Professional Documents
Culture Documents
Untitled
Uploaded by
mr copy xerox0 ratings0% found this document useful (0 votes)
7 views6 pagesA rootkit is a collection of software tools that allows a threat actor to gain unauthorized access and control over a computer system. Rootkits open backdoors and hide malicious software like viruses, ransomware, and keyloggers. They work by using a dropper to initiate installation, a loader to load the rootkit into memory by exploiting a buffer overflow, and the rootkit itself. Rootkits can be difficult to detect and remove since they aim to prevent detection by antivirus software and may install at a low level like the kernel. While prevention requires keeping systems updated and using strong security tools, detection and removal may involve reinstalling the operating system.
Original Description:
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentA rootkit is a collection of software tools that allows a threat actor to gain unauthorized access and control over a computer system. Rootkits open backdoors and hide malicious software like viruses, ransomware, and keyloggers. They work by using a dropper to initiate installation, a loader to load the rootkit into memory by exploiting a buffer overflow, and the rootkit itself. Rootkits can be difficult to detect and remove since they aim to prevent detection by antivirus software and may install at a low level like the kernel. While prevention requires keeping systems updated and using strong security tools, detection and removal may involve reinstalling the operating system.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
7 views6 pagesUntitled
Uploaded by
mr copy xeroxA rootkit is a collection of software tools that allows a threat actor to gain unauthorized access and control over a computer system. Rootkits open backdoors and hide malicious software like viruses, ransomware, and keyloggers. They work by using a dropper to initiate installation, a loader to load the rootkit into memory by exploiting a buffer overflow, and the rootkit itself. Rootkits can be difficult to detect and remove since they aim to prevent detection by antivirus software and may install at a low level like the kernel. While prevention requires keeping systems updated and using strong security tools, detection and removal may involve reinstalling the operating system.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 6
What is a rootkit?
“A rootkit is a program or, more often, a collection of software tools that
gives a threat actor remote access to and control over a computer or other
system. While there have been legitimate uses for this type of software,
such as to provide remote end-user support, most rootkits open a
backdoor on victim systems to introduce malicious software, such as
viruses, ransomware, keylogger programs or other types of malware, or to
use the system for further network security attacks. Rootkits often attempt
to prevent detection of malicious software by endpoint antivirus software.”
a collection of tools used by hackers to gain administrative
privileges on compromised machines
used to help hide other forms of malware.
What does it do?
allows someone, either legitimate or malicious, to maintain
command and control over a computer system, without the
computer system user knowing about it.
owner of the rootkit can execute files and changing system
configurations on the target machine.
can access log files or monitor activity to covertly spy on the user’s
computer usage.
**there are legitimate uses for rootkits too.
How does it work?
Rootkits are just one component of what is called a blended threat.
Blended threat typically consist of three snippets of code
1. A dropper
2. Loader
3. Rootkit
The dropper is the code that gets the rootkit’s installation started.
Once initiated, the dropper launches the loader program and then
deletes itself.
The loader causes a buffer overflow, which loads the rootkit into
memory.
How blend threat get to yourcomputer?
Through social engineering
Exploiting known vulnerabilities
Even from brute forcing.
Types of rootkits
User-mode rootkits
Run on a computer with administrative privileges.
This allows to alter security and hide processes, files, system
drivers, network ports, and even system services.
These rootkits remain installed on the infected computer by copying
required files to the computer’s hard drive, automatically launching
with every system boot.
**these rootkits will be detected by the anti-malware software.
Kernel-mode rootkit
Will place the rootkit on the same level as the operating system.
OS can no longer be trusted.
One kernel-mode toolkit that’s getting lots of attention is the Da
IOS rootkit.
**windows blue screen error might be caused by these rootkits.
User-mode/kernel-mode hybrid rootkit
A hybrid rootkit that combines user-mode characteristics (easy to
use and stable) with kernel-mode characteristics (stealthy).
The hybrid approach is very successful and the most popular
rootkit currently.
Bootkit or bootloader rootkit
This type of rootkit infects the Master Boot Record of a hard drive
or other storage device connected to the target system.
Bootkits can subvert the boot process and maintain control over the
system after booting and, as a result, have been used successfully
to attack systems that use full disk encryption.
Firmware rootkit
This takes advantage of software embedded in system firmware and
installs itself in firmware images used by network cards, basic
input/output systems, routers, or other peripherals or devices.
