Professional Documents
Culture Documents
2015-03 Windows XP
Uploaded by
Hernan Vallenilla Rumildo MixCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
2015-03 Windows XP
Uploaded by
Hernan Vallenilla Rumildo MixCopyright:
Available Formats
Looking into
Windows
Windows XP has reached the end of its
life – what are the implications?
VOLKER JUNG, ANTHONY BYATT – Microsoft’s successful no new patches and no active support. The effect of this
and very popular Windows XP operating system is now is that XP will slowly become unsecure, unreliable and
well over a decade old. While about 30 percent of Win- incompatible with most newly released IT hardware, such
dows users worldwide still rely on XP, an operating as PCs, PC components, network equipment and printers.
system as old as this cannot be supported forever. In other words, the end of the XP era is affecting many
Accordingly, Microsoft ceased XP support on April 8th, industrial applications and requires a proactive response
2014. This means there are no new security updates, from users.
Looking into Windows 3 9
The answers to these questions were not
1 Control/HMI (human-machine interface)
always straightforward and easy, and it be- systems to be evolved
came clear that there were indeed signifi-
System/HMI Comment
cant issues raised by the end of XP sup-
port. The most significant issues can be 800xA core systems
System 800xA
grouped into four major categories: (V5.0 and older)
− Security
Freelance Freelance systems (V6.2 – V9.1)
− Compliance
− Lack of independent software
Power Generation
vendor support Portal/Tenore
All Windows-based versions
− Hardware manufacturer support
All Windows-based versions;
Conductor NT count is number of servers,
Of these, security issues are the most critical. not number of systems
Process Portal B All versions
Windows XP security updates
In 2010, the Stuxnet worm made head-
lines around the world. With a size of just
500 kB, this malicious software attacked Once the host system is compromised,
at least 14 industrial sites in Iran, including the intruder may use it to distribute more
a uranium-enrichment plant. Stuxnet at- RATs to form a botnet – a collection of
tacked in three phases: First, it targeted compromised computers that are ma-
Microsoft Windows machines and net- nipulated in concert to cause further
works, then it sought out software (also disruption.
Windows-based) used to program indus-
trial control systems and finally it insinuat- Because a RAT enables administrative
ed itself into the programmable logic con- control, it allows the intruder to monitor
A
trollers used to control machinery. user behavior through keyloggers or other
t one time, the idea of running spyware; activate a webcam; access con-
an industrial application using Since Stuxnet, the target-rich landscape of fidential information; format drives; delete
Microsoft Windows would not industrial IT has been under a sustained or alter files; and so on.
have been entertained. How- assault that has grown ever more sophisti-
ever, when Microsoft introduced their Win- cated. For example, the so-called watering In June 2014, the Havex malware family
dows XP operating system over a decade hole strategy has been devised as a way to made headlines by attacking control sys-
ago, industry sat up and took notice. Win- introduce malware into the target systems. tems in different branches of industry,
dows XP provided the stability, flexibility In this strategy, the malicious party guess- including the energy sector. A RAT is a
and functionality needed by many indus- es or observes which websites the com- main component of Havex. The RAT tro-
trial users and soon appeared in every pany often uses,
imaginable type of application. then they infect it
and sit back and An intruder can manipulate
However, all good things come to an end: wait for the victim
On April 8th, 2014 the Windows XP era to visit the site and authentic user profiles on a
concluded when Microsoft support for the
product ceased. Of course, Microsoft had
unwittingly down-
load malware onto
system to allow outsiders
given ample notice and companies had their computer. This access.
been preparing for the switch for some strategic Web com-
years. Yet many questions had to be an- promise (SWC) tac-
swered: Could a standalone XP system tic catches victims unawares because the janized websites of industrial control sys-
continue to run unaffected? What would infected websites have previously been tem (ICS) and supervisory control and
happen if the XP system was integrated trusted. data acquisition (SCADA) manufacturers.
