Professional Documents
Culture Documents
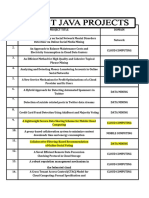
Final List DOT NET2012 IEEE Projects
Uploaded by
subathra31300 ratings0% found this document useful (0 votes)
2 views6 pagesCopyright
© © All Rights Reserved
Available Formats
DOC, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as DOC, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
2 views6 pagesFinal List DOT NET2012 IEEE Projects
Uploaded by
subathra3130Copyright:
© All Rights Reserved
Available Formats
Download as DOC, PDF, TXT or read online from Scribd
You are on page 1of 6
.
NET IEEE Projects List
Projects on Data Mining:
1. Adding Temporal Constraints to XML Schema
2. Combining Tag and Value Similarity for Data Extraction and Alignment
3. Coupled Behavior Analysis with Applications
4. Data Mining for XML Query-Answering Support
5. Document Clustering in Correlation Similarity Measure Space
6. Efficient and Effective Duplicate Detection in Hierarchical Data
7. Efficient Extended Boolean Retrieval
8. Organizing User Search Histories
9. Publishing Search Logs—A Comparative Study of Privacy Guarantees
10. Clustering with Multiviewpoint-Based Similarity Measure
11. Slicing: A new Approach for Privacy Preserving Data Publishing
12. Optimizing Bloom Filter Settings in Peer-to-Peer Multi-keyword Searching
13. Efficient Fuzzy Type-Ahead Search in XML Data
14. Outsourced Similarity Search on Metric Data Assets
Projects on Networking:
15. Finding Cheap Routes in Profit-Driven Opportunistic Spectrum Access
Networks: A Truthful Mechanism Design Approach
16. Online Adaptive Compression in Delay Sensitive Wireless Sensor Networks
17. AMPLE: An Adaptive Traffic Engineering System Based on Virtual Routing
Topologies
18. Design and Implementation of TARF: A Trust-Aware Routing Framework
for WSNs
19. SPOC: A Secure and Privacy-preserving Opportunistic Computing
Framework for Mobile-Healthcare Emergency
Web site: www.liotech.in
www.liotechprojects.com
Email id: liotechprojects@gmail.com
Contact no: 8519950799
.NET IEEE Project List
20. Topology control in mobile ad hoc Networks with cooperative
communications
Projects on Network Security:
21. A Hybrid Approach to Private Record Matching
22. Enabling Secure and Efficient Ranked Keyword Search over Outsourced
Cloud Data
23. On Privacy of Encrypted Speech Communications
24. Persuasive Cued Click-Points: Design, Implementation, and Evaluation of
a Knowledge-Based Authentication Mechanism
25. Privacy-Preserving Enforcement of Spatially Aware RBAC
26. Revisiting Defenses against Large-Scale Online Password Guessing
Attacks
27. Scalable and Secure Sharing of Personal Health Records in Cloud
Computing using Attribute-based Encryption
28. Security of Bertino-Shang-Wagstaff Time-Bound Hierarchical Key
Management Scheme for Secure Broadcasting
29. Enhancing Data Trustworthiness via Assured Digital Signing
30. Exploring Context and Content Links in Social Media: A Latent Space
Method
Projects on Mobile Computing:
31. An Iterative Algorithm for Trust Management and Adversary Detection
for Delay- Tolerant Networks
32. Message Drop and Scheduling in DTNs: Theory and Practice
33. Thwarting Control-Channel Jamming Attacks from Inside Jammers
34. Avoiding the Rush Hours: WiFi Energy Management via Traffic Isolation
35. Design of Efficient Multicast Protocol for IEEE 802.11n WLANs and
Cross-Layer Optimization for Scalable Video Streaming
Web site: www.liotech.in
www.liotechprojects.com
Email id: liotechprojects@gmail.com
Contact no: 8519950799
36. A Trigger Identification Service for Defending Reactive Jammers in WSN
