Professional Documents
Culture Documents
Cryptography
Uploaded by
Rolwin Paul Benedict0 ratings0% found this document useful (0 votes)
7 views1 pageCryptography Question Bank
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCryptography Question Bank
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
7 views1 pageCryptography
Uploaded by
Rolwin Paul BenedictCryptography Question Bank
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 1
Question Bank Module 4 and 5
Course: Cryptography Course Code: 18CS744
Note: The question bank serves as reference or study guide only
1 Explain Remote User- Authentication principles 10M
2 List 4 requirements that were defined by Kerberos. Assume a client C wants to 10M
communicate with a server S using Kerberos Version 4. How can it be achieved?
3 What is the role of Ticket Granting Server in Kerberos Version 4? 10M
4 Give a summary of Kerberos Version 4 Message Exchanges with a neat diagram 10M
and message exchanges. (or) Discuss elaborately how Kerberos Version 4
provides the different authentication services
5 What are the technical deficiencies in the Kerberos version 4 protocols? 10M
6 Explain with a diagram, how a client in one realm request for service in another 10M
realm. (or) Describe the authentication dialog used by Kerberos for obtaining
services from another realm.
7 Explain Kerberos Version 5 authentication dialogue. 10M
8 Describe the PGP Cryptographic Functions with a neat diagram. Or 10M
What is PGP? Examine how authentication and confidentiality is maintained
9 Give the reason for using PGP? 10M
Why does PGP generate a signature before Apply compression? With a neat
diagram, explain Transmission and Reception of PGP Messages
10 Define S/MIME. Explain the various headers defined in MIME. 10M
11 Explain the various S/MIME functions and Cryptographic Algorithms Used in 10M
S/MIME
12 Explain DKIM functional flow with a neat diagram. 10M
13 Draw a diagram to explain the IP security scenario and explain the benefits of 10M
IPsec (or) Draw a diagram to explain the IP security scenario and explain the
applications of IPsec.
14 Give the categorization of IPsec documents. Also list out the IPsec services. 10M
What do you mean by Security Association? Illustrate the parameters that 10M
identify the Security Association.
15 With a diagram explain the IPsec Architecture. Also explain the components 10M
SAD and SPD.
16 Draw and explain the IP Traffic Processing model for inbound and outbound 10M
packets.
17 With a neat diagram explain the top-level format of an ESP Packet. 10M
What is transport mode and tunnel mode authentication in IP? Describe how 10M
ESP is applied to both these modes?
18 With a neat diagram, explain the Basic combinations of Security Associations 10M
19 Explain the two types of key management supported by IPsec architecture. Also 10M
list the important features of IKE Key determination algorithm.
20 Explain IKE header and the payload formats with a help of a neat diagram. 10M
You might also like
- CHEAT SHEET PowerShell Commands For The MCSA 70Document4 pagesCHEAT SHEET PowerShell Commands For The MCSA 70Fletcher Mutukwa100% (1)
- Cryptography and Network Security QuestionsDocument6 pagesCryptography and Network Security QuestionsPAVANI SIDDAMNo ratings yet
- Cs 6701 - Cryptography & Network Security: Question BankDocument6 pagesCs 6701 - Cryptography & Network Security: Question BankBrinda BMNo ratings yet
- Advanced Junos Enterprise Routing: Lab DiagramsDocument72 pagesAdvanced Junos Enterprise Routing: Lab Diagrams3gero3No ratings yet
