Professional Documents
Culture Documents
Ransomware Four Shouldnt Ignore
Uploaded by
Manoj KumarOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Ransomware Four Shouldnt Ignore
Uploaded by
Manoj KumarCopyright:
Available Formats
At a glance
Ransomware Galore:
The Four You Shouldn’t Ignore
Ransomware. You know the risk is there.
Ransomware is a growing issue that isn’t going away anytime soon. The threat of
losing access to your mission-critical systems and data can keep you up at night. No
one wants to receive a hacker’s demand to pay now or lose your information forever.
That’s why you’ve already renewed your focus on data backup and recovery. It’s
hard, and you know you need to do it. Beyond that, do you know what your top
defensive priorities should be?
There are four more things that you absolutely must do.
Let’s Explore the Four You Shouldn’t Ignore.
© 2018 Cisco and/or its affiliates. All rights reserved.
At a glance
The Four You
Defending against ransomware requires more than When ransomware strikes, do you know how long
just a good backup strategy. You must take key it will take to restore everything from backup? What
preventative steps, while also readying your team to will you lose by being down for that long?
Shouldn’t Ignore act when it strikes.
An effective risk-based approach to prevention
To restore operations fast, many are tempted to
pay the small ransom. Don’t.
considers not only the threat but also your
vulnerabilities, the likelihood of occurrence, and Stop ransomware before this scenario happens to
the severity of impact. You already understand the you. There are many things you can do, but here
DNS-Level threat and potential ramifications. How about your are four critical steps that address your highest
Security vulnerabilities and the chances you’ll be affected? ransomware risks:
Vulnerable targets exist in every organization.
They’re your people.
Nearly anyone can be tricked into clicking malicious
links or opening harmful email attachments that
Email Security download ransomware. Then their infected devices
spread the ransomware across your network to
critical systems. Files are encrypted, systems
are slow or offline, and you’re presented with a
payment demand to get your data back.
Malware This attack method succeeds so often that hackers
Protection for continually target individuals each day. That’s why
the chances are very high that someone in your
Endpoints organization will do something soon that elevates
your risk of a ransomware infection. If you have
people in your organization, then the odds are
already stacked against you. You’re vulnerable to a
ransomware attack.
Incident
Response Plan
© 2018 Cisco and/or its affiliates. All rights reserved.
At a glance
The Four You Shouldn’t can trick people with real-looking (but fake) emails.
And those emails are laced with harmful links or
Ignore. attachments.
You can’t stop using email, so it’s wise to embed
DNS-Level Security
email security into your existing email system.
The Internet doesn’t work without
the Domain Name System (DNS), Defend against ransomware by stopping spam and
and neither does most ransomware. phishing emails. Remove malicious attachments.
Attackers need the flexibility of DNS, Users can’t click harmful links or open malicious
which is why ransomware usually attachments if they don’t actually get them. Mitigate
doesn’t have hard-coded IP addresses. More than email-borne ransomware risks.
90% of ransomware variants today rely on DNS to
That’s why you shouldn’t ignore email security.
Learn more about Cisco remain under the hacker’s control.
Cisco Email Security with Advanced Malware
Ransomware Defense You already run DNS on your network, so why not use
Protection (AMP) prevents ransomware from arriving
it to run ransomware out of your network?
today at: through email by stripping away the threat. It’s
another key part of the Cisco Ransomware Defense
With DNS-level security you can block access to
solution.
www.cisco.com/go/ known-bad domains. That means the end user’s
system simply can’t connect to malicious sites
ransomware because DNS-level security won’t give them bad Malware Protection for Endpoints
IP addresses. It’s the first line of defense against
No matter how hard you try, malware
ransomware, and it’s very effective.
will find a way to reach your users’
That’s why you shouldn’t ignore DNS-level security. devices and then spread through
your network. People will access bad
Cisco Umbrella provides DNS-level security, and websites, download harmful files,
is a key component of the Cisco Ransomware install fraudulent apps, blindly open attachments,
Defense solution. and share infected memory sticks. You can’t
completely prevent risky cyber behavior, despite all
Email Security of the security awareness training you’ve provided.
