Professional Documents
Culture Documents
Tshark PDF
Uploaded by
ElputoAmo XDOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Tshark PDF
Uploaded by
ElputoAmo XDCopyright:
Available Formats
Tshark: Strip WPA Wireless Captures by ESSID wi...
CATEGORIES
Code Snippets
Errors
http://www.question-defense.com/2010/03/29/tsha...
Home Insights Tshark: Strip WPA Wireless Captures by ESSID with Tshark
Search here..
Tshark: Strip WPA Wireless Captures by ESSID with Tshark
LATEST ARTICLES
purehate March 29, 2010 Insights 13 Comments
Insights
Labs
Security
A while ago I wrote a short tutorial on how to strip down a wireless capture which contained a wpa handshake
so that only eapol packets and beacon frames where left. I have since found a little bit better way to do it so I
decided to make a new post. In the previous article I showed how to strip by wlan.mgt frames containing the
2
Tweet
mac address. The problem with this is that it strips out lots of other packets which some programs use to
check for ESSID. I looked into the issue some more and found a way to strip just by essid.
How to Congure NVFax on
FreePBX
TextMate Find & Replace Using
Regular Expressions
CentOS Remove Old Kernels
PAGES
Backtrack Linux
Consulting
If you just want the command:
tshark -r <input file>
file> -R "eapol || wlan_mgt.tag.interpretation eq <essid> || (wlan.fc.type_subtype==0x08 && wl
Obviously you have to have tshark installed for this to work.
Contact
I also had a customer for our online wpa cracker server who was having trouble stripping a capture so I decided to whip
Documentation
Kali Linux
Tags
Tools
up a quick shell script to help him out.
#!/bin/bash
echo "This script requires tshark"
echo
echo "Checking for tshark"
type tshark &>/dev/null
&>/dev/null || { echo "I require tshark but it's not installed.
echo "tshark found"
echo
echo "Moving on...."
echo
echo "Please the path to the capture (ex. /home/john/NETGEAR.cap)"
read cap_path
echo
while [ ! -f
echo
echo
echo
echo
read
done
echo
echo "Please
read essid
Aborting." >&2; exit
"$cap_path" ];do
];do
"File cannot be found or does not exist"
"Please the path to the capture (ex. /home/john/NETGEAR.cap):"
cap_path
enter the ESSID (ex. NETGEAR)"
while [ -z "$essid" ]; do
echo "You still didnt enter any data n00b"
echo
echo "Please enter the ESSID (ex. NETGEAR)"
read essid
done
echo
echo "Stripping file...."
tshark -r $cap_path -R "eapol || wlan_mgt.tag.interpretation eq $essid || (wlan.fc.type_subtype==0x08 && wlan_m
echo
echo "Your stripped file should be located in the current directory and named stripped.cap."
If you want to use this simply create a le called stripper.sh and paste this script into it.
Next make the script executable by issuing the command:
chmod 755 stripper.sh
Once you have done that simply run the script.
Example of script being run:
[root@dev-tools ~]#
~]# ./strip.sh
This script requires tshark
Checking for tshark
tshark found
Moving on....
1 de 5
06/01/15 21:42
Tshark: Strip WPA Wireless Captures by ESSID wi...
http://www.question-defense.com/2010/03/29/tsha...
Please the path to the capture (ex. /home/john/NETGEAR.cap)
/home/john/NETGEAR.cap)
/root/old.cap
/root/old.cap
Please enter the ESSID (ex. NETGEAR)
NEUF_A268
Stripping file....
file....
Running as user "root" and group "root".
"root". This could be dangerous.
Your stripped file should be located in the current directory and named stripped.cap.
TOPICS
BEACON
SHARE
CAPTURE
DATA
EAPOL
FRAME
STRIPPED
TSHARK
WPA
Previous
Next
make: yacc: Command not found
on Cent OS
no such le to load rubygems
(LoadError)
Related Posts
How To Tell Exactly How Many
Spaces A ESSID Includes Using
airodump-ng Or Wireshark
Strip WPA Capture File Down To
EAPOL Packets Based On BSSID
Instead Of ESSID
View Wireless Authentication
Type Using Wireshark In Network
Capture: PSK, WPA
There are 13 Comments.
WLAN_7E6E
8:48 PM July 11, 2011
CRACIAS
Reply
ALEX
11:05 AM April 4, 2012
Hello WLAN_7E6E,
No problem. Thanks for taking the time to leave feedback.
