Professional Documents
Culture Documents
CSVS - Lab 4
Uploaded by
Aditi SharmaOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
CSVS - Lab 4
Uploaded by
Aditi SharmaCopyright:
Available Formats
CYBER SECURITY VULNERABILITIES AND SAFEGUARDS LAB
LAB 4: Fuzzing
FUZZING
Fuzzing is an automated software testing method that injects invalid, malformed, or unexpected
inputs into a system to reveal software defects and vulnerabilities. A fuzzing tool injects these
inputs into the system and then monitors for exceptions such as crashes or information leakage.
Fuzz testing offers a wide range of benefits to a security and quality program.
Fuzzing provides a good overall picture of the quality of the target system and software.
Fuzzing is the primary technique used by malicious hackers to find software
vulnerabilities. Using it in your security program helps you prevent zero-day exploits
from unknown bugs and weaknesses in your system.
Fuzzing has a low overhead for both cost and time. Once a fuzzer is up and running, it
can start to look for bugs on its own, with no manual/human intervention, and can
continue to do so for as long as needed.
Fuzzing helps uncover bugs that would not have been detected through conventional
testing methods or manual audits.
Types of Fuzz Testing
1. Application Fuzzing: This fuzzing method tests UI features such as buttons, input fields
in forms, or options in command-line programs. It can similarly be used to test API
commands.
2. Protocol Fuzzing: Protocols such as Hypertext Transfer Protocol (HTTP) are used to
exchange data over the web. Protocol fuzzing is used to test the behavior of a server
when bad content is sent over a given protocol.
3. File Format Fuzzing: File format fuzzing creates a corrupted file and presents it to the
target software for processing. This is relevant both for installed software and web
applications that accept files as input. Files are usually in standard formats,
such .jpg, .docx or .xml.
Some open source tools are:
sfuzz
wfuzz
ffuf
VAF
In this lab we are going to go through wfuzz and ffuf tools.
WFUZZ
Wfuzz is a tool designed for bruteforcing Web Applications, it can be used for finding resources
not linked directories, servlets, scripts, etc, bruteforce GET and POST parameters for checking
different kind of injections (SQL, XSS, LDAP,etc), bruteforce Forms parameters
(User/Password), Fuzzing, etc.
Installation:
The command to install wfuzz:
[kali@kali ~]$ sudo apt install wfuzz
Using wfuzz to find unlinked resources/webpage in a website
Unlinked resources or webpage is anything that is not accessible from the viewable webpage.
To print the available options and syntax use the command:
[kali@kali ~]$ wfuzz -h
To find unlinked webpages use the command:
[kali@kali ~]$ wfuzz -c -w <Wordlist> --hc <HTTP Status Code> -u <URL>/FUZZ
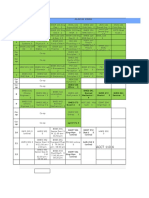
Current webpage links that can be seen:
After the scan we can see the unlinked webpages:
FFUF
ffuf is a fest web fuzzer written in Go language that allows typical directory discovery, virtual
host discovery (without DNS records) and GET and POST parameter fuzzing.
