Professional Documents
Culture Documents
Is Assignment 2020
Uploaded by
Tân Hoàng0 ratings0% found this document useful (0 votes)
9 views1 pageThis document outlines an assignment for an introduction to information security course. It includes 3 tasks: 1) compiling the Crypto++ library on Windows, Linux, or MacOS, 2) coding various hash functions and block ciphers using the Crypto++ library, and 3) testing the coded functions on input strings of varying lengths and recording average running times. Students are to submit a report with their hardware information, source codes, test results in table and graph form, and conclusions about how running time relates to input size.
Original Description:
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThis document outlines an assignment for an introduction to information security course. It includes 3 tasks: 1) compiling the Crypto++ library on Windows, Linux, or MacOS, 2) coding various hash functions and block ciphers using the Crypto++ library, and 3) testing the coded functions on input strings of varying lengths and recording average running times. Students are to submit a report with their hardware information, source codes, test results in table and graph form, and conclusions about how running time relates to input size.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
9 views1 pageIs Assignment 2020
Uploaded by
Tân HoàngThis document outlines an assignment for an introduction to information security course. It includes 3 tasks: 1) compiling the Crypto++ library on Windows, Linux, or MacOS, 2) coding various hash functions and block ciphers using the Crypto++ library, and 3) testing the coded functions on input strings of varying lengths and recording average running times. Students are to submit a report with their hardware information, source codes, test results in table and graph form, and conclusions about how running time relates to input size.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 1
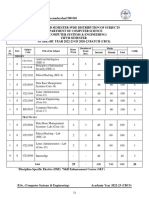
FACULTY OF INFORMATION TECHNOLOGY
SCHOOL YEAR: 2020 – 2021
SEMESTER I
INTRODUCTION TO INFORMATION SECURITY
ASSIGNMENT
1. TASK 1 - Compile Crypto++ on windows [or core linux (ubuntu or redhat), or
MacOS] (LINK download below).
2. TASK 2 - Coding for following functions:
- Hash Functions: SHA-1, SHA-2 (SHA-256 or SHA-512), SHA-3;
- Block ciphers: AES (Mode: ECB, CBC, CFB, OFB, CTR);
- Public Key Signature Schemes: DSA2, ECDSA.
3. TASK 3 - Test the functions in TASK-2 on windows (or core linux OS);
- Input string length: 256 bits, 512 bits, 1024 bits; 2048 bits; 4096 bits
- Running times: Count on the average of 1000 running times;
What to Submit: Report the results
- Information of your hardware platform (RAM, CPU, Operating system,...)
- The compiler version of the functions in Task 2 (including the source codes)
- The results of the tests in Task 3;
- Draw the results of test and report your conclusion:
Running times vs input sizes
Time: 4 weeks
Download library: https://www.cryptopp.com/#download
Reading the guides https://www.cryptopp.com/docs/ref/
You might also like
- ESP32 Programming for the Internet of Things: JavaScript, AJAX, MQTT and WebSockets SolutionsFrom EverandESP32 Programming for the Internet of Things: JavaScript, AJAX, MQTT and WebSockets SolutionsRating: 5 out of 5 stars5/5 (2)
- Question OneDocument4 pagesQuestion OneCollins MunuoNo ratings yet
- ISE - 7th Sem SyllabusDocument17 pagesISE - 7th Sem SyllabusPraveen TPNo ratings yet
- 20-CP-56 CCN Lab Report # 3Document8 pages20-CP-56 CCN Lab Report # 3Faria RaghibNo ratings yet
- B.Sc. III Sem22-23Document34 pagesB.Sc. III Sem22-23radhakrishn0729No ratings yet
