Professional Documents
Culture Documents
Adhoc and Sensor Networks Characteristics
Uploaded by
Mohammed AkilOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Adhoc and Sensor Networks Characteristics
Uploaded by
Mohammed AkilCopyright:
Available Formats
www.rejinpaul.
com
www.rejinpaul.com
SREE SASTHA INSTITUTE OF ENGINEERING AND TECHNOLOGY
CHEMBARAMBAKKAM, CHENNAI – 600123
DEPARTMENT OF COMPUTER SCIENCE AND ENGINEERING
CS6003 – Adhoc and Sensor Networks (Question Bank)
UNIT – 1
INTRODUCTION
Part – B
1. What are the characteristics and features of adhocnetwork? (6)(May/June
2012) Differentiate Cellular and Adhoc Network.(8)
The following are the characteristics and features of adhocnetwork:
Dynamic topology
Bandwidth constraints and variable links
Energy constrained nodes
Multi-hop communications
Limited security
Determining/detecting changing network topology
Maintaining network topology/connectivity
Scheduling of packet transmission and channel assignment
Routing
Determination of Network Topology
Maintaining Network Connectivity Under Changing Radio Conditions and
Mobility
Transmission Scheduling and Channel Assignment
Packet Routing
Differentiate Cellular and Adhoc Network
Download Useful Materials from Rejinpaul.com
www.rejinpaul.com
www.rejinpaul.com
2. Discuss in detail the characteristics of wireless channel.(8 or 16 Marks )
(May/June 2012)
1. Path Loss
Path loss can be expressed as the ratio of the power of the transmitted
signal to the power of the same signal received by the receiver, on a
given path. It is a function of the propagation distance.
Path loss is dependent on a number of factors such as the radio
frequency used and the nature of the terrain.
Download Useful Materials from Rejinpaul.com
www.rejinpaul.com
www.rejinpaul.com
There are two path loss model,
1. Free propagation model 2. Two ray model or two path model
Free propagation model
The simplest path loss model in which there is a direct-path signal between
the transmitter and the receiver, with no atmospheric attenuation or
multipath components.
The relationship between the transmitted power Pt and the received
power Pr is given by
Where Gt and Gr are the transmitter and receiver antenna gains,1
respectively, in the direction from the transmitter to the receiver, d
is the distance between the transmitter and receiver, and λ = c/f (is
the wavelength of the signal)
Two ray model
The signal reaches the receiver through two paths, one a line-of sight
path, and the other the path through which the reflected (or refracted,
or scattered) wave is received. According to the two-path model, the
received power is given by
Where Pt is the transmitted power, Gt and Gr represent the antenna
gains at the transmitter and the receiver, respectively, d is the distance
between the transmitter and receiver, and ht and hr are the heights of the
transmitter and the receiver, respectively.
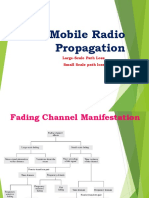
2. Fading
Fading refers to the fluctuations in signal strength when received
at the receiver. Fading can be classified into two types:
1. Fast fading/small-scale fading 2. Slow fading/large-scale fading.
Fast fading refers to the rapid fluctuations in the amplitude, phase, or
multipath delays of thereceived signal, due to the interference
between multiple versions (copies) of the same transmitted signal
arriving at the receiver at slightly different times.
Download Useful Materials from Rejinpaul.com
www.rejinpaul.com
www.rejinpaul.com
The time between the reception of the first version of the signal and the
last echoed signal is called delay spread.The multipath propagation of
the transmitted signal, which causes fast fading.
Slow fading occurs when objects that partially absorb the
transmissions lie between the transmitterand receiver.
Slow fading is so called because the duration of the fade may last for
multiple seconds or minutes.
Slow fading may occur when the receiver is inside a building and the
radio wave must pass through the walls of a building, or when the
receiver is temporarily shielded from the transmitter by a building.
Slow fading is also referred to as shadow fading since the objects
that cause the fade, which may be large buildings or other structures,
block the direct transmission path from the transmitter to the receiver.
Some common measures to overcome the fading effect are 1.Diversity 2.
Adaptive modulation
Diversity Mechanism
Based on the fact that independent paths between the same
transmitter and receiver nodes experience independent fading
effects.
By providing multiple logical channels between the transmitter and
receiver, and sending parts of the signal over each channel, the error
effects due to fading can be compensated.
1. Time diversity mechanisms aim at spreading the data over time
so that the effects of burst errorsare minimized.
2. Frequency diversity mechanisms spread the transmission over
a wider frequency spectrum, oruse multiple carriers for
transmitting the information.
3. Space diversity involves the use of different physical transmission
paths.
Adaptive Modulation Mechanisms
The channel characteristics are estimated at the receiver and the
estimates are sent by the receiver to the transmitter through a
feedback channel.
The transmitter adapts its transmissions based on the received
channel estimates in order to counter the errors that could occur due
to the characteristics of the channel. Adaptive techniques are usually
very complex to implement.
3. Interference
Download Useful Materials from Rejinpaul.com
www.rejinpaul.com
www.rejinpaul.com
Wireless transmissions have to counter interference from a wide
variety of sources. Two main forms of interference are adjacent
channel interference and co-channel interference.
1.Adjacent channel interference case, signals in nearby
frequencies have components outside theirallocated ranges. These
components may interfere with on-going transmissions in the adjacent
frequencies. It can be avoided by carefully introducing guard bands2
between the allocated frequency ranges.
2.Co-channel interference, sometimes also referred to as narrow-
band interference, is due to othernearby systems the same
transmission frequency. Narrow-band interference due to frequency
reuse in cellular systems can be minimized with the use of multiuser
detection.
A guard band is a small frequency band used to separate two adjacent
frequency bands in order to avoid interference between them.
Multiuser detection is an effective approach used to combat the
multiuser interference problems inherent in CDMA systems
Inter-symbol interference
Inter-symbol interference is another type of interference, where
distortion in the received signal is caused by the temporal spreading
and the consequent overlapping of individual pulses in the signal.
When this temporal spreading of individual pulses (delay spread) goes
above a certain limit (symbol detection time), the receiver becomes
unable to reliably distinguish between changes of state in the signal,
that is, the bit pattern interpreted by the receiver is not the same as
that sent by the sender.
Adaptive equalization is a commonly used technique for combating
inter-symbol interference.
4. Doppler Shift
The Doppler shift is defined as the change/shift in the frequency of the
received signal when the transmitter and the receiver are mobile with
respect to each other. If they are moving toward each other, then the
frequency of the received signal will be higher than that of the
transmitted signal, and if they are moving away from each other, the
frequency of the signal at the receiver will be lower than that at the
transmitter.