Memory rootkit
• Most types of rootkit infections can persist in systems for long
periods because they install themselves on permanent system
storage devices, but memory rootkits load themselves into
computer memory or RAM.
• Memory rootkits persist only until the system RAM is cleared,
usually after the computer is restarted.
Virtualized rootkit
These rootkits operate as malware that executes as a hypervisor
controlling one or many virtual machines (VMs).
Rootkits operate differently in a hypervisor-VM environment than
they do on a physical machine.
In a VM environment, the VMs controlled by the master hypervisor
machine appear to function normally, without noticeable
degradation to service or performance on the VMs that are linked to
the hypervisor.
This enables the rootkit to do its malicious work with less chance of
being detected since all VMs linked to the hypervisor appear to be
functioning normally.
Tips for preventing a rootkit attack
Although it is difficult to detect a rootkit attack, an organization can
build its defense strategy in the following ways:
Use strong antivirus and antimalware software. Typically, rootkit
detection requires specific add-ons to antimalware packages or
special-purpose antirootkit scanner software.
Keep software up to date. Rootkit users continually probe OSes and
other systems for security vulnerabilities. OS and system software
vendors are aware of this, so whenever they discover vulnerabilities
to their products, they immediately issue a security update to
eliminate them. As a best practice, IT should immediately update
software whenever a new release is issued.
Monitor the network. Network monitoring and observability
software can alert IT immediately if there is an unusually high level
of activity at any point along the network, if network
nodes suddenly start going offline or if there is any other sign of
network activity that can be construed as an anomaly.
Analyzebehavior. Companies that develop strong security
permission policies and continually monitor for compliance can
reduce the threat of rootkits. For example, if a user who normally
accesses a system during the daytime in San Jose, Calif., shows up
suddenly as an active user in Europe during nighttime hours, a
threat alert could be sent to IT for investigation.
Rootkit detection and removal
Once a rootkit compromises a system, the potential for malicious
activity is high, but organizations can take steps to remediate a
compromised system.
Rootkit removal can be difficult, especially for rootkits that have been
incorporated into OS kernels, into firmware or on storage device boot
sectors. While some antirootkit software can detect and remove some
rootkits, this type of malware can be difficult to remove entirely.
One approach to rootkit removal is to reinstall the OS, which, in many
cases, eliminates the infection. Removing bootloader rootkits may
require using a clean system running a secure OS to access the infected
storage device.
Rebooting a system infected with a memory rootkit removes the
infection, but further work may be required to eliminate the source of
the infection, which may be linked to command-and-control networks
with presence in the local network or on the public internet.
https://www.adlice.com/roguekiller/
https://support.kaspersky.com/utility#TDSSKiller
https://www.bleepingcomputer.com/download/malwarebytes-anti-
rootkit/
Examples of rootkit attacks
Phishing and social engineering attacks. Rootkits can enter
computers when users open spam emails and inadvertently
download malicious software. Rootkits also use keyloggers that
capture user login information. Once installed, a rootkit can give
hackers access to sensitive user information and take control of
computer OSes.
Application rootkit attacks. Rootkits can install themselves on
commonly used applications, such as spreadsheet and word
processing software. The hackers use application rootkits to gain
access to users' information whenever they open the infected
applications.
Network and internet of things (IoT) attacks. Significant security
threats come in with IoT devices and edge computing that lack the
security measures other systems and centralized computers have.
Hackers find and exploit these vulnerabilities by inserting rootkits
through edge points of entry. This can enable a rootkit to spread
throughout a network, taking over computers and workstations and
rendering them as zombie computers under outside control.
OS attacks. After entering a system, a kernel mode rootkit can
attack the system's OS. The attack can include modifying the
functionality of the OS, slowing system performance, and even
accessing and deleting files. Kernel mode rootkits usually enter
systems when a user inadvertently opens a malicious email or
executes a download from an unreliable source.
Credit card swipe and scan attacks. Criminals have used rootkits to
infect credit card swipers and scanners. The rootkits are
programmed to record credit card information and to send the
information to servers controlled by hackers. To prevent this, credit
card companies have adopted chip-embedded cards, which are
more impervious to attack.
