Professional Documents
Culture Documents
Emerging Threats: BRKSEC-2001
Uploaded by
jeffgrantinctOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Emerging Threats: BRKSEC-2001
Uploaded by
jeffgrantinctCopyright:
Available Formats
Emerging Threats
BRKSEC-2001
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 2
© 2008, Cisco Systems, Inc. All rights reserved. 1
14330_04_2008_c1.scr
Agenda
What? Where? Why?
Trends
Year in Review
Case Studies
Threats on the Horizon
Threat Containment
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 3
What?
Where?
Why?
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 4
© 2008, Cisco Systems, Inc. All rights reserved. 2
14330_04_2008_c1.scr
What? Where? Why?
What is a Threat?
A warning sign of possible trouble
Where are Threats?
Everywhere you can, and more importantly cannot, think of
Why are there Threats?
The almighty dollar (or euro, etc.), the underground cyber crime
industry is growing with each year
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 5
Examples of Attacks
Targeted Hacking
Malware Outbreaks
Economic Espionage
Intellectual Property Theft or Loss
Network Access Abuse
Theft of IT Resources
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 6
© 2008, Cisco Systems, Inc. All rights reserved. 3
14330_04_2008_c1.scr
Where Can I Get Attacked?
Operating System
Network Services
Applications
Users
Attack Attack
Anywhere Everywhere
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 7
Operational Evolution of Threats
Emerging Threat
Threat Evolution Unresolved Threat
Nuisance Threat
Policy and
Reaction
Socialized Formalized
Process Reactive Process
Process Process
Definition
Operational
Mitigation
Burden
Human Automated
Technology Manual Process
“In the Loop” Response
Evolution
End-User
Support
Burden
End-User No End-User “Help-Desk” Aware—
Increasingly
Awareness Knowledge Know Enough to Call
Self-Reliant
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 8
© 2008, Cisco Systems, Inc. All rights reserved. 4
14330_04_2008_c1.scr
Operational Evolution of Threats
Emerging Threat
Threat Evolution Unresolved Threat
Nuisance Threat
Policy and
Reaction
Socialized Formalized
Process Reactive Process
Process Process
Definition Operational
Mitigation
Burden
Human Automated
Technology Manual Process
“In the Loop” Response
Evolution
End-User
Support
Burden
End-User No End-User “Help-Desk” Aware—
Increasingly
Awareness Knowledge Know Enough to Call
Self-Reliant
“New”, Unknown, or Largest Volume of Problems
Problems We Haven’t Focus of Most of Day to Day
Solved Yet Security Operations
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 9
Why?
Fame
Not so much anymore (more on this with Trends)
Money
The root of all evil…(more on this with the Year in Review)
War
A battlefront just as real as the air, land, and sea
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 10
© 2008, Cisco Systems, Inc. All rights reserved. 5
14330_04_2008_c1.scr
Trends
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 11
Trends
Evolution of Hacker Motivation
No longer the Lone Hacker
The Cybercrime Industry
Hosting Services
Designer Malcode
BotNets
Spyware
Phishing
Fast Flux
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 12
© 2008, Cisco Systems, Inc. All rights reserved. 6
14330_04_2008_c1.scr
Evolution of Motivation
2002 2003 2004 2005 2006 2007 2008
Fame
SQL Slammer Netsky,
Bagle,
MyDoom Money
Zotob
Business
= Major Media Event
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 13
Evolution of Motivation
Fame is not all it’s cracked up to be
To make money effectively and without
detection you need to be unknown
People are prepared for what they know
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 14
© 2008, Cisco Systems, Inc. All rights reserved. 7
14330_04_2008_c1.scr
Operational Evolution of Threats
Emerging Threat
Threat Evolution Unresolved Threat
Nuisance Threat
Policy and
Reaction
Socialized Formalized
Process Reactive Process
Process Process
Definition Operational
Mitigation
Burden
Human Automated
Technology Manual Process
“In the Loop” Response
Evolution
End-User
Support
Burden
End-User No End-User “Help-Desk” Aware—
Increasingly
Awareness Knowledge Know Enough to Call
Self-Reliant
“New”, Unknown, or Largest Volume of Problems
Problems We Haven’t Focus of Most of Day to Day
Solved Yet Security Operations
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 15
No Longer the Lone Hacker
Hackers are forming development teams to work on
creating malicious code
Highly intelligent individuals are collaborating to create
new viruses and other malicious code
Software development tools for handling large projects
are being used
Development is not unlike normal software
development in the IT industry
The shared information and talents of many very skilled
hackers when working together can be worse than any
one working alone
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 16
© 2008, Cisco Systems, Inc. All rights reserved. 8
14330_04_2008_c1.scr
The Cybercrime Industry
Group develops custom malcode
Custom malcode is made available for purchase
ISP administrators are paid to host malicious code on
sites that they control
Malcode collects usernames and passwords as well as
credit card numbers
Credit card numbers and usernames and passwords
are for sale
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 17
Cybercrime Industry: In the Past
Writers Asset End Value
Tool and Toolkit Compromise Fame
Writers Individual Host
or Application
Theft
Malware Writers
Worms Espionage
Compromise (Corporate/
Viruses Environment Government)
Trojans
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 18
© 2008, Cisco Systems, Inc. All rights reserved. 9
14330_04_2008_c1.scr
Cybercrime Industry: Today
First Stage Second Stage
Writers Abusers Middle Men Abusers End Value
Tool and Toolkit Hacker/Direct Fame
Writers Attack Compromised
Host and
Theft
Application
Malware Writers Espionage
Extortionist/ (Corporate/
Machine DDoS-for-Hire Government)
Harvesting Bot-Net Creation
Worms
Extorted Pay-Offs
Viruses Spammer
Bot-Net Management:
For Rent, for Lease, for Commercial Sales
Trojans Sale
Phisher
Fraudulent Sales
Information Personal
Spyware
Harvesting Information
Pharmer/DNS
Poisoning Click-Through
Revenue
Information
Brokerage
Internal Theft: Identity Theft Financial Fraud
Abuse of
Privilege Electronic IP
Leakage
$$$ Flow of Money $$$
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 19
Cybercrime Industry: Hosting Services
Hosting services are for sale as part of the total
package
Hosting sites can hold a database of collected
information
Hosting sites can serve as a sales portal for
individuals wishing to purchase stolen information
Standard rates for data sales are being established
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 20
© 2008, Cisco Systems, Inc. All rights reserved. 10
14330_04_2008_c1.scr
Designer Malcode
Malcode that is designed to bypass virus scanners
is made for sale
Malcode is designed to collect information and upload
it to a database
Backup malcode is also available to replace the
active malcode once it begins to be detected by
virus scanners
Malcode is designed to be very difficult to reverse
engineer, or determine its functionality making it
harder to detect and harder to trace where the
data is being sent
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 21
“Noise” Level
Large Scale Worms
Public
Awareness
Targeted Attacks
2000 2008
Time
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 22
© 2008, Cisco Systems, Inc. All rights reserved. 11
14330_04_2008_c1.scr
Cyber Crime Profit Level
Targeted Attacks
Illicit
Dollars
Gained
Large Scale Worms
2000 2008
Time
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 23
Botnets
Botnet: A collection of compromised machines running programs
under a common command and control infrastructure
Building the Botnet:
Viruses, worms; infected spam; drive-by downloads; etc.