The Doppler shift fd is given by
Download Useful Materials from Rejinpaul.com
www.rejinpaul.com
www.rejinpaul.com
wherev is the relative velocity between the transmitter and receiver,
and λ is the wavelength of the signal.
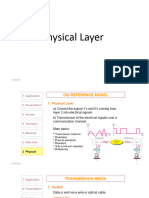
5. Transmission Rate Constraints
Two important constraints that determine the maximum rate of data
transmission on a channel are Nyquist's theorem and Shannon's
theorem.
Nyquist’s Theorem
The signalling speed of a transmitted signal denotes the number
of times per second the signal changes its value/voltage. The
number of changes per second is measured in terms of baud.
The baud rate is not the same as the bit rate/data rate of the signal
since each signal value may be used to convey multiple bits.
TheNyquist theorem gives the maximum data rate possible on a
channel. If B is the bandwidth of the channel (in Hz) and L is the
number of discrete signal levels/voltage values used, then the
maximum channel capacity C according to the Nyquist theorem
is given by
Shannon's Theorem
Noise level in the channel is represented by the SNR. It is the ratio of
signal power (S) to noise power (N), specified in decibels, that is, SNR
= 10 log10(S/N).
Shannon was his theorem on the maximum data rate possible on a
noisy channel. According to Shannon's theorem, the maximum data
rate C is given by
whereB is the bandwidth of the channel (in Hz).
3. Explain the application areas of adhoc networks.(8)(May/June 2012)
1. Military Application
Ad hoc wireless networks can be very useful in establishing
communication among a group of soldiers for tactical operations.
Download Useful Materials from Rejinpaul.com
www.rejinpaul.com
www.rejinpaul.com
Setting up of a fixed infrastructure for communication among group of
soldiers in enemy territories or in inhospitable terrains may not be
possible.
In such a case, ad hoc wireless networks provide required
communication mechanism quickly.
Coordination of military objects moving at high speeds such as fleets of
airplanes, warships.
Ad hoc used in secure communication, compromise of other security
threats and safety of personnel in the tactical operation.
In military application multiple high- power transceivers, each with the
ability to hop between different frequencies, with long life batteries
The primary nature of the communication required in a military
environment enforces certain important requirements on adhoc
wireless networks namely, Reliability, Efficiency, Secure
communication & Support for multicast routing.
2. Collaborative & Distributed computing
Ad hoc wireless network helps in collaborative computing, by
establishing temporary communication infrastructure for quick
communication with minimal configuration among a group of people in
a conference.
In distributed file sharing application reliability is of high importance
which would be provided by ad hoc network.
Other applications such as streaming of multimedia objects among
participating nodes in ad hoc Wireless networks require support for soft
real-time communication
Devices used for such applications could typically be laptops with add
-on wireless interface cards, enhanced personal digital assistants
(PDAs) or mobile devices with high processing power
3. Emergency Operations
Ad hoc wireless networks are very useful in emergency operations such
as search and rescue, crowd control and commando operations
The major factors that favour ad hoc wireless networks for such tasks
are self-configuration of the system with minimal overhead,
independent of fixed or centralised infrastructure, the freedom and
flexibility of mobility, and unavailability of conventional communication
infrastructure.
Download Useful Materials from Rejinpaul.com
www.rejinpaul.com
www.rejinpaul.com
In environments, where the conventional infrastructure based
communication facilities are destroyed due to a war or due to natural
calamities, immediate deployment of adhoc wireless networks would
be a good solution for co-ordinating rescue activities.
They require minimum initial network configuration with very little or
no delay
4. Wireless Mesh Network
Wireless mesh networks are ad hoc wireless network that are formed
to provide an alternate communication infrastructure for mobile or
fixed nodes/users, without the spectrum reuse constraint &
requirement of network planning of cellular network.
It provides many alternate paths for a data transfer session between a
source & destination, resulting in quick reconfiguration of the path
when the existing path fails due to node failure.
Since the infrastructure built is in the form of small radio relaying
devices, the investment required in wireless mesh networks is much
less than what is required for the cellular network counterpart.
The possible deployment scenarios of wireless mesh networks
include: residential zones, highways, business zones, important
civilian regions and university campuses
Wireless mesh networks should be capable of self-organization and
maintenance.
It operates at license-free ISM band around 2.4 GHz & 5 GHz.
It is scaled well to provide support to large number of points.
Major advantage is the support for a high data rate, quick & low cost of
deployment, enhanced services, high scalability, easy extendibility,
high availability & low cost per bit.
Wireless Sensor Networks:
Sensor networks are special category of Adhoc wireless network that
are used to provide a wireless communication infrastructure among the
sensors deployed in a specific application domain.
Sensor nodes are tiny devices that have capability of sensing physical
parameters processing the data gathered, & communication to the
monitoring system
Download Useful Materials from Rejinpaul.com
www.rejinpaul.com
www.rejinpaul.com
The issue that make sensor network a distinct category of adhoc
wireless network are the following:
1. Mobility of nodes :
Mobility of nodes is not a mandatory requirement in sensor networks.
For example, the nodes used for periodic monitoring of soil
properties are not required to be mobile & the nodes that are fitted
on the bodies of patients in a post -surgery ward of a hospital are
designed to support limited or partial mobility
In general, sensor networks need not in all cases be designed to
support mobility of sensor nodes.
2. Size of the network :
The number of nodes in sensor network can be much larger than
that in a typical ad hoc wireless network.
3. Density of deployment :
The density of nodes in a sensor network varies with the domain of
application. For example, Military applications require high availability
of the network, making redundancy a high priority.
4. Power constraints :
The power constraints in sensor networks are much more stringent
than those in ad hoc wireless networks. This is mainly because the
sensor nodes are expected to operate in harsh environmental or
geographical conditions, with minimum or no human supervision
and maintenance.
In certain case, the recharging of the energy source is impossible.
Running such a network, with nodes powered by a battery source with
limited energy, demands very efficient protocol at network, data link, and
physical layer.
The power sources used in sensor networks can be classified
into the following 3 categories:
1. Replenishable Power source: The power source can be replaced
when the existing source is fully drained.
2. Non-replenishable Power source: The power source cannot be
replenished once the network has been deployed. The
replacement of sensor node is the only solution.
3. Regenerative Power source: Here, Power source employed in
sensor network have the capability of regenerating power from
the physical parameter under measurement.