into another system? Would new hardware In total, 146 servers were attacked by
be needed and what would be the cost of Further, an intruder can manipulate authen- Havex; 88 variants of the Havex RAT
this across the entire organization? What tic user profiles on a system to allow out- were used; and 1500 IP addresses were
would the budget for the switch likely to siders access. PC configurations can also traced in an attempt to identify victims.
be? Could virtualization fix the problem? be manipulated and PCs can then, for Clearly, Havex represented a serious
What support would be available to mi- example, become the homes of remote attack on industry.
grate over onto a new system? access trojans (RATs) – malware pro-
grams that give an intruder administrative In July 2014, the “energetic bear” virus in-
control over the target computer. RATs fected over 1,000 energy firms in Europe
Title picture
can be infiltrated into a PC via an email and the United States. This virus theoreti-
Microsoft support for Windows XP ceased on
April 8th, 2014. What are the implications for attachment. cally allows hackers to take control of
industrial users? power plants.
4 0 ABB review 3|15
− Utilize domain name server (DNS)
2 XP upgrade strategies
sinkholes to block access to the real
website.
Controller
− Issue an alert when an endpoint-initiat-
3.1 ed remote desktop or virtual network
4.0
800xA
4.1
All 800xA 5.1 6.0 connection is detected.
5.0 − Prevent binary execution for temporary
6.2
7.1 users in the file system or issue an alert
7.2
Freelance
8.1
All Freelance 2013 2015 when this occurs.
8.2 − Whitelist service binaries in the operat-
9.1
DCI 800xA 5.1 6.0
ing system.
Freelance 2013 2015 − Issue an alert for service starts/stops/
Freelance
Conductor NT All 800xA 5.1 6.0 changes.
800xA 5.1 6.0
Harmony − Audit access control lists, etc.
Symphony + 2.0
MOD 300 800xA 5.1 6.0 − Make regular control system backups.
Freelance
Freelance 2013 2015 − Buy a stock of compatible IT parts.
PPB All 800xA 5.1 6.0
800xA 5.1 6.0
Harmony
Symphony + 2.0
Retaining Windows XP is becoming unten-
Freelance 2013 2015 able. It is an inevitable part of industrial IT
Freelance
800xA 5.1 6.0 life that an evolutionary software step has
PGP/Tenore All 800xA 5.1 6.0
Harmony to be taken every so often and the move
Symphony + 2.0
upwards from Windows XP is one of the
more significant of these. The move will
put users in a position where they are well
From these examples it is apparent that they are no longer able to satisfy compli- placed to meet the security, hardware,
the industrial IT environment is quite vul- ance requirements if they remain with software and compliance demands of the
nerable enough – and without critical Win- W indows XP. With so much personal and modern industrial IT world.
dows XP security updates, PCs are wide private data now stored on servers, data
open to attack by viruses, spyware and security is a very significant concern. ABB strongly recommends that customers
other malicious software that can steal or running Windows XP operating systems
damage business data and information. Lack of independent evaluate their system life-cycle plans and
Antivirus software no longer provides full software vendor support risk mitigation strategy. Simultaneously,
protection for XP systems. Any devices re- Many software vendors no longer support ABB is offering solutions that can remedy
maining with XP can be used by attackers their products that run on Windows XP as or mitigate risks and help customers better
as an entry point into IT networks. This they are unable to receive Windows XP protect their plants and personnel while
means that even computers running sup- updates. For example, the new Microsoft ensuring safe operations and continuous
ported operating systems can then also be Office package takes advantage of the production. Services are available to help
compromised. newest Windows and does not run on meet the needs of every customer – in-
Windows XP. cluding customers who are unable to up-
Hardware grade immediately and those who elect to
Most manufacturers of PC hardware, What to do remain on Windows XP.
