Professional Documents
Culture Documents
Foss Statement of Applicability Public
Uploaded by
aramaky2001Original Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Foss Statement of Applicability Public
Uploaded by
aramaky2001Copyright:
Available Formats
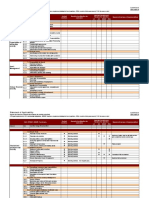
ISO 27001 Statement of Applicability
Reasons for selection
Control Included
implementation
requirements /
requirements
Adopted best
Contractual
ISO 27001:2013 Controls
assessment
obligations
Means of
practices
Business
Legal
Risk
Controls Sec Control Objective / Control
Management direction for information
5.1
security
A.5 Information
5.1.1 Policies for information security Yes X
Security policies
Review of the policies for information
5.1.2 Yes X
security
6.1 Internal Organization
Information security roles and
6.1.1 Yes X
responsibilities
6.1.2 Segregation of duties Yes X
A.6 Organization 6.1.3 Contact with authorities Yes X
of Information 6.1.4 Contact with special interest groups Yes X
security 6.1.5
Information security in project
Yes X
management
6.2 Mobile Devices and teleworking
6.2.1 Mobile Devices policy Yes X
6.2.2 Teleworking Yes X X
7.1 Prior to employment
A.7 Human 7.1.1 Screening Yes X
resource 7.1.2 Terms and conditions of employment Yes X X
security 7.2 During employment
7.2.1 Management responsibilities Yes X
FOSS’ Global Policy template page 3
If printed not controlled
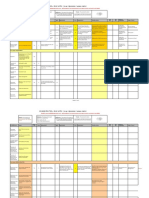
ISO 27001 Statement of Applicability
Reasons for selection
Control Included
implementation
requirements /
requirements
Adopted best
Contractual
ISO 27001:2013 Controls
assessment
obligations
Means of
practices
Business
Legal
Risk
Controls Sec Control Objective / Control
7.2.2 Information security, education and training Yes X
7.2.3 Disciplinary process Yes X X
7.3 Termination and change of employment
Termination or change of employment
7.3.1 Yes X
responsibilities
8.1 Responsibility for Assets
8.1.1 Inventory of assets Yes X
8.1.2 Ownership of assets Yes X
8.1.3 Acceptable use of assets Yes X
8.1.4 Return of assets Yes X
8.2 Information classification
A.8 Asset
8.2.1 Classification of information Yes X
management
8.2.2 Labelling of information Yes X
8.2.3 Handling of assets Yes X
8.3 Media handling
8.3.1 Management of removable media Yes X X
8.3.2 Disposal of media Yes X X
8.3.3. Physical media transfer Yes X X
A.9 Access 9.1 Business requirements of access control
control 9.1.1 Access control policy Yes X
FOSS’ Global Policy template page 4
If printed not controlled
ISO 27001 Statement of Applicability
Reasons for selection
Control Included
implementation
requirements /
requirements
Adopted best
Contractual
ISO 27001:2013 Controls
assessment
obligations
Means of
practices
Business
Legal
Risk
Controls Sec Control Objective / Control
9.1.2 Access to networks and network services Yes X
9.2 User access management
9.2.1 User registration and de-registration Yes X
9.2.2 User access provisioning Yes X
9.2.3 Management of privileged access rights Yes X
Management of secret authentication
9.2.4 Yes X X
information of users
9.2.5 Review of user access rights Yes X
9.2.6 Removal or adjustment of access rights Yes X
9.3 User responsibilities
9.3.1 Use of secret authentication information Yes X
9.4 System and application access control
9.4.1 Information access restriction Yes X
9.4.2 Secure log-on procedures Yes X
9.4.3 Password management system Yes X
9.4.4 Use of privileged utility programs Yes X
9.4.5 Access control to program source code Yes X
10.1 Cryptographic controls
A.10
10.1.1 Policy on the use of cryptographic controls Yes X X
