Professional Documents
Culture Documents
CIE3-CNS Set 2
Uploaded by
Thiru KumaraCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
CIE3-CNS Set 2
Uploaded by
Thiru KumaraCopyright:
Available Formats
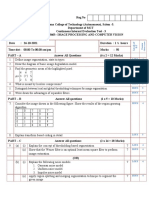
Reg.
No
Sona College of Technology (Autonomous), Salem -5.
Department of CSE
Continuous Internal Evaluation Test – 3
SET – 2 U19CS702 Cryptography
Common to All sections ( IV Year / Semester)
Date : Duration : 1 ½ hours
Outcomes
Levels of
Course
B.T
Time slot : 09.15 To 10.45 am/pm Marks : 50
PART – A Answer All Questions (6 x 2 = 12 Marks)
1. State the requirements of digital signatures. LOTS 4
2. What are the design objectives of HMAC? LOTS 4
3. State the protocol which suppresses the replay attacks and at the same time fix the problem of HOTS 4
Needham/Schroeder protocol.
4. What do you mean by Bastion Host? LOTS 5
5. Identify the security parameters that may be applicable when analyzing e-mail security HOTS 5
6. List out the features and usage of a good password. HOTS 5
PART – B Answer All questions (2 x 5 = 10 Marks)
7. Summarize the authentication dialogue used by Kerberos V4 for obtaining services. HOTS 4
8. Describe how PGP provides confidentiality and authentication services for email application LOTS 5
PART – C Answer All questions (2 x 14 = 28 Marks)
9. (a) (i) Explain the process of generating the message digest value using MD5 algorithm with 7 LOTS 4
necessary diagrams and steps.
(ii) Consider secret keys Ka and Kb are shared between A & KDC and B & KDC. 7 HOTS 4
Apply Needhem Schroder protocol to distribute session key Ks to A and B.
(OR)
(b) (i) What are the various ways of using hash functions in message authentication? 7 LOTS 4
Explain them with neat diagram.
(ii) Explain the requirements of digital signatures and analyze how problems related to 7 HOTS 4
digital signatures can be taken care of using an arbiter.
10. (a) (i) Explain the phases of SSL handshake protocol for 7 LOTS 5
a. Establishing security capabilities
b. Server authentication and key exchange
c. Client authentication and key exchange
(ii) A device with 192.168.1.147 tries to connect to a device with IP 7 HOTS 5
(192.0.9.40) ,then the connection is first verified by firewall that completes the
TCP three way handshaking process and if there is a consequent traffic arises
then how it will be detected using packet filtering method?
(OR)
(b) (i) Explain the functions of S/MIME 7 LOTS 5
(ii) Apply the Statistical Anomaly method for legitimate user where statistical tests are 7 HOTS 5
applied to observed behavior with a high level of confidence.
Bloom’s LOTS HOTS To
Percentage 50 50 1
You might also like
- CIE3-CNS Set 1Document2 pagesCIE3-CNS Set 1Thiru KumaraNo ratings yet
- Cie2 Set2 CNSDocument2 pagesCie2 Set2 CNSThiru KumaraNo ratings yet
- Cie2 Set1 CNSDocument2 pagesCie2 Set1 CNSThiru KumaraNo ratings yet
- Nws 2 Internal 2023-24-1Document2 pagesNws 2 Internal 2023-24-1deecodes13No ratings yet
- Network Security Protocols - S8 CSE-2019 Scheme-SyllabusDocument9 pagesNetwork Security Protocols - S8 CSE-2019 Scheme-SyllabusASHNA ANo ratings yet
- MCA-505 (E) : M.C.A. V Semester Network SecurityDocument2 pagesMCA-505 (E) : M.C.A. V Semester Network Securityabhinavgiri17No ratings yet
- (WWW - Entrance-Exam - Net) - Download DOEACC C Level Network Security & Cryptography Sample Paper 2Document2 pages(WWW - Entrance-Exam - Net) - Download DOEACC C Level Network Security & Cryptography Sample Paper 2DEBLEENA VIJAYNo ratings yet
