Professional Documents
Culture Documents
CISSP ISSAP Exam Outline v0120
Uploaded by
FedericoOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
CISSP ISSAP Exam Outline v0120
Uploaded by
FedericoCopyright:
Available Formats
Certification Exam Outline
Effective Date: October 14, 2020
About CISSP-ISSAP
The Information Systems Security Architecture Professional (ISSAP) is a CISSP who specializes in designing
security solutions and providing management with risk-based guidance to meet organizational goals. ISSAPs
facilitate the alignment of security solutions within the organizational context (e.g., vision, mission, strategy,
policies, requirements, change, and external factors).
The broad spectrum of topics included in the ISSAP Common Body of Knowledge (CBK®) ensure its relevancy
across all disciplines in the field of information security. Successful candidates are competent in the following
six domains:
• Architect for Governance, Compliance, and Risk Management
• Security Architecture Modeling
• Infrastructure Security
• Identity and Access Management Architecture
• Architect for Application Security
• Security Operations Architecture
Experience Requirements
Candidates must be a CISSP in good standing and have two years cumulative paid work experience in one
or more of the six domains of the CISSP-ISSAP CBK. You can learn more about CISSP-ISSAP experience
requirements and how to account for part-time work and internships at www.isc2.org/Certifications/CISSP-
ISSAP/experience-requirements.
Accreditation
CISSP-ISSAP is in compliance with the stringent requirements of ANSI/ISO/IEC Standard 17024.
Job Task Analysis (JTA)
(ISC)² has an obligation to its membership to maintain the relevancy of the CISSP-ISSAP. Conducted at regular
intervals, the Job Task Analysis (JTA) is a methodical and critical process of determining the tasks that are
performed by ISSAP credential holders. The results of the JTA are used to update the examination. This
process ensures that candidates are tested on the topic areas relevant to the roles and responsibilities of
today’s practicing information security professionals.
ISSAP Certification Exam Outline 2
CISSP-ISSAP Examination Information
Length of exam 3 hours
Number of items 125
Item format Multiple choice
Passing grade 700 out of 1000 points
Exam availability English
Testing center Pearson VUE Testing Center
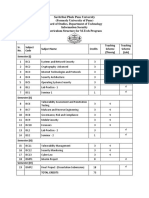
CISSP-ISSAP Examination Weights
Domains Weight
1. Architect for Governance, Compliance and Risk Management 17%
2. Security Architecture Modeling 15%
3. Infrastructure Security Architecture 21%
4. Identity and Access Management (IAM) Architecture 16%
5. Architect for Application Security 13%
6. Security Operations Architecture 18%
Total: 100%
ISSAP Certification Exam Outline 3
Domain 1:
Architect for Governance, Compliance
and Risk Management
1.1 Determine legal, regulatory, organizational and industry requirements
» Determine applicable information security standards and guidelines
» Identify third-party and contractual obligations (e.g., supply chain, outsourcing, partners)
» Determine applicable sensitive/personal data standards, guidelines and privacy regulations
» Design for auditability (e.g., determine regulatory, legislative, forensic requirements, segregation,
high assurance systems)
» Coordinate with external entities (e.g., law enforcement, public relations, independent assessor)
1.2 Manage Risk
» Identify and classify risks
» Assess risk
» Recommend risk treatment (e.g., mitigate, transfer, accept, avoid)
» Risk monitoring and reporting
ISSAP Certification Exam Outline 4
Domain 2:
Security Architecture Modeling
2.1 Identify security architecture approach
» Types and scope (e.g., enterprise, network, Service-Oriented Architecture (SOA), cloud, Internet of Things
(IoT), Industrial Control Systems (ICS)/Supervisory Control and Data Acquisition (SCADA))
» Frameworks (e.g., Sherwood Applied Business Security Architecture (SABSA), Service-Oriented Modeling
Framework (SOMF))
» Reference architectures and blueprints