Cryptography
10.1.2 Key management Yes X
FOSS’ Global Policy template page 5
If printed not controlled
ISO 27001 Statement of Applicability
Reasons for selection
Control Included
implementation
requirements /
requirements
Adopted best
Contractual
ISO 27001:2013 Controls
assessment
obligations
Means of
practices
Business
Legal
Risk
Controls Sec Control Objective / Control
11.1 Secure areas
11.1.1 Physical security perimeter Yes X
11.1.2 Physical entry controls Yes
11.1.3 Securing offices, rooms and facilities Yes X
Protecting against external and
11.1.4 Yes X
environmental threats
11.1.5 Working in secure areas Yes X
11.1.6 Delivery and loading areas N/A
A.11 Physical
11.2 Equipment
and
11.2.1 Equipment siting and protection Yes X
environmental
security 11.2.2 Supporting utilities Yes X
11.2.3 Cabling security Yes X
11.2.4 Equipment maintenance Yes X
11.2.5 Removal of assets Yes X
Security of equipment and assets off-
11.2.6 Yes X
premises
11.2.7 Secure disposal or re-use of equipment Yes X
11.2.8 Unattended user equipment Yes X
11.2.9 Clear desk and clear screen policy Yes X
A.12 Operations 12.1 Operational procedures and responsibilities
security 12.1.1 Documented operating procedures Yes X
FOSS’ Global Policy template page 6
If printed not controlled
ISO 27001 Statement of Applicability
Reasons for selection
Control Included
implementation
requirements /
requirements
Adopted best
Contractual
ISO 27001:2013 Controls
assessment
obligations
Means of
practices
Business
Legal
Risk
Controls Sec Control Objective / Control
12.1.2 Change management Yes X
12.1.3 Capacity management Yes X
Separation of development, testing and
12.1.4 Yes X X
operational environments
12.2 Protection from malware
12.2.1 Controls against malware Yes X
12.3 Backup
12.3.1 Information backup Yes X
12.4 Logging and monitoring
12.4.1 Event logging Yes X
12.4.2 Protection of log information Yes X
12.4.3 Administrator and operator logs Yes X
14.4.4 Clock synchronisation Yes X
12.5 Control of operational software
Installation of software on operational
12.5.1 Yes X
systems
12.6 Technical Vulnerability Management
12.6.1 Management of Technical vulnerabilities Yes X
12.6.2 Restrictions on software installation Yes X
12.7 Information systems audit considerations
12.7.1 Information systems audit controls Yes X
FOSS’ Global Policy template page 7
If printed not controlled
ISO 27001 Statement of Applicability
Reasons for selection
Control Included
implementation
requirements /
requirements
Adopted best
Contractual
ISO 27001:2013 Controls
assessment
obligations
Means of
practices
Business
Legal
Risk
Controls Sec Control Objective / Control
13.1 network security management
13.1.1 Network controls Yes X X
13.1.2 Security of network services Yes X
13.1.3 Segregation of networks Yes X
A.13 13.2 Information transfer
Communications Information transfer policies and
security 13.2.1 Yes X X
procedures
13.2.2 Agreements on information transfer Yes X
13.2.3 Electronic messaging Yes X X
Confidentiality or non-disclosure
13.2.4 Yes X
agreements
Security requirements of information
14.1
systems
Information security requirements analysis
14.1.1 Yes X X
A.14 system and specification
acquisition, Securing application services on public
14.1.2 Yes X X
development networks
and 14.1.3 Protecting application services transactions Yes X X
maintenance Security in development and support
14.2
processes
14.2.1 Secure development policy Yes X X
14.2.2 System change control procedures Yes X X
FOSS’ Global Policy template page 8
If printed not controlled