- Papers 2020Document33 pagesPapers 2020anish231003No ratings yet
- IET DAVV Be - Com - It-A - Apr - 2011Document19 pagesIET DAVV Be - Com - It-A - Apr - 2011jainam dudeNo ratings yet
- Computer NetworksDocument4 pagesComputer NetworksSavari RajNo ratings yet
- CNS R16 Q Paper-May 2019Document2 pagesCNS R16 Q Paper-May 2019Raghu NangunuriNo ratings yet
- Cryptography Quest Bank 02Document7 pagesCryptography Quest Bank 02Gurpreet SinghNo ratings yet
- CSC340 CN CDF V3.1Document2 pagesCSC340 CN CDF V3.1Faizan KhanNo ratings yet
- CN (18) 3rd IADocument1 pageCN (18) 3rd IASuhan BNo ratings yet
- NSP-PQP (Not Exact Syllabus)Document8 pagesNSP-PQP (Not Exact Syllabus)ASHNA ANo ratings yet
- Assignment Cover Sheet Qualification Module Number and TitleDocument8 pagesAssignment Cover Sheet Qualification Module Number and TitleIM 99No ratings yet
- Assignment Cover Sheet Qualification Module Number and TitleDocument8 pagesAssignment Cover Sheet Qualification Module Number and TitleIM 99No ratings yet
- Iat1 CNDocument24 pagesIat1 CNMj KumarNo ratings yet
- (CS6701 PTCS6701)Document3 pages(CS6701 PTCS6701)Russian CarxgameNo ratings yet
- Rr410502 Distributed SytemsDocument4 pagesRr410502 Distributed SytemsSrinivasa Rao GNo ratings yet
- CNE Micro Project FormatDocument13 pagesCNE Micro Project FormatRohan KambleNo ratings yet
- Assignment NO 5 (A) ACNDocument1 pageAssignment NO 5 (A) ACNdivya lokhandeNo ratings yet
- 9A04706 Digital Design Through Verilog HDL PDFDocument1 page9A04706 Digital Design Through Verilog HDL PDFTayyabunnissa BegumNo ratings yet
- Assignment 5 (B) ACNDocument1 pageAssignment 5 (B) ACNdivya lokhandeNo ratings yet
- ICT211e JAN 2017 Exam PaperDocument5 pagesICT211e JAN 2017 Exam PaperBenjamin TangNo ratings yet
- CNS Assignment 3Document1 pageCNS Assignment 3Aishwarya BiradarNo ratings yet
- Code: 9A05406 B.Tech III Year II Semester (R09) Regular & Supplementary Examinations May/June 2015Document1 pageCode: 9A05406 B.Tech III Year II Semester (R09) Regular & Supplementary Examinations May/June 2015subbuNo ratings yet
- Distinguish Between Local and Global Thresholding Techniques For Image SegmentationDocument2 pagesDistinguish Between Local and Global Thresholding Techniques For Image SegmentationLovely AnbuNo ratings yet
- 9A05406 Computer OrganizationDocument1 page9A05406 Computer OrganizationMahaboob SubahanNo ratings yet
- Cryptography and Network Security Feb 2020Document1 pageCryptography and Network Security Feb 2020Akshita dammuNo ratings yet
- Instructions:: Gujarat Technological UniversityDocument1 pageInstructions:: Gujarat Technological UniversityShweta JhaNo ratings yet
- Assessment Category: Assessment Title: Course Title: Semester: Course Code: Session: Instructor: Date Total Time InstructionsDocument2 pagesAssessment Category: Assessment Title: Course Title: Semester: Course Code: Session: Instructor: Date Total Time InstructionsMeharuNo ratings yet
- Mca Ass Semester IVDocument12 pagesMca Ass Semester IVvikram vikramNo ratings yet
- CS409 Cryptography and Network Security, December 2018 PDFDocument2 pagesCS409 Cryptography and Network Security, December 2018 PDFReshma SindhuNo ratings yet
- CS409 Cryptography and Network Security, December 2018Document2 pagesCS409 Cryptography and Network Security, December 2018Reshma SindhuNo ratings yet
- TLE 10 Second PT PrintDocument3 pagesTLE 10 Second PT PrintsergioNo ratings yet
