Professional Documents
Culture Documents
Data Storage Security Issues in Cloud Computing
Uploaded by
Srinivasa Rao TOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Data Storage Security Issues in Cloud Computing
Uploaded by
Srinivasa Rao TCopyright:
Available Formats
A Study of Data Storage Security Issues in Cloud Computing
ABSTRACT
Cloud computing provides on demand services to its clients. Data storage is among one of
the primary services provided by cloud computing. Cloud service provider hosts the data of
data owner on their server and user can access their data from these servers. As data, owners
and servers are different identities, the paradigm of data storage brings up many security
challenges. An independent mechanism is required to make sure that data is correctly hosted
in to the cloud storage server. In this paper, we will discuss the different techniques that are
used for secure data storage on cloud.
Keywords : Cloud computing, Data storage, Cloud storage server.
I. INTRODUCTION Cloud computing is the combination of many pre-existing technologies
that have matured at different rates and in different contexts. The goal of cloud computing
is to allow users to take benefit from all these technologies. Many organizations are moving
into cloud because it allows the users to store their data on clouds and can access at anytime
from anywhere. Data breaching is possible in cloud environment, since data from various
users and business organizations lie together in cloud. By sending the data to the cloud, the
data owners transfer the control of their data to a third person that may raise security
problems. Sometimes the Cloud Service Provider(CSP) itself will use/corrupt the data
illegally. Security and privacy stands as major obstacle on cloud computing i.e. preserving
confidentiality, integrity and availability of data. A simple solution is to encrypt the data
before uploading it onto the cloud. This approach ensures that the data are not visible to
external users and cloud administrators but has the limitation that plain text based searching
algorithm are not applicable. In this paper, we discuss the security flaws in data storage and
the mechanisms to overcome it.
II. CLOUD STORAGE Cloud storage is one of the primary use of cloud computing. We
can define cloud storage as storage of the data online in the cloud. A cloud storage system
is considered as a distributed data centres, which typically use cloud-computing
technologies and offers some kind of interface for storing and accessing data. When storing
data on cloud, it appears as if the data is stored in a particular place with specific name.
There are four main types of cloud storage:
Personal Cloud Storage
It is also known as mobile cloud storage. In this type storage, individual's data is stored in the
cloud, and he/she may access the data from anywhere.
Public Cloud Storage:
In Public cloud storage the enterprise and storage service provider are separate and there aren't
any cloud resources stored in the enterprise's data centre. The cloud storage provider fully
manages the enterprise's public cloud storage.
Private Cloud Storage:
In Private Cloud Storage the enterprise and cloud storage provider are integrated in the
enterprise's data centre. In private cloud storage, the storage provider has infrastructure in the
enterprise's data centre that is typically managed by the storage provider. Private cloud storage
helps resolve the potential for security and performance concerns while still offering the
advantages of cloud storage.
Hybrid cloud storage: It is a combination of public and private cloud storage where some critical
data resides in the enterprise's private cloud while other data is stored and accessible from a
public cloud storage provider.
II.CHARACTERISTIC OF CLOUD COMPUTING
There are five characteristics of cloud computing. The first one is on-demand self-service, where a
consumer of services is provided the needed resources without human intervention and interaction
with cloud provider. The second characteristic is broad network access, which means resources can
be accessed from anywhere through a standard mechanism by thin or thick client platforms such
mobile phone, laptop, and desktop computer. Resource pooling is another characteristic, which
means the resources are pooled in order for multi tenants to share the resources. In the multi-
tenant model, resources are assigned dynamically to a consumer and after the consumer finishes it,
it can be assigned to another one to respond to high resource demand. Even if the resources are
assigned to customers on demand, they do not know the location of these assigned resources.