Thanks.
alex
Reply
PETRU
7:27 AM November 3, 2011
Yup, verrrry interesting and educational .You guys are still the best ( I mean
americans , cose Im
not an american) .
I think Il use your WPA cracker too . Till the next time, bee healty and have fun .
Reply
ALEX
2 de 5
11:09 AM April 4, 2012
06/01/15 21:42
Tshark: Strip WPA Wireless Captures by ESSID wi...
http://www.question-defense.com/2010/03/29/tsha...
Hello Petru,
Thanks for the compliment. We however support a world where all are equal
and we share the same respect for all regardless of birthplace. Sorry for the
delayed response got overwhelmed with comments and just now trying to
catch up. Anyhow hope you nd our online password audit/password cracking
services at http://tools.question-defense.com useful and valuable.
Anyhow thanks for taking the time to post feedback on our site.
Thanks.
alex
Reply
FAISAL
3:02 AM April 4, 2012
hello sir already have password in handshake capture le how can see that
password
Reply
ALEX
11:12 AM April 4, 2012
Hello faisal,
You would need to use either software such as oclHashcat+ or aircrack-ng or an
online service like ours located at http://tools.question-defense.com. Good luck
and thanks for leaving feedback!
Thanks.
alex
Reply
COMPILINGENTROPY
5:54 PM December 6, 2012
Hmm, it seems your website thinks part of my command is html. heres the
actual command (last time!):
tshark -r [input le] -R eapol || wlan_mgt.tag.interpretation eq [essid] ||
(wlan.fc.type_subtype==008 && wlan_mgt.ssid eq [essid]) && wlan.bssid == [bssid] -w
[output le]
Reply
ALEX
9:41 AM December 27, 2012
Hello compilingEntropy,
Thanks for posting this! To post code in the comments you can use the
sourcecode short code like the below with square brackets at each end [ open
... and ] close.
OPEN_BRACKETsourcecode language=BASH light=TRUECLOSE_BRACKET
code here
OPEN_BRACKET/sourcecodeCLOSEBRACKET
Or email what you want posted in the comment above and I will add it from
within the admin.
Again thanks for taking the time to make this observation.
3 de 5
06/01/15 21:42
Tshark: Strip WPA Wireless Captures by ESSID wi...
http://www.question-defense.com/2010/03/29/tsha...
Thanks.
alex
Reply
IDIOTIC
8:15 AM May 24, 2013
what an idiot way .. i have the le in WINDOWS 2gb large .. how the f*** and
why the f*** i need to do that in linux moron .. show how you do it in
windows!!!
Reply
ALEX
12:33 PM May 24, 2013
Hello idiotic,
You can feel the brilliance in your comment You dont have to do anything in
Linux or Windows for that matter and most people stripping wireless packet
captures for this purpose do and are using Linux of some type. So glad you took
the time to shine on this post. Now we can only hope that you will bless us with
your presence again.
Thanks.
alex
Reply
@MIKE
4:42 PM October 19, 2013
it doesnt work. maybe extract wpa handshake but beacon frame is missing, so
aircrack-ng will say unsupported le format.
Reply
DANIEL
10:22 PM January 26, 2014
Neither this or your old post works i keep ending up with other aps and
clients but with the ssids striped
This is the output im getting using your code:
#
1
2
3
4
5
6
7
8
9
10
11
12
13
14
BSSID
<removed>
<removed>
<removed>
<removed>
<removed>
<removed>
<removed>
<removed>
<removed>
<removed>
<removed>
<removed>
<removed>
<removed>
ESSID
<blank>
<blank>
<blank>
<blank>
<blank>
<blank>
<blank>
<blank>
<blank>
<blank>
<blank>
<blank>
<blank>
<blank>
Encryption
WPA (0 handshake)
WPA (1 handshake)
WPA (0 handshake)
WPA (0 handshake)
WPA (0 handshake)
WPA (1 handshake)
WPA (1 handshake)
WPA (0 handshake)
WPA (0 handshake)
WPA (0 handshake)
WPA (0 handshake)
EAPOL+WPA (1 handshake)
WPA (1 handshake)
WPA (1 handshake)
I got it working i changed a few things
tshark -r ../dump-01.cap -R "(eapol || (wlan.fc.type_subtype == 0x08)) && (wlan.bs
Note the brackets
Output:
4 de 5
06/01/15 21:42
Tshark: Strip WPA Wireless Captures by ESSID wi...
