yet
- Diffie-Hellman Key ExchangeDocument6 pagesDiffie-Hellman Key Exchangesrk291No ratings yet
- Diffie-Hellman Key Exchange PDFDocument6 pagesDiffie-Hellman Key Exchange PDFZxzxzxz007No ratings yet
- Diffie-Hellman Key ExchangeDocument20 pagesDiffie-Hellman Key ExchangecezilcNo ratings yet
- Diffie-Hellman Key ExchangeDocument7 pagesDiffie-Hellman Key ExchangedeekshantNo ratings yet
- Elliptic Curve CryptographyDocument30 pagesElliptic Curve CryptographyAsha MuruganNo ratings yet
- Wiki Diffie-HellmanDocument7 pagesWiki Diffie-HellmanBerry HoekstraNo ratings yet
- Diffie-Hellman Key ExchangeDocument6 pagesDiffie-Hellman Key ExchangeMilica LukicNo ratings yet
- Cns 13 Exp VineshDocument2 pagesCns 13 Exp Vineshvinesh ryapakNo ratings yet
- Diffie-Hellman and Its Application in Security Protocols: ISO 9001:2008 CertifiedDocument5 pagesDiffie-Hellman and Its Application in Security Protocols: ISO 9001:2008 CertifiedHarish KumarNo ratings yet
- Assignment No 6Document3 pagesAssignment No 6spNo ratings yet
- TBS Answer Question No 1Document2 pagesTBS Answer Question No 1deepNo ratings yet
- Diffie Hellman WriteupDocument3 pagesDiffie Hellman WriteupSumitThoratNo ratings yet
- Prac V1Document4 pagesPrac V1Niket BhaleraoNo ratings yet
- Cys535 Lecture06Document37 pagesCys535 Lecture06Waseem LaghariNo ratings yet
- Transposition Techniques (Class-L7)Document49 pagesTransposition Techniques (Class-L7)Mahender Taneja0% (1)
- ISS Module 5,6 Searchable - MergedDocument45 pagesISS Module 5,6 Searchable - MergedjangalasidduNo ratings yet
- Exp 05Document4 pagesExp 0548Nara Amit GopalNo ratings yet
- Diffie HellmanDocument1 pageDiffie HellmanAhmed HeshamNo ratings yet
- Cryptography and Network Security: Fifth Edition by William StallingsDocument41 pagesCryptography and Network Security: Fifth Edition by William StallingsDineshkumar SNo ratings yet
- Diffie Hellman AlgorithmDocument11 pagesDiffie Hellman Algorithmjoxy johnNo ratings yet
- Class+Notes5 Diffie+Hellman+Key+Exchange+AlgorithmDocument2 pagesClass+Notes5 Diffie+Hellman+Key+Exchange+Algorithmk5c6hdvmq7No ratings yet
- Aim: To Implement Diffiehellman Key Exchange Protocol. Theory: Diffiehellman Key Exchange Is A Cryptographic Protocol That Allows TwoDocument3 pagesAim: To Implement Diffiehellman Key Exchange Protocol. Theory: Diffiehellman Key Exchange Is A Cryptographic Protocol That Allows Twocreative_g33kNo ratings yet
- Motivation For Key Exchange AlgorithmDocument3 pagesMotivation For Key Exchange AlgorithmDejene TechaneNo ratings yet
- NS2 CryptoProtocolsIIDocument46 pagesNS2 CryptoProtocolsIIThai TranNo ratings yet
- Group Theory in CS: Cryptography, Diffie-Hellman, and Elliptic CurvesDocument5 pagesGroup Theory in CS: Cryptography, Diffie-Hellman, and Elliptic CurvesMihir VahanwalaNo ratings yet
- Group B-Assignment No. 1 : CNSL Te-ItDocument3 pagesGroup B-Assignment No. 1 : CNSL Te-ItPriyanshu AgrawalNo ratings yet
- Diffle HuffmanDocument29 pagesDiffle HuffmanAnkit RajNo ratings yet
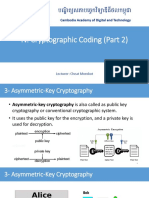
- 4.2. Cryptographic Coding (Part 2)Document27 pages4.2. Cryptographic Coding (Part 2)ReachNo ratings yet
- PR5 Diffie Hellman FinalDocument4 pagesPR5 Diffie Hellman FinalprafullaNo ratings yet
- Diffie Hellman Key ExchangeDocument8 pagesDiffie Hellman Key ExchangeAnonymous SNij6R3PNo ratings yet
- Deffiehellman AlgoDocument6 pagesDeffiehellman Algoparidhiagarwal129No ratings yet
- CHAPTER 05 - Public-Key CryptographyDocument29 pagesCHAPTER 05 - Public-Key CryptographyPNo ratings yet
- Implementation of Diffie-Hellman Algorithm - GeeksforGeeksDocument6 pagesImplementation of Diffie-Hellman Algorithm - GeeksforGeeksGodwin K NyamukondiwaNo ratings yet
- PR5 Diffie Hellman FinalDocument4 pagesPR5 Diffie Hellman FinalprafullaNo ratings yet