Malware continues to become more sophisticated, creating a gap in
current network defenses. Learn how to avert malware using a
modern approach that provides protection against both known andunknown threat
Injector tool
Injector
a tool to inject my rootkit into Windows kernel using vulnerable
drivers
You might also like
- Trend Micro RootkitsDocument3 pagesTrend Micro RootkitsgynxNo ratings yet
- Rootkits: What They Are and How To Fight Them: A Podcast Briefing Produced byDocument7 pagesRootkits: What They Are and How To Fight Them: A Podcast Briefing Produced bygynxNo ratings yet
- TLE10 Types of MalwaresDocument24 pagesTLE10 Types of MalwaresXavierNo ratings yet
- Cisco Introduction To Cyber Security Chap-2Document9 pagesCisco Introduction To Cyber Security Chap-2MukeshNo ratings yet
- Chapter 2 - Attacks, Concepts and TechniquesDocument21 pagesChapter 2 - Attacks, Concepts and TechniquesS. M. AkashNo ratings yet
- Club Hack Magazine 35 PDFDocument31 pagesClub Hack Magazine 35 PDFLeonardo Herrera RomeroNo ratings yet
- Topic 3 - MalwareDocument25 pagesTopic 3 - MalwareVinoth Vinoth100% (1)
- DL 10 Things RootkitsDocument5 pagesDL 10 Things Rootkitsmlmcbride33No ratings yet
- 威脅Document4 pages威脅ggyyNo ratings yet
- A Rule-Based Approach For Rootkit Detection: Jianxiong WangDocument4 pagesA Rule-Based Approach For Rootkit Detection: Jianxiong WangLaura UrsicaNo ratings yet
- Chapter 5 To 6 PDF-1Document33 pagesChapter 5 To 6 PDF-1Tora SarkarNo ratings yet
- Chris Ries - Inside Windows RootkitsDocument28 pagesChris Ries - Inside Windows RootkitsWhite909100% (2)
- Cyber Security Unit-5Document10 pagesCyber Security Unit-5shivasingh38025No ratings yet
- DFN5033 - Chapter 4 HARDENING OPERATING SYSTEM ROOTKITDocument10 pagesDFN5033 - Chapter 4 HARDENING OPERATING SYSTEM ROOTKITNURRUL ISMAILNo ratings yet
- Presentation 10Document8 pagesPresentation 10yaswanth kumar vittaNo ratings yet
- Comp Sys Sec Unit2Document5 pagesComp Sys Sec Unit2Kumar SahuNo ratings yet
- Implications of Rootkit To User Privacy: Term PaperDocument14 pagesImplications of Rootkit To User Privacy: Term PaperpraneethkorallaNo ratings yet
- Batch:2020 Kamra Submitted To: MR - Khwaja Bilal Submitted By: Abdul Moiz SattiDocument7 pagesBatch:2020 Kamra Submitted To: MR - Khwaja Bilal Submitted By: Abdul Moiz SattiSumreenSattiNo ratings yet
- The Faces of Computer Malware: by Michael P. KassnerDocument15 pagesThe Faces of Computer Malware: by Michael P. KassnerAlex MungaiNo ratings yet
- Ontology of MalwareDocument5 pagesOntology of MalwareJosielyn TarsNo ratings yet
- Gaining and Maintaining AccessDocument37 pagesGaining and Maintaining AccessSurbhi DahiyaNo ratings yet
- What Is MalwarDocument5 pagesWhat Is MalwarMajid GorsiNo ratings yet
- Txs-Rootkits and Digital ForensicsDocument11 pagesTxs-Rootkits and Digital Forensicsfrankstall130No ratings yet
- 7 VirusesDocument67 pages7 VirusesAbdul Rasheed Mohamed AliNo ratings yet
- Cyber SecurityDocument18 pagesCyber SecurityRajib MondalNo ratings yet
- MalwareDocument16 pagesMalwareVaiBhav AroraNo ratings yet
- Types of Malware and Its Nature of AttackDocument3 pagesTypes of Malware and Its Nature of Attackjocelle adlawan100% (1)
- Introduction To Cyber Security: Long QuestionsDocument37 pagesIntroduction To Cyber Security: Long Questionsnabin ku. dasNo ratings yet
