Professional Documents
Culture Documents
Final Corporate Presentation
Final Corporate Presentation
Uploaded by
Neil TOriginal Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Final Corporate Presentation
Final Corporate Presentation
Uploaded by
Neil TCopyright:
Available Formats
IHIL
Fihil Company Profile
IHIL Services Pvt. Ltd
www.fihil.com
IHIL
Company Profile
Multi Disciplinary BUSINESS RISK
Practices spans assurance services, consulting MANAGEEMNT
services and information risk management
Large Client Base
Covers banking, financial services, telecom,
manufacturing and insurance services
INFORMATION RISK
MANAGEMENT
Thought Leadership
Ahead of curve with thought leadership
Our
efforts in BFSI / telecom industry Verticals
CONSULTING &
Experience COMPLIANCE
Our team has over 60 man years of serviing
experience across industries
Team
TECHNOLOGY
Experts comprising of Bankers, IT Specialists,
MBAs, engineers and lawyers
Confidential @ Fihil Services Pvt Ltd www.fihil.com 2
IHIL
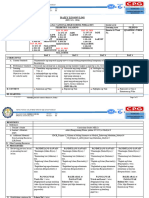
Business Risk Management Offerings
Technology Advisory
Advisory on technology and business
integrations
Technology Advisory
Internal Audit
Internal Audit
Check and continuous improvement
framework for management
Process Reviews
Governance controls reviews for the smooth
operations and sustenance
Fraud Risk Management Process Reviews
Technology Assurance
Technology review for the management and
compliance assurance
Technology Assurance Fraud Risk Management
Evaluation and Assessment of the fraud and
its impacts
Confidential @ Fihil Services Pvt Ltd www.fihil.com 3
IHIL
Information Risk Management Offerings
IT Governance Controls System Audits Mobile Audit Source Code Audit Vulnerability Tests
Governance review for technology System audits for applications, and Mobile Application Security Review of the source code for security Assessment of the security posture of
including systems, networks, infrastrucute Assessment loopholes the infrastructure / systems
application
Data Center Audit Business Continuity Plan Disaster Recovery Security Operation Forensic Investigation
Data Center review for benchmarks Review of existing business continuity Disaster Recovery Readiness Center
Security Operations in compliance with Forensic Investigation for frauds
and internal controls plan Assessment industry standards
Confidential @ Fihil Services Pvt Ltd www.fihil.com 4
IHIL
Consulting & Compliance Offerings
Technology Regulatory
Consulting Compliance ISO Compliances
Technology evaluation, cloud RBI, IRDA, TRAI, SEBI, SOX, ISO 27001,, ISO 22301, ISO
services, hybrid operations HIPAA Implementation and 20000-1, ISO 27701, ISO
Assurance 27018, ISO 27032, ISO 9001,
ISO
Cyber Compliance
Assistance in implementation
Process Consulting Industrial and assurance for cyber
Governance controls, Policies, Compliances compliance
Procedures, Realignment PCI DSS, PA DSS,,
consulting and assistance
Confidential @ Fihil Services Pvt Ltd www.fihil.com
IHIL
IT Audits
Application Security Cloud Security
Geplis dipsam volorib vendian debist Geplis dipsam volorib vendian debist
lignist quantium temab lignist quantium temab
Implementation Assurance
Geplis dipsam volorib vendian debist
Network Security
lignist quantium temab
Geplis dipsam volorib vendian debist
lignist quantium temab
Compliance Audit
Geplis dipsam volorib vendian debist
System Security lignist quantium temab
Geplis dipsam volorib vendian debist
lignist quantium temab
IT
Security
Confidential @ Fihil Services Pvt Ltd www.fihil.com 6
IHIL
Cyber Security Services
IDENTIFY
Cyber Security deliverables I We can help you pinpoint and identify the
necessary assets
Our team of experts can assist your
PROTECT
team to create the robust and
compliant cyber security framework P Our experts can help you to design the
appropriate level of controls around your assets
for your management and compliance
needs, DETECT
Our programs are custom tailored to
D Our expert team can help you to design and
implement best practices for smooth operations
address your specific needs.