- Investigating Cryptocurrencies: Understanding, Extracting, and Analyzing Blockchain EvidenceFrom EverandInvestigating Cryptocurrencies: Understanding, Extracting, and Analyzing Blockchain EvidenceRating: 5 out of 5 stars5/5 (1)
- Slide 1 - Authentication: Adobe Captivate Thursday, April 15, 2021Document55 pagesSlide 1 - Authentication: Adobe Captivate Thursday, April 15, 2021vinay kNo ratings yet
- Firepower NGFW Lab-Basics v1.7Document78 pagesFirepower NGFW Lab-Basics v1.7PopescuNo ratings yet
- Cryptography Quest Bank 02Document7 pagesCryptography Quest Bank 02Gurpreet SinghNo ratings yet
- Scribleindia IT2352 Cryptography and Network Security Question BankDocument7 pagesScribleindia IT2352 Cryptography and Network Security Question BankKavitha ManoharanNo ratings yet
- IV-I-Reg-NETWORK SECURITY & CRYPTOGRAPHYDocument2 pagesIV-I-Reg-NETWORK SECURITY & CRYPTOGRAPHYbodhu varunNo ratings yet
- CnsDocument7 pagesCnsKaram SalehNo ratings yet
- CNS QbankDocument4 pagesCNS QbankmasumiNo ratings yet
- Comprehensive guide to cryptography and network security protocolsDocument3 pagesComprehensive guide to cryptography and network security protocolsShahil SinghNo ratings yet
- QB CIE3 CryptographyDocument2 pagesQB CIE3 CryptographyThiru KumaraNo ratings yet
- CNS IMP QuestionsDocument2 pagesCNS IMP QuestionsMohammed JavidNo ratings yet
- Unit-I SNDocument4 pagesUnit-I SNYash SugandhiNo ratings yet
- Questionbank CryptoDocument4 pagesQuestionbank CryptoSantoshNo ratings yet
- CN Question Bank Module 1 2Document2 pagesCN Question Bank Module 1 2Atul JhaNo ratings yet
- Each Question Carries 3 MarksDocument2 pagesEach Question Carries 3 MarksjestinmaryNo ratings yet
- OSI Transport Layer: Network Fundamentals - Chapter 4Document22 pagesOSI Transport Layer: Network Fundamentals - Chapter 4Dondon GolesNo ratings yet
- Cryptography and Network SecurityDocument8 pagesCryptography and Network SecurityAnish KumarNo ratings yet
- Question Bank: ObjectivesDocument7 pagesQuestion Bank: ObjectivesManjunath YadavNo ratings yet
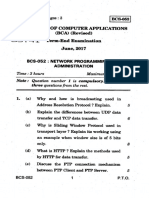
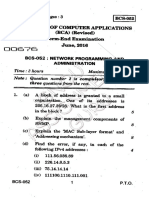
- Network Programming and ManagementDocument16 pagesNetwork Programming and ManagementepregithaNo ratings yet
- OSI Transport Layer: Network Fundamentals - Chapter 4Document19 pagesOSI Transport Layer: Network Fundamentals - Chapter 4meme saleh alharbiNo ratings yet
- OSI Transport Layer: Network Fundamentals - Chapter 4Document22 pagesOSI Transport Layer: Network Fundamentals - Chapter 4andshtNo ratings yet
- Network Security Assignment QuestionsDocument1 pageNetwork Security Assignment QuestionsRakshan TANo ratings yet
- Cryptography M T IIIDocument1 pageCryptography M T IIIManish WadkarNo ratings yet
- 6.CNS Unit Wise Question BankDocument2 pages6.CNS Unit Wise Question BankRajNo ratings yet
- Network Programming ImpDocument5 pagesNetwork Programming Impsharath_rakkiNo ratings yet
- Classical Encryption Techniques QuestionsDocument3 pagesClassical Encryption Techniques Questionsஜெயபிரகாஷ் பிரபுNo ratings yet
- Crypto Fundamentals, Standards & Network SecurityDocument5 pagesCrypto Fundamentals, Standards & Network SecurityGowthami KaviNo ratings yet
- 13344422 (1)Document52 pages13344422 (1)Rameshkumar MNo ratings yet
- CN Question Bank Module 1 2Document2 pagesCN Question Bank Module 1 2Sushmitha ChikkamaduNo ratings yet
- Unit - I QuestionsDocument2 pagesUnit - I QuestionsFarhana SathathNo ratings yet
- Instructor Materials Chapter 3: Network Protocols and CommunicationsDocument29 pagesInstructor Materials Chapter 3: Network Protocols and CommunicationsDany MaldonadoNo ratings yet
- ClassDocument4 pagesClassLailu NatchiyaNo ratings yet
- UnitDocument2 pagesUnitAmrendra SinghNo ratings yet