Controlling the Botnet:
Covert-channel of some form; typically IRC or custom IRC-like channel
Historically have used free DNS hosting services to point bots to the IRC server
Recent attempts to sever the command infrastructure of botnets has resulted in
more sophisticated control systems
Control services increasingly placed on compromised high-speed machines
(e.g. in academic institutions)
Redundant systems and blind connects are implemented for resiliency
Further Example as a Case Study
Source: www.wikipedia.com
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 24
© 2008, Cisco Systems, Inc. All rights reserved. 12
14330_04_2008_c1.scr
Using a Botnet to Spend Spam
1. A botnet operator propagates
by viruses, worms, spam,
and malicious websites
2. The PCs log into an IRC
server or other
communications medium
3. A spammer purchases
access to the botnet from
the operator
4. The spammer sends
instructions via the IRC
server to the infected PCs—
5. …causing them to send
out spam messages to
mail servers
Source: www.wikipedia.com
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 25
What about Spyware?
Still a major threat
Drive-by downloads still a major source of infestation
ActiveX vulnerabilities in particular enable this
However, confusing or misleading EULAs still a problem
A Trojan by any other name—
Spyware is increasingly indistinguishable from other forms of malware
Nasty race condition: sheer number of variants makes it very difficult
for technology solutions to hit 100% accuracy at a given moment
Rise of intelligent spyware
Directed advertising is more valuable than undirected
More sophisticated spyware matches user-gathered data with
directed advertising
Bot-based spyware is also more valuable, as it can be updated over time
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 26
© 2008, Cisco Systems, Inc. All rights reserved. 13
14330_04_2008_c1.scr
Phishing, Pharming, and Identity Theft
Phishing Pharming
MUNDO-BANK.COM MUNDO-BANK.COM
ited
olic S
Uns mail DN ning
E is o
Po
172.168.1.1 172.168.1.1
MUNDO- MUNDO-
MUNDO-BANK.COM BANK.COM BANK.COM
Come see us at
www.mundo-bank.com
ine
<172.168.254.254>
Onl
egular ing
172.168.254.254 R Bank 172.168.254.254
Hosts File:
mundo-bank.com = 172.168.254.254
Identity theft continues to be a problem If you’re a target:
Phishing scams growing in sophistication Consider “personalization” technologies
every day (e.g. user-chosen images on a webpage)
Protecting your users: implement some Support identified mail initiatives, like DKIM
technology, but don’t forget user education!!
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 27
Fast Flux
Malicious IP addresses are changing quickly
Botnets are the new DNS Servers
Very low time to live (TTL) in A Record
Infected hosts acting as DNS servers
Traditional DNS-based security measure not
longer effective
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 28
© 2008, Cisco Systems, Inc. All rights reserved. 14
14330_04_2008_c1.scr
What Does this Mean?
People utilizing the emerging threats of today want
them to stay unknown
What you don’t hear about is what you should be
concerned about
Intelligence is important
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 29
Operational Evolution of Threats
Emerging Threat
Threat Evolution Unresolved Threat
Nuisance Threat
Policy and
Reaction
Socialized Formalized
Process Reactive Process
Process Process
Definition
Operational
Mitigation
Burden
Human Automated
Technology Manual Process
“In the Loop” Response
Evolution
End-User
Support
Burden
End-User No End-User “Help-Desk” Aware—
Increasingly
Awareness Knowledge Know Enough to Call
Self-Reliant
“New”, Unknown, or Largest Volume of Problems
Problems We Haven’t Focus of Most of Day to Day
Solved Yet Security Operations
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 30
© 2008, Cisco Systems, Inc. All rights reserved. 15
14330_04_2008_c1.scr
Year in Review
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 31
2007 as a Year
Security fad: Month of Bugs
Fuzzers offer tremendous way to find vulnerabilities
Application vulnerabilities up 17% from 2006
According to the Cisco IntelliShield
Botnets control channels up 57% from 2006
According to ShadowServer.Org
1,200 new websites per day hosting malware
According to MessageLabs
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 32
© 2008, Cisco Systems, Inc. All rights reserved. 16
14330_04_2008_c1.scr
2007 as a Year
Global spam up 50% from 2006, considerable up tick
in types of spam attachment
According to IronPort
One unique phishing scam every 2 minutes in 2007
According to the PhishTank
Over 10 targeted malcode attacks per day, up from
1 per day in 2006
According to MessageLabs
163 million records with personal data compromised
in 2007—up from 48 million in 2006
According to Attrition.Org
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 33
Fuzzers in Action—Month of Bugs
Trend started in Mid 2006 with Month of Browser Bugs
Jan ’07—Month of Apple Bugs (MoAB)
Mar ’07—Month of PHP Bugs (MoPB)
April ’07—Month of MySpace Bugs (MoMYB)
May ’07—Month of ActiveX Bugs (MoAXB)
June ’07—Month of Search Engine Bugs (MoSEB)
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 34
© 2008, Cisco Systems, Inc. All rights reserved. 17
14330_04_2008_c1.scr
Stock Advice from Spam
Canadian company Diamant Art’s stock price tripled
in one day from .08 cents to .25 cents
No positive news released from the company
Spam touting the stock solely responsible for raise
in stock price
Most spam stock only increases stock price ~2%,
which is quickly lost
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 35
Stop Trading Spam Stocks
March 2007 US Securities and Exchange Commission
announced that 25 stocks were going to be suspended
from trading for 10 days
Not viewed as an effective way to stop stock spam
It is a start, government bodies are starting to wake up
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 36
© 2008, Cisco Systems, Inc. All rights reserved. 18
14330_04_2008_c1.scr
F.B.I. Nabs BotHerders
June 2007, the US F.B.I. announced the arrest of
3 different BotHerders who were responsible for over
1 million infected machines
Step in the right direction, even if it was relatively
small group
The real news: If the F.B.I. is on your trail then your
technology has matured
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 37
iPhone Releases, Gets Hacked
July 2007, less than one month
after the US release of Apple’s
highly anticipated iPhone a major
vulnerability was discovered
enabling a complete compromise
New vector, new attack
As other vendors scramble to
match the iPhone in functionality
similar attacks are likely
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 38
© 2008, Cisco Systems, Inc. All rights reserved. 19
14330_04_2008_c1.scr
Google Ads Link to Malicious Sites
December 2007, a security researcher discovers
that several sites using Google ads were linking to
malicious websites
Google swiftly reacted by shutting down the
ad providers
No way to know for certain how many users were
infected nor who was at fault
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 39
Radio Frequency ID (RFID) Cloning
Last 12 months has seen
several different
demonstrations highlighting
technology to clone RFID tags
Legal methods used to
suppress demonstrations
Current demonstrations are
more theoretical and not likely RFID is an automatic
to be easily carried out identification method, relying
on storing and remotely
retrieving data using devices
called RFID tags
- Wikipedia
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 40
