Professional Documents
Culture Documents
Checklist of ISO 27001 Mandatory Documentation en
Checklist of ISO 27001 Mandatory Documentation en
Uploaded by
Fitriah MartsyantiOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Checklist of ISO 27001 Mandatory Documentation en
Checklist of ISO 27001 Mandatory Documentation en
Uploaded by
Fitriah MartsyantiCopyright:
Available Formats
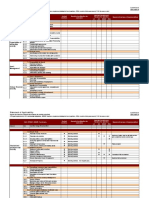
Checklist of Mandatory
Documentation Required by
ISO/IEC 27001
Copyright ©2021 Advisera Expert Solutions Ltd. All rights reserved.
Copyright © 2021 Advisera Expert Solutions Ltd. All rights reserved. 1
Table of Contents
1. Which documents and records are required? ...........................................................................................3
2. Commonly used non-mandatory documents............................................................................................5
3. How to structure most common documents and records ........................................................................6
4. Check out ISO 27001 compliance software .............................................................................................11
Copyright © 2021 Advisera Expert Solutions Ltd. All rights reserved. 2
1. Which documents and records are
required?
The list below shows the minimum set of documents and records required by the ISO/IEC 27001 2013 revision,
which was reviewed and confirmed by ISO in 2019 and is currently valid standard:
Documents* ISO 27001 clause number
Scope of the ISMS 4.3
Information Security Policy and Objectives 5.2, 6.2
Risk Assessment and Risk Treatment Methodology 6.1.2, 6.1.3
Statement of Applicability 6.1.3 d)
Risk Treatment Plan 6.1.3 e), 6.2, 8.3
Risk Assessment and Risk Treatment Report 8.2, 8.3
Definition of Security Roles and Responsibilities A.7.1.2, A.13.2.4
Inventory of Assets A.8.1.1
Acceptable Use of Assets A.8.1.3
Access Control Policy A.9.1.1
Operating Procedures for IT Management A.12.1.1
Secure System Engineering Principles A.14.2.5
Supplier Security Policy A.15.1.1
Incident Management Procedure A.16.1.5
Business Continuity Procedures A.17.1.2
Legal, Regulatory, and Contractual Requirements A.18.1.1
Copyright © 2021 Advisera Expert Solutions Ltd. All rights reserved. 3
Records* ISO 27001 clause number
Records of training, skills, experience and qualifications 7.2
Monitoring and measurement results 6.2, 9.1
Internal audit program 9.2
Results of internal audits 9.2
Results of the management review 9.3
Results of corrective actions 10.1
Logs of user activities, exceptions, and security events A.12.4.1, A.12.4.3
*Controls from Annex A can be excluded if an organization concludes there are no risks or other
requirements which would demand the implementation of a control.
This is by no means a definitive list of documents and records that can be used during the ISO 27001
implementation – the standard allows any other documents to be added to improve the level of
information security.
Copyright © 2021 Advisera Expert Solutions Ltd. All rights reserved. 4
2. Commonly used non-mandatory
documents
Other documents that are very often used are the following:
Documents ISO 27001 clause number
Procedure for document control 7.5
Controls for managing records 7.5
Procedure for internal audit 9.2
Procedure for corrective action 10.1
Bring your own device (BYOD) policy A.6.2.1, A.6.2.2, A.13.2.1
Mobile device and teleworking policy A.6.2.1, A.6.2.2, A.11.2.6
Information classification policy A.8.2.1, A.8.2.2, A.8.2.3, A.8.3.1, A.8.3.3,
A.9.4.1, A.13.2.3
Password policy A.9.2.1, A.9.2.2, A.9.2.4, A.9.3.1, A.9.4.3
Disposal and destruction policy A.8.3.2, A.11.2.7
Procedures for working in secure areas A.11.1.5
Clear desk and clear screen policy A.11.2.9
Change management policy A.12.1.2, A.14.2.4
Backup policy A.12.3.1
Information transfer policy A.13.2.1, A.13.2.2, A.13.2.3
Business impact analysis A.17.1.1
Exercising and testing plan A.17.1.3
Maintenance and review plan A.17.1.3
Business continuity strategy A.17.1.1, A.17.2.1
Copyright © 2021 Advisera Expert Solutions Ltd. All rights reserved. 5
3. How to structure most common
documents and records
Scope of the ISMS
This document is usually rather short, and written at the beginning of the ISO 27001 implementation.