- Computer Network-1 IA Question BankDocument5 pagesComputer Network-1 IA Question BankVeena GadadNo ratings yet
- Preparatory Plan CCN - 2022-23Document2 pagesPreparatory Plan CCN - 2022-23Dj RayNo ratings yet
- Computer Engineering Department: Gtu Important Questions Bank Subject Name: Information Ecurity Subject Code SemesterDocument5 pagesComputer Engineering Department: Gtu Important Questions Bank Subject Name: Information Ecurity Subject Code SemesterKaushal PardasaniNo ratings yet
- CSE - 4107 2022 Assignment 3Document2 pagesCSE - 4107 2022 Assignment 3Manzil TanvirNo ratings yet
- NB InstructorPPT Chapter5Document30 pagesNB InstructorPPT Chapter5QuocDat NguyenNo ratings yet
- CN - All Unitwise Question BankDocument6 pagesCN - All Unitwise Question Bankmmit123No ratings yet
- Crypto Assignment 1Document1 pageCrypto Assignment 1FuNnY OnENo ratings yet
- A New Mutuel Kerberos Authentication Protocol For Distributed SystemsDocument10 pagesA New Mutuel Kerberos Authentication Protocol For Distributed SystemsRahul prabhaNo ratings yet
- Cs2302 Computer Networks Question Bank Annauniversity 2010 Part VDocument5 pagesCs2302 Computer Networks Question Bank Annauniversity 2010 Part Vpitchrks19841No ratings yet
- BCS 052Document3 pagesBCS 052TSN PrasadNo ratings yet
- Iot & Wireless Sensor NetworksDocument3 pagesIot & Wireless Sensor NetworksrichaNo ratings yet
- Network Programming and Administration Exam QuestionsDocument3 pagesNetwork Programming and Administration Exam QuestionsKai OheyoNo ratings yet
- Cryptography Question Bank Wihout AnswersDocument4 pagesCryptography Question Bank Wihout AnswerskingraajaNo ratings yet
- Computer NetworkDocument11 pagesComputer NetworkKIRAN BHATTARAINo ratings yet
- 07TE762Document2 pages07TE762Shiva ShankarNo ratings yet
- Introduction To Networking Sample QuestionsDocument2 pagesIntroduction To Networking Sample QuestionsAamirNo ratings yet
- 15EC752-Iot & Wireless Sensor Networks - Question Bank Module-1 Overview of Internet of ThingsDocument3 pages15EC752-Iot & Wireless Sensor Networks - Question Bank Module-1 Overview of Internet of ThingsrichaNo ratings yet
- It2352 QB PDFDocument6 pagesIt2352 QB PDFvelkarthi92No ratings yet
- Sample Suggestions For StudentsDocument4 pagesSample Suggestions For Studentschirkut BiswasNo ratings yet
- Web Security 17L238Document30 pagesWeb Security 17L238Rakesh VenkatesanNo ratings yet
- Bcs DiplomaDocument1 pageBcs Diplomatafadzwa sidNo ratings yet
- CN Important QuestionsDocument3 pagesCN Important QuestionsKrishna ChandraNo ratings yet
- Unit - 1 (Introduction of Computer Networks)Document5 pagesUnit - 1 (Introduction of Computer Networks)Abhinavv GandhiNo ratings yet
- CICS and The CICS AdapterDocument22 pagesCICS and The CICS AdaptermgkietNo ratings yet
- BCS 052 PDFDocument35 pagesBCS 052 PDFLucky0% (1)
- Cryptpgrahy Simp TieDocument3 pagesCryptpgrahy Simp TieArshiya BegumNo ratings yet
- Remove PDF Watermarks with Online ToolDocument37 pagesRemove PDF Watermarks with Online ToolRolwin Paul BenedictNo ratings yet
- Module1 – Question Bank on Compiler Design ConceptsDocument13 pagesModule1 – Question Bank on Compiler Design ConceptsRolwin Paul BenedictNo ratings yet
- Computer GraphicsDocument3 pagesComputer GraphicsRolwin Paul BenedictNo ratings yet
- Design and Analysis of AlgorithmsDocument36 pagesDesign and Analysis of AlgorithmsRolwin Paul BenedictNo ratings yet
- UntitledDocument1 pageUntitledRolwin Paul BenedictNo ratings yet
- Web TechnologyDocument38 pagesWeb TechnologyRolwin Paul BenedictNo ratings yet
- Bda ImpDocument2 pagesBda ImpRolwin Paul BenedictNo ratings yet
