Professional Documents
Culture Documents
18.3 Issues in Redundant Topologies
Uploaded by
CCNA 200-301Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
18.3 Issues in Redundant Topologies
Uploaded by
CCNA 200-301Copyright:
Available Formats
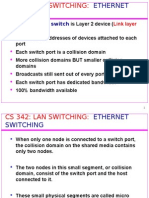
18.
3 Building Redundant Switched Topologies
Issues in Redundant Topologies
In the absence of a protocol to monitor link forwarding states, a redundant switch topology is
vulnerable to these conditions:
Continuous frame duplication: Without some loop-avoidance process, each switch floods
broadcast, multicast, and unknown unicast frames endlessly. Switches flood broadcast frames to
all ports except the port on which the frame was received. The frames then duplicate and travel
endlessly around the loop in all directions. The result of continuous broadcast frame duplication
is called a broadcast storm.
Multiple frame transmission: Multiple copies of unicast frames may be delivered to destination
stations. Many protocols expect to receive only a single copy of each transmission. Multiple
copies of the same frame can cause unrecoverable errors.
Media Access Control (MAC) database instability: Instability in the content of the MAC
address table results from the fact that different ports of the switch receive copies of the same
frame. Data forwarding can be impaired when the switch consumes the resources that are coping
with instability in the MAC address table.
For example, in the topology that is shown in the figure no Layer 2 loop prevention mechanism
is implemented. Suppose that host A sends a frame to host B. Host A resides on network
segment A, and host B resides on network segment B. Assume that none of the switches have
learned the address of host B.
Host A transmits the frame destined for host B on segment A.
Switch W receives the frame that is destined for host B, learns the MAC address of host A on
segment A, and floods it out to switches X and Y.
Switch X and switch Y both receive the frame from host A (via switch W) and correctly learn
that host A is on segment 1 for switch X and on segment 2 for switch Y. Switch X and switch Y
then forward the frame to switch Z. Switch Z receives two copies of the frame from host A: one
copy through switch X on segment 3 and one copy through switch Y on segment 4.
Assume that the first copy of the frame from switch X arrives first. Switch Z learns that host A
resides on segment 3. Because switch Z does not know where host B is connected, it forwards
the frame to all its ports (except the incoming port on segment 3) and therefore to host B and also
to switch Y.
When the second copy of the frame from switch Y arrives at switch Z on segment 4, switch Z
updates its table to indicate that host A resides on segment 4. Switch Z then forwards the frame
to host B and switch X.
In this example where no loop prevention mechanism exists the result is that host B has received
multiple copies of the frame, which can cause problems with the receiving application directly
on the host B.
Switches X and Y now change their internal tables to indicate that host A is on segment 3 for
switch X and on segment 4 for switch Y. The copies of the initial frame from host A being
received on different segments of the switches results in MAC database instability.
Furthermore, if the initial frame from host A was a broadcast frame, then all switches forward
the frames endlessly. Switches flood broadcast frames to all ports except the port on which the
frame was received. The frames then duplicate and travel endlessly around the loop in all
directions. They eventually would use all available network bandwidth and block transmission of
other packets on both segments. This situation results in a broadcast storm.
You might also like
- Network Devices Hubs, Switches, RoutersDocument24 pagesNetwork Devices Hubs, Switches, RoutersPaul67% (3)
- Ccna3 Mod7 STP PDFDocument77 pagesCcna3 Mod7 STP PDFminhtuanqniNo ratings yet
- Faculty of Engineering, Sciences & Technology: Assignment # 03 - Spring Semester 2020Document8 pagesFaculty of Engineering, Sciences & Technology: Assignment # 03 - Spring Semester 2020Muhammad Usman AfaqNo ratings yet
- What Is Layer 2 Switching LoopDocument3 pagesWhat Is Layer 2 Switching LooppriyasouravNo ratings yet