ISO 27001 Statement of Applicability
Reasons for selection
Control Included
implementation
requirements /
requirements
Adopted best
Contractual
ISO 27001:2013 Controls
assessment
obligations
Means of
practices
Business
Legal
Risk
Controls Sec Control Objective / Control
Technical review of applications after
14.2.3 Yes X X
operating platform
14.2.4 Restrictions on changes to software Yes X X
14.2.5 Secure system engineering principles Yes X
14.2.6 Secure development environment Yes X
14.2.7 Outsourced development Yes X
14.2.8 System security testing Yes X
14.2.9 System acceptance testing Yes X
14.3 Test data
14.3.1 Protection of test data Yes X
Information security in supplier
15.1
relationships
Information security policy for supplier
15.1.1 Yes X
relationships
Addressing security within supplier
A.15 Supplier 15.1.2 Yes X
agreements
relationships Information and communication technology
15.1.3 Yes X
supply chain
15.2 Supplier service delivery management
15.2.1 Monitoring and review of supplier services Yes X
15.2.2 Managing changes to supplier services Yes X
FOSS’ Global Policy template page 9
If printed not controlled
ISO 27001 Statement of Applicability
Reasons for selection
Control Included
implementation
requirements /
requirements
Adopted best
Contractual
ISO 27001:2013 Controls
assessment
obligations
Means of
practices
Business
Legal
Risk
Controls Sec Control Objective / Control
Management of Information security
16.1
incidents and improvements
16.1.1 Responsibilities and procedures Yes X X
16.1.2 Reporting information security events Yes X
A.16
16.1.3 Reporting information security weaknesses Yes X X
Information
security incident Assessment of and decision on information
16.1.4 Yes X
security events
management
16.1.5 Response to information security incidents Yes X
Learning from information security
16.1.6 Yes X
incidents
16.1.7 Collection of evidence Yes X X
17.1 Information security continuity
A.17 17.1.1 Planning information security continuity Yes X
Information Implementing information security
17.1.2 Yes X
continuity
security aspects
Verify, review and evaluate information
of business 17.1.3 Yes X
security continuity
continuity
17.2 Redundancies
management
Availability of information processing
17.2.1 Yes X
facilities
Compliance with legal and contractual
A.18 Compliance 18.1 requirements
FOSS’ Global Policy template page 10
If printed not controlled
ISO 27001 Statement of Applicability
Reasons for selection
Control Included
implementation
requirements /
requirements
Adopted best
Contractual
ISO 27001:2013 Controls
assessment
obligations
Means of
practices
Business
Legal
Risk
Controls Sec Control Objective / Control
Identification of applicable legislation and
18.1.1 Yes X
contractual requirements
18.1.2 Intellectual property rights Yes X
18.1.3 Protection of records Yes X
Privacy and protection of personally
18.1.4 Yes X
identifiable information
18.1.5 Regulation of cryptographic controls Yes X X
18.2 information security reviews
18.2.1 Independent review of information security Yes X
Compliance with security policies and
18.2.2 Yes X X
standards
18.2.3 Technical compliance review Yes X X
FOSS’ Global Policy template page 11
If printed not controlled
You might also like
- Iso 27001 Compliance ChecklistDocument47 pagesIso 27001 Compliance Checklistashik1234594% (18)
- Engineering and Commercial Functions in BusinessFrom EverandEngineering and Commercial Functions in BusinessRating: 5 out of 5 stars5/5 (1)
- CPP Domain 1 SheppDocument248 pagesCPP Domain 1 Sheppavsec100% (10)
