Professional Documents
Culture Documents
Avaya Port Matrix Avaya Workplace
Uploaded by
Alexandr “aat” AlCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Avaya Port Matrix Avaya Workplace
Uploaded by
Alexandr “aat” AlCopyright:
Available Formats
Avaya Port Matrix
Avaya Workplace 3.x
Avaya IX Workplace 3.x
Avaya Equinox 3.x
Avaya – Proprietary
Use pursuant to the terms of your signed agreement or Avaya policy.
January 2022 Avaya Port Matrix: Avaya Workplace 3.x 1
Comments? Infodev@avaya.com
Issue 1.7
January 12, 2022
Avaya – Proprietary
Use pursuant to the terms of your signed agreement or Avaya policy.
January 2022 Avaya Port Matrix: Avaya Workplace 3.x 2
Comments? Infodev@avaya.com
ALL INFORMATION IS BELIEVED TO BE CORRECT AT THE TIME OF
PUBLICATION AND IS PROVIDED "AS IS". AVAYA INC. DISCLAIMS ALL
WARRANTIES, EITHER EXPRESS OR IMPLIED, INCLUDING THE
WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR
PURPOSE AND FURTHERMORE, AVAYA INC. MAKES NO
REPRESENTATIONS OR WARRANTIES THAT THE INFORMATION
PROVIDED HEREIN WILL ELIMINATE SECURITY THREATS TO
CUSTOMERS’ SYSTEMS. AVAYA INC., ITS RELATED COMPANIES,
DIRECTORS, EMPLOYEES, REPRESENTATIVES, SUPPLIERS OR AGENTS
MAY NOT, UNDER ANY CIRCUMSTANCES BE HELD LIABLE FOR ANY
DIRECT, INDIRECT, SPECIAL, PUNITIVE, EXEMPLARY, INCIDENTAL OR
CONSEQUENTIAL DAMAGES ARISING OUT OF THE USE OF THE
INFORMATION PROVIDED HEREIN. THIS INCLUDES, BUT IS NOT LIMITED
TO, THE LOSS OF DATA OR LOSS OF PROFIT, EVEN IF AVAYA WAS
ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. YOUR USE OF THIS
INFORMATION CONSTITUTES ACCEPTANCE OF THESE TERMS.
© 2022 Avaya Inc. All Rights Reserved. All trademarks identified by the
® or ™ are registered trademarks or trademarks, respectively, of Avaya
Inc. All other trademarks are the property of their respective owners.
Avaya – Proprietary
Use pursuant to the terms of your signed agreement or Avaya policy.
January 2022 Avaya Port Matrix: Avaya Workplace 3.x 3
Comments? Infodev@avaya.com
1. Avaya IX Workplace Components
Avaya Workplace client is a rebranding of the Avaya IX Workplace which is in-turn rebranding of Avaya Equinox
client. In context of this document, references to Avaya Equinox or Avaya IX Workplace shall be treated as
synonymous with Workplace.
Avaya Workplace client is a high-performance enterprise collaboration tool for office and mobile employees.
Avaya Workplace provides access to multiple modalities such as IM/presence, text and multimedia messaging,
multi-party audio/video, and content sharing to give users real choice in how to connect and engage with other
people and groups.
Avaya Workplace offers a single contemporary user experience across platforms and devices including
desktops, smartphones and tablets.
When deploying Avaya Workplace in a Virtual Desktop environment, it is necessary to follow the firewall rules
pursuant to the Virtual Desktop provider specifications.
Supplemental Port Matrix information for Avaya Equinox Meetings Online can be found at:
https://support.avaya.com/public/index?page=content&id=FAQ115069
Supplemental Port Matrix information for Avaya Equinox with IP Office solutions can be found at:
https://downloads.avaya.com/css/P8/documents/101054165
2. Port Usage Tables
2.1 Port Usage Table Heading Definitions
Source System: System name or type that initiate connection requests.
Source Port: This is the default layer-4 port number of the connection source. Valid values include: 0 – 65535.
A “(C)” next to the port number means that the port number is configurable.
Destination System: System name or type that receives connection requests.
Destination Port: This is the default layer-4 port number to which the connection request is sent. Valid values
include: 0 – 65535. A “(C)” next to the port number means that the port number is configurable.
Transport/Application Protocol: This is the name associated with the layer-4 protocol higher level
application protocols.
Optionally Enabled / Disabled: This field indicates whether customers can enable or d
ab
is
lea layer-4 port by
changing its default port state setting. Valid values include: Yes or No
“No” means the default port state cannot be changed (e.g. enable or disabled).
“Yes” means the default port state can be changed and that the port can either be enabled or disabled.
Default Port State: A port is either open,closed or filte
rd
.
Open ports will respond to queries
Avaya – Proprietary
Use pursuant to the terms of your signed agreement or Avaya policy.
January 2022 Avaya Port Matrix: Avaya Workplace 3.x 4
Comments? Infodev@avaya.com
Closed ports may or may not respond to queries and are only listed when they can be optionally enabled.
Filtered ports can be open or closed. Filtered UDP ports will not respond to queries. Filtered TCP will respond to
queries but will not allow connectivity.
Avaya – Proprietary
Use pursuant to the terms of your signed agreement or Avaya policy.
January 2022 Avaya Port Matrix: Avaya Workplace 3.x 5
Comments? Infodev@avaya.com
2.2 Port Tables
Below are the tables which document the port usage for this product.
Source Destination
Transport / Optionally Default
Port Port Application Enabled / Port
State Description
System (Configurable System (Configurable Protocol Disabled?
