Professional Documents
Culture Documents
How To Recover and Decompress A Linux K... L Dumped MTD Partition - Alan C
How To Recover and Decompress A Linux K... L Dumped MTD Partition - Alan C
Uploaded by
hombre pocilga0 ratings0% found this document useful (0 votes)
35 views3 pagesOriginal Title
How to recover and decompress a Linux k...l dumped MTD partition – Alan C
Copyright
© © All Rights Reserved
Available Formats
PDF or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as PDF or read online from Scribd
0 ratings0% found this document useful (0 votes)
35 views3 pagesHow To Recover and Decompress A Linux K... L Dumped MTD Partition - Alan C
How To Recover and Decompress A Linux K... L Dumped MTD Partition - Alan C
Uploaded by
hombre pocilgaCopyright:
© All Rights Reserved
Available Formats
Download as PDF or read online from Scribd
You are on page 1of 3
272018 How to recover and decompress @ Linux kernel dumped MTD partion - Alan C. Assis
a blog about computers and other funny things
Alan C. Assis
How to recover and decompress a Linux kernel
dumped MTD partition
Lused the “dd” utility to recover the kernel image from my IP Camera. Now I want to analyze it
$ cp mtd2_Kernel.img /tmp/
Let see how is the kernel image:
$ file mtd2_kernel. img
mtd2_Kernel.img: u-boot legacy ulmage, Linux-2.6.24ss1, Linux/ARM, OS Kernel Imi
Hmm, it is u-boot ulmage, let us to remove the u-boot header:
$ dd if=mtd2_Kernel.img of=Image bs=64 skip=1
235514 records in
2355148 records out
1507264 bytes (1.5 MB) copied, @.0529103 s, 28.5 MB/s
Let see now:
$ file Image
Image: Linux kernel ARM boot executable zImage (little-endian)
Hmm, itis a zImage file, if I rename it and try to extract?
$ mv Image Image.gz
$ gunzip Image.gz
gzip: Image.gz: not in gzip format
No way!
{lesKLCRACKINGIREVERSE%20ENGINEERINGHow'20%0%420recover%20and%:20decompress%20a%20Linux%s20kerel¥s2Odumped'i20M... 1
272018 How to recover and decompress @ Linux kernel dumped MTD partion - Alan C. Assis
(After more search I found this suggestions (http://www linuxquestions.org/questions/programming-
9/how-to-obtain-image-from-zimage-824499/))
Let try it:
$ my Image.gz zImage
$ arm-linux-objdump -EL -b binary -D -m armvSt zImage | grep 8b1f
31e evessbif andeq r8, r8, pc, Isl fp
2840. 6cab1fa4 stevs 15, cri, [fp], {68}
3646 esbi fats ldmia ri!, {r@, r3, 74, 75, r6, r7, sl, ip, s
We are interested only in the first address (31e4 = 12772)
$ dd if=zImage of=piggy.gz bs=1 skip=12772
149449248 records in
149449240 records out
1494492 bytes (1.5 MB) copied, 2.36995 s, 631 kB/s
$ file piggy.gz
piggy.gz: gzip compressed data, last modified: Mon Apr 8 16:01:49 2013, max coi
$ gunzip piggy.gz
gzip: piggy.gz: decompression Ok, trailing garbage ignored
Great!!!
Now I can inspect the kernel symbols because /proc/ksyms and /proc/kallsyms are not present.
{lesKLCRACKINGIREVERSE%20ENGINEERING/How'2010%420recover%20and%20decompress%20a%20Linux%s20kernel¥s2Odumped’i20M... 218
272018 How to recover and decompress @ Linux kernel dumped MTD partion ~ Alan C. Assis
Advertisements
Master en Ciberseguridad
7800 3.900 €
Clic aqui
Master en Ciberseguridad ...
