Professional Documents
Culture Documents
NetSPI Scott Sutherland RedvsBlue v3.2
NetSPI Scott Sutherland RedvsBlue v3.2
Uploaded by
Rodrigues RicardoCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
NetSPI Scott Sutherland RedvsBlue v3.2
NetSPI Scott Sutherland RedvsBlue v3.2
Uploaded by
Rodrigues RicardoCopyright:
Available Formats
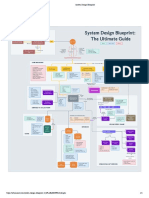
Introduc�on to common Brought to you by
R ed T eam Attacks & TM
B lue T eam Defens es
Common Red Team Common Common Blue Team
Attack Vectors and T echniques Attack K ill C hain Detective and P reventative C ontrols
C ommon Variations RED BLUE E ndpoint Network Process
Create Phishing TEAM TEAM
Prepare Phishing
Deny / log VRY requests User awareness training
Find Emails & Users Verify Emails & Users Deny / log EXPN requests Track company’s point of
Payloads & Sites Log RCPT commands executed presence and employee
LinkedIn.com Google.com
SMTP Send HTTP Office365 Create Buy A�acks NA sequen�ally
Large numbers of HTTP NTLM
exposure.
Monitor domain expira�ons
Server Test with OWA Content-Filter Expired
Data.com Bing.com
Cmds Emails NTLM MS APIs Excep�ons Domains from public resources requests
Send Phishing
Email filters, thresholds, and spam User awareness training
Email Sources Email Targets Email Content rules Incident response procedures
Email source verifica�on
Spoofed Spoofed Domain
Hacked Mass Targeted Pretext Malicious
Malicious Emails NA Blacklist checks
SPF record checks
Internal External Similar to Files &
Domain Domain Company
Account Mailing Mailing Scenario Links
Embedding to employee addresses Logs / SEIM / Alerts
Deliver the
Asset / config / patch mgmt. Email filters, thresholds, and spam User awareness training
Malicious Links Website Components Files An�-virus / HIDs / HIPs rules Incident response procedures
@ Secure group policy Deny / log relay requests
Port Geo
Phish Creden�al Java Applet
Brower
Browser Common Office Payloads Mail client configura�ons
MS Office Security Se�ngs
Secure caching provider
Web filtering / white lis�ng
Web Collec�on ClickOnce Add-On exec file Docs + Web browser configura�ons Authen�cated HTTP proxies
Scan Locate Exploit
Site Form HTA Exploit formats Macros to employee systems Logs / SEIM / Alerts Logs / SEIM / Alerts
Common Payload Command Types Run the Payload Asset / config / patch mgmt.
An�-virus / HIDs / HIPs
Commands
Secure group policy se�ngs User awareness training
NA
Commands Binaries Scripts Standard Assembly Byte Applica�on white lis�ng Incident response procedures
Code Least privilege enforcement
cmd, wmi, wrm, Executable, PS, VB, VBS, Code Code
�p, net, etc Installer, Library JS, Bat C, C++, C# shellcode Java, .Net on employee systems Logs / SEIM / Alerts
Asset / config / patch mgmt.
Common Local Persistence Methods Maintain Local An�-virus / HIDs / HIPs
Secure group policy se�ngs
Persistence
User awareness training
Applica�on white lis�ng NA
PW / Pvt Key File, Registry, WMI Incident response procedures
Custom Windows Scheduled Code / File Driver Least privilege enforcement
PW Hash & Applica�on Event Logs / SEIM / Alerts
Providers Service Task Modifica�on BIOS
Kerb Ticket Autoruns Trigger on employee systems FIM / WMI event triggers
Egress Ports Common Protocols Common Types Obtain Command & Asset / config / patch mgmt.