Range) Range)
Avaya Ephemeral HTTP servers used 80 TCP/HTTP No Closed File downloads
Equinox, (1024 – to support Auto- for service
Windows, 65535) configuration, discovery, PPM
macOS, iOS, Personal Profile
Android Manager
Avaya Ephemeral HTTP servers used 443 TLS/HTTPS No Closed File downloads
Equinox, (1024 – to support Auto- for service
Windows, 65535) configuration, discovery, PPM,
macOS, iOS, Personal Profile AADS
Android Manager
Avaya Ephemeral Client Enablement 7777 TLS/ Yes Closed Messaging
Equinox iOS, (1024 – Services (1024-65535) (Proprietary) between Avaya
Android 65535) Equinox and the
Client
Enablement
Services. 7777
is the default
port on the CES
server, however
confirm with the
CES system
administrator
that this is the
port in use for
your
deployment
Avaya Ephemeral Avaya Session 5060 TCP/SIP Yes Closed SIP signaling
Equinox, (1024 – Manager (SM) (1024-65535) traffic
Windows, 65535)
macOS, iOS,
Android
Avaya Ephemeral Avaya Session 5061 TLS/SIPS Yes Closed SIP signaling
Equinox, (1024 – Manager (SM) (1024-65535) traffic
Windows, 65535)
macOS, iOS,
Android
Avaya Ephemeral Avaya Session 3478 TCP/STUN No Closed STUN/TURN
Equinox, (1024 – Border Controller TCP/TURN Nat Traversal
Windows, 65535)
macOS, iOS,
Android
Avaya Ephemeral Avaya Session 5349 TLS/STUN No Closed STUN/TURN
Equinox, (1024 – Border Controller TLS/TURN Nat Traversal
Windows, 65535)
macOS, iOS,
Android
Avaya – Proprietary
Use pursuant to the terms of your signed agreement or Avaya policy.
January 2022 Avaya Port Matrix: Avaya Workplace 3.x 6
Comments? Infodev@avaya.com
Avaya Default range Media Gateway, 1024-65535 UDP/RTP, No Closed Media traffic
Equinox, is (5004 - Conferencing UDP/RTCP, (audio/video) for
Windows, 5203) Server, Application UDP/SRTP, SIP calls. The
macOS, iOS, Available Server, Desk Phone, UDP/SRTCP destination port
Android range is Soft Client, Avaya range listed in
Session Border this document
(1024 – Controller (1024-65535)
65535) highlights that
the actual
destination port
for media traffic
for any call is
dependent on
the destination
of the call and
negotiated in
real-time during
call setup. It is
not possible to
provide the
specific list of
ports that will be
negotiated for
all possible call
destinations in
this document
Avaya Ephemeral LDAP Server 389 TCP No Closed Enterprise
Equinox, (1024 – Directory
Windows, 65535) Contact Lookup
macOS
Avaya Ephemeral LDAP Server 636 TLS No Closed Enterprise
Equinox, (1024 – Directory
Windows, 65535) Contact Lookup
macOS
Media Ephemeral Avaya Equinox 1024-65535 UDP/RTP, No Closed Media traffic
Gateway, (1024 – UDP/RTCP, (audio/video) for
Conferencing 65535) UDP/SRTP, SIP calls. The
Server, UDP/SRTCP destination port
Application range listed in
Server, Desk this document
Phone, Soft (1024-65535)
Client highlights that
the actual
destination port
for media traffic
for any call is
dependent on
the destination
of the call and
negotiated in
real-time during
call setup. It is
not possible to
provide the
specific list of
ports that will be
negotiated for
all possible call
destinations in
this document
Equinox, Ephemeral Avaya Multimedia 443 TLS/HTTPS Yes Closed Messaging
Windows, Messaging server (1024-65535) traffic.
Avaya – Proprietary
Use pursuant to the terms of your signed agreement or Avaya policy.
January 2022 Avaya Port Matrix: Avaya Workplace 3.x 7
Comments? Infodev@avaya.com
macOS, iOS, (1024 –
Android 65535)
Equinox, Ephemeral DNS Servers 53 UDP/DNS No Closed Domain
Windows, (1024 – lookups, service
macOS, iOS, 65535) discovery
Android
Equinox, Ephemeral analytics.google.com 443 TCP/HTTPS Yes Closed Google
Windows, (1024 – Analytics
macOS, iOS, 65535)
Android
Avaya – Proprietary
Use pursuant to the terms of your signed agreement or Avaya policy.
January 2022 Avaya Port Matrix: Avaya Workplace 3.x 8
Comments? Infodev@avaya.com
2.3 Port table changes from Avaya Communicator 2.1 to Avaya Equinox 3.0
Port Changes from Avaya Communicator 2.1 to Avaya Equinox 3.0
Source Destination Network / Optionally Default
Port Port Application Enabled / Port
State Description
System (Configurable System (Configurable Protocol Disabled?
Range) Range)
Avaya Ephemeral Avaya Aura 443 TLS/HTTPS No Closed Device services e.g. Add,
Equinox, Device Remove, Search AADS
Windows, Services Contacts and file
macOS, downloads for service
iOS, discovery
Android
Avaya Ephemeral Avaya Aura 80 TCP/HTTP No Closed Web collaboration
Equinox, Web
Windows, Collaboration
macOS,
iOS,
Android
Avaya Ephemeral Avaya Aura 443 TLS/HTTPS No Closed Web collaboration
Equinox, Web Web
Windows, Collaboration Sockets
macOS,
iOS,
Android
Avaya Ephemeral Equinox 443 TLS/HTTPS No Closed Unified Conference
Equinox, Conferencing Control Server (equinox
Windows, Unified conferencing)
macOS, Conference
iOS, Control
Android
Avaya Ephemeral BFCP Peer 2070-2080 TCP/BFCP Yes Closed Binary Floor Control
Equinox, Protocol for sharing video
macOS
Avaya Ephemeral BFCP Peer 1024 -65503 UDP/BFCP Yes Closed Binary Floor Control
Equinox, Protocol for sharing video
macOS
Avaya – Proprietary
Use pursuant to the terms of your signed agreement or Avaya policy.