printers and network equipment have al- With so many issues to be overcome, what
ready stopped supporting Windows XP course of action should be taken? The rec-
on new hardware. This means that the ommendation made by Microsoft and all
software drivers required to run Windows cyber security companies is to upgrade
XP on such new hardware are, in most to Windows 7 or 8. This includes distrib-
cases, no longer available – ie, there will uted control system vendors with control
be no XP drivers for new hard disks, print- systems running operating systems with
ers, graphic cards, network equipment, W indows XP and older ➔ 1 – 2.
etc. Buying a replacement XP computer
will not be easy or cheap. XP-based hard- Of course, an evaluation can be made of
ware will become obsolete and hard to the cost of keeping XP installations safe
find. Unplanned shutdowns caused by versus upgrade costs. Remaining with
unavailability of hardware components Windows XP is a high-maintenance under- Volker Jung
will become more frequent. taking and requires tools and support from Process Automation Division
experienced cyber security companies. Mannheim, Germany
Compliance Some of the actions that need to be volker.jung@de.abb.com
Businesses that are governed by regula- undertaken include:
tory obligations, such as the Health Insur- − Reduce the size of the registry to Anthony Byatt
ance Portability and Accountability Act include only those services that are Editorial consultant
(HIPAA) in the United States, may find that absolutely needed. Louth Village, Ireland
Looking into Windows 4 1
You might also like
- Free Antivirus And Antimalware Software For Ubuntu & Linux MintFrom EverandFree Antivirus And Antimalware Software For Ubuntu & Linux MintNo ratings yet
- Open-Source Robotics and Process Control Cookbook: Designing and Building Robust, Dependable Real-time SystemsFrom EverandOpen-Source Robotics and Process Control Cookbook: Designing and Building Robust, Dependable Real-time SystemsRating: 3 out of 5 stars3/5 (1)
- Cyber Security": " (Defence in Depth Approach) Technical PresentationDocument54 pagesCyber Security": " (Defence in Depth Approach) Technical PresentationMurali SarangapaniNo ratings yet
- TP Os Cse 316 CompleteDocument10 pagesTP Os Cse 316 CompleteAshish SaxenaNo ratings yet
- Mainframe OS and Database IntegrationDocument5 pagesMainframe OS and Database Integrationsamu hayesNo ratings yet
- 2016 Paper FirmadyneDocument16 pages2016 Paper FirmadyneBuRnerNo ratings yet
- MCSLOB產品專案PAC-AX8 HMI進度Document6 pagesMCSLOB產品專案PAC-AX8 HMI進度莊勝翔No ratings yet
- Report of Cybersecurity: StuxnetDocument17 pagesReport of Cybersecurity: StuxnetAhmed MagedNo ratings yet
- Inside of StuxnetDocument6 pagesInside of Stuxnetajay_000No ratings yet
- Automated Dynamic Firmware Analysis at Scale - A Case Study On Embedded Web InterfacesDocument12 pagesAutomated Dynamic Firmware Analysis at Scale - A Case Study On Embedded Web InterfacesdeinemamaNo ratings yet
- Functions of Operating SystemDocument4 pagesFunctions of Operating SystemJitendra PradhanNo ratings yet
- Os 1Document46 pagesOs 1G.m. RajaNo ratings yet
- Individual Assignment Operating System: Quest 1. What Is Operating System? Give Any 4 Examples?Document9 pagesIndividual Assignment Operating System: Quest 1. What Is Operating System? Give Any 4 Examples?api-19433468No ratings yet