- Computer and Internet CrimesDocument7 pagesComputer and Internet CrimesEjDungoNo ratings yet
- Cyber Unit 5 - 1627632179 - 1697003597Document10 pagesCyber Unit 5 - 1627632179 - 1697003597xyz705638No ratings yet
- Computer Viruses: Hwang Sun AhDocument8 pagesComputer Viruses: Hwang Sun AhSun Ah HwangNo ratings yet
- Windows Hacking 2015 8 9Document2 pagesWindows Hacking 2015 8 9arun5918No ratings yet
- Computer Security AssignmentDocument3 pagesComputer Security Assignmenttehseeninter0% (1)
- 1563881800unit 2 Malware and Its Types EDITSDocument8 pages1563881800unit 2 Malware and Its Types EDITSMuhammad MalikNo ratings yet
- Nad Ns Unit6-Part1Document20 pagesNad Ns Unit6-Part1Akshay UtaneNo ratings yet
- Attacks Concepts and TechniquesDocument49 pagesAttacks Concepts and TechniquesShoua Iqbal100% (1)
- Types of Malicious SoftwareDocument2 pagesTypes of Malicious SoftwareLegesse SamuelNo ratings yet
- Digital Malware Analysis - V2Document33 pagesDigital Malware Analysis - V2apgnascimento96No ratings yet
- Five Tips RootkitsDocument2 pagesFive Tips Rootkitsss_kamalapurkarNo ratings yet
- Important Question Ethical HackingDocument27 pagesImportant Question Ethical Hackingsuthojuakhil21No ratings yet
- Hypervisor Based Mitigation Technique For Keylogger Spyware AttacksDocument6 pagesHypervisor Based Mitigation Technique For Keylogger Spyware AttacksOmar Neptali Montoya SalazarNo ratings yet
- Lo1 Security AashaDocument8 pagesLo1 Security AashawayneNo ratings yet
- CompTIA SecuritySY0501Cert Prep1ThreatsAttacksandVulnerabilitiesDocument32 pagesCompTIA SecuritySY0501Cert Prep1ThreatsAttacksandVulnerabilitiesMohannad JabaitiNo ratings yet
- Mama ArbDocument4 pagesMama ArbMarian SolivaNo ratings yet
- Understanding Virus ProtectionDocument6 pagesUnderstanding Virus ProtectionOgunmola TundeNo ratings yet
- Malware Classification & DamagesDocument7 pagesMalware Classification & Damagesnusha2907No ratings yet
- Ethics Lect5 MalwareDocument18 pagesEthics Lect5 Malwareomarnader16No ratings yet
- Ics Notesm3Document8 pagesIcs Notesm3Nischitha PNo ratings yet
- Introductiontoexploitationmetasploit 190312092949Document21 pagesIntroductiontoexploitationmetasploit 190312092949muna cliffNo ratings yet
- Malicious Code (Sometimes Called Malware) Is A Type of Software Designed To Take Over orDocument7 pagesMalicious Code (Sometimes Called Malware) Is A Type of Software Designed To Take Over orpartha_665590810No ratings yet
- Unit 5 - Cyber SecurityDocument9 pagesUnit 5 - Cyber SecurityDraxNo ratings yet
- Computer VirusesDocument6 pagesComputer VirusesJACOB MUDONHINo ratings yet
- Malicious and Destructive Software Adware: Joey Wassig AcisDocument3 pagesMalicious and Destructive Software Adware: Joey Wassig AcisJoey WassigNo ratings yet
- Lagutin, Carlo S. Bsit - 3CDocument2 pagesLagutin, Carlo S. Bsit - 3CCarlo LagutinNo ratings yet
- Jasmin Espiritu Artificial Intelliegence Bscs 4A Mr. Tan: What Is A Bot?Document2 pagesJasmin Espiritu Artificial Intelliegence Bscs 4A Mr. Tan: What Is A Bot?Rio Rosa BolanteNo ratings yet
- Unit 5 - Cyber SecurityDocument10 pagesUnit 5 - Cyber SecuritymonalisahooNo ratings yet
- CSS KNC301 Notes Unit 2 and Unit 3Document28 pagesCSS KNC301 Notes Unit 2 and Unit 3anchal kardamNo ratings yet
- Computer Security MCQDocument12 pagesComputer Security MCQpinkudon089No ratings yet