January 2022 Avaya Port Matrix: Avaya Workplace 3.x 9
Comments? Infodev@avaya.com
2.4 Port table changes from Avaya Equinox 3.0 to Avaya Equinox 3.1
Port Changes from Avaya Equinox 3.0 to Avaya Equinox 3.1
Source Destination Network / Optionally Default
Port Port Application Enabled / Port
State Description
System (Configurable System (Configurable Protocol Disabled?
Range) Range)
Avaya Ephemeral Microsoft 443 TCP/HTTPS No Closed Calendar meetings through
Equinox, Exchange Microsoft Exchange Web
macOS, Services (EWS)
iOS,
Android
2.5 Port table changes from Avaya Equinox 3.1 to Avaya Equinox 3.2
Port Changes from Avaya Equinox 3.1 to Avaya Equinox 3.2
Source Destination Network / Optionally Default
Port Port Application Enabled / Port
State Description
System (Configurable System (Configurable Protocol Disabled?
Range) Range)
Avaya Ephemeral Web Server 80 TCP/HTTP No Closed File downloads for
Equinox, to support Configuration
Windows, configuration
macOS, file.
iOS,
Android
Avaya Ephemeral Web Server 443 TLS/HTTPS No Closed File downloads for
Equinox, to support Configuration
Windows, configuration
macOS, file.
iOS,
Android
Avaya – Proprietary
Use pursuant to the terms of your signed agreement or Avaya policy.
January 2022 Avaya Port Matrix: Avaya Workplace 3.x 10
Comments? Infodev@avaya.com
Source Destination Network / Optionally Default
Port Port Application Enabled / Port
State Description
System (Configurable System (Configurable Protocol Disabled?
Range) Range)
Avaya Ephemeral Web 443 TLS/HTTPS No Closed Simple Certificate Enrollment
Equinox, Server to Protocol for certificate
Windows, support distribution.
macOS, SCEP
iOS,
Android
Avaya Ephemeral Web 80 TCP/HTTP No Closed Simple Certificate Enrollment
Equinox, Server to Protocol for certificate
Windows, support distribution.
macOS, SCEP
iOS,
Android
Avaya Ephemeral Avaya 443 HTTPS No Closed Media tunneled over HTTPS.
Equinox, Session
Windows, Border
macOS, Controller.
iOS,
Android
Avaya – Proprietary
Use pursuant to the terms of your signed agreement or Avaya policy.
January 2022 Avaya Port Matrix: Avaya Workplace 3.x 11
Comments? Infodev@avaya.com
2.6 Port table changes from Avaya Equinox 3.2 to Avaya Equinox 3.3
Port Changes from Avaya Equinox 3.2 to Avaya Equinox 3.3
Source Destination Network / Optionally Default
Port Port Application Enabled / Port
State Description
System (Configurable System (Configurable Protocol Disabled?
Range) Range)
Avaya Equinox, Ephemeral Web Server 443 TLS/HTTPS No Closed File downloads for
Windows, (1024 – to support Configuration
macOS, iOS, 65535) configuration
Android file.
Avaya Equinox, Ephemeral Web Server 443 TLS/HTTPS No Closed Simple Certificate
Windows, (1024 – to support Enrollment Protocol
macOS, iOS, 65535) SCEP for certificate
Android distribution.
Communication Ephemeral Avaya Aura 443 TLS/HTTPS No Closed HTTP to SIP
Services (1024 – Web Web Gateway supporting
Package 65535) Gateway Sockets WebRTC
Server-Sent Support for Apple
Events Push Notifications.
Avaya – Proprietary
Use pursuant to the terms of your signed agreement or Avaya policy.
January 2022 Avaya Port Matrix: Avaya Workplace 3.x 12
Comments? Infodev@avaya.com
2.7 Port table changes from Avaya Equinox 3.3 to Avaya Equinox 3.4
Port Changes from Avaya Equinox 3.3 to Avaya Equinox 3.4
Source Destination Network / Optionally Default
Port Port Application Enabled / Port
State Description
System (Configurable System (Configurable Protocol Disabled?
Range) Range)
Avaya Ephemeral Accounts.zang.io 443 TLS/HTTPS Yes Closed Avaya Cloud
Equinox, (1024 – account login
Windows, 65535)
macOS,
iOS,
Android
Avaya Ephemeral Spaces.zang.io 443 TLS/HTTPS Yes Closed Avaya Spaces API
Equinox, (1024 – Spacesapi.zang.io servers
Windows, 65535)
macOS,
iOS,
Android
Avaya Ephemeral IP Office SIP 5060 TCP/SIP Yes Closed SIP signaling traffic
Equinox, (1024 – server (1024 –
Windows, 65535) 65535)
macOS,
iOS,
Android
Avaya Ephemeral IP Office SIP 5061 TLS/SIPS Yes Closed SIP signaling traffic
Equinox, (1024 – server (1024 –
Windows, 65535) 65535)
macOS,
iOS,
Android
Avaya Ephemeral HTTP Proxy Ephemeral HTTP No Closed Proxy Configuration
Equinox, (1024 – (1024 – usage determined by
Windows, 65535) 65535) configuration. Proxy
macOS, configuration
iOS, retrieved from
Android Operating System.
Avaya Ephemeral HTTP Proxy Ephemeral HTTPS No Closed Proxy Configuration
Equinox, (1024 – (1024 – usage determined by
Windows, 65535) 65535) configuration. Proxy
macOS, configuration
iOS, retrieved from
Android Operating System.