You might also like
- Cloud: Get All The Support And Guidance You Need To Be A Success At Using The CLOUDFrom EverandCloud: Get All The Support And Guidance You Need To Be A Success At Using The CLOUDNo ratings yet
- Cloud computing: Moving IT out of the officeFrom EverandCloud computing: Moving IT out of the officeBCS, The Chartered Institute for ITNo ratings yet
- Heterogeneous Data Storage Management With DeduplicationDocument20 pagesHeterogeneous Data Storage Management With DeduplicationVivek KrishnanNo ratings yet
- SSRN-id3649074Document3 pagesSSRN-id3649074Riva MakNo ratings yet
- International Journal of Research Publication and Reviews: Miss. Ankita Singh, Mr. Vedant Naidu, Prof. Deepali ShahDocument3 pagesInternational Journal of Research Publication and Reviews: Miss. Ankita Singh, Mr. Vedant Naidu, Prof. Deepali ShahPatel rajNo ratings yet
- Security Issues On The CloudDocument9 pagesSecurity Issues On The CloudAnyway Chare100% (1)
- Final MaterialDocument63 pagesFinal MaterialAyman AwadNo ratings yet
- Cloud Storage Overview Explains Benefits and ModelsDocument4 pagesCloud Storage Overview Explains Benefits and ModelsSpidey McuNo ratings yet
- Cloud Computing and Associated ThreatsDocument17 pagesCloud Computing and Associated Threatsshubham dadheechNo ratings yet
- Secure Replication Management in Cloud StorageDocument4 pagesSecure Replication Management in Cloud StorageInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Introduction to Cloud Computing FundamentalsDocument24 pagesIntroduction to Cloud Computing FundamentalsJacebh NikhNo ratings yet
- Cloud computing overviewDocument27 pagesCloud computing overviewαηαητ αφπαωαΙNo ratings yet
- (IJCST-V4I2P7) : Jahangeer Qadiree, Mohd Ilyas MaqboolDocument5 pages(IJCST-V4I2P7) : Jahangeer Qadiree, Mohd Ilyas MaqboolEighthSenseGroupNo ratings yet
- Data Security in Cloud Oriented Application Using SSL/TLS ProtocolDocument7 pagesData Security in Cloud Oriented Application Using SSL/TLS ProtocolInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Topics Page NoDocument12 pagesTopics Page NoRozy BharimalNo ratings yet
- ABSTRACTDocument14 pagesABSTRACTdjamitbravoNo ratings yet
- Unit-5 CeDocument19 pagesUnit-5 Ce21R25A1202 DESETTY VINEETHNo ratings yet
- Cloud ComputingDocument10 pagesCloud ComputingKarthikNo ratings yet
- Achieving Secure, Scalable and Fine-Grained Data Access Control in Cloud ComputingDocument47 pagesAchieving Secure, Scalable and Fine-Grained Data Access Control in Cloud Computingpssumi2No ratings yet
- Cloud Computing Security Threats and ResponsesDocument5 pagesCloud Computing Security Threats and ResponsesZak HunterNo ratings yet
- A Survey On Data Security in Cloud Computing Issues and Mitigation TechniquesDocument5 pagesA Survey On Data Security in Cloud Computing Issues and Mitigation TechniquesInternational Journal of Research in Engineering and TechnologyNo ratings yet
- VariablesDocument10 pagesVariablesRay MaysNo ratings yet
- Cloud StoragepptDocument8 pagesCloud StoragepptArshdeep SinghNo ratings yet
- AnswersDocument13 pagesAnswersRokesh KumarNo ratings yet
- Cloud Database Performance and SecurityDocument9 pagesCloud Database Performance and SecurityP SankarNo ratings yet
- Cloud Computing Definition and ServicesDocument18 pagesCloud Computing Definition and ServicesAqsa KhanNo ratings yet
- Verify & Decrypt Multi-Keyword Ranked Search Over Encrypted Data On Cloud ServerDocument6 pagesVerify & Decrypt Multi-Keyword Ranked Search Over Encrypted Data On Cloud ServerInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Securing Cloud Data Storage: S. P. Jaikar, M. V. NimbalkarDocument7 pagesSecuring Cloud Data Storage: S. P. Jaikar, M. V. NimbalkarInternational Organization of Scientific Research (IOSR)No ratings yet
- Cloud StroageDocument10 pagesCloud StroagePUNJABI JUTTNo ratings yet