Normally, it is a stand-alone document, although it can be merged into an Information security policy.
Read more here: Problems with defining the scope in ISO 27001.
Information security policy and objectives
Information security policy is usually a short, top-level document describing the main purpose of the ISMS.
Objectives for the ISMS are usually a stand-alone document, but they can also be merged into the
Information security policy. Unlike the ISO 27001 2005 revision, there is no more need for both ISMS
Policy and Information security policy – only one Information security policy is needed.
Read more here: Information security policy – how detailed should it be?
Risk assessment and risk treatment methodology & report
Risk assessment and treatment methodology is usually a document of 4 to 5 pages, and it should be
written before the risk assessment and risk treatment are performed. The Risk assessment and treatment
report has to be written after the risk assessment and risk treatment are performed, and it summarizes
all the results.
Read more here: ISO 27001 risk assessment & treatment – 6 basic steps.
Statement of Applicability
The Statement of Applicability (or SoA) is written based on the results of the risk treatment – this is a
central document within the ISMS because it describes not only which controls from Annex A are
applicable, but also how they will be implemented, and their current status. You could also consider the
Statement of Applicability as a document that describes the security profile of your company.
Read more here: The importance of Statement of Applicability for ISO 27001.
Copyright © 2021 Advisera Expert Solutions Ltd. All rights reserved. 6
Risk treatment plan
This is basically an action plan on how to implement various controls defined by the SoA – it is developed
based on the Statement of Applicability, and is actively used and updated throughout the whole ISMS
implementation. Sometimes it can be merged into the project plan.
Read more here: Risk Treatment Plan and risk treatment process – What’s the difference?
For more information, look at this short handbook: ISO 27001 Risk Management in Plain English.
Security roles and responsibilities
The best method is to describe these throughout all policies and procedures, as precisely as possible.
Avoid expressions like "should be done," and instead use something like "CISO will perform xyz every
Monday at zxy hours." Some companies prefer to describe security roles and responsibilities in their job
descriptions; however, this may lead to lot of paperwork.
Security roles and responsibilities for third parties are defined in contracts.
Read more here: What is the job of Chief Information Security Officer (CISO) in ISO 27001?
Inventory of assets
If you didn't have such an inventory prior to the ISO 27001 project, the best way to create such a
document is directly from the result of the risk assessment – during the risk assessment all the assets and
their owners must be identified anyway, so you just copy the results from there.
Read more here: How to handle Asset register (Asset inventory) according to ISO 27001.
Acceptable use of assets
This is usually written in the form of a policy, and such a document can cover a very wide range of topics
because the standard doesn't define this control very well. Probably the best way to approach it is the
following: (1) leave it for the end of your ISMS implementation, and (2) all the areas & controls that you
haven't covered with other documents and that concern all employees, cover them with this policy.
Copyright © 2021 Advisera Expert Solutions Ltd. All rights reserved. 7
Access control policy
In this document, you can cover only the business side of approving access to certain information and
systems, or also the technical side of access control; further, you can choose to define rules for only logical
access, or also for the physical access. You should write this document only after you finish your risk
assessment and risk treatment process.
Operating procedures for IT management
You can write this as a single document, or as a series of policies and procedures – if you are a smaller
company, you will tend to have a smaller number of documents. Normally, you can cover all the areas
from sections A.12 and A.13 – change management, third-party services, backup, network security,
malicious code, disposal and destruction, information transfer, system monitoring, etc. You should write
this document only after you finish your risk assessment and risk treatment process.
Read more about IT management here: ITIL & ISO 20000 Blog.
Secure system engineering principles
This is a new control in ISO 27001, and requires that secure engineering principles be documented in the
form of a procedure or standard, and should define how to incorporate security techniques in all
architecture layers – business, data, applications and technology. These can include input data validation,
debugging, techniques for authentication, secure session controls, etc.