5. Data / Information fusion :
Data fusion refers to the aggregation of multiple packets into one
before relaying it.
Download Useful Materials from Rejinpaul.com
www.rejinpaul.com
www.rejinpaul.com
Data fusion mainly aims at reducing the bandwidth consumed by redundant
headers of the packets and reducing the media access delay involved
in transmitting multiple packets.
Information fusion aims at processing the sensed data at the
intermediate nodes and relaying the outcome to the monitor node.
6. Traffic Distribution :
The communication traffic pattern varies with the domain of
application in sensor networks.
For example, the environmental sensing application generates short
periodic packets indicating the status of the environmental parameter
under observation to a central monitoring station.
This kind of traffic requires low bandwidth.
Ad hoc wireless networks generally carry user traffic such as digitized &
packetized voice stream or data traffic, which demands higher bandwidth.
4. Briefly discuss about the path loss and fading. (16) (May/June 2013)
1. Path Loss
Path loss can be expressed as the ratio of the power of the transmitted
signal to the power of the same signal received by the receiver, on a
given path. It is a function of the propagation distance.
Path loss is dependent on a number of factors such as the radio
frequency used and the nature of the terrain.
Since several of these factors (in particular, the terrain) cannot be the
same everywhere, a single model may not be enough.
So, several models are required to describe the variety of transmission
environments.
There are two path loss maodel,
1. Free propagation model 2. Two ray model or two path model
Free propagation model
The simplest path loss model in which there is a direct-path signal between
the transmitter and the receiver, with no atmospheric attenuation or
multipath components.
The relationship between the transmitted power Pt and the received
power Pr is given by
Where Gt and Gr are the transmitter and receiver antenna gains,1
respectively, in the direction from the transmitter to the receiver, d
Download Useful Materials from Rejinpaul.com
www.rejinpaul.com
www.rejinpaul.com
is the distance between the transmitter and receiver, and λ = c/f (is
the wavelength of the signal)
Two ray model
The signal reaches the receiver through two paths, one a line-of sight
path, and the other the path through which the reflected (or refracted,
or scattered) wave is received. According to the two-path model, the
received power is given by
Where Pt is the transmitted power, Gt and Gr represent the antenna
gains at the transmitter and the receiver, respectively, d is the distance
between the transmitter and receiver, and ht and hr are the heights of the
transmitter and the receiver, respectively.
2. Fading
Fading refers to the fluctuations in signal strength when received at the
receiver. Fading can be classified into two types:
1. Fast fading/small-scale fading 2. Slow fading/large-scale fading.
Fast fading refers to the rapid fluctuations in the amplitude, phase, or
multipath delays of thereceived signal, due to the interference
between multiple versions (copies) of the same transmitted signal
arriving at the receiver at slightly different times.
The time between the reception of the first version of the signal and the
last echoed signal is called delay spread.The multipath propagation of
the transmitted signal, which causes fast fading.
The multipath propagation of the transmitted signal, which causes fast
fading, The multiple signal paths may sometimes add constructively or
sometimes destructively at the receiver, causing a variation in the
power level of the received signal.
Slow fading occurs when objects that partially absorb the
transmissions lie between the transmitterand receiver.
Slow fading is so called because the duration of the fade may last for
multiple seconds or minutes.
Download Useful Materials from Rejinpaul.com
www.rejinpaul.com
www.rejinpaul.com
Slow fading may occur when the receiver is inside a building and the
radio wave must pass through the walls of a building, or when the
receiver is temporarily shielded from the transmitter by a building.
Slow fading is also referred to as shadow fading since the objects
that cause the fade, which may be large buildings or other structures,
block the direct transmission path from the transmitter to the receiver.
Some common measures to overcome the fading effect are 1.Diversity
2. Adaptive modulation
Diversity Mechanism
Based on the fact that independent paths between the same
transmitter and receiver nodes experience independent fading
effects.
By providing multiple logical channels between the transmitter and
receiver, and sending parts of the signal over each channel, the error
effects due to fading can be compensated.
1. Time diversity mechanisms aim at spreading the data over time
so that the effects of burst errorsare minimized.
2. Frequency diversity mechanisms spread the transmission over
a wider frequency spectrum, oruse multiple carriers for
transmitting the information.
3. Space diversity involves the use of different physical transmission
paths.
Adaptive Modulation Mechanisms
The channel characteristics are estimated at the receiver and the
estimates are sent by the receiver to the transmitter through a
feedback channel.
The transmitter adapts its transmissions based on the received
channel estimates in order to counter the errors that could occur due
to the characteristics of the channel. Adaptive techniques are usually
very complex to implement.
5.Briefly explain in detail about the ISSUES IN AD HOC
WIRELESS NETWORKS.
The major issues that affect the design, deployment, &
performance of an ad hoc wireless network system are:
Download Useful Materials from Rejinpaul.com
www.rejinpaul.com
www.rejinpaul.com
1. Medium Access Scheme.
2. Transport Layer Protocol.
3. Routing.
4. Multicasting.
5. Energy Management.
6. Self-Organisation.
7. Security.
8. Addressing & Service discovery.
9. Deployment considerations.
10.Scalability.
11.Pricing Scheme.
12. Quality of Service Provisioning
1. Medium Access Scheme
The primary responsibility of a Medium Access Control (MAC) protocol
in adhoc wireless networks is the distributed arbitration for the shared channel
for transmission of packets. The major issues to be considered in designing a
MAC protocol for adhoc wireless networks are as follows:
Distributed Operation
Synchronization
Hidden Terminals
Exposed terminals
Throughput
Access delay
Fairness
Real-time Traffic support
Resource reservation
Ability to measure resource availability
Capability for power control:
Adaptive rate control:
Use of directional antennas:
2. Routing
The responsibilities of a routing protocol include exchanging the
route information; finding a feasible path to a destination. The major
challenges that a routing protocol faces are as follows:
Mobility :
Download Useful Materials from Rejinpaul.com
www.rejinpaul.com
www.rejinpaul.com
The Mobility of nodes results in frequent path breaks, packet
collisions, transient loops, stale routing information, and difficulty in
resource reservation.
Bandwidth constraint :
Since the channel is shared by all nodes in the broadcast region, the
bandwidth available per wireless link depends on the number of nodes &
traffic they handle.
Error-prone and shared channel :
The Bit Error Rate (BER) in a wireless channel is very high [10-5 to 10
-3 ] compared to that in its wired counterparts [ 10-12 to 10-9 ].
Consideration of the state of the wireless link, signal-to-noise ratio, and
path loss for routing in ad hoc wireless networks can improve the
efficiency of the routing protocol.
