Professional Documents
Culture Documents
Unit 14 Business Intelligence Holistic Assignment Adjusted IV 2019.02.07
Uploaded by
Dasun IsharaOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Unit 14 Business Intelligence Holistic Assignment Adjusted IV 2019.02.07
Uploaded by
Dasun IsharaCopyright:
Available Formats
Higher Nationals
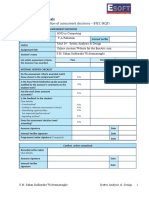
Internal verification of assessment decisions – BTEC (RQF)
INTERNAL VERIFICATION – ASSESSMENT DECISIONS
Programme title
Assessor Internal Verifier
Unit 14: Business Intelligence
1|Page
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Unit(s)
Assignment title
Pradeeban.A
Student’s name
List which assessment criteria Pass Merit Distinction
the Assessor has awarded.
2|Page
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
INTERNAL VERIFIER CHECKLIST
Do the assessment criteria awarded match
those shown in the assignment brief?
Y/N
Is the Pass/Merit/Distinction grade awarded
justified by the assessor’s comments on the Y/N
student work?
Has the work been assessed
accurately?
Y/N
Is the feedback to the student:
Give details:
• Constructive?
3|Page
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
• Linked to relevant assessment criteria?
• Identifying opportunities for Y/N
improved performance? Y/N
• Agreeing actions? Y/N
Y/N
Does the assessment decision need
amending?
Y/N
4|Page
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Assessor signature Date
Internal Verifier signature Date
Programme Leader signature (if required)
Date
Confirm action completed
Remedial action taken
Give details:
5|Page
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Assessor signature Date
Internal Verifier
signature
Date
Programme Leader
signature (if required)
Date
6|Page
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Higher Nationals - Summative Assignment Feedback Form
Student Name/ID Pradeeban.A / COL-A -064620
Unit 14: Business Intelligence
Unit Title
Assignment Number Assessor
Date Received
1st submission
Submission Date
7|Page
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Date Received 2nd
submission
Re-submission Date
Assessor Feedback:
LO1 Discuss business processes and the mechanisms used to support business decision-making.
Pass, Merit & Distinction P1
Descripts P2
D1
LO2 Compare the tools and technologies associated with business intelligence functionality.
8|Page
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Pass, Merit & Distinction P2
Descripts M2
D2
LO3 Demonstrate the use of business intelligence tools and technologies
Pass, Merit & Distinction P3
Descripts P4
M3
D3
LO4 Discuss the impact of business intelligence tools and technologies for
effective decision-making purposes and the legal/regulatory context in which
they are used.
Pass, Merit & Distinction P5
P6
9|Page
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Descripts M4
D4
Grade: Assessor Signature: Date:
Resubmission Feedback:
Grade: Assessor Signature: Date:
10 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Internal Verifier’s Comments:
Signature & Date:
* Please note that grade decisions are provisional. They are only confirmed once internal and external moderation has taken place and
grades decisions have been agreed at the assessment board.
Assignment Feedback
Formative Feedback: Assessor to Student
Action Plan
11 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Summative feedback
12 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Feedback: Student to Assessor
Assessor Date
signature
Student Date
signature
13 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Pearson Higher Nationals in
Computing
Unit 14: Business Intelligence
14 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Assignment 01
15 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
General Guidelines
1. A cover page or title page should be attached to your assignment. Use page 1 of this assignment
brief as your cover page and make sure all details are accurately filled.
2. The entire assignment brief should be attached as the first section of your assignment.
3. The assignment should be prepared using a word processing software.
4. The assignment should be word processing in an A4 sized paper.
5. Allow 1” margin on top, bottom and right sides of the paper and 1.25” on the left side (for
binding).
Word Processing Rules
16 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
1. The font size should be 12 point, and should be in the style of Time New Roman.
2. Set line spacing to 1.5. Justify all paragraphs.
3. Ensure that all headings are consistent in terms of size and font style.
4. Use footer function on the word processor to insert your name, unit, assignment no, and page
number on each page. This is useful if individual sheets get detached from the submission.
5. Use the spell check and grammar check function of the word processing application to review
the use of language on your assignment.
17 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Important Points:
1. Carefully check carefully the hand in date and the instructions given with the assignment. Late
submissions will not be accepted.
2. Ensure that sufficient time is spent to complete the assignment by the due date.
3. Do not wait till the last minute to get feedback on the assignment. Such excuses will not be
accepted for late submissions.
4. You must be responsible for efficient management of your time.
5. If you are unable to hand in your assignment on time and have valid reasons such as illness, you
may apply (in writing) for an extension.
6. Failure to achieve at least a PASS grade will result in a REFERRAL grade.
7. Non-submission of work without valid reasons will lead to an automatic REFERRAL. You will
then be asked to complete an alternative assignment.
8. If you use other people’s work or ideas in your assignment, it must be properly referenced, using
the HARVARD referencing system, in your text or any bibliography. Otherwise, you’ll be found
guilty of committing plagiarism.
9. If you are caught plagiarising, your grade will be reduced to a REFERRAL or at worst, you could
be excluded from the course.
18 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
19 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Student Declaration
I hereby, declare that I know what plagiarism entails, namely to use another’s work and to present it as
my own without attributing the sources in the correct form. I further understand what it means to
copy another’s work.
1. I know that plagiarism is a punishable offence because it constitutes theft.
2. I understand the plagiarism and copying policy of Edexcel UK.
3. I know what the consequences will be if I plagiarise or copy another’s work in any of the
assignments for this program.
4. I declare therefore that all work presented by me for every aspect of my program, will be my
own, and where I have made use of another’s work, I will attribute the source in the correct
way.
5. I acknowledge that the attachment of this document signed or not, constitutes a binding
agreement between myself and Edexcel UK.
6. I understand that my assignment will not be considered as submitted if this document is not
attached to the assignment.
20 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
ddeeban44@gmail.com 25/12/2020
Student’s Signature: Date:
(Provide E-mail ID) (Provide Submission Date)
21 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Higher National Diploma in Business
Assignment Brief
Student Name /ID Number Pradeeban.A / COL/A-064620
Unit Number and Title Unit 14 : Business Intelligence
Academic Year 2017/18
Unit Tutor
22 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Assignment Title Business Process Support Mechanisms
Issue Date
Submission Date
IV Name & Date
Submission format
23 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Submission to include:
Part 1: The submission is in the form of an individual written report. This should be written in a
concise, formal business style using single spacing and font size 12. You are required to make use
of headings, paragraphs and subsections as appropriate, and all work must be supported with
research and referenced using the Harvard referencing system. Please also provide a bibliography
using the Harvard referencing system. The recommended word limit is 2,000–2,500 words,
although you will not be penalised for exceeding the total word limit.
Part 2: Comprehensive table
Part 3: The submission is in the form of a ten-minute Microsoft® PowerPoint® style presentation.
The presentation can include links to performance data with additional speaker notes and a
bibliography using the Harvard referencing system. The presentation slides for the findings should
be submitted with speaker notes as one copy. You are required to make effective use of headings,
bullet points and subsections, as appropriate. Your research should be referenced using the Harvard
referencing system. The recommended word limit is 500 words, including speaker notes, although
you will not be penalised for exceeding the total word limit.
Unit Learning Outcomes:
24 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
LO1 Discuss business processes and the mechanisms used to support business decision-
making.
LO2 Compare the tools and technologies associated with business intelligence functionality
LO3 Demonstrate the use of business intelligence tools and technologies
LO4 Discuss the impact of business intelligence tools and technologies for effective decision-
making purposes and the legal/regulatory context in which they are used
25 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Assignment Brief and Guidance:
Business processes are pivotal to the operation, functionality and accomplishment of
organisational goals. As a collection or set of tasks/activities, business processes ensure that
the end goal of delivering a service or product to a customer is accomplished successfully.
Scenario:
Data and information is core to any organization and business process. The necessity of
26 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
having meaningful information is the key driver for effective decision making and problem-
solving. Business intelligence has evolved from technologies such as decision support systems
(DSS) to include tools and methods associated with data mining, data integration, data quality
and data warehousing in conjunction with other information management systems and
applications.
Suppose you are recently recruited as a Business Analyst to a leading Sri Lankan
Organisation. As your initial project, you are required to prepare a management report to
the Board of Directors including the following details.
Task 1:
Background details of the organization.
Identify and explain different business processes and supporting processes models used at the
selected organisation with examples .
Explain data that have been used by the different process models given above.
27 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Differentiation between data classification based on the selected organisation in terms of
structured, semi structured and unstructured.
What are the application software used in the given process models.
Evaluate the benefits and drawbacks of using application software as a mechanism for
business processing.
Discuss on business intelligence functionalities and the tools and techniques associated with
them using specific examples chosen from the selected organization processing.
Part 2
Compare the tools and technologies associated with the business intelligence
functionalities and support available for business decision making at various levels within
28 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
the organization
Compare the types of support available for Business Decision making at different
levels of the organizational structure
What are the business intelligence tools commonly used in selected organization?
Justify with specific examples of the key features of business intelligence
functionality
Part 3
Design a simple business intelligence tool/application with user friendly and functional
interfaces that can perform a specific task to support problem solving or decision
making at an advanced level the selected organization.
Provide a critical review of the design in terms of how it meets a specific user or business
requirement and identify what customization has been integrated into the design.
29 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Task 4
4.1Discuss the importance and the impact of business intelligence tools and technologies that
can be used by the organization for effective decision making
4.2Describe the legal/ regulatory issues involved in the secure exploitation of business
intelligence tools in an organization. What are the legal issues you can identify in the system
designed by you.
Identify new Business Intelligence trends and technologies that can be further enhance the
operational activities in the selected organizational context
Evaluate how organizations could use business intelligence to extend their target audience
and make them more competitive within the market, taking security legislation into
consideration
30 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Contents
31 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Introduction Business intelligence (BI)..........................................................................................19
Task 1.............................................................................................................................................21
1.1 Background details of the organization..................................................................................21
1.2 Business processing.................................................................................................................22
PLUCKING...................................................................................................................................22
WITHERING................................................................................................................................22
ROLLING.....................................................................................................................................22
FERMENTATION.........................................................................................................................23
DRYING.......................................................................................................................................23
GRADING (SIFTING)....................................................................................................................23
GRADING (SIFTING)....................................................................................................................24
Business Supporting process.........................................................................................................24
raw materials are easy to access...............................................................................................24
Supporting Infrastructure..........................................................................................................24
Reputation.................................................................................................................................25
High demand, both domestically and internationally...............................................................25
Quality Standards.......................................................................................................................26
Value Addition...........................................................................................................................26
Lion Logo....................................................................................................................................27
32 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
33 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Introduction Business intelligence (BI)
Business intelligence (BI) has been proliferated due to its increasing contribution to such as
business performance determination, data integration from disparate sources, data warehousing,
planning, forecasting, budgeting, and the decision making that guides business operation toward
desired performance (Singh and Singh, 2013). BI’s growing contribution to the business growing
34 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
performance has been recognized particularly for small and medium enterprises (SMEs) (Guarda
et al., 2013) through improving decision support (Singh and Singh, 2013). Nowadays BI
becomes an emerging trend in administering the decision making for conducting the changing
environment (Isık et al., 2013), and learning to take opportunities emerging form changing
circumstances (Guarda et al., 2013).
BI is an information system (IS) led application that integrates the process and technology to
lead to the decision making for managers and end users (Miah, 2014). It plays a significant role
in analysing the business environment and providing the decision making in achieving
competitive advantages emerging from uncertain often changes within the environment (Burton
et al., 2006, Isık et al., 2013). The current business environment is characterised with geopolitics
and economic power (Lenssen et al., 2012), complexity of new information, free market trading,
and high intensity of competition because of rapid acceleration of technological advancement
(Chi et al., 2009).
The growing rate of technological advancement amplified industrial revolution in the world
(Orlikowski and Barley, 2001). Growing effects of information systems, new emergent in
technology, rapid industrial revolution, and the globalization (Al-ma, 2013) cause business
environment is progressively being more turbulent (Cavalcante et al., 2011), which is beyond the
management capacity of SMEs. Newness in the business competition creates new opportunities
and threats for businesses (Stodder, 2013), which become the issue of business survival and
development. Taking opportunities and encountering unexpected threats open a challenge for
SMEs. Therefore, reviewing and restructuring the business decision become on priority.
35 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
The decision making is an emerging trend for practical solution in conducting the changing
environment (Chai et al., 2013). As BI is the decision making aid, SMEs require reconfiguring
BI for new decision making in conducting new changes within the environment (Stodder, 2013).
It is important to note that SMEs have not only begun using BI in improving decision support
(Guarda et al., 2013), they occupy a big portion of BI users. For example, approximately 85
percent of BI user firms are SMEs in Southwest China (Zhi and Guixian, 2010). Precisely, it is
evident that an appropriate level of BI application and SME’s rigor position have significant
effects in enhancing insights to each other. However, SMEs are characterised with limited
capability that constrains new innovation of BI in businesses (Ponelis and Britz, 2011) although
it is vital for new decision of SMEs.
From the viewpoint of interaction, BI and SMEs can be considered as two distinct entities. In
analysing the above discussion, two limitations are apparent that BI may face lack of
reconfiguration or new innovation due to SME’s incapability and SMEs face difficulties to
restructure decision making due to lack of BI reconfiguration. In effects, both entities fail to
benefit each other, which confine integrated contribution to national economic development.
Considering this issue, our study aims to identify the social reality view of relevant interaction
between BI and SMEs that may enable them learn from each other for their individual
development. We conducted a theoretical analysis for building a theoretical framework that may
represent an integrated view of previous studies relevant to this study context.
36 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Although research on theoretical link among BI and SMEs is vast to date (example . Grabova et
al., 2010, Zhi and Guixian, 2010, Ponelis and Britz, 2011, Guarda et al., 2013, Ponis and
Christou, 2013, Tarek and Adel, 2016), research on how BI and SMEs learn from each other,
that produces new contribution into IS-led business domain, is sparse. Therefore, this study is
entailed to generate new understanding on learning issue among BI and SMEs
Task 1
1.1 Background details of the organization.
journey began in 1992 when the government of Sri Lanka decided to privatize the
“Management” of the then existing 22 Regional Plantation Companies which consisted of Tea,
37 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Rubber, Coconut & Palm Oil.