» Security configuration (e.g., baselines, benchmarks, profiles)
» Network configuration (e.g., physical, logical, high availability, segmentation, zones)
2.2 Verify and validate design (e.g., Functional Acceptance Testing (FAT), regression)
» Validate results of threat modeling (e.g., threat vectors, impact, probability)
» Identify gaps and alternative solutions
» Independent Verification and Validation (IV&V) (e.g., tabletop exercises, modeling and simulation, manual
review of functions)
ISSAP Certification Exam Outline 5
Domain 3:
Infrastructure Security Architecture
3.1 Develop infrastructure security requirements
» On-premise, cloud-based, hybrid
» Internet of Things (IoT), zero trust
3.2 Design defense-in-depth architecture
» Management networks » Container security
» Industrial Control Systems (ICS) security » Cloud workload security
» Network security » Firmware security
» Operating systems (OS) security » User security awareness considerations
» Database security
3.3 Secure shared services (e.g., wireless, e-mail, Voice over Internet Protocol (VoIP), Unified
Communications (UC), Domain Name System (DNS), Network Time Protocol (NTP))
3.4 Integrate technical security controls
» Design boundary protection (e.g., firewalls, Virtual Private Network (VPN), airgaps, software defined
perimeters, wireless, cloud-native)
» Secure device management (e.g., Bring Your Own Device (BYOD), mobile, server, endpoint, cloud instance,
storage)
3.5 Design and integrate infrastructure monitoring
» Network visibility (e.g., sensor placement, time reconciliation, span of control, record compatibility)
» Active/Passive collection solutions (e.g., span port, port mirroring, tap, inline, flow logs)
» Security analytics (e.g., Security Information and Event Management (SIEM), log collection, machine
learning, User Behavior Analytics (UBA))
ISSAP Certification Exam Outline 6
Domain 3:
Infrastructure Security Architecture
3.6 Design infrastructure cryptographic solutions
» Determine cryptographic design considerations and constraints
» Determine cryptographic implementation (e.g., in-transit, in-use, at-rest)
» Plan key management lifecycle (e.g., generation, storage, distribution)
3.7 Design secure network and communication infrastructure (e.g., Virtual Private Network
(VPN), Internet Protocol Security (IPsec), Transport Layer Security (TLS))
3.8 Evaluate physical and environmental security requirements
» Map physical security requirements to organizational needs (e.g., perimeter protection and internal
zoning, fire suppression)
» Validate physical security controls
ISSAP Certification Exam Outline 7
Domain 4:
Identity and Access Management (IAM)
Architecture
4.1 Design identity management and lifecycle
» Establish and verify identity » Define authentication methods (e.g., Multi-Factor
Authentication (MFA), risk-based, location-based,
» Assign identifiers (e.g., to users, services,
knowledge-based, object-based, characteristics-
processes, devices)
based)
» Identity provisioning and de-provisioning
» Authentication protocols and technologies (e.g.,
» Define trust relationships (e.g., federated, stand- Security Assertion Markup Language (SAML),
alone) Remote Authentication Dial-In User Service
(RADIUS), Kerberos)
4.2 Design access control management and lifecycle
» Access control concepts and principles (e.g., » Roles, rights, and responsibilities related to
discretionary/mandatory, segregation/Separation system, application, and data access control
of Duties (SoD), least privilege) (e.g., groups, Digital Rights Management (DRM),
trust relationships)
» Access control configurations (e.g., physical,
logical, administrative) » Management of privileged accounts
» Authorization process and workflow (e.g., » Authorization (e.g., Single Sign-On (SSO), rule-
governance, issuance, periodic review, based, role-based, attribute- based)
revocation)
4.3 Design identity and access solutions
» Access control protocols and technologies (e.g., » Decentralized Identity and Access Management
eXtensible Access Control Markup Language (IAM) architecture (e.g., cloud-based, on-premise,
