Professional Documents
Culture Documents
p555 Lam
Uploaded by
api-37011360 ratings0% found this document useful (0 votes)
43 views5 pagesThree new combination algorithms with the minimal change property
Original Title
p555-lam
Copyright
© Attribution Non-Commercial (BY-NC)
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThree new combination algorithms with the minimal change property
Copyright:
Attribution Non-Commercial (BY-NC)
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
43 views5 pagesp555 Lam
Uploaded by
api-3701136Three new combination algorithms with the minimal change property
Copyright:
Attribution Non-Commercial (BY-NC)
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 5
Although the page size used in a storage hierarchy is
typically fixed when the subsystem is designed, it is
possible to simulate a variable size page by fetching a
group of contiguous pages in the address space whenever
one of them is referenced [3, 9, 12, 14]. Perhaps the
Programming Techniques M. Douglas Mcllroy*
number of pages included in a group could be varied
and Data Structures Editor
dynamically to ensure that the value of the fraction half-
referenced is kept within a desirable range. Three New Combination
It may therefore be possible that the fraction half-
referenced could be dynamically measured during the Algorithms with the
operation of a storge hierarchy, and used as a feedback Minimal Change Property
parameter to control the extent to which future storage
references are predicted when a page fault occurs by Clement W. H. Lam and Leonard H. Soicher
transferring a variable number of pages, and also to Concordia University
control the residence periods of those pages by adjusting
the number of first level storage page frames allocated to
each executing process.
A combination is a k-subset of an n-set. Classical
algorithms to generate all the combinations with the
Received 8/79; revised 5/80; accepted 6/81 minimal change and loopless properties were usually
complicated because they required special arrays in order
References to achieve the ioopless property. Three algorithms to
I. Baer, J. L., and Sager, G. R. Measurements and improvement of
program behaviour under paging systems. Statistical Computer
generate combinations with the minimal change property
Performance Evaluation. W. Freiberger (Ed.), Academic Press, New are presented. The first one is obtained by making a
York, 1972, 241-265. simple change to the ordinary method of recursive gen-
2. Belady, L. A. A study of replacement algorithms for a virtual
storage computer. I B M Sys. J. 5, 2 (1966) 78-101.
eration of combinations in reverse lexicographical order.
3. Bennett, B. T., and Franaszek, P. A. Permutation clustering: An The second algorithm, which has the ioopless property,
approach to on-line storage reorganization. I B M J. Res. and Develop. is obtained from the first one by using an ordinary stack
21, 6 (Nov. 1977) 528-533
4. Boon, C., and Bunyan, C. J., Eds., Virtual storage, lnfotech State
to remove the recursion. The third algorithm is an opti-
of the Art Report, Infotech International Ltd., Nicholson House, mized version of the second one. By timing comparisons,
Maidenhead, Berkshire, England, 1976. this final algorithm is considerably faster than the pre-
5. Chu, W. W., and Opderbeck, H. Performance of replacement
algorithms with different page sizes. IEEE Computer 7, 11 (Nov.
viously published combination algorithms, especially
1974) 14-21. when k is small compared to n.
6. Conti, C. J. Concepts for buffer storage. 1EEE Computer Group
News. 2, 8 (Mar. 1969) 9-13. CR Categories and Subject Descriptors: G.2.1 [Dis-
7. Denning, P. J. Virtual memory. Comp. Surv. 2, 3 (Sept. 1970), crete Mathematics]: Combinatorics--combinatorial
153-189. algorithms; F.2.2 [Analysis of Algorithms and Problem
8. Doran, R. W. Virtual memory. IEEE Computer. 9, 10 (Oct. 1976)
27-37. Complexity]: Nonnumerical Algorithms and Problems--
9. Doyle, M. S. The effects of program behaviour on the design of computations on discrete structures
storage hierarchies. Research Report CSRR-2071, Department of General Term: Algorithms
Applied Analysis and Computer Science, University of Waterloo,
Ontario, Canada (Aug. 1972). Additional Key Words and Phrases: combinations, sub-
10. Easton, M. C., and Fagin, R. Cold start vs warm start miss ratios. sets, minimal change, loopless algorithms
Comm. A C M 21, 10 (Oct. 1978) 866-872.
I 1. Ferrari, D. Program behaviour. 1EEE Computer, 9, 11 (Nov.