Location-dependent contention :
The load on the wireless channel varies with the number of nodes present
in a given geographical region.
This makes the contention for the channel high when the number of
nodes increases.
The high contention for the channel results in a high number of collisions &
a subsequent wastage of bandwidth.
Other resource constraints :
The constraints on resources such as computing power, battery power,
and buffer storage also limit the capability of a routing protocol. The major
requirements of a routing protocol in adhoc wireless networks are
the following.
1 Minimum route acquisition 2. Quick route
. delay reconfiguration
3 4. Distributed routing
. Loop-free routing approach
5
. Minimum control overhead 6. Scalability
7 8. Support for time-sensitive
. Provisioning of QoS traffic:
9. Security and privacy
3. Multicasting:
It plays important role in emergency search & rescue operations & in
military communication. Use of single link connectivity among the nodes in a
multicast group results in a tree-shaped multicast routing topology. Such a
tree-shaped topology provides high multicast efficiency, with low packet
Download Useful Materials from Rejinpaul.com
www.rejinpaul.com
www.rejinpaul.com
delivery ratio due to the frequency tree breaks. The major issues in
designing multicast routing protocols are as follows:
Robustness
Efficiency
Control overhead
Quality of Service
Efficient group management
Scalability
Security
4. Transport Layer Protocol
The main objectives of the transport layer protocols include:
Setting up & maintaining end-to-end connections, Reliable end-
to-end delivery of packets, Flow control & Congestion control.
Examples of some transport layers protocols are,
a. UDP (User Datagram Protocol) :
It is an unreliable connectionless transport layer protocol. It
neither performs flow control & congestion control. It do not take
into account the current network status such as congestion at
the intermediate links, the rate of collision, or other similar
factors affecting the network throughput.
b. TCP (Transmission Control Protocol):
It is a reliable connection-oriented transport layer protocol.
It performs flow control & congestion control. Here performance
degradation arises due to frequent path breaks, presence of stale
routing information, high channel error rate, and frequent
network partitions.
5. Pricing Scheme
Assume that an optimal route from node A to node B passes through
node C, & node C is not powered on.
Then node A will have to set up a costlier & non-optimal route to B.
The non-optimal path consumes more resources & affects the throughput of the system.
As the intermediate nodes in a path that relay the data packets expend
their resources such as battery charge & computing power, they should
be properly compensated.
Hence, pricing schemes that incorporate service compensation or service
reimbursement are required.
Download Useful Materials from Rejinpaul.com
www.rejinpaul.com
www.rejinpaul.com
6. Quality of Service Provisioning (QoS)
QoS is the performance level of services offered by a service
provider or a network to the user.
QoS provisioning often requires ,Negotiation between host & the
network.
Resource reservation schemes.
Priority scheduling & Call admission control.
QoS parameters :
Applications Corresponding QoS parameter
1 Multimedia
. application - 1. Bandwidth & Delay
2
. Military application - 2.Security & Reliability
3 - 3.Finding trustworthy intermediate hosts &
. Defense application routing
4 Emergency search
. and - 4 .Availability
rescue operations
5 Hybrid wireless - 5.Maximum available link life, delay, bandwidth
. network & channel
utilization.
7. Self-Organization
One very important property that an ad hoc wireless network should
exhibit is organizing & maintaining the network by itself.
The major activities that an ad hoc wireless network is required to
perform for self-organization are, Neighbour discovery, Topology
organization & Topology reorganization (updating topology
information)
8. Security
Security is an important issue in ad hoc wireless network as the
information can be hacked. Attacks against network are of 2 types :
I. Passive attack → Made by malicious node to obtain information
transacted in the network without disrupting the operation.
II. Active attack → They disrupt the operation of network.
Download Useful Materials from Rejinpaul.com
www.rejinpaul.com
www.rejinpaul.com
Further active attacks are of 2 types :
1. External attack: The active attacks that are executed by
nodes outside the network.
2. Internal attack: The active attacks that are performed by nodes
belonging to the samenetwork.
The major security threats that exist in ad hoc wireless networks are as
follows :
Denial of service
The attack affected by making the network resource unavailable for
service to other nodes, either by consuming the bandwidth or by
overloading the system.
Resource consumption
The scarce availability of resources in ad hoc wireless network makes it
an easy target for internal attacks, particularly aiming at consuming
resources available in the network.
The major types of resource consumption attacks are,
Energy depletion
Buffer overflow
Host impersonation
A compromised internal node can act as another node and respond
with appropriate control packets to create wrong route entries, and
can terminate the traffic meant for the intended destination node.
Information disclosure
A compromised node can act as an informer by deliberate disclosure of
confidential information to unauthorized nodes.
Interference
A common attack in defense applications to jam the wireless
communication by creating a wide spectrum noise.
9. Addressing and service discovery
Addressing & service discovery assume significance in ad hoc wireless
network due to the absence of any centralised coordinator.
An address that is globally unique in the connected part of the ad hoc
wireless network is required for a node in order to participate in
communication.
Auto-configuration of addresses is required to allocate non-duplicate addresses to the
nodes.
10. Energy Management
Energy management is defined as the process of managing the sources &
consumers of energy in a node or in the network for enhancing the
lifetime of a network.
Download Useful Materials from Rejinpaul.com
www.rejinpaul.com
www.rejinpaul.com
Features of energy management are :
→ shaping the energy discharge pattern of a node’s battery to
enhance battery life.
→ finding routes that consumes minimum energy.
→Using distributed scheduling schemes to improve battery life.
→Handling the processor & interface devices to minimize power
consumption.
Energy management can be classified into the following categories :
o Transmission power management
o Battery energy management
o Processor power management
o Devices power management
10. Scalability
Scalability is the ability of the routing protocol to scale well in a
network with a large number of nodes.
It requires minimization of control overhead & adaptation of the routing
protocol to the network size.
12. Deployment Considerations
The deployment of a commercial ad hoc wireless network has
the following benefits when compared to wired networks.
Low cost of deployment
Incremental deployment
Short deployment time
Reconfigurability
6.What are the major issues to be considered in deploying an ad hoc
wireless network?
a) Scenario of deployment :
The scenario of deployment has significance because the capability
required for a mobile node varies with the environment in which it is used.
The following are some of the different scenarios in which the
deployment issues vary widely :
1. Military deployment :
Download Useful Materials from Rejinpaul.com
www.rejinpaul.com
www.rejinpaul.com
It can be either, Data-centric network : Handle a different pattern
of data traffic & can be partially comprised of static nodes. Eg : a
wireless sensor network.