(XACML), Lightweight Directory Access Protocol hybrid)
(LDAP))
» Privileged Access Management (PAM)
» Credential management technologies (e.g., implementation (for users with elevated
password management, certificates, smart cards) privileges)
» Centralized Identity and Access Management » Accounting (e.g., logging, tracking, auditing)
(IAM) architecture (e.g., cloud-based, on-premise,
hybrid)
ISSAP Certification Exam Outline 8
Domain 5:
Architect for Application Security
5.1 Integrate Software Development Life Cycle (SDLC) with application security architecture
(e.g., Requirements Traceability Matrix (RTM), security architecture documentation, secure
coding)
» Assess code review methodology (e.g., dynamic, manual, static)
» Assess the need for application protection (e.g., Web Application Firewall (WAF), anti-malware, secure
Application Programming Interface (API), secure Security Assertion Markup Language (SAML))
» Determine encryption requirements (e.g., at-rest, in-transit, in-use)
» Assess the need for secure communications between applications and databases or other endpoints
» Leverage secure code repository
5.2 Determine application security capability requirements and strategy (e.g., open source,
Cloud Service Providers (CSP), Software as a Service (SaaS)/Infrastructure as a Service
(IaaS)/ Platform as a Service (PaaS) environments)
» Review security of applications (e.g., custom, Commercial Off-the-Shelf (COTS), in-house, cloud)
» Determine application cryptographic solutions (e.g., cryptographic Application Programming Interface (API),
Pseudo Random Number Generator (PRNG), key management)
» Evaluate applicability of security controls for system components (e.g., mobile and web client applications;
proxy, application, and database services)
5.3 Identify common proactive controls for applications (e.g., Open Web Application Security
Project (OWASP))
ISSAP Certification Exam Outline 9
Domain 6:
Security Operations Architecture
6.1 Gather security operations requirements (e.g., legal, compliance, organizational, and
business requirements)
6.2 Design information security monitoring (e.g., Security Information and Event Management
(SIEM), insider threat, threat intelligence, user behavior analytics, Incident Response (IR)
procedures)
» Detection and analysis
» Proactive and automated security monitoring and remediation (e.g., vulnerability management, compliance
audit, penetration testing)
6.3 Design Business Continuity (BC) and resiliency solutions
» Incorporate Business Impact Analysis (BIA) » Establish Recovery Time Objectives (RTO) and
Recovery Point Objectives (RPO)
» Determine recovery and survivability strategy
» Design secure contingency communication
» Identify continuity and availability solutions (e.g.,
for operations (e.g., backup communication
cold, warm, hot, cloud backup)
channels, Out-of-Band (OOB))
» Define processing agreement requirements (e.g.,
provider, reciprocal, mutual, cloud, virtualization)
6.4 Validate Business Continuity Plan (BCP)/Disaster Recovery Plan (DRP) architecture
6.5 Design Incident Response (IR) management
» Preparation (e.g., communication plan, Incident » Eradication
Response Plan (IRP), training) » Recovery
» Identification » Review lessons learned
» Containment
ISSAP Certification Exam Outline 10
Additional Examination Information
Supplementary References
Candidates are encouraged to supplement their education and experience by reviewing
relevant resources that pertain to the CBK and identifying areas of study that may need
additional attention.
View the full list of supplementary references at www.isc2.org/certifications/References.
Examination Policies and Procedures
(ISC)² recommends that ISSAP candidates review exam policies and procedures prior to
registering for the examination. Read the comprehensive breakdown of this important
information at www.isc2.org/Register-for-Exam.
Legal Info
For any questions related to (ISC)²’s policies, please contact the (ISC)2 Legal Department at
legal@isc2.org.
Any Questions?