1976) 7-8.
12. Franaszek, P. A., and Bennett, B. T. Adaptive variation of the
transfer unit in a storage hierarchy. 1BM J. Res. and Devel. 22, 4
(July 1978) 405-412. This research was supported in part by the Natural Sciences and
13. Hatfield, D. J. Experiments on page size, program access Engineering Research Council, Canada and the Ministry of Education
patterns, and virtual memory performance. IBM J. Res. and Develop. of Quebec.
16, I (Jan. 1972) 58-66. * Former editor of Programming Techniques and Data Structures,
14. Joseph, M. An analysis of paging and program behaviour. The of which Ellis Horowitz is the current editor.
Computer Journal. 13, 1 (Feb. 1970)48-54. Authors' Present Addresses: Clement W.H. Lain, Department of
15. Kuck, D. J., and Lawrie, D. FI. The use and performance of Computer Science, Concordia University, 1455 Maisonneuve Blvd
memory hierarchies; A survey. Report No. 363, Department of West, Montreal, Quebec, Canada H3G IM8; Leonard H. Soicher,
Computer Science, University of Illinois at Champaign-Urbana (Dec. University of Cambridge, Department of Pure Mathematics and Math-
1969). ematical Statistics, 16 Mill Lane, Cambridge CB2 ISB, England.
16. Liptay, J. S. Structural aspects of the System/360 model 85--The Permission to copy without fee all or part of this material is
cache. I B M Sys. J. 7, 1 (1968), 15-21. granted provided that the copies are not made or distributed for direct
17. Mattson, R. L., et al. Evaluation techniques for storage commercial advantage, the ACM copyright notice and the title of the
hierarchies. IBM Sys. J. 9, 2 (1970) 78-117. publication and its date appear, and notice is given that copying is by
18. Spirn, J. Program Behaviour: Models and Measurements. Elsevier- permission of the Association for Computing Machinery. To copy
North Holland, New York, (1977). otherwise, or to republish, requires a fee and/or specific permission.
© 1982 ACM 0001-0782/82/0800-0555 $00.75.
555 Communications August 1982
of Volume 25
the ACM Number 8
1. Introduction Algorithm 1. Recursive generation of combinations with
minimal change property.
A combination is a k-subset of an n-set. A combina- procedure ALGOR1 ( i : integer);
tion generation has the minimal change property if every v a r j : integer;
combination, except the first, is obtained from the pre- begin
vious combination by replacing only one element. As if i rood 2 = 0
introduced by Ehrlich [2, 3], a combination algorithm is then
loopless if the maximum number of operations required for j := i to a[i+ 1] - 1 do
to generate each combination, except the first one, is a begin a[i] : = j ; A L G O R I ( i - 1 ) end
constant independent of n and k. We assume throughout else
this paper that the underlying n-set is {1, 2 . . . . . n} and f o r j := a[i+l] - 1 downto i do
that n_> k > 0. begin a[i] : = j ;
Our work is motivated by the algorithm of Bitner i f / = 1 then PROCESS else ALGOR1 ( i - 1 )
et al. [1], which was the most efficient and simplest end
method published in the generation of combinations end; (* A L G O R I *)
with the minimal change and loopless properties. The After assigning the value n + 1 to a[k + 1], the initial
description of this algorithm is repeated in [5], which call to generate all the combinations is A L G O R I (k).
also contains a summary of other combination algori- It is a simple exercise to prove that Algorithm 1
thms published. Bitner's algorithm is based on the binary generates all the different k-subsets of the n-set {1,
reflected Gray code and uses a special implementation 2 . . . . . n}. We shall now prove that it has the minimal
of a stack in order to achieve the loopless property. change property. First of all, we give the following
Interestingly, we can show that our algorithms generate definitions.
combinations in the same order as Bitner's if k is even Let a[l .. k] be a combination with a[k + l] = n +
and in the reverse order if k is odd. However, our 1. For l __ i <_ k, we define
Algorithm 1 is based on making a minor change to the
i if i is even,
usual recursive method that generates combinations in start(/)= a[i+ 1 ] - 1 if iisodd,
reverse lexicographical order. This change destroys the
ordering and the generated combinations then have the = (a[i + l] - 1 if i is even,
minimal change property. The second algorithm uses
stop (i) if i is odd.
only a standard stack to eliminate recursion and to
The element a[i] is said to be moveable if a[i] ~ stop (i).
achieve the loopless property. The final algorithm is an
The idea o f moveability is intimately related to the
optimized version of the second one, obtained by treating
execution of Algorithm 1. After returning from the pro-
separately some frequently occurring cases and by im-
cedure PROCESS, the next combination is generated by
plementing a special stack as in Bitner's algorithm. In
backing up the recursion stack until an i is found such
our test runs, our Algorithm 3 is 9 times faster than
that a[i] is moveable. The element a[/] is changed and
Bitner's algorithm when n = 24, k = 6.