An�-virus / HIDs / HIPs
Firewall Rules / Segmenta�on
NIDs / NIPs
Control Channel
Secure group policy se�ngs Fix Up Protocols User awareness training
DNS SSH FTP Torrent Bind Shell Applica�on white lis�ng Web Filtering / White Lis�ng Incident response procedures
TCP IPv4 HTTP Least privilege enforcement Authen�cated HTTP Proxies
ICMP Telnet NFS IM Beacon Reverse Shell
UDP IPv6 HTTPS Logs / SEIM / Alerts Logs / SEIM / Alerts
NTP Rlogin SMB SMTP Web Shell from employee systems
An�-virus / HIDs / HIPs
Weak Configura�ons Local Exploits Escalate Local Secure group policy se�ngs
Applica�on white lis�ng
Privileges
Admin awareness training
Least privilege enforcement Logs / SEIM / Alerts
Weak Password Incident response procedures
Insecure Insecure Insecure Insecure Excessive Logs / SEIM / Alerts
or Password OS APP DEP / ASLR / SEH
Service Schtask GPO Protocol Privilege
Storage Method on employee systems Micro virtualizing / sandboxes
Steal
Common local Targets Perform Local Asset / config / patch mgmt.
An�-virus / HIDs / HIPs
Authen�ca�on Tokens
Password /
Password Kerberos OS, Domain,
Users & Cache Services & Installed Files &
Recon / Discovery Secure group policy se�ngs
Applica�on white lis�ng
Least privilege enforcement
Logs / SEIM / Alerts
Admin awareness training
Incident response procedures
Hash Ticket & Network
Private Key
(PTH) (PTT) Informa�on
Groups & Logs Processes Apps Registry on employee systems Logs / SEIM / Alerts
Passive Locate Domain, Ent.
Perform Network
HIDs / HIPs
Firewall rules / segmenta�on
Ac�ve Discovery Logs / SEIM / Alerts
NIDs / NIPs
Recon & Forest Admins Canaries
Recon / Discovery
Honey pots Admin awareness training
- Local & Domain User Accounts
Ping & DNS & Share & DB, SP & Remote Tarpits Incident response procedures
Trace Domain - Domain Computer Accounts
Port ADS Logon Sessions Canary networks, systems, & accounts
Sniffing Mail Svr - Local and Network Files
Route
Scanning Queries Scanning Scanning
GPOs & SPN
& Processes on internal networks File Audi�ng
Logs / SEIM / Alerts
Stolen Asset / config / patch mgmt.
Authen�ca�on Tokens
Common Methods Perform Lateral An�-virus / HIDs / HIPs
Secure group policy se�ngs
Firewall Rules / Segmenta�on
NIDs / NIPs
Don’t use shared local accounts
Use a separate domain user and
Movement
Honey Pots
Applica�on white lis�ng server admin accounts
Password Kerberos DB, App Remote Tarpits
Password / MGMT Windows Sched File GPO, Least privilege enforcement Maintain secure configs
Canary networks, systems, & accounts
Hash Ticket & VM Exploit, Logs / SEIM / Alerts Incident response procedures
Private Key Services Service Task Share SCCM
(PTH) (PTT) Servers Physical between systems/networks Host-based Firewall
Logs / SEIM / Alerts
Steal Admin A�ack
Escalate Domain
Asset / config / patch mgmt.