- Statement of Applicability For ISMS - IsO 27001Document5 pagesStatement of Applicability For ISMS - IsO 27001pvendaraNo ratings yet
- ISO 13485 Process Matrix ExampleDocument3 pagesISO 13485 Process Matrix Examplesaiavi100% (1)
- ISO 27001 Gap Analysis Sample Excerpt PDFDocument8 pagesISO 27001 Gap Analysis Sample Excerpt PDFsathish kumarNo ratings yet
- ISO 27001 ChecklistDocument9 pagesISO 27001 ChecklistOuhonNo ratings yet
- Iso 27001 Checklist Template: Information Security PoliciesDocument3 pagesIso 27001 Checklist Template: Information Security PoliciesBlanche AlmondNo ratings yet
- Iso 27001 Statement of ApplicabilityDocument2 pagesIso 27001 Statement of ApplicabilityaalfonsopNo ratings yet
- Checklist of ISO 27001 Mandatory DocumentationDocument12 pagesChecklist of ISO 27001 Mandatory Documentationprtiamshah75% (4)
- Smeta 6.0 Measurement CriteriaDocument94 pagesSmeta 6.0 Measurement CriteriaLayflo50% (2)
- SAP - ABAP CDS Development User Guide: WarningDocument91 pagesSAP - ABAP CDS Development User Guide: WarningKrishna Kshera SagareNo ratings yet
- What Are Batch Element Entry (BEE) ?: B E E (BEE)Document20 pagesWhat Are Batch Element Entry (BEE) ?: B E E (BEE)arun9698No ratings yet
- Assignment For ISO27001 ConsultantDocument17 pagesAssignment For ISO27001 ConsultantArrazaq ZakariaNo ratings yet
- ISMS Statement of Applicability For ISMS Course Participant ExerciseDocument12 pagesISMS Statement of Applicability For ISMS Course Participant ExerciseCyber Guru100% (1)
- Databricks Iso 27001 27017 27018 Statement of ApplicabilityDocument35 pagesDatabricks Iso 27001 27017 27018 Statement of ApplicabilitySudhanshu Kumar SinhaNo ratings yet
- Goodhabitz B V Statement of ApplicabilityDocument16 pagesGoodhabitz B V Statement of ApplicabilityHc herveNo ratings yet
- Iso 27001 FBR ChecklistDocument9 pagesIso 27001 FBR Checklistk200341No ratings yet
- IC ISO 27001 Checklist 10838Document2 pagesIC ISO 27001 Checklist 10838ahlem moussaNo ratings yet
- NTask IA T 012 Internal Audit ChecklistDocument45 pagesNTask IA T 012 Internal Audit ChecklistSonyaNo ratings yet
- ISO QGCIO-Sample-SoA-annd-Essential-8-for-workshopDocument25 pagesISO QGCIO-Sample-SoA-annd-Essential-8-for-workshopRudini RudiniNo ratings yet
- Name Docs - SOA Equinix-EMEA Statement of ApplicabilityDocument8 pagesName Docs - SOA Equinix-EMEA Statement of ApplicabilityNatália GomesNo ratings yet
- ISO27k ISMS 4.4 Implementation and Certification Process 2022Document1 pageISO27k ISMS 4.4 Implementation and Certification Process 2022sungrayNo ratings yet
- Aspect and Impact OfficeDocument41 pagesAspect and Impact OfficevisutsiNo ratings yet
- ISO 27001 Statement of Applicability Template LMDocument4 pagesISO 27001 Statement of Applicability Template LMVathasil VasasiriNo ratings yet
- ISO 27001 Auditor Checklist PDFDocument9 pagesISO 27001 Auditor Checklist PDFHack 786No ratings yet
- IC ISO 27001 Checklist 10838Document2 pagesIC ISO 27001 Checklist 10838Raj KumarNo ratings yet
- ISO 27001 OutlookDocument3 pagesISO 27001 OutlookGani HartatoNo ratings yet
- ISO27001 Gap AnalysisDocument7 pagesISO27001 Gap Analysissu yuNo ratings yet
- ISO 14001:2015-Environmental Management Systems: Md. Sahadat HossainDocument56 pagesISO 14001:2015-Environmental Management Systems: Md. Sahadat HossainPinku KhanNo ratings yet
- Introduction To ISO StandrdsDocument24 pagesIntroduction To ISO StandrdsdurgaNo ratings yet
- Pecb-27001 4F2ECD Mauaeela-IndexDocument9 pagesPecb-27001 4F2ECD Mauaeela-IndexpunditNo ratings yet
- Document Review Report FormDocument2 pagesDocument Review Report Formdrmohamed120No ratings yet