Who doesn’t use email? There’s You need advanced malware protection for all of
almost no way to conduct business your endpoints -- user devices and critical servers.
today without it. Unfortunately email
is also the most common entry point Endpoints are the entry points. They are also the
for ransomware because hackers systems holding your critical information. You need a
© 2018 Cisco and/or its affiliates. All rights reserved.
At a glance
way to analyze and stop malware from running In Line with Cyber Best Practices More Beyond the Four
on those devices and hosts.
The Four Your Shouldn’t Ignore were not simply Don’t stop after you’ve made progress on the
That’s why you shouldn’t ignore malware pulled from thin air. They are in line with existing Four. Cisco Ransomware Defense goes a lot
protection for all of your endpoints. and well-regarded cybersecurity best practices further and provides:
like the Center for Internet Security (CIS)
Cisco AMP for Endpoints delivers essential Controls. For example: Network Segmentation. Logically separate the
malware protection for endpoints, and is the third things on your network that shouldn’t be actually
key technology in the layered Cisco Ransomware CIS Control 3: Secure Configurations for talking with one another.
Defense Solution. Hardware and Software on Mobile Devices,
Laptops, Workstations, and Servers. DNS-level Visibility and Enforcement. Know what’s on your
security provided by Cisco Umbrella is one of network and how they communicate for a clear,
Incident Response Plan consistent access policy.
many secure configurations that help harden the
You know the importance of system and minimize vulnerabilities.
business continuity and disaster
recovery planning, which is why CIS Control 7: Email and Web Protection. Cisco
you’ve already bolstered your data Email Security with AMP is a natural fit with this
backup program. It’s difficult and control.
time-consuming, but it’s necessary especially
CIS Control 8: Malware Defenses. Both Cisco
considering today’s growing ransomware threat.
AMP for Endpoints and Cisco Email Security with
Of course, you can’t begin restoring anything until AMP offer the critical malware defenses outlined
after you’ve resolved the cause. Do you know by this control.
what to do during critical moments after detecting
CIS Control 19: Incident Response and
an attack? How will you respond to quickly contain
Management. Cisco Incident Response Services
the damage? Without a solid response plan, a
can help you develop the comprehensive
ransomware outbreak will cause chaos.
set of people and process controls that CIS
That’s why you shouldn’t ignore the value of recommends. What we call an “Incident
incident response planning. Response Plan” is the really same detailed
incident response infrastructure discussed in this
Cisco Services Incident Response experts can Control. Plus our Incident Response experts can
help you develop that response plan, and also help you take the necessary corrective action
deal with active cyberattacks that are causing when you’re suffering from an active ransomware
damage now. We encourage our Incident outbreak or other cyberattack.
Response Services to complement the Cisco © 2018 Cisco and/or its affiliates. All rights reserved. Cisco and the Cisco logo
are trademarks or registered trademarks of Cisco and/or its affiliates in the U.S.
Ransomware Defense Solution’s preventative and other countries. To view a list of Cisco trademarks, go to this URL: www.