- Lynx FuzzerDocument6 pagesLynx FuzzerJohn NihaNo ratings yet
- System Administration EssentialsDocument8 pagesSystem Administration EssentialsMay Thu HanNo ratings yet
- It Takes Virtualization To Make An Agile Infrastructure: Part IV of A Series of AMD White Papers On 64-Bit ComputingDocument8 pagesIt Takes Virtualization To Make An Agile Infrastructure: Part IV of A Series of AMD White Papers On 64-Bit ComputingchamikosNo ratings yet
- 1 Virtualization Technology Literature ReviewDocument9 pages1 Virtualization Technology Literature Reviewyo yoNo ratings yet
- Patch Auditing in Infrastructure As A Service Clouds: Lionel Litty David LieDocument11 pagesPatch Auditing in Infrastructure As A Service Clouds: Lionel Litty David LiepulaksayNo ratings yet
- Unix 2 PCDocument3 pagesUnix 2 PCkrishnaeieNo ratings yet
- Windows NT: A Symmetric Multiprocessing Operating SystemDocument40 pagesWindows NT: A Symmetric Multiprocessing Operating SystemAkash KadhidNo ratings yet
- Dr. B.R. Ambedkar National Institute of Technology: Computer Networks CSX-321Document34 pagesDr. B.R. Ambedkar National Institute of Technology: Computer Networks CSX-321Gaurav SachdevaNo ratings yet
- Ame DatasheetDocument3 pagesAme DatasheetJackNo ratings yet
- Overview of Computer Hardware and Software TypesDocument7 pagesOverview of Computer Hardware and Software TypesRailey Tac-anNo ratings yet
- Another Architecture: PVM On Windows 95/NTDocument8 pagesAnother Architecture: PVM On Windows 95/NTduttbhavikNo ratings yet
- Stuxnet VirusDocument28 pagesStuxnet VirusAashish DhivarNo ratings yet
- Sec14 Paper Costin PDFDocument17 pagesSec14 Paper Costin PDFAhmed HamoudaNo ratings yet
- Network Software-: Types of Communication SoftwareDocument10 pagesNetwork Software-: Types of Communication SoftwaredavidNo ratings yet
- SWAM Stuxnet Worm Analysis in MetasploitDocument6 pagesSWAM Stuxnet Worm Analysis in MetasploitYusuf KılıçNo ratings yet
- 2022 Staticspeed Vunerability Report TemplateDocument57 pages2022 Staticspeed Vunerability Report Templateplaneta zeskNo ratings yet
- PT RevDocument10 pagesPT RevNubskie 314No ratings yet
- Bringing Virtualization To The X86 Architecture With The Original Vmware WorkstationDocument51 pagesBringing Virtualization To The X86 Architecture With The Original Vmware WorkstationYogirajNo ratings yet
- Block2 - Introduction - To - Operating SystemsDocument44 pagesBlock2 - Introduction - To - Operating SystemsAlbert NgiruwonsangaNo ratings yet
- Unit-I Programming For Problem Solving: HardwareDocument9 pagesUnit-I Programming For Problem Solving: HardwareSaurabh PandeyNo ratings yet
- IICT Lecture # 09 Softwars Its TypesDocument39 pagesIICT Lecture # 09 Softwars Its Typesvideolytical607No ratings yet
- Tech Trend Notes: High-Reflect Ance, Dielectric Mirrors Real T Ime Intrusion DetectionDocument9 pagesTech Trend Notes: High-Reflect Ance, Dielectric Mirrors Real T Ime Intrusion Detectionrocky2219No ratings yet
- UsingANSI ISA99Intech2011Jan FebDocument6 pagesUsingANSI ISA99Intech2011Jan FebQadir MohtashamNo ratings yet
- OS Services GuideDocument7 pagesOS Services GuideWiner EmolotrabNo ratings yet