Supplier security policy
This is also a new control in ISO 27001, and such policy can cover a wide range of controls – how the
screening of potential contractors is done, how the risk assessment of a supplier is made, which security
clauses to insert into the contract, how to supervise the fulfilment of contractual security clauses, how to
change the contract, how to close the access once the contract is terminated, etc.
Read more here: 6-step process for handling supplier security according to ISO 27001.
Incident management procedure
This is an important procedure which defines how the security weaknesses, events and incidents are
reported, classified and handled. This procedure also defines how to learn from information security
incidents, so that they can be prevented the next time. Such a procedure can also invoke the Business
continuity plan if an incident has caused a lengthy disruption.
Copyright © 2021 Advisera Expert Solutions Ltd. All rights reserved. 8
Business continuity procedures
These are usually business continuity plans, incident response plans, recovery plans for business side of
the organization, and disaster recovery plans (recovery plans for IT infrastructure). These are the best
described in the ISO 22301 standard, the leading international standard for business continuity.
To learn more, click here: Business continuity plan: How to structure it according to ISO 22301.
Legal, regulatory, and contractual requirements
This list should be made as early in the project as possible, because many documents will have to be
developed according to these inputs. This list should include not only responsibilities for complying with
certain requirements, but also the deadlines.
Records of training, skills, experience and qualifications
These records are normally maintained by the human resources department – if you don't have such a
department, anyone who usually maintains the employee's records should be doing this job. Basically, a
folder with all the documents inserted in it will do.
Read more here: How to perform training & awareness for ISO 27001 and ISO 22301.
Monitoring and measurement results
The easiest way to describe the way controls are to be measured is through policies and procedures which
define each control – normally, this description can be written at the end of each document, and such
description defines the kinds of KPIs (key performance indicators) that need to be measured for each
control or group of controls.
Once this measurement method is in place, you have to perform the measurement accordingly. It is
important to report these results regularly to the persons who are in charge of evaluating them.
Read more here: ISO 27001 control objectives – Why are they important?
Internal audit program
The Internal audit program is nothing else but a 1-year plan for performing the audits – for a smaller
company this could be only one audit, whereas for a larger organization this could be a series of, e.g., 20
internal audits. This program should define who would perform the audits, methods, audit criteria, etc.
Read more here: How to make an Internal Audit checklist for ISO 27001 / ISO 22301.
Copyright © 2021 Advisera Expert Solutions Ltd. All rights reserved. 9
Results of internal audits
An internal auditor must produce the Audit report, which includes the audit findings (observations and
corrective actions). Such report must be produced within a couple of days after an internal audit is
performed. In some cases, the internal auditor will have to check whether all the corrective actions have
been performed as expected.
Results of the management review
These records are normally in the form of meeting minutes – they have to include all the materials that
were involved at the management meeting, as well as all the decisions that were made. The minutes can
be in paper or digital form.
Read more here: Why is management review important for ISO 27001 and ISO 22301?
Results of corrective actions
These are traditionally included in Corrective action forms (CARs). However, it is much better to include
such records in some application that is already used in an organization for Help Desk – because corrective
actions are nothing but to-do lists with clearly defined responsibilities, tasks and deadlines.
Read more here: Practical use of corrective actions for ISO 27001 and ISO 22301.
Logs of user activities, exceptions, and security events
These are normally kept in two forms: (1) in digital form, automatically or semi-automatically produced
as logs of various IT and other systems, and (2) in paper form, where every record is written manually.
Procedure for document control
This is normally a stand-alone procedure, 2 or 3 pages long. If you already implemented some other
standard like ISO 9001, ISO 14001, ISO 22301 or similar, you can use the same procedure for all these
management systems. Sometimes it is best to write this procedure as the first document in a project.
Read more here: Document management in ISO 27001 & BS 25999-2.
You can use this free ISO online tool for handling your documentation, i.e., using it as a document
management system (DMS).