Firewall Rules / Segmenta�on
Escalate to Root Domain An�-virus / HIDs / HIPs
NIDs / NIPs
Don’t use shared local accounts
Authen�ca�on Tokens DCs Secure group policy se�ngs Use a separate domain user and
Privileges
Honey Pots
Applica�on white lis�ng server admin accounts
Password Kerberos Exploits, Domain Exploits Tarpits
Password / Shared Delegated Privs Least privilege enforcement Maintain secure configs
Hash Ticket Kerberoast Trusts & Kerberoast Canary networks, systems, & accounts
Logs / SEIM / Alerts Incident response procedures
Private Key
(PTH) (PTT) & GPP
Password Nested Groups
SID History GPO via common vectors Host-based Firewall
Logs / SEIM / Alerts
Least Privilege Enforcement
Common Data Stores Common Data Targets Find and Access Two-Factor Authen�ca�on
Data Encryp�on and Secure Key
Firewall Rules / Segmenta�on
NIDs / NIPs
User awareness training
Incident response procedures
Honey Pots
Mail File Database Code
PII
IP & Financial
Insider Sensi�ve Data Management
File, Applica�on, and Database
Tarpits
Canary networks, systems, & accounts
Manage keys securely
Consolidate and isolate sensi�ve
PHI Trading Audi�ng data stores
Servers Servers Servers Repositories Research Data
CHD Info in common data stores Host DLP / Logs / SEIM / Alerts
Logs / SEIM / Alerts
Common Protocols Physical
Exfiltrate
Firewall Rules / Segmenta�on
Data Handling HIDs / HIPs Email Server Configura�on
TCP/UDP, v4/6 Media Host DLP Network DLP
Sensi�ve Data
User awareness training
Large file upload detec�on Fix Up Protocols
Common & Standard & C2 and Staged Large Compression Incident response procedures
LAN & USB CD Mail client/server se�ngs Web Filtering / Auth Proxy
Wireless Uncommon Custom Alterna�ve & not & Small Encoding Logs / SEIM / Alerts Canary Data Samples
& SD DVD using common channels
Ports Protocols Channels Staged Files Encryp�on Logs / SEIM / Alerts
Stolen Two Common Internet Facing
Authen�ca�on Tokens Factor Interfaces
Maintain Remote Access Enforce Two-factor authen�ca�on on
all external interfaces
Firewall rules / segmenta�on
NIDs / NIPs Admin awareness training
Without a C2
Limit Terminal Service, Citrix, and
Canary networks, systems, Incident response procedures
Password Kerberos Private Key RDP Office365 VDE access to specific groups during
Password / Web Web Based applica�ons, and accounts Enforce strong account policies
specific hours
Hash Ticket Token Seed VPN SSH Azure Logged events / SEIM / alerts
Private Key Shells Citrix & TS using common interfaces Geo / IP limi�ng
(PTH) (PTT) Skeleton Key VDE AWS
Author: Sco� Sutherland, NetSPI 2016
Version: 3.2
You might also like
- System Design BlueprintDocument1 pageSystem Design BlueprintyashNo ratings yet
- 1 Web App Hacking Password Reset Functionality m1 SlidesDocument8 pages1 Web App Hacking Password Reset Functionality m1 SlidessebyhNo ratings yet
- 37 Signs The Bitcoin Bear Market Is OverDocument39 pages37 Signs The Bitcoin Bear Market Is OverKurt GrelaNo ratings yet
- Apollo Education Group FY '16 10-KDocument147 pagesApollo Education Group FY '16 10-KDaily Caller News FoundationNo ratings yet
- Micro Insurance in IndiaDocument127 pagesMicro Insurance in IndiaVineet SukumarNo ratings yet
- Cloud - PenTest - AWS - and - Azure - by - Joas - 1640693784 2021-12-28 12 - 16 - 31Document1 pageCloud - PenTest - AWS - and - Azure - by - Joas - 1640693784 2021-12-28 12 - 16 - 31Marcio Serafim BorbaNo ratings yet