#
BSSID
1
<removed>
ESSID
<removed>
http://www.question-defense.com/2010/03/29/tsha...
Encryption
WPA (1 handshake)
I purposly remove the bssid and ssids from all aps the onces with didnt return any
ssid even though in the original cap le they where there
Reply
Pingback: Shell Script to Strip Wireless WPA Captures with Tshark
Leave a Reply
Name *
Email *
Captcha *
three = 15
POST COMMENT
Question Defense 2015
5 de 5
06/01/15 21:42
You might also like
- C6-KONE KCE. Training On Wiring DiagramDocument29 pagesC6-KONE KCE. Training On Wiring DiagramElputoAmo XD88% (8)
- C11-Schindler-MX-GC Release 4 MRL. Basic Maintenance TasksDocument26 pagesC11-Schindler-MX-GC Release 4 MRL. Basic Maintenance TasksElputoAmo XD86% (7)
- Dorks-12 10 19-04 46 17Document36 pagesDorks-12 10 19-04 46 17Jhon Mario CastroNo ratings yet
- 13.3.2-Lab - Use-Ping-And-Traceroute-To-Test-Network-Connectivity - CESAR RIOSDocument11 pages13.3.2-Lab - Use-Ping-And-Traceroute-To-Test-Network-Connectivity - CESAR RIOSL HammeRNo ratings yet
- 12.4.1.2 Lab - Isolate Compromised Host Using 5-TupleDocument18 pages12.4.1.2 Lab - Isolate Compromised Host Using 5-TupleJangjang KatuhuNo ratings yet
- Snort 2.9.15.1Document28 pagesSnort 2.9.15.1Edward Peter Lyn100% (1)
- 1.1.1.8 Packet Tracer - Using Traceroute To Discover The Network InstructionsDocument5 pages1.1.1.8 Packet Tracer - Using Traceroute To Discover The Network InstructionsSer SarNo ratings yet
- IMC - SCR - Rev - E8 (42-02-7200E)Document449 pagesIMC - SCR - Rev - E8 (42-02-7200E)ElputoAmo XDNo ratings yet
- TLM Recs 2.7 SP1Document95 pagesTLM Recs 2.7 SP1Shankar Narayanan100% (2)
- DRBD-Cookbook: How to create your own cluster solution, without SAN or NAS!From EverandDRBD-Cookbook: How to create your own cluster solution, without SAN or NAS!No ratings yet
- Linux For Elastix Administrators-LabDocument15 pagesLinux For Elastix Administrators-LabMarioNo ratings yet
- Asterisk Workshop 2011Document20 pagesAsterisk Workshop 2011Anton RaharjaNo ratings yet
- IT46 en VoIP4D Laboratory Tutorial AsteriskNOWDocument31 pagesIT46 en VoIP4D Laboratory Tutorial AsteriskNOWictnewNo ratings yet
- Building and Running OpenBSC With Asterisk - v1.0Document5 pagesBuilding and Running OpenBSC With Asterisk - v1.0dchardwareNo ratings yet
- PBX - Freepbx Install GuideDocument4 pagesPBX - Freepbx Install GuideZainudin AboedNo ratings yet
- BlackHat DC 2011 Brennan Denial Service-SlidesDocument38 pagesBlackHat DC 2011 Brennan Denial Service-SlidesHoang Chi LinhNo ratings yet
- Asterisk NowDocument82 pagesAsterisk Nowkambojk100% (1)
- Astertest - Asterisk Stress Testing Tool PDFDocument24 pagesAstertest - Asterisk Stress Testing Tool PDFIsmael ItriagoNo ratings yet
- Elastix "Without Tears" 200+ Tips For Building Ipbx Server VoipDocument258 pagesElastix "Without Tears" 200+ Tips For Building Ipbx Server VoipMC. Rene Solis R.100% (5)
- Issabel ServerDocument32 pagesIssabel ServerBaher MohamedNo ratings yet
- Install Process Freepbx Centos 5.1Document35 pagesInstall Process Freepbx Centos 5.1gerardinhoNo ratings yet
- CNS 320 Week7 LectureDocument62 pagesCNS 320 Week7 Lecturealb3rtlin100% (1)
- Lab 7a: Ethernet, IP and TCP: 1 DetailsDocument14 pagesLab 7a: Ethernet, IP and TCP: 1 DetailsmNo ratings yet