This paved the path for a strategic joint venture between XYZ Plantations PLC and Tata Tea
Ltd. of India. With this the plantations that came under its wings, received a new lease of life in
terms of latest technology, financial stability and personal care where the workers are concerned,
by effectively engaging in uplifting the life of the community economically, socially and
culturally.
In 1992 up to 1996 XYZ Plantations was in the management custody of Lankem Plantations
(Pvt) Ltd. It was only in the latter part of 1996 that Estates Management Services (Pvt) Ltd came
to take on this all important role and steer XYZ Plantations to what it is today.
With the joint venture with Tata Tea India,
XYZ Plantations PLC did take up the challenge of converting the trade into a productive and
competitive one. The unique three crop advantage, tea, rubber and oil palm did provide XYZ
Plantations the opportunity to move in many directions in terms of getting involved with the day
to day lives of the people in Sri Lanka. In total the area of plantations spread over an area of
12,442.13 ha (hectares) out of which 41% was tea, 18% rubber and 8% under palm oil
cultivation. Approximately 7% was kept aside for the purpose of fuel wood and the remaining
was uncultivated.
38 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
1.2 Business processing
Tea manufacture is the process of transformation of freshly plucked green tea leaves to black
tea. The process itself is long, requires much care, attention, control and a scientific
understanding of the complicated physical and chemical changes in the leaf as the manufacture
progresses. There are several distinctive processes that take place in the manufacture of black
teas.
PLUCKING
The green leaf is harvested on a regular basis at intervals ranging from 5 days to 8 days from
each field. The plucking of the soft two leaves and the bud is generally undertaken by well
trained women, because of the agility of feminine hands. The manufacture begins from the time
the leaf is plucked in the field, and to ensure it retains its freshness, the leaf is sent to the
factories from the fields three to four times a day.
39 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
WITHERING
No sooner it is received at the factory, the leaf is weighed and spread on troughs. Withering, is
a process, where conditioned air is circulated between the leaves, initially to remove any
surface moisture and thereafter to concentrate and chemically breakdown the tea juices. It takes
10 hours to 14 hours for the physical and chemical changes to take place, and bring the leaf to
soft and rubbery condition suitable for the next stage of manufacture.
ROLLING
Is the process by which the leaf is twisted and the leaf cell walls ruptured to bring the juices to
the surface of the leaf. The rolling machines have deep jacket, a pressure cap to apply pressure
on the leaf, and the table itself has battens and a cone at the center to twist the leaf. There are
also the more modern “Rotor vane” machines, which also give the same twisting and turning
effect. This process takes about 20 to 30 minutes.
40 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Thereafter to separate the twisted leaf from the untwisted, and to reduce the heat buildup, the
rolled leaf is passed over a roll breaker. This machine has meshed which separate rolled leaf.
The unrolled is put back into the rollers for further rolling whilst the rolled leaf is fermented.
FERMENTATION
Of the tea juices is an essential process in the manufacture of black tea. Fermentation is the
oxidization of the enzymes in the juices, which bring out the flavor, strength and the color of
the liquors and infusions. Fermentations is generally carried out on glass or tiled tables.
As fermentation progresses there is a color change of the leaf from greenish to coppery brown.
The degree of fermentation is judged by the color and aroma.
41 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
DRYING
The primary objective of drying is the extraction of moisture and the arresting of fermentation.
The fermented leaf contains from 45% to 50% moisture. The leaf is passed through driers,
which have circuits of trays with perforation, on which are conveyed the fermented leaf.
The drying process takes about 20 to 25 minutes and the initial temperature is about 120
Degrees F(50 Degrees C) and is finished off at a temperature of 200 Degrees F (93 Degrees C)
to 220 degrees F (105 Degrees C) . The moisture content of the teas when drying is completed
is approximately 2% to 3% and the coppery brown fermented tea particles are now back.
GRADING (SIFTING)
The fired teas after cooling are graded / sifted according to size and shape, as the trade
demands. The different grades of tea are identified nomenclature. On completion of the
grading, teas are stored in airtight bins of boxes. The sifting is carried out on a series of grading
42 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
and cleaning machines, which have several trays of different mesh sizes, to separate the tea
particles to the various grades of tea and to remove the stalk and fiber.
GRADING (SIFTING)
The fired teas after cooling are graded / sifted according to size and shape, as the trade
demands. The different grades of tea are identified nomenclature. On completion of the
grading, teas are stored in airtight bins of boxes. The sifting is carried out on a series of grading
and cleaning machines, which have several trays of different mesh sizes, to separate the tea
particles to the various grades of tea and to remove the stalk and fiber.
43 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Business Supporting process
raw materials are easy to access
Sri Lanka has some of the world’s most renown tea plantations. As a result, accessing the raw
materials in order to supply your tea business can be very easy. In addition, as you will not
have to pay customs tax to import the products, it will be cheaper as well. In addition to this,
you can- personally source the raw materials for your products.
44 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Supporting Infrastructure
As tea is one of the most lucrative businesses in the country, much supporting infrastructure has
been built to accommodate its demand. As such, as a potential owner of a tea business, you will
have easy access to machinery needed for the production process of tea leaves.
Reputation
Sri Lankan tea is a globally recognized product. As such, when launching your product, you
will already have a ready consumer base.
45 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
High demand, both domestically and internationally
Tea is one of the most widely consumed beverages in the world. Therefore, there is always a
demand for your product both domestically and internationally. With the rise in popularity of
bubble tea with younger consumers, the f&b industry has also shown a rise in their demand for
tea products.
Specialties Associated With Products Sri Lankan tea recognized as Ceylon Tea in the world is
renowned for its high quality, aroma, and taste. As the third largest tea producer and perhaps
the second largest exporter in the world, Sri Lanka is in the forefront of tea exports to the world
market. This is a position that Sri Lanka has maintained over the years. There are three major
geographical zones for tea cultivation in the country and the production of each cultivation has
unique features in it.
High/Upcountry: Above 1,200 m
Nuwara Eliya - Delicately fragrant
• Udapussellawa - Exquisitely tangy
• Uva - Exotically aromatic
• Dimbula - Refreshingly mellow
Mid-Country: Between 600 m. - 1,200 m.
46 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
• Kandy - Intensely full-bodied Low-Country:
Below 600 m.
• Sabaragamuwa - Smooth & full-bodied
• Ruhuna - Distinctively unique
Uva teas from Eastern Highlands contain unique seasonal characters and are widely used in
many quality blends particular in Germany and Japan. The medium grown teas provide thick
coloury varieties which are popular in Australia, Europe, Japan and North America. The teas
produced in low grown areas are mainly popular in Western Asia, Middle Eastern countries and
CIS and BRICS countries. Most factories in these areas produced what are known as leafy
grade of tea where the tea leaves are well twisted and can grade into long particles.
Quality Standards
Sri Lankan Tea industry maintains the highest quality in the world market and ISO 3720 is the
minimum standard applies for the products. Sri Lanka has the capability to produce the cleanest
tea in the world in terms of minimum pesticide residues. Methyl Bromide was removed from
47 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
the production process in 2012. Sri Lanka also is adjusting well to the stringent ISO 22000
series and to the health & safety regulations stipulated by the European Community. Growers
are constantly educated to practice Good Agricultural Practices (GAP). The Processing/
Manufacturing facilities owned by the export companies comply with local standards (SLSI)
and also with International Quality Standards such as ISO, HACCP, and EU Standards.
Traceability throughout the supply chain is monitored in order to guarantee a safe product to
the consumers.
Value Addition
Sri Lanka exports more than 50% of tea in value added form. The Value added product range of
Sri Lankan tea includes green tea, flavored tea, organic tea, instant tea, iced tea, and readyto-
drink tea. Tea based soap, bath gel, shampoo and cosmetic products have recently been added
to this product range. Sri Lanka boasts the biggest Tea Research Institute in the world.
Colombo also has the biggest concentration of tea bagging plants in the world.
48 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Lion Logo
Ceylon Tea Lion Logo which appears on Ceylon tea packs denotes not only the country of
origin but also the quality of Ceylon Tea. Sri Lanka Tea Board is the legitimate owner of the
Ceylon Tea Lion logo which has been registered in many countries in the world. The usage of
Lion Logo is subject to the following conditions:
(a) The Lion Logo can be used only on consumer packs of Ceylon tea.
(b) The packs should contain 100% pure Ceylon tea. 6
(c) The brands which use the Lion Logo should be packed in Sri Lanka. Overseas
Importers/packers are not allowed to use the Lion Logo on their tea packs even if the packs
contain pure Ceylon Tea.
(d) The brands which use the Lion Logo should conform to the quality standards set out by the
Sri Lanka Tea Board.
49 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
1.3 Business processes the organization in different levels and processes
A business process is a series of step performed by a group of stakeholders to achieve a
concrete goal these steps are repeated many times sometimes by multiple users and ideally in a
standardized and optimized way A business process can be manual or automat if manual the
process is achieved without the aid of automation or assisting technology if automated a
technology aid been put into place which assists users in implementing the process in a more
accurate standardized or optimized manner it is the fundamental building block for several
related ideas such as business process management process automation
In other words a business can be defined as a collection liked tasks which find their end in the
delivery of a service or product to a client A business process has also been defined as a set of
activities and tasks that once completed will accomplish an organization goal the process must
involve clearly
Defined input and a single output these inputs are made up of all of the factors which contribute
(either directly or indirectly ) to the added value of a service or product these factors can be
categorized into management process operational process and supporting business process
Operational processes
Operational processes (or primary processes): Operational or primary processes deal with the
core business and value chain. These processes deliver value to the customer by helping to
50 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
produce a product or service. Operational processes represent essential business activities that
accomplish business objectives, e.g., generating revenue. Some examples of this include taking
customer orders and managing bank accounts.
Supporting processes
Supporting processes (or secondary processes): Support processes are the processes which do
not deliver the final product/service to the client, but it creates an environment that is suitable
for the primary processes to function smoothly. These processes do not directly generate value
to the customer. Having said that, the support processes are also vital for the enterprise
Supporting processes back core processes and functions within an organization. Examples of
supporting or management processes include accounting, HR management and workplace
safety. One key differentiator between operational and support processes is that support
processes do not provide value to customers directly.
Management processes
Management processes do not add value to the end customer. These processes are more
oriented to monitoring and analyzing the business activities. These processes deal in up scaling
the business, introducing new verticals and bringing innovation to the firm. Management
processes are goal oriented and aim at designing and achieving tangible as well as intangible
targets. Management processes measure, monitor and control activities related to business
procedures and systems. Examples of management processes include internal communications,
51 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
governance, strategic planning, budgeting, and infrastructure or capacity management. Like
supporting processes, management processes do not provide value directly to the customers.
References Sri Lanka Export Development Board , INDUSTRY CAPABILITY REPORT
Type of Business Processes
business processes span industries, both vertical and hotel and can include any type of
business operation
Examples include
Manufacturing product assembly process, a quality assurance process, a corrective/prevue
maintenance process
Finance an Invoicing process, a billing process, a risk management process
52 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Health - a medical assessment, a drug approval
Banking- customer on-boarding credit check
Travel - trip booking agent billing
53 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Defense-a situation room process, emergency management process
HR-a starters process, a leavers process, vacation request
Public Sector - application for a government service
54 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Compliance - a safety audit, a legal check
Sales Information Technology
Quotes/ Pricing – Incised & Fix
Underwriting IT request Management
Contract Approval . Access Control
Now Cent Onboard Portfolio Manager
Compensation Change Control
Meeting Planning App/System Support
RFP admin
Legal Finance
Contract Management Invoice admin
Invitation Procurement
New Flip/Case
Project Budget Approval
Management
Regulatory Filing Expense Management
Legal Doc Management budge Panning
Customer Service Human Resources
Case Management Recruitment
Client Feedback New Hire Onboarding
Inquiry Management Compensation Pan & Admin
55 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Escalation Management Benefits Administration
SAM management Performance Management
Support Services Training
Employee State Change
Transfer /Relocation
leave Management
Compliance Product development and Research
Know Your Customer Requirement
Patriot Act Product Specifications
Sarbanes Oy Change Request Man
HIPAA Research
Basel Lifecycle Management
GLBA
FISMA
Manufacturing Marketing
Resource prominent Adverting
Order Management Events Management
Change request Packaging a Poring
Trading Partner
Communication
Management
Deed /Recall Man Creative Development
Equipment/System Repair
Quality Assurance
Operations
Inventory Management
56 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Order Furmint
Clint Management
Events Management
Facts Management
Award Distribution
57 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Table 1
1.4 Differentiation between structured, semi structured and unstructured.
Big Data includes huge volume, high velocity, and extensible variety of data. These are 3 types:
Structured data, Semi-structured data, and Unstructured data.
58 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Structured data
Structured data is data whose elements are addressable for effective analysis. It has been
organized into a formatted repository that is typically a database. It concerns all data which can
be stored in database SQL in a table with rows and columns. They have relational keys and can
easily be mapped into pre-designed fields. Today, those data are most processed in the
development and simplest way to manage information. Example: Relational data.
Semi-Structured data
Semi-structured data is information that does not reside in a relational database but that have
some organizational properties that make it easier to analyze. With some process, you can store
them in the relation database (it could be very hard for some kind of semi-structured data), but
Semi-structured exist to ease space. Example: XML data.
59 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Unstructured data
Unstructured data is a data which is not organized in a predefined manner or does not have a
predefined data model, thus it is not a good fit for a mainstream relational database. So for
Unstructured data, there are alternative platforms for storing and managing, it is increasingly
prevalent in IT systems and is used by organizations in a variety of business intelligence and
analytics applications. Example: Word, PDF, Text, Media logs.
SEMI-STRUCTURED UNSTRUCTURED
PROPERTIES STRUCTURED DATA DATA DATA
60 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
It is based on
It is based on Relational XML/RDF(Resource It is based on character
Technology database table Description Framework). and binary data
Matured transaction and No transaction
Transaction various concurrency Transaction is adapted management and no
management techniques from DBMS not matured concurrency
Version Versioning over tuples, Versioning over tuples or
management row, tables graph is possible Versioned as a whole
61 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
It is more flexible than
structured data but less It is more flexible and
It is schema dependent flexible than unstructured there is absence of
Flexibility and less flexible data schema
It is very difficult to scale It’s scaling is simpler than
Scalability DB schema structured data It is more scalable.