- Net PI Blog: Attacking Android Applications With DebuggersDocument28 pagesNet PI Blog: Attacking Android Applications With DebuggersTestuno TestunoNo ratings yet
- Whitepapr of EtherconnectDocument40 pagesWhitepapr of EtherconnectLiberty JoachimNo ratings yet
- S7 - BlockchainApplication Copy 2Document9 pagesS7 - BlockchainApplication Copy 2Lorenzo PenninoNo ratings yet
- Digital Currency Stocks Bonds: The Most Popular Cryptocurrency Terms and Phrases CryptocurrencyDocument75 pagesDigital Currency Stocks Bonds: The Most Popular Cryptocurrency Terms and Phrases CryptocurrencySAGIR MUSA SANINo ratings yet
- 4 Foundations of Security What Neil Daswani, Christoph KernDocument418 pages4 Foundations of Security What Neil Daswani, Christoph KernSmachew GedefawNo ratings yet
- A 4chan Approach For Trading & Investing in CryptocurrenciesDocument12 pagesA 4chan Approach For Trading & Investing in CryptocurrenciesJanaê PereiraNo ratings yet
- How To Build A Gaming PC 2012Document27 pagesHow To Build A Gaming PC 2012Dev AcharyaNo ratings yet
- 1 COBIT Removed MergedDocument86 pages1 COBIT Removed MergedGunjan ShivhareNo ratings yet
- Scsu PDFDocument18 pagesScsu PDFRushil PrajapatiNo ratings yet
- Blockchain Learning SyllabusDocument4 pagesBlockchain Learning SyllabusHimanshu TomarNo ratings yet
- Multi-Biometric Authentication Through Hybrid Cryptographic SystemDocument4 pagesMulti-Biometric Authentication Through Hybrid Cryptographic SystemiirNo ratings yet
- BEAM One PagerDocument2 pagesBEAM One PagerBeamPrivacy100% (1)
- PokeMoney Smart Contract Security ReportDocument25 pagesPokeMoney Smart Contract Security ReportaKNo ratings yet
- Trip Symposium and Exhibition 2018: Fourteenth IcaoDocument72 pagesTrip Symposium and Exhibition 2018: Fourteenth IcaoTalent BeaNo ratings yet
- Domain 2 - Governance and Management - MasterDocument86 pagesDomain 2 - Governance and Management - MasterRabab AlsaidalaniNo ratings yet
- Zero-Knowledge ProofDocument16 pagesZero-Knowledge ProoflkwriterNo ratings yet
- Program: What Is The Entrepreneurship and Small Business Certification (ESB) ?Document2 pagesProgram: What Is The Entrepreneurship and Small Business Certification (ESB) ?Yara KamarNo ratings yet
- Attacks Defence PDF 1662563695Document1 pageAttacks Defence PDF 1662563695Alexandre OSNo ratings yet
- NetSPI Scott Sutherland RedvsBlue v3.2 PDFDocument1 pageNetSPI Scott Sutherland RedvsBlue v3.2 PDFPatrick CloarecNo ratings yet
- SD Blueprint MergedDocument160 pagesSD Blueprint MergedHrithik VemparalaNo ratings yet
- Switch PortDocument4 pagesSwitch PortPartha Pratim HazarikaNo ratings yet
- System Design BlueprintDocument1 pageSystem Design BlueprintSathiamoorthy DuraisamyNo ratings yet
- Fleury - MITRE KILL CHAINDocument1 pageFleury - MITRE KILL CHAINVinicius CaldiniNo ratings yet
- Learn Cyber SecurityDocument1 pageLearn Cyber SecurityPHẠM MINH TRÍNo ratings yet
- 03 SMTP DNS and HTTPS AnalyticsDocument40 pages03 SMTP DNS and HTTPS AnalyticsSaw GyiNo ratings yet
- Du CVMDocument6 pagesDu CVM1977amNo ratings yet
- Red Team Ops - Mind MapDocument1 pageRed Team Ops - Mind Map0xt3stNo ratings yet
- 3 Months E-Learning 3 Months InternshipDocument17 pages3 Months E-Learning 3 Months InternshipSRS ENTERPRISE LIMITEDNo ratings yet
- Iclass Student Enrollment Form-Jun23Document1 pageIclass Student Enrollment Form-Jun23Amine RachedNo ratings yet