- AsteriskTwilioSIPTrunkingv2 0Document9 pagesAsteriskTwilioSIPTrunkingv2 0TheKLBNo ratings yet
- Leni Andriani - 3.1.2.6 Lab - Working With Text Files in The CLIDocument10 pagesLeni Andriani - 3.1.2.6 Lab - Working With Text Files in The CLILeni AndrianiNo ratings yet
- Exploiting Windows10 8 7Document2 pagesExploiting Windows10 8 7Ashok KumarNo ratings yet
- FreePBX AdministrationDocument2 pagesFreePBX AdministrationFaizal MnNo ratings yet
- Ping and Traceroute UnderstandingDocument22 pagesPing and Traceroute Understandingdavekrunal46No ratings yet
- Asterisk Configuration To Work With Mobile Through OpenBTSDocument4 pagesAsterisk Configuration To Work With Mobile Through OpenBTSTarik KazazNo ratings yet
- Agentlogin Queues AsteriskDocument3 pagesAgentlogin Queues AsteriskaonesimeNo ratings yet
- 9.3.8 Lab - Exploring NmapDocument7 pages9.3.8 Lab - Exploring Nmapbui lamNo ratings yet
- Ping and TracerouteDocument10 pagesPing and TraceroutejayNo ratings yet
- ATIS and ATCDocument31 pagesATIS and ATCMiguel Angel Gutierrez Gambetta100% (1)
- Perform An Experiment For Port Scanning With Nmap, Superscan or Any Other Equivalent SoftwareDocument4 pagesPerform An Experiment For Port Scanning With Nmap, Superscan or Any Other Equivalent SoftwaresangeetadineshNo ratings yet
- How To Troubleshoot ISDN On PRIDocument11 pagesHow To Troubleshoot ISDN On PRIDavi Sadaseeven SaminadenNo ratings yet
- Network Security Lab: What Is Nmap?Document4 pagesNetwork Security Lab: What Is Nmap?Deepanshu SharmaNo ratings yet
- Wireshark LabDocument12 pagesWireshark LabNimesh NaikNo ratings yet
- Lab 3 - RTP Header CompressionDocument6 pagesLab 3 - RTP Header CompressiondjmckcNo ratings yet
- Asterisk TutorialDocument8 pagesAsterisk TutorialYusuf SiddiquiNo ratings yet
- Fundamentals of Wireless LANs AnswerDocument74 pagesFundamentals of Wireless LANs Answermario1349No ratings yet
- Sip I A MDocument594 pagesSip I A MRodrigo SenadorNo ratings yet
- Router Security Configuration GuideDocument291 pagesRouter Security Configuration GuideghaniNo ratings yet
- Learn Linux DD Command - 15 Examples With All OptionsDocument25 pagesLearn Linux DD Command - 15 Examples With All Optionsanon_578762250No ratings yet
- Asterisk Admin Guide 13.5Document857 pagesAsterisk Admin Guide 13.5Pedro VargasNo ratings yet
- Asterisk 1.4.0 CLI CommandsDocument8 pagesAsterisk 1.4.0 CLI Commandsclicke86No ratings yet
- Ping WiresharkDocument15 pagesPing WiresharkSneha KanwadeNo ratings yet
- 1.1 Overview: From PSAPDocument8 pages1.1 Overview: From PSAPAbhilash BrahmaNo ratings yet
- How To Troubleshoot DTMF On ISDN PRIDocument11 pagesHow To Troubleshoot DTMF On ISDN PRIaskerder wangNo ratings yet
- 12.4.1.1 Lab - Interpret HTTP and DNS Data To Isolate Threat Actor PDFDocument17 pages12.4.1.1 Lab - Interpret HTTP and DNS Data To Isolate Threat Actor PDFInteresting facts ChannelNo ratings yet
- IPsec VPN Penetration Testing With BackTrack ToolsDocument6 pagesIPsec VPN Penetration Testing With BackTrack Toolsksenthil77No ratings yet
- Top Linux Monitoring ToolsDocument38 pagesTop Linux Monitoring ToolsRutch ChintamasNo ratings yet
- Metasploit FrameworkDocument8 pagesMetasploit FrameworkItz TuhinNo ratings yet
