Professional Documents
Culture Documents
ISMS Pending-Santha
ISMS Pending-Santha
Uploaded by
Sundararajan srinivasan0 ratings0% found this document useful (0 votes)
21 views4 pagesThis document outlines control requirements for various departments at Asirvad to enhance security of their applications. It lists 14 control requirements for the applications department including implementing role-based access control, blocking user access on resignation, changing known passwords, implementing multi-factor authentication, reviewing audit logs and access rights periodically, conducting security testing, and establishing a change advisory board. The CTO, Joshy, is identified as the responsible head to ensure these controls are implemented.
Original Description:
Copyright
© © All Rights Reserved
Available Formats
XLSX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThis document outlines control requirements for various departments at Asirvad to enhance security of their applications. It lists 14 control requirements for the applications department including implementing role-based access control, blocking user access on resignation, changing known passwords, implementing multi-factor authentication, reviewing audit logs and access rights periodically, conducting security testing, and establishing a change advisory board. The CTO, Joshy, is identified as the responsible head to ensure these controls are implemented.
Copyright:
© All Rights Reserved
Available Formats
Download as XLSX, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
21 views4 pagesISMS Pending-Santha
ISMS Pending-Santha
Uploaded by
Sundararajan srinivasanThis document outlines control requirements for various departments at Asirvad to enhance security of their applications. It lists 14 control requirements for the applications department including implementing role-based access control, blocking user access on resignation, changing known passwords, implementing multi-factor authentication, reviewing audit logs and access rights periodically, conducting security testing, and establishing a change advisory board. The CTO, Joshy, is identified as the responsible head to ensure these controls are implemented.
Copyright:
© All Rights Reserved
Available Formats
Download as XLSX, PDF, TXT or read online from Scribd
You are on page 1of 4
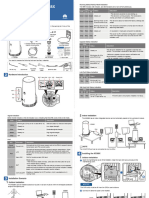
Sl.
No Control required Department Responsible
Head : Joshy (CTO)
1. Role Base Access Control (RBAC) to be defined
and periodic User and Privilege access review Application
required.
Review report must be approved and signed.
1
Procedure must be implemented to block User
access in HRMS/ all applications on the same day of Application
2 Resignation.
All the Passwords know must be changed which are
known to the resigned user on the same day and Application
3 record of the activity must be maintained.
Procedure for usage of Generic Accounts in
applications and it must be reviewed periodically Application
4 and recorded the review report.
Security Plan and its security related test cases Application
5 verification for the Change implementation
Password Policy must be uniquely followed in
Applications. Application
Asirvad Password Policy configuration in
Applications
6
MFA Authentication must be implemented for all
Application
7 critical applications of Asirvad
Audit trail logs (Applications/ Cloud Environment)
must be reviewed Monthly basis and review report Application
8 must be maintained
VAPT to be done for all applications. Application
9
User based Login must be maintained for all
Application
applications
10
Process set up for the maintenance of Generic Login
Application
11 ID's in Applications.
How the access is provisioned and deprovisioned. Application
12
Conduct BCP DR drill for all the critical applications Application
13 and networks
Change Advisory Board (CAB) establishment Application
For Critial Changes which is having business impact
14
Legal warning banners shall be displayed before
Application
15 application login screen.
Review of logical access rights shall be periodically
Application
16 performed.
Specific Secure fields in Database of applications Application
17 shall be encrypted.
All releases shall be approved by the CTO from Application
18 Asirvad.
All changes shall be tracked in the Applications and it
Application
19 can be tracked by reports.
Release logs/ versions shall be periodically reviewed
by AML to identify any unauthorised changes. Application
20
Record retention standards for data shall be defined
by AML for outsourced development and software Application
21 management.