RESPOND
R We can help you to design a proper response
mechanism around your cyber security incidents
RECOVER
C Our experts can help you to design and test
your recovery mechanism in record time
Confidential @ Fihil Services Pvt Ltd www.fihil.com 7
IHIL
Security Audits
Vulnerability Assessment and Penetration Testing Services
APPLICATION
SECURITY
Web and Standalone Application
SECURITY AUDIT & ASSURANCE
security services
SERVICES
Our team of experts having latest update on the
IOT & DEVICES SECURITY
MOBILE SECURITY applicable security for your systems can assist you for
Security of the IoT devices and
Android, iOS application and the identification of your security baseline.
systems
transaction security services
Our experts in addition to security experience carry
various certifications like CEH, CISSP, OSCP, CISA,
CIPP,
NETWORK
Our team will provide you the assistance to
SCADA SECURITY SECURITY
Geplis dipsam volorib vendian
identify your security baseline. Our experts
Robotic and Automation devices debist lignist quantium
can pinpoint the exact applicable solution
security services
instead of regular recommendations.
API SECURITY
Your API gateway security
assessment services
Confidential @ Fihil Services Pvt Ltd www.fihil.com 8
IHIL
Our Compliance Portfolio
Implementation, Assessment and Trainings
Our team can assist you in any of the above compliances. To demonstrate your
strength and assurance for the regulatory and non regulatory requirements.
Confidential @ Fihil Services Pvt Ltd www.fihil.com 9
IHIL
Case Study : Network Security in Trading Platform
Root Cause
SECURITY OF INFRASTRUCTURE It was found that due to non configuration of the integrity verification, the
system is susceptible to the unauthorised bypass of the system
Trading platform has implemented a new
network protocol as a part of infrastructure Detection
improvement. Before implementation of the During the security checks, it is found that the system can be bypassed. The
technology,, it is given a test run for testing attack is simulated though manual tools
purpose.
Correction
The integrity checks controls are implemented which has prevented the
bypass of the system
Prevention
Through security verification of implemented system the security loophole I
s closed.
Confidential @ Fihil Services Pvt Ltd www.fihil.com 10
IHIL
Case Study : Device Security in Payment Platform
Root Cause
SECURE PAYMENT DEVICES The communication from device to backed server is not encrypted
A Bank was testing a new payment hardware
device. As a part of the new payment platform Detection
support through embedded devices the devices During security checks, it is found that if the communication between
are designed with necessary security device and backed server was intercepted, it can be easily read and modified
leading to fraudulent transactions
requirements.
Correction
Communication channel is encrypted using the strong dynamic level of
encryption
Prevention
The fraudulent modification is prevented using this security testing
Confidential @ Fihil Services Pvt Ltd www.fihil.com 11
IHIL
Case Study : Application Security Mobile Platform
Root Cause
A cryptocurrency exchange wallet The security keys and wallet transaction token ID are not linked with each
other. These IDs are not validated for the transaction purpose
A mobile wallet is a frontend of an
cryptocurrency exchange platform. All the Detection
transactions were performed through the During the security testing we have found that bitcoin exchange addresses
mobile wallets are validated through integrity checks.
Correction
The security keys and transactions are validated before transaction for
verification through user
Prevention
Thus an identity impersonation attack was prevented on the cryptocurrency
wallet.
Confidential @ Fihil Services Pvt Ltd www.fihil.com 12
IHIL
Case Study : API Security
Root Cause
Digital Identity Provider The API gateway was vulnerable to identity impersonation checks because
of lack of two-way verification prior to onboarding
A Digital Identity Provides is using the API
for franchise interfaces. All the franchisees Detection
were connected through API gateway. All the During the testing we observed that the server is not validating the
transactions were performed through the API franchisee and users along with the user data at server side before
processing the identity generation service
gateway. They wanted to test the solution for
security purposes. Correction
A two-way verification for user and franchisee was implemented for end
users and franchisee operators.