62 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
New technology, not
Robustness Very robust very spread
Query Structured query allow Queries over anonymous Only textual queries are
performance complex joining nodes are possible possible
Table2
63 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
1.5 Application Software
A variety of applications prepare to make a software program. These packages have
commonplace capabilities, capabilities, and consumer interface.
Enterprise Resource Planning software: This software help in looking after the specific
organizational desires. They are frequently used in a huge commercial enterprise setup.
Content Access software program: It is used for accessing special form of content without
making any adjustments to it. An exception to this kind of software program is the software
program used for enhancing the content itself. The content gets entry to software are useful for
human beings inside the field of digital content.
Collaborative Microsoft software program: These are regularly net-based totally software
program, which contains using extra than 1 character.
64 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Enterprise Infrastructure software: It helps the software systems in an employer. Normally, the
one of a-kind databases, email servers, and so on., are covered under this class.
Media Development software program: This software is utilized by human beings in both the
print and the digital software program
Application Suite
Microsoft Office, iWork, Open Office, etc., are examples of utility suite, as they arrive bundled
with a number of packages like the phrase processor, spreadsheet, and so forth.
65 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Enterprise Resource Software
There are extraordinary varieties of software that come beneath the class. The examples are
consumer relationship management software program, economic software program, medical
billing software, departmental software program, time management software, IT Helpdesk
software program, church control software program, manufacturing software, etc.
66 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Content Access Software
Most folks have definitely used this form of the software program. As a count of truth, internet
browsers are nothing but content material get right of entry to software. The other examples are
media players, help browsers, and so on.
Collaborative Software
The examples of collaborative software are emails, blogs, Wikipedia, etc.
67 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Enterprise Infrastructure Software
This includes the exceptional database control, document management, workflow control,
digital asset control, undertaking control, belongings control, and many others.
Media Development Software
Animation, laptop publishing, HTML editing software, and so forth., are a number of the
examples below this category.
It is obvious that that software has simplified a number of obligations for a purchaser. At the
identical time, you can see that these computer software programs were helpful for harnessing
the computing energy to finish numerous person or organizational obligations. The software
68 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
program interacting with the quantity of customers has additionally grown to be less difficult,
which has paved the manner for revolution within the subject of conversation.
Application software is answerable for the green functionality of computing gadgets. The
benefits and drawbacks of software are enlisted inside the article beneath.
Our computer systems and cellular devices are all loaded with all forms of the software
program, and every software has a special purpose to meet. It is essential to first apprehend the
differences between software and machine software program. System software program is the
programming and the coding that is utilized by the diverse components within the tool to speak
with every different. There are thousands and thousands of instructions and commands which
might be transferred from one aspect to every other with every passing 2d, and the machine
software allows this float of the communique. Additionally, the person using the tool does no
longer immediately have interaction with or use the gadget software program, because it’s far
all happening within the tool itself.
On the alternative hand, utility software program is that which is used directly by means of the
consumer for the only reason for finishing a sure undertaking. This kind of software program
needs to be mounted one by one on a tool, and it regularly has interfaces that permit
communique between the gadget and the person, hence giving upward push too many one-of-a-
kind advantages and downsides. For example, don’t forget an application that lets you work
with databases. This is a software that is used for a specific utility, so it falls below this
category. It is universally assumed that they’ve many benefits, and you will be tough pressed to
69 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
locate hazards for the identical because, in the long run, the cause of all these devices is to
perform many obligations with their assistance.
Application Software
The one-of-a-kind forms of utility software are utilized by person customers and business
companies as nicely, and that they have many benefits of doing so. This consists of the phrase
processing software program, database software, multimedia software, modifying software
program, and many another one of a kind sorts as nicely. All these software programs are both
furnished in my opinion, or they are packaged collectively and offered through enterprise to
commercial enterprise sellers. When an entire type of them are integrated collectively and
offered to an enterprise, they are able to soak up the shape of employer software, instructional
software, simulation software program, statistics employee software, and so forth.
70 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
1.6 Advantages of using application software as a mechanism for business processing.
Advantages
When you start to compare, you will discover that the pros outweigh the cons very easily. With
that in thoughts, right here are a number of their maximum famous and widely time honoured
blessings. Note that during this scenario, we are speaking of utility software this is designed for
a selected purpose, for use either by way of individuals or by using organizations.
The chance of viruses invading custom-made programs could be very small, given that any
business that incorporates it can restrict access and may provide with the method to guard their
community as well Program
71 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Licensed application software receives regular updates from the developer for safety motives.
Additionally, the also regularly sends personnel to accurate any problems which can get up
occasionally
Their single biggest advantage is that they meet the exact needs of the user. Since they are
designed specifically with one purpose in mind, the user knows that he has to use one specific
software to accomplish his task.
Disadvantages
As is the case with all such subjects, there are certain dangers of such software program as
nicely. Though these aren’t spoken approximately very frequently, nor are they highlighted, the
reality is that they do exist and have an effect on positive users. But humans have time-honored
those misgivings and nevertheless keep to apply for such software program because their utility
and significance is a lot greater profound than their weaknesses.
72 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Developing utility software program designed to meet unique purposes can prove to be pretty
high priced for builders. This can affect their price range and their revenue glide, in particular if
too much time is spent developing a software program that is not generally proper.
Some software program which can be designed specifically for a certain commercial enterprise,
might not be well matched with different popular software. This is something which can show
to be the main stumbling block for many agencies.
Developing them is something that takes a variety of time because it wishes consistent verbal
exchange between the developer and the patron. This delays the whole production procedure,
which could show to be harmful in a few cases.
Application software program that is used usually by many human beings, and then shared
online, incorporates a totally real hazard of infection by a pc virus or other malicious programs.
73 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Task 1
1.7 Business Intelligence Techniques
There are several business intelligence techniques companies can put to use to gain valuable
insights to inform decision-making. Here’s a look at the most common BI techniques.
Analytics
Analytics is a business intelligence technique that involves the study of available data to extract
meaningful insights and trends. This is a popular BI technique since it lets businesses deeply
understand the data they have and drive ultimate value with data-driven decisions. For instance,
a marketing organization can use analytics to establish the customer segments that are highly
likely to convert to new customers, and call centers leverage speech analytics to monitor
74 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
customer sentiment, improve the customer experience, and for quality assurance purposes, just
to name a few.
Predictive Modeling
Predictive modeling is a BI technique that utilizes statistical techniques to create models that
could be used in forecasting probabilities and trends. With predictive modeling, it is possible to
predict the value for a particular data item as well as the attributes using multiple statistical
models.
75 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
OLAP
Online analytical processing is a technique for solving analytical problems with different
dimensions. The most important value in OLAP is its multidimensional aspect that lets users
identify problems from different perspectives. OLAP could be used to complete tasks such as
budgeting, CRM data analysis, and financial forecasting.
Data Mining
Data mining is a technique for discovering patterns in huge datasets and often incorporates
database systems, statistics, and machine learning to find these patterns. Data mining is an
integral process for data management as well as the pre-processing of data since it ensures
appropriate data structuring. End users could also use data mining to create models that reveal
76 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
these patterns. For instance, a business could mine CRM data to predict which leads will most
likely buy a certain solution or product.
Model Visualization
The model visualization technique is used to transform the discovered facts into histograms,
plots, charts and other visuals that aid in proper interpretation of the insights
77 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Business Intelligence Tools
BI tools are all about helping you better understand trends and derive insights from data in
order to make strategic and tactical business decisions. Here’s a rundown of a few popular
business intelligence tools companies leverage to derive insights.
Sisense
the Sisense BI tool could be a great option. It is incredibly user friendly and allows everyone
within an organization to manage, analyze and visualize complex datasets without involving the
IT department. This tool lets you gather data from various sources, including Google Analytics
78 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
and AdWords. Since this tool uses in-chip technology, data processing is faster compared to
other BI tools.
SAP Business Intelligence
SAP Business Intelligence provides an array of advanced analytics solutions including machine
learning, BI predictive analytics, and planning and analysis. This enterprise-level applications
for client/server systems offers data visualization and analytics applications, reporting and
analysis, mobile analytics and office integration. SAP is a robust solution intended for all roles
(management, end uses and IT) and offers a ton of functionalities in a single platform.
79 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Dundas BI
Dundas BI is a browser-based BI tool that allows users to connect to multiple data sources in
real-time. It provides great visualizations in tables, graphs and charts that could be customized
and viewed from mobile devices and desktops. Users can easily build reports and extract
certain performance metrics for purposes of analysis. Dundas offers support to all company
types and across different industries.
Here are few valued competences of Microsoft Power BI tool:
80 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Integrates seamlessly with existing applications:
Power BI integrates easily with your existing business environment allowing you to adopt
analytics and reporting capabilities. Microsoft Azure consultants can also help in leveraging
this intuitive tool to embed interactive visuals in your applications easily.
Rich personalized dashboards:
The crowning feature of Power BI is the information dashboards, which can be customized to
meet the exact need of any enterprise. You can easily embed the dashboards and BI reports in
the applications to provide a unified user experience
81 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
No memory and speed constraints:
Shifting an existing BI system to powerful cloud environment with Power BI embedded
eliminates memory and speed constraints ensuring data is quickly retrievable and analyzed.
Extracting business intelligence rapidly and accurately:
It helps in transforming your enterprise data into rich visuals, thus extracting business
intelligence for enhanced decision making.
82 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Balanced simplicity and performance:
The in-memory analysis technology and DAX scripting language are both exquisite examples
of a balance between simplicity and performance.
Supports Advanced Data services :
Microsoft Power BI development teams can help integrate the environment seamlessly with
advanced cloud services like Cognitive services, Cortana or Bot framework. Thus, providing
results for the verbal data query given using natural language.
83 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Business Intelligence Functions
Data Illustration Software - The main benefit of data illustration is discovering correlations.
With filters, the user is able to manipulate the data to only show certain ranges of information.
Data Integration Software
The information access needs of each business differ greatly. From the data sources used, to the
dashboard or report design requirements, to the security needed; every company has their own
unique set of requirements that must be fulfilled. One important topic that is often forgotten is
that of data source integration. If data cannot be retrieved, it cannot be used to produce reports.
Style Intelligence provides interfaces for multiple data source types and a flexible Java API that
can interface with any custom data source.
84 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Data Management Technology
Data management technology refers to methods used by business to organize, secure, store,
and retrieve information. Every company, no matter how large or small it may be, creates an
infinite amount of data through its every day activities. Data management technology, typically
in the form of software, is used to draw meaningful conclusions and formulate actionable goals
Database Access Software
An explanation of Style Intelligence's architecture and ability to access multiple, disparate
databases, any via a JDBC connector as well as OLAP cubes, flat files, Web services and other
databases. Database access software is a core component of Nessoft’s business intelligence
software platform. The software can access multiple, disparate databases, any via a JDBC
connector as well as OLAP cubes, flat files, Web services and other databases. Speedy Data
Access is enabled by Nessoft’s patent-pending Data Block technology across a variety of data
sources including relational databases, multi-dimensional databases, Web services,
85 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
flat files and more.
86 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Task 2 2.1 Business Decision making at different levels of the organizational
structure
87 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Figure 1
Reference Unit 14 business intelligence page number 21- 25
Strategic Decision (Unstructured Decision)
These decisions or plans are normally long term decisions, which are having implications for
the next five years and above. Lot of risk and uncertainty is involved in long term (Between
five to ten years). Decisions are unstructured, ad hoc and needs to be forward looking The
environment is wide scope with less frequent actions. Unstructured data are involved with the
level in summarized version Proper strategic plan is a must. Strategic planning needs a through
scanning and analysis of external environment to seek information. Strategic planning involves
deciding and developing strategic plans to achieve strategic objectives (or goals) Top
management typically develops the strategic plans.
88 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Ex Technology decisions (Choice of appropriate technology, equipment's, process choice and
degree of automation). Capacity decisions (Amount, timing and type). Facilities decisions Site
location and specializations), Vertical integration: Direction, extent and balance
These decisions are critical to the success and better performance of the organization. These
decisions influence the competitive positions of the organization and help to position the
operations strategy of the organization.
Characteristics of Strategic Decisions
1. Strategic level production planning helps to achieve the goals in the best possible way
89 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
2. It helps to achieve the competitive advantages and to develop core competence
3. It helps to develop strengths and eliminate weaknesses to encash the available
opportunities
4. It gives direction to growth and development of business 5. Strategic level planning lays
foundations for tactical goals and operational goals
90 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
5. These planning decisions are critical to success or failure of the organization.
6. Strategic decisions are to be taken with less information and also in the environment of
uncertainty
7. and risk All the strategic level planning is always associated with risk and it is used in
some futuristic assumption
91 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Tactical Decision Semi Structured Decision)
These decisions relate to the implementation of strategy decisions They are directed
towards developing divisional plans structuring workflows establishing distribution
channel, acquisition of resources such men materials and money the downs are taken at
the middle level of management Tactical decisions cover shorter time (between three to
five year) frames and is associated with less uncertainty and hence lower risk as
compared to strategic decisions Tactical planning involves less uncertainty and hence
lower A compared to strategic planning Mainly the planning requires internally generated
data
92 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Tactical Decision include
1. Establishing parameters for meaning operational efficiency and productivity
2. Making plans to improve utilization of existing resources.
93 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
3. Prepare equipment and manpower planning
4. Panning for modernisation of the facilitates and automation
5. Specific technology and tools to chance production efficiency of productivity
94 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
6. Prepares work plans for process redesign, methods improvement and job design.
7. Make or buy decision
8. A Projections regarding soil requirements for future work assignment and prepare
the skill development plans
95 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
9. Planning for medium term maintenance (preventive and condition monitor to
enhance the availability of production facilities.
Operational Decisions (Structured Decision)
These decisions relate to day to-day operations of the enterprise. They have a short term
horizon (maximum One year as they are taken repetitively. These decisions are based on facts
regarding the events and do not require much of business judgments. Operational decisions are
taken at lower levels of management. As the information is needed for helping the manager to
take rational well informed decisions, information systems need to focus on the process of
managerial decision making Normally these types of decisions are frequent, detailed and arrow
focused deterministic in the sense that uncertainty is very low. The decisions are expressed in
terms of action, which can be quantified.