(ISC)² Americas
Tel: +1-866-331-ISC2(4722)
Email: membersupport@isc2.org
(ISC)² Asia Pacific
Tel: +852-2850-6951
Email: membersupportapac@isc2.org
(ISC)² EMEA
Tel: +44-203-960-7800
Email: membersupportemea@isc2.org
ISSAP Certification
v0720 Exam Outline 11
You might also like
- Cybersecurity by ISC2-UpdatedDocument13 pagesCybersecurity by ISC2-UpdatedYe Zeiya Shein60% (5)
- Certified in Cybersecurity Exam Outline Aug22Document8 pagesCertified in Cybersecurity Exam Outline Aug22R Nil100% (1)
- Cissp-Issap: The Ultimate Guide To TheDocument13 pagesCissp-Issap: The Ultimate Guide To TheFedericoNo ratings yet
- CSSLP Exam Outline Sept2020Document14 pagesCSSLP Exam Outline Sept2020ziaur060382No ratings yet
- CEoutlineDocument14 pagesCEoutlineqwerty3111No ratings yet
- CCSPDocument14 pagesCCSPngtonhNo ratings yet
- CCSP Certification Exam OutlineDocument14 pagesCCSP Certification Exam OutlineironmanNo ratings yet
- CSSLP Exam Outline-V1013Document13 pagesCSSLP Exam Outline-V1013Abdul AhadNo ratings yet
- CSSLP Exam OutlineDocument13 pagesCSSLP Exam OutlineLuis Felipe GaleanoNo ratings yet
- CSSLP Exam Outline-V1013Document13 pagesCSSLP Exam Outline-V1013Ram RaghavanNo ratings yet
- Certification: Exam OutlineDocument15 pagesCertification: Exam Outlinejustforfun2009No ratings yet
- CCSP Exam OutlineDocument15 pagesCCSP Exam OutlineMaudyNo ratings yet
- CISSP Exam Outline PDFDocument15 pagesCISSP Exam Outline PDFsriNo ratings yet
- CISSP Domain 1 Guide: Security and Risk Management FundamentalsDocument16 pagesCISSP Domain 1 Guide: Security and Risk Management FundamentalsRomeo SincereNo ratings yet
- SSCP Certification Exam OutlineDocument13 pagesSSCP Certification Exam Outlinehalakahiki82No ratings yet
- SSCP Exam OutlineDocument11 pagesSSCP Exam OutlineironmanNo ratings yet
- CISSP Exam Outline-V1115Document16 pagesCISSP Exam Outline-V1115AsadMalikNo ratings yet
- Cissp CursDocument7 pagesCissp Cursf7vbzqcfztNo ratings yet
- Catalyst - Cybersecurity Offerings - 050522 - ENG - v3Document18 pagesCatalyst - Cybersecurity Offerings - 050522 - ENG - v3Justo EbangNo ratings yet
- CAP Exam OutlineDocument12 pagesCAP Exam OutlineHyder BasetNo ratings yet
- CISSP Exam Outline English April 2021 PDFDocument16 pagesCISSP Exam Outline English April 2021 PDFKevin MonkamNo ratings yet
- CISM Chapter3-Info Sec Program DevelopmentDocument62 pagesCISM Chapter3-Info Sec Program DevelopmentLakshmiNo ratings yet
- CISSP ISSAP DomainRefreshDocument8 pagesCISSP ISSAP DomainRefreshIvan KasparekNo ratings yet
- Kareem PKIDocument6 pagesKareem PKIRohit LalwaniNo ratings yet
- CompTIA CASP+ CAS-004 Exam Objectives (6.0)Document20 pagesCompTIA CASP+ CAS-004 Exam Objectives (6.0)black mannaNo ratings yet
- GSC20 Session8 Security Laura ISOIECDocument70 pagesGSC20 Session8 Security Laura ISOIECRoberto MonteroNo ratings yet
- Kaspersky ICS Security Assessment: Why You Should Do ThisDocument2 pagesKaspersky ICS Security Assessment: Why You Should Do Thishangtuah79No ratings yet
- Secure Web Application DevelopmentDocument3 pagesSecure Web Application DevelopmentMangesh AbnaveNo ratings yet
- 350 701 Scor PDFDocument4 pages350 701 Scor PDFDinesh ShahiNo ratings yet
- Building Security Operation CenterDocument37 pagesBuilding Security Operation CenterMuhdir Hisyam Abdul Karim100% (1)