- Talos InsightDocument155 pagesTalos InsightCyril MbedeNo ratings yet
- Embedded Event Manager Not Just ForDocument1 pageEmbedded Event Manager Not Just ForPA2 ksplNo ratings yet
- A Forensic Analysis of APT Lateral Movement in Windows EnvironmentDocument40 pagesA Forensic Analysis of APT Lateral Movement in Windows EnvironmentSai PradeepNo ratings yet
- SecOps Made Simple With AI Automation and SAASDocument20 pagesSecOps Made Simple With AI Automation and SAAStola02000No ratings yet
- Stakeholders Register: Wilmont's Drone Project 001 Wilmont's Pharmacy Diogo Pimenta Concept 01 30/04/2020Document3 pagesStakeholders Register: Wilmont's Drone Project 001 Wilmont's Pharmacy Diogo Pimenta Concept 01 30/04/2020freddy ramdinNo ratings yet
- Exchange Online Protection OverviewDocument32 pagesExchange Online Protection OverviewAlber MunirNo ratings yet
- Internet and Computer TermsDocument590 pagesInternet and Computer TermsHeba SirryNo ratings yet
- Wireless Penetration Testing FlowchartDocument1 pageWireless Penetration Testing FlowchartChris MuncyNo ratings yet
- PictureDocument2 pagesPicturePooja JainNo ratings yet
- Iclass Student Enrollment Form - CMDocument1 pageIclass Student Enrollment Form - CMBoris IvanovNo ratings yet
- A Forensic Analysis of Apt Lateral Movement in Windows EnvironmentDocument48 pagesA Forensic Analysis of Apt Lateral Movement in Windows EnvironmentCleber MacielNo ratings yet
- RF Optimization Guide V3Document13 pagesRF Optimization Guide V3Stone OkoNo ratings yet
- Stuck Thread 253 Middleware Magic PDFDocument10 pagesStuck Thread 253 Middleware Magic PDFvenzaltiusNo ratings yet
- Cisco's Talos Intelligence Group Blog - Player 3 Has Entered The Game - Say Hello To 'WannaCry'Document19 pagesCisco's Talos Intelligence Group Blog - Player 3 Has Entered The Game - Say Hello To 'WannaCry'Hood171No ratings yet
- Osi Model: Presented By:-Karan MehtaDocument19 pagesOsi Model: Presented By:-Karan Mehtamrgodzilla00000000009No ratings yet
- Hacking Ético: Cacería de Vulnerabilidades: Owasp Latam Tour 2015Document41 pagesHacking Ético: Cacería de Vulnerabilidades: Owasp Latam Tour 2015Javier Mauricio GetialNo ratings yet
- Content: - Expiration ProcessingDocument8 pagesContent: - Expiration Processingapi-3756722No ratings yet
- Voice Over Internet Protocol (Voip) : - An IntroductionDocument17 pagesVoice Over Internet Protocol (Voip) : - An IntroductionengrasadzamanNo ratings yet
- PSAT PresentationDocument29 pagesPSAT Presentationmuhammad haritsNo ratings yet
- Cat RAM - Hardware Detail and Set Up ProcessDocument35 pagesCat RAM - Hardware Detail and Set Up ProcessDjebali Mourad100% (1)
- Cisco Firepower and Radware Technical OverviewDocument14 pagesCisco Firepower and Radware Technical OverviewAlfredo Claros100% (1)
- 7720 C IpoccDocument25 pages7720 C IpoccDilene SánchezNo ratings yet
- Og FortireconDocument2 pagesOg FortireconErick BarriosNo ratings yet
- Security Analytics Architecture For APT: Dale Long, Sr. Technology Consultant, RSA SecurityDocument33 pagesSecurity Analytics Architecture For APT: Dale Long, Sr. Technology Consultant, RSA SecurityDodo winyNo ratings yet
- It Policy Socialization 2008Document40 pagesIt Policy Socialization 2008FitaRosmaniaNo ratings yet
- MLNX-OS Release NotesDocument36 pagesMLNX-OS Release Notesrainbow007No ratings yet