- Risk Management Software: Strikerisk V6.0 Iec/En 62305-2 Protection Against LightningDocument4 pagesRisk Management Software: Strikerisk V6.0 Iec/En 62305-2 Protection Against Lightningwise manNo ratings yet
- Embedded SystemsDocument5 pagesEmbedded Systemsnjaukk.msmgggNo ratings yet
- Group 6 CET2Document11 pagesGroup 6 CET2jhon paul espinarNo ratings yet
- Virtualizing the Machine Beneath the OSDocument13 pagesVirtualizing the Machine Beneath the OSIbnu Drajat SalamNo ratings yet
- SW Vulnerabilities and Control HijackingDocument65 pagesSW Vulnerabilities and Control HijackingNike LamNo ratings yet
- Operating System Functions, Types and HistoryDocument6 pagesOperating System Functions, Types and HistoryMominaIdreesNo ratings yet
- Mrs. Hazel B. France Mrs. Hazel B. France IT Department IT DepartmentDocument75 pagesMrs. Hazel B. France Mrs. Hazel B. France IT Department IT DepartmentHazel Mjkristell Basallote FranceNo ratings yet
- Kernel Design Comparison: Member Names: Roll #Document15 pagesKernel Design Comparison: Member Names: Roll #Shiraz SiddiqNo ratings yet
- Practical-1: A. LINUX ArchitectureDocument16 pagesPractical-1: A. LINUX ArchitectureAnand BapodaraNo ratings yet
- Operating Systems: Security and PrivacyDocument8 pagesOperating Systems: Security and PrivacyAlison Jane de SilvaNo ratings yet
- Tutorials: Operating System Concepts (9 Edition) - Silberschatz, Galvin andDocument4 pagesTutorials: Operating System Concepts (9 Edition) - Silberschatz, Galvin andDebashish PalNo ratings yet
- Chapter5 Ingles TecnicoDocument6 pagesChapter5 Ingles TecnicowhitemerNo ratings yet
- Introduction To Operating SystemDocument5 pagesIntroduction To Operating SystemDebashish PalNo ratings yet
- Linux Linux Kernel: Main Articles: andDocument7 pagesLinux Linux Kernel: Main Articles: andPrincess Joy SarmaNo ratings yet
- Mainframe operating systems beyond IBM's OS/360Document6 pagesMainframe operating systems beyond IBM's OS/360Md. Shahajada Imran 1520675642No ratings yet
- Windows Vs LinuxDocument13 pagesWindows Vs LinuxShuaib QureshiNo ratings yet
- Multi-Core Programming: Shameem Akhter Jason RobertsDocument22 pagesMulti-Core Programming: Shameem Akhter Jason RobertsSatish SinghNo ratings yet
- Learning Experiences Learning Outcome 2 - Install Operating System and Drivers For Peripherals/DevicesDocument33 pagesLearning Experiences Learning Outcome 2 - Install Operating System and Drivers For Peripherals/DevicesAlexandra FernandezNo ratings yet
- OS FunctionsDocument5 pagesOS FunctionsJohnNo ratings yet
- VEE15Document14 pagesVEE15ma haijunNo ratings yet
- Wonderware InTouch Machine Edition en 0814Document9 pagesWonderware InTouch Machine Edition en 0814Binh Thai HYNo ratings yet
- Network OSDocument5 pagesNetwork OSEmmalyn TestaNo ratings yet
- An Overview of Computer SystemsDocument23 pagesAn Overview of Computer SystemsMULLAIVANESH A VNo ratings yet
- Citizen 200GX/15: Precopy2.CabDocument2 pagesCitizen 200GX/15: Precopy2.CabHernan Vallenilla Rumildo MixNo ratings yet
- Product Environmental Profile1Document5 pagesProduct Environmental Profile1Hernan Vallenilla Rumildo MixNo ratings yet
- Products Environmental Pro-FileDocument5 pagesProducts Environmental Pro-FileHernan Vallenilla Rumildo MixNo ratings yet
- Product Environmental Profile1Document5 pagesProduct Environmental Profile1Hernan Vallenilla Rumildo MixNo ratings yet
