Professional Documents
Culture Documents
OPENING PRAYERg3
OPENING PRAYERg3
Uploaded by
Klaudine Santos0 ratings0% found this document useful (0 votes)
8 views14 pagesOriginal Title
OPENING-PRAYERg3
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
8 views14 pagesOPENING PRAYERg3
OPENING PRAYERg3
Uploaded by
Klaudine SantosCopyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 14
NETIQUTTE
*When you enter the online class or google meet you
should have a great good morning or good afternoon
to your prof.
*Mute the mic when someone is speaking
*Avoid using capital letters in each word
*Avoid using emoji or stickers when sending an
email to prof
* I want to say before the end of google meet to
may prof is thank you or good bye
According to the dictionary of Military and
Associated Terms of the US Department of
Defense, information systems security is
“The protection of information and
information systems against unauthorized
access or modification of information,
whether in storage, processing, or transit,
and against denial of service .
*Why are information systems are
vulnerable to destruction,error and
abuse.
In short, if you operate a business today, you need to make
security and con trol a top priority. Security refers to the
policies, procedures, and technical mea sures used to prevent
unauthorized access, alteration, theft, or physical damage to
information systems
>Why system and Vulnerable
When large amounts of data are stored in electronic form, they
are vulnerable to many kinds of threats. Through
communications networks, information sys tems in different
locations are interconnected.
CONTEMPORARY SECURITY CHALLENGES AND VULNERABILITIES
WI-FI SECURITY CHALLENGES
*What is the business value of security
and control?
Companies have very valuable information assets to protect.
Systems often house confidential information about individuals’
taxes, financial assets, medi cal records, and job performance
reviews. They also can contain information on
corporateoperations, including trade secrets, new product
development plans, and marketing strategies. Government
systems may store information on weap ons systems, intelligence
Legal and Regulatory Requirements for Electronic
Records Management
Electronic Evidence and Computer Forensics
*What are the components of an
organizational framework for security and
control?
Even with the best security tools, your information
systems won’t be reliable and secure unless you
know how and where to deploy them.
>Information Systems Controls
>Risk Assessment
>Security Policy
>The Role of Auditing
*What are the most important tools and
technologies for safeguarding
information resources?
Businesses have an array of technologies for protecting their
information resources.
They include tools for managing user identities, preventing
unau
thorized access to systems and data, ensuring system availability
and ensuring software quality
>Identity Management and Authentication
-Authentication
-Biometric authentication
>Firewalls, Intrusion Detection Systems,
and Antivirus Software
Without protection against malware and intruders,
connecting to the Internet would be very dangerous.
Firewalls, intrusion detection systems, and antivirus
software have become essential business tools.
-Firewalls
- Intrusion Detection Systems
-Antivirus and Antispyware Software
- Unified Threat Management Systems
*Encryption and Public Key Infrastructure
-Many businesses use encryption to protect digital
information that they store, physically transfer, or send
over the Internet.
*Ensuring System Availability
As companies increasingly rely on digital networks for
revenue and opera tions, they need to take additional
steps to ensure that their systems and appli cations are
always available.
>Controlling Network Traffic: Deep Packet
Inspection
> Securing Mobile Platforms
*Ensuring Software Quality
In addition to implementing effective security and controls,
organizations can improve system quality and reliability by
employing software metrics and rig orous software testing.
Software metrics are objective assessments of the sys tem in
the form of quantified measurements.
