Professional Documents
Culture Documents
Fake Base Station Identification and Detection (5G RAN6.1 - Draft A)
Uploaded by
VVLOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Fake Base Station Identification and Detection (5G RAN6.1 - Draft A)
Uploaded by
VVLCopyright:
Available Formats
5G RAN
Fake Base Station Identification
and Detection Feature Parameter
Description
Issue Draft A
Date 2021-12-30
HUAWEI TECHNOLOGIES CO., LTD.
Copyright © Huawei Technologies Co., Ltd. 2022. All rights reserved.
No part of this document may be reproduced or transmitted in any form or by any means without prior
written consent of Huawei Technologies Co., Ltd.
Trademarks and Permissions
and other Huawei trademarks are trademarks of Huawei Technologies Co., Ltd.
All other trademarks and trade names mentioned in this document are the property of their respective
holders.
Notice
The purchased products, services and features are stipulated by the contract made between Huawei and
the customer. All or part of the products, services and features described in this document may not be
within the purchase scope or the usage scope. Unless otherwise specified in the contract, all statements,
information, and recommendations in this document are provided "AS IS" without warranties, guarantees
or representations of any kind, either express or implied.
The information in this document is subject to change without notice. Every effort has been made in the
preparation of this document to ensure accuracy of the contents, but all statements, information, and
recommendations in this document do not constitute a warranty of any kind, express or implied.
Huawei Technologies Co., Ltd.
Address: Huawei Industrial Base
Bantian, Longgang
Shenzhen 518129
People's Republic of China
Website: https://www.huawei.com
Email: support@huawei.com
Issue Draft A Copyright © Huawei Technologies Co., Ltd. i
(2021-12-30)
5G RAN
Fake Base Station Identification and Detection
Feature Parameter Description Contents
Contents
1 Change History.........................................................................................................................1
1.1 5G RAN6.1 Draft A (2021-12-30)...................................................................................................................................... 1
2 About This Document.............................................................................................................3
2.1 General Statements................................................................................................................................................................ 3
2.2 Differences Between NR FDD and NR TDD................................................................................................................... 4
2.3 Differences Between NSA and SA..................................................................................................................................... 4
2.4 Differences Between High Frequency Bands and Low Frequency Bands............................................................ 4
3 Overview....................................................................................................................................6
4 Fake Base Station Identification and Detection in SA Networking............................ 7
4.1 Principles.................................................................................................................................................................................... 7
4.1.1 Principles and Procedure of Fake Base Station Detection..................................................................................... 7
4.1.2 Fake Base Station Whitelist Management................................................................................................................11
4.1.3 Geographic Display of Fake Base Stations............................................................................................................... 11
4.1.4 Fake Base Station Detection Results...........................................................................................................................12
4.2 Network Analysis.................................................................................................................................................................. 12
4.2.1 Benefits................................................................................................................................................................................. 12
4.2.2 Impacts.................................................................................................................................................................................. 12
4.3 Requirements......................................................................................................................................................................... 13
4.3.1 Licenses................................................................................................................................................................................. 13
4.3.2 Software................................................................................................................................................................................13
4.3.3 Hardware.............................................................................................................................................................................. 13
4.3.4 Others.................................................................................................................................................................................... 14
4.4 Operation and Maintenance............................................................................................................................................. 14
4.4.1 Data Configuration........................................................................................................................................................... 14
4.4.1.1 Data Preparation............................................................................................................................................................ 14
4.4.1.2 Using MML Commands............................................................................................................................................... 15
4.4.1.3 Using the MAE-Deployment...................................................................................................................................... 15
4.4.2 Activation Verification..................................................................................................................................................... 15
4.4.3 Network Monitoring......................................................................................................................................................... 15
5 Fake Base Station Identification and Detection in NSA Networking....................... 16
6 Glossary................................................................................................................................... 18
Issue Draft A Copyright © Huawei Technologies Co., Ltd. ii
(2021-12-30)
5G RAN
Fake Base Station Identification and Detection
Feature Parameter Description Contents
7 Reference Documents...........................................................................................................19
Issue Draft A Copyright © Huawei Technologies Co., Ltd. iii
(2021-12-30)
5G RAN
Fake Base Station Identification and Detection
Feature Parameter Description 1 Change History
1 Change History
This chapter describes changes not included in the "Parameters", "Counters",
"Glossary", and "Reference Documents" chapters. These changes include:
● Technical changes
Changes in functions and their corresponding parameters
● Editorial changes
Improvements or revisions to the documentation
1.1 5G RAN6.1 Draft A (2021-12-30)
This issue introduces the following changes to 5G RAN5.1 01 (2021-03-05).
Issue Draft A Copyright © Huawei Technologies Co., Ltd. 1
(2021-12-30)
5G RAN
Fake Base Station Identification and Detection
Feature Parameter Description 1 Change History
Technical Changes
Change Parameter RAT Base Station
Description Change Model
Enhanced the None FDD 3900 and 5900
fake base station Low-frequency series base
identification and TDD stations
detection function DBS3900
and added High-frequency
TDD LampSite and
locating and DBS5900
impact LampSite
quantification
functions.
Specifically,
● Comprehensive
spoofed fake
base station
detection
● Fake base
station
locating
● Quantitative
data added to
fake base
station
detection
reports.
For details, see
4.1 Principles.
Editorial Changes
Revised descriptions.