37. Resource-Aware Video Multicasting via Access Gateways in Wireless
Mesh Networks
38. Low Power Consumption Solutions for Mobile Instant Messaging
39. Converge Cast: On the Capacity and Delay Tradeoffs
40. Catching Packet Droppers and Modifiers in Wireless Sensor Networks
41. Network Assisted Mobile Computing with Optimal Uplink Query
Processing
42. ES-MPICH2: A Message Passing Interface with Enhanced Security
43. Detection and Localization of Multiple Spoofing Attackers in Wireless
Networks
44. Cooperative Download in Vehicular Environments
45. Uncoordinated Cooperative Communications in Highly Dynamic
Wireless Networks
46. The Three-Tier Security Scheme in Wireless Sensor Networks with
Mobile Sinks
Projects on Image Processing:
47. Automatic Image Equalization and Contrast Enhancement Using
Gaussian Mixture Modeling
48. Image Authentication Using Distributed Source Coding
49. Analyzing Image Deblurring Through Three Paradigms
50. Smile Detection by Boosting Pixel Differences
51. Fast Vanishing-point Detection in Unstructured Environments
52. An Online Learning Approach to Occlusion Boundary Detection
53. Robust Face-Name Graph Matching for Movie Character Identification
54. Shadow Removal Using Bilateral Filtering
55. Combining Head Pose and Eye Location Information for Gaze Estimation
Web site: www.liotech.in
www.liotechprojects.com
Email id: liotechprojects@gmail.com
Contact no: 8519950799
.NET IEEE Project List
56. A Secret-Sharing-Based Method for Authentication of Grayscale
Document Images via the Use of the PNG Image With a Data Repair
Capability
57. Distributed Throughput Maximization in Wireless Networks via Random
Power Allocation
Projects on Cloud Computing:
58. Cashing in on the Cache in the Cloud
59. Cooperative Provable Data Possession for Integrity Verification in Multi-
Cloud Storage
60. pCloud: A Distributed System for Practical PIR
61. Cloud Computing Security: From Single to Multi-Clouds
62. Privacy-Preserving Public Auditing for Secure Cloud Storage
63. Monitoring Service Systems from a Language-Action Perspective
64. HASBE: A Hierarchical Attribute-Based Solution for Flexible and Scalable
Access Control in Cloud Computing
65. Ensuring Distributed Accountability for Data Sharing in the Cloud
66. Enhanced Data Security Model for Cloud Computing
New projects:
1. Ensuring Distributed Accountability for Data Sharing in the Cloud
2. Enhanced Data Security Model for Cloud Computing
3. Catching Packet Droppers and Modifiers in Wireless Sensor Networks
4. Cloud Computing Security: From Single to Multi-Clouds
5. Privacy-Preserving Public Auditing for Secure Cloud Storage
6. Monitoring Service Systems from a Language-Action Perspective
7. HASBE: A Hierarchical Attribute-Based Solution for Flexible and
Scalable Access Control in Cloud Computing
8. Network Assisted Mobile Computing with Optimal Uplink Query
Processing
Web site: www.liotech.in
www.liotechprojects.com
Email id: liotechprojects@gmail.com
Contact no: 8519950799
9. A Message Passing Interface with Enhanced Security
10. Detection and Localization of Multiple Spoofing Attackers in Wireless
Networks(video available)
11. Exploring Context and Content Links in Social Media: A Latent Space
Method
12. Cooperative Download in Vehicular Environments
13. Uncoordinated Cooperative Communications in Highly Dynamic
Wireless Networks
14 The Three-Tier Security Scheme in Wireless Sensor Networks with
Mobile Sinks
15. Distributed Throughput Maximization in Wireless Networks via
Random Power Allocation(video available)
16. Efficient Fuzzy Type-Ahead Search in XML Data
17. Creating Evolving User Behavior Profiles Automatically