Prevention
Due to early detection, the end user identity impersonation fraud is
prevented
Confidential @ Fihil Services Pvt Ltd www.fihil.com 13
IHIL
Case Study : Technology Performance Consulting
Root Cause
Global Multilocation Setup Due to recent acquisitions and setup integrations, the systems are not
defined a coordinated synchronised schedule
A testing laboratory has a setup across the
globe in various domain. They have a Detection
centralised Identity and Access Management The server load coming from multiple locations is extracted and correlated
Server in Germany. The server was facing with network bandwidth data to identify the exact issue
heavy utilization despite having recommended
hardwares Correction
The geographies are defined with a scheduled synchronization along with
trust configurations
Prevention
Thus the system is utilised in an effective way to manage the user identity
and access load across the globe
Confidential @ Fihil Services Pvt Ltd www.fihil.com 14
IHIL
Case Study : Compliance Implementation Consulting
Training
Automobile Manufacturing Company We have trained the teams for their respective roles in Business Continuity
Business Continuity Management System.
The company was looking for a consultant Framework Implementation
who can assist them in alignment towards the Alignment of the processes, Impact Assessment, Risk Prioritizations,
ISO 22301 framework. Operational Processes alignment, Implementation Roamap
Operational Guidance
Alignment of Policies and Procedures. Testing and execution of Failure
Scenarios and Reporting
Internal & External Assessment
Internal Review through independent auditor. And Certification through the
Certifying Agency
Confidential @ Fihil Services Pvt Ltd www.fihil.com 15
IHIL
Case Study : Breach Investigation in Banking Platform
Root Cause
Unauthorised transactions The end user mobile was taken remote control by a malware application that
stole the transaction codes
Unauthorised transactions has been performed
through mobile banking. During the daily Detection
review it has been noticed that there are During the review of the user account, applications, networks, it has been
unauthorised transactions performed in a user found that user was conned to install a remote malware software. The
software created a backdoor on mobile to read and write user data on mobile
account
Correction
The user is made aware about such transactions and mobile application is
updated to stop such interception of data through encryption and other
methods
Prevention
Such frauds are prevented by creating a user awareness campaigns and
through the application protection controls
Confidential @ Fihil Services Pvt Ltd www.fihil.com 16
IHIL
Our Approach
DOMAIN EXPERTS TECHNOLOGY EXPERTS
Our domain experts that suit your need work Expert in technology implementation and operations
very closely with your team aim to identify your pain areas and suggest a most
suitable solution
INDUSTRIAL CONSULTANTS GOVERNANCE EXPERTS
Expert opinion across the globe are
People who are expert in people management and
used to give you’re the best
process work closely with you to achieve the results
achievable result
in defined time
Confidential @ Fihil Services Pvt Ltd www.fihil.com 17
IHIL
Our Leadership Team
Expert Team for your one stop solution
Name Experience Sector
Nikhil Firke 12 Assurance, Technology, Compliance
Kishor Mohite 25 Governance, Process, Compliance
Sameer Sawant 25 Technology, Process