All software applications developed by vendors for
AML shall be centrally managed by the IT Application
22 Department.
The vendor shall intimate AML before revoking or
modifying admin access from servers. Application
23
Procedure to be established
Approvals shall be obtained from AML before
granting an admin access in servers/systems. Application
24 Procedure to be established
Application administrator logs shall be monitored to
identity any fraudulent activates. Application
25
26 Data classification Application
Electronic copy of the Business, Finance, PII,
Architecture,Project Plans, Design and Regulatory
documents must be stored in centralised repository with Application
VPN access
27
To be Completed By Status
Change Advisory
Board-Charter.docx
You might also like
- 3.1 Factory Acceptance TestingDocument6 pages3.1 Factory Acceptance TestingJean-Pierre AwuNo ratings yet
- Cognizant Academy Claims Management System FSE - Business Aligned Project Case Study SpecificationDocument11 pagesCognizant Academy Claims Management System FSE - Business Aligned Project Case Study Specificationall in oneNo ratings yet
- Online Complaint Management SystemDocument67 pagesOnline Complaint Management Systemamol Akolkar ( amolpc86)88% (66)
- SM-17-9th Ed FinalDocument48 pagesSM-17-9th Ed FinaljiajiaNo ratings yet
- Application Performance Management (APM) in the Digital Enterprise: Managing Applications for Cloud, Mobile, IoT and eBusinessFrom EverandApplication Performance Management (APM) in the Digital Enterprise: Managing Applications for Cloud, Mobile, IoT and eBusinessNo ratings yet
- Test Scenario For Online Marketplace.: Test Scenario # Requirement Itest Scenario Description Test CasesDocument1 pageTest Scenario For Online Marketplace.: Test Scenario # Requirement Itest Scenario Description Test CasesHrithik KapilNo ratings yet
- MicroPHAZIR AG UserGuideDocument72 pagesMicroPHAZIR AG UserGuideGiovanni P BNo ratings yet
- Project Organization StructureDocument47 pagesProject Organization StructuresemereNo ratings yet
- Annexure XII Technical and Functional Specification PDFDocument11 pagesAnnexure XII Technical and Functional Specification PDFAndy_sumanNo ratings yet
- SiemensWhitePaper SoftwareBasedValidationDocument7 pagesSiemensWhitePaper SoftwareBasedValidationMinh Nhut LuuNo ratings yet
- Scada Integrator RFQ - s2019-94Document36 pagesScada Integrator RFQ - s2019-94M. FakNo ratings yet
- Project Scope-Statement Willmont Pharmacy CaseDocument6 pagesProject Scope-Statement Willmont Pharmacy CaseMohammed Shebin100% (2)
- Lecture 03 - Sre - Se2001 (Bse)Document31 pagesLecture 03 - Sre - Se2001 (Bse)muazzam22No ratings yet
- Complete IT and InfoSec RFP For HRMSDocument22 pagesComplete IT and InfoSec RFP For HRMSshwetank sharmaNo ratings yet
- Scoping SheetDocument5 pagesScoping SheetLalitNo ratings yet
- VISHAL ROHIT ProjectDocument35 pagesVISHAL ROHIT ProjectAtharvaNo ratings yet
- Document 2Document17 pagesDocument 2abhinandan PandeyNo ratings yet
- Sga AcuarioDocument30 pagesSga AcuarioCacha MexNo ratings yet
- Profile Balaji Vinayagamoorthy OS DeveloperDocument5 pagesProfile Balaji Vinayagamoorthy OS Developerhmaloo11No ratings yet
- Swiggy Clone Application Specification DocumentDocument15 pagesSwiggy Clone Application Specification Documentamar singhNo ratings yet
- Logistics and Warehouse Management System: Page 1 of 10Document10 pagesLogistics and Warehouse Management System: Page 1 of 10Kr VedantNo ratings yet
- Pharmacy SystemDocument63 pagesPharmacy Systemsurenderb63% (19)
- EIS SM Suggested AnswersDocument9 pagesEIS SM Suggested AnswersRaghav BhatNo ratings yet
- Sr. No. Attribute Activity Description Process ReferenceDocument21 pagesSr. No. Attribute Activity Description Process ReferenceWajahat AliNo ratings yet
- Monitor Qlik Sense SitesDocument43 pagesMonitor Qlik Sense SitesLucki Alan Fernandez SalcedoNo ratings yet
- Ch2 SW ProcessesDocument30 pagesCh2 SW ProcessesHafiza Iqra MaqboolNo ratings yet