18. Outsourced Similarity Search on Metric Data Assets
19. A Genetic Programming Approach to Record Deduplication
Web site: www.liotech.in
www.liotechprojects.com
Email id: liotechprojects@gmail.com
Contact no: 8519950799
You might also like
- Intelligent Vehicular Networks and Communications: Fundamentals, Architectures and SolutionsFrom EverandIntelligent Vehicular Networks and Communications: Fundamentals, Architectures and SolutionsRating: 1 out of 5 stars1/5 (1)
- Miller, T.J.E. - SPEED's Electric MotorsDocument307 pagesMiller, T.J.E. - SPEED's Electric Motorsmiculurs100% (13)
- Computer Science Project IdeasDocument3 pagesComputer Science Project IdeasMallikarjun Rao100% (1)
- Dhaval Patel Ccna Rectify FaultsDocument12 pagesDhaval Patel Ccna Rectify FaultsDhaval PatelNo ratings yet
- SiemensEnergy IndustrialHeatPumpsDocument25 pagesSiemensEnergy IndustrialHeatPumpsHélder FernandoNo ratings yet
- Non Idrive To Cic Retrofit Vlad's E92 (MR - Vys)Document6 pagesNon Idrive To Cic Retrofit Vlad's E92 (MR - Vys)leonNo ratings yet
- Ieee 2022-23 Cse TitlesDocument5 pagesIeee 2022-23 Cse TitlesNexgen TechnologyNo ratings yet
- 2014 Total 70 List TitlesDocument7 pages2014 Total 70 List TitlesDhanunjayReddyNo ratings yet
- Ieee 2021-22 Java and DotnetDocument18 pagesIeee 2021-22 Java and DotnetNexgen TechnologyNo ratings yet
- Ieee 2013 Java ProjectsDocument3 pagesIeee 2013 Java ProjectsSagar Paul'gNo ratings yet
- Final Java TitlesDocument1 pageFinal Java TitlessushikumNo ratings yet
- IEEE Java Projects List - SPARKTECH 8904892715Document8 pagesIEEE Java Projects List - SPARKTECH 8904892715utsav thNo ratings yet
- MSC Intern Titles 2019Document7 pagesMSC Intern Titles 2019Harikrishnan ShunmugamNo ratings yet
- IEEE 2010 TitlesDocument3 pagesIEEE 2010 TitlesSiva PrasadNo ratings yet
- Java IEEE Projects ListDocument3 pagesJava IEEE Projects ListVenkat SaiNo ratings yet
- Ieee Java List 9959969919Document1 pageIeee Java List 9959969919Saidi ReddyNo ratings yet
- Big Data Analytics, Machine Learning and Network Security TopicsDocument11 pagesBig Data Analytics, Machine Learning and Network Security TopicsSanjay KumarNo ratings yet
- S.No Java (IEEE-2016) : Data Mining Over Encrypted Data On CloudDocument8 pagesS.No Java (IEEE-2016) : Data Mining Over Encrypted Data On CloudShanmugaSundaram CbeNo ratings yet
- Project TitlesDocument4 pagesProject TitlesVasanth KumarNo ratings yet
- 2010 IEEE New Titles on Data, Java & NetworksDocument2 pages2010 IEEE New Titles on Data, Java & Networksvinaiz1984No ratings yet
- 14 New IEEE Latest TitlesDocument13 pages14 New IEEE Latest Titlesgpramesh75No ratings yet
- Java IEEE 2015 Project ListDocument3 pagesJava IEEE 2015 Project Listanand kumarNo ratings yet
- Dot Net Titles 2013-2014Document3 pagesDot Net Titles 2013-2014onepointerNo ratings yet
- 2014 and 2015 IEEE ProjectsDocument7 pages2014 and 2015 IEEE ProjectsTmksManjuNo ratings yet
- Project IdeasDocument6 pagesProject IdeasSidraKhanNo ratings yet
- Computer Science ProjectsDocument2 pagesComputer Science ProjectspothirajkalyanNo ratings yet
- 2017-2018 Software Ieee Final Year Project TitlesDocument2 pages2017-2018 Software Ieee Final Year Project Titlesmindworkz proNo ratings yet
- Computer Science Project ListDocument8 pagesComputer Science Project ListALi FarHanNo ratings yet
- Project TitleDocument8 pagesProject TitleVishakha YadavNo ratings yet
- Techno Info Solutions: Java Ieee 2015Document5 pagesTechno Info Solutions: Java Ieee 2015immurugappanNo ratings yet