Avaya Ephemeral IP Office HTTP 443 HTTPS Yes Closed HTTP contacts and
Equinox, (1024 – server (1024 – presence traffic
Windows, 65535) 65535)
macOS,
iOS,
Android
Avaya – Proprietary
Use pursuant to the terms of your signed agreement or Avaya policy.
January 2022 Avaya Port Matrix: Avaya Workplace 3.x 13
Comments? Infodev@avaya.com
2.8 Port table changes from Avaya Equinox 3.4 to Avaya Equinox 3.4.8
Source Destination Network / Optionally Default
Port Port Application Enabled / Port
State Description
System (Configurable System (Configurable Protocol Disabled?
Range) Range)
Avaya Ephemeral Apple Push 5223,2195,2196, TLS/HTTPS Yes Closed Apple Push Notifications.
Equinox (1024 – Notifications 2197,443 For Apple guidance see:
iOS 65535) https://support.apple.com/en-
us/HT203609
Avaya Ephemeral Google 5228, 5229, TLS/HTTPS Yes Closed Google Firebase Notifications. For
Equinox (1024 – Firebase 5230 Google guidance see
iOS, 65535) Notifications https://firebase.google.com/docs/cloud-
Android messaging/concept-options
2.9 Port table changes from Avaya Equinox 3.4.8 to Avaya Equinox 3.6
Source Destination Network / Optionally Default
Port Port Application Enabled / Port
State Description
System (Configurable System (Configurable Protocol Disabled?
Range) Range)
Avaya Ephemeral Identity 443 TLS/HTTPS No Closed AADS O-Auth services
Equinox (1024 – Provider supports redirection to a third-
65535) party identity server.
Network Control to the Identity
Provider is via AADS O-Auth
provisioning.
Avaya Ephemeral Avaya 8443 TLS/HTTPS No Closed For O-Auth deployments
Equinox, Aura where Key cloak is deployed
Windows, Device on AADS, the AADS service
macOS, Services may redirect Equinox clients to
iOS, another server port.
Android
Avaya – Proprietary
Use pursuant to the terms of your signed agreement or Avaya policy.
January 2022 Avaya Port Matrix: Avaya Workplace 3.x 14
Comments? Infodev@avaya.com
2.10 Port table changes from Avaya Equinox 3.6 to Avaya IX Workplace 3.7
Source Destination Network / Optionally Default
Port Port Application Enabled / Port
State Description
System (Configurable System (Configurable Protocol Disabled?
Range) Range)
Equinox, Ephemeral https://avayaucclient.firebaseio.com 443 TCP/HTTPS Yes Closed Firebase
Windows, (1024 – Analytics
macOS, 65535)
iOS,
Android
2.11 Port table changes from Avaya IX Workplace 3.7 to Avaya IX Workplace 3.8.2
Source Destination Network / Optionally Default
Port Port Application Enabled / Port
State Description
System (Configurable System (Configurable Protocol Disabled?
Range) Range)
Avaya IX Ephemeral Accounts.avayacloud.com 443 TLS/HTTPS Yes Closed Avaya
Workplace, (1024 – Cloud
Windows, 65535) account
macOS, login
iOS,
Android
Avaya IX Ephemeral Spaces.avayacloud.com 443 TLS/HTTPS Yes Closed Avaya
Workplace, (1024 – Spacesapi.avayacloud.com Spaces API
Windows, 65535) server
macOS,
iOS,
Android
2.12 Port table changes from Avaya IX Workplace 3.11 to Avaya Workplace 3.12
Source Destination Network / Optionally Default
Port Port Application Enabled / Port
State Description
System (Configurable System (Configurable Protocol Disabled?
Range) Range)
Avaya Ephemeral asistant.apps.avaya.com 443 HTTPS Yes Closed Avaya
Assistant (1024 – Assistant
(for 65535) (for
Microsoft Microsoft
Teams) Teams)
Avaya – Proprietary
Use pursuant to the terms of your signed agreement or Avaya policy.
January 2022 Avaya Port Matrix: Avaya Workplace 3.x 15
Comments? Infodev@avaya.com
2.13 Port table changes from Avaya Workplace 3.13 to Avaya Workplace 3.14
Source Destination Network / Optionally Default
Port Port Application Enabled / Port
State Description
System (Configurable System (Configurable Protocol Disabled?
Range) Range)
Avaya Call Ephemeral callassist.avayacloud.com 443 HTTPS Yes Closed Avaya Call
(for (1024 –
Microsoft 65535)
Teams)
Avaya Call Ephemeral Avaya Aura Device 443 HTTPS Yes Closed Device
(for (1024 – Services (AADS) services.
Microsoft 65535) Eg.: Add,
Teams) Remove and
configuration
downloads
for service
discovery
Avaya Call Ephemeral Office365 443 HTTPS Yes Closed Office 365
(for (1024 – Contact
Microsoft 65535) retrieval
Teams)
2.14 Port table changes from Avaya Workplace 3.14 to Avaya Workplace 3.16
Source Destination Network / Optionally Default
Port Port Application Enabled / Port
State Description
System (Configurable System (Configurable Protocol Disabled?
Range) Range)
Avaya Ephemeral appanalytics.avaya.com 443 HTTPS Yes Closed Avaya
Workplace (1024 – Analytics
for 65535)
Windows
2.15 Port table changes from Avaya Workplace 3.18 to Avaya Workplace 3.19
Source Destination Network / Optionally Default
Port Port Application Enabled / Port
State Description
System (Configurable System (Configurable Protocol Disabled?
Range) Range)
Avaya Ephemeral www.googleapis.com 443 HTTPS Yes Closed Google
Workplace (1024 – Calendar
for 65535)
Windows
Avaya – Proprietary
Use pursuant to the terms of your signed agreement or Avaya policy.