Installation
The command to install ffuf is:
[kali@kali ~]$ sudo apt install ffuf
Using ffuf to find unlinked resources/webpages in a website
To print the available options and syntax use the command:
[kali@kali ~]$ ffuf -h
To find unlinked webpages use the command:
[kali@kali ~]$ ffuf -c -r -u <URL>/FUZZ -w <Wordlist> -fc <HTTP code to filter>
Current webpage links that can be seen:
After the scan we can see the unlinked webpages:
You might also like
- Penetration Testing of Computer Networks Using Burpsuite and Various Penetration Testing ToolsFrom EverandPenetration Testing of Computer Networks Using Burpsuite and Various Penetration Testing ToolsNo ratings yet
- Penetration Testing of Computer Networks Using BurpSuite and Various Penetration Testing ToolsFrom EverandPenetration Testing of Computer Networks Using BurpSuite and Various Penetration Testing ToolsNo ratings yet
- Fuzz Testing (Fuzzing) Tutorial - What Is, Types, Tools & ExampleDocument8 pagesFuzz Testing (Fuzzing) Tutorial - What Is, Types, Tools & ExampleanchalNo ratings yet
- Fuzzing or Fuzz TestingDocument3 pagesFuzzing or Fuzz TestingSHAIRA KAYE CABANTINGNo ratings yet
- Automated ScannersDocument8 pagesAutomated ScannersRakshith UNo ratings yet
- Ten Open-Source Security Testing Tools!Document7 pagesTen Open-Source Security Testing Tools!saporadisNo ratings yet
- Owasp Zap 2.9: Getting Started GuideDocument10 pagesOwasp Zap 2.9: Getting Started GuideCarlos ZuluagaNo ratings yet
- ZAPGettingStartedGuide-2 6 PDFDocument10 pagesZAPGettingStartedGuide-2 6 PDFyoyo maNo ratings yet
- Assignment - 1: TerminatorDocument6 pagesAssignment - 1: TerminatorRishav SharmaNo ratings yet
- Firefox Add-OnsDocument9 pagesFirefox Add-OnsWhite Box SecurityNo ratings yet
- Api ToolsDocument4 pagesApi Toolsstevebently934No ratings yet
- OWASP ZAP Getting Started GuideDocument10 pagesOWASP ZAP Getting Started GuideNobitaJuniorNo ratings yet
- Anti Fuzzing PDFDocument5 pagesAnti Fuzzing PDFAnonymous HyQMW7WRNo ratings yet
- 5 SecurityTestingDocument10 pages5 SecurityTestingIlham AbNo ratings yet
- Top Burp Suite Extension Used by PentestersDocument27 pagesTop Burp Suite Extension Used by PentestersitssconsultoresNo ratings yet
- Web PentestDocument9 pagesWeb PentestsatheeshbabunNo ratings yet
- Pentest Workplan: Information Gathering and Vulnerability AnalysisDocument5 pagesPentest Workplan: Information Gathering and Vulnerability AnalysisLe ChauveNo ratings yet
- DF 3Document9 pagesDF 3Thakor KaushalNo ratings yet
- 21BCE5311 Ism Lab1Document16 pages21BCE5311 Ism Lab1UtkarshNo ratings yet
- Pen Testing With Burp SuiteDocument41 pagesPen Testing With Burp Suiteazmath100% (2)
- Pen Testing BasicsDocument153 pagesPen Testing BasicsChristopher C. Cheng100% (2)
- Mal AnalysingDocument7 pagesMal AnalysingFarer Farer100% (1)
- Application Security - Secure Software DevelopmentDocument7 pagesApplication Security - Secure Software DevelopmentSampth KarunarathneNo ratings yet
- Ntro OM: Duction PutingDocument17 pagesNtro OM: Duction PutingPaula Louise SantosNo ratings yet
- SWE2005 - Software Testing - Review 1.1.2Document15 pagesSWE2005 - Software Testing - Review 1.1.2Sanjay dbzNo ratings yet
- Module 06Document16 pagesModule 06Hurjay NaguitNo ratings yet
- Dsouza Fortify 07 ReportDocument10 pagesDsouza Fortify 07 ReportPrasadNo ratings yet
- Test For Configuration and Deployment Aim: DescriptionDocument8 pagesTest For Configuration and Deployment Aim: DescriptionAswathy L CNo ratings yet