A L G O R 1 is then called recursively until i = 1. The next
All the algorithms were coded in Pascal and tested
combination is then available. We now show that this
extensively on a CDC Cyber 172/2. The programs are
new combination differs from the previous one by re-
available from the authors.
placing one element.
THEOREM 2.1. Algorithm 1 has the minimal change prop-
erty.
2. The Three Algorithms
PROOF. Let a l l . . k ] be a given combination. If none of
In this paper, the algorithms are presented in Pascal. the a[i]'s is moveable, the algorithm terminates. Other-
A k-subset is represented by a global array a [ 1 . . k] of wise, let a[i] be the moveable element with the smallest
integers. The d u m m y element a[k + 1] is often used to index. In other words, a[j] = stop(j) for all j < i and
store the value n + 1. Every time a combination is a[i] ~ stop(i). It is clear that the next combination is
generated, the procedure PROCESS is called to process obtained without changing any a[j] where j > i. The
that combination. element a[i] is either increased by l or decreased by 1
It is clear that all the k-subsets can be generated in depending on the parity of i. The remaining elements
reverse lexicographical order by k nested loops. These a[j], j < i, are assigned the value start ( j ) in decreasing
nested loops can be reduced to a single loop by using order o f j . Table I summarizes the differences between
recursion. Algorithm 1 is obtained by insisting that the the old and the new combinations.
loop which controls the generation of the element a[i] If i > l, then the new combination differs from the
shall depend on the parity of the index variable i. This old one either by replacing i - l by x + 1 or by replacing
algorithm will have the minimal change property. x by i - l, depending on the parity of i. If i = 1 then x
556 Communications August 1982
of Volume 25
the ACM Number 8
Table 1. The Effect of Generating a N e w C o m b i n a t i o n W h e n a[i] is begin POP (i);
the Moveable Element with the Smallest Index.
ifimod2=Othen
i even i odd begin a [ i - l ] := a[i]; a[i] := a[O + 1;
if a[0 < a [ i + l ] - 1 then PUSH (i);
old new old new
P U S H ( i - 1);
a[i] x x + 1 x x- 1 if i > 2 then P U S H (i-2)
a[i--l] i-- 1 x x- 1 i- 1 end else
a[i-- 2] i-- 2 i-- 2 i-- 2 i-- 2
begin
if i > 1 t h e n a [ i - l ] : = i - 1;
a[q := a[/'] - 1;
a[l] 1 1 1 1 if a[i] > i then
begin PUSH (i);
i f / > 1 then PUSH (i-1)
is replaced by x - 1. Hence, the algorithm has the end
minimal change property. [] end;
PROCESS
The preceding proof describes the necessary changes end (* main loop *)
to go from one combination to the next, provided that
the moveable element with the smallest index is known. The efficiency of Algorithm 2 depends on how effi-
The standard method to eliminate the recursion in Al- ciently the stack operations can be implemented. Using
gorithm 1 would be to push the index i of each recursive the method of counting operations, as in [4], Algorithm
call, in decreasing order, onto a stack. However, in 2 is comparable in efficiency to Bitner's algorithm.