- CMN Security ManagerDocument6 pagesCMN Security ManagerazzuNo ratings yet
- SOC Building1Document36 pagesSOC Building1Van NguyenNo ratings yet
- Certified in Cybersecurity Exam Outline Aug22 PDFDocument8 pagesCertified in Cybersecurity Exam Outline Aug22 PDFraspberries1No ratings yet
- SECURITY CLEARANCE - Top Secret - SCI Eligible CertificationsDocument7 pagesSECURITY CLEARANCE - Top Secret - SCI Eligible CertificationsAshwani kumarNo ratings yet
- CCST+Cybersecurity+Objecitve+Domain Cisco Final wCiscoLogoDocument3 pagesCCST+Cybersecurity+Objecitve+Domain Cisco Final wCiscoLogoQazi ZayadNo ratings yet
- CisspDocument16 pagesCisspRyan GlasgowNo ratings yet
- Imt Security ArchitectDocument8 pagesImt Security ArchitectazzuNo ratings yet
- Week 7 - FinalDocument12 pagesWeek 7 - Finalapi-414181025No ratings yet
- Hemanth CybersecurityDocument5 pagesHemanth Cybersecuritymujahidpro6No ratings yet
- ISS404: Security Architecture, Design and Models SyllabusDocument2 pagesISS404: Security Architecture, Design and Models SyllabusLeNantais SonderangeboteNo ratings yet
- Sri RajaDocument6 pagesSri RajaAshwani kumarNo ratings yet
- At A Glance: Prisma CloudDocument2 pagesAt A Glance: Prisma CloudAishwarya PradhanNo ratings yet
- Astr Cyber Security ServicesDocument7 pagesAstr Cyber Security ServicesAstr CyberNo ratings yet
- Course Overview: This Course Provides In-Depth Coverage of The Eight Domains Required To Pass The CISSP ExamDocument30 pagesCourse Overview: This Course Provides In-Depth Coverage of The Eight Domains Required To Pass The CISSP ExamAbdul GhaffarNo ratings yet
- COURSE 1 Basics of CybersecurityDocument7 pagesCOURSE 1 Basics of CybersecuritySohamNo ratings yet
- CISSP Fast Track Master: CISSP Essentials for Exam Success - Exam Cram Notes: 1st Edition - 2024From EverandCISSP Fast Track Master: CISSP Essentials for Exam Success - Exam Cram Notes: 1st Edition - 2024No ratings yet
- CISSPDocument2 pagesCISSPzollian.fxNo ratings yet
- CompTIA CySA cs0 003+objectivesDocument12 pagesCompTIA CySA cs0 003+objectivesabhilashNo ratings yet
- ProfileDocument18 pagesProfileVinay Kumar ThakurNo ratings yet
- IT Security Responsibilities Shift When Moving to the CloudDocument4 pagesIT Security Responsibilities Shift When Moving to the CloudLorenzoNo ratings yet
- Kaspersky Security Assessment ServicesDocument8 pagesKaspersky Security Assessment ServicesmeimNo ratings yet
- Pune University IS Tech. SyllabusDocument9 pagesPune University IS Tech. SyllabusPav TechnicalsNo ratings yet
- Lead - Security Architecture and Engineering JDDocument2 pagesLead - Security Architecture and Engineering JDHaemletNo ratings yet
- Comptia Security+ Sy0-601: Course ContentDocument8 pagesComptia Security+ Sy0-601: Course ContentShiva Chandrasekharan50% (2)
- Chief IT Security ManagerDocument2 pagesChief IT Security Managerprabu rNo ratings yet
- Cybersecurity: It Specialist Exam ObjectivesDocument3 pagesCybersecurity: It Specialist Exam ObjectivesMercy EbiojoNo ratings yet
- Physical Security Consulting & Project ManagementDocument21 pagesPhysical Security Consulting & Project ManagementMalcolm CooperNo ratings yet
- CAP Exam OutlineDocument10 pagesCAP Exam OutlineironmanNo ratings yet