Copyright © 2021 Advisera Expert Solutions Ltd. All rights reserved. 10
Controls for managing records
The easiest way is to describe the control of records in each policy or procedure (or other document) that
requires a record to be created. These controls are normally written toward the end of each document,
and are usually in the form of a table that describes where the record is archived, who has access, how it
is protected, for how long it is archived, etc.
Procedure for internal audit
This is normally a stand-alone procedure that can be 2 to 3 pages long, and has to be written before the
internal audit begins. As with the Procedure for document control, one Procedure for internal audit can
be used for any management system.
Read more here: Dilemmas with ISO 27001 & BS 25999-2 internal auditors.
More information about internal audit you can find in this free online training: ISO 27001 Internal Auditor
Course.
Procedures for corrective action
This procedure shouldn't be more than 2 or 3 pages long, and it can be written at the end of the
implementation project, although it is better to write it earlier so that employees can get used to it.
For more information, please take a look at this useful handbook: Managing ISO Documentation: A Plain
English Guide.
4. Check out ISO 27001 compliance
software
To get the templates for all mandatory documents and the most common non-mandatory documents,
along with the wizard that helps you fill out those templates, sign up for a 30-day free trial of Conformio,
the leading ISO 27001 compliance software.
Copyright © 2021 Advisera Expert Solutions Ltd. All rights reserved. 11
Advisera Expert Solutions Ltd Email: support@advisera.com
for electronic business and business consulting U.S. (international): +1 (646) 759 9933
Zavizanska 12, 10000 Zagreb United Kingdom (international): +44 1502 449001
Croatia, European Union Toll-Free (U.S. and Canada): 1-888-553-2256
Toll-Free (United Kingdom): 0800 808 5485
Australia: +61 3 4000 0020
Copyright © 2021 Advisera Expert Solutions Ltd. All rights reserved. 12
You might also like
- Secure & Simple – A Small-Business Guide to Implementing ISO 27001 On Your Own: The Plain English, Step-by-Step Handbook for Information Security PractitionersFrom EverandSecure & Simple – A Small-Business Guide to Implementing ISO 27001 On Your Own: The Plain English, Step-by-Step Handbook for Information Security PractitionersNo ratings yet
- Iso 27001 Compliance ChecklistDocument47 pagesIso 27001 Compliance Checklistashik1234594% (18)
- ISO 27001 Controls – A guide to implementing and auditingFrom EverandISO 27001 Controls – A guide to implementing and auditingRating: 5 out of 5 stars5/5 (1)
- Information security - Edition 2022: Risk management. Management systems. The ISO/IEC 27001:2022 standard. The ISO/IEC 27002:2022 controls.From EverandInformation security - Edition 2022: Risk management. Management systems. The ISO/IEC 27001:2022 standard. The ISO/IEC 27002:2022 controls.No ratings yet
- Ontario Security Guard License Free Practice QuizzesDocument2 pagesOntario Security Guard License Free Practice QuizzesQuiz Ontario75% (12)
- Iso 27001 Implementation RoadmapDocument1 pageIso 27001 Implementation RoadmapVaibhav Nagariya100% (7)
- ISO/IEC 27002 Implementation Guidance and MetricsDocument14 pagesISO/IEC 27002 Implementation Guidance and MetricsNoticeBored100% (17)