- Unit - V 1. Cloud Computing Security ChallengesDocument23 pagesUnit - V 1. Cloud Computing Security ChallengesAn JeevanNo ratings yet
- Cloud Computing Guide: Types, Benefits & How It WorksDocument40 pagesCloud Computing Guide: Types, Benefits & How It WorksHimanshu SoniNo ratings yet
- A Multikeyword Ranked Search Technique With Provision For Dynamic Update of Encrypted Documents in CloudDocument8 pagesA Multikeyword Ranked Search Technique With Provision For Dynamic Update of Encrypted Documents in CloudPallaviNo ratings yet
- Enhancing Cloud Security Using Multicloud Architecture and Device Based IdentityDocument6 pagesEnhancing Cloud Security Using Multicloud Architecture and Device Based IdentityshreyassrinathNo ratings yet
- DropStore A Secure Backup System Using Multi-Cloud and Fog ComputingDocument10 pagesDropStore A Secure Backup System Using Multi-Cloud and Fog ComputingPremkNo ratings yet
- 2 - New Title & New PaperDocument5 pages2 - New Title & New PaperNagabhushanamDonthineniNo ratings yet
- Effective Service Security Schemes in Cloud Computing: K.Sravani, K.L.A.NiveditaDocument6 pagesEffective Service Security Schemes in Cloud Computing: K.Sravani, K.L.A.NiveditaInternational Journal of computational Engineering research (IJCER)No ratings yet
- A Survey On Security and Privacy in Cloud Computing: Mir Toornaw IslamDocument9 pagesA Survey On Security and Privacy in Cloud Computing: Mir Toornaw IslamtamernadeemNo ratings yet
- Cloud StorageDocument8 pagesCloud StorageUchechukwu MarizuNo ratings yet
- Titel SelactiveDocument18 pagesTitel SelactiveDe HNo ratings yet
- B0501 02-0812 PDFDocument5 pagesB0501 02-0812 PDFIJMERNo ratings yet
- History: Cloud Storage Is A Model ofDocument5 pagesHistory: Cloud Storage Is A Model ofAditya JainNo ratings yet
- Data Storage in Secured Multi-Cloud Storage in Cloud ComputingDocument4 pagesData Storage in Secured Multi-Cloud Storage in Cloud ComputingInternational Journal of computational Engineering research (IJCER)No ratings yet
- Innovative Intelligence Over The Internet - "The Cloud"Document3 pagesInnovative Intelligence Over The Internet - "The Cloud"MYTHILI RAMESHNo ratings yet
- Data Storage Technology and Its Development Based On Cloud ComputingDocument4 pagesData Storage Technology and Its Development Based On Cloud ComputingLong Phùng PhiNo ratings yet
- Cloud ComputingDocument4 pagesCloud ComputingProtelionNo ratings yet
- Data Storage 2pdfDocument5 pagesData Storage 2pdfIsrat6730 JahanNo ratings yet
- Data Storage and Third Party Audting Services (National Conference Paper by Vrushali, Nouman)Document4 pagesData Storage and Third Party Audting Services (National Conference Paper by Vrushali, Nouman)Nouman KhanNo ratings yet
- Layers and Types of Cloud ComputingDocument16 pagesLayers and Types of Cloud ComputingJayeshS CS:CZ GamingNo ratings yet
- Multi-Cloud Secure Data Storage Using Cryptographic TechniquesDocument4 pagesMulti-Cloud Secure Data Storage Using Cryptographic TechniquesvikasbhowateNo ratings yet
- Real World Challenges of Cloud ComputingDocument23 pagesReal World Challenges of Cloud ComputingVarsha PrabhuNo ratings yet
- Cloud ComputingDocument2 pagesCloud Computingxf2bkjrqwgNo ratings yet
- PP 216-221 A Conceptual Architecture For Securing Public Cloud Moving FromDocument6 pagesPP 216-221 A Conceptual Architecture For Securing Public Cloud Moving FromEditorijset IjsetNo ratings yet
- Cloud Computing SecurityDocument10 pagesCloud Computing SecurityAYISHA NISARNo ratings yet
- Datastoragesecurityincloudcomputing 150625060610 Lva1 App6891Document17 pagesDatastoragesecurityincloudcomputing 150625060610 Lva1 App6891asdasdNo ratings yet
- A Novel Data Authentication and Monitoring Approach Over CloudDocument4 pagesA Novel Data Authentication and Monitoring Approach Over CloudseventhsensegroupNo ratings yet