- Arabian Gulf Oilfield Services-HSE Management SystemDocument73 pagesArabian Gulf Oilfield Services-HSE Management Systemmartahan manurungNo ratings yet
- SFR ISO 27001 2013 Statement of ApplicabilityDocument27 pagesSFR ISO 27001 2013 Statement of ApplicabilityMilton Manuel Ortiz LopezNo ratings yet
- DQSHolding - 812E1 - High Level Structure ISO 27001Document1 pageDQSHolding - 812E1 - High Level Structure ISO 27001MTOLLERNo ratings yet
- Audit Planning Matrix: PT EssentraDocument4 pagesAudit Planning Matrix: PT EssentraHerik RenaldoNo ratings yet
- QGCIO Sample SoA Annd Essential 8 For WorkshopDocument29 pagesQGCIO Sample SoA Annd Essential 8 For WorkshopMark VerdeNo ratings yet
- Statement of Applicability: ISO 27001:2013 Controls Justifikasi Kontrol Area Klausul Deskripsi Diterapkan? (Y/T)Document4 pagesStatement of Applicability: ISO 27001:2013 Controls Justifikasi Kontrol Area Klausul Deskripsi Diterapkan? (Y/T)nazar nurdinNo ratings yet
- SFR ISO 27001 2013 Statement of ApplicabilityDocument27 pagesSFR ISO 27001 2013 Statement of Applicabilitywalid ElNo ratings yet
- Iso 27001 Checklist Template: Information Security PoliciesDocument7 pagesIso 27001 Checklist Template: Information Security Policiesnils havnenNo ratings yet
- Ic Iso 27001 Checklist 10838 PDFDocument7 pagesIc Iso 27001 Checklist 10838 PDFnils havnenNo ratings yet
- Statement of ApplicabilityDocument10 pagesStatement of Applicabilityholamundo123No ratings yet
- Document Reference ISMS06005: ISO/IEC 27001:2013 Statement of ApplicabilityDocument15 pagesDocument Reference ISMS06005: ISO/IEC 27001:2013 Statement of ApplicabilityLyubomir GekovNo ratings yet
- Information Security: Statement of Applicability For The UK & Ireland BusinessDocument13 pagesInformation Security: Statement of Applicability For The UK & Ireland BusinessPatrick CloarecNo ratings yet
- ISMS Statement of ApplicabilityDocument20 pagesISMS Statement of ApplicabilityROBERTO DA SILVA ALMEIDA100% (2)
- 07 SoA-final OkDocument10 pages07 SoA-final OkFerry AstikaNo ratings yet
- Awareness Session On Environmental Management System (EMS) Based On ISO 14001:2015 RequirementsDocument23 pagesAwareness Session On Environmental Management System (EMS) Based On ISO 14001:2015 RequirementsRahul SharmaNo ratings yet
- L - ISO27k ISMS Implementation and Certification ProcessDocument1 pageL - ISO27k ISMS Implementation and Certification Processvelibor27No ratings yet
- ISO 26000 - Tool - Issue - MatrixDocument8 pagesISO 26000 - Tool - Issue - Matrixadistira jsNo ratings yet
- Group EMS Manual: Environmental Management System, EMSDocument28 pagesGroup EMS Manual: Environmental Management System, EMSCandiceNo ratings yet
- WTG - Statement of ApplicabilityDocument19 pagesWTG - Statement of ApplicabilityThabo KholoaneNo ratings yet
- Correspondence Iso 20k 27k and 9kDocument4 pagesCorrespondence Iso 20k 27k and 9kabrahamNo ratings yet
- ISO 27001 - High Level StructureDocument1 pageISO 27001 - High Level StructureМиша МакухNo ratings yet
- Iec - 60204 - 1 - Patrick Gehlen - Siemens PDFDocument28 pagesIec - 60204 - 1 - Patrick Gehlen - Siemens PDFAlbertoNo ratings yet
- Quality Manual CDocument50 pagesQuality Manual CRavikumar qsolutionsNo ratings yet
- Geocycle Introduction To OH&S 2012Document25 pagesGeocycle Introduction To OH&S 2012Safrin SangiaNo ratings yet
- International Engineering Safety Management Good Practice Handbook Volume 0Document2 pagesInternational Engineering Safety Management Good Practice Handbook Volume 0Mohan KumarNo ratings yet
- ISMS RiskusixtyDocument32 pagesISMS Riskusixtynidelel214No ratings yet