- How Switches WorkDocument1 pageHow Switches WorkarsiemarNo ratings yet
- Layer 2 Switching Loop: MAC AddressDocument2 pagesLayer 2 Switching Loop: MAC AddressashuangelNo ratings yet
- Chapter 1 - SolutionsDocument3 pagesChapter 1 - SolutionsNaida KukuruzovićNo ratings yet
- Spaning Tree Protocol STPDocument88 pagesSpaning Tree Protocol STPapi-216820839No ratings yet
- Network - Layer2sw. VlansDocument16 pagesNetwork - Layer2sw. Vlansزينب جواد اسد كاظمNo ratings yet
- Homework Title / No.: 3 Course CodeDocument10 pagesHomework Title / No.: 3 Course CodeSurendra Singh Chauhan0% (1)
- Ccna Press STPDocument64 pagesCcna Press STPsadam017No ratings yet
- SwitchingDocument6 pagesSwitchingUziNo ratings yet
- Lec Tel Eng 7Document14 pagesLec Tel Eng 7Mohammad Mostofa Kamal KowshikNo ratings yet
- Virtual Circuit NetworkDocument6 pagesVirtual Circuit NetworkJules BamweNo ratings yet
- V Blast Vs D Blast PDFDocument9 pagesV Blast Vs D Blast PDFShashank Mishra100% (1)
- Chapter 5 - Analyzing Ethernet Lan SwitchingDocument79 pagesChapter 5 - Analyzing Ethernet Lan Switchingchris topherNo ratings yet
- Chapter 2 - Assignment #1Document2 pagesChapter 2 - Assignment #1Ericka Sublino NasingaoNo ratings yet
- CCENT Chapter 7 Key TopicsDocument3 pagesCCENT Chapter 7 Key Topicshoang nguyen baNo ratings yet
- Unit - IiDocument35 pagesUnit - IiJit AggNo ratings yet
- Chapter 11 Extending LANsDocument15 pagesChapter 11 Extending LANskokome35No ratings yet
- Resumen Cap7bDocument5 pagesResumen Cap7batilio2No ratings yet
- CN Unit-4 Imp QA'sDocument22 pagesCN Unit-4 Imp QA'shajirasabuhiNo ratings yet
- 100 101Document207 pages100 101rocevaNo ratings yet
- Unit 2 WholeDocument24 pagesUnit 2 Wholepriya nmNo ratings yet
- CCN NOTS Final Unit - 3Document39 pagesCCN NOTS Final Unit - 3Bruce Randall100% (3)
- Computer Bank 1Document2 pagesComputer Bank 1orchid21No ratings yet
- Unit 2 Mobile Telecommunication Systems Medium Access Control (MAC) Address Is A Hardware Address Use To Uniquely Identify EachDocument43 pagesUnit 2 Mobile Telecommunication Systems Medium Access Control (MAC) Address Is A Hardware Address Use To Uniquely Identify EachVani BaskaranNo ratings yet
- Um InterfaceDocument17 pagesUm InterfacePrakash MauryaNo ratings yet
- Lecture-2 MACDocument45 pagesLecture-2 MACFahim Hasan AlifNo ratings yet
- Data Link Control Protocol.Document32 pagesData Link Control Protocol.Fatimah FarheenNo ratings yet
- MODULE 8 - Ethenet SwitchingDocument4 pagesMODULE 8 - Ethenet SwitchingGrecu GianiNo ratings yet
- Chapter 5Document42 pagesChapter 5Bezabh AbebawNo ratings yet
- 311 FinalDocument4 pages311 Finalapi-358841842No ratings yet
- Network Core: Lecturer SlidesDocument17 pagesNetwork Core: Lecturer SlidesevhyajahNo ratings yet
- hw4 SolDocument4 pageshw4 SolIkhtear SharifNo ratings yet
- Comparison of OSPF and RIP: AbstractDocument6 pagesComparison of OSPF and RIP: AbstractSushma LuhachNo ratings yet
- Switching Concepts: MAC Address TableDocument8 pagesSwitching Concepts: MAC Address Tablemobio jeanNo ratings yet
- Ethernet SwitchDocument15 pagesEthernet SwitchVo Ngoc HoangNo ratings yet
- CN 04 Coduri HandoutDocument19 pagesCN 04 Coduri HandoutTeoMiuNo ratings yet
- Chapter05 SGDocument16 pagesChapter05 SGAnis KhalafNo ratings yet
- Exercícios - Parte 1 - Só PerguntasDocument4 pagesExercícios - Parte 1 - Só PerguntasMarcos PereiraNo ratings yet
- Computer Networks Homework HelpDocument8 pagesComputer Networks Homework HelpassignmentpediaNo ratings yet
- What Is A MAC Address?Document20 pagesWhat Is A MAC Address?peeyushNo ratings yet
- 006 Switching ConceptsDocument8 pages006 Switching ConceptszinebNo ratings yet
- Flow Control: Model of Frame TransmissionDocument7 pagesFlow Control: Model of Frame TransmissionEmmanuel SaweNo ratings yet
- Medium Access Control: Carrier Sense Multiple Access With Collision DetectionDocument33 pagesMedium Access Control: Carrier Sense Multiple Access With Collision DetectionMhmd NeamatNo ratings yet
- Spanning Tree ProtocolDocument5 pagesSpanning Tree ProtocoljeffdehamNo ratings yet
- Medium Access Control Sublayer (Chapter 4) - CSHub PDFDocument15 pagesMedium Access Control Sublayer (Chapter 4) - CSHub PDFSpeed PianoNo ratings yet
- Medium Access Control Sublayer (Chapter 4) - CSHub PDFDocument15 pagesMedium Access Control Sublayer (Chapter 4) - CSHub PDFSpeed PianoNo ratings yet
