Professional Documents
Culture Documents
Quiz 1 Crypto CS01083112
Uploaded by
65xh6w6jsqOriginal Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Quiz 1 Crypto CS01083112
Uploaded by
65xh6w6jsqCopyright:
Available Formats
CCSB3113: Cryptography
Quiz 1
DATE: 31/10/2023; TIME: 10:40 AM
Name - LINGGAESWARAN
Student ID: CS01083112
Section 1: Choose one answer.
Q1. What is the main aim of cryptography?
a. To make information completely inaccessible to unauthorized parties
b. To make information only partially accessible to authorized parties
c. To make information more convenient to access
d. To make information more prone to interception
Q2. Which type of cryptography uses a single key for both encryption and decryption?
a. Symmetric cryptography
b. Asymmetric cryptography
c. Quantum cryptography
d. Steganography
Q3. The process of converting plaintext into unreadable scrambling can be called:
a. Decryption
b. Encryption
c. Hashing
d. Encoding
Q4. What type of cryptographic attack enabling an attacker to observe one or more plaintext–ciphertext pairs
that are formed with the secret key. In this attack the attacker also is trying to derive information from the
differences in the ciphertext to reveal the plaintext?
a. Known-Plaintext Attack
b. Brute Force Attack
c. Frequency Analysis
d. Chosen Ciphertext Attack
Q5. Which of the following is NOT a symmetric encryption algorithm?
a. AES
b. RSA
c. DES
d. None of the above
Q6. What type of cryptographic technique involves replacing each letter in the plaintext with another letter to
maintain the original letter’s position in the alphabet, such as shifting the alphabet by a fixed number of
positions in a Caesar Cipher?
a. Substitution Cipher
b. Transposition Cipher
c. Vigenère Cipher
d. Keyless Transposition Cipher
Q7. In a transposition cipher, how does the encryption process work?
a. Letters are replaced with different letters based on a predefined substitution table.
b. A combination of letters and symbols are used to represent the plaintext.
c. Letters are shifted by a fixed number of positions in the alphabet.
d. The position of letters in the plaintext is changed, but the letters themselves remain the same.
Q8. Which of the following statements is true about the security of substitution and transposition ciphers?
a. Substitution ciphers are generally more secure than transposition ciphers.
b. Transposition ciphers are generally more secure than substitution ciphers.
c. Both substitution and transposition ciphers are considered highly secure in modern cryptography.
d. Both substitution and transposition ciphers are vulnerable to modern cryptographic attacks and are not
considered secure for protecting sensitive information.
Q9. Encrypt the word: STUDENT with key: UNITEN using Vigenère Cipher. A Table is attached in Appendix 1.
a. NRIVLRL
b. FRKMYEY
c. LFCUUJW
d. MGCWIAN
Q10. Encrypt the following word with Caesar Cipher. Word= I LIKE CRYPTOGRAPHY; Key= +24.
a. M PMOI GVCTXSKVETLC
b. K NKMG ETARVQITCRJA
c. F IFHB ZOVMQLDOXMEV
d. G JGIC APWNRMEPYNFW
How to answer Question 1: 2A or 5C
Section 2: Short Answer.
1. Explain the concept of a substitution cipher and provide an example.
A substitution cipher is a method of encrypting messages by replacing letters with other letters or
symbols based on a predetermined key.
Example:
Plaintext: HELLO
Key: H->X, E->Q, L->M, O->A
Encrypted: XQMMA
2. Define a transposition cipher and describe its working principle. Provide one example of a
transposition encryption technique.
A transposition cipher is a method that rearranges the letters of the plaintext in a specific way, without
changing the letters themselves and Transposition ciphers are relatively simple to implement and can
be quite effective against brute-force attacks, but they can be vulnerable to frequency analysis attacks.
One example of a transposition encryption technique is the columnar transposition cipher. which works
by writing the plaintext out in rows and then rearranging the columns in a different order.