Sanjay Gore 40 Governance, Process, Technology, Compliance
Vinayak N 18 Technology, Compliance
Shirish D 28 Process, Technology, Assurance
Sujit Varma 16 Technology
Shruti S 20 Financial Assurance
Shruti P 10 Training
Confidential @ Fihil Services Pvt Ltd www.fihil.com 18
IHIL
Project Governance
Objective Project Governance
Fihil Team Client Team
Feedback and ENGAGEMENT MANAGEMENT LEAD
Corrections
DIRECTOR PROJECT MANAGER
Benchmarking
Review Meeting
ENGAGEMENT
MANAGER
Regular Review ENGAGEMENT PROJECT MANAGER
Issues and Action Plan
MANAGER TEAM LEAD
ENGAGEMENT LEAD Team Reporting and Review
Day to Day Issues ENGAGEMENT LEAD TEAM LEAD
ENGAGEMENT TEAM
Day to Day Interaction
Escalation Matrix
Escalation Level Engagement Lead Engagement Manager Engagement Director
Issue Unresolved For 1 day 3 days 5 days
Confidential @ Fihil Services Pvt Ltd www.fihil.com
IHIL
Roles and Responsibilities
ENGAGEMENT TEAM MANAGER DIRECTOR VALUE ADDS
o Day to day interaction with o Regular interaction with o Technical inputs and quality
process owners and onsite / offsite specialist team review of the deliverables
stakeholders o Exhaustive reviews of daily o Close looping of the exceptions
o Obtain understanding of activities and deliverables from a business perspective
system and processes o Time to time coordination with o Monthly onsite interaction with
o Extraction of data and data process owners and the team and Ooredoo
analytics stakeholders management
o Updation of standard operating o Monitoring of team activities o Quarterly meetings and
procedures o Reporting of daily / weekly / updates to senior management
o Cross departmental monthly dashboards and
coordination of revenue update meeting with
assurance activities stakeholders
o Prompt escalations for o Draft deliverable discussion
observations and project issues and inputs on leading practices
Confidential @ Fihil Services Pvt Ltd www.fihil.com
IHIL
Our Clientele
Confidential @ Fihil Services Pvt Ltd www.fihil.com
IHIL
Thank You
Contact Person: Nikhil Firke
Email : nikhil.firke@fihil.com || Website: www.fihil.com || Phone: +91-8169697915
Address:
Head Office: 5, Girijeet Apartment, Lane 1-C, Badhan, Pune – 411021
Mumbai Office: Samarth Ashish, Lane 3, jai Hind Colony, Dombivali (W), Thane 421202
Email : info@fihil.com || Website: www.fihil.com || Phone: +91-8169697915
Confidential @ Fihil Services Pvt Ltd www.fihil.com
You might also like
- FINAL Letter of Application-Bsp 2 (Edited)Document13 pagesFINAL Letter of Application-Bsp 2 (Edited)almharie Estela100% (5)
- General Conditions of Passenger and Baggage CarriageDocument51 pagesGeneral Conditions of Passenger and Baggage CarriageŞəmsəddin CəfərovNo ratings yet
- Module E & F FinalDocument40 pagesModule E & F Finalonthelinealways100% (1)
- Auditing Information Systems: Enhancing Performance of the EnterpriseFrom EverandAuditing Information Systems: Enhancing Performance of the EnterpriseNo ratings yet
- Adopting Principles of World Class Manufacturing WCM To Drive EHS ExcellenceDocument77 pagesAdopting Principles of World Class Manufacturing WCM To Drive EHS ExcellenceYe BarronNo ratings yet
- Culminating Activity 2021 - Btt1O-A Franchise Proposal (20%)Document2 pagesCulminating Activity 2021 - Btt1O-A Franchise Proposal (20%)GR - 09CT 733899 North Park SSNo ratings yet
- Ohio Department of Job and Family Services Contract Amendment #9 C-2021-14-0677-9Document21 pagesOhio Department of Job and Family Services Contract Amendment #9 C-2021-14-0677-9Dan MonkNo ratings yet