96 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Characteristics of Operational Decisions
1. Plans are definite and action oriented
2. Plans are expressed in terms of parameters, which can be quantified,
97 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
3. Plans give the detailed instructions regarding
4. What to be done? 4 5 Who should da?
5. When and where?
98 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
6. The plans are quantified and are expressed measurable units and hence comparison
between planned and actual is easy
7. It helps to monitor the progress of the plan and take corrective action if needed to
achieve the target
99 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Task 2 2.2 Organization commonly using Business intelligence tools
SAP Business Intelligence
Qlik Sense
Sisense
Microsoft Power BI
Clear Analytics
Oracle BI
SAP Business Intelligence
SAP Business Intelligence offers several advanced analytics solutions including real-time BI
predictive analytics, machine learning, and planning & analysis. The Business Intelligence
platform in particular, offers reporting & analysis, data visualisation & analytics applications,
100 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
office integration and mobile analytics. SAP is a robust software intended for all roles (IT, end
uses and management) and offers tons of functionalities in one platform.
Qlik Sense
Qlik Sense is a product of Qlik, a company also known for another business intelligence tool
called QlikView. You can use Qlik Sense from any device at any time. The user interface of
Qlik Sense is optimized for touchscreen, which makes it a very popular bi tool. A big
difference with QlikView is the feature Storytelling. Users add their experience to the data and
by using snapshots and highlights making the right analysis and decisions has become a lot
easier
101 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Sisense
This user-friendly tool allows anyone within your organisation to manage large and complex
datasets as well as analyse and visualise this data without IT department getting involved. It lets
you bring together data from a wide variety of sources as well including AdWords, Google
Analytics and Salesforce. Not to mention, because it uses in-chip technology, data is processed
quite quickly compared to other tools.
102 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Figure 2
Microsoft Power BI
Microsoft Power BI is a web-based business analytics tool suite which excels in data
visualisation. It allows users to identify trends in real-time and has brand new connectors that
allow you to up your game in campaigns. Because it’s web-based, Microsoft Power BI can be
103 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
accessed from pretty much anywhere. This software also allows users to integrate their apps
and deliver reports and real-time dashboards.
104 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Figure 3
Clear Analytics
This BI tool is an intuitive Excel-based software that can be used by employees with even the
most basic knowledge of Excel.
What get is a self-service Business Intelligence system that offers several BI features such as
creating, automating, analysing and visualisation company’s data.
105 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Figure 4
106 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Oracle BI
Oracle BI is an enterprise portfolio of technology and applications for business intelligence.
This technology gives users pretty much all BI capabilities, such as dashboards, proactive
intelligence, alerts, ad hoc, and more. Oracle is also great for companies who need to analyse
large data volumes (from Oracle and non-Oracle sources) as it is a very robust solution.
107 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
108 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Figure 5
109 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Task 3 3.1functional interfaces
Export Growth in the sector from 2010 to 2013
110 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Table3
References Sri Lanka Export Development Board , INDUSTRY CAPABILITY REPORT
111 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
2010 World Total (Quantity - Kg) and world total value $
World Total (Quantity -
Description World Total (Value)
Kg)
Tea Packets 115,298,737 549
112 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Tea Bags 18,743,078 131
Tea in Bulk 169,742,690 651
Instant Tea 1,612,220 11
Green Tea 696,814 3
Other Tea nest 21,763,974 93
Total 327,857,513 1,439
113 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Table4
This dashboard can be show 2010 World Total (Quantity - Kg) and world total value $
114 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Figure 6
2011 World Total (Quantity - Kg) and world total value $
World
World Total
Total % Growth
Description (Quantity -
(Value) to 2011
Kg) 2011
2011
Tea Packets 131,617,734 718 31
Tea Bags 1,939,805 10 -93
115 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Tea in Bulk 175,876,070 697 7
Instant Tea 48,965 0 -96
Green Tea 985,662 4 18
Other Tea nest 10,654,702 46 -50
Total 321,122,938 1,476 3
116 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Table5
This dashboard can be show 2011 World Total (Quantity - Kg) and world total value $ and
growth %
Figure 7
2012 World Total (Quantity - Kg) and world total value $
117 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
World Total (Quantity - World Total (Value)
Description % Growth to 2012
Kg) 2012 2012
Tea Packets 127,616,453 666 -7
Tea Bags 889,866 4 -57
Tea in Bulk 183,644,779 700 0
Instant Tea 10,906 0 -86
Green Tea 995,195 4 2
118 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Other Tea
5,258,332 23 -50
nest
Total 318,415,531 1,398 -5
Table6
This dashboard can be show 2012 World Total (Quantity - Kg) and world total value $ and
growth %
119 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Figure 8
2013 World Total (Quantity - Kg) and world total value $
Description World Total (Quantity - Kg) World Total % Growth to 2013
120 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
2013 (Value) 2013
Tea
124,162,313 715 7
Packets
Tea Bags 1,381,252 7 67
Tea in
188,102,422 785 12
Bulk
Instant Tea 5,266 -7
Green Tea 1,033,074 5 13
121 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Other Tea
3,050,573 15 -36
nest
Total 317,734,900 1,527 9
Table7
This dashboard can be show 2013 World Total (Quantity - Kg) and world total value $ and
growth %
122 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Figure 9
This dashboard swing 2010,2012,2013 years world total value $ and world total quantity and
growth % (three type of data and three deferent years Export Growth at one dashboard)
123 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Figure 10
This dashboard 2010and 2012,2013 years world total Export value
124 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Figure 11
This dashboard 2010and 2012,2013 years world total export quantity kg
125 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Figure 12
The export revenue has been fluctuated over the last three years due to the economic crisis in
the world. However the value of exports has been increased by 3.37% in year 2013 compared
126 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
to the total earnings from January to July in year 2012 and 2013. The tea exports account for
about 14% percent for the total exports and about 62% contributes for the total agriculture
exports in the country. The tea sector is expected to achieve the export target of US $ 2,500
Million in year 2015.
How Can Custom Business Dashboards Accelerate Decision-Making?
The Visual Power Visualizing Data At-A-Glance
You must be familiar with your car’s dashboard. It’s such an integral part of the vehicle’s
operation. The swift-view of data helps navigate easily and is comprehensible even when you are
driving at immense speed.
127 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
The dashboards are analytical tools that help to visualize data across industries. With trendy
UI/UX, you get an uncluttered picture of critical activities at your fingertips. The result can
quickly work on the crucial metrics and KPIs for better decisions and situational understanding.
You can see the data depicted in icons, colors, charts, or other cues. Now, it’s uncomplicated for
to view your business, team, or project’s performance. Dashboards reflect data that help you
navigate your way through everyday tasks seamlessly. When you get to a quick-view of essential
data, it is easy to spot deviations and take quick corrective measures. The best part can also
choose to make a custom business dashboard instead of an off-the-shelf solution.
The Bias Facet Improving Analytics Culture
Bias is an intrinsic part of analytics, and even Gartner acknowledges it . The BI dashboard
development process may have some subtle elements of bias. How do you deal with bias?
can use provocative thinking in understanding and removing preferences. must remember that
dashboards aren’t magic cure-alls. It is significant to look at data, keeping in mind the limits of
the tools and perception.
When take the right steps toward improving your analytics culture, will find the benefits coming
back in multiples. The more manage biases with precision, the more get unbiased views. The
result can make reliable decisions.
The Hyper dashboard features the most salient information, right up front. It tracks not only the
current earnings but also earnings from the previous week. This gives the user immediate
128 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
context. There’s a certain amount of benchmarking that users can perform, based on this neat and
thoughtful addition
Based on the previous week’s earnings, the user can compare the current week’s earnings to
make decisions on whether revenue and sales are on par or to try to find reasons why it would be
lagging (the season or a poorly-performing campaign, for example).
Invoicing Dashboard
Effective dashboards are those that are cross-functional. Take, for example, the desktop app
mockup. This dashboard connects scheduling and appointments handily with revenue projections
and tracking
The revenue and financial aspect of the dashboard also includes data points on three separate
earnings: monthly, profitability (which is essentially a calculation), and earnings per hour.
Cross-functional dashboards can essentially help users draw conclusions about the relationships
between the two or more functions that the app tracks.
Decision-Making: For a professional to gain the best insights into data and analyse it properly,
they need to identify the things to act upon and streamline workflow. Dashboards gather data
from multiple sources and combine them in a single interface for a detailed overview of the
business while reducing reporting time.
129 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Benefits of a BI dashboard
A BI dashboard is an easy-to-understand, visualized summary of data analysis that provides an
at-a-glance overview of multiple areas of the business.
130 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Enhanced visibility
BI dashboards provide greater visibility with information available whenever it is required to
ensure businesses are better placed to respond to changing market conditions.
Timesaving efficiency
With BI dashboards, you are no longer wasting valuable time generating reports from multiple
systems. Instead, data is drawn from a centralized source and displayed as an easy to interpret
visual overview.
131 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Better forecasting
With greater insight into the buying cycle of each customer, future demand can be more
accurately predicted using historic information. Businesses can more effectively plan for
demand fluctuations for the next business cycle, setting measurable goals and deliverables for
greater success.
Key performance indicators
BI dashboards source data from multiple areas displaying the information as easy to understand
visuals in real-time. This provides managers with an overview of current KPIs to assess
different areas of performance while creating actionable insights.
132 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Inventory control
With analytics and a real-time vision of inventory stock details, sales staff know what items are
in stock and where they are located. BI dashboards improve inventory control using detailed
historic data to optimize supply quantities and inventory allocation across stores and minimizing
the risk of stockouts.
Real-time customer analytics
With real-time, accurate insight on current customers purchasing behaviors, you have a better
chance of achieving higher retention rates and increased revenue. Real-time insight allows sales
teams to concentrate on the right customers at the right time, ensuring marketing efforts and
activities are focused toward the right clients.
Better decision-making
Whether you’re providing reporting and analysis for the entire organization or functional areas of
the business, a BI dashboard allows companies to analyses key data quickly and meticulously.
Visualized interactivity serves to deliver overwhelming amounts of data in a way that is easy to
understand. With the ability to easily identify what the data really means; better decisions can be
made relevant to the business.
133 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Task 3.2 Advantages OF dartboard design
Data transparency – Data is any company’s most important asset. However, it doesn’t do
much good if no one can understand or access it. A well-designed dashboard provides on-
demand access of all of your most important metrics.
Access to data – As the name implies, a dashboard gathers multiple data sources, including
Excel, into a single interface. That means you can immediately see a detailed overview of your
business in one quick glance. Better yet, it reduces the amount of time it takes to compile
reports, saving you time.
Better decision making – Dashboards provide an unbiased view not only of the company’s
performance overall, but each department as well. If each department is able to access the
dashboard, it can offer a foundation for further dialogue and great decision making. For
example, the sales and marketing department can align their data and experiences to increase
customer acquisitions and improve demand generation. Business dashboards provide a good
starting point for these decisions, which is one of the biggest advantages of dashboards.
134 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Accountability – While it’s always nice to see what you’re doing right, you also need to see
and understand what you’re doing wrong in order to increase your performance. Business
dashboards can show you exactly where your trouble areas are and arm you with the
information you need to improve. Also, by making the dashboards visible throughout the
company, they can hold different departments accountable for both the ups and downs.
Interactivity – Some of the best dashboards provide a dynamic experience. Rather than
providing static information, you and your users can filter data, interact with charts to see
changes over time, and even allow for an ad-hoc component for on-the-fly. That means you can
get as much or as little detail on specific metrics as you want.
Gamification – Your metrics, whether traffic to your website or products sold, are the key
numbers you want to continuously improve upon. The top businesses have managed to gamify
certain business metrics to increase the likelihood of customer retention. If you’re considering
gamification, business dashboards can track the success of your efforts.
135 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
What is Microsoft Power BI?
As mentioned, business intelligence (BI) is one of the top trends for 2017. Soon, every function –
from sales to management to HR – will need to be familiar with Power BI because they will have
to use it daily.
Business analytics platforms enable companies to join data from disparate systems, analyze data
through visually stunning dashboards, and easily share insights with colleagues and executives. It
brings the power of big data to everyone through easy-to-understand visualizations.
Microsoft Power BI is one of the leading BI solutions. Its ease-of-use and high reconfigurability
give it flexibility and accessibility. This makes it ideal for organizations looking to quickly
implement BI without sacrificing key features.
136 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
How Power BI Works
Microsoft Power BI uses datasets which you import or connect to. For example, customer data,
sales data, and internal supply chain data can all be connected to Power BI. The software comes
in both on-premise and cloud service options, giving your organization flexibility.
This data is used to create reports. A report is a page or more of data visualizations – tables,
charts, graphs, etc. Since each dataset can be reused, the same data can appear on multiple
reports.
This gives users the data they need across functions. It also enables reports to visually display
multiple sets of data as needed. Users can refresh, explore, and reuse data according to the
permissions set by administrators.
Power BI Services & Features
Power BI’s robust analytics suite gives users the ability to create powerful, insightful dashboards
and reports. Microsoft uses several key components to flexibly meet your specific business
needs:
Power BI Gateway: Acts as the central core for Power BI, delivering reports and
visualizations to users while helping keep database access controlled and secure.
137 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Power BI Mobile: Enables users to view their reports in real-time on their tablets or
smartphones. This ensures users are always connected to the data that matters to them.
Power BI Desktop: Lets analysts create reports, explore data connections, and add more data
sources. It also allows users to publish reports and data into easily shareable docs.
The Business intelligence tool designs how help organizations
I business is still using spreadsheets, email, and database files to share data, then Power
Power BI joins all your data from disparate systems (including SharePoint, Google Analytics,
Azure, Marketo, Facebook, QuickBooks, and much more) into a centralized home for your
data. This allows everyone in your organization to focus on metrics important to them.
138 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Power BI’s drag and drop UX lets you quickly find the insights you need and visualize them.
Employees at every level can now:
Identify trends
Maximize profitability
Make smarter decisions
Pick out business opportunities easier
Anticipate and overcome challenges earlier
Since harnessing big data will be critical for businesses to remain competitive in 2017, a
business intelligence solution like Power BI is essential. The cost and time-saving benefits, as
well as the ability to identify new opportunities, make the difference between growing or losing
market share.