- Statement of Applicability For ISO 27001Document34 pagesStatement of Applicability For ISO 27001Samer Al Basha100% (3)
- ISO 27001 BMS-2017 - DocumentDocument17 pagesISO 27001 BMS-2017 - Documentdeepceh100% (2)
- ISO 27001:2013 Statement of ApplicabilityDocument21 pagesISO 27001:2013 Statement of Applicabilityketanms70% (10)
- ISO 27001 Vs ISO 22301 Matrix ENDocument17 pagesISO 27001 Vs ISO 22301 Matrix ENIonut GabrielNo ratings yet
- Statement ISMS ScopeDocument4 pagesStatement ISMS ScopeshkjnuNo ratings yet
- ISO 27001 2022 How To Conduct An ISMS Gap Analysis 1684315308Document23 pagesISO 27001 2022 How To Conduct An ISMS Gap Analysis 1684315308Harshit mathur100% (4)
- Becoming Resilient – The Definitive Guide to ISO 22301 Implementation: The Plain English, Step-by-Step Handbook for Business Continuity PractitionersFrom EverandBecoming Resilient – The Definitive Guide to ISO 22301 Implementation: The Plain English, Step-by-Step Handbook for Business Continuity PractitionersRating: 5 out of 5 stars5/5 (3)
- Information Security Risk Management for ISO27001/ISO27002From EverandInformation Security Risk Management for ISO27001/ISO27002Rating: 4.5 out of 5 stars4.5/5 (3)
- ISO 27001 Gap Analysis Sample Excerpt PDFDocument8 pagesISO 27001 Gap Analysis Sample Excerpt PDFsathish kumarNo ratings yet
- Statement of Applicability For ISMS - IsO 27001Document5 pagesStatement of Applicability For ISMS - IsO 27001pvendaraNo ratings yet
- ISO/IEC 27001:2022: An introduction to information security and the ISMS standardFrom EverandISO/IEC 27001:2022: An introduction to information security and the ISMS standardRating: 5 out of 5 stars5/5 (3)
- Main Changes in ISO 27001-2022Document3 pagesMain Changes in ISO 27001-2022Umesh Rane80% (5)
- Risk Assessment and Risk Treatment MethodologyDocument4 pagesRisk Assessment and Risk Treatment MethodologyAhmad Nawaz100% (1)
- List of Documents ISO 27001 ISO 27017 ISO 27018 Cloud-EnDocument13 pagesList of Documents ISO 27001 ISO 27017 ISO 27018 Cloud-EnseshaNo ratings yet
- Iso 27001 Statement of Applicability Ism Not 008Document7 pagesIso 27001 Statement of Applicability Ism Not 008balaji100% (3)
- Checklist of Mandatory Documentation Required by ISO 27001 2013Document9 pagesChecklist of Mandatory Documentation Required by ISO 27001 2013Jamil Ahmad Saad100% (1)
- Preparations for the ISO Implementation Project – A Plain English Guide: A Step-by-Step Handbook for ISO Practitioners in Small BusinessesFrom EverandPreparations for the ISO Implementation Project – A Plain English Guide: A Step-by-Step Handbook for ISO Practitioners in Small BusinessesRating: 5 out of 5 stars5/5 (1)
- ISO 27001 PresentacionDocument21 pagesISO 27001 Presentacionmadul2000100% (1)
- DOC06 - ISO 27001-2013 ISMS Manual TOPDocument25 pagesDOC06 - ISO 27001-2013 ISMS Manual TOPIRIE100% (1)
- Iso27002 PDFDocument12 pagesIso27002 PDFPablo Brito100% (3)
- ISO27k ISMS Internal Audit ProcedureDocument9 pagesISO27k ISMS Internal Audit ProcedurePavuluri Ravindra100% (1)
- Audit Report ISO 27001 UK Rev 1 - Response-V1Document12 pagesAudit Report ISO 27001 UK Rev 1 - Response-V1Gonzalo MoralesNo ratings yet
- ISO/IEC 27001 Informa2on Security Management System: Presented by Daminda PereraDocument23 pagesISO/IEC 27001 Informa2on Security Management System: Presented by Daminda Pererafeezee7750% (2)
- ISO27001Document8 pagesISO27001Ankit PachnandaNo ratings yet