User-centric network: Consists of highly mobile nodes with or
without any support from any infrastructure.
Eg :soldiers or armored vehicles carrying soldiers
equipped with wireless communication devices.
2. Emergency operations deployment :
Demands a quick deployment of rescue personnel equipped with
hand-held communication equipment.
The network should provide support for time-sensitive traffic such as voice &
video.
Short data messaging can be used in case the resource constraints
do not permit voice communication.
3. Commercial wide-area deployment :
Eg : wireless mesh networks.
The aim of the deployment is to provide an alternate communication
infrastructure for wireless communication in urban areas & areas
where a traditional cellular base station cannot handle the traffic
volume.
4. Home network deployment :
Deployment needs to consider the limited range of the devices that are to be
connected by the network.
Eg : short transmission range avoid network patitions.
b) Required longevity of network :
If the network is required for a short while, battery-powered mobile nodes
can be used.
If the connectivity is required for a longer duration of time, fixed radio
relaying equipment with regenerative power sources can be deployed.
b) Area of coverage :
Determined by the nature of application for which the network is set
up.
Eg : the home area network is limited to the surroundings of a home.
The mobile nodes’ capabilities such as the transmission range & associated
hardware, software, & power source should match the area of coverage required.
c) Service availability :
Defined as the ability of an ad hoc wireless network to provide service
even with the failure of certain nodes. Has significance in a Fully
mobile ad hoc wireless network used for tactical communication & in
partially fixed ad hoc wireless network used in commercial
communication infrastructure such as wireless mesh networks.
d) Operational integration with other infrastructure :
Download Useful Materials from Rejinpaul.com
www.rejinpaul.com
www.rejinpaul.com
Considered for improving the performance or gathering additional
information, or for providing better QoS.
In military environment, integration of ad hoc wireless networks with
satellite networks or unmanned aerial vehicles (UAVs) improves the
capability of the ad hoc wireless networks.
e) Choice of protocol :
The choice of protocols at different layers of the protocol stack is to be
done taking into consideration the deployment scenario.
A TDMA-based & insecure MAC protocol may not be the best suited
compared to a CDMA-based MAC protocol for a mil itary application.
UNIT – 2
Part – B
1. Discuss in detail the contention based protocol with scheduling and reservation
mechanism.(12)(May/June 2012)
Contention-based protocols with reservation mechanisms
Synchronous protocols: All nodes need to be synchronized. Global time
synchronization is difficult to achieve.
Asynchronous protocols: These protocols use relative time information for
effecting reservations.
Example of Contention-based protocols with reservation
mechanisms
Distributed Packet Reservation Multiple Access Protocol (D-
PRMA)
It extends the centralized packet reservation multiple access (PRMA) scheme
into a distributed scheme that can be used in ad hoc wireless networks.
PRMA was designed in a wireless LAN with a base station.
D-PRMA extends PRMA protocol in a wireless LAN.
D-PRMA is a TDMA-based scheme.
The channel is divided into fixed- and equal-sized frames along the time axis.
Download Useful Materials from Rejinpaul.com
www.rejinpaul.com
www.rejinpaul.com
Each frame is composed of s slots and each slot consists of m minislots.
Each minislot is further divided into two control fields, RTS/BI and CTS/BI.
These control fields are used for slot reservation and for overcoming the
hidden terminal problem.
All nodes having packets ready for transmission contend for the first minislot
of each slot.
The remaining (m-1) minislots are granted to the node that wins the
contention.
Also, the same slot in each subsequent frame can be reserved for this
winning terminal until it completes its packet transmission session.
Within a reserved slot, communication between the source and receiver
nodes takes by means of either time division duplexing (TDD) or frequency
division duplexing (FDD).
Any node that wants to transmit packets has to first reserve slots.
A certain period at the beginning of each minislot is reserved for carrier
sensing.
In order to prioritize nodes transmitting voice traffic over nodes transmitting
normal data traffic, two rules are followed in D-PRMA
1st rule->voice nodes are allowed to start contending from minislot 1 with
probability p=1.Others with p<1
2nd rule -> only if the node winning the minislot contention is a voice node,
it is permitted to reserve thesame slot in each subsequent frame until the
end of the session
In order to avoid the hidden terminal problem, all nodes hearing the CTS sent
by the receiver are not allowed to transmit during the remaining period of
that same slot
In order to avoid the exposed terminal problem, a node hearing the RTS but
not the CTS is still allowed to transmit
Requirement 1 ->when a node wins the contention in minislot 1, other
terminals must be prevented fromusing any of the remaining (m-1) minislots
in the same slot for contention
Requirement 2 -> when a slot is reserved in subsequent frames, other
nodes should be prevented fromcontending for those reserved slots
D-PRMA is more suited for voice traffic than for data traffic applications
Contention-based protocols with scheduling mechanisms
o Node scheduling is done in a manner so that all nodes are treated
fairly and no node is starved of bandwidth.
o Scheduling-based schemes are also used for enforcing priorities among
flows whose packets are queued at nodes.
o Some scheduling schemes also consider battery characteristics.
Example of Contention-based protocols with scheduling
mechanisms
Download Useful Materials from Rejinpaul.com
www.rejinpaul.com
www.rejinpaul.com
2. List and explain the issues in designing a MAC protocol for adhoc wireless
networks.(16)(May/June 2013)
The main issues in designing MAC protocol for ad hoc wireless network are:
Bandwidth efficiency
Bandwidth must be utilized in efficient manner
Minimal Control overhead
BW = ratio of BW used for actual data transmission to the total
available BW
Quality of service support
Essential for supporting time-critical traffic sessions
Download Useful Materials from Rejinpaul.com
www.rejinpaul.com
www.rejinpaul.com
They have resource reservation mechanism that takes into
considerations the nature of wireless
channel and the mobility of nodes
Synchronisation
MAC protocol must consider synchronisation between nodes in
the network
Synchronisation is very important for BW (time slot) reservation
by nodes
Exchange of control packets may be required for achieving time
synchronisation among nodes
Hidden and exposed terminal problems
The hidden terminal problem refers to the collision of packets at a
receiving node due to the simultaneous transmission of those nodes
that are not within the direct transmission range of the sender but are
within the transmission range of the receiver.
Collision occurs when both nodes transmit packets at the same time
without knowing about the transmission of each other.
S1 and S2 are hidden from each other & they transmit simultaneously
to R1 which leads to collision
The exposed terminal problem refers to the inability of a node, which is
blocked due to transmission by a nearby transmitting node, to transmit
to another node
If S1 is already transmitting to R1, then S3 cannot interfere with on-
going transmission & it cannot transmit to R2.