Issue Draft A Copyright © Huawei Technologies Co., Ltd. 2
(2021-12-30)
5G RAN
Fake Base Station Identification and Detection
Feature Parameter Description 2 About This Document
2 About This Document
2.1 General Statements
Purpose
Feature Parameter Description documents are intended to acquaint readers with:
● The technical principles of features and their related parameters
● The scenarios where these features are used, the benefits they provide, and
the impact they have on networks and functions
● Requirements of the operating environment that must be met before feature
activation
● Parameter configuration required for feature activation, verification of feature
activation, and monitoring of feature performance
NOTE
This document only provides guidance for feature activation. Feature deployment and
feature gains depend on the specifics of the network scenario where the feature is
deployed. To achieve optimal gains, contact Huawei professional service engineers.
Software Interfaces
Any parameters, alarms, counters, or managed objects (MOs) described in Feature
Parameter Description documents apply only to the corresponding software
release. For future software releases, refer to the corresponding updated product
documentation.
Issue Draft A Copyright © Huawei Technologies Co., Ltd. 3
(2021-12-30)
5G RAN
Fake Base Station Identification and Detection
Feature Parameter Description 2 About This Document
2.2 Differences Between NR FDD and NR TDD
Function Name Difference Chapter/Section
Fake base station None 4 Fake Base
identification and Station
detection in SA Identification and
networking Detection in SA
Networking
Fake base station None 5 Fake Base
identification and Station
detection in NSA Identification and
networking Detection in NSA
Networking
2.3 Differences Between NSA and SA
Function Name Difference Chapter/Section
Fake base station Supported only in SA networking 4 Fake Base
identification and Station
detection in SA Identification and
networking Detection in SA
Networking
Fake base station Supported only in NSA networking 5 Fake Base
identification and Station
detection in NSA Identification and
networking Detection in NSA
Networking
2.4 Differences Between High Frequency Bands and
Low Frequency Bands
This document refers to frequency bands belonging to FR1 (410–7125 MHz) as
low frequency bands, and those belonging to FR2 (24250–52600 MHz) as high
frequency bands. For details about FR1 and FR2, see section 5.1 "General" in 3GPP
TS 38.104 V15.5.0.
Issue Draft A Copyright © Huawei Technologies Co., Ltd. 4
(2021-12-30)
5G RAN
Fake Base Station Identification and Detection
Feature Parameter Description 2 About This Document
Function Name Difference Chapter/Section
Fake base station None 4 Fake Base
identification and Station
detection in SA Identification and
networking Detection in SA
Networking
Fake base station None 5 Fake Base
identification and Station
detection in NSA Identification and
networking Detection in NSA
Networking
Issue Draft A Copyright © Huawei Technologies Co., Ltd. 5
(2021-12-30)
5G RAN
Fake Base Station Identification and Detection
Feature Parameter Description 3 Overview
3 Overview
Attackers use simple wireless devices and dedicated open-source software to
disguise these devices as base stations on the live network. These devices are
called fake base stations. A fake base station attracts surrounding UEs to camp on
its served cells through strong signals. It launches spoofing attacks on UEs and
interferes with normal communications between the network and UEs, affecting
network performance and causing exceptions, such as handover failures and
abnormal service drops. In addition, this may disconnect the UEs from operators'
networks and attach these disconnected UEs to fake base stations.
When a UE accesses an operator's network, its international mobile subscriber
identity (IMSI) is transmitted in plaintext and this information will be ciphered
only after the UE passes access authentication and an air interface security
context is established. This vulnerability allows an attacker to eavesdrop on the
IMSI of a UE over the air interface by using a fake base station, leading to privacy
leakage.
In SA or NSA networking, UEs whose SIM cards are not changed are exposed to
this vulnerability. This version supports the identification and detection of fake
base stations in SA networking and NSA networking.
Issue Draft A Copyright © Huawei Technologies Co., Ltd. 6
(2021-12-30)
5G RAN
Fake Base Station Identification and Detection 4 Fake Base Station Identification and Detection in
Feature Parameter Description SA Networking
4 Fake Base Station Identification and
Detection in SA Networking
4.1 Principles
4.1.1 Principles and Procedure of Fake Base Station Detection
An attacker can use a fake base station to attack a UE only after the UE is
attached to a cell served by the fake base station. Then, the attacker can initiate
attacks such as message spoofing, tampering, and eavesdropping on the UE. A
fake base station absorbs a UE, which interferes with normal communication
between the UE and network, resulting in handover failures, interference-induced
service drops, and cell reselection.
Principles of Fake Base Station Identification and Detection
The fake base station identification and detection function collects and analyzes
statistics based on handover failure (HO) events and cell global identifier (CGI)
measurement events reported by UEs, and identifies abnormal cells that are not
within the network planning scope, as shown in Figure 4-1.
Issue Draft A Copyright © Huawei Technologies Co., Ltd. 7
(2021-12-30)
5G RAN
Fake Base Station Identification and Detection 4 Fake Base Station Identification and Detection in
Feature Parameter Description SA Networking
Figure 4-1 Principles of fake base station identification and detection
The fake base station identification and detection function performs:
● Handover event analysis, by collecting statistics on inter-cell handover
exceptions to detect abnormal neighboring cells.
● ANR analysis, by comparing neighboring cell parameters (including PCIs, CGIs,
TACs, and frequencies) in CGI measurement reports (MRs) with NE
configuration and network engineering parameters to identify abnormal cells
that are not within the network planning scope. PCI, CGI, and TAC stand for
physical cell identifier, cell global identifier, and tracking area code,
respectively.