- Answer To Selected Problems in Chapter 1Document1 pageAnswer To Selected Problems in Chapter 1moahamd hashemNo ratings yet
- Ee132b HW3Document4 pagesEe132b HW3Ahmed HassanNo ratings yet
- HDLC ProtocolsDocument13 pagesHDLC ProtocolsraviNo ratings yet
- Switching Interview Questions and Answers Vol 1.0Document14 pagesSwitching Interview Questions and Answers Vol 1.0Eduardo AguilarNo ratings yet
- An Ethernet Switch: Link Layer Device)Document37 pagesAn Ethernet Switch: Link Layer Device)nswaziNo ratings yet
- Lab 5 Introduction To Packet Tracer and Cisco RouterDocument26 pagesLab 5 Introduction To Packet Tracer and Cisco RouternoumanNo ratings yet
- ALOHADocument5 pagesALOHAtonmoyNo ratings yet
- Cn-Unit Iii-NotesDocument39 pagesCn-Unit Iii-NotesRobin RobinNo ratings yet
- Ethernet: An Introduction: Fast Ethernet Operates 10 Times Faster, I.e., at 100 Mbps. Recently, There HasDocument4 pagesEthernet: An Introduction: Fast Ethernet Operates 10 Times Faster, I.e., at 100 Mbps. Recently, There Hasaksagar22No ratings yet
- Technical Product Specification Intel Server Board S2600CP FamilyDocument231 pagesTechnical Product Specification Intel Server Board S2600CP FamilyBagusNo ratings yet
- Slido Questions For Module 3: A) Framing B) Errorcontrol C) FlowcontrolDocument4 pagesSlido Questions For Module 3: A) Framing B) Errorcontrol C) Flowcontrolblessy thomasNo ratings yet
- 01 TE384 - Lecture 1 - Telecom - NetworksDocument53 pages01 TE384 - Lecture 1 - Telecom - Networksmaka bojangNo ratings yet
- Debug 1214Document14 pagesDebug 1214Abdul RozakNo ratings yet
- DSL Technologies1Document39 pagesDSL Technologies1Mohammed AatifNo ratings yet
- Reselection Priority High 7: RSRP - 114 DBMDocument2 pagesReselection Priority High 7: RSRP - 114 DBMโดราเอม่อน คัก คักNo ratings yet
- ABB Serial Data ConvertersDocument13 pagesABB Serial Data ConvertersRodrigo Valdez CuellarNo ratings yet
- Lista 56Document68 pagesLista 56LautaroRivasNo ratings yet
- S.No Product Range Description PriceDocument3 pagesS.No Product Range Description PriceSrinivasaPerumalNo ratings yet
- Networkingdevices 161021181705Document41 pagesNetworkingdevices 161021181705Andrew C. BrazaNo ratings yet
- LEMKEN Cable Guide 2022 enDocument47 pagesLEMKEN Cable Guide 2022 enMaxi Reiter100% (1)
- DTS Gfx4-Profi 0406 EngDocument2 pagesDTS Gfx4-Profi 0406 EngVladimirAgeevNo ratings yet
- Chapter (1) : Optical Networking Technologies TechnologiesDocument39 pagesChapter (1) : Optical Networking Technologies TechnologiesIbrahim ElghawilNo ratings yet
- Lte ADocument133 pagesLte AAkhmad Hafid IrawanNo ratings yet
- ZIGBEEDocument9 pagesZIGBEEPriya KabirNo ratings yet
- 05-Basic Principles of Mobile CommunicationsDocument37 pages05-Basic Principles of Mobile CommunicationsMohamed TatouNo ratings yet
- Ar9271 20120907Document152 pagesAr9271 20120907Carlos Ben AdonayNo ratings yet
- Samsung Lyon-External Rev 1.0Document74 pagesSamsung Lyon-External Rev 1.0dregonlexa100% (1)
- FiberHome Optical Network Overview Kntelecom IrDocument49 pagesFiberHome Optical Network Overview Kntelecom IrRobert MorrisNo ratings yet
- Computer Networking Fundamentals Chapter 3 (A)Document37 pagesComputer Networking Fundamentals Chapter 3 (A)wfidayuNo ratings yet
- Cau Hinh Ring VFT - Ring 6400 Va VFT - 2469491727108411727Document3 pagesCau Hinh Ring VFT - Ring 6400 Va VFT - 2469491727108411727Kien Nguyen ThaiNo ratings yet
- Cisco Nexus 9500 Series SwitchesDocument7 pagesCisco Nexus 9500 Series SwitchesChienHQ VTNo ratings yet
- DCN Over VlanDocument14 pagesDCN Over VlanHedi PrimaNo ratings yet
- Manual Del TSX Cusb485Document2 pagesManual Del TSX Cusb485Germán Walter RufanachtNo ratings yet
- AGS-20 New SIAE IDUDocument14 pagesAGS-20 New SIAE IDUFernando TejedaNo ratings yet
- TC Log stk1Document6 pagesTC Log stk1JuanoNo ratings yet
- 6.4.2.4 Lab - Building Straight-Through and Crossover UTP CablesDocument5 pages6.4.2.4 Lab - Building Straight-Through and Crossover UTP CablesDinesh Pudasaini0% (1)
- Rtl8211fsi Vs CGDocument100 pagesRtl8211fsi Vs CGDhananjay MathaneNo ratings yet
- Vm-742B Network CommunicationDocument3 pagesVm-742B Network Communicationravi_fdNo ratings yet
- Optone 1100ASeriesDocument3 pagesOptone 1100ASeriesiman wahyudinNo ratings yet