The hidden & exposed terminal problems reduce the throughput of a
network when traffic load is high
Error-prone shared broadcast channel
Download Useful Materials from Rejinpaul.com
www.rejinpaul.com
www.rejinpaul.com
When a node is receiving data, no other node in its neighbourhood
should transmit
A node should get access to the shared medium only when its
transmission do not affect any ongoing session
MAC protocol should grant channel access to nodes in such a
manner that collisions are minimized
Protocol should ensure fair BW allocation
Distributed nature/lack of central coordination
Do not have centralized coordinators
Nodes must be scheduled in a distributed fashion for gaining access
to the channel
MAC protocol must make sure that additional overhead, in terms of
BW consumption, incurred due to this control information is not very
high
Mobility of nodes
Nodes are mobile most of the time
The protocol design must take this mobility factor into consideration so
that the performance of the system is not affected due to node
mobility
3. List the important goals of designing a MAC protocol for adhoc wireless networks.
(12)(May/June 2013)
The following are the design goals of designing a MAC protocol for adhoc
wireless networks:
The operation of a protocol should be distributed
The protocol should provide QoS support for real-time traffic
The access delay, which refers to the average delay experienced
by any packet to get transmitted, must be kept low
The available bandwidth must be utilized efficiently
The protocol should ensure fair allocation of bandwidth to nodes
Control overhead must be kept as low as possible
The protocol should minimize the effects of hidden and exposed
terminal problems
The protocol must be scalable to large networks
It should have power control mechanisms in order to efficiently
manage energy consumption of the nodes
The protocol should have mechanisms for adaptive data rate
control
Download Useful Materials from Rejinpaul.com
www.rejinpaul.com
www.rejinpaul.com
It should try to use directional antennas which can provide
advantages such as reduced interference, increased spectrum
reuse, and reduced power consumption
The protocol should provide time synchronization among nodes
4. Classify and define sender initiated protocols.(4)(May/June 2013)
5. Explain in detail about contention based protocol with reservation.(16)(Nov/Dec
2013)(Nov/Dec 2014)
Download Useful Materials from Rejinpaul.com
You might also like
- Home Automation System Using Internet of Things: AbstractDocument9 pagesHome Automation System Using Internet of Things: AbstractPartha Parida0% (1)
- Ps2 Mobile CommunicationDocument10 pagesPs2 Mobile Communicationchikku090700No ratings yet
- Chapter 3 Part 1Document40 pagesChapter 3 Part 1Behailu AsmareNo ratings yet
- Wireless Mobile Communication Unit 3Document28 pagesWireless Mobile Communication Unit 3Siva KumarNo ratings yet
- Chapter Two Small Scale FadingDocument43 pagesChapter Two Small Scale FadingGuta MekesaNo ratings yet
- LF - bt1006 - E01 - 0 Lte Ofdm Principle 32Document29 pagesLF - bt1006 - E01 - 0 Lte Ofdm Principle 32Camilo Bazan HerediaNo ratings yet
- Multipath Propagation and Its Influence on DigitalDocument19 pagesMultipath Propagation and Its Influence on Digitalthabiso.moropaNo ratings yet
- 2 Marks & 13 MarksDocument23 pages2 Marks & 13 MarksECE JPNo ratings yet
- My WaveDocument8 pagesMy WaveFrancis LubangoNo ratings yet
- Channel Sounding CONNECT2013Document7 pagesChannel Sounding CONNECT2013Marcelo NunesNo ratings yet
- U 1 NotesDocument62 pagesU 1 Notessai tharunNo ratings yet
- Wireless Communication FundamentalsDocument9 pagesWireless Communication FundamentalsRavi TejaNo ratings yet
- Chapter One 1.0Document35 pagesChapter One 1.0Arazim Olorundare SheuNo ratings yet
- What Are Different Categories of Antenna and Give An Example of Each?Document8 pagesWhat Are Different Categories of Antenna and Give An Example of Each?Anonymous qYuxgojGe3No ratings yet
- A Survey of Various Propagation Models For Mobile Communication-2003Document32 pagesA Survey of Various Propagation Models For Mobile Communication-2003Manuel Lapeyre CorzoNo ratings yet
- Wireless Notes 2Document34 pagesWireless Notes 2Umair Zahid KhanNo ratings yet
- Two Marks WCDocument6 pagesTwo Marks WCbaby yodaNo ratings yet
- K. RAMAKRISHNAN COLLEGE EC6801 Wireless Communication Question Bank Part ADocument14 pagesK. RAMAKRISHNAN COLLEGE EC6801 Wireless Communication Question Bank Part Aهيثم محمد عبده قائد المخلافيNo ratings yet
- Unit - 1: Introduction of Wireless NetworksDocument23 pagesUnit - 1: Introduction of Wireless NetworksRashmi BhadoriyaNo ratings yet
- Mobile Radio Propagation EffectsDocument42 pagesMobile Radio Propagation EffectsShakeel HashmiNo ratings yet
- Chapter 4MIMODocument15 pagesChapter 4MIMOSachin KumarNo ratings yet
- Elements of Communication SystemDocument31 pagesElements of Communication SystemsujithNo ratings yet
- Channel Hazards and Remedies for Mobile CommunicationsDocument9 pagesChannel Hazards and Remedies for Mobile Communicationsavenger hulkNo ratings yet
- Basic CDMA Concepts ExplainedDocument38 pagesBasic CDMA Concepts ExplainedsumitgoraiNo ratings yet
- Microwave DesignDocument28 pagesMicrowave Designjanine mujeNo ratings yet
- Assignment 2Document4 pagesAssignment 2hamza shahbazNo ratings yet
- Unit 1 MANET NotesDocument24 pagesUnit 1 MANET NotesSrie Teja N150232No ratings yet
- Propagation Models PDFDocument7 pagesPropagation Models PDFbikuttanNo ratings yet