© 2008, Cisco Systems, Inc. All rights reserved. 20
14330_04_2008_c1.scr
Pretexting Makes Headlines
Hewlett Packard admits using Pretexting is the act of
pretexting to investigate creating and using an
internal officers invented scenario (the
pretext) to persuade a
Xbox Live accounts suffer from target to release
information or perform
pretexting attacks an action and is usually
Group calling itself Clan Infamous done over the telephone
claimed to steal 10 accounts a day - Wikipedia
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 41
P2P Networks Used for DoS Attacks
Flaw in open source peer-to-peer hub software DC++
Allowed attacker to direct clients to any site resulting
in a DoS
Large amount of blackmail money demanded to
prevent attack
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 42
© 2008, Cisco Systems, Inc. All rights reserved. 21
14330_04_2008_c1.scr
Conclusions from 2007
Botnets have come into their own
Targeted attacks are increasingly the norm
Cybercrime industry pushing “innovation” in malware
Focus on applications
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 43
Case Studies
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 44
© 2008, Cisco Systems, Inc. All rights reserved. 22
14330_04_2008_c1.scr
Case Studies
Corporate Liability
TJX Company’s customer database compromised
Malware in Action
Storm worm analyzed
Malware Industry
Gozi worm’s cybercrime links
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 45
Corporate Liability—About the Company
TJX is the parent company for a family of
discount retailers
United States
Marshalls
TJ-Maxx
HomeGoods
Canada
Winners
HomeSense
UK, Ireland, Germany
TK-Maxx
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 46
© 2008, Cisco Systems, Inc. All rights reserved. 23
14330_04_2008_c1.scr
Corporate Liability—How it Happened
Attack originated at a Marshalls
store in St. Paul, Minnesota
Attackers used telescope-shaped
antenna to read WiFi signals
WiFi enabled price scanners targeted to get
network access info
Once on the network, database was targeted
Data harvesting started mid 2005 and carried
through end of 2006
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 47
Corporate Liability—What was Affected
Initially thought to be 45.6M credit
card numbers compromised, later
updated to 90M
Included “Track 2 Data”
Biggest credit card number heist
in history
Over 80 GB of network traffic send
to outside server
90,000,000
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 48
© 2008, Cisco Systems, Inc. All rights reserved. 24
14330_04_2008_c1.scr
Corporate Liability—Example of Use
Nov. ’06 Florida law enforcement claims at least 10
thieves used credit card data in a gift card scheme
Over $8M in gift cards purchased
6 people tied to gift card scheme were arrested
Gift card scheme was carried out months before
TJX discovered the compromise
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 49
Corporate Liability—Aftermath
Believed to be responsible for between $68M and
$83M fraud in over 13 countries
Class-action consumer lawsuit settled
$20 store voucher
3 years credit monitoring
$20,000 ID Theft Coverage
Banks and financial institutions sued
Yet to be determined
Estimated costs to TJX are over $150M
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 50
© 2008, Cisco Systems, Inc. All rights reserved. 25
14330_04_2008_c1.scr
Corporate Liability—Conclusions
Every company needs to be concerned
Does not have to be credit cards
Governments creating laws requiring disclosure
One incident can cost much more than years of
a quality security infrastructure
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 51
Malware in Action—Storm Worm
Started as PDF spam in early 2007
Evolved to use e-card and YouTube invites
Uses spam with links to malicious sites as main vector
of propagation
Utilizes social engineering techniques to trick users
to malicious sites
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 52
© 2008, Cisco Systems, Inc. All rights reserved. 26
14330_04_2008_c1.scr
Malware in Action—Storm Worm
Email spam example:
To: Tony Hall
From: Dale Hammond
Subject: Dear Friend
Hi. Nice to meet u and my friend operates a company .i have got
something from him and i must say that the quality is so good .SO i tell u
the truth and hope u can connect him and welocme to his website
www.ouregoods.com. If u have any questions u can add
ouregoods@hotmail.com we are pleasure to help ,good luck to u!
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 53
Malware in Action—Storm Worm
Infected 1 BotHerder
Webserver
4
1. BotHerder updates
malcode on webtrap
2. Initiate new spam 3
pointing to webtrap
3. User reads the spam
and clicks link Infected
4. User machine
infected
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 54
© 2008, Cisco Systems, Inc. All rights reserved. 27
14330_04_2008_c1.scr
Malware in Action—Storm Worm
game0.exe—Backdoor/downloader
game1.exe—SMTP relay
game2.exe—Email address stealer
game3.exe—Email virus spreader
game4.exe—DDoS attack tool
game5.exe—Updated copy of Storm Worm dropper
Source: www.secureworks.com
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 55
Malware in Action—Storm Worm
403014 Copy(c:\game0.exe->C:\WINDOWS\disnisa.exe)
77e6bc59 WriteFile(h=7a0)
403038 RegOpenKeyExA
(HKCU\Software\Microsoft\Windows\CurrentVersion\Run)
40305f RegSetValueExA (disnisa)
Copies itself to C:\Windows\disnisa.exe
Set registry to run on startup
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 56
© 2008, Cisco Systems, Inc. All rights reserved. 28
14330_04_2008_c1.scr
Malware in Action—Storm Worm
402ba0 WinExec(w32tm/config/syncfromflags:manual
/manualpeerlist:time.windows.com,time.nist.gov,100)
77e7d0b7 WaitForSingleObject(788,64)
40309b
CreateProcessA(C:\WINDOWS\disnisa.exe,(null),0,(null))
4030df WinExec(netsh firewall set allowedprogram
"C:\WINDOWS\disnisa.exe" enable,100)
Sync with Microsoft Time Server
Start process
Edit firewall rules to allow network access
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 57
Malware in Action—Storm Worm
77e7ac53 CreateRemoteThread(h=ffffffff,
start=404b05)
40da1b bind(b8, port=7018)
40d9c7 listen(h=b8 )
40a262 WaitForSingleObject(d4,2710)
Connect with remote machine
Wait for a command
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 58
© 2008, Cisco Systems, Inc. All rights reserved. 29
14330_04_2008_c1.scr
Hub and Spoke Topology
Controller communicates
directly with bots
Simplest but limited ability
to scale
Single points of failure
BotHerder
DNS record to BotHerder
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 59
Peer To Peer (P2P) Topology
All bots perform
distribution
Multiple paths from
controller to bots
Scales well, very resilient
No single point of failure
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 60
© 2008, Cisco Systems, Inc. All rights reserved. 30
14330_04_2008_c1.scr
Storm Worm Conclusions
Very sophisticated
“Victim of its own success”, yet still difficult to
shut down
Just one example, there are others we don’t
know about
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 61
The Industry in Action: GOZI
GOZI was a custom made application designed
to harvest data
Went undetected for over 50 days
Collected at least 10,000 records belonging to
over 5,000 home users
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 62
© 2008, Cisco Systems, Inc. All rights reserved. 31
14330_04_2008_c1.scr
GOZI: The Discovery
Originally discovered because a user reported that
an account he accessed at work was compromised
Work computer was searched, suspicious malware
discovered