- Gujarat Technological UniversityDocument2 pagesGujarat Technological Universitythakornikita001.nt10No ratings yet
- Stage 1 Repor1Document16 pagesStage 1 Repor1Zack OverfieldNo ratings yet
- CU-2021 B.Sc. (Honours) Computer Science Semester-IV Paper-CC-10 QPDocument2 pagesCU-2021 B.Sc. (Honours) Computer Science Semester-IV Paper-CC-10 QPKuntalMukherjeeNo ratings yet
- Linux and OS Question SEM FINAL QUESTION BANKDocument65 pagesLinux and OS Question SEM FINAL QUESTION BANKIndia RaniNo ratings yet
- B.Tech IV Year I Semester (R15) Regular Examinations November/December 2018Document5 pagesB.Tech IV Year I Semester (R15) Regular Examinations November/December 2018pruthviNo ratings yet
- Course: Microprocessors & Interfacing: Nayana@gec - Ac.inDocument3 pagesCourse: Microprocessors & Interfacing: Nayana@gec - Ac.inSahil ShaikhNo ratings yet
- Software Requirements Specification: (An Application Software For Estimating Software Development .)Document10 pagesSoftware Requirements Specification: (An Application Software For Estimating Software Development .)Firoz AhmadNo ratings yet
- CNE Micro Project FormatDocument13 pagesCNE Micro Project FormatRohan KambleNo ratings yet
- r7410407 Operating SystemsDocument4 pagesr7410407 Operating SystemssivabharathamurthyNo ratings yet
- Data Com EndDocument2 pagesData Com EndDebmalya GhoshNo ratings yet
- 6th Sem.Document17 pages6th Sem.suraj pahariNo ratings yet
- CA727 CN Final AssessmentDocument1 pageCA727 CN Final Assessmentbikky kumar sharmaNo ratings yet
- R05320506-SOFTWARE-TESTING-METHODOLOGIES May 2008Document5 pagesR05320506-SOFTWARE-TESTING-METHODOLOGIES May 2008api-19718334No ratings yet
- (4937) - 1001 M.Sc. Computer Science CS - 101: Principles of Programming Languages (2013 Pattern) (Semester - I)Document63 pages(4937) - 1001 M.Sc. Computer Science CS - 101: Principles of Programming Languages (2013 Pattern) (Semester - I)XIAOBEL TradingsNo ratings yet
- D11 D12 D13 0354 MidtermDocument2 pagesD11 D12 D13 0354 MidtermRISHABH KUMAR TIWARY 20BCE10139No ratings yet
- Candidates Are Required To Give Their Answers in Their Own Words As Far As Practicable. The Figures in The Margin Indicate Full MarksDocument2 pagesCandidates Are Required To Give Their Answers in Their Own Words As Far As Practicable. The Figures in The Margin Indicate Full MarksAdhikari SushilNo ratings yet
- Cse QP2022 B20ef0501Document4 pagesCse QP2022 B20ef0501Ash SGNo ratings yet
- Surya Group of Institutions Internal Assessment Test-IDocument2 pagesSurya Group of Institutions Internal Assessment Test-ISathiya Ravi PNo ratings yet
- QP9 CNS QPDocument2 pagesQP9 CNS QPreshmapdscemailboxNo ratings yet
- 54115-mt - Network Security & CryptographyDocument1 page54115-mt - Network Security & CryptographySRINIVASA RAO GANTA100% (1)
- Assignment - DBB1105 - BBA 1 - Set-1 and 2 - Nov - 2021Document2 pagesAssignment - DBB1105 - BBA 1 - Set-1 and 2 - Nov - 2021NikhilNo ratings yet
- Gujarat Technological University: InstructionsDocument2 pagesGujarat Technological University: InstructionsShweta JhaNo ratings yet
- 3.CN2 - Dec 2017 Jan 2018Document2 pages3.CN2 - Dec 2017 Jan 2018Pruthviraj VNo ratings yet
- Internet Security: Cryptographic Principles, Algorithms and ProtocolsFrom EverandInternet Security: Cryptographic Principles, Algorithms and ProtocolsNo ratings yet
- Samarth Arora: Curriculum VitaeDocument2 pagesSamarth Arora: Curriculum VitaeAditya SinghalNo ratings yet