- Kertas Kerja 4Document39 pagesKertas Kerja 4Adhavan M AnnathuraiNo ratings yet
- Corporate Management, Governance, and Ethics Best PracticesFrom EverandCorporate Management, Governance, and Ethics Best PracticesNo ratings yet
- Responsible AI Governance Maturity ModelDocument10 pagesResponsible AI Governance Maturity Modelaramaky2001No ratings yet
- Smart Consumer Metering Status As On 25-Aug-2023Document4 pagesSmart Consumer Metering Status As On 25-Aug-2023aramaky2001No ratings yet
- Wireshark NotesDocument159 pagesWireshark Notesaramaky2001No ratings yet
- CDW Business Continuity Reference Guide 1Document28 pagesCDW Business Continuity Reference Guide 1aramaky2001No ratings yet
- Masterclass Strategy DocumentationDocument2 pagesMasterclass Strategy Documentationaramaky2001No ratings yet
- Wixlib - Bain Brief How Utilities Are D - 43654Document8 pagesWixlib - Bain Brief How Utilities Are D - 43654aramaky2001No ratings yet
- IT Hardware Cos Seek Clarity On Import Licensing ProcessDocument2 pagesIT Hardware Cos Seek Clarity On Import Licensing Processaramaky2001No ratings yet
- Solid State Transformer Concepts in Traction and Smart Grid Applications - PDF RoomDocument185 pagesSolid State Transformer Concepts in Traction and Smart Grid Applications - PDF Roomaramaky2001No ratings yet
- EE392n Lecture9ciscoDocument39 pagesEE392n Lecture9ciscoaramaky2001No ratings yet
- General RequirementsDocument3 pagesGeneral Requirementsaramaky2001No ratings yet
- Meter Data Management System (MDMDocument7 pagesMeter Data Management System (MDMaramaky2001No ratings yet
- ReportsDocument5 pagesReportsaramaky2001No ratings yet
- Cyber SecDocument4 pagesCyber Secaramaky2001No ratings yet
- Customer IndexingDocument3 pagesCustomer Indexingaramaky2001No ratings yet
- Communication Network ElementsDocument5 pagesCommunication Network Elementsaramaky2001No ratings yet
- Electrical Stress Monitoring of Distribution Transformers Using Smart Grid Techniques - PDF RoomDocument116 pagesElectrical Stress Monitoring of Distribution Transformers Using Smart Grid Techniques - PDF Roomaramaky2001No ratings yet
- PGID IUW2022 BrochureDocument14 pagesPGID IUW2022 Brochurearamaky2001No ratings yet
- Cybersecurity in Smart Grids, Challenges and SolutionsDocument14 pagesCybersecurity in Smart Grids, Challenges and Solutionsaramaky2001No ratings yet
- Modem Dimensions - AMISP-Contract-January-2021Document8 pagesModem Dimensions - AMISP-Contract-January-2021aramaky2001No ratings yet
- OPC Unified ArchitectureDocument8 pagesOPC Unified Architecturearamaky2001No ratings yet
- Enabling Business Transformation: Focus On Financing: Infrastructure StrategiesDocument5 pagesEnabling Business Transformation: Focus On Financing: Infrastructure Strategiesaramaky2001No ratings yet
- CB Insights - The Tech Enabled Office JourneyDocument75 pagesCB Insights - The Tech Enabled Office Journeyaramaky2001No ratings yet
- Sisa Top 5 Forensic Driven Learnings 2022 23Document20 pagesSisa Top 5 Forensic Driven Learnings 2022 23aramaky2001No ratings yet
- Smart and Sustainable Utilities: Communication, Infrastructure Technology and Testing SolutionsDocument26 pagesSmart and Sustainable Utilities: Communication, Infrastructure Technology and Testing Solutionsaramaky2001No ratings yet
- Ranking - Jul2021Document7 pagesRanking - Jul2021aramaky2001No ratings yet
- Total Cost of EngagementDocument8 pagesTotal Cost of Engagementaramaky2001No ratings yet
- The New Cfo of The Future: Finance Functions in The Twenty-First CenturyDocument25 pagesThe New Cfo of The Future: Finance Functions in The Twenty-First Centuryaramaky2001No ratings yet