- Statistical method with POW consensus approach for cloud and fog computingDocument10 pagesStatistical method with POW consensus approach for cloud and fog computingPRATIMA ACHARYANo ratings yet
- Major Project ListDocument11 pagesMajor Project ListNationalinstituteDsnrNo ratings yet
- Project IdeasDocument107 pagesProject IdeasShobhitNo ratings yet
- Java TitlesDocument1 pageJava TitlesteamcseNo ratings yet
- Dot Net Ieee 2011 Projects ListsDocument4 pagesDot Net Ieee 2011 Projects Listsservices4projectsNo ratings yet
- PVR Technologies 2015-16 Java TitlesDocument4 pagesPVR Technologies 2015-16 Java TitlesPvrtechnologies NelloreNo ratings yet
- Final Year Project Ideas For Computer Science and Engineering StudentsDocument8 pagesFinal Year Project Ideas For Computer Science and Engineering StudentsFatin NinieNo ratings yet
- Computer Science Projects For College StudentsDocument3 pagesComputer Science Projects For College Studentsnagasaikiran ponnapalliNo ratings yet
- Technologies ..: CreativeDocument20 pagesTechnologies ..: CreativeAditya PrakashNo ratings yet
- Java Projects-2023Document5 pagesJava Projects-2023veerendranathNo ratings yet
- Major Java Project ListDocument8 pagesMajor Java Project ListveerendranathNo ratings yet
- IEEE - 2013 E-Soft IT SotluionsDocument32 pagesIEEE - 2013 E-Soft IT SotluionsSarayu NagarajanNo ratings yet
- Java - Ieee 2012: S.No. Project Title DomainDocument2 pagesJava - Ieee 2012: S.No. Project Title DomainRamesh AnkathiNo ratings yet
- Best Ieee Java IEEE Topics 2017-2018: Cloud ComputingDocument2 pagesBest Ieee Java IEEE Topics 2017-2018: Cloud Computingnandhaku2No ratings yet
- S.N O Project Title TechDocument2 pagesS.N O Project Title TechSriKanthNo ratings yet
- 1 4020 5263 4Document427 pages1 4020 5263 4Jyothsna Priya KattakindaNo ratings yet
- Javaieee 2010&2009Document2 pagesJavaieee 2010&2009Srinivas MuppalaNo ratings yet
- DOT NET 2013 IEEE PROJECTSDocument3 pagesDOT NET 2013 IEEE PROJECTSSitaram ChikkalaNo ratings yet
- Dot Net Ieee Projects List:: MR - Venkatsai 9642222622 Www.3tinfotech - CoDocument2 pagesDot Net Ieee Projects List:: MR - Venkatsai 9642222622 Www.3tinfotech - CoVenkat SaiNo ratings yet
- IEEE Projects & Software Developments by ECWAY TechnologiesDocument2 pagesIEEE Projects & Software Developments by ECWAY TechnologiesRaghu NathNo ratings yet
- Edge Intelligence For Next Generation Wireless NetworksDocument2 pagesEdge Intelligence For Next Generation Wireless Networkstnerber3586No ratings yet
- Dear Candidate: Real Time IT, IEEE and VLSI Projects For 2009 Batch Passed Out StudentsDocument9 pagesDear Candidate: Real Time IT, IEEE and VLSI Projects For 2009 Batch Passed Out StudentsSvsn Sandeep SvsnNo ratings yet
- Computer Science & It TopicsDocument5 pagesComputer Science & It Topics2306 Karthick TNo ratings yet
- List of Topics ForMTPDocument4 pagesList of Topics ForMTPpassworsNo ratings yet
- Dot Net Ieee Project Titles 2017 - 2018: For More Details Contact MR - SARAVANAN - +91 9751812341Document10 pagesDot Net Ieee Project Titles 2017 - 2018: For More Details Contact MR - SARAVANAN - +91 9751812341Kpsmurugesan KpsmNo ratings yet
- Synopsis Format and Suggested Project TitlesDocument7 pagesSynopsis Format and Suggested Project TitlesKartik Wadehra100% (1)
- Title Here: S.A. Engineering College, Chennai - 77. Department of CseDocument50 pagesTitle Here: S.A. Engineering College, Chennai - 77. Department of CseArvind S KumarNo ratings yet
- List of IEEE Projects - 2011Document3 pagesList of IEEE Projects - 2011sushikumNo ratings yet
- 2014 Ieee Project Dotnet TitlesDocument6 pages2014 Ieee Project Dotnet TitlesRaghu NathNo ratings yet