- Cloud Security - A Primer by Yogesh Gupta, CISSP® CCSK CCSP - The Cloud, Services, Standards - PeerlystDocument8 pagesCloud Security - A Primer by Yogesh Gupta, CISSP® CCSK CCSP - The Cloud, Services, Standards - PeerlystrossloveladyNo ratings yet
- Expert Security Architect with 20+ Years ExperienceDocument6 pagesExpert Security Architect with 20+ Years ExperienceImteyaz AhmadNo ratings yet
- CISSP Certification Exam Study Guide: (Cerified Information Systems Security Professional)From EverandCISSP Certification Exam Study Guide: (Cerified Information Systems Security Professional)No ratings yet
- RomanianDocument19 pagesRomanianFedericoNo ratings yet
- NoticeDocument4 pagesNoticeFedericoNo ratings yet
- Index 2Document1 pageIndex 2FedericoNo ratings yet
- 2022.02.09 Vspace Pro Enterprise Edition 12.7.0 Release NotesDocument24 pages2022.02.09 Vspace Pro Enterprise Edition 12.7.0 Release NotesFedericoNo ratings yet
- RX UpdateDocument1 pageRX UpdateFedericoNo ratings yet
- DanskDocument18 pagesDanskFedericoNo ratings yet
- Chinese BIG5Document18 pagesChinese BIG5FedericoNo ratings yet
- UzbekDocument19 pagesUzbekFedericoNo ratings yet
- Eesti keeles WinHTTrack kasutajate juhend</40Document18 pagesEesti keeles WinHTTrack kasutajate juhend</40FedericoNo ratings yet
- LCQ 1 User ManualDocument9 pagesLCQ 1 User ManualFedericoNo ratings yet
- Release Notes: Production VersionDocument15 pagesRelease Notes: Production VersionFedericoNo ratings yet
- Siemens Enterprise Communications: Product Name: Openstage SIP Product Version: V2 Software Release Version: V2R2.48.0Document25 pagesSiemens Enterprise Communications: Product Name: Openstage SIP Product Version: V2 Software Release Version: V2R2.48.0FedericoNo ratings yet
- How To Reset A FortiGate Firewall To Factory Default Settings - Tech EncyclopediaDocument10 pagesHow To Reset A FortiGate Firewall To Factory Default Settings - Tech EncyclopediaFedericoNo ratings yet
- Package Contents: Quickstart GuideDocument2 pagesPackage Contents: Quickstart GuideFedericoNo ratings yet
- Replace Map Light Bulb Socket ColorDocument2 pagesReplace Map Light Bulb Socket ColorFedericoNo ratings yet
- Gps Vehicle Tracker User Manual: PrefaceDocument13 pagesGps Vehicle Tracker User Manual: PrefaceFedericoNo ratings yet
- Lista Comandi Tk1m06Document3 pagesLista Comandi Tk1m06Shahram SherkatNo ratings yet
- Ftkimager UgDocument62 pagesFtkimager UgVăn HảiNo ratings yet
- Lista Comandi Tk1m06Document3 pagesLista Comandi Tk1m06Shahram SherkatNo ratings yet
- Quickhash Gui V3.3.0: The Free, Graphical, Cross-Platform, Data Hashing ToolDocument39 pagesQuickhash Gui V3.3.0: The Free, Graphical, Cross-Platform, Data Hashing ToolAlfredo DíazNo ratings yet
- WP9038ADAM User's ManualDocument7 pagesWP9038ADAM User's ManualWifi SetNo ratings yet
- A Hydraulic Wood Pallet MachineDocument15 pagesA Hydraulic Wood Pallet MachineAgonafirNo ratings yet
- Color Palette Blue and YellowDocument4 pagesColor Palette Blue and YellowdresscodebytereNo ratings yet
- Mitsubishi Dpmme96nsrsenDocument32 pagesMitsubishi Dpmme96nsrsenDasuki FahmiNo ratings yet
- Panasonic+Ag-hvx200p An e Mc,+Ag-hvx202en+Parts,+Service+ManualDocument382 pagesPanasonic+Ag-hvx200p An e Mc,+Ag-hvx202en+Parts,+Service+ManualDJDogbone100% (1)