You might also like
- CnsDocument7 pagesCnsSunny KumarNo ratings yet
- Ijret - Enhancing Security of Caesar Cipher Using Different MethodsDocument6 pagesIjret - Enhancing Security of Caesar Cipher Using Different MethodsInternational Journal of Research in Engineering and TechnologyNo ratings yet
- Cryptography and Network Security MsmeDocument27 pagesCryptography and Network Security Msmesanthosh n prabhuNo ratings yet
- MCQ - Cryptography BasicsDocument8 pagesMCQ - Cryptography Basicsvikes singh100% (1)
- Cryptography: BY, Ayesha FarhinDocument41 pagesCryptography: BY, Ayesha FarhinnidhirgusainNo ratings yet
- InfoSecurity Lect Week3Document31 pagesInfoSecurity Lect Week3Shaheer ArshadNo ratings yet
- U21CS601 CT Unit 123 Part B QADocument13 pagesU21CS601 CT Unit 123 Part B QASanthosh kannaNo ratings yet
- Cryptography Stallings CH02 AnswersDocument6 pagesCryptography Stallings CH02 Answerszaikoryu100% (1)
- Cryptex TutDocument15 pagesCryptex Tutaditya7398No ratings yet
- Classical Encryption TechniquesDocument36 pagesClassical Encryption Techniquesباسل طفورNo ratings yet
- CH 3Document46 pagesCH 3አርቲስቶቹ Artistochu animation sitcom by habeshan memeNo ratings yet
- Cryptography BankDocument6 pagesCryptography BankLady BugNo ratings yet
- Test Bank For Cryptography and Network Security Principles and Practice 6th Edition by Stallings ISBN 0133354695 9780133354690Document36 pagesTest Bank For Cryptography and Network Security Principles and Practice 6th Edition by Stallings ISBN 0133354695 9780133354690stacyfoxiwdmxzntys100% (22)
- Unit 1 Part1Document73 pagesUnit 1 Part1CSK Marana waiter100% (1)
- Unit IIDocument27 pagesUnit II20AD022 KAMALI PRIYA SNo ratings yet
- Ch3 CryptoDocument90 pagesCh3 CryptoArif AbdulelamNo ratings yet
- Chapter 2 IAS)Document41 pagesChapter 2 IAS)Abduu MizaabNo ratings yet
- Cryptography and The Public Key InfrastructureDocument2 pagesCryptography and The Public Key InfrastructureAli MaksumNo ratings yet
- Cryptography NotesDocument24 pagesCryptography NotesAsif KoujaganurNo ratings yet
- Application of Linear Algebra in Cryptography - Judithlopez - S20216454WDocument14 pagesApplication of Linear Algebra in Cryptography - Judithlopez - S20216454WJudithNo ratings yet
- P02-Symmetric-key Encryption 3Document56 pagesP02-Symmetric-key Encryption 3omar.alnajjar.3001No ratings yet
- 598 3156 1 PBDocument8 pages598 3156 1 PBstephenlim7986No ratings yet
- Unit - Ii: Traditional Symmetric-Key CiphersDocument124 pagesUnit - Ii: Traditional Symmetric-Key Cipherssanthosh RNo ratings yet
- Practical Lesson 3Document2 pagesPractical Lesson 3Famous BusinessmanNo ratings yet
- Chapter 2 & 3Document20 pagesChapter 2 & 3Yakubu AliuNo ratings yet
- CSS Module 1Document108 pagesCSS Module 1bexid78084No ratings yet
- Module 1 PDFDocument18 pagesModule 1 PDFYashaswiniNo ratings yet
- Various Ciphers in Classical CryptographyDocument8 pagesVarious Ciphers in Classical CryptographySHAURYA SINGHNo ratings yet
- Dr. Muhammad Zubair AhmadDocument84 pagesDr. Muhammad Zubair AhmadUzair Maya100% (1)
- CryptographyDocument23 pagesCryptographyVagi GowdaNo ratings yet
- Group AssignmentDocument16 pagesGroup AssignmentJoelNo ratings yet
- C&NS Unit-1Document35 pagesC&NS Unit-1gayatriNo ratings yet
- Nis Que Bank Unit 3Document1 pageNis Que Bank Unit 3localhost54322No ratings yet