- Products Environmental Pro-FileDocument5 pagesProducts Environmental Pro-FileHernan Vallenilla Rumildo MixNo ratings yet
- Product Environmental Profile1Document5 pagesProduct Environmental Profile1Hernan Vallenilla Rumildo MixNo ratings yet
- Product Environmental Profile1Document5 pagesProduct Environmental Profile1Hernan Vallenilla Rumildo MixNo ratings yet
- Product Environmental Profile: Apacs+ Ahf216 Module APACS+ IO, Communication ModulesDocument5 pagesProduct Environmental Profile: Apacs+ Ahf216 Module APACS+ IO, Communication ModulesHernan Vallenilla Rumildo MixNo ratings yet
- Delta-2000 Ug PDFDocument138 pagesDelta-2000 Ug PDFJUAN CARLOS BERNAL MEJIANo ratings yet
- SMPS Controller: Features DescriptionDocument11 pagesSMPS Controller: Features DescriptionAdah BumboneNo ratings yet
- High surge SCRs for power suppliesDocument5 pagesHigh surge SCRs for power suppliesHernan Vallenilla Rumildo MixNo ratings yet
- Fbi200 and Fbi100 Fieldbus IsolatorDocument3 pagesFbi200 and Fbi100 Fieldbus IsolatorHernan Vallenilla Rumildo MixNo ratings yet
- Customer First For Ecostruxure™ Foxboro DcsDocument8 pagesCustomer First For Ecostruxure™ Foxboro DcsHernan Vallenilla Rumildo MixNo ratings yet
- lm2907n PDFDocument4 pageslm2907n PDFHernan Vallenilla Rumildo MixNo ratings yet
- Product Environmental Profile1Document5 pagesProduct Environmental Profile1Hernan Vallenilla Rumildo MixNo ratings yet
- LM 335Document14 pagesLM 335bootmagictranNo ratings yet
- STMicroelectronics M4T28 BR12SH1 Datasheet PDFDocument13 pagesSTMicroelectronics M4T28 BR12SH1 Datasheet PDFHernan Vallenilla Rumildo MixNo ratings yet
- Nte5400 06 PDFDocument2 pagesNte5400 06 PDFHernan Vallenilla Rumildo MixNo ratings yet
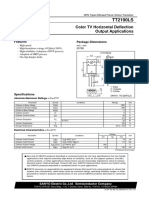
- TT2190LS: Color TV Horizontal Deflection Output ApplicationsDocument4 pagesTT2190LS: Color TV Horizontal Deflection Output ApplicationsFreddyNo ratings yet
- E4 LELit PDFDocument3 pagesE4 LELit PDFHernan Vallenilla Rumildo MixNo ratings yet
- TTL Ic 7448Document3 pagesTTL Ic 7448haseeb ahmad ch.0% (1)
- UCC2810NDocument14 pagesUCC2810NHernan Vallenilla Rumildo MixNo ratings yet
- TDA2030ADocument15 pagesTDA2030AAtsivatlaNo ratings yet
- Driver Latitude D610Document1 pageDriver Latitude D610Hernan Vallenilla Rumildo MixNo ratings yet
- Voltage Detector ?az70xxDocument12 pagesVoltage Detector ?az70xxHernan Vallenilla Rumildo MixNo ratings yet
- Voltage Detector ?az70xxDocument12 pagesVoltage Detector ?az70xxHernan Vallenilla Rumildo MixNo ratings yet
- TT2190LS: Color TV Horizontal Deflection Output ApplicationsDocument4 pagesTT2190LS: Color TV Horizontal Deflection Output ApplicationsFreddyNo ratings yet
- k790 TOSHIBA (2SK790) FETDocument5 pagesk790 TOSHIBA (2SK790) FETHernan Vallenilla Rumildo MixNo ratings yet
- Pa 3400 SeriesDocument6 pagesPa 3400 SeriesJesus Caño vargasNo ratings yet
- Module 3 - Managing Data, Application, and Host Security NewDocument61 pagesModule 3 - Managing Data, Application, and Host Security Newtroll masterNo ratings yet
- 11 Penetration Testing Tools The Pros UseDocument7 pages11 Penetration Testing Tools The Pros UseCleórbete SantosNo ratings yet