Not one of the 30 leading anti-virus companies
detected Gozi at the time
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 63
GOZI: The Highlights
Targeted SSL data
Modularized code (Professional grade)
Spread through iFrame IE browser vulnerability
No detection in anti-virus produces for weeks, months
Customized to target specific sensitive data
Posted on-line for “customer” purchases of stolen data
Home PCs largely infected
Accounts at top financial, retail, health care, and
government services affected
Estimated black market value of at least $2 million
Source: www.secureworks.com
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 64
© 2008, Cisco Systems, Inc. All rights reserved. 32
14330_04_2008_c1.scr
GOZI: The Investigation
Organization ready to code new undetectable malware
Willing to offer tech support
Others willing to help with infection
Gozi main server located in Russia
Source: www.secureworks.com
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 65
GOZI: Conclusions
Truly a new industry
Pushing the envelop, trying to stay undetected
Operating in countries where it is difficult to get
shut down
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 66
© 2008, Cisco Systems, Inc. All rights reserved. 33
14330_04_2008_c1.scr
Threats on the Horizon
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 67
Threats on the Horizon
Automated social engineering
Web 2.0
Voice over IP threats
Video files format vulnerabilities
Mobile devices
Data leakage
Outsourcing
Distributed workforce
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 68
© 2008, Cisco Systems, Inc. All rights reserved. 34
14330_04_2008_c1.scr
Automated Social Engineering
In an effort to convince users to “click here”, malware
will use collected data to enhance the veracity of
targeted spam
Malcode can scan previous emails in a person’s inbox
and send a “reply”
Simply adding:
Hey,
Forgot to tell you to check out this site:
http://bad.site.com
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 69
Web 2.0
Hugely popular social sites (MySpace, Facebook)
offer many potential victims for attackers
Data easy to gather to assist in targeted attacks
Very dynamic, big potential for buggy software to
be present
Attracts users who are not necessarily computer
proficient
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 70
© 2008, Cisco Systems, Inc. All rights reserved. 35
14330_04_2008_c1.scr
Voice over IP Threats
“Vishing”—voice way to attempt a phishing scheme
Well understood business risk is promoting integration
of security technologies in voice deployments
Limited pool of technical experts on voice within
attacker community
Follow the money: No well-established business model
driving financial incentives to attack
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 71
Voice Security Opportunities
Eavesdropping:
Earliest attacks focused on this (VOMIT); however, effective
deployment of secure voice makes this very difficult (easier to
use other means to access info)
SPIT: SPAM over internet telephony
Potential to be a serious annoyance, but significant barriers to
this being an effective source of profit (Vishing)
Some are technical, but most involve our current use patterns
for telephony (used on a per-phone basis, not in a “list” format)
Denial of service
Disgruntled employees or extortionists may target the voice
infrastructure by a variety of mechanisms
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 72
© 2008, Cisco Systems, Inc. All rights reserved. 36
14330_04_2008_c1.scr
Video File Format Vulnerabilities
Researchers in 2007 continued to uncovered many
important to critical video file format vulnerabilities in:
QuickTime
Real Player
Windows Media Player
Flash
Documented examples of video file attacks in 2007,
not yet mainstream
With rise of video it is only a matter of time
The next “hot” YouTube video just might be dangerous…
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 73
New Opportunity: Proliferation of Devices
The Challenge Opportunities for Attack
• New types of devices are • Attacks on the back-end
joining the network: All of these systems provides an
Hand-helds, smart phones, cameras, ingress point into some form of
tools, physical security systems, etc. back-end system
Both the method of communication
• Diversity of OSs: and the device itself are targets
More devices means more operating
systems and custom applications • Attacks on the device
Proliferation leaves many
• Embedded OSs opportunities for taking control
Process controllers, kiosks, ATMs, of a system
lab tools, etc.
• Attacks on data
IT department often not involved
in procurement—little attention paid Sensitive data is becoming
to security increasingly distributed
and uncontrolled
For example, one environment got
hacked from an oscilloscope
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 74
© 2008, Cisco Systems, Inc. All rights reserved. 37
14330_04_2008_c1.scr
Attacks on Data: Data Leakage
Still a hot topic this year
Broad term encompassing multiple
different challenges:
Security of Data at rest
Security of Data in motion
Identity-based access control
Both malicious and inadvertent disclosures
Issue has become topical typically for “Compliance” reasons
However, broader topic involves business risk management
How do I avoid inadvertent disclosures?
How do I protect my information assets from flowing to my competitors?
How do I avoid ending up in the news?
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 75
Architectural View of Data Leakage:
New Challenges
Server/Application Network Transit End Users Endpoint Systems
Systems
Endpoint
Enforcement Points Internal Consumers
Application
Front End
Endpoint Enforcement
Centralized Data Transit Enforcement Points
Stores: Points
Structured and
Unstructured External Consumers Decentralized Data
Stores
What’s Changed? Enforcement points Technical Translation Problem: How to
and data consumers are roughly reliably test a given data set for membership
the same; however, a new actor in a “unit of information” (e.g. how to
introduced: “Data” verifiably determine if a given mass of bits is
Quantization Problem: How to group “source code”)
data elements into units of information Policy Construction Problem: How to
relevant to the business? scalable build policy for data flows across a
large environment?
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 76
© 2008, Cisco Systems, Inc. All rights reserved. 38
14330_04_2008_c1.scr
Mobile Data Continues: PC on a Stick
New “smart drives” and other similar technology extending
the existing threats to data posed by portable storage
devices
Devices carry a virtual computing environment in a
secure storage, typically plugged in via USB to any
open computer
All workspace, preference, and data information is kept
within the device, but computing resources of the host
machine are used for manipulation and processing
Challenges:
Analogous to SSL VPN security challenges, only now you
can lose the device in a cab
Unknown endpoint environment challenges: keyboard
loggers and splicers, monitor taps, webcams
Malicious software embedded in data or documents
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 77
Trend: Outsourcing
Motivations: Outsourcers have all the potential to
be disgruntled employees in search of revenge, only
more so—outsourcers typically feel less loyalty to the
outsourcing organization
Opportunity: In many organizations, outsourcers are
given full intranet access
Considerations:
How do you balance the need to access required applications while
providing necessary controls to mitigate risk?