139 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
PROVIDE BUSINESS INFORMATION QUICKLY AND EFFICIENTLY
Many business decisions need to be made on the spot, and to ensure sure you’re making the right
one, you need access to information. Information isn’t just numbers in a column, but also what
those numbers mean for your organization. Using BI software gives you this information at the
click of a button to help you gain a competitive advantage.
COME UP WITH PERFORMANCE INDICATORS ALIGNED WITH YOUR BUSINESS
STRATEGIES
When companies focus on doing tasks that are not aligned with their strategy, this leads to both
time and money wasted. To avoid this, you need to establish metrics that come with performance
indicators that are aligned with your company strategies. BI tools can help you in this regard by
providing the metrics so you can focus on improving performance where it really matters.
EMPOWER EMPLOYEES THROUGH DATA ACCESS
BI solutions enable employees to make informed, data-driven decisions by giving them access to
relevant, real-time data. This allows organizations to maximize information across all levels and
empowers employees for professional and personal growth. Having an empowered workforce
can make a company more competitive in the global business arena.
140 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
SAVE TIME ON ENTERING DATA AND MAKING REPORTS
Manual data entry is prone to human error, even when it’s copied and pasted from another
source. Not only that, it also takes a lot of time to do properly. By using a well-configured BI
system, you eliminate time spent on data entry and decrease the amount of time spent on
performing calculations. BI tools also allow for quick report generation and data visualization
where you can see all the information you need in one place. By saving time on creating reports,
you can see how your business is doing and make profitable decisions quickly.
GAIN MORE CUSTOMER INSIGHTS
Meeting customers’ needs is what drives businesses forward, which is why it’s important that
you are able to discover patterns in customer behavior. Without BI tools, it is difficult to know
what customers really want without spending hours upon hours poring over past reports. BI
software allows you to identify which customers should be prioritized in order to increase
customer satisfaction and improve your market reputation.
SHOW IMPORTANT INFORMATION ABOUT YOUR SALES
One of the primary functions of BI applications is to reveal sales information, especially if you
work with multiple sales partners. With BI on hand, your team is able to know which sales
partners perform well and which need to exert more effort.
IDENTIFY AREAS WHERE YOU CAN CUT COSTS
BI software allows you to see which areas of your business you can save money on, such as
inventory. There may be an excess in your inventory, which translates to extra costs not only in
terms of acquisition, but also maintenance. Once you know where you can increase productivity
and cut costs, you can take the necessary action to increase your savings.
141 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
INCREASE EMPLOYEE PRODUCTIVITY
With BI tools, you are able to monitor the tasks, output and overall performance of your team.
This enables you to identify where you can streamline work processes and make your operations
more efficient, therefore increasing the productivity of your workforce.
ACHIEVE GREATER SOCIAL MEDIA INTELLIGENCE
Organizations leverage social media to connect with existing and potential customers. You can
use BI software to gain insights on consumer behavior and identify avenues for actively
connecting with people to expand your customer base.
142 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Great dashboards are clear, intuitive, and customizable.
They communicate information quickly.
They display information clearly and efficiently.
They show trends and changes in data over time.
They are easily customizable.
The most important widgets and data components are effectively presented in a
limited space.
An initial customization of visual data and information to key user requirements will help
improve usability and eliminate the need for different user personas.
Great dashboards
All essential information is immediately accessible.
Data is prioritized.
Information is displayed clearly in a visual hierarchy on one screen.
143 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
The design provides a coherent overview that includes sparse, clear initial data with additional
opportunities to drill down for more.
Elements (chart, table, form) are displayed in a minimized view with the ability to bring up
more details in a modal window or go to a page with more detail.
The design improves usability with filters allowing users to customize how data is displayed
and filters content using labels, categories, and KPIs.
Patching Customized Objects
This section explains how to re-apply a customization to an object that has been patched. For
example, if you install an Oracle BI Applications patch that modifies the Supply Chain and
Order Management application, must manually re-apply customizations that have made to the
Supply Chain and Order Management application.
144 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
A patch only installs changed repository objects, not the whole Work Repository. Therefore,
must re-apply customizations to mappings that have been changed by the patch. For example, if
a patch only modifies the Supply Chain and Order Management application, must manually re-
apply customizations that you have made to the Supply Chain and Order Management
application. The patch does not affect customizations in other applications.
As part of customizing an ETL task (including interfaces and package under a specific task
folder), you copy the task folder to be customized to a Custom folder, version the copy once to
freeze the original state, and version the copy again to capture the customized state. To modify
and version ETL customizations, see Extending Mappings in Oracle Business Analytics
Warehouse.
can customize and patch different ODI objects. Depending on the object, must follow different
steps to merge the patch and customizations.
If an object is customized, but is not being patched, this section does not apply. Similarly, if an
object is patched but is not customized, don’t need to follow these steps.
145 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Patching Customized Datastores
As part of the customization methodology, datastores that are customized are first versioned to
represent the original out-of-the-box state and versioned again to represent the customized
state. If have customized a datastore and want to patch the datastore, the patching process
merges the datastore to reflect the custom and patch changes in the same datastore. You might
want to create another version of the datastore prior to applying the patch, which represents the
patched and customized state.
Avoid bottlenecks and problems in a fragile market.
"Business intelligence is critical to both executives and owners equally as it provides insights
into the true health of an organization that are not readily available from a profit and loss
statement.
146 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
There are a plethora of BI applications available on the market today that integrate with your
accounting software. The key is to understand which is best for type of business as each has its
own pros/cons and features. Business intelligence is not just about tracking KPIs (key
performance indicators) once a month or quarter. BI includes forecasting to avoid bottlenecks
and provide perfect timing for decision making such as purchasing or new hires. An easy-to-
read dashboard that is reviewed weekly will help be more informed and avoid problems in a
very fragile market
147 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Task 04
4.1 importance and the impact of business intelligence tools and technologies
Important
Relevant and accurate reporting:
Using different kinds of data sources, employees can customize their reports and monitor KPIs.
Real-time generated reports offer the most pertinent data, which help companies make faster and
better decisions. Data from sales, finance, or operations are used to create easily accessible
reports, have great visualizations with the help of charts, graphs, tables, etc. These reports offer
faster insights, access, accuracy, and relevancy.
Key Insights
BI reporting tools assist in monitoring. To get the complete insight on revenue, losses, gains, the
productivity of the employees, performances of the employees (individual and team-based.) It
148 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
provides valuable information about the positives and the negatives. With these tools, companies
can easily track the metrics and be current with what’s happening and what’s to come by setting
up alerts, getting real-time information on the KPIs, and alerting any pitfalls that otherwise could
have gone unnoticed.
Stay ahead in the game:
Companies of all sizes have vast amounts of data. Moreover, managing and using data for
business decisions provides a competitive edge. BI offers incredible benefits with the help of this
data in terms of forecasting, budgeting, planning, and staying on top of things via analysis.
Competitive analysis helps companies to know the competition and the performance of their
competitors as well. This, in turn, leads to finding out how to differentiate one’s products from
others. It goes the same for services as well.
Quality and accurate data:
The success of any kind within an enterprise is data-dependent. Quality of data defines the
quality of the company and its success. Any inaccuracies or flaws in the data can turn businesses
upside down. BI tools help businesses in cleaning up data, creating data of high quality,
collecting, updating, and analysing data to gain the most relevant insight on what’s going on
within the company.
149 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Improved customer satisfaction:
Business intelligence software mainly helps companies to not just learn about their employees
but their customers too. When it comes to customer behaviour, user personas, feedback, BI lets
you in on all the insights. These BI tools help to identify what’s lacking with your services or
products and enhance customer satisfaction by making necessary changes. Real-time data on the
customer’s feedback help in bringing corrective changes and deliver excellent customer service
and satisfaction.
Improve growth patterns:
BI assists companies in gaining a competitive edge by helping them find new opportunities and
build smarter strategies. With the help of all the data, you can identify market trends and help
improve profit margins for the company. New sales trends can be identified by leveraging data
from the internal and external markets, analysing the data. The market conditions can help spot
any business issues that can otherwise go unnoticed.
Efficiency and accuracy:
BI tools offer a single source of information; it helps the employees or the executive hierarchy to
spend more time on productivity and less time on managing data. This way, employees can focus
on producing reports and timely deliverables in real-time. This accurate information leads to
better decision making and helps companies achieve long and short-term goals.
150 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Faster decision making:
BI reduces the times a company has to lose a customer, revenue, or deal with inaccurate
information or slow processes. It is essential in gaining a competitive edge for companies to
make faster and accurate decisions by leveraging the existing data, at the right time, and improve
decision making.
Greater operational efficiency and increased revenue:
BI tools offer business data, which makes the leaders and employees of a company think about
the decisions made, processes implemented, and strategies executed. Getting a 360-degree view
on all the dimensions to help companies identify issues and improve operations, increased sales,
and in turn, increase revenue.
Bigger profits:
Most businesses find profit margins as a big concern. BI tools can analysis from the enormous
volumes of data any discrepancies, inefficiencies, errors, etc. It helps expand profit margins, and
the sales teams get better insights for future sales and analysis where to spend the budgets in the
future.
151 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Impacts
Data-driven decision making
Before the introduction of advanced data analytics, business leaders tended to guess how best to
improve business processes. Nowadays, complex analytics provide managers with unique
insights into company processes. Data-driven decision making has become the norm, and BI
tools keep executives up to date. Those decisions may impact sales forecasts, budget planning,
employee bonuses and satisfaction, as well as enhance customer experience. Many of these
analyses can lead to company-wide changes which would not have occurred otherwise.
Moreover, BI tools function as a platform to build intelligent reports, KPIs and dashboards to
keep the team on the same page and allow them to act accordingly.
Performance
Among the elements which negatively influences employee productivity are lack of clear goals
and an overall sense of purpose. Burnout, frustration, and micr0management are all bottlenecks
to effective decision-making. However, BI may prompt both employees and management to
152 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
overcome these difficulties by optimizing their workdays and reacting quickly to changes. This
way, each employee feels responsible for the company’s performance.
As a result, the team becomes more agile and the company much more competitive. Business
Intelligence dashboards may turn the chain of command upside down, and instead of top-down
management most of the decisions are passed to business managers and frontline reps who have
the autonomy to act. Thus there will be an immediate boost in productivity, work quality, and
customer happiness.
The increase in employee efficiency is achieved due to the elimination of time-wasting, trivial
and redundant tasks such as compiling data from different locations. Employees with Business
Intelligence dashboards have all the important information they need at their fingertips. Focusing
on important tasks makes the employees more efficient and feel more fulfilled.
Agility
High-performing and efficient workers are also, unsurprisingly, agile workers. Business
Intelligence dashboard is also a time-saving tool which compels workers to focus their efforts
and attention on finding innovative solutions. Agile and self-organizing teams do not require to
be told which task to take on. Business Intelligence dashboards can help outline key parameters
concerning management expectations and present employees with hard data.
Among the chief characteristics of data is its objectivity. Numbers are numbers, not feelings.
This may be hard to grasp in times when things do not go according to plan and a team which
153 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
has been working on a project feels disheartened and unmotivated. With all the facts in one
place, it’s easier to make conscious decisions and attempt to gain a wider perspective on the
situation.
Task 4
4.2 Business Intelligence and Security
Business intelligence strategy has ushered in a new era for organizations the world over. A
strong focus on data analysis has business leaders enjoying reduced costs, increased efficiency,
and all around better section making. When previously unheard-of ROI is touted in headlines
regularly, it sparks more businesses follow suit and jump on the Bi movement. However, many
do so without considering the full implications of business intelligence on data security. The
mere act of producing receiving or housing data always poses a danger if left unsecured Those
Incorporating BI strategy Into their operations are at least more aware of their data, of what it is
and where it is housed. But knowledge doesn't equate to security, The Insights drawn from BI
and data analysis are no longer unstructured Is and Os, but highly sensitive easily understandable
information, making it even more valuable to a hacker, If they can steal data that has already
been analysed, then they are in effect stealing the very keys to your success.
Reference Unit 14 business intelligence page number 45- 53
154 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Law and Ethics in Information Security
The rules the members of a society create to balance the individual rights to self-determination
against the needs of the society as a whole are called taws. Laws are rules that mandate or
prohibit certain behaviour, hey are drawn from ethics which define socially acceptable
behaviours. The key difference between laws and ethics is that laws carry the authority of a
governing body, and ethic do not Ethics in turn are based on cultural mores the fixed moral
attitudes or customs of a particular group. Some ethical standards are universal. For example,
murder, theft, assault, and arson are actions that deviate from ethical and legal codes throughout
the world
Policy Verses Law
Within an organization, information securities professionals help maintain security via the
establishment and enforcement of policies. These policies guidelines that describe acceptable and
unacceptable employee behaviours in the workplace function as organizational laws complete
with penalties, judicial practices and sanctions to require compliance. Because these policies
function as laws, they must be crafted and implemented with the same care to ensure that they
are complete, appropriate, and fairly applied to everyone in the workplace. The difference
between a policy and a law, however, that ignorance of a policy san acceptable defines. Thus, for
a policy to become enforceable, it must meet the following five criteria
155 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Dissemination (distribution)-The organization must be able to demonstrate that the relevant
policy has been made readily available for review by the employee. Common dissemination
techniques include hard copy and electronic distribution.