- (External) ABDM Wrapper ProposalDocument4 pages(External) ABDM Wrapper Proposalchaks.gautyNo ratings yet
- KRA01: Identifying and Implementation of 5 Improvement in INFRADocument2 pagesKRA01: Identifying and Implementation of 5 Improvement in INFRASalil SharmaNo ratings yet
- Document 2Document17 pagesDocument 2abhinandan PandeyNo ratings yet
- Factory Management SystemDocument43 pagesFactory Management SystemVishal ShevareNo ratings yet
- Software Requirements SpecificationDocument7 pagesSoftware Requirements SpecificationshivaniNo ratings yet
- Administraor Roles and ResponsibilitiesDocument4 pagesAdministraor Roles and Responsibilitiesmkm969No ratings yet
- Manaj Kualitas SI-Software Quality Factors: Likmi/RaDocument29 pagesManaj Kualitas SI-Software Quality Factors: Likmi/RaNewDedi Liyus MardiNo ratings yet
- UIApplicationDelegate ProtocolDocument38 pagesUIApplicationDelegate ProtocolQamar SaleemNo ratings yet
- Acceptable Application Policy - INVITPOAAP2014001Document4 pagesAcceptable Application Policy - INVITPOAAP2014001swarup deyNo ratings yet
- 6 - MSA 2019-2020 - Application Portfolio Management Application Performance ManagementDocument16 pages6 - MSA 2019-2020 - Application Portfolio Management Application Performance ManagementRudhi WahyudiNo ratings yet
- How To Test Banking Domain Applications: A Complete BFSI Testing GuideDocument52 pagesHow To Test Banking Domain Applications: A Complete BFSI Testing GuideMamatha K NNo ratings yet
- ApplicationDocument4 pagesApplicationsinghkuranjitNo ratings yet
- Group 6 - IT Deployment Risks Part 3Document47 pagesGroup 6 - IT Deployment Risks Part 3Ria CruzNo ratings yet
- Cis ReportDocument19 pagesCis ReportKirsten MontefalcoNo ratings yet
- Chapter 4 - Requirements EngineeringDocument91 pagesChapter 4 - Requirements EngineeringBabar Ali RoomiNo ratings yet
- Lecture 4 System RequirementsDocument22 pagesLecture 4 System RequirementsShabanizamanaNo ratings yet
- Com/erp-Software/syspro/? From - Category 72Document6 pagesCom/erp-Software/syspro/? From - Category 72Vonna TerribleNo ratings yet
- Terms and Conditions:: Section: XIXDocument4 pagesTerms and Conditions:: Section: XIXHOD TD GITNo ratings yet
- Migrating To Cloud Based ERP SolutionDocument4 pagesMigrating To Cloud Based ERP SolutionVenkat KadajariNo ratings yet
- Sr. No. Name of Programs NoDocument33 pagesSr. No. Name of Programs NoMOHIT VERMANo ratings yet
- SRS - Beit For CLP LabDocument5 pagesSRS - Beit For CLP LabjyotsnaNo ratings yet
- RSA EnVision Platform PCI ComplianceDocument4 pagesRSA EnVision Platform PCI Compliancemmacias78No ratings yet
- Section 302 Section 404: 1. Organizational Structure ControlDocument6 pagesSection 302 Section 404: 1. Organizational Structure Controlfathma azzahroNo ratings yet
- Synopsis: Project On Stock Management System For Saw Mill IndustriesDocument4 pagesSynopsis: Project On Stock Management System For Saw Mill IndustriesRavidutt BelvalNo ratings yet
- Project Scope StatementDocument2 pagesProject Scope StatementsadotNo ratings yet
- MAM Guide v7 0Document56 pagesMAM Guide v7 0Nithin GowdaNo ratings yet
- 10 Software MaintenanceDocument35 pages10 Software MaintenanceKavitha RaniNo ratings yet
- The ArcSight Compliance Tool KitDocument24 pagesThe ArcSight Compliance Tool Kitsrmv59No ratings yet
- Ch2 SW ProcessesDocument58 pagesCh2 SW ProcessesDeependra GuptaNo ratings yet
- Lecture2 - SW Processes and AgileDocument79 pagesLecture2 - SW Processes and Agileasmm.rahamanNo ratings yet
- Chapter 20 IT Concepts and ControlsDocument10 pagesChapter 20 IT Concepts and ControlsJaalib MehmoodNo ratings yet
- UI UX: Interaction Design Visual DesignDocument7 pagesUI UX: Interaction Design Visual DesignRohan ShirdhankarNo ratings yet
- Software Requirement SpecificationsDocument10 pagesSoftware Requirement Specifications18IT031 Mohammed Marzuk Ali SNo ratings yet