- IEEE PROJECTS 2012 - 2013: www.6ss - inDocument6 pagesIEEE PROJECTS 2012 - 2013: www.6ss - inBala BalaNo ratings yet
- AbstractDocument1 pageAbstractprojectinbangalore279No ratings yet
- Project Ideas: JAVA IEEE Project ListDocument2 pagesProject Ideas: JAVA IEEE Project ListPankaj BanshiwalNo ratings yet
- Java TitlesDocument2 pagesJava TitlesapexhrmailNo ratings yet
- Network Coding: Fundamentals and ApplicationsFrom EverandNetwork Coding: Fundamentals and ApplicationsMuriel MedardNo ratings yet
- Course Title Instructor: Managing Customer Experience and Relationships: A Strategic FrameworkDocument11 pagesCourse Title Instructor: Managing Customer Experience and Relationships: A Strategic FrameworkAyyaz ReshiNo ratings yet
- Cannon Pixma Ip2000 ManualDocument92 pagesCannon Pixma Ip2000 ManualJames Melo-Gurny BobbyNo ratings yet
- First CP Propellers with Fuel-saving Kappel BladesDocument4 pagesFirst CP Propellers with Fuel-saving Kappel BladesFuchsbauNo ratings yet
- Satcon 500 KW Inverter SpecDocument4 pagesSatcon 500 KW Inverter SpecSagar SinghNo ratings yet
- Use of Source MAC Address Field in SpannDocument6 pagesUse of Source MAC Address Field in SpannPraveen RaiNo ratings yet
- OSI ModelDocument5 pagesOSI Modelcemerlang satuNo ratings yet
- Online EarningDocument3 pagesOnline Earningwordwork373No ratings yet
- Brochure Club V SeriesDocument8 pagesBrochure Club V SeriesAlberto PanameñoNo ratings yet
- SLS-7.5.3-L-095 BioVIEW and BioVID 1080+ Spec Sheet For EmailDocument4 pagesSLS-7.5.3-L-095 BioVIEW and BioVID 1080+ Spec Sheet For Email2095nanoNo ratings yet
- Siwes RDocument52 pagesSiwes RDr Mo EntertainmentNo ratings yet
- Control AveoDocument42 pagesControl AveoKiko GonzalezNo ratings yet
- Amuel Arbone: BjectiveDocument1 pageAmuel Arbone: BjectiveLol jkNo ratings yet
- Burn ISO Images Natively in Windows 7Document8 pagesBurn ISO Images Natively in Windows 7Meghana JainNo ratings yet
- Medical RoboticsDocument5 pagesMedical Roboticsapi-355890357No ratings yet
- Power Electronics & SCRDocument55 pagesPower Electronics & SCRsoumyaranjan_kar34No ratings yet
- Massey Ferguson 263 TRACTORS (GB) Service Parts Catalogue Manual (Part Number 819774)Document14 pagesMassey Ferguson 263 TRACTORS (GB) Service Parts Catalogue Manual (Part Number 819774)zhuangfuqian31No ratings yet
- Hydraulic Regenerative Braking System PDFDocument12 pagesHydraulic Regenerative Braking System PDFhai dangNo ratings yet
- Media Queries BreakpointsDocument1 pageMedia Queries BreakpointsMaría del MarNo ratings yet
- MGT 513 Technology Forecasting and Assessment Fall 2014Document14 pagesMGT 513 Technology Forecasting and Assessment Fall 2014Arun VenkatesanNo ratings yet
- MACC Manual Guide Solid State Converter Installation Operation MaintenanceDocument26 pagesMACC Manual Guide Solid State Converter Installation Operation Maintenancelnoriega9637No ratings yet
- G Ym 6 F 8 HEtoev 4 GEbDocument6 pagesG Ym 6 F 8 HEtoev 4 GEbPrakhar AgarwalNo ratings yet
- Clio Brochure Uk PDFDocument52 pagesClio Brochure Uk PDFTõnis TranzeNo ratings yet
- Asterisk Installation On Centos 5Document3 pagesAsterisk Installation On Centos 5kumargupt117No ratings yet
- GP 48-04Document27 pagesGP 48-04snikraftar1406No ratings yet
- Various Methods For Transistor Biasing Hand WrittenDocument3 pagesVarious Methods For Transistor Biasing Hand WrittenPaulo Louies Ordonio Dimasangal100% (1)
- Charles H. Cox III Analog Optical Links Theory and Practice Cambridge Studies in Modern OpDocument303 pagesCharles H. Cox III Analog Optical Links Theory and Practice Cambridge Studies in Modern OpAG Octavio100% (1)