Reference Unit 14 business intelligence page number 45- 53
Review (reading)- The organization must be able to demonstrate that it disseminated the
document in an intelligible form, including versions for illiterate, non English reading and
reading impaired employees Common techniques include recordings of the policy in English and
alternate language
Comprehension (understanding) The organization must be able to demonstrate that the employee
understood the requirements and content of the policy. Common techniques include quizzes and
other assessments
Compliance (agreement)- The organization must be able to demonstrate that the employee reed
to comply with the policy through act or affirmation. Common techniques include logon banners
which require a specific action (mouse click or keystroke) to acknowledge agreement, or a
156 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
signed document dearly Indicating the employee has read, understood, and agreed to comply
with the policy
Uniform enforcement. The organization must be able to demonstrate that the policy has been
uniformly enforced, regardless of employee status or assignment. Only when all of these
conditions are met can an organization penalize employees who violate the policy without fear of
legal retribution
Laws involved in information Security
General Computer Crime Law
The Computer Fraud and Abuse Act of 196 (CFA Act) as the cornerstone of many computer
related lesson Laws and entertainment efforts it was amended in October 1996 by the National
Information infrastructure Protection Act of 1996, which modified several sections of the
previous and increased the penates selected crime The punishment for offense prosecuted
under this statute varies from fin imprisonment up to 20 years, or both. The severity of the
penalty depends on the value of the information obtained and whether the offense s judged to
have been committed
1 For purposes of commercial advantage
157 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
2. for private financial gain
3. In furtherance of a criminal act
Computer Security Act of 1987 it was one of the first attempts.to protect federal computer
systems by establishing minimum acceptable security practices
Reference Unit 14 business intelligence page number 45- 53
Privacy Laws
Many organizations are collecting swapping , and selling personal information as a commodity,
and many people are looking to government for protection of their privacy
158 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Privacy of Customer information
Federal Privacy Act of 1974- regulates government agencies and holds them accountable if they
release private information about individuals or businesses without permission.
Electronic Communications Privacy Act of 1986-ta collection of statutes that regulates the
interception of wire, electronic, and oral communications
Health Insurance Portability and Accountability Act of 1996 (HIPAA) also known as the
Kennedy Kestenbaum Act, protect the confidentiality and security of health care data by
establishing and enforcing standards and by standardizing electronic data interchange HIPAA
affects all health care organizations including doctors practices, health clinics, life insurers, and
universities, as well as some organizations that have sell Insured employee health programs.
HIPAA specifies stiff penalties for organizations that fail to comply with the law, with fines up
to $250,000 and or 10 years imprisonment for knowingly misusing client information. It also
requires a comprehensive assessment of information security systems, policies, and procedures
where health care information is handled or maintained Electronic signatures have become
more common, and HIPAA provides guidelines for the use of these signatures based on
security standards that ensure message integrity, user authentication, and nonrepudiation
159 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Financial Services Modernization Act or Gramm-Leach Bliley Act of 1999 contains a number
of provisions focusing on facilitating affiliation among banks, securities firms, and insurance
companies. Specifically, this act requires all financial institutions to disclose the privacy
policies on the sharing of nonpublic personal Information
Reference Unit 14 business intelligence page number 45- 53
Copyright law
Intellectual property is a protect asset in the united states the U.S copyright laws extend this
privilege to the published word including electronic formats fair use allows copyrighted
materials to be used to support news resorting teaching scholarship and a number of similar
activities as long as the use is for educational or library purposes is not for profit and is not
excessive as long as proper acknowledgement is provided to the original author of such works
including a proper description of the location of source materials (citation) and the work is not
represented as ones own it is entirely permissible to include portions of someone else work as
reference
160 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Area Act Year Description
Telecommunications Telecommunications 1934 Regulates interstate and foreign
Deregulation and telecommunication (amended 1996
161 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Competition Act of and 2001)
1996 Update to
communication Act
of 1934 (47 USC 151
et seq)
Freedom of Freedom of 1966 Allows for the disclosure of
information information Act of previously unreleased information
1974 and documents controlled by the U.
S. government
Privacy Federal privacy Act of 1974 Governs federal agency use of
1974 personal information
Copyright Copyright Act of 1976 1976 Protects intellectual property,
Update to U. S including publications and software
Copyright Law (17
USC)
162 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Access to stored Unlawful Access to 1986 Provides penalties for illegally
communications stored accessing stored communication
Communication (18 (such as e-mail and voice mail)
USC 2701) stored by a service provider
Threats to computer Computer Fraud and 1986 Defines and formalizes law to
Abuse Act ( also counter threats from computer -
known as fraud and related acts and offences (amended
Related Activity in 1996,2001,and 2006
Connection with
computer) (18 USC
1030)
Federal agency Computer security 1987 Requires all federal computer
information security Act of 1987 systems that contain classified
information to have security plans
in place, and requires periodic
security training for all individuals
who operate, design manage such
systems
Copy protection Digital millilumen 1998 Provides specific penalties for
163 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
copyright Act (update removing copyright protection from
to 17 UCS 101) media
Terrorism USA patriots Act of 2001 Define stiffer penalties for
2002 (update to 18 prosecution of terrorist crimes
USC 1030)
Reference Unit 14 business intelligence page number 45- 53
Table 8
Cyber Security management
Cyber security comprises technologies , process and control that are designed to protest stamp
network and data from cyber attacks Effective cyber security reduces the risk of cyber
164 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
attacks, and product organizations and individuals from the unauthored exploitation of system,
networks and technologies
Elements of cyber security
application Security Application security the use of software, hardware, and procedural method
to product applications from external threats
information Security Information security o f strategies for managing the processes tools and
policies necessary to prevent, detect, document and counter threats to digital and non digital
information
Cloud providers are creating new security tools to help enterprise users better secure their their
, but the bottom line remains Moving to the cloud is not a panacea for performing due
diligence when comes to cyber security
Disaster Recovery / business Continuity planning A disaster Recovery plan (DRP) in
documented, structured approach with instructions for responding to unplanned incidents
Typically, disaster recovery planning Involves an analysis of business processes and continuity
needs a bus continuity plan (BCP) is document that consists of the critical information an
organization needs to continue operating during un planned event
165 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Operational Security OPSEC operational security) is an analytical process that classifies
information assets and determines the controls required to protect these assets
End User Education
Types of security Threats
Ransom ware is a type of malware that involves an attacker locking the victim's computer
system files, typically through encryption and demanding a payment to decrypt and unlock
them.
Malware is any file or program used to harm a computer user, such as worms, computer
viruses, Trojan horses and spyware.
166 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Social engineering is an attack that relies on human interaction to trick users into breaking
security procedures in order to gain sensitive information that is typically protected.
Phishing is a form of fraud where fraudulent emails are sent that resemble emails from
reputable sources: however, the intention of these emails is to steal sensitive data, such as credit
card or login information
Cyber Security and bi
Internet security is a major issue in our world. People and businesses worry about whether or
not there information safe and private People don’t want their identities to be stolen, and
businesses dos want any of their information leak Following are the top three ways that
business intelligence can prevent cybercrime.
167 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Reference Unit 14 business intelligence page number 45- 53
Analysis previous attacks
As a business, it's extremely important that you take a look at all of the times you have been
hacked or cyber security has been breached Can take this data and see where trends le Perhaps
your inf a vulnerable at the same time every year, Perhaps cyber hackers attack using the same
formula A intelligence tool can help you make sense of it all. With this information, you can
plan for cyber the future This can be crucial for protecting information in the hands of your
business
168 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
A Analyte previous attacks
As a business, itis extremely important that you take a look at all of the times you have been
handed on cyber security has been breached. El can take this data and see where trends lie
Perhaps information is vulnerable at the same time every year. Perhaps cyber hackers attack
using the same formula A business intelligence tool can help you make sense of it all. With
this information, you can plan for cyber attacks in the future. This can be crucial for protecting
information in the hands of your business
Cyber Security and big Data
big data has developed a new role in preventing adversaries from taking advantage of the
massive amounts of military intelligence, trade secrets, and personal and financial data
available through systems at al levels. Organizations are being encouraged to transition to
169 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
intelligence-driven security for a broader view and vulnerabilities. This requires analyzing
external threat intelligence feeds, cloud based calendar and documents social network activity
loc website generated information feeds and other non tradition sources of security information.
Big data's advantages le in the ability to analyze massive numbers of potential security events
and make connections between them to create a prioritized list of threats cybersecurity
professionals hope to stay ahead of cyber criminals with all the advantages of big data at the
disposal
In the era of big data, awareness is the first line of defense against cybercrime. As one
recent survey revealed, mast cybersecurity professionals know that they need to worry
about big data, but they don't always dearly understand what it means
Organizations should integrate customized processes and technical solutions geared to
their
specific risks and requirements to collect process, store, analyze and share data
Integrating big data analytics into a solid infrastructure to provide and develop security
solution essential - as is employing an expert IT staff to deploy them
170 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Strengthening cyber security teams with highly skilled data scientists and analytics
experts may become increasingly essential.
Future investments in technology should lean toward flexible, analytics-based solutions
that can change as business requirements and security threats evolve.
171 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Big data offers advantages to both the world of business and the underworld of hackers and
cyber criminals. With continuous effort, investment in technology and awareness, cybersecurity
professionals can win the battle against this and other complex challenges that new technology
will surely bring.
Reference Unit 14 business intelligence page number 45- 53
172 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Data security issues involved in organizations
information systems are frequently exposed to various types of threats which can cause
different types of damages that might lead to significant financial losses. Information security
damages can range from small losses to entire information system destruction. The effects of
various threats vary considerably some affect the confidentiality or Integrity of data while
others affect the availability of a system. Currently, organizations are struggling to understand
what the threats to their information assets are and how to obtain the necessary means to
combat them which continues to pose a challenge
Technology with Weak Security - New technology is being released every day. More times
than not, new gadgets have some form of Internet access but no plan for security. This presents
a very serious risk - each unsecured connection means vulnerability.
Social Media Attacks - Cybercriminals are leveraging social media as a medium to distribute a
complex geographical attack called "water holing. The attackers identify and infect a cluster of
websites they believe members of the targeted organization will visit. .
173 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Mobile Malware - Security experts have seen risk in mobile device security since the early
stages of their connectivity to the Internet. The minimal mobile foul play among the lory list of
recent attacks has users far les concerned than they should be. Considering our culture's
unbreakable reliance on cell phones and how little cybercriminals have targeted them. It creates
a catastrophic threat
Third-party Entry - Cybercriminals prefer the path of least resistance. Target is the poster child
of a major network attack through third party entry points
Social Engineering -Cybercriminals know intrusion techniques have a shelf life. They have
turned to reliable non-technical methods like social engineering which rely on social interaction
and psychological manipulation to gain access to confidential data. This form of intrusion is
unpredictable and effective
Lack of Encryption - Protecting sensitive business data in transit and at rest is a measure few
industries have yet to embrace, despite its effectiveness
Corporate Data on Personal Devices - Whether an organization distributes corporate phones or
confidential data is still being accessed on personal devices. Mobile management tools exist to
174 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
functionality but securing the loopholes has not made it to the priority list for many
organizations
Inadequate Security Technology - Investing in software that monitors the security of a network
has beer a growing trend in the enterprise space after 2014's painful rip of data breaches. The
software is desired to send alerts when intrusion attempts occur, however the alerts are only
valuable if someone is available to address them. Companies are relying too heavily on
technology to fully protect against attack when it i meant to be a managed tool
Reference Unit 14 business intelligence page number 45- 53
175 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
4.3
Business Intelligence Trends
Analyzing a large volume of data, then figuring out what to do with it is not an easy task. After
initial collection and analysis, a Business Intelligence (BI) analyst weighs the decision-making
responsibility with reference to the information at hand. This type of analysis is critical for
planning, optimizing time, and directing work in almost all aspects of business. Business
Intelligence helps companies focus their projects on certain areas which in turn make their
strategies successful. Why? Data doesn’t typically lie, and when a BI analyst is able to compile
and gain insights from hoards upon hoards of data, the insights derived will almost always
point to a solid solution.
the emerging business intelligence trends are:
Artificial Intelligence (AI)
Automation
Storytelling
Data Governance
176 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Natural Language Processes
Artificial Intelligence (AI)
The growth of Artificial Intelligence (AI) adoption is already a reality in most companies and
those who do not adopt it in 2019 may consider that they are falling behind. Almost 40% of
companies already have some type of AI automation, and a larger percentage have projects
underway for deployment as soon as possible.
The use of chatbots is a good example. As much as technology still lacks in some ways,
companies are working on constant improvements to tune their systems. And as this is a strong
trend, its smooth operation is on the agenda of improvements for all companies that already
adopt AI in any industry.
177 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Automation of human tasks
According to Gartner estimates, by 2020 over 40% of all data science tasks will be done by
machines without human interference. In fact, this is already a reality in many industries, and
automating any step in any process is the goal of all IT managers. The demand for business
intelligence analytics is always huge and there are not enough qualified people to meet it, so
automating processes have been paramount to the smooth running of the productivity stages of
any corporation.
Data Governance (keeping data secure)
The IT industry, which manages technological innovations, needs to have data governance.
This is a strong business intelligence trend. Companies and industries that have clear
governance have higher rankings and operate BI and data management more effectively. If the
data collected is not well managed or the information is not accurate, it can lead to a general
lack of trust in leaders.
178 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
In addition, it is important that companies follow the General Data Protection Regulation
(GDPR) that is already in place to ensure that data governance is not ignored.
Natural Language Processing (NLP)
Even though natural language processing (NLP) has been around for a few years, it has not
performed well and adhered because there is not a great demand for text-based queries.
Experts in the field believe that the new trend for NLQ would be a voice command. It is easier
to combine with mobile BI and will certainly have greater adhesion and effectiveness.
A good example is the iPhone Siri Assistant, which is used when the user is on mobile and not
on the computer. In addition to these trends, there are many innovations being developed.
Always try to know what is in the testing phase, what is feasible, and what's new in the IT
market.
179 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Business Intelligence Technologies
Data Warehousing
Data Warehouseman data warehouse (DW, DWH), or an enterprise data warehouse (EDW), is
a system that can be used for data analysis or with a reporting software. Say you work for a
company that uses multiple sources to keep track of transactional data. You want to view order
data from the past 5 years. Just thinking about exporting these lists and sifting through them all
gives me a headache. You can use a data warehouse to integrate data from one or more
disparate sources, which creates a central repository of data. Basically, this maintains a copy of
information from the source transaction systems so that you only need a single query engine to
view the data you need. A data warehouse is useful if you want a big picture of your
organization/enterprise, to keep historical data, to improve the quality of your data (more
consistent, less bad data, etc.), or to combine all data from different sources into a single data
model.
The main goal of a data warehouse is to combine data from different data sources and types of
data source. The main benefit of using a data warehouse is that all of the associated data can
then be used in disparate applications or in a singular application. Meaning you can better
connect the dots between your different business systems.
180 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Dashboards
Business Intelligence Technology- Dashboard A dashboard is an informative, easily readable,
usually one page, real-time user interface that shows a visual representation of data using
graphs and charts. By real-time, we mean that most dashboards can be pulled up on a web page
that is linked to a database so that the data shown is constantly updated and refreshed.