C6 CACY
space for
Boras erste
emereiacc)
linux (https://acassis.wordpress.com/category/linux/)
acassis
June 4, 2015June 4, 2015
3 thoughts on “How to recover and decompress a Linux
kernel dumped MTD partition”
Pingback: Using strings to recreate a Linux kernel config | Alan C. Assis
ponnex says
December 7, 2015 at 8:18 am
I would like to know how would you inspect kernel symbols from piggy file? @
Reply
acassis says:
December 7, 2015 at 12:10 pm
Hi Ponnex,
It depends on if kernel was compiled with enabled symbols (-g option in gec). BR, Alan
Reply
{les KLCRACKINGIREVERSE%20ENGINEERINGHow’20%0% 20recover%20and%20decompress% 20:
Liewx3420kernel"s20dumped%20M.. 3/3
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5814)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1092)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (845)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (590)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (897)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (540)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (348)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (822)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (122)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (401)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- How To Solve The Malwarebytes CrackMe - ..Document17 pagesHow To Solve The Malwarebytes CrackMe - ..hombre pocilgaNo ratings yet
- SAS v1.0 AzeriaDocument20 pagesSAS v1.0 Azeriahombre pocilgaNo ratings yet
- Hacking Android Phone. How Deep The Rabbit Hole GoesDocument27 pagesHacking Android Phone. How Deep The Rabbit Hole Goeshombre pocilgaNo ratings yet
- How To Reverse EngineerDocument4 pagesHow To Reverse Engineerhombre pocilgaNo ratings yet
- Reverse Engineering An Android Application (APK Hacking)Document5 pagesReverse Engineering An Android Application (APK Hacking)hombre pocilgaNo ratings yet
- Unpacking Find 7 (A) Kernel Zimages For ..Document2 pagesUnpacking Find 7 (A) Kernel Zimages For ..hombre pocilgaNo ratings yet
- How To Extract and Disassemble A Linux ..Document6 pagesHow To Extract and Disassemble A Linux ..hombre pocilgaNo ratings yet
- Reverse Engineering Android's AbootDocument5 pagesReverse Engineering Android's Aboothombre pocilgaNo ratings yet
- 2014 EN AdvancedBootkitTechniquesOnAndroid ChenZhangqiShendiDocument66 pages2014 EN AdvancedBootkitTechniquesOnAndroid ChenZhangqiShendihombre pocilgaNo ratings yet
- Visual Binary File Analysis With Python - CmattoonDocument38 pagesVisual Binary File Analysis With Python - Cmattoonhombre pocilgaNo ratings yet
- Woot17 Paper KurmusDocument9 pagesWoot17 Paper Kurmushombre pocilgaNo ratings yet
- Permeate Pump 7 14 17Document12 pagesPermeate Pump 7 14 17hombre pocilgaNo ratings yet
- ES FANOXPC FICHA CM FaseTemperatura ST-ST-D GC17 R02Document1 pageES FANOXPC FICHA CM FaseTemperatura ST-ST-D GC17 R02hombre pocilgaNo ratings yet
- Apertura de Colecciones HID - Windows Drivers - Microsoft LearnDocument2 pagesApertura de Colecciones HID - Windows Drivers - Microsoft Learnhombre pocilgaNo ratings yet
- New-48v Lifepo4 Battery User ManualDocument19 pagesNew-48v Lifepo4 Battery User Manualhombre pocilgaNo ratings yet
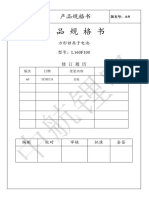
- BL8023C Datasheet V1.5Document6 pagesBL8023C Datasheet V1.5hombre pocilgaNo ratings yet
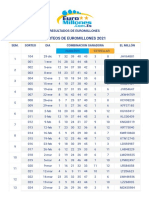
- Resultados Euromillones 2020Document4 pagesResultados Euromillones 2020hombre pocilgaNo ratings yet
- EVE 160ah LF160 Product SpecificationDocument12 pagesEVE 160ah LF160 Product Specificationhombre pocilgaNo ratings yet
- Resultados Euromillones 2019Document4 pagesResultados Euromillones 2019hombre pocilgaNo ratings yet
- Resultados Euromillones 2021Document4 pagesResultados Euromillones 2021hombre pocilgaNo ratings yet
- JK BMS Bluetooth Manual: Tel/whatsapp:86-13924612941Document19 pagesJK BMS Bluetooth Manual: Tel/whatsapp:86-13924612941hombre pocilgaNo ratings yet
- CATL 271ah DatasheetDocument15 pagesCATL 271ah Datasheethombre pocilgaNo ratings yet
- CALB 100ah L160F100Document23 pagesCALB 100ah L160F100hombre pocilgaNo ratings yet