- What Is: Voice Over Internet Protocol (Also Called Voip, Ip Telephony, Internet TelephonyDocument9 pagesWhat Is: Voice Over Internet Protocol (Also Called Voip, Ip Telephony, Internet Telephonybansalanuj24No ratings yet
- GP Report (Key Exchange)Document20 pagesGP Report (Key Exchange)Manish 'MySt' SinghNo ratings yet
- Dttf/Nb479: Dszquphsbqiz Day 25: FT Latedaysle AvgDocument8 pagesDttf/Nb479: Dszquphsbqiz Day 25: FT Latedaysle AvgMaulik DantaraNo ratings yet
- Public Key AlgorithmsDocument9 pagesPublic Key AlgorithmsCharishmaNo ratings yet
- Cryptography and Network SecurityDocument9 pagesCryptography and Network SecurityMestar PrincessNo ratings yet
- CSE 5636 - Network Security CYB 5290 - Secure Data Communica Ons and Networks Public Key Cryptography IDocument21 pagesCSE 5636 - Network Security CYB 5290 - Secure Data Communica Ons and Networks Public Key Cryptography IVikram GuptaNo ratings yet
- 03 ZKDocument2 pages03 ZKDaudet Polycarpe TiomelaNo ratings yet
- Lecture 07Document15 pagesLecture 07Mushtaq AhmadNo ratings yet
- Publickey CrptographyDocument12 pagesPublickey CrptographyDhanapal AngNo ratings yet
- NS2-Cryptographic Protocols IIDocument46 pagesNS2-Cryptographic Protocols IICảnhNo ratings yet
- Public Cryptosystem RDocument12 pagesPublic Cryptosystem RgamerNo ratings yet
- Public Key Cryptography: EJ JungDocument12 pagesPublic Key Cryptography: EJ JungsharnobyNo ratings yet
- Diffie-Hellman Key Exchange: The SetupDocument2 pagesDiffie-Hellman Key Exchange: The SetupRam BabuNo ratings yet
- Odlyzko1 PsDocument10 pagesOdlyzko1 PsAmador Perez LopezNo ratings yet
- The Discrete Logarithm ProblemDocument5 pagesThe Discrete Logarithm ProblemSushil AzadNo ratings yet
- CHAPTER 5: Public-Key Cryptography I. RSA: Two Different KeysDocument43 pagesCHAPTER 5: Public-Key Cryptography I. RSA: Two Different KeysMin KhantNo ratings yet
- Cryptography: N Participants Is A Method of Encoding A 'Secret'Document19 pagesCryptography: N Participants Is A Method of Encoding A 'Secret'lakshman_kumar0416No ratings yet
- Public Key CryptographyDocument35 pagesPublic Key CryptographyFaReeD HamzaNo ratings yet
- Diffie HellmanDocument2 pagesDiffie Hellmanapi-3737802No ratings yet
- Cryptography and Network Security Chapter 10: Chapter 10 - Other Public Key CryptosystemsDocument5 pagesCryptography and Network Security Chapter 10: Chapter 10 - Other Public Key CryptosystemsA L P H ANo ratings yet
- Lecture 23Document26 pagesLecture 23saminayeem2No ratings yet
- ASCLD/LAB-International: Supplemental Requirements For The Accreditation of Forensic Science Testing LaboratoriesDocument35 pagesASCLD/LAB-International: Supplemental Requirements For The Accreditation of Forensic Science Testing LaboratoriessushmaNo ratings yet
- INCS 741: Cryptography: Hash and MAC AlgorithmsDocument15 pagesINCS 741: Cryptography: Hash and MAC AlgorithmssushmaNo ratings yet
- Cryptography and Network Security: Fifth Edition by William StallingsDocument33 pagesCryptography and Network Security: Fifth Edition by William Stallingspowe2ajNo ratings yet
- K Dsa PDFDocument4 pagesK Dsa PDFsushmaNo ratings yet
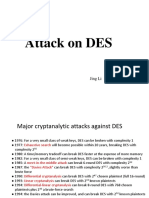
- Atttack On DESDocument33 pagesAtttack On DEStejashwiniNo ratings yet
- Taxonomy of Parallel Computing ParadigmsDocument9 pagesTaxonomy of Parallel Computing ParadigmssushmaNo ratings yet
- Lab 2 - 4th Chemistry 2023-2024Document3 pagesLab 2 - 4th Chemistry 2023-2024christismithjaNo ratings yet
- Seragam MPP UnitDocument15 pagesSeragam MPP UnitKangen HijauNo ratings yet
- Scientific Researcher in Medical PowerPoint TemplatesDocument34 pagesScientific Researcher in Medical PowerPoint TemplatesnitsauNo ratings yet
- UntitledDocument10 pagesUntitledZain AhmadNo ratings yet
- Lee Cristine Anne M. Bsa 2BDocument7 pagesLee Cristine Anne M. Bsa 2Bkristine torresNo ratings yet
- AChew 2Document34 pagesAChew 2IISER MOHALINo ratings yet