- Ch02 - SWProcesses - 0Document58 pagesCh02 - SWProcesses - 0Babar Ali RoomiNo ratings yet
- ISMS Pending-AmithDocument11 pagesISMS Pending-AmithSundararajan srinivasanNo ratings yet
- Monthly Review StatusDocument3 pagesMonthly Review StatusSundararajan srinivasanNo ratings yet
- Bus Route - Chennai - March2023Document16 pagesBus Route - Chennai - March2023Sundararajan srinivasanNo ratings yet
- ISMSPoloicy 1Document14 pagesISMSPoloicy 1Sundararajan srinivasanNo ratings yet
- ZOOM Setup Features 062017Document12 pagesZOOM Setup Features 062017Sundararajan srinivasanNo ratings yet
- 11I Cloning (Multi Node To Single Node) : Appstier MergeDocument3 pages11I Cloning (Multi Node To Single Node) : Appstier MergeniaamNo ratings yet
- UEL Student Guide v1.9Document44 pagesUEL Student Guide v1.9Ifeanyi AnanyiNo ratings yet
- Project SRS DocumentDocument54 pagesProject SRS Documentdgcharitha33% (3)
- Partner Membership Center To Partner Center TransitionDocument45 pagesPartner Membership Center To Partner Center TransitionGopinath GandhavadiNo ratings yet
- Belt Weigh FeederDocument808 pagesBelt Weigh Feedersatfas100% (1)
- TMP 17804-MFA Registration578347740Document7 pagesTMP 17804-MFA Registration578347740Kirshna SarkariNo ratings yet
- Manual Kobo Toolbox: Office For The Coordination of Humanitarian Affairs (OCHA) in West and Central AfricaDocument35 pagesManual Kobo Toolbox: Office For The Coordination of Humanitarian Affairs (OCHA) in West and Central AfricaPrinceNo ratings yet
- Charismathics Smart Security Interface © User Manual V 5.0 For LINUXDocument18 pagesCharismathics Smart Security Interface © User Manual V 5.0 For LINUXvazmutenNo ratings yet
- Nano Spot UserDocument19 pagesNano Spot UserjaiherdNo ratings yet
- UntitledDocument2 pagesUntitledBonisani NdabaNo ratings yet
- Practical - 1: Aim: To Select The Project Title and Assign Requirement Engineering To The Project TitleDocument6 pagesPractical - 1: Aim: To Select The Project Title and Assign Requirement Engineering To The Project TitlePatelNo ratings yet
- iVMS-4500 (Android) Mobile Client Software User Manual V1.0Document17 pagesiVMS-4500 (Android) Mobile Client Software User Manual V1.0Black-q NewmanNo ratings yet
- 00 - Requirment Documentation - SRSDocument6 pages00 - Requirment Documentation - SRSPritee ChouguleNo ratings yet
- CIS Sybase ASE 15.0 Benchmark v1.0.0Document62 pagesCIS Sybase ASE 15.0 Benchmark v1.0.0Vinoth SivasubramanianNo ratings yet
- Login ControlsDocument26 pagesLogin Controlsapi-19796528No ratings yet
- User Guide Citizen Registration 18+Document14 pagesUser Guide Citizen Registration 18+most subscribed channel on you tubeNo ratings yet
- (SAMS) Safety Assessment Management System - Cebu Pacific AirDocument22 pages(SAMS) Safety Assessment Management System - Cebu Pacific AirParba B. RichlieNo ratings yet
- Staff User GuideDocument68 pagesStaff User GuideSeemaNo ratings yet
- Middle - 02. 190227 - MBF LTE Middle P2.2 - EdenNet Acceptance Test - Rev1.0Document27 pagesMiddle - 02. 190227 - MBF LTE Middle P2.2 - EdenNet Acceptance Test - Rev1.0Hồ Mạnh QuýNo ratings yet
- CHFI Exam Questions PDFDocument29 pagesCHFI Exam Questions PDFNelson MandelaNo ratings yet
- BPCL Portal Access Help DocumentDocument21 pagesBPCL Portal Access Help DocumentSembodaiRV AgenciesNo ratings yet
- Orbisbux FAQDocument2 pagesOrbisbux FAQNOLDAGONo ratings yet
- 5G Outdoor CPE N5368X Quick Start GuideDocument5 pages5G Outdoor CPE N5368X Quick Start GuidenviscaqNo ratings yet
- Software Requirements Specification For Tumblr 2Document20 pagesSoftware Requirements Specification For Tumblr 2Amogh VarshneyNo ratings yet
- JNTUA Student Portal 2Document10 pagesJNTUA Student Portal 2Bhanu KodaliNo ratings yet
- Case Lab SRSDocument7 pagesCase Lab SRSVS Deepak RajpurohitNo ratings yet
- User Manual RMC-v2 - 3Document26 pagesUser Manual RMC-v2 - 3carlosf_6No ratings yet
- Envision CRL Rules PDFDocument182 pagesEnvision CRL Rules PDFjerkuserNo ratings yet