- Assg 4Document22 pagesAssg 4mr copy xeroxNo ratings yet
- Husna Faheem project (1)Document95 pagesHusna Faheem project (1)mr copy xeroxNo ratings yet
- I Am Sharing 'FRST Pages of The Project' With YouDocument11 pagesI Am Sharing 'FRST Pages of The Project' With Youmr copy xeroxNo ratings yet
- N Chandrasekhar - Mainframe - ResumeDocument2 pagesN Chandrasekhar - Mainframe - Resumemr copy xeroxNo ratings yet
- Sudheer Loan Letter PDFDocument7 pagesSudheer Loan Letter PDFmr copy xeroxNo ratings yet
- Bioavailability and Ence: OequivaDocument32 pagesBioavailability and Ence: Oequivamr copy xeroxNo ratings yet
- Adobe Scan Mar 25, 2023Document12 pagesAdobe Scan Mar 25, 2023mr copy xeroxNo ratings yet
- Graphs - 1Document11 pagesGraphs - 1mr copy xeroxNo ratings yet
- CDF62846-CEAA-4ABF-821D-4C86DBCD2F3BDocument2 pagesCDF62846-CEAA-4ABF-821D-4C86DBCD2F3Bmr copy xeroxNo ratings yet
- Venky Researchproject2023Document37 pagesVenky Researchproject2023mr copy xeroxNo ratings yet
- P ART4Document5 pagesP ART4mr copy xeroxNo ratings yet
- k4 Win Seminar FINALDocument33 pagesk4 Win Seminar FINALmr copy xeroxNo ratings yet
- 1A06CC97-3CA9-4FFC-B82F-182A54E0A867Document1 page1A06CC97-3CA9-4FFC-B82F-182A54E0A867mr copy xeroxNo ratings yet
- Vinay RecomendationDocument1 pageVinay Recomendationmr copy xeroxNo ratings yet
- G8 Report MajorDocument64 pagesG8 Report Majormr copy xeroxNo ratings yet
- Assignment: On Social and Preventive PharmacyDocument2 pagesAssignment: On Social and Preventive Pharmacymr copy xeroxNo ratings yet
- UntitledDocument1 pageUntitledmr copy xeroxNo ratings yet
- A Dual Port Substrate Integrated Wave Antenna For X-Band ApplicationsDocument48 pagesA Dual Port Substrate Integrated Wave Antenna For X-Band Applicationsmr copy xeroxNo ratings yet
- VCEH B Tech Project Report 1Document70 pagesVCEH B Tech Project Report 1mr copy xeroxNo ratings yet
- Majorreport FinalDocument70 pagesMajorreport Finalmr copy xeroxNo ratings yet
- Tax Invoice: 8-3-833/114 Near Satya Sai Kalyana Mandapam GSTIN/UIN: 36AAIFD9474F1Z4 State Name: Telangana, Code: 36Document1 pageTax Invoice: 8-3-833/114 Near Satya Sai Kalyana Mandapam GSTIN/UIN: 36AAIFD9474F1Z4 State Name: Telangana, Code: 36mr copy xeroxNo ratings yet
- MR Guthula PDFDocument1 pageMR Guthula PDFmr copy xeroxNo ratings yet
- VCEH B Tech Project ReportDocument66 pagesVCEH B Tech Project Reportmr copy xeroxNo ratings yet
- Maths Question Bank With Solutions - M I PDFDocument45 pagesMaths Question Bank With Solutions - M I PDFmr copy xeroxNo ratings yet
- ReportDocument70 pagesReportmr copy xeroxNo ratings yet
- PrintDocument2 pagesPrintmr copy xeroxNo ratings yet
- Adobe Scan 19 Mar 2023 PDFDocument6 pagesAdobe Scan 19 Mar 2023 PDFmr copy xeroxNo ratings yet
- Udyam Dashboard DetailsDocument3 pagesUdyam Dashboard Detailsmr copy xeroxNo ratings yet
- Talent ManagementDocument2 pagesTalent Managementmr copy xeroxNo ratings yet
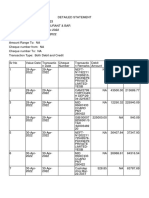
- Detailstatement - 20 3 2023@14 58 47Document12 pagesDetailstatement - 20 3 2023@14 58 47mr copy xeroxNo ratings yet
- ICDL: International Computer Driving License: Module 7: The Internet and CommunicationDocument16 pagesICDL: International Computer Driving License: Module 7: The Internet and CommunicationLoïc JEAN-CHARLESNo ratings yet