- Lab Manual No 7 MCSDDocument12 pagesLab Manual No 7 MCSDRanna FarooquiNo ratings yet
- CIS Fall 2022-TCP IPDocument5 pagesCIS Fall 2022-TCP IPMahnoor SiddiquiNo ratings yet
- University Institute of Engineering Department of Computer Science & EngineeringDocument6 pagesUniversity Institute of Engineering Department of Computer Science & EngineeringPragnya RajNo ratings yet
- Anil DT 2Document6 pagesAnil DT 2Pragnya RajNo ratings yet
- Page 1 of 10Document10 pagesPage 1 of 10cj07101973No ratings yet
- p9 Ins VedantDocument2 pagesp9 Ins Vedantjay limbadNo ratings yet
- TEACHING AND EVALUATION SCHEME FOR 6th Semester (CSE) (Wef 2020-21)Document25 pagesTEACHING AND EVALUATION SCHEME FOR 6th Semester (CSE) (Wef 2020-21)SWARNA LATANo ratings yet
- 1-Using The Following Code Write A Function To Insert A New Node in A Specific Position in The LinkedlistDocument2 pages1-Using The Following Code Write A Function To Insert A New Node in A Specific Position in The Linkedlistmohamed elgammlNo ratings yet
- 03 Syllabus 2021 22Document103 pages03 Syllabus 2021 22gokaraju421No ratings yet
- Course Outline On Certified Ethical Hacker v10 - 2020Document2 pagesCourse Outline On Certified Ethical Hacker v10 - 2020A.S.M.RashelNo ratings yet
- Lab Assignment 2Document2 pagesLab Assignment 2KHUSH 2.0No ratings yet
- Cybersecurity in Intelligent Transportation SystemDocument8 pagesCybersecurity in Intelligent Transportation SystemPalak NigamNo ratings yet
- BCA 1st Sem Assignment 2020-21 22 23Document11 pagesBCA 1st Sem Assignment 2020-21 22 23jiveeNo ratings yet
- School of Information Technology and Engineering FALL Semester - 2021-22Document2 pagesSchool of Information Technology and Engineering FALL Semester - 2021-22stress bustersNo ratings yet
- A6902 en 1Document2 pagesA6902 en 1MJ TarhiniNo ratings yet
- Dotnet - New 2022 TopicsDocument12 pagesDotnet - New 2022 TopicsPraveen kumar .vNo ratings yet
- VL7002 - Security Solutions in VlsiDocument10 pagesVL7002 - Security Solutions in VlsiRaja PirianNo ratings yet
- Summer Training Report: Jaypee Institute of Information TechnologyDocument11 pagesSummer Training Report: Jaypee Institute of Information TechnologyRohit ChaurasiaNo ratings yet
- Cloud Computing ItDocument3 pagesCloud Computing ItPatricioNo ratings yet
- Assessment 1 CommandsDocument3 pagesAssessment 1 Commandsuday kiranNo ratings yet
- Iscf pg2013 14 PDFDocument34 pagesIscf pg2013 14 PDFSumanNo ratings yet
- Cia Ii Ita14 Ethical Hacking Desceptive QuestionsDocument1 pageCia Ii Ita14 Ethical Hacking Desceptive QuestionsVijay.PNo ratings yet
- Areej Ghazal CVDocument2 pagesAreej Ghazal CVapi-463853015No ratings yet
- 17-Esp8266 Nodemcu Ultrasonicsensor Thingspeak Api Whatsapp Nodemcu Server-04-07-2023Document4 pages17-Esp8266 Nodemcu Ultrasonicsensor Thingspeak Api Whatsapp Nodemcu Server-04-07-2023dummyfr07No ratings yet
- MSEI-022 (P) Post Graduate Diploma in Information Security (Pgdis) Term-End Practical Examination December, 2018 Msei-022 (P) : Network SecurityDocument1 pageMSEI-022 (P) Post Graduate Diploma in Information Security (Pgdis) Term-End Practical Examination December, 2018 Msei-022 (P) : Network SecurityEknoorNo ratings yet
- Training Outline - Industrial Cybersecurity DC v2Document3 pagesTraining Outline - Industrial Cybersecurity DC v2AmmarNo ratings yet
- Sayed MDocument3 pagesSayed Meng_sayed_19859783No ratings yet
- IT - Teaching Scheme - VII - 040909064708 - 1Document1 pageIT - Teaching Scheme - VII - 040909064708 - 1Kelly McclureNo ratings yet
- Ty.b.sc - Computersciencesyllabus Course OutcomesDocument36 pagesTy.b.sc - Computersciencesyllabus Course OutcomesSarsawathi ANo ratings yet
- Diploma in Computer Science & EngineeringDocument39 pagesDiploma in Computer Science & Engineeringamitsingh63051No ratings yet