January 2022 Avaya Port Matrix: Avaya Workplace 3.x 16
Comments? Infodev@avaya.com
2.16 Port table changes from Avaya Workplace 3.19 to Avaya Workplace 3.20
Source Destination Network / Optionally Default
Port Port Application Enabled / Port
State Description
System (Configurable System (Configurable Protocol Disabled?
Range) Range)
Avaya Ephemeral WebLM Licensing Server 443 HTTPS Yes Closed WebLM
Workplace (1024 – Licensing
for 65535)
Windows
2.17 Port table changes from Avaya Workplace 3.21 to Avaya Workplace 3.24
Source Destination Network / Optionally Default
Port Port Application Enabled / Port
State Description
System (Configurable System (Configurable Protocol Disabled?
Range) Range)
Avaya Ephemeral IX 443 HTTPS Yes Closed IX Messaging Server (Officelinx)
Workplace (1024 – Messaging
65535) Server
Avaya Ephemeral Google 5228, 5229, TLS/HTTPS Yes Closed Google Firebase Notifications.
Workplace (1024 – Firebase 5230
for 65535) Notifications
Android
Avaya – Proprietary
Use pursuant to the terms of your signed agreement or Avaya policy.
January 2022 Avaya Port Matrix: Avaya Workplace 3.x 17
Comments? Infodev@avaya.com
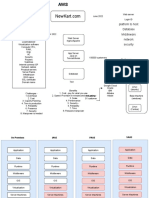
3. Port Usage Diagram
Avaya – Proprietary
Use pursuant to the terms of your signed agreement or Avaya policy.
January 2022 Avaya Port Matrix: Avaya Workplace 3.x 18
Comments? Infodev@avaya.com
A: Overview of TCP/IP Ports
What are ports and how are they used?
TCP and UDP use ports (defined at http://www.iana.org/assignments/port-numbers) to route traffic
arriving at a particular IP device to the correct upper layer application. These ports are logical descriptors
(numbers) that help devices multiplex and de-multiplex information streams. Consider your desktop PC.
Multiple applications may be simultaneously receiving information. In this example, email may use
destination TCP port 25, a browser may use destination TCP port 80 and a telnet session may use
destination TCP port 23. These logical ports allow the PC to de-multiplex a single incoming serial data
packet stream into three mini-streams inside the PC. Furthermore, each of the mini-streams is directed to
the correct high-level application because the port numbers identify which application each data mini-
stream belongs. Every IP device has incoming (Ingress) and outgoing (Egress) data streams.
Ports are used in TCP and UDP to name the ends of logical connections which carry data flows. TCP
and UDP streams have an IP address and port number for both source and destination IP devices. The
pairing of an IP address and a port number is called a socket (discussed later). Therefore, each data
stream is uniquely identified with two sockets. Source and destination sockets must be known by the
source before a data stream can be sent to the destination. Some destination ports are “open” to receive
data streams and are called “listening” ports. Listening ports actively wait for a source (client) to make
contact to a destination (server) using a specific port that has a known protocol associate with that port
number. HTTPS, as an example, is assigned port number 443. When a destination IP device is
contacted by a source device using port 443, the destination uses the HTTPS protocol for that data
stream conversation.
Port Type Ranges
Port numbers are divided into three ranges: Well Known Ports, Registered Ports, and Dynamic Ports
(sometimes called Private Ports).
Well Known Ports are those numbered from 0 through 1023.
Registered Ports are those numbered from 1024 through 49151
Dynamic Ports are those numbered from 49152 through 65535
The Well Known and Registered ports are assigned by IANA (Internet Assigned Numbers Authority) and
are found here: http://www.iana.org/assignments/port-numbers.
Well Known Ports
For the purpose of providing services to unknown clients, a service listen port is defined. This port is
used by the server process as its listen port. Common services often use listen ports in the well-known
port range. A well-known port is normally active meaning that it is “listening” for any traffic destined for a
specific application. For example, well known port 23 on a server is actively waiting for a data source to
contact the server IP address using this port number to establish a Telnet session. Well known port 25 is
waiting for an email session, etc. These ports are tied to a well understood application and range from 0
to 1023.
In UNIX and Linux operating systems, only root may open or close a well-known port. Well Known Ports
are also commonly referred to as “privileged ports”.
Registered Ports
Avaya – Proprietary
Use pursuant to the terms of your signed agreement or Avaya policy.
January 2022 Avaya Port Matrix: Avaya Workplace 3.x 19
Comments? Infodev@avaya.com
Unlike well-known ports, these ports are not restricted to the root user. Less common services register
ports in this range. Avaya uses ports in this range for call control. Some, but not all, ports used by Avaya
in this range include: 1719/1720 for H.323, 5060/5061 for SIP, 2944 for H.248 and others. The registered
port range is 1024 – 49151. Even though a port is registered with an application name, industry often
uses these ports for different applications. Conflicts can occur in an enterprise when a port with one
meaning is used by two servers with different meanings.
Dynamic Ports
Dynamic ports, sometimes called “private ports”, are available to use for any general purpose. This
means there are no meanings associated with these ports (similar to RFC 1918 IP Address Usage).
These are the safest ports to use because no application types are linked to these ports. The dynamic
port range is 49152 – 65535.
Avaya – Proprietary
Use pursuant to the terms of your signed agreement or Avaya policy.
January 2022 Avaya Port Matrix: Avaya Workplace 3.x 20
Comments? Infodev@avaya.com
Sockets
A socket is the pairing of an IP address with a port number. An example would be 192.168.5.17:3009,
where 3009 is the socket number associated with the IP address. A data flow, or conversation, requires
two sockets – one at the source device and one at the destination device. The data flow then has two
sockets with a total of four logical elements. Each data flow must be unique. If one of the four elements
is unique, the data flow is unique. The following three data flows are uniquely identified by socket number
and/or IP address.