- Blackberry Uem: Installation and UpgradeDocument54 pagesBlackberry Uem: Installation and UpgradesshreddyNo ratings yet
- Windows Server 2012 R2 NIC Teaming (LBFO) Deployment and ManagementDocument56 pagesWindows Server 2012 R2 NIC Teaming (LBFO) Deployment and ManagementBon Jun A Cuevas100% (1)
- SIP With EtherealDocument12 pagesSIP With EtherealSujit DwiNo ratings yet
- CS2302 Computer Networks Anna University Engineering Question Bank 4 UDocument48 pagesCS2302 Computer Networks Anna University Engineering Question Bank 4 UkuttymythuNo ratings yet
- Simple-Ostinato: Release 0.0.1Document41 pagesSimple-Ostinato: Release 0.0.1Sorabh MohindruNo ratings yet
- Adasd 213123 HasdDocument14 pagesAdasd 213123 HasdAnonymous (Akcent Hoong)No ratings yet
- Passleader 400-101 Study GuideDocument8 pagesPassleader 400-101 Study Guidealia davin0% (1)
- Module 9: Qos Concepts: Instructor MaterialsDocument58 pagesModule 9: Qos Concepts: Instructor Materialspatrick gucakeNo ratings yet
- Banglalink Internet Manua Setup GuideDocument25 pagesBanglalink Internet Manua Setup GuideBoktiar HossainNo ratings yet
- Change LogDocument23 pagesChange LogKatja MILENKOVICNo ratings yet
- PAN-OS Release NotesDocument116 pagesPAN-OS Release NotesT ANo ratings yet
- HUAWEI AR120 AR150 AR160 and AR200 Series Enterprise Routers Datasheet PDFDocument24 pagesHUAWEI AR120 AR150 AR160 and AR200 Series Enterprise Routers Datasheet PDFcdsenthilNo ratings yet
- HTTP OverviewDocument14 pagesHTTP OverviewMac GarrNo ratings yet
- Pa 3200 SeriesDocument4 pagesPa 3200 SeriesBatkhishig Tumen-OidovNo ratings yet
- Setting Up 802.1x AuthentiactionDocument4 pagesSetting Up 802.1x AuthentiactionruletriplexNo ratings yet
- Using Ostinato V1-0Document16 pagesUsing Ostinato V1-0JOEL RAMIREZNo ratings yet
- DES-3028 28P 52 52P CLI v1.00Document250 pagesDES-3028 28P 52 52P CLI v1.00Regivaldo PereiraNo ratings yet
- Datasheet XC220 G3v 2.0Document3 pagesDatasheet XC220 G3v 2.0Daniel Perez OsorioNo ratings yet
- Voice Over IP (VoIP)Document54 pagesVoice Over IP (VoIP)Peter R. Egli100% (1)
- Electronic Switching Harshita Uptu NotesDocument2 pagesElectronic Switching Harshita Uptu NotesHarsh Vardhan100% (1)
- IP QoSDocument12 pagesIP QoSMichel HuizingNo ratings yet
- Cisco Ios Cheat Sheet - Router CommandsDocument2 pagesCisco Ios Cheat Sheet - Router CommandsCCNAResourcesNo ratings yet
- DNS and EmailDocument23 pagesDNS and EmailAbhishek kumar singh100% (1)
- MSTP Configuration PDFDocument106 pagesMSTP Configuration PDFRandy DookheranNo ratings yet
- UNV IPC2122SR3-PF40 (60) - C 2MP Mini Fixed Bullet Network Camera V2.71Document3 pagesUNV IPC2122SR3-PF40 (60) - C 2MP Mini Fixed Bullet Network Camera V2.71itachiNo ratings yet
- Experiment No. 7: 1.aim: Implementation of Bluetooth Network For Data Transfer From One Node To OtherDocument9 pagesExperiment No. 7: 1.aim: Implementation of Bluetooth Network For Data Transfer From One Node To OtherAnil kadamNo ratings yet
- Laporan Infrastruktur Sistem InformasiDocument25 pagesLaporan Infrastruktur Sistem InformasisaktirolNo ratings yet
- Internet Protocol Television (Iptv)Document17 pagesInternet Protocol Television (Iptv)openid_QrS6xpoINo ratings yet
- Force10 Networks' Traverse and Traverseedge Family of Multiservice Transport PlatformsDocument2 pagesForce10 Networks' Traverse and Traverseedge Family of Multiservice Transport PlatformsMichele BrunelliNo ratings yet