- Hacking For Beginners The Complete Guide - Barnes TimDocument48 pagesHacking For Beginners The Complete Guide - Barnes TimPom KanaNo ratings yet
- Business Result Intermediate: Student's Book Answer KeyDocument4 pagesBusiness Result Intermediate: Student's Book Answer KeyVat UdomkevinNo ratings yet
- WebFilter - Quiz - Attempt Review2Document2 pagesWebFilter - Quiz - Attempt Review2DuangkamonNo ratings yet
- How To Be A Human Firewall at WorkDocument1 pageHow To Be A Human Firewall at WorkCorey MolinelliNo ratings yet
- Week 3 - Empowerment TechnologyDocument15 pagesWeek 3 - Empowerment TechnologyNoel BuctotNo ratings yet
- FortiaiDocument4 pagesFortiaiAlex Naranjo EscalonaNo ratings yet
- Hands-On Ethical Hacking and Network Defense, 3rd EditionDocument30 pagesHands-On Ethical Hacking and Network Defense, 3rd EditionSiddhartha Bikram KarkiNo ratings yet
- Securing Sensitive Data and SystemsDocument7 pagesSecuring Sensitive Data and SystemsCROSTNo ratings yet
- Cybersecurity NotesDocument6 pagesCybersecurity NotesAinchase IshmaelNo ratings yet
- AssignmentDocument5 pagesAssignmentDmytro StachkoNo ratings yet
- Teaching and Learning Activity: Suggested SolutionsDocument4 pagesTeaching and Learning Activity: Suggested SolutionsBonginkosiNo ratings yet
- Lecture 2 - Network Security ThreatsDocument44 pagesLecture 2 - Network Security ThreatsHenry ChipindaNo ratings yet
- A Deep Survey On Types of Cyber Attacks in VANETDocument12 pagesA Deep Survey On Types of Cyber Attacks in VANETslimaneNo ratings yet
- Innovative Defense Strategies For Securing SCADA & Control SystemsDocument14 pagesInnovative Defense Strategies For Securing SCADA & Control SystemsJohnNo ratings yet
- Drill 2Document4 pagesDrill 2Julie TungculNo ratings yet
- Guide On Managing and Notifying Data Breaches Under The PDPA 15 Mar 2021Document40 pagesGuide On Managing and Notifying Data Breaches Under The PDPA 15 Mar 2021Ghaza Al GhifariNo ratings yet
- Url Shortner in Blogger CodeDocument32 pagesUrl Shortner in Blogger CodeIrfan ShaikNo ratings yet
- Threat Hunting With SplunkDocument122 pagesThreat Hunting With SplunkJesus MoraNo ratings yet
- QT ProposalDocument91 pagesQT Proposalsajadul.cseNo ratings yet
- Thousands of Hikvision Cameras Vulnerable to ExploitsDocument9 pagesThousands of Hikvision Cameras Vulnerable to ExploitsCARLOS ROANo ratings yet
- Kaspersky Virus Removal Tool 2010: How it Automatically Removes VirusesDocument9 pagesKaspersky Virus Removal Tool 2010: How it Automatically Removes ViruseslilacahayaNo ratings yet
- Monitor and Administer System and Network SoftwareDocument73 pagesMonitor and Administer System and Network SoftwareBiniyam Efrem100% (1)
- HUAWEI HiSecEngine USG6600E Series Firewalls (Fixed-Configuration) DatasheetDocument10 pagesHUAWEI HiSecEngine USG6600E Series Firewalls (Fixed-Configuration) DatasheetAnilNo ratings yet
- Bonet Englis Case StudyDocument3 pagesBonet Englis Case Studycaaraaa fellNo ratings yet
- Application Hacking PPT-1Document23 pagesApplication Hacking PPT-1ShivaniNo ratings yet
- Bailey SPD5 - 20201010 V2 - FormattedDocument15 pagesBailey SPD5 - 20201010 V2 - FormattedM Hassaan KhalidNo ratings yet
- A Forensic Analysis of APT Lateral Movement in Windows EnvironmentDocument40 pagesA Forensic Analysis of APT Lateral Movement in Windows EnvironmentSai PradeepNo ratings yet