- NSC Unit Important QuestionsDocument50 pagesNSC Unit Important Questionsyuvaraaj aletiNo ratings yet
- Classical CryptographyDocument19 pagesClassical CryptographyMahiya Rahman RafaNo ratings yet
- Lec26 28 (Cryptography)Document6 pagesLec26 28 (Cryptography)Vaibhav JainNo ratings yet
- Classical Encryption Techniques: M. Odeo LecturerDocument39 pagesClassical Encryption Techniques: M. Odeo LecturerSNo ratings yet
- Encryption StandardsDocument76 pagesEncryption Standardsbhasker7100% (1)
- Is Lab ManualDocument114 pagesIs Lab ManualprathamgunjNo ratings yet
- Computer Security and Cryptography ExamsDocument6 pagesComputer Security and Cryptography ExamsLucien YemahNo ratings yet
- Chapter 3 - Cryptography and Encryption TechniquesDocument88 pagesChapter 3 - Cryptography and Encryption TechniquesEthio FanaNo ratings yet
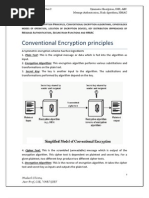
- Introduction To Cryptography Conventional Encryption ModelDocument6 pagesIntroduction To Cryptography Conventional Encryption ModelpaagalsaalaNo ratings yet
- Seminar RepDocument55 pagesSeminar RepArpit SharmaNo ratings yet
- Ins ImpDocument41 pagesIns ImpLAPPY HUBNo ratings yet
- 4.cryptography Handout 2Document87 pages4.cryptography Handout 2Miki AberaNo ratings yet
- Classical Encryption TechniqueDocument18 pagesClassical Encryption TechniquetalebmuhsinNo ratings yet
- Me NSEC ch3Document85 pagesMe NSEC ch3hassan darwishiNo ratings yet
- IT1352-part A B QADocument10 pagesIT1352-part A B QAsujithamohanNo ratings yet
- Unit 1 - 2022Document177 pagesUnit 1 - 2022Ghetiya NirajNo ratings yet
- Lecture#02 Part 1 - Classical Encryption TechniquesDocument30 pagesLecture#02 Part 1 - Classical Encryption TechniquesfasihNo ratings yet
- Lecture#02 - Classical Encryption TechniquesDocument57 pagesLecture#02 - Classical Encryption TechniquesfasihNo ratings yet
- Symmetric Encryption, DES, AES, MAC, Hash Algorithms, HMACDocument76 pagesSymmetric Encryption, DES, AES, MAC, Hash Algorithms, HMACMukesh86% (7)
- BlockChain Technology & Blueprint Ultimate Guide: Learn Everything You Need To Know For Beginners & ExperiencedFrom EverandBlockChain Technology & Blueprint Ultimate Guide: Learn Everything You Need To Know For Beginners & ExperiencedNo ratings yet
- Nomenclatura - Encyclopedia of modern Cryptography and Internet Security: From AutoCrypt and Exponential Encryption to Zero-Knowledge-Proof Keys [Paperback]From EverandNomenclatura - Encyclopedia of modern Cryptography and Internet Security: From AutoCrypt and Exponential Encryption to Zero-Knowledge-Proof Keys [Paperback]No ratings yet
- New Frontiers in Cryptography: Quantum, Blockchain, Lightweight, Chaotic and DNAFrom EverandNew Frontiers in Cryptography: Quantum, Blockchain, Lightweight, Chaotic and DNANo ratings yet
- Practical Cryptography in Python: Learning Correct Cryptography by ExampleFrom EverandPractical Cryptography in Python: Learning Correct Cryptography by ExampleNo ratings yet
- Cryptography And Computer Science: Design Manual For Algorithms, Codes And CiphersFrom EverandCryptography And Computer Science: Design Manual For Algorithms, Codes And CiphersNo ratings yet
- BreakevenDocument4 pagesBreakevenmichaelurielNo ratings yet
- Well Control Daily Checklist Procedure VDocument13 pagesWell Control Daily Checklist Procedure VmuratNo ratings yet
- Modular Construction in Oil & Gas - The EPC PerspectiveDocument3 pagesModular Construction in Oil & Gas - The EPC PerspectiveSandeep DalviNo ratings yet