- Shogun 2001 Fuel ProblemDocument6 pagesShogun 2001 Fuel ProblemJose GilmerNo ratings yet
- Movement For TelanganaDocument5 pagesMovement For TelanganaTanu RdNo ratings yet
- Sample Report - Container Loading SupervisionDocument16 pagesSample Report - Container Loading SupervisionmeyNo ratings yet
- Checklist of Mandatory Documentation Required by ISO 27001 2013Document9 pagesChecklist of Mandatory Documentation Required by ISO 27001 2013toughnedglass100% (1)
- Information Security Management System (Manual) : Manak Waste Management PVT LTDDocument14 pagesInformation Security Management System (Manual) : Manak Waste Management PVT LTDApoorva Arora100% (1)
- Doc01 - ISO 27001-2013 ISMS Manual TOPDocument29 pagesDoc01 - ISO 27001-2013 ISMS Manual TOPIRIE86% (7)
- ISMS Statement of ApplicabilityDocument20 pagesISMS Statement of ApplicabilityROBERTO DA SILVA ALMEIDA100% (2)
- IsmsDocument21 pagesIsmsYamini Gupta100% (2)
- Documents-Manual-Procedures - HTM: D106: Demo of Information Security System Document KitDocument12 pagesDocuments-Manual-Procedures - HTM: D106: Demo of Information Security System Document KitMuhamm ad Faris Al GhifaryNo ratings yet
- ISMS Statement of Applicability For ISMS Course Participant ExerciseDocument12 pagesISMS Statement of Applicability For ISMS Course Participant ExerciseCyber Guru100% (1)
- Anonymized ISO 27001 Assessment ReportDocument50 pagesAnonymized ISO 27001 Assessment Reporta100% (1)
- ISO 27001-2013 ISMS Policy PDFDocument6 pagesISO 27001-2013 ISMS Policy PDFSunil AroraNo ratings yet
- Iso 27001Document43 pagesIso 27001SRISHTI MALHOTRA100% (1)
- ISO - IEC 27001 Standard - Information Security Management SystemsDocument3 pagesISO - IEC 27001 Standard - Information Security Management SystemsPiiseth KarPearNo ratings yet
- Generic ISMS Documentation Checklist v1Document5 pagesGeneric ISMS Documentation Checklist v1Gaali_GcNo ratings yet
- ISO 27001 Implementation - in SMEDocument81 pagesISO 27001 Implementation - in SMEbudi.hw748No ratings yet
- Documentation and Records Required For ISO/IEC 27001 CertificationDocument28 pagesDocumentation and Records Required For ISO/IEC 27001 CertificationKonstantinos ZerbNo ratings yet
- ISO 27001 - GuideDocument12 pagesISO 27001 - GuideDolce Bombonca60% (5)
- ISO 27001 2013 Compliance Audit ChecklistDocument70 pagesISO 27001 2013 Compliance Audit Checklistgsuriv100% (2)
- Iso 27001 Risk Assessment TemplateDocument3 pagesIso 27001 Risk Assessment TemplateLyubomir GekovNo ratings yet
- ISO27k Controls Cross Check 2013Document6 pagesISO27k Controls Cross Check 2013Samer Al BashaNo ratings yet
- ISO27001Document6 pagesISO27001astaswastika100% (2)
- Step-By-Step Explanation of ISO 27001/ISO 27005 Risk ManagementDocument15 pagesStep-By-Step Explanation of ISO 27001/ISO 27005 Risk ManagementLyubomir Gekov100% (1)
- ISO 27001 Risk Management ApproachDocument52 pagesISO 27001 Risk Management ApproachSuneel100% (1)
- Shankar Subramaniyan: ISO27001: Implementation & Certification Process OverviewDocument24 pagesShankar Subramaniyan: ISO27001: Implementation & Certification Process Overviewje100% (1)
- The Ultimate Survival Guide To Iso 27001 ComplianceDocument25 pagesThe Ultimate Survival Guide To Iso 27001 Complianceihab100% (2)
- Reports ISO 27001Document43 pagesReports ISO 27001Prashanti GaonkarNo ratings yet
- ISMS SOA Statement of Applicability V1.2 TeamplteDocument11 pagesISMS SOA Statement of Applicability V1.2 Teampltekabir79No ratings yet