- UntitledDocument95 pagesUntitledRolwin Paul BenedictNo ratings yet
- Automotive Engineering: History of AutomobileDocument64 pagesAutomotive Engineering: History of AutomobileRolwin Paul BenedictNo ratings yet
- AEDocument10 pagesAERolwin Paul BenedictNo ratings yet
- IA1 UpdatedDocument2 pagesIA1 UpdatedRolwin Paul BenedictNo ratings yet
- Pig InstallDocument5 pagesPig InstallRolwin Paul BenedictNo ratings yet
- IOT Technology Explained: Evolutionary Phases, Differences Between IT & OT NetworksDocument13 pagesIOT Technology Explained: Evolutionary Phases, Differences Between IT & OT NetworksJerrinNo ratings yet
- 21 20 3 FCS10 UPC CUPS RCM Config and Admin GuideDocument29 pages21 20 3 FCS10 UPC CUPS RCM Config and Admin GuideNguyễn Lương QuyềnNo ratings yet
- Brksec 3032Document76 pagesBrksec 3032GabrieleNo ratings yet
- Certificate Validation ProcessDocument20 pagesCertificate Validation ProcessUser name second nameNo ratings yet
- Security Certification: Cyberops Associate V1.0Document116 pagesSecurity Certification: Cyberops Associate V1.0refka babouriNo ratings yet
- FSP 150CC: Intelligent Carrier Ethernet Service DemarcationDocument2 pagesFSP 150CC: Intelligent Carrier Ethernet Service DemarcationAnonymous EZs87xptbNo ratings yet
- FortiGate 1240BDocument6 pagesFortiGate 1240Bw0lfmast3rNo ratings yet
- MIT - Design and Feasibility ReportsDocument3 pagesMIT - Design and Feasibility ReportsMuhamad Andri KurniawanNo ratings yet
- Manual Router Comtrend CT5361T - A3.3Document132 pagesManual Router Comtrend CT5361T - A3.3Rafael MongeNo ratings yet
- Kyland Products at A GlanceDocument32 pagesKyland Products at A GlanceSGQNo ratings yet
- HMC Best PracticesDocument57 pagesHMC Best Practicesselvaraj1950100% (1)
- User Manual MG900Document147 pagesUser Manual MG900Stephen Strange100% (1)
- Multi Cluster Multi Cloud Service Mesh With CNCF's Kuma and Envoy 1Document12 pagesMulti Cluster Multi Cloud Service Mesh With CNCF's Kuma and Envoy 1Zarko ZivanovicNo ratings yet
- Sneak Past Pay-For WiFi With DNS TunnelingDocument5 pagesSneak Past Pay-For WiFi With DNS TunnelingmardefondoNo ratings yet
- Configuring A High Availability Cluster (Heartbeat) On CentOSDocument14 pagesConfiguring A High Availability Cluster (Heartbeat) On CentOSMukesh BarnwalNo ratings yet
- Network ProtocolsDocument12 pagesNetwork ProtocolsELIANA NASHANo ratings yet
- Manage L2+ switches with PoE, stacking and securityDocument5 pagesManage L2+ switches with PoE, stacking and securityHuy DoanNo ratings yet
- SAPROUTER Installation Instructions OrigiinalDocument4 pagesSAPROUTER Installation Instructions OrigiinalvenkatNo ratings yet
- SE0132Document5 pagesSE0132Paul WallNo ratings yet
- Techpubs en US Junos13.3 Information-Products Pathway-Pages Ngna-Solutions Next-generation-network-Addressing-solutionsDocument330 pagesTechpubs en US Junos13.3 Information-Products Pathway-Pages Ngna-Solutions Next-generation-network-Addressing-solutionsSneeking DeaNo ratings yet
- Livre AoIP PDFDocument135 pagesLivre AoIP PDFfdbttTKLCNo ratings yet
- WellGate 2504 and WellGate 2540 P2P Hotline ApplicationDocument17 pagesWellGate 2504 and WellGate 2540 P2P Hotline ApplicationMuhammad Shahroz AfzalNo ratings yet
- LAB 5 IP and ICMPDocument5 pagesLAB 5 IP and ICMPParth PatelNo ratings yet
- Linux iptables packet filtering HOWTODocument25 pagesLinux iptables packet filtering HOWTOFaye OhNo ratings yet
- Cisco Packet TracerDocument32 pagesCisco Packet TracerMuhammad Shehzad Ali KhanNo ratings yet
- Sonicwall IPSDocument4 pagesSonicwall IPSPhạm Ngọc TríNo ratings yet
- Clodbess CIDocument10 pagesClodbess CIAlok RanjanNo ratings yet