- Basics of Information Security Course Code: 4360702Document8 pagesBasics of Information Security Course Code: 4360702BJAYG2005No ratings yet
- ES Course Handout (BIT451)Document3 pagesES Course Handout (BIT451)Afshan KaleemNo ratings yet
- Itexamanswers Net Ccna Security v2 0 Chapter 8 Exam AnswersDocument17 pagesItexamanswers Net Ccna Security v2 0 Chapter 8 Exam AnswersDDDDNo ratings yet
- BCA SEMESTER-VI Assignments 2021-22Document6 pagesBCA SEMESTER-VI Assignments 2021-22Ankit SharmaNo ratings yet
- UG 4-1 R19 CSE SyllabusDocument33 pagesUG 4-1 R19 CSE SyllabusMasimukkala SunithaNo ratings yet
- Lab7 CLCDocument23 pagesLab7 CLCnguyenquangphuoc5922No ratings yet
- Resume SAAIDI YassineDocument2 pagesResume SAAIDI YassineYassine SaaidiNo ratings yet
- Mobile ComptingDocument1 pageMobile ComptingDinesh RathiNo ratings yet
- Scheme 3 YearDocument33 pagesScheme 3 YearShwetta BajpaiNo ratings yet
- IT Autonomous B Tech 6 Sem SyllebusDocument18 pagesIT Autonomous B Tech 6 Sem SyllebusamanraoxNo ratings yet
- VLSI &embedded SystemsDocument38 pagesVLSI &embedded SystemsOLLURI ROHITNo ratings yet
- My CVDocument2 pagesMy CVyarakhaledweschoolNo ratings yet
- IT1100 - Tutorial 4 - 2024Document1 pageIT1100 - Tutorial 4 - 2024thedarkhell123No ratings yet
- BCA Old Scheme 2016, 2017, 2018 BatchDocument83 pagesBCA Old Scheme 2016, 2017, 2018 Batchchetan mitraNo ratings yet
- SSS MDocument2 pagesSSS Mapi-3820998No ratings yet
- S.Y.B.Sc. (Computer Science) ElectronicsDocument14 pagesS.Y.B.Sc. (Computer Science) ElectronicsMayuri ChebleNo ratings yet
- Sub: Advanced Computer Network & Security (PGCSE202) Session: M.Tech 2 Sem 2020 Continuous Assessment - 1Document1 pageSub: Advanced Computer Network & Security (PGCSE202) Session: M.Tech 2 Sem 2020 Continuous Assessment - 1Avik DasNo ratings yet
- Revised Syllabus and Scheme of Examination Effective From July 2010-11Document14 pagesRevised Syllabus and Scheme of Examination Effective From July 2010-11Arjun DubeyNo ratings yet
- CSE Proposed Syllabus 2009-10Document27 pagesCSE Proposed Syllabus 2009-10accommodateNo ratings yet
- DT 1.2 DivyanshuDocument11 pagesDT 1.2 DivyanshuGautam MandoliyaNo ratings yet
- BSC (Hons) Computer Science With Network Security: School of Innovative Technologies and EngineeringDocument13 pagesBSC (Hons) Computer Science With Network Security: School of Innovative Technologies and EngineeringHarryNo ratings yet
- PG Syllabus 2016-18Document67 pagesPG Syllabus 2016-18b.nandhu2810No ratings yet
- AWSNDocument1 pageAWSNHari Hara SudhanNo ratings yet
- BLOCKCHAI SyllabusDocument27 pagesBLOCKCHAI SyllabusChennamadhavuni SahithiNo ratings yet
- My CVDocument2 pagesMy CVdangvu16022002No ratings yet
- Part 6 - Bluetooth SecurityDocument33 pagesPart 6 - Bluetooth SecurityTân HoàngNo ratings yet
- Part 9 - Security in Mobile Telecommunication NetworksDocument22 pagesPart 9 - Security in Mobile Telecommunication NetworksTân HoàngNo ratings yet
- Part 8 - WiMAX SecurityDocument34 pagesPart 8 - WiMAX SecurityTân HoàngNo ratings yet
- Part 11 - Security in Next Generation Mobile NetworksDocument18 pagesPart 11 - Security in Next Generation Mobile NetworksTân HoàngNo ratings yet
- Part 7 - Wi-Fi SecurityDocument52 pagesPart 7 - Wi-Fi SecurityTân HoàngNo ratings yet
- Software Engineering (503074) : Excercise 1Document2 pagesSoftware Engineering (503074) : Excercise 1Tân HoàngNo ratings yet
- Cryptanalysis of Mono-Alphabetic Substitution Ciphers Using Genetic Algorithms and Simulated AnnealingDocument5 pagesCryptanalysis of Mono-Alphabetic Substitution Ciphers Using Genetic Algorithms and Simulated AnnealingTân HoàngNo ratings yet