● Additional analysis for fake base stations with spoofed base station
parameters on the live network, to determine that a base station is a fake
base station if:
– The TAC of the target neighboring cell is different from that of the
serving cell.
– The inter-site distance meets the requirements illustrated in Figure 4-2.
Issue Draft A Copyright © Huawei Technologies Co., Ltd. 8
(2021-12-30)
5G RAN
Fake Base Station Identification and Detection 4 Fake Base Station Identification and Detection in
Feature Parameter Description SA Networking
Figure 4-2 Requirements for the inter-site distance of fake base stations
Procedure of Fake Base Station Identification and Detection
Figure 4-3 illustrates the process of fake base station identification and detection.
Issue Draft A Copyright © Huawei Technologies Co., Ltd. 9
(2021-12-30)
5G RAN
Fake Base Station Identification and Detection 4 Fake Base Station Identification and Detection in
Feature Parameter Description SA Networking
Figure 4-3 Function process
1. On the MAE-Evaluation, an operator subscribes to related NE information.
2. The operator imports the complete network engineering parameters to the
MAE-Evaluation.
3. On the MAE-Evaluation, the operator specifies the target region for fake base
station identification and detection.
4. On the MAE-Evaluation, the operator checks whether ANR-related functions
are enabled in the target region. If the ANR-related functions are disabled, the
operator is advised to enable them first. Otherwise, the accuracy of fake base
station identification and detection results will be affected. For details about
the ANR-related functions, see Prerequisite Functions.
5. On the MAE-Evaluation, the operator manages the fake base station whitelist.
The operator can add known fake base stations that do not need to be
displayed in the results to the whitelist. For details, see 4.1.2 Fake Base
Station Whitelist Management.
6. On the MAE-Evaluation, the operator views the fake base station
identification and detection results. The MAE-Evaluation allows queries on
hourly and daily results. The result output includes the following information:
Issue Draft A Copyright © Huawei Technologies Co., Ltd. 10
(2021-12-30)
5G RAN
Fake Base Station Identification and Detection 4 Fake Base Station Identification and Detection in
Feature Parameter Description SA Networking
– Fake base station information list
– Geographic display of fake base stations (For details, see 4.1.3
Geographic Display of Fake Base Stations.)
– Fake base station detection results (For details, see 4.1.4 Fake Base
Station Detection Results.)
7. The operator checks the fake base stations on the live network.
NOTE
For details about how to handle fake base station detection results and how to use
the MAE, see MAE-Evaluation Operation and Maintenance in iMaster MAE Product
Documentation (EulerOS, TaiShan).
Application Constraints of Fake Base Station Identification and Detection
Application constraints of fake base station identification and detection are as
follows:
● This function can identify intra-frequency stationary fake base stations.
● This function can identify inter-frequency stationary fake base stations.
● This function can identify cells with abnormal PCIs, CGIs, or TACs served by
fake base stations.
● Cells with spoofed PCIs, CGIs, and TACs served by fake base stations can be
identified through remote rather than local detection of comprehensive
spoofed fake base stations.
● For network border areas, such as areas on the cross-vendor, cross-city, and
cross-management-domain network borders, it is recommended that
operators import network engineering parameters of neighboring networks to
reduce false identification of fake base stations.
● A base station that is disconnected from the OSS and has incorrect
configurations may be incorrectly identified as a fake base station if its service
interaction with its surrounding base stations is abnormal.
● The fake base station identification and detection function allows queries on
hourly and daily results. Therefore, fake base stations can be detected by this
function at least one hour after they appear.
4.1.2 Fake Base Station Whitelist Management
Operators can add known fake base stations that have been processed to the
whitelist. In the query results of fake base station detection, whitelisted fake base
stations are filtered out and not displayed. The fake base station whitelist can be
imported, exported, or deleted.
NOTE
For details, see MAE-Evaluation Operation and Maintenance in iMaster MAE Product
Documentation (EulerOS, TaiShan).
4.1.3 Geographic Display of Fake Base Stations
The geographic display of fake base stations involves:
● The grid locations of UEs affected by fake base stations, which reflect the
coverage of fake base stations.
Issue Draft A Copyright © Huawei Technologies Co., Ltd. 11
(2021-12-30)
5G RAN
Fake Base Station Identification and Detection 4 Fake Base Station Identification and Detection in
Feature Parameter Description SA Networking
● Fake base station locating results, which indicate the locations of fake base
stations that are calculated based on UE-reported measurement results
related to fake base stations.
– Prerequisites for viewing fake base station locating results: A fake base
station locating task has been started for a specified region on the MAE-
Evaluation.
– Dependency of fake-base station locating: Intra- and inter-frequency MR
sampling has been enabled on NEs.
– Impacts of fake base station locating: As inter-frequency MR sampling
needs to be enabled on the NE side, the service traffic volume may
decrease by approximately 6.5% in heavy-load scenarios.
– Errors of fake base station locating: There is a 70% probability that the
locating error ranges from 100 m to 200 m, only for stationary fake base
stations in dense urban areas.
– Restrictions on fake base station locating: This function applies only in
dense urban areas with an inter-site distance of approximately 500 m.
NOTE
For details, see MAE-Evaluation Operation and Maintenance in iMaster MAE Product
Documentation (EulerOS, TaiShan).