- SAP Hybris Architecture PDFDocument30 pagesSAP Hybris Architecture PDFSuresh SuresettiNo ratings yet
- EY Advisory ServicesDocument3 pagesEY Advisory ServicesPhil LewisNo ratings yet
- Data Analytics Getting Started and Beyond 2-9 2016 Experis PresentationDocument51 pagesData Analytics Getting Started and Beyond 2-9 2016 Experis Presentationinfo-499850No ratings yet
- Assessment For ComplianceDocument21 pagesAssessment For CompliancearunalrnNo ratings yet
- Next Gen Ia GovernanceDocument11 pagesNext Gen Ia GovernanceAlexchandar AnbalaganNo ratings yet
- Policy Development & The 4 Cobit Domain ProcessesDocument18 pagesPolicy Development & The 4 Cobit Domain ProcessesJasper Bollen100% (1)
- 4 SOC Consulting v5Document54 pages4 SOC Consulting v5berrezegNo ratings yet
- ePROTECT 360 - Managed Security Services Presentation - BOCH Systems-CostDocument28 pagesePROTECT 360 - Managed Security Services Presentation - BOCH Systems-CostKevin AniNo ratings yet
- 4 SOC ConsultingDocument54 pages4 SOC Consultingriadelidrissi100% (3)
- IcfrDocument12 pagesIcfrAnupam BaliNo ratings yet
- ePROTECT 360 - Corporate - ProfileDocument27 pagesePROTECT 360 - Corporate - ProfileKevin AniNo ratings yet
- Synoptek Company Profile v1.0Document49 pagesSynoptek Company Profile v1.0Diwakar BindoraNo ratings yet
- 01) Risk Based Internal Audit - CA. Rachana DaftaryDocument37 pages01) Risk Based Internal Audit - CA. Rachana DaftaryL N Murthy KapavarapuNo ratings yet
- IT Audit Awareness 2303pdfDocument34 pagesIT Audit Awareness 2303pdfAARTI MaidNo ratings yet
- Update Intro To IT Audit Support v4Document41 pagesUpdate Intro To IT Audit Support v4Handayani Tri WijayantiNo ratings yet
- About PT PISTIS DIGITAL INDONESIA - v0.2 PDFDocument11 pagesAbout PT PISTIS DIGITAL INDONESIA - v0.2 PDFBudi Setiawan SantosoNo ratings yet
- Internal Audit Risk Assessment Audit Committee ReportDocument14 pagesInternal Audit Risk Assessment Audit Committee ReportKatka JánošíkováNo ratings yet
- IT GovernanceDocument31 pagesIT Governancehank moodyNo ratings yet
- Kuliah Ke 6 Thema: Fungsi, Map Proses Dan Nilai / Target Performansi (Kpi) Security ManagementDocument60 pagesKuliah Ke 6 Thema: Fungsi, Map Proses Dan Nilai / Target Performansi (Kpi) Security Managementolivil juenNo ratings yet
- KPMG - Nigeria - Transforming Internal Audit and Control Through Digital InnovationDocument21 pagesKPMG - Nigeria - Transforming Internal Audit and Control Through Digital InnovationPablo Cuevas CalvettiNo ratings yet
- IT Risk Management FinalDocument11 pagesIT Risk Management Finalmohamed aliNo ratings yet
- Accounting Management Presentation Ver 2Document34 pagesAccounting Management Presentation Ver 2Aries H MunandarNo ratings yet
- HRM PresnDocument9 pagesHRM Presndilsediltak_01No ratings yet
- Tapestry-SOC 2 Proposal - Visionet StaffingDocument10 pagesTapestry-SOC 2 Proposal - Visionet StaffingNaveenchdrNo ratings yet
- 3 Module 1Document91 pages3 Module 1Divyesh yadavNo ratings yet
- Admission, Recruitment & Assessment ServicesDocument6 pagesAdmission, Recruitment & Assessment ServicesNeha SinghNo ratings yet
- Hedge Funds Capability ModelDocument8 pagesHedge Funds Capability ModelCapability ModelNo ratings yet
- Mohammed Akber Hussaini Syed - 19575 - R - BDocument2 pagesMohammed Akber Hussaini Syed - 19575 - R - Bsohaib siddiqueNo ratings yet
- Pengawasan Era 4.0Document23 pagesPengawasan Era 4.0bnkp thomasNo ratings yet