- RHCSA Red Hat Enterprise Linux 9: Training and Exam Preparation Guide (EX200), Third EditionFrom EverandRHCSA Red Hat Enterprise Linux 9: Training and Exam Preparation Guide (EX200), Third EditionNo ratings yet
- iPhone 14 Guide for Seniors: Unlocking Seamless Simplicity for the Golden Generation with Step-by-Step ScreenshotsFrom EverandiPhone 14 Guide for Seniors: Unlocking Seamless Simplicity for the Golden Generation with Step-by-Step ScreenshotsRating: 5 out of 5 stars5/5 (3)
- Kali Linux - An Ethical Hacker's Cookbook - Second Edition: Practical recipes that combine strategies, attacks, and tools for advanced penetration testing, 2nd EditionFrom EverandKali Linux - An Ethical Hacker's Cookbook - Second Edition: Practical recipes that combine strategies, attacks, and tools for advanced penetration testing, 2nd EditionRating: 5 out of 5 stars5/5 (1)
- iPhone Unlocked for the Non-Tech Savvy: Color Images & Illustrated Instructions to Simplify the Smartphone Use for Beginners & Seniors [COLOR EDITION]From EverandiPhone Unlocked for the Non-Tech Savvy: Color Images & Illustrated Instructions to Simplify the Smartphone Use for Beginners & Seniors [COLOR EDITION]Rating: 5 out of 5 stars5/5 (3)
- Excel : The Ultimate Comprehensive Step-By-Step Guide to the Basics of Excel Programming: 1From EverandExcel : The Ultimate Comprehensive Step-By-Step Guide to the Basics of Excel Programming: 1Rating: 4.5 out of 5 stars4.5/5 (3)
- Hacking : The Ultimate Comprehensive Step-By-Step Guide to the Basics of Ethical HackingFrom EverandHacking : The Ultimate Comprehensive Step-By-Step Guide to the Basics of Ethical HackingRating: 5 out of 5 stars5/5 (3)
- Linux For Beginners: The Comprehensive Guide To Learning Linux Operating System And Mastering Linux Command Line Like A ProFrom EverandLinux For Beginners: The Comprehensive Guide To Learning Linux Operating System And Mastering Linux Command Line Like A ProNo ratings yet
- Mastering Linux Security and Hardening - Second Edition: Protect your Linux systems from intruders, malware attacks, and other cyber threats, 2nd EditionFrom EverandMastering Linux Security and Hardening - Second Edition: Protect your Linux systems from intruders, malware attacks, and other cyber threats, 2nd EditionNo ratings yet
- React.js for A Beginners Guide : From Basics to Advanced - A Comprehensive Guide to Effortless Web Development for Beginners, Intermediates, and ExpertsFrom EverandReact.js for A Beginners Guide : From Basics to Advanced - A Comprehensive Guide to Effortless Web Development for Beginners, Intermediates, and ExpertsNo ratings yet
- Mastering Swift 5 - Fifth Edition: Deep dive into the latest edition of the Swift programming language, 5th EditionFrom EverandMastering Swift 5 - Fifth Edition: Deep dive into the latest edition of the Swift programming language, 5th EditionNo ratings yet
- Linux: A Comprehensive Guide to Linux Operating System and Command LineFrom EverandLinux: A Comprehensive Guide to Linux Operating System and Command LineNo ratings yet
- Azure DevOps Engineer: Exam AZ-400: Azure DevOps Engineer: Exam AZ-400 Designing and Implementing Microsoft DevOps SolutionsFrom EverandAzure DevOps Engineer: Exam AZ-400: Azure DevOps Engineer: Exam AZ-400 Designing and Implementing Microsoft DevOps SolutionsNo ratings yet
- RHCSA Exam Pass: Red Hat Certified System Administrator Study GuideFrom EverandRHCSA Exam Pass: Red Hat Certified System Administrator Study GuideNo ratings yet








































































![iPhone Unlocked for the Non-Tech Savvy: Color Images & Illustrated Instructions to Simplify the Smartphone Use for Beginners & Seniors [COLOR EDITION]](https://imgv2-2-f.scribdassets.com/img/audiobook_square_badge/728318688/198x198/f3385cbfef/1715193157?v=1)