When negotiating contracts, are there any provisions for data security
and integrity? Are there any provisions to audit the security posture?
What legal recourses does the organization have in the event of
compromise? Jurisdictional issues, liability and responsibility, etc.
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 78
© 2008, Cisco Systems, Inc. All rights reserved. 39
14330_04_2008_c1.scr
Trend: Distributed Workforce
De-perimeterization is real
True “federated” security systems are a long ways off yet
Layers of defense and policy enforcement are critical
Drop bad traffic as close to the source as possible, but ensure
you’ve
got at least a couple of “last lines of defense”
Costs and risks to data integrity should be a part of any
calculation to adopt new business practices
There may be hidden costs that are not well understood
People and Processes Key to Mitigate Risk
User awareness and effective business processes are as
important to technology solutions
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 79
Coping with Threats
Conclusion and Recommendations
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 80
© 2008, Cisco Systems, Inc. All rights reserved. 40
14330_04_2008_c1.scr
What’s My Exposure?
Appropriate Risk Mitigation
Risk is at the core of all
security policy decisions
With emerging threats,
Level of Mitigation
there’s always something
out there that can affect Risk Averse
your business
Effective understanding Risk Tolerant
of business risk is critical
to determining priorities in
your response plan
Level of Risk Aversion
The Challenge: Every
application is business
critical to someone
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 81
Example: Network-Based
Structured Data Controls
Credit Card Credit Card
1234-5678-9012-3456 Mask XXXX-XXXX-XXXX-3456
Social Security Social Security
123-45-6789 Mask XXX-XX-XXXX
Driver’s License Driver’s License
A123456 Block A123456
Employee ID Employee ID
S-924600 Mask XXXX
Patient ID Patient ID
134-AR-627 Block 134-AR-627
Request
Response
Cisco AVS 3100
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 82
© 2008, Cisco Systems, Inc. All rights reserved. 41
14330_04_2008_c1.scr
Tackling Malware:
Solutions Across the Network
Remote/Branch Office
Data Center
Management
Network
Internet
Connections
Corporate Network
Internet
Corporate
LAN Business
Remote Access Partner
Systems Access
Extranet
Connections
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 83
Tackling Malware:
Solutions Across the Network
Remote/Branch Office
Data Center Endpoint Protection
Infection prevention:
STOP Cisco Security Agent
Management
Infection remediation:
Network GO desktop anti-virus;
Microsoft and other anti-
spyware SW
Internet
Connections
Corporate Network
Internet
STOP
Corporate Network-Based
LAN Business
Content Control
GO Remote Access Partner
Multi-function
Systems Access security devices
GO
Firewalls
STOP
Network Admission Extranet
Control Intrusion prevention
GO Connections
systems
Ensure endpoint
policy compliance Proxies
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 84
© 2008, Cisco Systems, Inc. All rights reserved. 42
14330_04_2008_c1.scr
Mitigating Risk of Data Leakage:
Basic Steps
1. Protect Non-managed Machines: Remote access (employee, partner,
and vendor) from non-managed machines pose a serious risk.
Deploy protection technology in your remote access systems such as
Cisco Secure Desktop in the Cisco ASA 5500
2. Deploy Network-based Structured Data Controls: Data elements
such as Credit Card numbers or SSNs can be monitored and
controlled in return traffic using application firewalls (such as AVS
3100)
3. Lockdown Managed Endpoints: Lock down removable media
systems, such as USB ports and CD burners, using Cisco
Security Agent
4. Application Access Control: Enforce “need to know” access control
policies in the network at transit control points (e.g. in firewalls)
5. Content Inspection Services: Build out a network-wide sensor grid for
visibility and audit. Primary focus areas: email; instant messaging
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 85
Incident Response Basics
Incident Response Life Cycle Most important step:
Step 1
Pre-Incident Second most important step:
Planning
Step 5
1
Most commonly skipped step:
Post-Incident Step 1
Policy and Detection
Process 5 2 and Analysis Second most commonly
Analysis skipped step:
Step 5
4 3
Containment
Recovery
and Control
Adapted from reports at www.gartner.com and www.securityfocus.com
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 86
© 2008, Cisco Systems, Inc. All rights reserved. 43
14330_04_2008_c1.scr
What Should I Do?
Process, process, process:
Implement strong processes up front, document them,
and use them
User education campaigns:
Ensure there is an end-user education component of your
broader information security strategy
Make effective use of technology:
Technology exists to mitigate much of your risk of exposure
to new threats—make sure you’re using what’s available
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 87
Technology Recommendations
Stay informed: Subscribe to a threat
information service
A cost effective way to stay on top of things
Stay informed: Actually read the information
coming from your threat information service
Summaries are quick
Utilize your infrastructure
Use tools that you already have available
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 88
© 2008, Cisco Systems, Inc. All rights reserved. 44
14330_04_2008_c1.scr
Technology Recommendations
Change the game: Deploy NAC
Raise the bar on the level of protection at the internal edge
Develop and implement a complete “incident
response system”
Include technologies like IPS that enable visibility and
protection; ensure you’ve got the tools to help (like MARS)
Get tested! Engage a reputable penetration testing firm
Deploy anomaly technologies
Anomaly detection technologies can catch some emerging
threats before they’re well known
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 89
Intelligence Service Example
Cisco IntelliShield Alert Manager
Threat and Vulnerability
Intelligence Alerting Service
Receive Vital Intelligence that
Is Relevant and Targeted to
Your Environment
Tactical, operational and strategic
intelligence
Vendor neutral
Life cycle reporting
Vulnerability workflow
management system
Comprehensive searchable
alert database
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 90
© 2008, Cisco Systems, Inc. All rights reserved. 45
14330_04_2008_c1.scr
Intelligence Summary Example
Cisco IntelliShield Cyber Risk Reports
A Strategic Intelligence Report
that Highlights Current Security
Activity and Mid-to Long-range
Perspectives
Addresses seven major risk
management categories:
vulnerability, physical, legal, trust,
identity, human, and geopolitical.