4.1.4 Fake Base Station Detection Results
The following fake base station detection results can be exported:
● Fake base station information list
● Statistics on the impacts of fake base stations on the live network, including
the number of affected cells, number of handover failures, and number of
abnormal service drops
● Information about cells affected by each fake base station, including the
impacts on handover-related Indicators
NOTE
For details, see MAE-Evaluation Operation and Maintenance in iMaster MAE Product
Documentation (EulerOS, TaiShan).
4.2 Network Analysis
4.2.1 Benefits
None
4.2.2 Impacts
Network Impacts
When fake base station locating is enabled, inter-frequency MR subscription tasks
must be delivered to NEs in the selected area. When NEs are heavily loaded,
subscribing to inter-frequency MRs may decrease the service traffic volume by
approximately 6.5%.
Issue Draft A Copyright © Huawei Technologies Co., Ltd. 12
(2021-12-30)
5G RAN
Fake Base Station Identification and Detection 4 Fake Base Station Identification and Detection in
Feature Parameter Description SA Networking
Function Impacts
None
4.3 Requirements
4.3.1 Licenses
To enable fake base station detection on the MAE-Evaluation, the license for fake
base station detection must be activated. For details, see MAE-Evaluation
Operation and Maintenance in iMaster MAE Product Documentation (EulerOS,
TaiShan).
4.3.2 Software
Before activating this function, ensure that its prerequisite functions have been
activated and mutually exclusive functions have been deactivated. For detailed
operations, see the relevant feature documents.
Prerequisite Functions
RAT Function Name Function Switch Reference
FDD Intra-RAT ANR NR_NR_ANR_SW option of ANR
Low- the
frequency NRCellAlgoSwitch.AnrSwitch
TDD parameter
High-
frequency
TDD
FDD PCI collision PCI_COLLISION_DETECT_SW ANR
Low- detection option of the
frequency NRCellAlgoSwitch.AnrSwitch
TDD parameter
High-
frequency
TDD
Mutually Exclusive Functions
None
4.3.3 Hardware
Base Station Models
3900 and 5900 series base stations. 3900 series base stations must be configured
with the BBU3910.
Issue Draft A Copyright © Huawei Technologies Co., Ltd. 13
(2021-12-30)
5G RAN
Fake Base Station Identification and Detection 4 Fake Base Station Identification and Detection in
Feature Parameter Description SA Networking
DBS3900 LampSite and DBS5900 LampSite. DBS3900 LampSite must be
configured with the BBU3910.
Boards
All NR-capable main control boards and baseband processing units support this
function. For details, see the BBU technical specifications in 3900 & 5900 Series
Base Station Product Documentation.
RF Modules
All NR-capable RF modules support this function. For details, see the technical
specifications of RF modules in 3900 & 5900 Series Base Station Product
Documentation.
4.3.4 Others
None
4.4 Operation and Maintenance
Operation and maintenance of this function is performed on the MAE.
4.4.1 Data Configuration
4.4.1.1 Data Preparation
After logging in to the MAE-Client, operators can perform the following three
steps to enable fake base station identification and detection in SA networking:
1. Create a customized analysis region for fake base station identification and
detection in SA networking. For details, see section "Managing Customized
Regions" by choosing "Operation and Maintenance" > "MAE-Evaluation
Operation and Maintenance" > "Topic" in MAE Product Documentation
(EulerOS, TaiShan).
2. Check whether the prerequisite functions of fake base station identification
and detection in SA networking are enabled for cells in the created analysis
region. For details about the prerequisite functions, see Prerequisite
Functions.
If the prerequisite functions are disabled, it is recommended that the
prerequisite functions be enabled before the fake base station identification
and detection in SA networking is enabled. Otherwise, the accuracy of the
detection results will be affected.
3. Enable the fake base station identification and detection in SA networking for
the created analysis region. For details, see "How Do I Turn on the Fake BTS
Detection Switch?" by choosing "Operation and Maintenance" > "MAE-
Evaluation Operation and Maintenance"> "Topic" > "Coverage Report" in MAE
Product Documentation (EulerOS, TaiShan).
Issue Draft A Copyright © Huawei Technologies Co., Ltd. 14
(2021-12-30)
5G RAN
Fake Base Station Identification and Detection 4 Fake Base Station Identification and Detection in
Feature Parameter Description SA Networking
4.4.1.2 Using MML Commands
None
4.4.1.3 Using the MAE-Deployment
For detailed operations, see Feature Configuration Using the MAE-Deployment.
4.4.2 Activation Verification
After this function is enabled, check whether this function has taken effect by
following the instructions provided in "How Do I Turn on the Fake BTS Detection
Switch?" by choosing "Operation and Maintenance" > "MAE-Evaluation Operation
and Maintenance"> "Topic" > "Coverage Report" in MAE Product Documentation
(EulerOS, TaiShan).
4.4.3 Network Monitoring
None
Issue Draft A Copyright © Huawei Technologies Co., Ltd. 15
(2021-12-30)
5G RAN
Fake Base Station Identification and Detection 5 Fake Base Station Identification and Detection in
Feature Parameter Description NSA Networking
5 Fake Base Station Identification and
Detection in NSA Networking
Fake base station identification and detection in NSA networking is implemented
on the MAE-Evaluation of the OSS, as shown in Figure 5-1. The network areas for
fake base station identification and detection can be selected as required. Base
stations collect data such as NE configuration data, abnormal events, and
measurement reports, and report them to the MAE-Evaluation. The MAE-
Evaluation analyzes the reported data to determine whether fake base stations
perform IMSI capture attacks over the air interface and generates information
about possible fake base stations in the area.