- POV 6 Build For CloudDocument1 pagePOV 6 Build For Cloudsriram tennetiNo ratings yet
- Full Text 02Document95 pagesFull Text 02Vineeth VsNo ratings yet
- Old Engineering Physics Question PaperDocument1 pageOld Engineering Physics Question PaperHithes PathiyilNo ratings yet
- Error AnalysisDocument6 pagesError Analysisagbas20026896No ratings yet
- TALLY TIPS, TRICKS AND HACKS - Tallypdf PDFDocument11 pagesTALLY TIPS, TRICKS AND HACKS - Tallypdf PDFBhanwar Singh RathoreNo ratings yet
- Thanh Tri BridgeDocument43 pagesThanh Tri Bridgeminhan220979No ratings yet
- Car and Driver Buyer's Guide 2010Document151 pagesCar and Driver Buyer's Guide 2010killjoymsfNo ratings yet
- Film Processor: Operation ManualDocument42 pagesFilm Processor: Operation ManualCamila LopezNo ratings yet
- Intellectual Property Rights: and Starting A New BusinessDocument49 pagesIntellectual Property Rights: and Starting A New BusinessintubeNo ratings yet
- PPG-Self Directed Workforce Company OverviewDocument3 pagesPPG-Self Directed Workforce Company OverviewKrishNo ratings yet
- Powerpoint TemplateDocument12 pagesPowerpoint TemplateMarina ZaharciucNo ratings yet
- DocumentsDocument135 pagesDocumentsupsc.bengalNo ratings yet
- HVAC Maintenance PDFDocument13 pagesHVAC Maintenance PDFКирилл СоколовNo ratings yet
- CHF Impact Assessment Somali RegionDocument58 pagesCHF Impact Assessment Somali RegionYousuf INo ratings yet
- Annual Report 14 PDFDocument96 pagesAnnual Report 14 PDFgopalNo ratings yet
- Problem Set: Exchange Rates: International EconomicsDocument16 pagesProblem Set: Exchange Rates: International EconomicsLucia Yuste MoreiraNo ratings yet
- Research Paper On N Queen ProblemDocument7 pagesResearch Paper On N Queen Problemxvrdskrif100% (1)
- Thesis Abhishek MishraDocument45 pagesThesis Abhishek Mishrasuperiorsambrial examcellNo ratings yet
- Science, Technology, and Society: World History: Chapter OutlineDocument7 pagesScience, Technology, and Society: World History: Chapter OutlineRhea PicaNo ratings yet
- G.R. No. 193138, August 20, 2018 Aniceto G. Saludo, JR., Petitioner, V. Philippine National BANK, Respondent. Decision Jardeleza, J.Document12 pagesG.R. No. 193138, August 20, 2018 Aniceto G. Saludo, JR., Petitioner, V. Philippine National BANK, Respondent. Decision Jardeleza, J.Gellian eve OngNo ratings yet
- Passenger Ship FamiliarisationDocument130 pagesPassenger Ship FamiliarisationChalet Balnear GoaNo ratings yet
- 1 2019年5月亚太语法Document16 pages1 2019年5月亚太语法lin zhuNo ratings yet
- GE 4 Clyden'sDocument3 pagesGE 4 Clyden'sJoe RandyNo ratings yet
- Marketing 3rd Quarter ReviewerDocument10 pagesMarketing 3rd Quarter ReviewerJohn Cris BuanNo ratings yet
- PETE 411 Well Drilling: Surge and Swab PressuresDocument40 pagesPETE 411 Well Drilling: Surge and Swab PressuresJosue FishNo ratings yet
- CH 02Document35 pagesCH 02greeshmaNo ratings yet
- Powerpoint Presentation Dissertation DefenseDocument4 pagesPowerpoint Presentation Dissertation DefenseIDon'TWantToWriteMyPaperNorthLasVegas100% (1)


















































![Nomenclatura - Encyclopedia of modern Cryptography and Internet Security: From AutoCrypt and Exponential Encryption to Zero-Knowledge-Proof Keys [Paperback]](https://imgv2-2-f.scribdassets.com/img/word_document/421844479/149x198/e9c664736d/1617232007?v=1)