The PSARs are a result of
collaborative efforts, information
sharing, and collective security
expertise of senior analysts from
Cisco security services that
include the IntelliShield team
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 91
Utilize Your Infrastructure
Cisco Applied Intelligence Responses
Actionable Intelligence that
Can Be Used on Existing
Cisco Infrastructure
Vulnerability Characteristics
Mitigation Technique Overview
Risk Management
Device-Specific Mitigation
and Identification
Cisco IOS® Routers and Switches
Cisco IOS NetFlow
Cisco ASA, PIX®, and FWSM Firewalls
Cisco Intrusion Prevention System
Cisco Security Monitoring, Analysis,
and Response System
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 92
© 2008, Cisco Systems, Inc. All rights reserved. 46
14330_04_2008_c1.scr
Incident Response and Threat
Prevention Systems
Considerations for Building
CS-MARS CSM a System
Cisco Security Cisco Catalyst®
Agent (CSA) Cisco ASA 5500 Service Monitoring Console:
Adaptive Security Modules
Appliance
A strong monitoring console
Cisco ISR is essential—without that,
Routers
you’re blind
CSA Internet Intranet
Breadth of Network
Control Points:
Have IPS technology ready in
Integrated Data
Monitoring, as many locations as possible,
Branch Correlation, and even if you’re not using it—it’ll
Protection Center
Response
Protection be there when you need it
Day Zero Converged Security Fine-grained Endpoint Control:
Server
Endpoint Perimeter Management
Protection Protection
Protection Ensure your endpoint security
software provides granular use
control, in addition to protective
services
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 93
Some Closing Thoughts
Do not get overwhelmed
Small steps can make a
big difference
Remember, to survive a
bear attack, you don’t
have to be fastest
person…you just need
to be faster than the
next guy
Do not be the least
prepared
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 94
© 2008, Cisco Systems, Inc. All rights reserved. 47
14330_04_2008_c1.scr
Q and A
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 95
Recommended Reading
Continue your Cisco Live
learning experience with further
reading from Cisco Press
Check the Recommended
Reading flyer for suggested
books
Available Onsite at the Cisco Company Store
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 96
© 2008, Cisco Systems, Inc. All rights reserved. 48
14330_04_2008_c1.scr
Complete Your Online
Session Evaluation
Give us your feedback and you could win Don’t forget to activate
fabulous prizes. Winners announced daily. your Cisco Live virtual
account for access to
Receive 20 Passport points for each session all session material
evaluation you complete. on-demand and return
for our live virtual event
Complete your session evaluation online now in October 2008.
(open a browser through our wireless network Go to the Collaboration
to access our portal) or visit one of the Internet Zone in World of
stations throughout the Convention Center. Solutions or visit
www.cisco-live.com.
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 97
BRKSEC-2001
14330_04_2008_c1 © 2008 Cisco Systems, Inc. All rights reserved. Cisco Public 98
© 2008, Cisco Systems, Inc. All rights reserved. 49
14330_04_2008_c1.scr
You might also like
- Safe and Secure Cyber-Physical Systems and Internet-of-Things SystemsFrom EverandSafe and Secure Cyber-Physical Systems and Internet-of-Things SystemsNo ratings yet
- Security for Small Computer Systems: A Practical Guide for UsersFrom EverandSecurity for Small Computer Systems: A Practical Guide for UsersTricia SaddingtonNo ratings yet
- Self-Defending Networks: Cisco Integrated SecurityDocument26 pagesSelf-Defending Networks: Cisco Integrated SecuritySurya NarayanaNo ratings yet
- Roles - CERT inDocument1 pageRoles - CERT inapi-27477209No ratings yet
- Industry Collaboration To Address Emerging Security Threats: Cisco Network Admission Control Program Co-SponsorsDocument25 pagesIndustry Collaboration To Address Emerging Security Threats: Cisco Network Admission Control Program Co-SponsorsstrabaseNo ratings yet
- Understanding, Preventing, and Defending Against Layer 2 AttacksDocument61 pagesUnderstanding, Preventing, and Defending Against Layer 2 AttacksjeffgrantinctNo ratings yet
- Cybersecurity / Regulatory Overview: Tracy Monteith Director, Cybersecurity Black & Veatch Management ConsultingDocument23 pagesCybersecurity / Regulatory Overview: Tracy Monteith Director, Cybersecurity Black & Veatch Management ConsultingANDRU TUDOR BADIUNo ratings yet
- Cheating in The Internet Era: Cisco Security Innovations For Combating The Exam ThreatDocument13 pagesCheating in The Internet Era: Cisco Security Innovations For Combating The Exam ThreatjeffgrantinctNo ratings yet
- SB Fortideceptor OtDocument5 pagesSB Fortideceptor OtYhoni SunarkoNo ratings yet
- Sec Testing KaneDocument100 pagesSec Testing KaneFran jimenezNo ratings yet
- CSAv1 Exam BlueprintDocument3 pagesCSAv1 Exam BlueprintTrần Anh TuấnNo ratings yet
- Cyber Risk Management 800-39 - DR Ron Ross WebEX 04-12-2011Document20 pagesCyber Risk Management 800-39 - DR Ron Ross WebEX 04-12-2011drbrydieNo ratings yet
- Top 10 OS/400 Security Risks: October 2004Document50 pagesTop 10 OS/400 Security Risks: October 2004lazaroNo ratings yet
- Materi Arief Santoso CISCODocument46 pagesMateri Arief Santoso CISCORaihan Rakha NaufalNo ratings yet
- Brksec-1021 (2018)Document84 pagesBrksec-1021 (2018)Paul ZetoNo ratings yet
- VIP Partner Summit22 - FortiGuard SecurityDocument23 pagesVIP Partner Summit22 - FortiGuard Securityfsdfd sdfsdfNo ratings yet
- Enclosure PUF Hardwear Io NL 2019Document64 pagesEnclosure PUF Hardwear Io NL 2019ascascdNo ratings yet
- BRKSEC-2061 Cisco + SourceFire Threat-Centric Security ApproachDocument85 pagesBRKSEC-2061 Cisco + SourceFire Threat-Centric Security ApproachluisNo ratings yet
- Cisco Physical and Logical SecurityDocument15 pagesCisco Physical and Logical Securityfnky_byNo ratings yet
- Cybersecurtity Essentials FDocument52 pagesCybersecurtity Essentials F0918453312No ratings yet