Issue Draft A Copyright © Huawei Technologies Co., Ltd. 16
(2021-12-30)
5G RAN
Fake Base Station Identification and Detection 5 Fake Base Station Identification and Detection in
Feature Parameter Description NSA Networking
Figure 5-1 Fake base station identification and detection in NSA networking
In NSA networking, IMSI-related access messages over the air interface are
processed or forwarded by eNodeBs, but not gNodeBs. Signal interference and
simulation in fake base station attacks are also targeted at eNodeBs. Therefore,
the eNodeBs are the real victims. In fake base station identification and detection
in NSA networking, eNodeBs collect and report data to the MAE-Evaluation. For
details about related requirements and operations, see Fake Base Station
Identification and Detection in eRAN Feature Documentation.
Issue Draft A Copyright © Huawei Technologies Co., Ltd. 17
(2021-12-30)
5G RAN
Fake Base Station Identification and Detection
Feature Parameter Description 6 Glossary
6 Glossary
For the acronyms, abbreviations, terms, and definitions, see Glossary.
Issue Draft A Copyright © Huawei Technologies Co., Ltd. 18
(2021-12-30)
5G RAN
Fake Base Station Identification and Detection
Feature Parameter Description 7 Reference Documents
7 Reference Documents
● 3GPP TS 38.104: "NR; Base Station (BS) radio transmission and reception"
● ANR
● MAE-Evaluation Operation and Maintenance in MAE Product Documentation
(EulerOS, TaiShan)
● Fake Base Station Identification and Detection in eRAN Feature
Documentation
● "Technical Specifications" in 3900 & 5900 Series Base Station Product
Documentation
Issue Draft A Copyright © Huawei Technologies Co., Ltd. 19
(2021-12-30)
You might also like
- Video Accelerator (RAN19.0 - Draft A)Document46 pagesVideo Accelerator (RAN19.0 - Draft A)Abdel SbeitiNo ratings yet
- q2 Long Quiz 002 EntreDocument8 pagesq2 Long Quiz 002 EntreMonn Justine Sabido0% (1)
- eRAN15.1 Overview: Huawei Technologies Co., LTDDocument17 pageseRAN15.1 Overview: Huawei Technologies Co., LTDJuan Ulises CapellanNo ratings yet
- Channel State Management (ERAN16.1 - 01)Document70 pagesChannel State Management (ERAN16.1 - 01)BorchikNo ratings yet
- Astm A 478 - 97Document2 pagesAstm A 478 - 97neno2405No ratings yet
- Wholesale (TDD) (eRAN15.1 - 01) PDFDocument63 pagesWholesale (TDD) (eRAN15.1 - 01) PDFFaizal JamaludeenNo ratings yet
- DL CoMP (eRAN12.1 - 02)Document57 pagesDL CoMP (eRAN12.1 - 02)CosminDNo ratings yet
- Manual MIB 303S-13/33Document58 pagesManual MIB 303S-13/33Daniel Machado100% (1)
- BP Azspu Driver Fatigue & Tiredness Management ProcedureDocument11 pagesBP Azspu Driver Fatigue & Tiredness Management ProcedureEl Khan100% (1)
- Compact Bandwidth (FDD) (eRAN13.1 - 05)Document122 pagesCompact Bandwidth (FDD) (eRAN13.1 - 05)Alina Ali Malik100% (3)
- HRM OmantelDocument8 pagesHRM OmantelSonia Braham100% (1)
- LTE - Control Channel IRC - Feature LOFD-001094 - DraftDocument10 pagesLTE - Control Channel IRC - Feature LOFD-001094 - Draftbrahiti3100% (1)
- Huawei SingleRAN Hardware Roadmap (2016Q4)Document44 pagesHuawei SingleRAN Hardware Roadmap (2016Q4)MiradoniainaRakotoarimananaNo ratings yet
- Carpio V ValmonteDocument2 pagesCarpio V ValmonteErvin John Reyes100% (2)
- 5G RAN Feature DocumentationDocument39 pages5G RAN Feature DocumentationMauro SpiriNo ratings yet
- Lampsite: Huawei Indoor MBB SolutionDocument19 pagesLampsite: Huawei Indoor MBB SolutionUwz MejahNo ratings yet
- Training Course - 5G RAN3.0 Intra-Band CADocument20 pagesTraining Course - 5G RAN3.0 Intra-Band CAVVLNo ratings yet
- Training Course - 5G RAN3.0 Wireless Network Planning Main SlidesDocument49 pagesTraining Course - 5G RAN3.0 Wireless Network Planning Main SlidesVVLNo ratings yet
- LTE FDD and NR Spectrum Sharing (SRAN18.1 - Draft A)Document228 pagesLTE FDD and NR Spectrum Sharing (SRAN18.1 - Draft A)VVLNo ratings yet
- LTE FDD and NR Spectrum Sharing (SRAN18.1 - Draft A)Document228 pagesLTE FDD and NR Spectrum Sharing (SRAN18.1 - Draft A)VVLNo ratings yet
- Training Course - SRAN16.0 Mobility ManagementDocument24 pagesTraining Course - SRAN16.0 Mobility ManagementVVLNo ratings yet