- If GPS Signal Simulator Development and Verification - 03.20184.LeiDongDocument182 pagesIf GPS Signal Simulator Development and Verification - 03.20184.LeiDongA. VillaNo ratings yet
- Configuration Notes 1204 FXO With AsteriskDocument12 pagesConfiguration Notes 1204 FXO With Asteriskgerma01gNo ratings yet
- Linux FundamentalsDocument76 pagesLinux Fundamentalsfa1c0n kingNo ratings yet
- Hunting Malware With Volatility v2.0Document40 pagesHunting Malware With Volatility v2.0akronareaguyNo ratings yet
- Wireshark Notes-OSI and TCP-IPDocument34 pagesWireshark Notes-OSI and TCP-IPanzieriNo ratings yet
- 26.1.7 Lab - Snort and Firewall RulesDocument8 pages26.1.7 Lab - Snort and Firewall RulesFata HasanNo ratings yet
- Filesystem PDFDocument50 pagesFilesystem PDFRaja Shahbaz KhalidNo ratings yet
- CEH Lesson 3 - Enumeration and System HackingDocument36 pagesCEH Lesson 3 - Enumeration and System HackingLouise RealNo ratings yet
- Cisco Certified Security Professional A Complete Guide - 2020 EditionFrom EverandCisco Certified Security Professional A Complete Guide - 2020 EditionNo ratings yet
- Asterisk and App - RPTDocument7 pagesAsterisk and App - RPTElputoAmo XDNo ratings yet
- TMS 600 RDocument69 pagesTMS 600 RElputoAmo XDNo ratings yet
- 06 ProxmarkDocument27 pages06 ProxmarkElputoAmo XDNo ratings yet
- Fujitsu-Siemens Pocket Loox N520, 720 Pinout: 26 Pin Asus Mypal Proprietary ConnectorDocument2 pagesFujitsu-Siemens Pocket Loox N520, 720 Pinout: 26 Pin Asus Mypal Proprietary ConnectorElputoAmo XDNo ratings yet
- FX1N Harware ManualDocument15 pagesFX1N Harware ManualElputoAmo XDNo ratings yet
- Motion 4000 Traction v9 42-02-2P25 A6Document480 pagesMotion 4000 Traction v9 42-02-2P25 A6ElputoAmo XDNo ratings yet
- Icontrol AC Rel 3 4 42-02-2223 B5Document414 pagesIcontrol AC Rel 3 4 42-02-2223 B5ElputoAmo XDNo ratings yet
- The MagPi - November 2018Document100 pagesThe MagPi - November 2018ElputoAmo XD100% (1)
- 42-95-0004 C6 IntellaNetDocument318 pages42-95-0004 C6 IntellaNetElputoAmo XDNo ratings yet
- Schemi Schindler Miconic LX OleoDocument22 pagesSchemi Schindler Miconic LX OleoElputoAmo XD100% (1)
- Computer Soundcard To Radio InterfaceDocument5 pagesComputer Soundcard To Radio InterfaceElputoAmo XD67% (3)
- Motion 2000 Hydraulic V9 42-02-1P21 A9Document294 pagesMotion 2000 Hydraulic V9 42-02-1P21 A9ElputoAmo XDNo ratings yet
- Icontrol DC Aug 08 Rel 42-02-7222 B7Document788 pagesIcontrol DC Aug 08 Rel 42-02-7222 B7ElputoAmo XDNo ratings yet
- IMC Performa ASME 2000 42-02-7205 Rev B3Document470 pagesIMC Performa ASME 2000 42-02-7205 Rev B3ElputoAmo XDNo ratings yet
- Tricon 42-02-2T00 F4Document301 pagesTricon 42-02-2T00 F4ElputoAmo XDNo ratings yet
- Motion 2000 Hydraulic v8 42-02-1P20 B7Document248 pagesMotion 2000 Hydraulic v8 42-02-1P20 B7ElputoAmo XD100% (1)
- 42-02-G004 B4 Motion GroupDocument86 pages42-02-G004 B4 Motion GroupElputoAmo XDNo ratings yet
- HMC HS - (Asme 2000) - (42 02 1021 - A9)Document174 pagesHMC HS - (Asme 2000) - (42 02 1021 - A9)ElputoAmo XDNo ratings yet
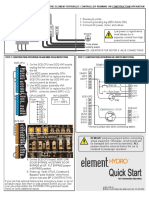
- 42-QR-1P26 B3 Element Hydro Quick StartDocument1 page42-QR-1P26 B3 Element Hydro Quick StartElputoAmo XDNo ratings yet
- VFMC-PTC Series M 42-02-2p22 Rev b9Document367 pagesVFMC-PTC Series M 42-02-2p22 Rev b9ElputoAmo XDNo ratings yet