- Cisco Cyber Security Analyst Specialist CertificationDocument84 pagesCisco Cyber Security Analyst Specialist CertificationSofNo ratings yet
- ECOLE IT - 5SOP - IntroductionSecOpsDocument17 pagesECOLE IT - 5SOP - IntroductionSecOpsmbaye ndoye dialloNo ratings yet
- Fundamentals of Securing EtherNetIP NetworksDocument57 pagesFundamentals of Securing EtherNetIP NetworksHuber QuinteroNo ratings yet
- 1 Cyber Asset ProtectionDocument4 pages1 Cyber Asset Protectionevss_raghavendraNo ratings yet
- CyberSecurity Careerguide 13decDocument7 pagesCyberSecurity Careerguide 13decJITENDRANo ratings yet
- Enhance Cybersecurity Protection: Building The Right Cybersecurity CoverageDocument5 pagesEnhance Cybersecurity Protection: Building The Right Cybersecurity CoveragekEWQ 865kNo ratings yet
- Program ManagementDocument114 pagesProgram Managementmccsuresh2No ratings yet
- Attack and Breach - Datasheets - ControlledDocument2 pagesAttack and Breach - Datasheets - Controlleddigitlabs.marketingNo ratings yet
- BRKSEC2004Document214 pagesBRKSEC2004DC FanNo ratings yet
- Bsi10 Ops PDFDocument5 pagesBsi10 Ops PDFTrong Thua HuynhNo ratings yet
- Cisco Identity Services Engine and ASA Next-Generation Firewall ServicesDocument51 pagesCisco Identity Services Engine and ASA Next-Generation Firewall ServicesnelsonNo ratings yet
- SB Protecting Ot InfrastructuresDocument5 pagesSB Protecting Ot InfrastructuresYhoni SunarkoNo ratings yet
- SIMATIC NET IKPI Chap08 Industrial Security English 2015Document28 pagesSIMATIC NET IKPI Chap08 Industrial Security English 2015gayip94718No ratings yet
- SCADA Security OverviewDocument16 pagesSCADA Security Overviewtevexin998100% (1)
- Fortinet Security Solution Presentation - 06032019 - IDocument67 pagesFortinet Security Solution Presentation - 06032019 - IKopi mencos56No ratings yet
- Symantec Internet Security Threat Report, Trends For 2010 Volume 16, Published April 2011Document20 pagesSymantec Internet Security Threat Report, Trends For 2010 Volume 16, Published April 2011Reed ShipleyNo ratings yet
- CASE Java Course OutlineDocument23 pagesCASE Java Course Outlineram ramNo ratings yet
- Material For Students LCSPC V092019A enDocument105 pagesMaterial For Students LCSPC V092019A enecayllahuah100% (3)
- Building Security: IS 2620: Developing Secure SystemsDocument45 pagesBuilding Security: IS 2620: Developing Secure SystemsJose ToledoNo ratings yet
- Building Security: IS 2620: Developing Secure SystemsDocument45 pagesBuilding Security: IS 2620: Developing Secure SystemsjosephNo ratings yet
- DB-Mehari 2010 Exc en 2-20Document654 pagesDB-Mehari 2010 Exc en 2-20NarayanaRaoNo ratings yet
- Cybersecurity For Protection and Control Systems: An Overview of Proven Design SolutionsDocument10 pagesCybersecurity For Protection and Control Systems: An Overview of Proven Design SolutionslalithaNo ratings yet
- White Paper Automated Penetration Testing: Can IT Afford Not To?Document9 pagesWhite Paper Automated Penetration Testing: Can IT Afford Not To?gynxNo ratings yet
- Lezione Argiolu - Master Roma3!3!12-2010 - Test Di Application SecurityDocument26 pagesLezione Argiolu - Master Roma3!3!12-2010 - Test Di Application SecurityWB_YeatsNo ratings yet
- Deep Security Container Protection Customer PresentationDocument42 pagesDeep Security Container Protection Customer PresentationsaurabhbectorNo ratings yet
- The Threat Is Real, What Are You Doing About It?Document1 pageThe Threat Is Real, What Are You Doing About It?za3amNo ratings yet
- Patch Management SolutionsDocument25 pagesPatch Management Solutionssentoubudo1647No ratings yet
- 2019-06-26 Item 4 - Role of Security Reviews in Building Cyber ResilienceDocument26 pages2019-06-26 Item 4 - Role of Security Reviews in Building Cyber ResilienceSumaiyaNo ratings yet
- CEH Module 01: Introduction To Ethical HackingDocument37 pagesCEH Module 01: Introduction To Ethical HackingAhmad Mahmoud100% (9)
- Cyber Security Course in Kerala, KochiDocument14 pagesCyber Security Course in Kerala, Kochiamallblitz0No ratings yet
- KH Faisal Presentation Final RevisedDocument22 pagesKH Faisal Presentation Final RevisedjaishankarNo ratings yet
- Intelligent CybersecurityDocument1 pageIntelligent CybersecurityAlmaNo ratings yet
- CP FirewallDocument20 pagesCP FirewallAlika JainNo ratings yet
- Critical Infrastructure ResilienceDocument12 pagesCritical Infrastructure ResiliencePinnNo ratings yet
- S02.s2 Amenazas ModernasDocument23 pagesS02.s2 Amenazas ModernasRonald ChesterNo ratings yet
- Ism 4Document63 pagesIsm 4Shashwat MishraNo ratings yet
- Securing The Network: Building A Simple NetworkDocument11 pagesSecuring The Network: Building A Simple Networkamapreet.scorpioNo ratings yet
- ICND110S01L02 - Securing The NetworkDocument11 pagesICND110S01L02 - Securing The NetworkDpr SbyNo ratings yet
- Cisco Workload Optimization Manager-BRKCLDv-2011Document24 pagesCisco Workload Optimization Manager-BRKCLDv-2011Pawan BhattaraiNo ratings yet
- Layer of Protection Analysis: SciencedirectDocument11 pagesLayer of Protection Analysis: SciencedirectDigitalMastersTXNo ratings yet
- IEEE 802.3az Energy Efficient Ethernet: Build Greener NetworksDocument9 pagesIEEE 802.3az Energy Efficient Ethernet: Build Greener Networksplext0rNo ratings yet
- Monitoring and Mitigating Threats: BRKSEC-2004Document66 pagesMonitoring and Mitigating Threats: BRKSEC-2004jeffgrantinctNo ratings yet
- Self-Defending Network Support For PCI: BRKSEC-2008Document56 pagesSelf-Defending Network Support For PCI: BRKSEC-2008jeffgrantinctNo ratings yet
- Strategies and Tactics:: Application Troubleshooting SimplifiedDocument69 pagesStrategies and Tactics:: Application Troubleshooting SimplifiedjeffgrantinctNo ratings yet
- Inside The Perimeter: Six Steps To Improve Your Security MonitoringDocument43 pagesInside The Perimeter: Six Steps To Improve Your Security MonitoringjeffgrantinctNo ratings yet
- Advanced SAN Troubleshooting: Mike FraseDocument60 pagesAdvanced SAN Troubleshooting: Mike FrasejeffgrantinctNo ratings yet
- Advanced Data Center Virtualization: BRKDCT-3831Document62 pagesAdvanced Data Center Virtualization: BRKDCT-3831jeffgrantinctNo ratings yet