- Unit IDocument48 pagesUnit IManochandar ThenralmanoharanNo ratings yet
- Fundamentals of Microwaves & Satellite TechnologiesDocument55 pagesFundamentals of Microwaves & Satellite TechnologiesRodric PeterNo ratings yet
- Small Scale FadingDocument18 pagesSmall Scale FadingkarthikNo ratings yet
- Small Scale FadingDocument58 pagesSmall Scale FadingShahjahan AfridiNo ratings yet
- Microwave, Radar and Satellite Communication Systems ExplainedDocument9 pagesMicrowave, Radar and Satellite Communication Systems ExplainedPatrick AfefohNo ratings yet
- Ec 71 QBDocument16 pagesEc 71 QBepregithaNo ratings yet
- Fifth Semester Wireless Communication Two Marks With Answers Regulation 2013Document12 pagesFifth Semester Wireless Communication Two Marks With Answers Regulation 2013PRIYA RAJI78% (9)
- Lecture 1 - Microwave SystemsDocument53 pagesLecture 1 - Microwave SystemsAbdul SuboorNo ratings yet
- Mobile Radio Propagation Path Loss and Small-Scale FadingDocument59 pagesMobile Radio Propagation Path Loss and Small-Scale FadingMohd KaifNo ratings yet
- Unit II Possible Questions With AnswersDocument19 pagesUnit II Possible Questions With AnswersNithish.V.J.No ratings yet
- IJCER (WWW - Ijceronline.com) International Journal of Computational Engineering ResearchDocument5 pagesIJCER (WWW - Ijceronline.com) International Journal of Computational Engineering ResearchInternational Journal of computational Engineering research (IJCER)No ratings yet
- How Fiber Optics WorksDocument4 pagesHow Fiber Optics Worksxyz156No ratings yet
- Politécnica University of Puerto Rico - Hato Rey Computer Engineering Department Assignment 2Document5 pagesPolitécnica University of Puerto Rico - Hato Rey Computer Engineering Department Assignment 2Christian Perez PerezNo ratings yet
- Lecture 3 Physical LayerDocument38 pagesLecture 3 Physical LayerBatool SajidaNo ratings yet
- Johnrose HynsonDocument4 pagesJohnrose HynsonRomel SilaoNo ratings yet
- EX NO: 01 Wireless Channel Simulation Including Fading and Doppler Effects 05-11-20 AimDocument5 pagesEX NO: 01 Wireless Channel Simulation Including Fading and Doppler Effects 05-11-20 AimKamal Cruz LeNo ratings yet
- CHAPTER Four: Wireless Networks PrinciplesDocument50 pagesCHAPTER Four: Wireless Networks Principlesachut achutNo ratings yet
- Oc All Units Notes and Question BankDocument193 pagesOc All Units Notes and Question BankArpit RajputNo ratings yet
- RF Communication Circuit DesignDocument32 pagesRF Communication Circuit DesignAkhilesh MohanNo ratings yet
- Supervisory Control and Data Transmission EquipmentDocument31 pagesSupervisory Control and Data Transmission EquipmentMU Len GANo ratings yet
- Unit 2Document37 pagesUnit 2Rakesh MenonNo ratings yet
- 5.3 Tuorial Co5Document14 pages5.3 Tuorial Co5HarreniNo ratings yet
- WC UNIT 1 Two Marks2021 22Document5 pagesWC UNIT 1 Two Marks2021 22r jeyanthiNo ratings yet
- Electronics QuestionDocument13 pagesElectronics QuestionAkash NegiNo ratings yet
- Subjective 1) What Is Encapsulation? Discuss Generic Routing EncapsulationDocument6 pagesSubjective 1) What Is Encapsulation? Discuss Generic Routing EncapsulationShannon GonsalvesNo ratings yet
- Win, Scholtz - 1998 - Impulse Radio How It WorksDocument3 pagesWin, Scholtz - 1998 - Impulse Radio How It WorksAhmed AbdelraheemNo ratings yet
- Lecture 3 - Physical LayerDocument38 pagesLecture 3 - Physical LayerMuhammad Noman JavidNo ratings yet
- Electronics Interview QuestionsDocument8 pagesElectronics Interview QuestionsEhsan FirdausNo ratings yet
- MICROWAVE COMMUNICATION SYSTEM DESIGN by Kathleen Sales, Pia Libutan, Gem Cabanos & Pau PantonDocument13 pagesMICROWAVE COMMUNICATION SYSTEM DESIGN by Kathleen Sales, Pia Libutan, Gem Cabanos & Pau PantonKathleen Sales100% (1)
- Physical LayerDocument33 pagesPhysical LayerUmer HanifNo ratings yet
- Ec2401 - Wireless Communication - Question Bank Unit IDocument10 pagesEc2401 - Wireless Communication - Question Bank Unit Inazareth621No ratings yet
- Digital Transmission: Ref: Data and Computer Communications, William StallingDocument16 pagesDigital Transmission: Ref: Data and Computer Communications, William StallingSwet SheershNo ratings yet
- Signal Integrity: From High-Speed to Radiofrequency ApplicationsFrom EverandSignal Integrity: From High-Speed to Radiofrequency ApplicationsNo ratings yet
- Shred X - Workout PlanDocument5 pagesShred X - Workout PlanMohammed AkilNo ratings yet
- Andrew Lockwood: Trading Cheat SheetDocument18 pagesAndrew Lockwood: Trading Cheat SheetSifisoNo ratings yet
- 218 - EC8352, EC6303 Signals and Systems - Important Questions 2Document4 pages218 - EC8352, EC6303 Signals and Systems - Important Questions 2Mohammed AkilNo ratings yet
- Guru Mann's Ultimate Back Workout & Nutrition PlanDocument9 pagesGuru Mann's Ultimate Back Workout & Nutrition Planshyam pandeyNo ratings yet
- Guru Mann's Dumbbell Home Workout SplitDocument5 pagesGuru Mann's Dumbbell Home Workout Splitashish chopraNo ratings yet
- Ind Nifty BankDocument2 pagesInd Nifty BankEshaan ChadhaNo ratings yet
- Justice L Nageshwara Rao of Supreme Court in The Case of Narendra Vs K MeenaDocument11 pagesJustice L Nageshwara Rao of Supreme Court in The Case of Narendra Vs K MeenaMohammed AkilNo ratings yet
- Electrical Engineering and Instrumentation QuestionsDocument20 pagesElectrical Engineering and Instrumentation QuestionsMohammed AkilNo ratings yet
- Assignment ques-WPS Office 5Document1 pageAssignment ques-WPS Office 5Mohammed AkilNo ratings yet
- Assignment ques-WPS OfficeDocument2 pagesAssignment ques-WPS OfficeMohammed AkilNo ratings yet