Data Flow 1: 172.16.16.14:1234 - 10.1.2.3:2345
Data Flow 2: 172.16.16.14.1235 - 10.1.2.3:2345
Data Flow 3: 172.16.16.14:1234 - 10.1.2.4:2345
Data flow 1 has two different port numbers and two different IP addresses and is a valid and typical
socket pair.
Data flow 2 has the same IP addresses and the same port number on the second IP address as data flow
1, but since the port number on the first socket differs, the data flow is unique.
Therefore, if one IP address octet changes, or one port number changes, the data flow is unique.
Figure 1, below, is an example showing ingress and egress data flows from a PC to a web server.
Socket Example Diagram
Client HTTP-Get Source 192.168.1.10:1369 Destination 10.10.10.47:80 Web Server
TCP-info Destination 192.168.1.10:1369 Source 10.10.10.47:80
Figure 1. Socket Example
Notice the client egress stream includes the client’s source IP and socket (1369) and the
destination IP and socket (80). The ingress stream has the source and destination information
reversed because the ingress is coming from the server.
Avaya – Proprietary
Use pursuant to the terms of your signed agreement or Avaya policy.
January 2022 Avaya Port Matrix: Avaya Workplace 3.x 21
Comments? Infodev@avaya.com
Understanding Firewall Types and Policy Creation
Firewall Types
There are three basic firewall types:
• Packet Filtering
• Application Level Gateways (Proxy Servers)
• Hybrid (Stateful Inspection)
Packet Filtering is the most basic form of the firewalls. Each packet that arrives or leaves the network has
its header fields examined against criterion to either drop the packet or let it through. Routers configured
with Access Control Lists (ACL) use packet filtering. An example of packet filtering is preventing any
source device on the Engineering subnet to telnet into any device in the Accounting subnet.
Application level gateways (ALG) act as a proxy, preventing a direct connection between the foreign
device and the internal destination device. ALGs filter each individual packet rather than blindly copying
bytes. ALGs can also send alerts via email, alarms or other methods and keep log files to track
significant events.
Hybrid firewalls are dynamic systems, tracking each connection traversing all interfaces of the firewall and
making sure they are valid. In addition to looking at headers, the content of the packet, up through the
application layer, is examined. A stateful inspection firewall also monitors the state of the connection and
compiles the information in a state table. Stateful inspection firewalls close off ports until the connection
to the specific port is requested. This is an enhancement to security against port scanning i.
Firewall Policies
The goals of firewall policies are to monitor, authorize and log data flows and events. They also restrict
access using IP addresses, port numbers and application types and sub-types.
This paper is focused with identifying the port numbers used by Avaya products so effective firewall
policies can be created without disrupting business communications or opening unnecessary access into
the network.
Knowing that the source column in the following matrices is the socket initiator is key in building some
types of firewall policies. Some firewalls can be configured to automatically create a return path through
the firewall if the initiating source is allowed through. This option removes the need to enter two firewall
rules, one for each stream direction, but can also raise security concerns.
Another feature of some firewalls is to create an umbrella policy that allows access for many independent
data flows using a common higher layer attribute. Finally, many firewall policies can be avoided by
placing endpoints and the servers that serve those endpoints in the same firewall zone.
iThe act of systematically scanning a computer's ports. Since a port is a place where information goes
into and out of a computer, port scanning identifies open doors to a computer. Port scanning has
legitimate uses in managing networks, but port scanning also can be malicious in nature if someone is
looking for a weakened access point to break into your computer.
Avaya – Proprietary
Use pursuant to the terms of your signed agreement or Avaya policy.
January 2022 Avaya Port Matrix: Avaya Workplace 3.x 22
Comments? Infodev@avaya.com
You might also like
- Equinox Port-MatrixDocument10 pagesEquinox Port-MatrixDanielNo ratings yet
- Avaya Port Matrix: Avaya Aura Media Server 7.7Document16 pagesAvaya Port Matrix: Avaya Aura Media Server 7.7AshishNo ratings yet
- C - CURE 9000 and iSTAR: Port AssignmentsDocument21 pagesC - CURE 9000 and iSTAR: Port AssignmentsRider hoyos fangNo ratings yet
- Ccure 9000 Istar PortDocument20 pagesCcure 9000 Istar PortLuis Tarott100% (1)
- CC9K v2 90 Ports GD 8200 1950 42 A0 enDocument19 pagesCC9K v2 90 Ports GD 8200 1950 42 A0 enAntonio MouraNo ratings yet
- Avaya Equinox For MAC: Limited VOIPDocument1 pageAvaya Equinox For MAC: Limited VOIPnuevo celularNo ratings yet