- Huawei 434789548 Massive MIMO TDD ERAN15 1 Draft A PDFDocument215 pagesHuawei 434789548 Massive MIMO TDD ERAN15 1 Draft A PDFALEXANDRE JOSE FIGUEIREDO LOUREIRONo ratings yet
- Training Course - 5G RAN3.0 Hyper CellDocument19 pagesTraining Course - 5G RAN3.0 Hyper CellVVLNo ratings yet
- Uplink Interference Cancellation (ERAN12.1 - 06)Document42 pagesUplink Interference Cancellation (ERAN12.1 - 06)waelq2003No ratings yet
- Northbound Management Feature Description (SRAN15.1)Document36 pagesNorthbound Management Feature Description (SRAN15.1)klajdiNo ratings yet
- VoLTE and ViLTE: Voice and Conversational Video Services over the 4G Mobile NetworkFrom EverandVoLTE and ViLTE: Voice and Conversational Video Services over the 4G Mobile NetworkNo ratings yet
- LTE and NR Power Sharing (SRAN18.1 - Draft A)Document70 pagesLTE and NR Power Sharing (SRAN18.1 - Draft A)VVLNo ratings yet
- Cmas (5G Ran6.1 - 01)Document31 pagesCmas (5G Ran6.1 - 01)VVL1959No ratings yet
- Macsec (Sran18.1 Draft A)Document18 pagesMacsec (Sran18.1 Draft A)VVLNo ratings yet
- Training Course - 5G RAN3.0 Mobility Management Feature Introduction v1.3Document40 pagesTraining Course - 5G RAN3.0 Mobility Management Feature Introduction v1.3VVLNo ratings yet
- IP Active Performance Measurement (SRAN18.1 - Draft A)Document59 pagesIP Active Performance Measurement (SRAN18.1 - Draft A)VVLNo ratings yet
- Huawei IManager SONMaster SolutionDocument26 pagesHuawei IManager SONMaster SolutionUsman100% (5)
- DRX (5G Ran3.1 - 02)Document40 pagesDRX (5G Ran3.1 - 02)VVLNo ratings yet
- Configuration Management (SRAN16.1 01)Document22 pagesConfiguration Management (SRAN16.1 01)VVLNo ratings yet
- Feature Difference FDDVSTDD SAvsNSA FR1vsFR2 EngDocument21 pagesFeature Difference FDDVSTDD SAvsNSA FR1vsFR2 EngVVLNo ratings yet
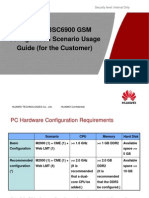
- Common BSC6900 GSM Configuration Scenario Usage Guide (For The Customer) - 20101124-CDocument59 pagesCommon BSC6900 GSM Configuration Scenario Usage Guide (For The Customer) - 20101124-CKathan ThakrarNo ratings yet
- Huawei 4G Eran 11.1Document510 pagesHuawei 4G Eran 11.1SWati100% (3)
- QoS Management ERAN3!0!02 PDFDocument72 pagesQoS Management ERAN3!0!02 PDFPedro_1976No ratings yet
- Comp (Low-Frequency TDD) (5g Ran3.1 - 02)Document37 pagesComp (Low-Frequency TDD) (5g Ran3.1 - 02)VVLNo ratings yet
- Lte V2Document117 pagesLte V2ajay_kangra100% (1)
- Mimo (FDD) (5g Ran6.1 - Draft A)Document54 pagesMimo (FDD) (5g Ran6.1 - Draft A)VVLNo ratings yet
- Mimo (FDD) (5g Ran6.1 - Draft A)Document54 pagesMimo (FDD) (5g Ran6.1 - Draft A)VVLNo ratings yet
- Throughput Issue Troubleshooting: Huawei Technologies Co., LTDDocument48 pagesThroughput Issue Troubleshooting: Huawei Technologies Co., LTDmajidjan100% (1)
- Huawei LTE CSFB Solution Main Slides V4.2Document31 pagesHuawei LTE CSFB Solution Main Slides V4.2Ejaz Ahmad100% (3)
- Fault Management (SRAN17.1 01)Document45 pagesFault Management (SRAN17.1 01)VVLNo ratings yet
- Massive Mimo Ahr (TDD) (5g Ran6.1 - Draft A)Document64 pagesMassive Mimo Ahr (TDD) (5g Ran6.1 - Draft A)VVLNo ratings yet
- Cell Combination (5G RAN6.1 - Draft A)Document67 pagesCell Combination (5G RAN6.1 - Draft A)VVLNo ratings yet
- 5G RAN6.1 Feature and Function Change SummaryDocument42 pages5G RAN6.1 Feature and Function Change SummaryVVL1959No ratings yet
- IPv4 Transmission (SRAN18.1 - Draft A)Document169 pagesIPv4 Transmission (SRAN18.1 - Draft A)VVLNo ratings yet
- Multi-Band Compatibility (5G RAN6.1 - Draft A)Document21 pagesMulti-Band Compatibility (5G RAN6.1 - Draft A)VVLNo ratings yet
- Training Course - 5G RAN3.0 QoS ManagementDocument20 pagesTraining Course - 5G RAN3.0 QoS ManagementVVLNo ratings yet
- Multi-Sector Evolution (5G RAN6.1 - Draft A)Document29 pagesMulti-Sector Evolution (5G RAN6.1 - Draft A)VVLNo ratings yet
- eRAN18.1 LTE FDD Massive MIMO Solution User GuideDocument105 pageseRAN18.1 LTE FDD Massive MIMO Solution User Guideturi313100% (1)
- 5G RAN2.0 Beam Management HuaweiDocument42 pages5G RAN2.0 Beam Management Huaweimahmoud100% (1)