- Bernyanyi Lagu PopulerDocument52 pagesBernyanyi Lagu Populerwinda100% (1)
- sHIMADZU - Specification Sheet - LCMS-8050Document2 pagessHIMADZU - Specification Sheet - LCMS-8050luisruedaNo ratings yet
- UV Visible SpectrophotometryDocument7 pagesUV Visible SpectrophotometryMircamal QafarliNo ratings yet
- Graphic Infographic Designed: ALLPPT Layout Clean Text Slide For Your PresentationDocument42 pagesGraphic Infographic Designed: ALLPPT Layout Clean Text Slide For Your Presentationsofta novaNo ratings yet
- What Is Atomic Absorption Spectroscopy?: Atomization System, The Monochromator and The Detection System (Figure 1)Document3 pagesWhat Is Atomic Absorption Spectroscopy?: Atomization System, The Monochromator and The Detection System (Figure 1)Belal FatahNo ratings yet
- Businessman Hand Golden Key PowerPoint TemplatesDocument48 pagesBusinessman Hand Golden Key PowerPoint Templatesdeni wahyudinNo ratings yet
- Rumusan Kursus Permohonan Reman Dan Permohonan Pelbagai Kes JenayahDocument34 pagesRumusan Kursus Permohonan Reman Dan Permohonan Pelbagai Kes JenayahApulNo ratings yet
- USP43 Methacholine ChlorideDocument2 pagesUSP43 Methacholine ChlorideAlejandro RestrepoNo ratings yet
- Linear Arrangement With Two Variable Questions Specially For Sbi Po PrelimsDocument42 pagesLinear Arrangement With Two Variable Questions Specially For Sbi Po PrelimsAKaSh DAsNo ratings yet
- A Practical Guide To Microstructural Analysis of Cementitious MaterialsDocument3 pagesA Practical Guide To Microstructural Analysis of Cementitious Materialsኦርቶዶክስ ተዋህዶNo ratings yet
- TELPON SEKARANG Telp WA 0821 1305 0400 Fundamental Parameters XRF Kab. Minahasa Selatan Sulawesi UtaraDocument4 pagesTELPON SEKARANG Telp WA 0821 1305 0400 Fundamental Parameters XRF Kab. Minahasa Selatan Sulawesi UtarajoniNo ratings yet
- Dolls House World - November 2016Document84 pagesDolls House World - November 2016viento100% (2)
- DCC40132 Topic 4 Planning SchedulingDocument59 pagesDCC40132 Topic 4 Planning SchedulingMuhd FareezNo ratings yet
- Forensics High School Complete ListdocxDocument3 pagesForensics High School Complete Listdocxshah bohtanNo ratings yet
- Legal Med Word SearchDocument1 pageLegal Med Word SearchLEANNE RUMBAOANo ratings yet
- CH 135 Exam II A KeyDocument6 pagesCH 135 Exam II A Keynguyen ba trungNo ratings yet
- Answer to A PERT network consists of the activities in the following list. Times are given in weeks. Activity a m b Б Predecessor..Document3 pagesAnswer to A PERT network consists of the activities in the following list. Times are given in weeks. Activity a m b Б Predecessor..vinayak kapoorNo ratings yet
- Analisis Jejas Gigitan Pada Kasus Forensik Klinik: Erwin KristantoDocument7 pagesAnalisis Jejas Gigitan Pada Kasus Forensik Klinik: Erwin KristantoNurul FajrinaNo ratings yet
- Dna Fingerprinting WorksheetDocument3 pagesDna Fingerprinting WorksheetBailey PoeNo ratings yet
- An Introduction To Surface Analysis by XPS and AES. John F. Watts and John Wolstenholme An Introduction To Surface Analysis by XPS and AES. John F. Watts and John WolstenholmeDocument18 pagesAn Introduction To Surface Analysis by XPS and AES. John F. Watts and John Wolstenholme An Introduction To Surface Analysis by XPS and AES. John F. Watts and John WolstenholmeRahul GhoshNo ratings yet
- Isolasi Dan Pemisahan Senyawa Alkaloid Dari Buah Mahkota DEWA (Phaleria Macrocarpa Boerl.) DENGAN METODE KROMATOGRAFI CAIRDocument7 pagesIsolasi Dan Pemisahan Senyawa Alkaloid Dari Buah Mahkota DEWA (Phaleria Macrocarpa Boerl.) DENGAN METODE KROMATOGRAFI CAIRFitra DamanhuryNo ratings yet
- Art APPDocument25 pagesArt APPRey DordasNo ratings yet
- Determination of Beer ColorDocument2 pagesDetermination of Beer ColorRubens MattosNo ratings yet
- Gravel Flushing 20221222Document14 pagesGravel Flushing 20221222Arjun PandeyNo ratings yet