- Ipv6 Security Threats and Mitigations: Brksec-2003Document61 pagesIpv6 Security Threats and Mitigations: Brksec-2003jeffgrantinctNo ratings yet
- Advanced SAN Design - Virtualization Technologies and Intelligent Applications Design ConsiderationsDocument40 pagesAdvanced SAN Design - Virtualization Technologies and Intelligent Applications Design ConsiderationsjeffgrantinctNo ratings yet
- Design and Implementation of Storage Media Encryption: BRKSAN-2893Document35 pagesDesign and Implementation of Storage Media Encryption: BRKSAN-2893jeffgrantinctNo ratings yet
- I/O Consolidation in The Data Center: BRKSAN-2821Document53 pagesI/O Consolidation in The Data Center: BRKSAN-2821jeffgrantinctNo ratings yet
- SAN Extension Design and Operation: BRKSAN-2704Document47 pagesSAN Extension Design and Operation: BRKSAN-2704jeffgrantinctNo ratings yet
- Introduction To Storage Area Networks (SAN) : BRKSAN-1701Document42 pagesIntroduction To Storage Area Networks (SAN) : BRKSAN-1701jeffgrantinctNo ratings yet
- Network Design Considerations in A Blade Server Environment - LAN & StorageDocument31 pagesNetwork Design Considerations in A Blade Server Environment - LAN & StoragejeffgrantinctNo ratings yet
- DC Migration and Consolidation Discovery Methodology: BRKDCT-2863Document35 pagesDC Migration and Consolidation Discovery Methodology: BRKDCT-2863jeffgrantinctNo ratings yet
- Vmware Integration: Brkdct-2868Document44 pagesVmware Integration: Brkdct-2868jeffgrantinctNo ratings yet
- Leviton Power Solutions-2 To None in The Industry: "Protecting A Connected World"Document51 pagesLeviton Power Solutions-2 To None in The Industry: "Protecting A Connected World"jeffgrantinctNo ratings yet
- Introduction To Cisco'S Netflow Technology: Slide 1Document29 pagesIntroduction To Cisco'S Netflow Technology: Slide 1jeffgrantinctNo ratings yet
- Implementing Data Center Services (Interoperability, Design and Deployment)Document31 pagesImplementing Data Center Services (Interoperability, Design and Deployment)jeffgrantinctNo ratings yet
- Understanding The Lightweight Access Point Protocol (Lwapp) : White PaperDocument5 pagesUnderstanding The Lightweight Access Point Protocol (Lwapp) : White PaperjeffgrantinctNo ratings yet
- Lwap 1000 Ap Q&aDocument5 pagesLwap 1000 Ap Q&ajeffgrantinctNo ratings yet
- Optical Technology and Systems For The EnterpriseDocument89 pagesOptical Technology and Systems For The EnterprisejeffgrantinctNo ratings yet
- Teleconference: Demystifying NAC: Going Beyond Basic Admission ControlDocument25 pagesTeleconference: Demystifying NAC: Going Beyond Basic Admission ControljeffgrantinctNo ratings yet
- TB - Instant Wi FiDocument3 pagesTB - Instant Wi Fiseema gopalanNo ratings yet
- Msrit 7-8 Sem Syllabus BookDocument55 pagesMsrit 7-8 Sem Syllabus BookWendy Bass100% (1)
- Red Hat Enterprise Linux 6 Security Guide en USDocument224 pagesRed Hat Enterprise Linux 6 Security Guide en USAnuragBoraNo ratings yet
- Lect 05Document18 pagesLect 05Nguyen Quoc KhaiNo ratings yet
- What Is A Confined Space Hazard Assessment and Control ProgramDocument5 pagesWhat Is A Confined Space Hazard Assessment and Control Programdroffilcz27No ratings yet
- PasesDocument7 pagesPasesshedadNo ratings yet
- Heat Trace Testing Procedures1Document18 pagesHeat Trace Testing Procedures1camspsNo ratings yet
- Javascript CookiesDocument8 pagesJavascript CookiesArchie SrivastavaNo ratings yet
- Installing and Configuring The FAN Courier Shipping Plugin For WoocommerceDocument8 pagesInstalling and Configuring The FAN Courier Shipping Plugin For WoocommerceDacian Florin DeduNo ratings yet
- PCO Accreditation Application Form (Renewal)Document3 pagesPCO Accreditation Application Form (Renewal)car3laNo ratings yet
- N Procure InstallationDocument2 pagesN Procure InstallationManan ParikhNo ratings yet
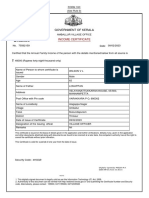
- Government of Kerala: Income CertificateDocument1 pageGovernment of Kerala: Income Certificatelissy WilsonNo ratings yet
- Site 2 Site VPNDocument31 pagesSite 2 Site VPNwinter00No ratings yet
- R12 DMZ ConfigurationDocument6 pagesR12 DMZ ConfigurationMuhd QNo ratings yet
- Read Fireware Log MSGDocument17 pagesRead Fireware Log MSGaqueyNo ratings yet
- CNT 1670730Document42 pagesCNT 1670730parashar1505No ratings yet
- LAN Architecture Diagram and ComponentsDocument6 pagesLAN Architecture Diagram and ComponentsCik Ieda SuhaimiNo ratings yet
- Leitura e Compreensão de Texto - EnglishDocument4 pagesLeitura e Compreensão de Texto - Englishglenda2008No ratings yet
- Ilantus Sign On Express Vs Softex OmnipassDocument8 pagesIlantus Sign On Express Vs Softex OmnipassrenokurianNo ratings yet
- What Is Quantum Communication? Why Quantum Repeaters Are Important? What Are Quantum Repeaters?Document2 pagesWhat Is Quantum Communication? Why Quantum Repeaters Are Important? What Are Quantum Repeaters?Arijit SahaNo ratings yet
- BR Course InfoDocument87 pagesBR Course InfokarthickNo ratings yet
- (Susan Loepp, William K. Wootters) Protecting InformationDocument305 pages(Susan Loepp, William K. Wootters) Protecting Informationlev76No ratings yet
- List of LINUX Troubleshooting CommandsDocument2 pagesList of LINUX Troubleshooting Commandsjeetmajumdar007No ratings yet
- C. Bartholomae Altiranisches WörterbuchDocument1,044 pagesC. Bartholomae Altiranisches WörterbuchnesanurphotNo ratings yet
- Training Material - HSEDocument27 pagesTraining Material - HSEfaizalpsNo ratings yet
- Brochure (Pdf/Brochure - PDF) : Student RegistrationDocument3 pagesBrochure (Pdf/Brochure - PDF) : Student Registrationanurag vermaNo ratings yet
- Management Information System of EDCLDocument47 pagesManagement Information System of EDCLAbir MohammadNo ratings yet
- ATK ConfigurationDocument7 pagesATK Configurationpresto prestoNo ratings yet
- Application Summary: IMPORTANT REMINDER: Be at The DFA Processing Site at Least 1 Hour BEFORE Your Scheduled AppointmentDocument1 pageApplication Summary: IMPORTANT REMINDER: Be at The DFA Processing Site at Least 1 Hour BEFORE Your Scheduled AppointmentCamille OlivarNo ratings yet
- Ee793 Assignment 1Document5 pagesEe793 Assignment 1Jayesh SongaraNo ratings yet