- Transformative Change at PPLDocument24 pagesTransformative Change at PPLAli A. KhokhArNo ratings yet
- KINDRED HEALTHCARE, INC 10-K (Annual Reports) 2009-02-25Document329 pagesKINDRED HEALTHCARE, INC 10-K (Annual Reports) 2009-02-25http://secwatch.comNo ratings yet
- DPWH Cost EstimationDocument67 pagesDPWH Cost EstimationAj Abe92% (12)
- 4 A Industrial RevolutionDocument41 pages4 A Industrial Revolutionabekhti2008No ratings yet
- Taxation Philippine Tax and Income System Assignments and QuizdocxDocument20 pagesTaxation Philippine Tax and Income System Assignments and QuizdocxMicaella ShayneNo ratings yet
- MF 660Document7 pagesMF 660Sebastian Vasquez OsorioNo ratings yet
- Successfully Allocating Risk and Negotiating A PPP ContractDocument12 pagesSuccessfully Allocating Risk and Negotiating A PPP ContractWilliam Tong100% (1)
- BPI vs. Posadas, G.R. No. L - 34583, 1931Document8 pagesBPI vs. Posadas, G.R. No. L - 34583, 1931Nikko AlelojoNo ratings yet
- Spectrochem Chemindex 2016 17Document122 pagesSpectrochem Chemindex 2016 17Nivedita Dube0% (1)
- Lucero Flores Resume 2Document2 pagesLucero Flores Resume 2api-260292914No ratings yet
- D.E.I Technical College, Dayalbagh Agra 5 III Semester Electrical Engg. Electrical Circuits and Measurements Question Bank Unit 1Document5 pagesD.E.I Technical College, Dayalbagh Agra 5 III Semester Electrical Engg. Electrical Circuits and Measurements Question Bank Unit 1Pritam Kumar Singh100% (1)
- Shell Omala s2 GX 320 TdsDocument2 pagesShell Omala s2 GX 320 TdsOnie Hammamz OylNo ratings yet
- 1.1 Cruz v. DENR PDFDocument7 pages1.1 Cruz v. DENR PDFBenBulacNo ratings yet
- BW-Africa 2023 BrochureDocument12 pagesBW-Africa 2023 BrochureDanial DarimiNo ratings yet
- Chapter 1Document2 pagesChapter 1Reymond Homigop GalarpeNo ratings yet
- Water Cooled Centrifugal Chiller (150-3000RT)Document49 pagesWater Cooled Centrifugal Chiller (150-3000RT)remigius yudhiNo ratings yet
- Aermod - DRM - Course NotesDocument25 pagesAermod - DRM - Course NotesGhulamMustafaNo ratings yet
- JQuery Interview Questions and AnswersDocument5 pagesJQuery Interview Questions and AnswersShailesh M SassNo ratings yet
- Refference 01 Sheethal Visa Rejection Reason ExplanationDocument3 pagesRefference 01 Sheethal Visa Rejection Reason ExplanationAniket PatelNo ratings yet
- Chapter IDocument38 pagesChapter ITuyền PhạmNo ratings yet
- Section 12-22, Art. 3, 1987 Philippine ConstitutionDocument3 pagesSection 12-22, Art. 3, 1987 Philippine ConstitutionKaren LabogNo ratings yet
- 2008 Reverse Logistics Strategies For End-Of-life ProductsDocument22 pages2008 Reverse Logistics Strategies For End-Of-life ProductsValen Ramirez HNo ratings yet
- Beneparts Quotation BYBJ192388 20191024Document1 pageBeneparts Quotation BYBJ192388 20191024احمد عبدهNo ratings yet
- MushroomDocument8 pagesMushroomAkshay AhlawatNo ratings yet
- The Van Conversion Bible - The Ultimate Guide To Converting A CampervanDocument170 pagesThe Van Conversion Bible - The Ultimate Guide To Converting A CampervanPil100% (3)
- JKR SPJ 1988 Standard Specification of Road Works - Section 1 - GeneralDocument270 pagesJKR SPJ 1988 Standard Specification of Road Works - Section 1 - GeneralYamie Rozman100% (1)
- LOVDocument43 pagesLOVMei FadillahNo ratings yet
- Understanding FreeRTOS SVCDocument11 pagesUnderstanding FreeRTOS SVCshafi hasmani0% (1)
- Foreclosure of REMDocument10 pagesForeclosure of REMShanelle NapolesNo ratings yet