IN OUR CLASS WE
DON'T DO EASY
WE MAKE EASY
HAPPEN THROUGH
HARD WORK AND
LEARNING
You might also like
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (122)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (590)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (842)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5807)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (401)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (897)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1091)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (346)
- Sales Quotes Ebook v3Document31 pagesSales Quotes Ebook v3am_jalu100% (2)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The Quintessence of Wisdom-120112Document36 pagesThe Quintessence of Wisdom-120112Nagarajan Vaitheeswaran100% (3)
- Custom Pathfinder Character SheetDocument2 pagesCustom Pathfinder Character SheetLordCoSaX100% (2)
- Double-Layer Bow Turban TUTORIALDocument25 pagesDouble-Layer Bow Turban TUTORIALcindmau4No ratings yet
- Motor Relearning ProgrammeDocument22 pagesMotor Relearning ProgrammeUzra ShujaatNo ratings yet
- Katherine Johnson Mary Jackson and Dorothy VaughanDocument8 pagesKatherine Johnson Mary Jackson and Dorothy Vaughanapi-326382783No ratings yet
- AR - 8701 Landscape Design - FullDocument115 pagesAR - 8701 Landscape Design - FullASWIN KUMAR N S100% (3)
- Tvl-He - Fbs-Q4-Las-2 Week 2 Melc 2 - Undertake Suggestive Selling and Upselling StrategiesDocument8 pagesTvl-He - Fbs-Q4-Las-2 Week 2 Melc 2 - Undertake Suggestive Selling and Upselling StrategiesEcho Siason EleccionNo ratings yet
- Blank Thinking Maps 1Document9 pagesBlank Thinking Maps 1Klaudine SantosNo ratings yet
- I Chose That Field of Study Because I've Always Been Interested inDocument2 pagesI Chose That Field of Study Because I've Always Been Interested inKlaudine SantosNo ratings yet
- Alcu Logo Making Mechanics FinalDocument2 pagesAlcu Logo Making Mechanics FinalKlaudine SantosNo ratings yet
- The Tourism and Industry Hospitality1 Hms 1dDocument11 pagesThe Tourism and Industry Hospitality1 Hms 1dKlaudine SantosNo ratings yet
- Targe T: Events ManagementDocument15 pagesTarge T: Events ManagementKlaudine SantosNo ratings yet
- Facebook: Case Study No. 1Document7 pagesFacebook: Case Study No. 1Klaudine SantosNo ratings yet
- Rfid Propels The Angkasa Library Management System.: Summary To The Case # 8Document4 pagesRfid Propels The Angkasa Library Management System.: Summary To The Case # 8Klaudine SantosNo ratings yet
- Condition Assessment of Concrete StructuresDocument28 pagesCondition Assessment of Concrete Structuresmoizm53No ratings yet
- Caterpillar 966d Wheel Loader Parts Manual4Document10 pagesCaterpillar 966d Wheel Loader Parts Manual4Ahmad Waqar BhattiNo ratings yet
- Grade 10 Division Numeracy Post Test 2024Document10 pagesGrade 10 Division Numeracy Post Test 2024emzxe30No ratings yet
- Can You Find All The Hidden Words in This Word Search? Words Can Go in The Following DirectionsDocument3 pagesCan You Find All The Hidden Words in This Word Search? Words Can Go in The Following Directionspj501No ratings yet
- Different Types OF: Loans and AdvancesDocument19 pagesDifferent Types OF: Loans and Advancesharesh KNo ratings yet
- Yvonne Barnes-Holmes PBBT - Denmark Sep 2023 AarhusDocument2 pagesYvonne Barnes-Holmes PBBT - Denmark Sep 2023 AarhusGiancarlo ZPNo ratings yet
- The Motives of Oedipus RexDocument3 pagesThe Motives of Oedipus RexKhaya PaladaNo ratings yet
- International Migration, Racism, Discrimination and XenophobiaDocument37 pagesInternational Migration, Racism, Discrimination and XenophobiaSara KheiriNo ratings yet
- Complete The Blanks With The Words and Phrases From The Box. Be Careful! There Are 2 Extra Words/phrasesDocument1 pageComplete The Blanks With The Words and Phrases From The Box. Be Careful! There Are 2 Extra Words/phrasesAnnaNo ratings yet
- The Characteristics of Thai Movies and Factors Contributing To Becoming Widely Known in International Markets PDFDocument6 pagesThe Characteristics of Thai Movies and Factors Contributing To Becoming Widely Known in International Markets PDFDisneyboiNo ratings yet
- KinematicsDocument7 pagesKinematicsOrlee Villafañe JrNo ratings yet
- Session 09 Present ProgressiveDocument15 pagesSession 09 Present ProgressiveKevin GuevaraNo ratings yet
- CS Foundation - Sale of Goods Act, 1930Document45 pagesCS Foundation - Sale of Goods Act, 1930uma mishraNo ratings yet
- Company Law PDFDocument15 pagesCompany Law PDFRohan PatelNo ratings yet
- CA-33 Part - 1 (Section 1 To 5) PDFDocument205 pagesCA-33 Part - 1 (Section 1 To 5) PDFSumit ShekhawatNo ratings yet
- Solar Powered DC Fridge Owners ManualDocument20 pagesSolar Powered DC Fridge Owners ManualPawel Vlad LatoNo ratings yet
- Cam All Information by WikipediaDocument19 pagesCam All Information by WikipediaZexmexNo ratings yet
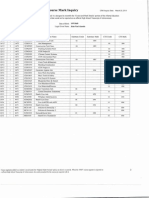
- LastthreemonthPayslip 11Document7 pagesLastthreemonthPayslip 11delicata.benNo ratings yet
- Cyber SecurityDocument10 pagesCyber SecurityHappy Surjya DaimaryNo ratings yet
- 21st Century of ChristianityDocument13 pages21st Century of ChristianityAllem Jude Candelaria OliNo ratings yet
- Img 20150510 0001Document2 pagesImg 20150510 0001api-284663984No ratings yet
- A Word From The Chair: Gerontology LuncheonDocument4 pagesA Word From The Chair: Gerontology LuncheonLeonard SanchezNo ratings yet