- IMC-MG (42-02-6202 Rev B3)Document332 pagesIMC-MG (42-02-6202 Rev B3)ElputoAmo XDNo ratings yet
- M-AUDIO FW - HIGH SIERRA - Instructions - NEWDocument5 pagesM-AUDIO FW - HIGH SIERRA - Instructions - NEWRenato ZadiNo ratings yet
- TES5Edit LogDocument621 pagesTES5Edit LogKurniawan WijayaNo ratings yet
- Fiddler Customrules JsDocument8 pagesFiddler Customrules JsNguyen ThanhNo ratings yet
- Power Point Presentation Android TechnologyDocument21 pagesPower Point Presentation Android Technologynitish_singh_1No ratings yet
- CP400Soft Manual EN PDFDocument333 pagesCP400Soft Manual EN PDFmodelador3dNo ratings yet
- Symantec Data Loss Prevention Installation Guide For Linux: Last Updated: September 24, 2020Document105 pagesSymantec Data Loss Prevention Installation Guide For Linux: Last Updated: September 24, 2020artreisNo ratings yet
- VoIP - A2Billing v2.2 Install GuideDocument12 pagesVoIP - A2Billing v2.2 Install GuideGiraffeNo ratings yet
- OS Practical FileDocument47 pagesOS Practical FileDevil IVORNo ratings yet
- Support MatrixDocument17 pagesSupport MatrixSohan GoleNo ratings yet
- H.264-1080P Remote Wireless Camera Operating Instructions: I. Mode Represented by Key IndicatorDocument8 pagesH.264-1080P Remote Wireless Camera Operating Instructions: I. Mode Represented by Key Indicatorfauzan080No ratings yet
- HP Workstation Intel Rapid Storage Technology Remaping of PCIe Storages DevicesDocument21 pagesHP Workstation Intel Rapid Storage Technology Remaping of PCIe Storages DevicesKarim MessoussiNo ratings yet
- MSDE2 K LogDocument2 pagesMSDE2 K LogShanaj MlNo ratings yet
- Speed Up Your Windows PCDocument12 pagesSpeed Up Your Windows PCwilmarafNo ratings yet
- Undocumented Settings For Delphi, Kylix and C++BuilderDocument12 pagesUndocumented Settings For Delphi, Kylix and C++BuilderYacine SouilahNo ratings yet
- OKIOCAM Snapshot and Recorder Installation & Navigation Guide (Windows)Document17 pagesOKIOCAM Snapshot and Recorder Installation & Navigation Guide (Windows)Yvan GarciaNo ratings yet
- OPERA 5 Oracle 11.2.0.4 Database InstallationDocument20 pagesOPERA 5 Oracle 11.2.0.4 Database InstallationImms RocksNo ratings yet
- ZHPCleaner (S)Document3 pagesZHPCleaner (S)Pedro Enrique RosalesNo ratings yet
- Change Windows MAC Address PDFDocument34 pagesChange Windows MAC Address PDFJuan Alberto Corniel JiménezNo ratings yet
- Patching NoteDocument2 pagesPatching NoteOgwuche Oche SimonNo ratings yet
- SAP GV Session Pre-Step QuestionsDocument3 pagesSAP GV Session Pre-Step Questionssdk27bNo ratings yet
- BMC Atrium Discovery and Dependency MappingDocument89 pagesBMC Atrium Discovery and Dependency MappingJorge LuqueNo ratings yet
- Load RunnerDocument13 pagesLoad Runnerapi-3828931No ratings yet
- Hardware Emulated by GNS3Document8 pagesHardware Emulated by GNS3hfredianNo ratings yet
- Fiery User GuideDocument36 pagesFiery User GuideCraig MusgravesNo ratings yet
- P7 Virtualization BestpracticeDocument20 pagesP7 Virtualization BestpracticearamisNo ratings yet
- SMPDocument1 pageSMPbutcherrlNo ratings yet
- Help File: Basic Brand Manual & GuidelinesDocument8 pagesHelp File: Basic Brand Manual & GuidelineschamsiNo ratings yet
- Log2 AnsiDocument17 pagesLog2 AnsizkovaNo ratings yet