Algorithm 2, we only push the indices of the moveable Algorithm 3 is derived from Algorithm 2 by making
a[i]'s. Thus, the top element of the stack contains the changes that improve the efficiency. The major change
smallest index i such that a[i] is moveable. In general, is to treat i = 1 and i = 2 as special cases. We shall prove
Algorithm 2 proceeds as follows. After an i is popped in the next theorem that these two cases occur frequently.
from the stack, a[i] and, if necessary, a[i - 1] are We define a(i) as the number of times i is popped
changed. These operations may cause a[i - 1] and from the stack in Algorithm 2. Let C(r, s) be the number
a[i - 2] to be moveable. The indices of the moveable
of combinations or r things taken s at a time, and let
C(r,s) = 0ifr<s.
elements among a[i], a[i - 1], and a[i - 2] are then
pushed onto the stack in decreasing order. At this point,
THEOREM 2.2 a ( i ) = C(n - i, k - i + 1).
the new combination has been generated and the stack
has been updated. We now have a nonrecursive algo- PROOF. If i is odd, then o~(i) is equal to the number of
rithm with the minimal change and loopless properties. ways of choosing a[i] < . . . < a [ k ] from the set {i +
In the description of Algorithm 2, we assume the l . . . . . n}. Hence a(i) is given by Theorem 2.2. If i is
existence of the standard stack operations PUSH (i), even, then a(i) is equal to the number of ways of choosing
POP (i), and the Boolean function STACKEMPTY, a[i] < . . . < a [ k ] from the set {i, . . . . n} with the extra
which returns the value of true if the stack is empty. The condition that a[i] ~ a[i + 1]-1. As usual, we assume
procedure C L E A R S T A C K empties the stack. a[ k + 1] = n + 1. Each of these choices can be generated
by choosing a[i] < . . . < a [ k ] from {i + 1. . . . . n} and
Algorithm 2. Nonrecursive generation of combinations
then subtracting 1 from a[i]. Hence Theorem 2.2 is also
with minimal change and loopless properties.
correct when i is even. []
(* initialization *)
CLEARSTACK; Every time an i is popped from the stack, a new
if k mod 2 = 0 then combination is generated. We define P(i) as the proba-
begin a [ k + l ] := n + 1; a[k] := k; bility that a combination is generated by popping i from
if k < n then P U S H (k) the stack.
end else Thus
begin a[k] := n; 1'(i) = a ( i ) / C(n, k)
if k < n then
begin PUSH (k); By simple algebraic manipulations, one can show that
i l k > 1 then P U S H ( k - l )
P(1) = 1 - k / n ,
end
P(2) = (1 - k / n ) [ k / ( n - 1)], and
end;
P(I) + e(2) = 1 - k ( k - l ) / [ n ( n - 1)] (1)
fori:= 1 tok- 1 doa[i]:=i;
PROCESS; (* first combination *) Equation (1) implies that the probability of popping
(* main loop to generate all other combinations *) an i > 2 from the stack is approximately ( k / n ) 2. If k is
while not S T A C K E M P T Y do small compared to n, then this is a rare event. This
557 Communications August 1982
of Volume 25
the A C M Number 8
observation suggests that one should optimize the han- begin t[top-1] := t[top]; t[top] := top + 1
dling of the two cases, i = 1 and i = 2. In Algorithm 3, end;
whenever a 2 is popped from the stack, all the combi- top := top - 2
nations obtainable by changing only a[1] and a[2] are end else
generated in two nested loops. A side effect of this begin a[top] := a[top] - 1;
optimization step is that the portion of the algorithm if a[top] > top then
handling the cases where i > 2, does not have to test the begin top := top - 1; a[top] := top
condition i > 2 nor the condition i > 1. Hence, this end else
segment of the algorithm becomes simpler. One should begin a [ t o p - 1 ] := top - 1; i := top;
note also that 2 is now the smallest i that can be pushed top := t[top]; t[i] := i + 1
onto the stack. However, we must now treat k = 1 as a end
special case. end;
The next improvement is to make the stack opera- PROCESS
tions more efficient. On the C D C Cyber 172/2, stack end
operations are not basic instructions. We found through
The remaining case k = 1, can be handled easily with a
timing tests that it is most efficient to implement the
single loop and the code for it is not shown.
stack in a manner similar to Bitner et al. [1]. The vector
t[2.. k] is used to implement the stack. The convention
is that if i is in the stack, then t[i] gives the next element
3. Concluding Remarks
down in the stack. I f i is not in the stack, then t[i] is i +
1. The variable top contains the top element of the stack.
We shall give some empirical and theoretical com-
The bottom of the stack is denoted by 0. To avoid
parisons between Bitner's algorithm and Algorithm 3.
popping and then pushing the same element, the element
Algorithm 3 was coded with the remainder tests mod 2
top is popped from the stack only if a[top] = stop(top).
replaced by indexing into a precomputed Boolean array.