- Group Assignment - 2 - Kelompok 1Document4 pagesGroup Assignment - 2 - Kelompok 1JamesWilliamNo ratings yet
- Reconnaisance AttackDocument13 pagesReconnaisance Attackapi-537419578No ratings yet
- IGCSE ICT MCQ Mock 1 - FullDocument4 pagesIGCSE ICT MCQ Mock 1 - Fullrahimuddin100% (1)
- Empowerment Technologies: Second Semester, 3 QuarterDocument42 pagesEmpowerment Technologies: Second Semester, 3 Quarterjhna mggyNo ratings yet
- 1563881800unit 2 Malware and Its Types EDITSDocument8 pages1563881800unit 2 Malware and Its Types EDITSMuhammad MalikNo ratings yet
- Vs. Cisco Iron Port: Top Attacks and BreachesDocument2 pagesVs. Cisco Iron Port: Top Attacks and BreachesZiveskNo ratings yet
- Spyware Anatomy TechRepublicDocument2 pagesSpyware Anatomy TechRepublicAlleyRogerNo ratings yet
- McAfee Activate - Enter 25-Digit Activation CodeDocument11 pagesMcAfee Activate - Enter 25-Digit Activation CodeJames PotterNo ratings yet
- MCQ For 1st Mid 4 (1) CbsDocument19 pagesMCQ For 1st Mid 4 (1) CbsGejiNo ratings yet
- Chapter2 MalwareDocument82 pagesChapter2 MalwareOscar CopadoNo ratings yet
- Network Security-Virus Attacks and Defence Using Antivirus SoftwareDocument3 pagesNetwork Security-Virus Attacks and Defence Using Antivirus SoftwareAhsan SakheeNo ratings yet
- TLE ICT 10 Quiz 2.2Document2 pagesTLE ICT 10 Quiz 2.2PreNo ratings yet
- Online Access and Computer SecurityDocument17 pagesOnline Access and Computer Securitysagar salalNo ratings yet
- KOMALA Annual Work Report in 2023Document7 pagesKOMALA Annual Work Report in 2023kamidikamalakarNo ratings yet
- ITE-6101-2013T (UGRD) Computing Fundamentals: My CoursesDocument21 pagesITE-6101-2013T (UGRD) Computing Fundamentals: My CoursesRochelle Ann DianeNo ratings yet
- How To InstallDocument2 pagesHow To InstallAli Hossain AdnanNo ratings yet
- Chapter 5. Cybersecurity and Risk Management TechnologyDocument30 pagesChapter 5. Cybersecurity and Risk Management Technologyarmando.lykajovel.dllNo ratings yet
- Cyber Security Awareness - ExamDocument3 pagesCyber Security Awareness - ExamRahul PatelNo ratings yet
- NSE1 Key Cybersecurity Terms-ENDocument6 pagesNSE1 Key Cybersecurity Terms-ENitachi uchihaNo ratings yet
- Accounting Information Systems: Fifteenth EditionDocument19 pagesAccounting Information Systems: Fifteenth Editionsyafiq rossleyNo ratings yet
- Emtech Q2 Las Week 3 (2021-2022)Document4 pagesEmtech Q2 Las Week 3 (2021-2022)rosellerNo ratings yet
- Yoga Book: User GuideDocument21 pagesYoga Book: User GuideFrancisco GarcíaNo ratings yet
- The Impact of Cyber Threats On Social Networking SitesDocument10 pagesThe Impact of Cyber Threats On Social Networking Sitesプリンシペ カールNo ratings yet
- Integrated Malware Analysis Using Machine Learning PDFDocument8 pagesIntegrated Malware Analysis Using Machine Learning PDFMike RomeoNo ratings yet
- Physical Security DefinitionDocument1 pagePhysical Security DefinitionJoyce De Guzman100% (1)
- GC-F - 005 - Formato - Taller 5 Cyber AttackDocument6 pagesGC-F - 005 - Formato - Taller 5 Cyber AttackNico MendezNo ratings yet
- Empowerment Week2Document3 pagesEmpowerment Week2dabidNo ratings yet
- Ciber CrimeDocument12 pagesCiber CrimeAshutosh ShuklaNo ratings yet
- 2011 - The Cyber Threat Landscape Challenges and Future Research DirectionsDocument13 pages2011 - The Cyber Threat Landscape Challenges and Future Research DirectionsTomNo ratings yet