- Scheme For Secured Cloud Access and Storage EnvironmentDocument23 pagesScheme For Secured Cloud Access and Storage EnvironmentModjtaba GharibyarNo ratings yet
- 001 Cloud ComputingDocument3 pages001 Cloud Computingcarlos oliva martiNo ratings yet
- Cloud Security and Its InfrastructureDocument22 pagesCloud Security and Its InfrastructureRahul saini100% (1)
- Cloud ComputingLiteraturesurveyDocument18 pagesCloud ComputingLiteraturesurveyengineeringwatchNo ratings yet
- Cloud Computing Made Simple: Navigating the Cloud: A Practical Guide to Cloud ComputingFrom EverandCloud Computing Made Simple: Navigating the Cloud: A Practical Guide to Cloud ComputingNo ratings yet
- There Are Two Ways To Install Hadoop in UbantuDocument10 pagesThere Are Two Ways To Install Hadoop in UbantuSrinivasa Rao TNo ratings yet
- Page Rank With Apache Spark GraphxDocument8 pagesPage Rank With Apache Spark GraphxSrinivasa Rao TNo ratings yet
- What Is Big DataDocument4 pagesWhat Is Big DataSrinivasa Rao TNo ratings yet
- Big Data Sources and EvolutionDocument7 pagesBig Data Sources and EvolutionSrinivasa Rao TNo ratings yet
- Mongodb IndexesDocument31 pagesMongodb IndexesSrinivasa Rao TNo ratings yet
- Real-World Examples of Cloud ComputingDocument2 pagesReal-World Examples of Cloud ComputingSrinivasa Rao TNo ratings yet
- Dynamic Programming: How Can We Calculate F (20) ?Document10 pagesDynamic Programming: How Can We Calculate F (20) ?Srinivasa Rao TNo ratings yet
- Mongodb MCQDocument3 pagesMongodb MCQSrinivasa Rao TNo ratings yet
- What Is A Cloud? 1) What Is Cloud Computing?Document2 pagesWhat Is A Cloud? 1) What Is Cloud Computing?Srinivasa Rao TNo ratings yet
- Hadoop Installation StepsDocument16 pagesHadoop Installation StepsSrinivasa Rao TNo ratings yet
- Software and Hardware Requirements For Data Science and Machine Learning LabsDocument1 pageSoftware and Hardware Requirements For Data Science and Machine Learning LabsSrinivasa Rao TNo ratings yet
- MSC Comp SC Syllabus Cbcs 09072016Document37 pagesMSC Comp SC Syllabus Cbcs 09072016Srinivasa Rao TNo ratings yet
- Grid Computing Grid Computing Is A Type of Distributed Computing That Combines The Resources ofDocument3 pagesGrid Computing Grid Computing Is A Type of Distributed Computing That Combines The Resources ofSrinivasa Rao TNo ratings yet
- MSC PG Exams IV MID SEM 2021Document1 pageMSC PG Exams IV MID SEM 2021Srinivasa Rao TNo ratings yet
- CC MCQDocument28 pagesCC MCQSrinivasa Rao TNo ratings yet
- Cloud Computing Deployment ModelsDocument5 pagesCloud Computing Deployment ModelsSrinivasa Rao TNo ratings yet
- What Is Cloud Computing Reference ModelDocument3 pagesWhat Is Cloud Computing Reference ModelSrinivasa Rao TNo ratings yet
- Cloud StorageDocument11 pagesCloud StorageSrinivasa Rao TNo ratings yet
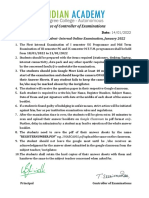
- Guidelines-Students-Online Exam Jan-2022Document1 pageGuidelines-Students-Online Exam Jan-2022Srinivasa Rao TNo ratings yet
- R Programming Presentation Schedule and AttendanceDocument1 pageR Programming Presentation Schedule and AttendanceSrinivasa Rao TNo ratings yet
- MCA Admission ListDocument3 pagesMCA Admission ListSrinivasa Rao TNo ratings yet
- The Cornell Note-taking System: 5 Steps to Effective NotesDocument1 pageThe Cornell Note-taking System: 5 Steps to Effective NotesSrinivasa Rao TNo ratings yet
- Big Data Analytics With Hadoop: SDM Institute of TechnologyDocument2 pagesBig Data Analytics With Hadoop: SDM Institute of TechnologySrinivasa Rao TNo ratings yet
- Cloud Computing ArchitectureDocument4 pagesCloud Computing ArchitectureSrinivasa Rao T100% (1)
- Oppo ColorOS - 7.1-ENGDocument245 pagesOppo ColorOS - 7.1-ENGlaurent llacelNo ratings yet
- Bengaluru Central University: Bachelor of Computer Applications, SYLLABUS (2019-20 ONWARDS)Document35 pagesBengaluru Central University: Bachelor of Computer Applications, SYLLABUS (2019-20 ONWARDS)roopashree obaleshNo ratings yet