- CB Insights - What Are Smart CitiesDocument37 pagesCB Insights - What Are Smart Citiesaramaky2001No ratings yet
- Best Practices in Creating A Strategic Finance Function: Sap InsightDocument16 pagesBest Practices in Creating A Strategic Finance Function: Sap Insightaramaky2001No ratings yet
- 7.1. Alfa Laval Service ManualDocument156 pages7.1. Alfa Laval Service ManualAndré HeunisNo ratings yet
- Cosivis eDocument208 pagesCosivis eZadiel MirelesNo ratings yet
- 7.2.5 APQP Phase 2 Checklist Dec 2013Document21 pages7.2.5 APQP Phase 2 Checklist Dec 2013Mani Rathinam RajamaniNo ratings yet
- Pioneer PLX 500kDocument15 pagesPioneer PLX 500kFabiNo ratings yet
- Forensic Investigation On Whatsapp Web Using Framework Integrated Digital Forensic Investigation Framework Version 2Document10 pagesForensic Investigation On Whatsapp Web Using Framework Integrated Digital Forensic Investigation Framework Version 2Th3 CKSNo ratings yet
- What Exactly Is An Information SystemDocument2 pagesWhat Exactly Is An Information SystemPeir Gen LowNo ratings yet
- Release 6.0: Technical Solution ManualDocument14 pagesRelease 6.0: Technical Solution ManualcosconorNo ratings yet
- Government Approved Workshop Gazette NotificationDocument9 pagesGovernment Approved Workshop Gazette NotificationadheesNo ratings yet
- 92.railway Track Pedestrain Crossing Without Using StaircaseDocument3 pages92.railway Track Pedestrain Crossing Without Using StaircaseMaragoni MukeshNo ratings yet
- ZAPI AC-1 ManualDocument62 pagesZAPI AC-1 ManualMarcos Gregorio da SilvaNo ratings yet
- Module 1 Introduction To ElectronicsDocument4 pagesModule 1 Introduction To ElectronicsAldrin VillanuevaNo ratings yet
- UNIX PermissionsDocument4 pagesUNIX PermissionsIngiaNo ratings yet
- Plant Maintenance StrategyDocument8 pagesPlant Maintenance Strategymirdza94No ratings yet
- Windows Processor Requirements Windows 11 Supported AMD Processors - Microsoft DocsDocument1 pageWindows Processor Requirements Windows 11 Supported AMD Processors - Microsoft DocscursantcataNo ratings yet
- ZR6 Mb-E Andy 0413 Final PDFDocument42 pagesZR6 Mb-E Andy 0413 Final PDFMihohohoNo ratings yet
- Troubleshoot EMC CelerraVNX IntegrationDocument3 pagesTroubleshoot EMC CelerraVNX IntegrationchengabNo ratings yet
- 1 Question Bank For Unit 1Document11 pages1 Question Bank For Unit 1Ajay KareNo ratings yet
- Waste SegregationDocument14 pagesWaste SegregationTrexy HerederoNo ratings yet
- Define Field SelectionDocument3 pagesDefine Field SelectionSenthil NayagamNo ratings yet
- 01 OnePlus Mobiles by United Mobile Flyer 05821Document2 pages01 OnePlus Mobiles by United Mobile Flyer 05821Malik Amir AbbasNo ratings yet
- Amstrad CPC Serial Interface User GuideDocument23 pagesAmstrad CPC Serial Interface User GuideBrian LorpNo ratings yet
- M1 Section 1. Assignment 1 Metacognitive Reading ReportDocument2 pagesM1 Section 1. Assignment 1 Metacognitive Reading ReportLandThere100% (1)
- S4 Analytics OptionsDocument6 pagesS4 Analytics Optionsnewkaox2009No ratings yet
- Total Quality Management Six SigmaDocument304 pagesTotal Quality Management Six Sigmajuancgr77No ratings yet
- Delta Series FiltersDocument12 pagesDelta Series Filtersgiovanni1912No ratings yet
- LogDocument548 pagesLogRegine CalipayNo ratings yet
- Mohammed M. Windows Forensics Analyst Field Guide... 2023Document318 pagesMohammed M. Windows Forensics Analyst Field Guide... 2023rick.bullard6348No ratings yet
- Lab ManualDocument10 pagesLab ManualtheNo ratings yet