Dashboards show summaries, key trends, comparisons, and exceptions in both current and
historical data. This can enable you to see at a glance the performance and status of different
parts of an organization and to make informed business decisions. For example, a sales
dashboard may show the different product lines sold, the performance of salespeople, or the
sales numbers for different regions of the world.
Many dashboards have a drill capability and will allow you to instantly discover more detailed
information or view the data from another angle. The key benefits of dashboards are the ability
to visualize data anytime, to easily spot trends, to keep track of key performance indicators, and
to quickly gain total visibility or snapshots without having to run multiple reports.
181 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Ad Hoc Reporting
Self Service Data Insights Ad hoc as a Latin phrase simply translates to for this. It refers to a
solution that was created for a specific question or problem and is not meant to be changed or
adapted for different tasks. Ad hoc reporting is a common business term that references a report
or model that is produced for the purpose of answering a specific business question. The main
reason for ad hoc reporting may be to fill in a blank on an as-needed basis where a regular
report did not. Or, it may be used to aid the making of an important business decision.
For example, as the manager of a shop, you may need to decide whether you should purchase
new equipment. You can create some ad hoc reporting to determine if purchasing the
equipment would increase profitability. Lastly, the data retrieved from an ad hoc report will be
specific to answering one question, but can also be analyzed even deeper using a Web Report
or a dashboard designer.
Here are some additional benefits of Ad Hoc Reporting:
Self-service/Ad-hoc Reporting Makes Your Users Agile: Users are able to create, edit, and
reuse reports and dashboards easily and more agilely than having to go to your development
team every time they need a new report.
Interactive and Self-Service Tools Can Be More Easily Accessed: Self-Service and Ad hoc
tools are often web-based, meaning they can be accessed from any device connected to the
182 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
web. This allows end users to be more mobile for data discovery and decision support
anywhere.
Additional Interactivity and Flexibility: Ad hoc doesn’t just mean the creation of reports, or
even the editing of reports. Many self-service tools go beyond these functionalities with
increased types of interactivity such as drill down, sorting, filtering, etc. These all allow end
users to further explore their data for a more efficient workflow and for data discovery.
Your Users Can Edit and Reuse Widgets for Easier Collaboration Self-service analytics tools
often come built in with the ability to save, edit, reuse, and share full reports, dashboards, or
widgets. This can make collaborative decision making easier by giving multiple users the same
data resources easily, while simultaneously enabling them to do their own data discovery.
Data Discovery
Data Discovery Sometimes called knowledge discovery, data discovery is essentially a pattern
finding tool. Finding an understandable structure among dozens of fields in large relational
databases is usually difficult. Data discovery software can analyze a large amount of data to
183 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
locate information from that set and extract previously unfound patterns, outliers, associations,
and correlations. Because the uses of data discovery are so broad and are frequently also
applied to forms of large-scale data, information processing, and applications of computer
decision support systems, many times the term is used as a buzzword or to add value for
marketing purposes.
One example of data discovery in play is if you use the data discovery capacity of a software to
analyze regional sales patterns of coffee sales. You may discover that college students buy
more iced coffee Monday to Friday, and iced coffee buyers are more likely to purchase a
doughnut. You could use this newfound information to increase revenue by moving promotions
on iced coffee to weekends, and offering a deal for doughnuts with iced coffee.
Cloud Data Services
Cloud Data Services More likely than not, you’re already using some sort of cloud-based
service, whether it’s for business or personal purposes. An increasing number of businesses are
flocking to the cloud data service providers due to the new efficiency and capabilities they can
offer. Using cloud data services means you can access IT resources, data storage, customer
184 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
relationship management, enterprise resource planning, and marketing automation from
anywhere.
Data integration, transformation, management and security activities are no longer tethered to
physical bodies. This means you can access information from anywhere at any time, providing
unprecedented speed, agility, reliability, and security. You can choose to use private, public, or
hybrid clouds given the type of data integration and data quality maintenance you need. With
low overhead and easy scalability, it’s no wonder many businesses are jumping on the cloud
bandwagon.
Here are some additional benefits of using cloud for embedded reporting:
Implement and Deploy Quickly: Deploying a solution in the cloud can be much faster than
traditional deployments, with pre-built administrative structures, spinning up a cloud resource
can be very easy. Many reporting solutions also may have a pre-installed executable available
in cloud marketplaces such as AWS marketplace, for even faster deployment times.
Create a Competitive Edge: Embedded reporting allows you to empower your users with
enterprise level reporting capabilities faster and easier than developing them yourself. This can
be a huge competitive advantage if your in a marketplace which has yet to meet this demand.
Scale and Administer with Ease: Cloud can also enable you to scale up and down with ease.
The rise of cloud is built on a foundation of efficient scaling, and as long as the embedded
reporting system you’re using can match these capabilities you can easily scale for peak load
times. Report’s architecture was built to scale, allowing you to fully deploy in the cloud without
185 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
affecting baseline performance. Its architecture includes failover capabilities so there are no
single points of failure, as well as a variety of performance features such as load balancing to
help make your reporting more efficient. The administrative capabilities Report provides also
help you limit the number of administrative resources needed to handle large numbers of
customers by automating many of the workflows you would have to handle yourself if you
developed out a reporting component.
4.4 What is a business intelligence system?
According to Solomon Nash and Paul Gray, professors at Kennesaw State University and
Claremont Graduate University, a business intelligence system consists of data gathering, data
storage, knowledge management, and analysis.
186 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Data gathering collects information from every source and funnels it into one place. An
example of technology that powers this is a customer data platform like Segment.
Data storage safely hosts all of that data in a data warehouse, like Amazon Redshift.
Knowledge management is how all this data gets disseminated throughout an organization.
Analysis is, well, the analysis of this data to aid in decision-making.
what companies use business intelligence?
Most organizations do some form of business intelligence, but it’s not uncommon for a lot of it
to be manual work. For instance, a small startup’s “data gathering” may be manually exporting
CSVs from each data source. If they store all those spreadsheets on Google Drive, that’s
essentially their data warehouse.
This kind of process works OK up to a point, but it’s not sustainable for most businesses.
187 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
BI tools (especially self-service BI tools) manage your business’s data in a way that’s more
secure, easier to manage, and simpler to use. And the best BI tools automate much of the
system we outlined above, allowing employees to focus their efforts on analysis and taking
action.
The companies that benefit most from using business intelligence tend to be those that require
their employees to make independent decisions quickly. This makes it a good fit for startups,
data-centric companies, and companies looking to grow rapidly.
How is business intelligence used?
Business intelligence has as positive a impact on an organization's people as it does on
performance, projects, and decisions. Business Intelligence is used to turn data into actionable
information for leadership, management, organization and decision making. The following are
some of the ways organizations are learning to use business intelligence:
188 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Analyzing customer behaviors, buying patterns and sales trends
Measuring, tracking and predicting sales and financial performance
Budgeting and financial planning and forecasting
Tracking the performance of marketing campaigns
Optimizing processes and operational performance
Improving delivery and supply chain effectiveness
Web and e-commerce data analytics
Customer relationship management
Risk analysis
Strategic value driver analysis
What’s the difference between business intelligence and competitive intelligence?
There are a number ways to view discrepancies between business intelligence and competitive
intelligence. Competitive intelligence is defined as the process of gathering and analyzing
intelligence about a business's external environment, such as the market landscape for a
189 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
particular industry or a business's competitors. In contrast, business intelligence is understood
as internal business insights, what your company is doing.
Business Intelligence and Competitive Intelligence may technically have different definitions,
however they are closely related and must work together to make informed business objectives.
Some consider competitive to be a subset of business intelligence because the information
gathered from competitive intelligence adds value to data collected from BI and decision
making.
It is important to note that many business intelligence tools have competitive intelligence
functionality. For example, dashboards can be used to track competitors to identify
opportunities in areas such as keywords and social media content
Organizational benefits of implementing business intelligence
Quick answers to critical business questions.
Align activities with strategy.
Reduce time spent on data entry and manipulation.
Gain in depth real time insights into customers.
190 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Benchmark data against competitor and historical data for continuous improvements.
Identify and analyze areas to cut costs and for budget allocation.
Boost internal productivity by spending time on what’s important.
business intelligence how can help at companies
BI can help measure company progress.
Business intelligence applications can be used to create a hierarchical performance metric, which
analyses how a business performs across several key sectors. These sectors can include time,
cost, resources, scope, quality and actions. The performance metric is designed to keep track of
various markers that are important to shareholders, executives, employees, and customers and
ensure that the company remains healthy, efficient, and profitable. Should the company fall short
of any of the metrics, the problem can be diagnosed and solved before it evolves into a much
bigger mess.
191 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
BI can create company benchmarks.
Benchmarking is the process of comparing one company's progress across certain important
factors with industry best practices. Business intelligence can help a company rise far above
industry benchmarks by increasing speed and decreasing costs. Benchmarking allows
companies to quickly and easily spot the areas where they may be falling short of their
competition. Benchmarking also helps companies identify the rivals that are the most likely to
pose a threat, which can help a business stay motivated to do its best.
192 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
BI can uncover hidden, forgotten, or lost data.
Business knowledge discovery is a process that involves mining data from archives and hard
drives long forgotten in dusty warehouses or buried beneath hundreds of newer files in a
computer system. One of business intelligence's primary functions is to better organize and
manage this data -- and all future data -- so as to allow a company instantaneous access to
records from almost any date, year, or time, regarding anything from efficiency to sales to
profits to losses. Having access to this additional data is crucial in helping a company avoid
past mistakes and learn from previous strategies, leaders, and techniques.
193 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Determine the ROI of marketing strategy.
"In a market saturated with apps, social media platforms, analytics tools, and pay-per-click
campaigns, business intelligence is crucial in helping small businesses figure out if the
marketing strategy they've invested in is producing ROI (return on investment). Business
intelligence can translate into analytics reports where businesses can base decisions on solid
research, data, and facts,
194 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Derive knowledge from a sea of data.
"Business intelligence today is more important than ever. Ninety percent of the data that exists
today the world over was created in the last two years alone. Going forward, the rate of data
creation is only going to accelerate. The chief reason for that is the explosion of social media
channels and the burgeoning number of users disseminating data at breakneck speeds.
What's the point of all that sea of data without an iota of insightful information?
Businesses are finding it a conundrum to decipher meaningful insights out of it all. This is
where business intelligence can chip in. It brings a method to the madness of all that petabytes
of data floating around. It is the art of deriving knowledge from all the business processes to
help enterprises gain a head start to better understand customer needs and market dynamics.
195 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Improving performance, delivering on customer promises, and building long-term customer
relationships are some of the benefits of BI.
Track inventory and capitalize on trends.
"Business intelligence or analytics has become critical in retail given the fast pace at which
consumers expect orders to be delivered to their doorsteps (the Amazon effect). Retailers and
brands need to know where their inventory is located and how well it’s selling. Analytics
provides this insight to buyers and executives so they can capitalize on buying trends.
196 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Usage of business intelligence
With a host of functions and a distinct role BI brings immense benefits for business. Typical Bi
solution allow to do the following
Enhance decision making
Increase operational efficiency
improve internal business process
measure corporate performance
generate new revenues
gain competitive advantages
identify market trend and directions
spot business problem
prepare for future challenges
although the above example may be too general in scope and circumstance each can have a
profound and lasting impact on a business. itemizing specific advantage of BI for company may
need another article suffice to say that business intelligence will permeate and influence every
aspect of business process sale marketing management administration, operations, performance
197 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
, targets directions simple because each of these areas require large data that need to be collect
filtered analyzed and known by key people who decides the what when who and how to keep
business healthy and profitable .
Reference Unit 14 business intelligence page number 43
198 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
References
References Sri Lanka Export Development Board
References Sri Lanka Export Development Board , INDUSTRY CAPABILITY REPORT
Reference Unit 14 business intelligence page number 21- 25
Reference Unit 14 business intelligence page number 43
Reference Unit 14 business intelligence page number 45- 53
Reference Unit 14 business intelligence page number 45- 53
199 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
Grading Rubric
Grading Criteria Achieved Feedback
LO1 Discuss business processes and the mechanisms
used to support business decision-making.
200 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
P1 Examine, using examples, the terms ‘Business
Process’ and ‘Supporting Processes’.
M1 Differentiate between unstructured and semi-
structured data within an organisation.
D1 Evaluate the benefits and drawbacks of using
application software as a mechanism for business
processing.
201 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
LO2 Compare the tools and technologies associated
with business intelligence functionality
P2 Compare the types of support available for business
decision-making at varying levels within an
organization.
M2 Justify, with specific examples, the key features of
business intelligence functionality.
202 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
D2 Compare and contrast a range of information
systems and technologies that can be used to support
organisations at operational, tactical and strategic
levels.
LO3 Demonstrate the use of business intelligence tools
and technologies
P3 Determine, with examples, what business
intelligence is and the tools and techniques associated
203 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
with it.
P4 Design a business intelligence tool, application or
interface that can perform a specific task to support
problem-solving or decision-making at an advanced
level.
204 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
M3 Customise the design to ensure that it is user
friendly and has a functional interface.
D3 Provide a critical review of the design in terms of
how it meets
a specific user or business requirement and identify
what customisation has been integrated into the
design.
205 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
LO4 Discuss the impact of business intelligence tools
and technologies for effective decision-making
purposes and the legal/regulatory context in which
they are used
P5 Discuss how business intelligence tools can
contribute to effective decision-making.
206 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
P6 Explore the legal issues involved in the secure
exploitation of business intelligence tools.
M4 Conduct research to identify specific examples of
organisations that have used business intelligence
tools to enhance or improve operations
207 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
D4 Evaluate how organisations could use business
intelligence to extend their target audience and make
them more competitive within the market, taking
security legislation into consideration.