- Quickfuzz: An Automatic Random Fuzzer For Common File FormatsDocument8 pagesQuickfuzz: An Automatic Random Fuzzer For Common File FormatsMoni ShafiqNo ratings yet
- CS GTU Study Material Presentations Unit-3 26112020052923AMDocument37 pagesCS GTU Study Material Presentations Unit-3 26112020052923AMHarsh JoshiNo ratings yet
- SoftwareDocument4 pagesSoftwareRio HerlambangNo ratings yet
- 10 Most Popular Password Cracking ToolsDocument10 pages10 Most Popular Password Cracking Toolspravesh2231100% (1)
- VAPT Lab Assignment 4Document12 pagesVAPT Lab Assignment 4Abhishek HajareNo ratings yet
- (v2022.9) Burp Suite - Leading Software For Web Security Testing - AppNee Freeware GroupDocument5 pages(v2022.9) Burp Suite - Leading Software For Web Security Testing - AppNee Freeware GroupAjay MaluNo ratings yet
- Study Report On AntivirusDocument4 pagesStudy Report On Antivirusram9kumar678No ratings yet
- Malware AnalysisDocument9 pagesMalware Analysispavan kcNo ratings yet
- Penetresting Tools Used in Ethical HackingDocument5 pagesPenetresting Tools Used in Ethical Hackingranjan rajaNo ratings yet
- Afe ManualDocument12 pagesAfe ManualZim ZumNo ratings yet
- Reverse Honey TrapDocument8 pagesReverse Honey TrapelabirNo ratings yet
- SoftwareDocument9 pagesSoftwarerhaivienripalda786No ratings yet
- W3-Scrape - A Windows Based Reconnaissance Tool For Web Application FingerprintingDocument6 pagesW3-Scrape - A Windows Based Reconnaissance Tool For Web Application Fingerprintingakejuis2No ratings yet
- SoftwareDocument11 pagesSoftwareJm Venki100% (1)
- 2-Tools For Automating VAPTDocument1 page2-Tools For Automating VAPTAyush SinghNo ratings yet
- Pentest With Metasploit - OverviewDocument42 pagesPentest With Metasploit - OverviewPiyush RautNo ratings yet
- FIREWALLSDocument6 pagesFIREWALLSNOREEN KEITH MAMOLO100% (1)
- Bug Tracking SoftwareDocument5 pagesBug Tracking SoftwareMYTHILI RAMESH0% (1)
- Security Notes4Document12 pagesSecurity Notes4Nafisa AhmadNo ratings yet
- WWW Stationx Net Penetration Testing Tools For Kali LinuxDocument12 pagesWWW Stationx Net Penetration Testing Tools For Kali Linuxteguebzanga.zidaNo ratings yet
- Welcome To UFT: For More Details Please Contact Us: US: +1 718 819 9361 INDIA: +91 8099776681Document14 pagesWelcome To UFT: For More Details Please Contact Us: US: +1 718 819 9361 INDIA: +91 8099776681Jp CordezNo ratings yet
- Module 7+8Document11 pagesModule 7+8Apurva KeskarNo ratings yet
- Cyber Security Unit-5Document10 pagesCyber Security Unit-5shivasingh38025No ratings yet
- By:-Abhishek PasrichaDocument27 pagesBy:-Abhishek PasrichaSatheessh KonthalaNo ratings yet
- Malware Analysis Sandbox: Project OnDocument16 pagesMalware Analysis Sandbox: Project OnPrabhat Verma100% (1)
- WP SI 10 Network Security ToolsDocument6 pagesWP SI 10 Network Security ToolsHari SetiawanNo ratings yet
- Software Testing Is An Investigation Conducted To Provide Stakeholders With InformationDocument10 pagesSoftware Testing Is An Investigation Conducted To Provide Stakeholders With InformationRobert BayanidNo ratings yet
- Open Source SotwareDocument57 pagesOpen Source SotwareMohan KumarNo ratings yet
- Information Security ManagementDocument12 pagesInformation Security ManagementARYA DUBEY 20BCE0908No ratings yet
- Digital Malware Analysis - V2Document33 pagesDigital Malware Analysis - V2apgnascimento96No ratings yet
- Module 4Document45 pagesModule 4Ewen BenanaNo ratings yet