- Deployment Guide-Dell Wyse VworkspaceDocument20 pagesDeployment Guide-Dell Wyse VworkspaceCromNo ratings yet
- Ports CCURE9000 V2.8Document21 pagesPorts CCURE9000 V2.8MoisesManuelBravoLeonNo ratings yet
- Avaya Call Reporting: 4.2 CapacitaciónDocument25 pagesAvaya Call Reporting: 4.2 CapacitaciónMartin MottaNo ratings yet
- AAM7 2PortMatrixr1Document16 pagesAAM7 2PortMatrixr1Ashish100% (1)
- DG APV BlackboardDocument23 pagesDG APV BlackboardnorazlisamNo ratings yet
- IP Office Edition Release 5.0 SIP Trunking Configuration GuideDocument14 pagesIP Office Edition Release 5.0 SIP Trunking Configuration GuideAllu RinmexicoNo ratings yet
- Avaya Session Border Controller For Enterprise 7.1 SP11 Release NotesDocument14 pagesAvaya Session Border Controller For Enterprise 7.1 SP11 Release NotesDaniel SepulvedaNo ratings yet
- Avaya Port MatrixDocument22 pagesAvaya Port MatrixAshishNo ratings yet
- Dot1x Feasibility StudyDocument22 pagesDot1x Feasibility StudyGary FreemanNo ratings yet
- AVAYA Verint ACM SODocument28 pagesAVAYA Verint ACM SOroberszrNo ratings yet
- OTS Solution Document WiFi v08082023Document30 pagesOTS Solution Document WiFi v08082023RamaJeyam RNo ratings yet
- ASBCE PortMatrix 6.3Document14 pagesASBCE PortMatrix 6.3Juan Pablo Torres FerradaNo ratings yet
- SystemPlatform System and Procedure OverviewDocument59 pagesSystemPlatform System and Procedure Overviewcrojasmo44No ratings yet
- Cloud Training Exa Cs OverviewDocument48 pagesCloud Training Exa Cs Overviewambipac@yahoo.comNo ratings yet
- Witness AES AnDocument43 pagesWitness AES Ansaud80No ratings yet
- Via Remote Access Solution GuideDocument25 pagesVia Remote Access Solution GuideRoan VillalobosNo ratings yet
- Avaya IP Office Contact Center OverviewDocument35 pagesAvaya IP Office Contact Center OverviewMarthaGutnaraNo ratings yet
- Oracle CloudDocument34 pagesOracle Cloudlakshmi narayanaNo ratings yet
- SI6 UserGuide InventoryServerDocument56 pagesSI6 UserGuide InventoryServermat wueNo ratings yet
- Advanced Troubleshooting and Update - Edition 15 DT00XTE278Document483 pagesAdvanced Troubleshooting and Update - Edition 15 DT00XTE278sidney SantiagoNo ratings yet
- Call Reporting Installation GuideDocument18 pagesCall Reporting Installation GuideSophorn TyNo ratings yet
- Avaya Call Management System Release 13 Platform Upgrade and Data MigrationDocument82 pagesAvaya Call Management System Release 13 Platform Upgrade and Data MigrationAsnake TegenawNo ratings yet
- Logging Into AADSDocument4 pagesLogging Into AADSpawarsanjuNo ratings yet
- 2018 - Avaya Call Reporting Installation Guide - Final V2Document18 pages2018 - Avaya Call Reporting Installation Guide - Final V2ursus006No ratings yet
- Avaya B5800 Branch Gateway Professional Services Offer V1Document9 pagesAvaya B5800 Branch Gateway Professional Services Offer V1Fabio Luis BraceiroNo ratings yet
- Alu Asm61 CS1KDocument47 pagesAlu Asm61 CS1KAdrian KumarNo ratings yet
- Telefonica - WAN OptimizationDocument22 pagesTelefonica - WAN OptimizationSandro R. S. MacielNo ratings yet
- SECS05L04_Configuring Cisco IOS Firewall Authentication ProxyDocument25 pagesSECS05L04_Configuring Cisco IOS Firewall Authentication ProxyKhoa Huynh DangNo ratings yet
- Hosted FAS Expert Service BrochureDocument6 pagesHosted FAS Expert Service Brochure101183No ratings yet
- IVI 2548 Appliance Series OsDocument6 pagesIVI 2548 Appliance Series OsBonni Al AminNo ratings yet
- High Availability Server Implementation Using NGINX, Keepalived, and Varnish To Ease Web Server AccessDocument6 pagesHigh Availability Server Implementation Using NGINX, Keepalived, and Varnish To Ease Web Server AccessBouslah YasserNo ratings yet
- Security Hardening Guidelines: Vmware Sd-Wan by VelocloudDocument7 pagesSecurity Hardening Guidelines: Vmware Sd-Wan by VelocloudCCIE DetectNo ratings yet
- Cisco ASA 5520Document47 pagesCisco ASA 5520sayritabelenNo ratings yet
- Interoperability Report: Alcatel-Lucent OT8118/8128 Aerohive Networks, AP120, 121, 141, 330 and 350Document22 pagesInteroperability Report: Alcatel-Lucent OT8118/8128 Aerohive Networks, AP120, 121, 141, 330 and 350Mohamed SalhiNo ratings yet
- HCL AppScan Enterprise v9.0.3.14 Used PortsDocument3 pagesHCL AppScan Enterprise v9.0.3.14 Used PortsGulliber R. CairoNo ratings yet
- Vmware Vcloud Requirement 11q1 White PaperDocument8 pagesVmware Vcloud Requirement 11q1 White Paperhassan mahmoodNo ratings yet
- CXW02 - Dynamic Segmentation - Lab GuideDocument55 pagesCXW02 - Dynamic Segmentation - Lab Guidetest testNo ratings yet
- OTBI Enterprise For HCM: Security OverviewDocument37 pagesOTBI Enterprise For HCM: Security OverviewupmuthukumarmcomNo ratings yet
- Dot1x Cisco 96xDocument31 pagesDot1x Cisco 96xaliveli85No ratings yet
- Switch Alcatel 9700Document6 pagesSwitch Alcatel 9700pepa bemeNo ratings yet
- Ims 4Document30 pagesIms 4Alessandro PazNo ratings yet