cisco.com/go/trademarks. Third-party trademarks mentioned are the property of
technologies. their respective owners. The use of the word partner does not imply a partnership
relationship between Cisco and any other company. (1110R)
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (894)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (587)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (119)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2219)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- IT Heads PAN IndiaDocument704 pagesIT Heads PAN IndiaSantaji Gade50% (12)
- Question 1 - Mounting MethodDocument3 pagesQuestion 1 - Mounting MethodMuhd IlyasNo ratings yet
- Pipeline Schedule PDFDocument54 pagesPipeline Schedule PDFganeshdhage100% (2)
- Manual For Cold Room System (As Built)Document261 pagesManual For Cold Room System (As Built)YerlanNo ratings yet
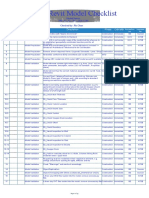
- Revit Model Checklist: Model Name: PRF - P2 - FXX - PXX - CNS-CON Checked By: Ric ChanDocument79 pagesRevit Model Checklist: Model Name: PRF - P2 - FXX - PXX - CNS-CON Checked By: Ric ChanRajaNo ratings yet
- 7360022802PL ForeScoutDocument71 pages7360022802PL ForeScoutManoj KumarNo ratings yet
- 1003 HR Senior IT Bangalore ContactsDocument49 pages1003 HR Senior IT Bangalore ContactsOrganic Nuts0% (1)
- 1003 HR Senior IT Bangalore ContactsDocument49 pages1003 HR Senior IT Bangalore ContactsOrganic Nuts0% (1)
- Ransomware Four Shouldnt IgnoreDocument4 pagesRansomware Four Shouldnt IgnoreManoj KumarNo ratings yet
- Paper Thermo Mechanical EngineeringDocument14 pagesPaper Thermo Mechanical EngineeringAdif HerawanNo ratings yet
- Best U102eDocument2 pagesBest U102ePurcellMurrayNo ratings yet
- Cable Connection & Sealing of Sacrificial AnodesDocument5 pagesCable Connection & Sealing of Sacrificial AnodesmandiNo ratings yet
- Residential Enclosure Options for Surface and Flush MountingDocument26 pagesResidential Enclosure Options for Surface and Flush MountingramadhanNo ratings yet
- OSI 17th DistrictDocument703 pagesOSI 17th DistrictClifford Stone100% (1)
- Architectural Drawing TypesDocument28 pagesArchitectural Drawing TypesAr Ayoushika AbrolNo ratings yet
- Compression Techniques For Digital Hearing AidsDocument77 pagesCompression Techniques For Digital Hearing AidsDario SevieriNo ratings yet
- Goz - Study of The Numerical Instabilities in Lagrangian Tracking of Bubbles and Particles in Two Phase FlowDocument7 pagesGoz - Study of The Numerical Instabilities in Lagrangian Tracking of Bubbles and Particles in Two Phase FlowguilhermehsssNo ratings yet
- JSF 2 - MykongDocument97 pagesJSF 2 - MykongSanthiPippallaNo ratings yet
- Primer commercial tumble dryers guideDocument8 pagesPrimer commercial tumble dryers guideUmar MajeedNo ratings yet
- Introduction To BGP: Border Gateway ProtocolDocument7 pagesIntroduction To BGP: Border Gateway ProtocolKevin KimNo ratings yet
- Creation of Websphere Process Server Custom Server ProfileDocument39 pagesCreation of Websphere Process Server Custom Server Profilesatya.sid8421100% (3)
- FlangeDocument10 pagesFlangeNurul LailyahNo ratings yet
- Jji JoistsDocument48 pagesJji JoistsESNo ratings yet
- Ecofit Pure: en Installation and Maintenance InstructionsDocument56 pagesEcofit Pure: en Installation and Maintenance Instructionsandywl09No ratings yet
- PartsCatalogue EDL26000TE (Q9C3)Document50 pagesPartsCatalogue EDL26000TE (Q9C3)CRISTIAN BARRIOSNo ratings yet
- HuukorDocument1 pageHuukorCynthia MukhwevhoNo ratings yet
- Gecko SMA HR User ManualDocument31 pagesGecko SMA HR User ManualjhunNo ratings yet
- JBL 2242H 800W 460mm Subwoofer with Super Vented Gap CoolingDocument2 pagesJBL 2242H 800W 460mm Subwoofer with Super Vented Gap Coolingadalberto teranNo ratings yet
- NS1 Work Plan Procedure For CW Piping Installation Rev.4Document47 pagesNS1 Work Plan Procedure For CW Piping Installation Rev.4namdq-1No ratings yet
- Radial Piston PumpDocument10 pagesRadial Piston PumpRavikumar GangadharanNo ratings yet
- 2.4 - Mr. H.W.H.R. Hemapala - Resident Engineer (Matale) PDFDocument20 pages2.4 - Mr. H.W.H.R. Hemapala - Resident Engineer (Matale) PDFmpchanakaNo ratings yet
- Motivaciono PismoDocument2 pagesMotivaciono PismoOgnjen NestorovićNo ratings yet
- Rudiger Urbanke Lecture PDFDocument70 pagesRudiger Urbanke Lecture PDFArdevaNo ratings yet
- J Kurozawa Marketing ResumeDocument3 pagesJ Kurozawa Marketing ResumeJon KurozawaNo ratings yet