- SANS FOR610 - Reverse-Engineering Malware: Malware Analysis Tools and TechniquesDocument40 pagesSANS FOR610 - Reverse-Engineering Malware: Malware Analysis Tools and TechniquesNhat Long NguyenNo ratings yet
- Instant Download Principles of Virology Ebook PDF FREEDocument11 pagesInstant Download Principles of Virology Ebook PDF FREEwalter.penn362100% (51)
- Anaerobic Fermentation of Substrate With High NitrDocument9 pagesAnaerobic Fermentation of Substrate With High NitrHanna SetyoNo ratings yet
- BSMS Drexel ScheduleDocument4 pagesBSMS Drexel ScheduleAmy ZhiNo ratings yet
- What Is Splunk - (Easy Guide With Pictures) - Cyber Security KingsDocument9 pagesWhat Is Splunk - (Easy Guide With Pictures) - Cyber Security Kingsrokoman kungNo ratings yet
- EAPP POWERPOINT BY Prof. Deo S. FabroaDocument98 pagesEAPP POWERPOINT BY Prof. Deo S. FabroaAlen Jay MagsicoNo ratings yet
- Resume - Lifestyle Medicine RDDocument1 pageResume - Lifestyle Medicine RDapi-338995106No ratings yet
- Tle q4 l5 Quiz Google FormsDocument5 pagesTle q4 l5 Quiz Google FormsEdilbert Bonifacio GayoNo ratings yet
- UNIT 2 - LESSON 1 - Overview To Qualitative ResearchDocument31 pagesUNIT 2 - LESSON 1 - Overview To Qualitative ResearchmikkaellaNo ratings yet
- Top10 Structural Engineer Interview Questions and AnswersDocument17 pagesTop10 Structural Engineer Interview Questions and Answersmodest_dhu100% (1)
- IndraneelRakshit ResumeDocument7 pagesIndraneelRakshit ResumeIndraneel RakshitNo ratings yet
- Backup PolicyDocument2 pagesBackup PolicyEdwin SemiraNo ratings yet
- CLI Basics: Laboratory ExerciseDocument5 pagesCLI Basics: Laboratory ExerciseJhalen Shaq CarrascoNo ratings yet
- Wind Seismic CalculationsDocument4 pagesWind Seismic Calculationsumesh0% (1)
- She-Ra Gem Tutorial by Anna Anderson - Cosplay and CoffeeDocument13 pagesShe-Ra Gem Tutorial by Anna Anderson - Cosplay and CoffeeAnna AndersonNo ratings yet
- Benefits of BIM For Master PlumbersDocument2 pagesBenefits of BIM For Master PlumbersDavid GeminaNo ratings yet
- Scribd Sap SD Pricing in Depth Configuration GuideDocument136 pagesScribd Sap SD Pricing in Depth Configuration GuideRavi SubramanianNo ratings yet
- SimNowUsersManual4 6 1Document271 pagesSimNowUsersManual4 6 1MichelleNo ratings yet
- Banking Financial InstitutionsDocument252 pagesBanking Financial Institutionspraise ferrerNo ratings yet
- VedicReport2 28 202412 53 08PMDocument55 pagesVedicReport2 28 202412 53 08PM처곧ᄉJimmyNo ratings yet
- Persuasion PyramidDocument1 pagePersuasion PyramidKenzie DoctoleroNo ratings yet
- Clarion CX Basics FundamentalsDocument15 pagesClarion CX Basics FundamentalsRajesh VenkatNo ratings yet
- BAMBOO U - 5 Ways To Process BambooDocument11 pagesBAMBOO U - 5 Ways To Process BambooeShappy HomeNo ratings yet
- Cs Supply ChainDocument7 pagesCs Supply ChainJoy MartinezNo ratings yet
- SP7 PDFDocument1,025 pagesSP7 PDFkushaljp8989No ratings yet
- Report Mii 1023 Marketing Management 2Document6 pagesReport Mii 1023 Marketing Management 2qibNo ratings yet
- Seminar ReportDocument25 pagesSeminar ReportChethan kumar D NNo ratings yet
- Clutch Bearing 2008-Application GuideDocument17 pagesClutch Bearing 2008-Application GuidemagdyfifaNo ratings yet
- Table of Specifications With Test in Science - Quarter 4 - (Week 3 and Week 4)Document4 pagesTable of Specifications With Test in Science - Quarter 4 - (Week 3 and Week 4)Sarah Jane Lagura Rele50% (2)
- Fermentación BatchDocument8 pagesFermentación BatchJennifer A. PatiñoNo ratings yet
- ReportDocument10 pagesReportNeeraj KishoreNo ratings yet