- 1.2 Training Course - 5g Massive MimoDocument38 pages1.2 Training Course - 5g Massive Mimoمهدي مهديNo ratings yet
- Cell Outage Detection and Recovery (5G RAN6.1 - 02)Document27 pagesCell Outage Detection and Recovery (5G RAN6.1 - 02)VVL1959No ratings yet
- Training Course - 5G RAN3.0 Beam ManagementDocument34 pagesTraining Course - 5G RAN3.0 Beam ManagementVVLNo ratings yet
- Leadership Style SurveyDocument3 pagesLeadership Style SurveyJanelle BergNo ratings yet
- MDT Feature Parameter Description: Issue DateDocument28 pagesMDT Feature Parameter Description: Issue DatesostashkinNo ratings yet
- LTE Air InterfaceDocument60 pagesLTE Air InterfaceJoan Velasquez50% (2)
- Fma (Sran16.1 02)Document92 pagesFma (Sran16.1 02)Didier SepulvedaNo ratings yet
- Multi-RAT Coordinated Energy Saving (SRAN18.1 - Draft A)Document199 pagesMulti-RAT Coordinated Energy Saving (SRAN18.1 - Draft A)VVLNo ratings yet
- Parameter ReferenceDocument10,430 pagesParameter ReferenceCesarNo ratings yet
- Comp (5g Ran6.1 - Draft A)Document68 pagesComp (5g Ran6.1 - Draft A)VVLNo ratings yet
- LTE FDD and NR Uplink Spectrum Sharing (SRAN18.1 - Draft A)Document45 pagesLTE FDD and NR Uplink Spectrum Sharing (SRAN18.1 - Draft A)VVLNo ratings yet
- Hyper Cell (5G RAN3.1 - Draft A)Document25 pagesHyper Cell (5G RAN3.1 - Draft A)VVL1959100% (1)
- Anr (5G Ran2.1 - 01)Document39 pagesAnr (5G Ran2.1 - 01)waelq2003No ratings yet
- Cell Combination (5G RAN6.1 - 02)Document60 pagesCell Combination (5G RAN6.1 - 02)VVL1959No ratings yet
- CPRI Compression (5G RAN6.1 - Draft A)Document41 pagesCPRI Compression (5G RAN6.1 - Draft A)VVLNo ratings yet
- Multi-Operator Sharing (5G RAN6.1 - Draft A)Document202 pagesMulti-Operator Sharing (5G RAN6.1 - Draft A)VVLNo ratings yet
- Modulation Schemes (5G RAN6.1 - Draft A)Document36 pagesModulation Schemes (5G RAN6.1 - Draft A)VVLNo ratings yet
- Modulation Schemes (5G RAN6.1 - Draft A)Document36 pagesModulation Schemes (5G RAN6.1 - Draft A)VVLNo ratings yet
- LTE Spectrum Coordination (ERAN18.1 - Draft A)Document35 pagesLTE Spectrum Coordination (ERAN18.1 - Draft A)VVLNo ratings yet
- Mimo (TDD) (5g Ran6.1 - Draft A)Document95 pagesMimo (TDD) (5g Ran6.1 - Draft A)VVLNo ratings yet
- Training Document IManager U2000-CME V200R016 Site Deployment Guide (GUI)Document69 pagesTraining Document IManager U2000-CME V200R016 Site Deployment Guide (GUI)PhucNo ratings yet
- Multi-Frequency Convergence (5G RAN6.1 - Draft A)Document71 pagesMulti-Frequency Convergence (5G RAN6.1 - Draft A)VVLNo ratings yet
- MIMO (eRAN13.1 02)Document274 pagesMIMO (eRAN13.1 02)Shashank PrajapatiNo ratings yet
- Flow Control (5G RAN6.1 - Draft A)Document34 pagesFlow Control (5G RAN6.1 - Draft A)VVLNo ratings yet
- Finman General Assurance Corporation Vs - The Honorable Court of AppealsDocument2 pagesFinman General Assurance Corporation Vs - The Honorable Court of AppealsNorie De los ReyesNo ratings yet
- FMA (SRAN16.1 - Draft A)Document91 pagesFMA (SRAN16.1 - Draft A)VVL1959No ratings yet
- Mobility Management (5G RAN6.1 - Draft A)Document244 pagesMobility Management (5G RAN6.1 - Draft A)VVL100% (1)
- Access Class Control (eRAN15.1 - 01) PDFDocument57 pagesAccess Class Control (eRAN15.1 - 01) PDFwaelq2003No ratings yet
- Mobility Load Balancing (5G RAN6.1 - Draft A)Document132 pagesMobility Load Balancing (5G RAN6.1 - Draft A)VVLNo ratings yet
- Monitoring Management (SRAN18.1 - Draft A)Document190 pagesMonitoring Management (SRAN18.1 - Draft A)VVLNo ratings yet
- MmWave Beam Management (High-Frequency TDD) (5G RAN6.1 - Draft A)Document44 pagesMmWave Beam Management (High-Frequency TDD) (5G RAN6.1 - Draft A)VVLNo ratings yet
- Ipsec (Sran18.1 Draft A)Document187 pagesIpsec (Sran18.1 Draft A)VVLNo ratings yet
- License Control Item Lists (5G RAN6.1 - Draft A)Document33 pagesLicense Control Item Lists (5G RAN6.1 - Draft A)VVLNo ratings yet
- Backhauling / Fronthauling for Future Wireless SystemsFrom EverandBackhauling / Fronthauling for Future Wireless SystemsKazi Mohammed Saidul HuqNo ratings yet