- Ec6401 PDFDocument2 pagesEc6401 PDFMohammed AkilNo ratings yet
- CS6003Document10 pagesCS6003Rethina Sabapathi PandiyanNo ratings yet
- Ec6802 QB Rejinpaul Iii PDFDocument10 pagesEc6802 QB Rejinpaul Iii PDFSuvathi SarathNo ratings yet
- Ec6401 PDFDocument2 pagesEc6401 PDFMohammed AkilNo ratings yet
- Cs 6003Document2 pagesCs 6003Mohammed AkilNo ratings yet
- Ec6401 PDFDocument2 pagesEc6401 PDFMohammed AkilNo ratings yet
- Ec6401 PDFDocument2 pagesEc6401 PDFMohammed AkilNo ratings yet
- Ec6802 QB Rejinpaul Iii PDFDocument10 pagesEc6802 QB Rejinpaul Iii PDFSuvathi SarathNo ratings yet
- EC6401Document2 pagesEC6401Mohammed AkilNo ratings yet
- Ec6401 PDFDocument2 pagesEc6401 PDFMohammed AkilNo ratings yet
- EC6401Document2 pagesEC6401Mohammed AkilNo ratings yet
- Electrical Engineering and Instrumentation QuestionsDocument20 pagesElectrical Engineering and Instrumentation QuestionsMohammed AkilNo ratings yet
- Fatima Michael College of Engineering & TechnologyDocument4 pagesFatima Michael College of Engineering & TechnologyMohammed AkilNo ratings yet
- CS6003 2M RejinpaulDocument15 pagesCS6003 2M RejinpaulMohammed AkilNo ratings yet
- 188 - EC6701 RF and Microwave Engineering - Important QuestionsDocument16 pages188 - EC6701 RF and Microwave Engineering - Important QuestionsMohammed AkilNo ratings yet
- Cs6003 Asn Rejinpaul Iq Am19Document1 pageCs6003 Asn Rejinpaul Iq Am19Druthvik SNo ratings yet
- 188 - EC6701 RF and Microwave Engineering - Important QuestionsDocument16 pages188 - EC6701 RF and Microwave Engineering - Important QuestionsMohammed AkilNo ratings yet
- GSM Based Water Quality Monitoring System Using ArduinoDocument6 pagesGSM Based Water Quality Monitoring System Using Arduinoesubalew tadesseNo ratings yet
- Literature Review of Voice Controlled WheelchairDocument6 pagesLiterature Review of Voice Controlled Wheelchairfvhacvjd100% (1)
- Time Sync Protocols Surveyed for Wireless Sensor NetworksDocument11 pagesTime Sync Protocols Surveyed for Wireless Sensor NetworkszbouzghaNo ratings yet
- Technical Seminar ReportDocument32 pagesTechnical Seminar ReportGowthami Singh RajputNo ratings yet
- Underwater Wireless Sensor Network: A Review: Shraddha S. Chafale, Prof. N.M. DhandeDocument5 pagesUnderwater Wireless Sensor Network: A Review: Shraddha S. Chafale, Prof. N.M. DhandeAnonymous lPvvgiQjRNo ratings yet
- Ronds Solutions BrochureDocument10 pagesRonds Solutions BrochurePakistan Hockey TeamNo ratings yet
- An Overview of Internet of Things (IoT) PDFDocument16 pagesAn Overview of Internet of Things (IoT) PDFHamzuz ôsčãrNo ratings yet
- Integration of WSN With Iot Applications: A Vision, Architecture, and Future ChallengesDocument25 pagesIntegration of WSN With Iot Applications: A Vision, Architecture, and Future ChallengesNasriMohsenNo ratings yet
- Wireless Ad Hoc Networks Course OverviewDocument8 pagesWireless Ad Hoc Networks Course OverviewShivesh SinghNo ratings yet
- Midterm 4thDocument29 pagesMidterm 4thMaryam AsadNo ratings yet
- Feasibility and Challenges of 5G Network DeploymenDocument16 pagesFeasibility and Challenges of 5G Network DeploymenAkashNo ratings yet
- Design of A Real Time Smart Honking SystemDocument6 pagesDesign of A Real Time Smart Honking SystemArka MajumdarNo ratings yet
- Electricity Generation Through StaircaseDocument263 pagesElectricity Generation Through Staircaseanu_collegeNo ratings yet
- Building Wireless Sensor Networks Using Arduino - Sample ChapterDocument23 pagesBuilding Wireless Sensor Networks Using Arduino - Sample ChapterPackt Publishing100% (1)
- UNIT-II-EC8702-Adhoc and Wireless Sensor NetworksDocument34 pagesUNIT-II-EC8702-Adhoc and Wireless Sensor NetworksparantnNo ratings yet
- Data Dissemination in Wireless Sensor Networks Using Software AgentsDocument7 pagesData Dissemination in Wireless Sensor Networks Using Software AgentsomjeeNo ratings yet
- A Study On Smart Irrigation System Using IoT For S PDFDocument4 pagesA Study On Smart Irrigation System Using IoT For S PDFMuhammad UsmanNo ratings yet
- IOT4ALLDocument203 pagesIOT4ALLMarco Antonio Poveda OñateNo ratings yet
- MS8391-EV: Multiple Sensor Network CameraDocument2 pagesMS8391-EV: Multiple Sensor Network Cameraana cireraNo ratings yet
- Thesis-2 0 1 1Document42 pagesThesis-2 0 1 1Jake BasinganNo ratings yet
- Sensors 16 01892 v2 PDFDocument22 pagesSensors 16 01892 v2 PDFnitish anandNo ratings yet
- Journal of Computer Science Research - Vol.4, Iss.3 July 2022Document38 pagesJournal of Computer Science Research - Vol.4, Iss.3 July 2022Bilingual PublishingNo ratings yet
- ST Journal of Research 4.1 - Wireless Sensor NetworksDocument164 pagesST Journal of Research 4.1 - Wireless Sensor Networksclara_colombo1996No ratings yet
- Distributed Jammer Network Impact and CharacterizationDocument6 pagesDistributed Jammer Network Impact and CharacterizationAaron GalvezNo ratings yet
- Advances in Mechanical and Electronic Engineering Volume 3 PDFDocument526 pagesAdvances in Mechanical and Electronic Engineering Volume 3 PDFMoustafa KeddiNo ratings yet
- FANET Application Scenarios and Mobility Models - 2017Document4 pagesFANET Application Scenarios and Mobility Models - 2017Eru Adha DenyNo ratings yet
- Black Box System DesignDocument55 pagesBlack Box System DesignVin Ay ReddyNo ratings yet
- 4 - Internet of Things (IoT)Document92 pages4 - Internet of Things (IoT)Kirubel DessieNo ratings yet
- EC8702 - Wireless Sensor and Ad Hoc NetworksDocument2 pagesEC8702 - Wireless Sensor and Ad Hoc NetworksDharani KumarNo ratings yet