- JeevanUmang - 5-1-2021 8.21.13 PDFDocument8 pagesJeevanUmang - 5-1-2021 8.21.13 PDFSrinivasa Rao TNo ratings yet
- Guidelines To ChiefDocument56 pagesGuidelines To ChiefSrinivasa Rao TNo ratings yet
- Resume: Mamatha.KDocument2 pagesResume: Mamatha.KSrinivasa Rao TNo ratings yet
- Test Driven Development of Embedded SystemsDocument7 pagesTest Driven Development of Embedded Systemsjpr_joaopauloNo ratings yet
- SAP PP Interview QuestionDocument8 pagesSAP PP Interview QuestionAshishNo ratings yet
- Dell-1708fp User's Guide En-UsDocument55 pagesDell-1708fp User's Guide En-UsFareez TaherNo ratings yet
- Midnight Blue Gold Fun Patterns and Illustrations Tech Predictions Presentation Party-1Document13 pagesMidnight Blue Gold Fun Patterns and Illustrations Tech Predictions Presentation Party-1KAKI V N S V VIGNESH CSEUG-2020No ratings yet
- Gujarat Technological UniversityDocument2 pagesGujarat Technological UniversityTushar MaruNo ratings yet
- Exam 2 Cheat SheetDocument3 pagesExam 2 Cheat Sheetapi-352975129No ratings yet
- The Self-Taught Programmer The Definitive Guide To Programming ProfessionallyDocument278 pagesThe Self-Taught Programmer The Definitive Guide To Programming Professionallyjack Reacher100% (58)
- Digital Electronics and OpticsDocument90 pagesDigital Electronics and OpticsSteve MachariaNo ratings yet
- c08138459 PDFDocument96 pagesc08138459 PDFTaviUlmeanuNo ratings yet
- JAVADocument66 pagesJAVAanoojaNo ratings yet
- A 1Document2 pagesA 1Phong PiloNo ratings yet
- Computer Organization & Assembly Language: 1 - An IntroductionDocument35 pagesComputer Organization & Assembly Language: 1 - An IntroductionAhmad NaeemNo ratings yet
- COMSOL Multiphysics: Installation GuideDocument136 pagesCOMSOL Multiphysics: Installation Guiderosem83236No ratings yet
- Software Testing Types and LevelsDocument60 pagesSoftware Testing Types and LevelsstarNo ratings yet
- AN17831ADocument9 pagesAN17831AJose LeonNo ratings yet
- DocumentationDocument146 pagesDocumentationgothickaNo ratings yet
- Software Architecture Evolution From n-Tier to SOADocument58 pagesSoftware Architecture Evolution From n-Tier to SOAWalter MenezesNo ratings yet
- Vsphere With KubernetesDocument12 pagesVsphere With Kubernetesleroy23No ratings yet
- Winrunner Testing Winrunner 1Document8 pagesWinrunner Testing Winrunner 1SrujanaNo ratings yet
- Scattering Mechanisms in Β-Ga2O3 Junctionless SOI MOSFET - Investigation of Electron Mobility and Short Channel EffectsDocument6 pagesScattering Mechanisms in Β-Ga2O3 Junctionless SOI MOSFET - Investigation of Electron Mobility and Short Channel Effects刘锦成No ratings yet
- LMX 2326Document19 pagesLMX 2326So Was RedNo ratings yet
- CSE-311 Microprocessor & Interfacing Course OutlineDocument2 pagesCSE-311 Microprocessor & Interfacing Course OutlineEngnrMemonNo ratings yet
- Implementation of 8 Bit Adder Using Xilinx AimDocument22 pagesImplementation of 8 Bit Adder Using Xilinx AimManimegalaiNo ratings yet
- Cisco Scale Router BoxesDocument110 pagesCisco Scale Router BoxesRyan LarshNo ratings yet
- JSF @RoseIndiaDocument251 pagesJSF @RoseIndiamalli.gontla3724No ratings yet
- ChordanaPlay Manual enDocument37 pagesChordanaPlay Manual enBen ZhouNo ratings yet
- SAGE X3 Architecture Guide v11Document35 pagesSAGE X3 Architecture Guide v11briand28No ratings yet
- Acer Aspire VN7-791 VN7-791G 1 Wistron Poseidon 860M - Rev1Document86 pagesAcer Aspire VN7-791 VN7-791G 1 Wistron Poseidon 860M - Rev1amir diazNo ratings yet
- Huawei OceanStor V3 Converged Storage Pre-Sales TrainingDocument49 pagesHuawei OceanStor V3 Converged Storage Pre-Sales TrainingHUMANMANNo ratings yet
- ASP Virtual Implementation PDFDocument724 pagesASP Virtual Implementation PDFmulyadiNo ratings yet