- Interference Avoidance (5G RAN6.1 - Draft A)Document57 pagesInterference Avoidance (5G RAN6.1 - Draft A)VVL100% (1)
- Biotechnology WebquestDocument2 pagesBiotechnology Webquestapi-353567032No ratings yet
- Parameter HuaweiDocument21 pagesParameter HuaweiFouad TehariNo ratings yet
- RSVD para List NRDocument1,346 pagesRSVD para List NRJarbas Borges100% (1)
- Training Document - Imanager M2000-CME V200R011 Introduction To The Working Principles (Basics) - 20111106-B-1.1Document41 pagesTraining Document - Imanager M2000-CME V200R011 Introduction To The Working Principles (Basics) - 20111106-B-1.1samba51130% (1)
- Hyper Cell (5G RAN6.1 - Draft A)Document46 pagesHyper Cell (5G RAN6.1 - Draft A)VVL100% (1)
- IPv6 Transmission (SRAN18.1 - Draft A)Document97 pagesIPv6 Transmission (SRAN18.1 - Draft A)VVLNo ratings yet
- Flexible User Steering (5G RAN6.1 - Draft A)Document48 pagesFlexible User Steering (5G RAN6.1 - Draft A)VVLNo ratings yet
- 30 LTE ERAN7.0 PCI Conflict Detection Self-OptimizationDocument22 pages30 LTE ERAN7.0 PCI Conflict Detection Self-OptimizationPhan AnNo ratings yet
- Fake Base Station Identification and Detection (eRAN17.1 - Draft A)Document16 pagesFake Base Station Identification and Detection (eRAN17.1 - Draft A)Ahmed YunesNo ratings yet
- Training Course - 5G RAN2.1 Frame Structure and Physical Resources v1.01Document33 pagesTraining Course - 5G RAN2.1 Frame Structure and Physical Resources v1.01hamidreza farzanianNo ratings yet
- Azure Subscription and Service Limits, Quotas, and ConstraintsDocument54 pagesAzure Subscription and Service Limits, Quotas, and ConstraintsSorinNo ratings yet
- 819-5917-April 2021-Domestic Warranty Policy ManualDocument46 pages819-5917-April 2021-Domestic Warranty Policy ManualDean KershnerNo ratings yet
- French Revolution EssayDocument2 pagesFrench Revolution Essayapi-346293409No ratings yet
- O-CNN: Octree-Based Convolutional Neural Networks For 3D Shape AnalysisDocument11 pagesO-CNN: Octree-Based Convolutional Neural Networks For 3D Shape AnalysisJose Angel Duarte MartinezNo ratings yet
- LaMOT Rupture DiscsDocument20 pagesLaMOT Rupture Discshlrich99No ratings yet
- CH 2 How LAN and WAN Communications WorkDocument60 pagesCH 2 How LAN and WAN Communications WorkBeans GaldsNo ratings yet
- Case Chart Complete (Business Law)Document29 pagesCase Chart Complete (Business Law)LimShuLingNo ratings yet
- Far160 Pyq Feb2023Document8 pagesFar160 Pyq Feb2023nazzyusoffNo ratings yet
- Uporedna Tabela Addinol-Ovih UljaDocument4 pagesUporedna Tabela Addinol-Ovih UljaasimpeksNo ratings yet
- Suggested Answers Spring 2015 Examinations 1 of 8: Strategic Management Accounting - Semester-6Document8 pagesSuggested Answers Spring 2015 Examinations 1 of 8: Strategic Management Accounting - Semester-6Abdul BasitNo ratings yet
- B&G 3DX LiteratureDocument2 pagesB&G 3DX LiteratureAnonymous 7xHNgoKE6eNo ratings yet
- cv20672778 Prashanth - Sadak Operations-ManagerDocument4 pagescv20672778 Prashanth - Sadak Operations-ManagerBhasker NiftyNo ratings yet
- Hilti AnchorDocument5 pagesHilti AnchorGopi KrishnanNo ratings yet
- Design of Accurate Steering Gear MechanismDocument12 pagesDesign of Accurate Steering Gear Mechanismtarik RymNo ratings yet
- Charts & Publications: Recommended Retail Prices (UK RRP)Document3 pagesCharts & Publications: Recommended Retail Prices (UK RRP)KishanKashyapNo ratings yet
- 201183-B-00-20 Part ListDocument19 pages201183-B-00-20 Part ListMohamed IsmailNo ratings yet
- Stryker Endoscopy SDC Pro 2 DVDDocument2 pagesStryker Endoscopy SDC Pro 2 DVDWillemNo ratings yet
- Kudla Vs PolandDocument4 pagesKudla Vs PolandTony TopacioNo ratings yet
- Induction-Llgd 2022Document11 pagesInduction-Llgd 2022Phạm Trúc QuỳnhNo ratings yet
- KL1508 KL1516: 8/16-Port Cat 5 High-Density Dual Rail LCD KVM SwitchDocument5 pagesKL1508 KL1516: 8/16-Port Cat 5 High-Density Dual Rail LCD KVM SwitchnisarahmedgfecNo ratings yet
- Risk-Based IA Planning - Important ConsiderationsDocument14 pagesRisk-Based IA Planning - Important ConsiderationsRajitha LakmalNo ratings yet