- Oneecm Profile Fy23 v3Document15 pagesOneecm Profile Fy23 v3abdelrahman zyadaNo ratings yet
- CIA - Part 3 - OrientationDocument23 pagesCIA - Part 3 - OrientationBhargav BandaruNo ratings yet
- PWC Pharma Internal AuditDocument3 pagesPWC Pharma Internal AuditYogesh BhardwajNo ratings yet
- Developing The IT Audit PlanDocument36 pagesDeveloping The IT Audit PlanDelis SiledNo ratings yet
- GTAG 10 - Biz Cont - Forweb CX1 PDFDocument40 pagesGTAG 10 - Biz Cont - Forweb CX1 PDFpiornelNo ratings yet
- Internal Audit HospitalDocument30 pagesInternal Audit HospitalReddy Shekar PNo ratings yet
- 8 - Secure Risk Solutions (SRS)Document10 pages8 - Secure Risk Solutions (SRS)Nour elshikhNo ratings yet
- Introduction of IT GovernanceDocument22 pagesIntroduction of IT GovernanceRudi RudiNo ratings yet
- SHARE 2012-1ation SecurityDocument25 pagesSHARE 2012-1ation SecurityAntwan BellNo ratings yet
- CA Enterprise SecurityDocument7 pagesCA Enterprise SecurityRAMNo ratings yet
- 0318 TEC Cyber Security Brochure PDFDocument4 pages0318 TEC Cyber Security Brochure PDFDinesh GuptaNo ratings yet
- World-Class Functionality For All Business Users' NeedsDocument20 pagesWorld-Class Functionality For All Business Users' NeedsBalaji MugunthanNo ratings yet
- Itrm FinalDocument5 pagesItrm Finalmohamed aliNo ratings yet
- 02 - AFA - PPT - Unit 5Document38 pages02 - AFA - PPT - Unit 5tfknrNo ratings yet
- Section-Wise and Skill-Wise Weightage: Final (Old) Paper 6: Information Systems Control and Audit (100 Marks)Document3 pagesSection-Wise and Skill-Wise Weightage: Final (Old) Paper 6: Information Systems Control and Audit (100 Marks)Anil AntonyNo ratings yet
- IT Governance - Performance Measures FinalDocument34 pagesIT Governance - Performance Measures FinalYuvi RajhaNo ratings yet
- Internet of Things and Smart Manufacturing Internet of Things and Smart ManufacturingDocument20 pagesInternet of Things and Smart Manufacturing Internet of Things and Smart ManufacturingSherry SherNo ratings yet
- Gain A Complete View of Risk & ComplianceDocument22 pagesGain A Complete View of Risk & ComplianceAnonymous FGHdopuaYNo ratings yet
- CustomerConnect Apr2020 Enterprise Digital Transformation Using IoT Blockchain AIDocument24 pagesCustomerConnect Apr2020 Enterprise Digital Transformation Using IoT Blockchain AIslavikgNo ratings yet
- Inter CA EIS - Chapter 1Document81 pagesInter CA EIS - Chapter 1Ready 4 BooyahNo ratings yet
- Next Gen BankingDocument8 pagesNext Gen BankingTarang Shah0% (1)
- 1.ISAUD - Information Technology Risk and Controls PDFDocument28 pages1.ISAUD - Information Technology Risk and Controls PDFRabbani AzizNo ratings yet
- DSS Overview and UpdatesPresentationDecember2013Document17 pagesDSS Overview and UpdatesPresentationDecember2013Mona BakriNo ratings yet
- COBIT 2019 Overview - v1.1Document38 pagesCOBIT 2019 Overview - v1.1Stephanie GumapacNo ratings yet
- GICs Talent Report 1Document18 pagesGICs Talent Report 1DS PNo ratings yet
- Governance of the Extended Enterprise: Bridging Business and IT StrategiesFrom EverandGovernance of the Extended Enterprise: Bridging Business and IT StrategiesNo ratings yet
- Integrated Project Control: State of the Art Reports 1987 SeriesFrom EverandIntegrated Project Control: State of the Art Reports 1987 SeriesA D BerryNo ratings yet
- Fihil Services Detailed BrochureDocument47 pagesFihil Services Detailed BrochureNeil TNo ratings yet