- Avaya NMS Vision SIP AppNotesDocument36 pagesAvaya NMS Vision SIP AppNotesgaborkNo ratings yet
- Brochure AVEVA PlantSCADA AccessAnywhere 21-12Document3 pagesBrochure AVEVA PlantSCADA AccessAnywhere 21-12rahilgalaxyNo ratings yet
- Avaya Call Management System: Release 12 LAN Backup User GuideDocument94 pagesAvaya Call Management System: Release 12 LAN Backup User GuideRoberto MontagnanaNo ratings yet
- 8021x DynamicVlanAssignmentDocument43 pages8021x DynamicVlanAssignmentBarisNo ratings yet
- IPOfficePort Matrix 11 0 4Document31 pagesIPOfficePort Matrix 11 0 4Darwin VanegasNo ratings yet
- IP Agent Configuration in CMDocument23 pagesIP Agent Configuration in CMSaud HussainNo ratings yet
- Impact AACC62 PDFDocument78 pagesImpact AACC62 PDFShobhit TiwariNo ratings yet
- Test 5Document2 pagesTest 5rafiki.gameiroNo ratings yet
- AppWall Implementation Plan V10 AppWall Verion 5 6Document7 pagesAppWall Implementation Plan V10 AppWall Verion 5 6Juan Pablo Guerrero CuevaNo ratings yet
- Axway CORP Deck - 042123Document22 pagesAxway CORP Deck - 042123Mohd Aljafree AliasNo ratings yet
- Configuration of Microsoft ISA Proxy Server and Linux Squid Proxy ServerFrom EverandConfiguration of Microsoft ISA Proxy Server and Linux Squid Proxy ServerNo ratings yet
- Configuration and Evaluation of Some Microsoft and Linux Proxy Servers, Security, Intrusion Detection, AntiVirus and AntiSpam ToolsFrom EverandConfiguration and Evaluation of Some Microsoft and Linux Proxy Servers, Security, Intrusion Detection, AntiVirus and AntiSpam ToolsNo ratings yet
- Cucm B Upgrade-Guide-1251su2 Chapter 01100-TasksDocument18 pagesCucm B Upgrade-Guide-1251su2 Chapter 01100-TasksFlavio AlonsoNo ratings yet
- SMB Integration Operational ModelDocument9 pagesSMB Integration Operational Modelanarki85No ratings yet
- Linux Squirrelmail Server With Dovecot: Submitted byDocument9 pagesLinux Squirrelmail Server With Dovecot: Submitted byanurag_0290No ratings yet
- DS HiT 7300 Flexi-Rate Interface Modules 74C0119Document2 pagesDS HiT 7300 Flexi-Rate Interface Modules 74C0119mp0% (1)
- CIS Oracle Linux 7 Benchmark v3.0.0Document530 pagesCIS Oracle Linux 7 Benchmark v3.0.0Julio Andres PerezNo ratings yet
- RFID Vehicle Parking SystemDocument13 pagesRFID Vehicle Parking SystemFrancis Jr CastroNo ratings yet
- GPRS Data ProtocolDocument46 pagesGPRS Data ProtocolSammy Manuel DominguezNo ratings yet
- Config SSO IBM WebSphere Portal and DominoDocument25 pagesConfig SSO IBM WebSphere Portal and DominoFernando Rodrigo DriNo ratings yet
- Basic DWDM Components.Document16 pagesBasic DWDM Components.Pradeep Kumar SahuNo ratings yet
- Optimize WiFi with inSSIDerDocument10 pagesOptimize WiFi with inSSIDerDavid E. I. GallardoNo ratings yet
- Huawei B593u 12 Lte Cpe Datasheet SpecificationsDocument26 pagesHuawei B593u 12 Lte Cpe Datasheet SpecificationsVictor HalohoNo ratings yet
- FIREEYEDocument3 pagesFIREEYEdonna.nixNo ratings yet
- RHEL 6/CentOS 6 PCI Hardening GuideDocument4 pagesRHEL 6/CentOS 6 PCI Hardening GuidettyX100% (1)
- Chapter Test Css g12Document30 pagesChapter Test Css g12flash driveNo ratings yet
- Apache MetronDocument60 pagesApache MetronMarco GuastalegnameNo ratings yet
- Moxa Mgate 5135 5435 Series Datasheet v1.0Document6 pagesMoxa Mgate 5135 5435 Series Datasheet v1.0Dewa Dewi nurulNo ratings yet
- Cisco UBR7200 Series Software Configuration GuideDocument324 pagesCisco UBR7200 Series Software Configuration GuideMiki RubirozaNo ratings yet
- Dell Networking Campus Switching and Mobility Reference Architecture 3.0Document86 pagesDell Networking Campus Switching and Mobility Reference Architecture 3.0conmar5mNo ratings yet
- Public Cloud ComparisonDocument2 pagesPublic Cloud ComparisonKailashj7No ratings yet
- Basic Cisco Ios Cli CommandsDocument4 pagesBasic Cisco Ios Cli CommandsSa MirNo ratings yet
- Kismet Wireless Network GuideDocument28 pagesKismet Wireless Network GuideArchistrage100% (1)
- Alcatel Speed Touch Pro CLI GuideDocument198 pagesAlcatel Speed Touch Pro CLI Guidescaracco100% (2)
- 1G N 2GDocument36 pages1G N 2GAnu KhareNo ratings yet
- BKACAD 70 351 Final TopologyDocument1 pageBKACAD 70 351 Final TopologyonggayNo ratings yet
- How To Bridge Private Two LANDocument41 pagesHow To Bridge Private Two LANst3liosNo ratings yet
- SAPPIO - Course Administering Microsoft Exchange Server 2016-2019Document8 pagesSAPPIO - Course Administering Microsoft Exchange Server 2016-2019Shabeer UppotungalNo ratings yet
- AbbreviationDocument35 pagesAbbreviationMuhammad Adil FarooqNo ratings yet
- ComNet CNGE2FE24MSPOE Instruction ManualDocument139 pagesComNet CNGE2FE24MSPOE Instruction ManualJMAC SupplyNo ratings yet
- Acer AT110 F2 Specifications: Product OverviewDocument11 pagesAcer AT110 F2 Specifications: Product OverviewAgung T. ApriyantoNo ratings yet
- Platform To Host Database Middleware Network Security: Data CenterDocument32 pagesPlatform To Host Database Middleware Network Security: Data CenterDinesh SehgalNo ratings yet