- Red Alert ManualDocument17 pagesRed Alert ManualAlek KingNo ratings yet
- Double Rail Parameter-1Document15 pagesDouble Rail Parameter-1cassanova jackNo ratings yet
- Door Sensor ProjectDocument6 pagesDoor Sensor ProjectMehmood ul Hassan100% (1)
- Hackathon-PSP Server Integration and UsageDocument26 pagesHackathon-PSP Server Integration and Usageoptimium888No ratings yet
- Exploring Microsoft Office Word 2007 Ch1Document28 pagesExploring Microsoft Office Word 2007 Ch1crazybobblaskeyNo ratings yet
- Resume of Brianjkim1980Document1 pageResume of Brianjkim1980api-28487603No ratings yet
- PT100 Temperature Sensor User ManualDocument24 pagesPT100 Temperature Sensor User ManualFerdy 13No ratings yet
- Linux and Windows IntegrationDocument13 pagesLinux and Windows IntegrationTaban SimonNo ratings yet
- Polygraphy Midterm LectureDocument99 pagesPolygraphy Midterm Lecturejetlee estacionNo ratings yet
- The MIB Includes The System Information Transmitted On BCH. Signalling Radio Bearer: N/A Rlc-Sap: TM Logical Channel: BCCH Direction: Network To UEDocument5 pagesThe MIB Includes The System Information Transmitted On BCH. Signalling Radio Bearer: N/A Rlc-Sap: TM Logical Channel: BCCH Direction: Network To UESreenath VenkataNo ratings yet
- PracticalsDocument70 pagesPracticalsprogrammerNo ratings yet
- Chapter 8 PDF AdaptedDocument42 pagesChapter 8 PDF Adaptedapi-540102596No ratings yet
- Whats New NanoCADDocument19 pagesWhats New NanoCADHaytham ZaghloulNo ratings yet
- PowerPoint VBA TutorialDocument17 pagesPowerPoint VBA TutorialKalai selvanNo ratings yet
- Humalyzer Primus: Semi-Automatic Microprocessor Controlled PhotometerDocument2 pagesHumalyzer Primus: Semi-Automatic Microprocessor Controlled Photometerali zeidNo ratings yet
- Unit III Maths 3Document53 pagesUnit III Maths 3gkk001No ratings yet
- Polynomial Roots - MATLAB RootsDocument3 pagesPolynomial Roots - MATLAB RootsAilton SorlagNo ratings yet
- How To Query Asham Tele Points (Telebirr)Document13 pagesHow To Query Asham Tele Points (Telebirr)Fayisa ETNo ratings yet
- Collaborative and Content-Based Recommendation SystemsDocument9 pagesCollaborative and Content-Based Recommendation SystemsUMA MNo ratings yet
- Analyzing & Testing. Dilatometry. Method, Instruments, Applications From - 180 C To 2800 C. Leading Thermal AnalysisDocument36 pagesAnalyzing & Testing. Dilatometry. Method, Instruments, Applications From - 180 C To 2800 C. Leading Thermal AnalysisMary SmileNo ratings yet
- Wireless Charging Laptop Power BankDocument3 pagesWireless Charging Laptop Power BankraffyNo ratings yet
- TourismDocument39 pagesTourismDinesh Vashisth D C50% (6)
- Hundreds Gather in Clarke Quay For Spontaneous Countdown, Champagne Sprayed Into Crowd - Mothership - SG - News From Singapore, AsDocument1 pageHundreds Gather in Clarke Quay For Spontaneous Countdown, Champagne Sprayed Into Crowd - Mothership - SG - News From Singapore, AsZayar LwinNo ratings yet
- PotencialFlowF - White Fluid Mechanics 2009Document29 pagesPotencialFlowF - White Fluid Mechanics 2009Eldin Celo Celebic100% (1)
- Advantages and Disadvantages of Using InstagramDocument2 pagesAdvantages and Disadvantages of Using InstagramJoefrey Pujadas BalumaNo ratings yet