- Microsoft Technologies Applications Architecture ReviewDocument7 pagesMicrosoft Technologies Applications Architecture ReviewNeil TNo ratings yet
- A Practical Approach To Ipv6 MigrationDocument14 pagesA Practical Approach To Ipv6 MigrationNeil TNo ratings yet
- How To Implement ModSecurity OWASP Core Rule Set in NginxDocument2 pagesHow To Implement ModSecurity OWASP Core Rule Set in NginxNeil TNo ratings yet
- NGINX Tuning For Best PerformanceDocument5 pagesNGINX Tuning For Best PerformanceNeil TNo ratings yet
- WordPress Security GuideDocument13 pagesWordPress Security GuideNeil TNo ratings yet
- PLDT AcoDocument1 pagePLDT AcoWesNo ratings yet
- 55966bos45368may20 p5 cp3 PDFDocument26 pages55966bos45368may20 p5 cp3 PDFankush sharmaNo ratings yet
- Immediate Resignation Letter TemplateDocument1 pageImmediate Resignation Letter TemplateDeejay FarioNo ratings yet
- 16791438752764yK1bDoQ8rrIwoU2 PDFDocument8 pages16791438752764yK1bDoQ8rrIwoU2 PDFSurajNo ratings yet
- OxfordAQA 9625 BU02 WRE Jun22 v1.0Document4 pagesOxfordAQA 9625 BU02 WRE Jun22 v1.0MirandaxxNo ratings yet
- Citizen's Hand Book Volume-ViiDocument196 pagesCitizen's Hand Book Volume-ViisuranjanacNo ratings yet
- Site Meeting 01Document4 pagesSite Meeting 01Fakrul AdliNo ratings yet
- Full Download Multinational Financial Management 10th Edition Shapiro Solutions Manual PDF Full ChapterDocument36 pagesFull Download Multinational Financial Management 10th Edition Shapiro Solutions Manual PDF Full Chaptertightlybeak.xwf5100% (19)
- Company Law: Assignment ONDocument10 pagesCompany Law: Assignment ONsandeepNo ratings yet
- The Production of Specialty RubberDocument2 pagesThe Production of Specialty RubberfebiantiNo ratings yet
- Warranty: VFD-V SeriesDocument1 pageWarranty: VFD-V Seriestricky777No ratings yet
- IGCSE RecruitmentDocument29 pagesIGCSE RecruitmentIan Julius AlcarazNo ratings yet
- MFRS 137 (CH 5)Document30 pagesMFRS 137 (CH 5)WAN AMIRUL MUHAIMIN WAN ZUKAMALNo ratings yet
- PYQ June 2018Document4 pagesPYQ June 2018Nur Amira NadiaNo ratings yet
- Meagal Stelplast Steering A New PathDocument12 pagesMeagal Stelplast Steering A New PathAnirban KarNo ratings yet
- Financial Management: I. Concept NotesDocument6 pagesFinancial Management: I. Concept NotesDanica Christele AlfaroNo ratings yet
- Cobit 5 (Part 1) YesDocument35 pagesCobit 5 (Part 1) YesNandaaa SuryaNo ratings yet
- VaselineDocument8 pagesVaselinenurul9535No ratings yet
- Abstract Blue Cube PowerPoint TemplatesDocument13 pagesAbstract Blue Cube PowerPoint TemplatesNguyễn SơnNo ratings yet
- Ifrs Edition: Prepared by Coby Harmon University of California, Santa Barbara Westmont CollegeDocument79 pagesIfrs Edition: Prepared by Coby Harmon University of California, Santa Barbara Westmont CollegeJhoni LieNo ratings yet
- List of Submitted ProjectDocument4 pagesList of Submitted ProjectBhagyashreeNo ratings yet
- DLL - Q2 - Fil8 - Week 8Document6 pagesDLL - Q2 - Fil8 - Week 8Felibeth SaladinoNo ratings yet
- CSRA at Galance ISAE 3410 FinalDocument6 pagesCSRA at Galance ISAE 3410 FinalELTIN YULI ASTUTINo ratings yet
- Theories & Concept in International MarketingDocument18 pagesTheories & Concept in International MarketingKath De GuzmanNo ratings yet
- CSS Fee Structure Table Must Set in System Based On CSS's Prakas - Current Year PDFDocument1 pageCSS Fee Structure Table Must Set in System Based On CSS's Prakas - Current Year PDFsimchandoeunNo ratings yet
- Lock Out Tag Out ProceduresDocument52 pagesLock Out Tag Out ProceduresDavid Arputharaj100% (5)