208 | P a g e
Pradeeban.A Col/A-064620 Unit_14 Business Intelligence
You might also like
- A-008550-1624862702015-80342-BIIII-converted (44445)Document69 pagesA-008550-1624862702015-80342-BIIII-converted (44445)Hansi RanasingheNo ratings yet
- Unit 30-Application Development-Reworded-2021Document15 pagesUnit 30-Application Development-Reworded-2021Jimmy CyrusNo ratings yet
- Unit 14 - Business IntelligenceDocument14 pagesUnit 14 - Business IntelligenceIshara EroshiNo ratings yet
- 1183-1620008969581-UNIT 14 - Business Inteligent Assignment - Reworded 2021Document18 pages1183-1620008969581-UNIT 14 - Business Inteligent Assignment - Reworded 2021Harshi PereraNo ratings yet
- How - Business - Intelligence - Help - Organizations ResearchDocument105 pagesHow - Business - Intelligence - Help - Organizations Researchmojoxe100% (3)
- BI Assignment7Document38 pagesBI Assignment7Shaku MakuNo ratings yet
- AssDocument15 pagesAssOntime Bestwriters50% (2)
- Computing Research Project QuestionDocument7 pagesComputing Research Project QuestionkarkiakNo ratings yet
- A-008550-1624879801227-80375-57-Unit 19-DsaDocument80 pagesA-008550-1624879801227-80375-57-Unit 19-DsaHansi RanasingheNo ratings yet
- H I ĐĂNG Assigment 3 1641Document17 pagesH I ĐĂNG Assigment 3 1641Huynh Ngoc Hai Dang (FGW DN)No ratings yet
- Internal Verification of Assessment Decisions - BTEC (RQF) : Higher NationalsDocument27 pagesInternal Verification of Assessment Decisions - BTEC (RQF) : Higher NationalsSusira MednisNo ratings yet
- A-065211-1606734174791-53830-Unit 10 Web Design and Development - KavinDocument115 pagesA-065211-1606734174791-53830-Unit 10 Web Design and Development - KavinRehan RatnaweeraNo ratings yet
- 786-1601897169527-Unit 10 - Web Design and Development - 2020Document9 pages786-1601897169527-Unit 10 - Web Design and Development - 2020Kevin JeromNo ratings yet
- Business Intelligance Pradeep SirDocument5 pagesBusiness Intelligance Pradeep SirRohim Acharya100% (1)
- 785-1601896966591-Unit 04 - Database - 2020Document13 pages785-1601896966591-Unit 04 - Database - 2020Udeshika WanninayakeNo ratings yet
- Unit 10 Web Design and DevelopmentDocument13 pagesUnit 10 Web Design and DevelopmentCULPRIT BOY0% (2)
- A-008550-1624688646968-80386-Unit 34 - System Analysis and Design.Document103 pagesA-008550-1624688646968-80386-Unit 34 - System Analysis and Design.Hansi Ranasinghe100% (1)
- Business Intelligence-LO3Document13 pagesBusiness Intelligence-LO3Shaku MakuNo ratings yet
- Internal Verification of Assessment Decisions - Btec (RQF) : Jghigher NationalsDocument32 pagesInternal Verification of Assessment Decisions - Btec (RQF) : Jghigher NationalsSusira MednisNo ratings yet
- BI - Assignment-Part 1&2Document41 pagesBI - Assignment-Part 1&2Shaku Maku50% (2)
- P5: Analyze Research and Data Using Appropriate Tools and TechniquesDocument4 pagesP5: Analyze Research and Data Using Appropriate Tools and TechniquesSaurav Lamichhane0% (1)
- Harsha Akka 013759 Unit 13 CRP Report PDFDocument94 pagesHarsha Akka 013759 Unit 13 CRP Report PDFMinda RajanNo ratings yet
- 789-1601897728690-Unit 6 Managing A Successful Computing Research Project - 2020Document14 pages789-1601897728690-Unit 6 Managing A Successful Computing Research Project - 2020Kevin JeromNo ratings yet
- Col e 004653 MSCP Com079Document41 pagesCol e 004653 MSCP Com079AliNo ratings yet
- A-019730-1659516307423-163428-W.M.supun Anjana Jayasinghe Advanced Programming - Reworded - 2021Document115 pagesA-019730-1659516307423-163428-W.M.supun Anjana Jayasinghe Advanced Programming - Reworded - 2021Dishan SanjayaNo ratings yet
- 3467 HND 10 Hajanya Kalaruban Database Devolopment Management SystemDocument90 pages3467 HND 10 Hajanya Kalaruban Database Devolopment Management Systemronica100% (1)
- A 019730 1634729704082 114149 W.M.S.a.jayasinghe Unit 10 Web Design and Development - Reworded - 2021Document69 pagesA 019730 1634729704082 114149 W.M.S.a.jayasinghe Unit 10 Web Design and Development - Reworded - 2021Dishan Sanjaya100% (1)
- SAD Assignment - NewDocument10 pagesSAD Assignment - Newpratheep100% (1)
- Unit 10 Website Design and Development (Spring 2021) 2 of 2Document3 pagesUnit 10 Website Design and Development (Spring 2021) 2 of 2Ultra ChannelNo ratings yet
- Unit 20 - Assignment Brief 1Document2 pagesUnit 20 - Assignment Brief 1Võ Ngọc HùngNo ratings yet
- Report of BI - Nguyễn Văn HiếuDocument33 pagesReport of BI - Nguyễn Văn HiếuHiếu NguyễnNo ratings yet
- Assignment 1: Business IntelligenceDocument40 pagesAssignment 1: Business IntelligenceThanh TaiNo ratings yet
- Unit 14 - Assignment Brief 2Document2 pagesUnit 14 - Assignment Brief 2Thanh TaiNo ratings yet
- 200-1540467149117-Unit 04 Database-Assignment HolisticDocument17 pages200-1540467149117-Unit 04 Database-Assignment HolisticMahesh Pradeep0% (2)
- Unit 19 - Data Structure & AlgorithmsDocument6 pagesUnit 19 - Data Structure & AlgorithmsThandar Lwin0% (1)
- WDD-IN0719A22H-Nishant Shah-Assignment 1Document29 pagesWDD-IN0719A22H-Nishant Shah-Assignment 1Nishant ShahNo ratings yet
- A-011814-1612368830998-72379-Lahiru Viraj - ME24716 - 799-1601899513739-Unit 18 - Discrete MathematicsDocument89 pagesA-011814-1612368830998-72379-Lahiru Viraj - ME24716 - 799-1601899513739-Unit 18 - Discrete MathematicsLahiru VirajNo ratings yet
- ABC Assignment PDFDocument64 pagesABC Assignment PDFRaishaNo ratings yet
- HNDCS - Unit 34 LO1Document5 pagesHNDCS - Unit 34 LO1Y.h. Tariq100% (1)
- HND in Computing Networking Unit 2 Assignment 1 SampleDocument85 pagesHND in Computing Networking Unit 2 Assignment 1 SampleronicaNo ratings yet
- MSCP SampleDocument41 pagesMSCP SampleRomali KeerthisingheNo ratings yet
- MSCP Pasi NewDocument38 pagesMSCP Pasi NewHimsara vihanNo ratings yet
- Business Intelligence-LO1Document10 pagesBusiness Intelligence-LO1Shaku MakuNo ratings yet
- Assignment 1: BTEC HND Diploma in Computing and Systems DevelopmentDocument14 pagesAssignment 1: BTEC HND Diploma in Computing and Systems DevelopmentDuy Trịnh0% (1)
- 788-1601897459456-Unit 05 - Security - 2020Document14 pages788-1601897459456-Unit 05 - Security - 2020Career and EducationNo ratings yet
- Managing Successful Computing Project AssignmentDocument49 pagesManaging Successful Computing Project AssignmentRajesh PrabhakarNo ratings yet
- Unit 04 - Database AssignmentDocument131 pagesUnit 04 - Database AssignmentThushan LakshithaNo ratings yet
- Unit 04 - Database Design and Development Reworded 2021Document47 pagesUnit 04 - Database Design and Development Reworded 2021Cool Martt50% (2)
- MATHS EsoftDocument84 pagesMATHS EsoftAshen WeerasingheNo ratings yet
- 54-1547092378635-Unit 34 SAD - Assignment 2018.11.13Document14 pages54-1547092378635-Unit 34 SAD - Assignment 2018.11.13Kevin JeromNo ratings yet
- Higher Nationals in Computing: Unit 03: Professional Practice Assignment 1Document42 pagesHigher Nationals in Computing: Unit 03: Professional Practice Assignment 1Vy NguyễnNo ratings yet
- A-008550-1619669549760-55540 - Unit 10 - Web Design New SubDocument83 pagesA-008550-1619669549760-55540 - Unit 10 - Web Design New SubHansi RanasingheNo ratings yet
- 04-DDD.Assignment 1 frontsheet 2018-2019-đã chuyển đổi PDFDocument12 pages04-DDD.Assignment 1 frontsheet 2018-2019-đã chuyển đổi PDFl1111c1anh-5No ratings yet
- ABC Different Code Premnath PDFDocument81 pagesABC Different Code Premnath PDFRaishaNo ratings yet
- New BI Assignment - HND Batch 7 8Document48 pagesNew BI Assignment - HND Batch 7 8Malsha NishaniNo ratings yet
- A 019730 1647416384898 137822 W.M.supun Anjana Business InteligentDocument138 pagesA 019730 1647416384898 137822 W.M.supun Anjana Business InteligentDishan SanjayaNo ratings yet
- Higher NationalsDocument82 pagesHigher NationalsRaishaNo ratings yet
- BiiiiDocument104 pagesBiiiiarmirshadh22No ratings yet
- E126764-1672500710955-199830-OPM AssignmentDocument73 pagesE126764-1672500710955-199830-OPM AssignmentDilusha DasanayakaNo ratings yet
- 1183-1620008969581-UNIT 14 - Business Inteligent Assignment - Reworded 2021Document30 pages1183-1620008969581-UNIT 14 - Business Inteligent Assignment - Reworded 2021Chanaka SandaruwanNo ratings yet
- Q1. What Is JDBC? Explain Different Types JDBC Drivers With Suitable DiagramDocument64 pagesQ1. What Is JDBC? Explain Different Types JDBC Drivers With Suitable DiagramjyebbwycqmfkuxNo ratings yet
- Reaction Paper DementiaDocument1 pageReaction Paper DementiaElla MejiaNo ratings yet
- José Guadalupe PosadaDocument19 pagesJosé Guadalupe PosadaJudy Baca100% (1)
- Practical CS ProcessingDocument483 pagesPractical CS ProcessinganAMUstudent100% (2)
- NCP81205Document1 pageNCP81205Tom TomNo ratings yet
- Titus Selection of DiffuserDocument14 pagesTitus Selection of DiffuserhanyassawyNo ratings yet
- Unseen Passage 2Document6 pagesUnseen Passage 2Vinay OjhaNo ratings yet
- Epidemiological Triad of HIV/AIDS: AgentDocument8 pagesEpidemiological Triad of HIV/AIDS: AgentRakib HossainNo ratings yet
- GENUS Clock Gating Timing CheckDocument17 pagesGENUS Clock Gating Timing Checkwasimhassan100% (1)
- Simple Love Spells That WorkDocument14 pagesSimple Love Spells That Workagg24ankitNo ratings yet
- 28 ESL Discussion Topics Adult StudentsDocument14 pages28 ESL Discussion Topics Adult StudentsniallNo ratings yet
- Applied Computational AerodynamicsDocument15 pagesApplied Computational AerodynamicsjoereisNo ratings yet
- Review Systems of Linear Equations All MethodsDocument4 pagesReview Systems of Linear Equations All Methodsapi-265647260No ratings yet
- Letter of Intent Date: 18-Feb-2019 Mr. Ravi Mishra,: For Multiplier Brand Solutions PVT LTDDocument2 pagesLetter of Intent Date: 18-Feb-2019 Mr. Ravi Mishra,: For Multiplier Brand Solutions PVT LTDRavi MishraNo ratings yet
- AR Financial StatementsDocument281 pagesAR Financial StatementsISHA AGGARWALNo ratings yet
- Electric Valve Actuator Type Car: For 2 & 3-Way Valves Type G/L/M/S 2Fm-T & G/L/M/S 3Fm-T Page 1 of 4 0-4.11.08-HDocument4 pagesElectric Valve Actuator Type Car: For 2 & 3-Way Valves Type G/L/M/S 2Fm-T & G/L/M/S 3Fm-T Page 1 of 4 0-4.11.08-HMuhd Khir RazaniNo ratings yet
- Research Paper Effect of Mobile Banking On Customer-823Document11 pagesResearch Paper Effect of Mobile Banking On Customer-823amittaneja28No ratings yet
- Grade 8 Mathematics Checkpoint Booklet AY 23-24Document270 pagesGrade 8 Mathematics Checkpoint Booklet AY 23-24Arta riaNo ratings yet
- Review of Related Literature and Related StudiesDocument23 pagesReview of Related Literature and Related StudiesReynhard Dale100% (3)
- EHR StandardsIndia - August 2013-32630521Document54 pagesEHR StandardsIndia - August 2013-32630521kartiksinhNo ratings yet
- Federal Government Employees Housing FoundationDocument2 pagesFederal Government Employees Housing FoundationMuhammad Shakil JanNo ratings yet
- G2A Glitch DONT LEAK 2Document7 pagesG2A Glitch DONT LEAK 2qDeficiencyNo ratings yet
- Corporate Profile of Multimode GroupDocument6 pagesCorporate Profile of Multimode GroupShaheen RahmanNo ratings yet
- Marketing Measurement Done RightDocument16 pagesMarketing Measurement Done RightWasim Ullah0% (1)
- Autodesk Design Review: About DWF and DWFXDocument7 pagesAutodesk Design Review: About DWF and DWFXNesreNo ratings yet
- 064 DIR - Launching Whipping Creme & Skimmed Milk Di Channel Horeka (Subdist Masuya)Document3 pages064 DIR - Launching Whipping Creme & Skimmed Milk Di Channel Horeka (Subdist Masuya)indra sapta PrahardikaNo ratings yet
- Game On Series BibleDocument28 pagesGame On Series Bibleapi-513832615No ratings yet
- SOP For Operation & Calibration of PH Meter - QualityGuidancesDocument9 pagesSOP For Operation & Calibration of PH Meter - QualityGuidancesfawaz khalilNo ratings yet
- Practice Quiz Reflection Project Initiation and Key ComponentsDocument3 pagesPractice Quiz Reflection Project Initiation and Key ComponentsFalastin Tanani67% (3)
- STS Reviewer FinalsDocument33 pagesSTS Reviewer FinalsLeiNo ratings yet