- ISO 27001 Complinace Checklist1Document49 pagesISO 27001 Complinace Checklist1tauqeer25100% (2)
- ISMS Control Checklist 2022Document31 pagesISMS Control Checklist 2022Anele Patriarca100% (1)
- Second Law Analysis If IC EnginesDocument16 pagesSecond Law Analysis If IC Enginesdjermounimohamed100% (1)
- HR Plan and Program For ThriDocument2 pagesHR Plan and Program For Thrifitrah jaya100% (1)
- A320 34-36 L3 E (Jan2001 CMP)Document222 pagesA320 34-36 L3 E (Jan2001 CMP)HENIGUEDRINo ratings yet
- Script - US Real Estate, Housing CrashDocument5 pagesScript - US Real Estate, Housing CrashMayumi AmponNo ratings yet
- Data Structures Through C++: Chapter - 1 1.1. C++ Class Overview-Basic Oop ConceptsDocument31 pagesData Structures Through C++: Chapter - 1 1.1. C++ Class Overview-Basic Oop ConceptsajNo ratings yet
- Naranjo, Cassandra Angelica R.: Ferdinand Marcos SRDocument3 pagesNaranjo, Cassandra Angelica R.: Ferdinand Marcos SRcassseeeyyyNo ratings yet
- Hist C12 Indian History 3Document190 pagesHist C12 Indian History 3kane21232874No ratings yet
- Examen Parcial Semana 4 Esp Segundo Bloque Ingles General II Grupo3 PDFDocument12 pagesExamen Parcial Semana 4 Esp Segundo Bloque Ingles General II Grupo3 PDFOmar alvarez FalcoNo ratings yet
- Credai ChennaiDocument92 pagesCredai ChennaiDIKSHA VERMANo ratings yet
- Anchor BoltDocument7 pagesAnchor BoltChris OngNo ratings yet
- Department of Electronics &telecommunication Engineering Sem:VIII Question Bank of Satellite CommunicationDocument4 pagesDepartment of Electronics &telecommunication Engineering Sem:VIII Question Bank of Satellite CommunicationPavan WaseNo ratings yet
- List of Companies TaglinesDocument11 pagesList of Companies TaglinesAastha KumarNo ratings yet
- Drilon vs. LimDocument1 pageDrilon vs. LimCyrus AvelinoNo ratings yet
- WebADI Whitepaper - Updated Sept2017Document31 pagesWebADI Whitepaper - Updated Sept2017ShriNo ratings yet
- Newsletter May 2022 Vol 2Document7 pagesNewsletter May 2022 Vol 2api-243482260No ratings yet
- CIP Annual Report 2009Document116 pagesCIP Annual Report 2009cip-libraryNo ratings yet
- TPH (Total Petroleum Hydrocarbons) : Immunoassay Method 10050Document10 pagesTPH (Total Petroleum Hydrocarbons) : Immunoassay Method 10050Cindy Valenzuela RuedaNo ratings yet
- R A Scheme FORMS PDFDocument3 pagesR A Scheme FORMS PDFJnyanendra Kumar PradhanNo ratings yet
- Hacienda Luisita vs. Presidential Agrarian Reform CouncilDocument74 pagesHacienda Luisita vs. Presidential Agrarian Reform CouncilJoyce VillanuevaNo ratings yet
- Catalogue Modular KitchenDocument88 pagesCatalogue Modular Kitchenswizar pradhanNo ratings yet
- 12 CFT - 21-BID-024 - FEED 2.0 ANNEX XI - Quality Management - VF FinalDocument3 pages12 CFT - 21-BID-024 - FEED 2.0 ANNEX XI - Quality Management - VF FinalbarryNo ratings yet
- Industech Exhibitor List 2020Document5 pagesIndustech Exhibitor List 2020kuldeepNo ratings yet
- Steel Window Brochure PDFDocument12 pagesSteel Window Brochure PDFVidya HittiNo ratings yet
- Quick Sizer Guide For SAPDocument76 pagesQuick Sizer Guide For SAPpkv001No ratings yet
- Himachal Pradesh Staff Selection Commission Hamirpur Distt. HAMIRPUR (H.P.) - 177001Document29 pagesHimachal Pradesh Staff Selection Commission Hamirpur Distt. HAMIRPUR (H.P.) - 177001abhishek bhardwajNo ratings yet
- Temenos SolutionDocument5 pagesTemenos SolutionAkhilNo ratings yet