The pushing of one or more successive elements onto the
Bitner's algorithm was coded in Pascal. After verifying
stack is performed by one assignment statement.
its correctness, we did timing comparisons. Some sample
Algorithm 3. Optimized version of Algorithm 2 for results are shown in Table II. The unit of time is a
k>l. second. The timing statistics do not include the time
spent in calling the procedure PROCESS. In the table,
top := 0; (* clear the stack *)
the notation T+ corresponds to the Pascal compiler's
if k rood 2 = 0 then
option that includes runtime tests and T - corresponds
begin a [ k + l ] := n + 1; a[k] := k;
to no runtime tests. Also, timing can fluctuate by as
i l k < n then top := k
m u c h as l0 percent on our C D C Cyber 172/2 computer.
end else
As used by Ives in [4], we can also compare the two
begin a[k] := n;
algorithms by counting the n u m b e r of operations per-
ifk<nthentop:=k- 1
formed. A representative operation is the assignment
end;
operation. To generate the next combination, Bitner's
a[1] := l;
algorithm needs a m i n i m u m of 7 and a m a x i m u m of 9
t[k] := O;
assignment operations. W h e n top > 2, Algorithm 3 needs
for i : = 2 t o k - ldo
either 3 or 5 assignment operations to generate the next
begin a[i] := i; t[i] := i + 1 end;
combination. The latter case occurs if the element top is
PROCESS; (* first combination *)
to be deleted from the stack. When top = 2, Algorithm
(* main loop to generate all other combinations *)
3 takes 4 assignment operations to generate the first
while top < > 0 do
combination, and each of the remaining combinations
if top = 2 then
generated in the two nested repeat loops requires either
begin (* special handling for a[2] and a[1] *)
l or 2 assignment operations. The counts for all the other
top := t[2]; t[2] := 3;
types of operations can be obtained in a similar manner.
repeat
We now make two final observations. First of all, the
a[1] := a[2]; a[2] := a[2] + 1;
analysis of Algorithm 3 depends on how often a[top] =
PROCESS;
repeat a[1] := a[l] - 1;
Table II. Timing Comparison of Algorithm 3 and Bitner's Algorithm
PROCESS
with Time in Seconds.
until a[l] = 1
until a[2] = a[3] - 1 Algorithm 3 Bitner's Algorithm
end else n k T+ T- T+ T-
begin
if top mod 2 = 0 then 24 6 1.6 1.4 13.9 9.3
22 11 16.2 11.8 66.1 44.1
begin a [ t o p - 1 ] := a[top]; a[top] := a[top] + 1;
24 18 5.9 3.6 13.2 8.8
if a[top] = a[top+ 1] - 1 then
558 Communications August 1982
of Volume 25
the ACM Number 8
stop(top). In such a situation, the element top has to be Programming Techniques M. Douglas Mcllroy*
deleted from the stack and more operations are required and Data Structures Editor
to generate the next combination. When k > top > 2,
one can show that the probability for a specific value of The Solution for the
top that a[top] = stop(top) is a(top + l)/a(top), which Branching Factor of the
reduces to (k - top + l ) / ( n - top). Hence, when k is
small compared to n, it is very unlikely that the next Alpha-Beta Pruning
combination is generated by using the theoretical maxi- Algorithm and its Optimality
m u m n u m b e r of operations.
I f k is very small compared to n, then P(I), the Judea Pearl
probability that a combination is generated by changing University of California, Los Angeles
only a[1], is approximately 1. In this case, almost all the
combinations are generated by the single statement a[1]
:= a[1] - 1. It is doubtful that any combination algorithm This paper analyzes N,.d, the average number of
would require less work than this to generate a combi- terminal nodes examined by the a - f l pruning algorithm
nation. in a uniform game tree of degree n and depth d for which
the terminal values are drawn at random from a contin-
Received 8/79; revised 10/81; accepted 11/81
uous distribution. It is shown that increasing the search
References depth by one extra step would increase N,~d by a factor
1. Bitner, J.R., Ehrlich, G., and Reingold, E.M. Efficient generation (called the branching factor) ~t~_,(n) = ~,/1 - ~n ~ n 3/4
of the binary reflected Gray code and its applications. Comm. ,4 CM, where ~,~ is the positive root of x" + x - 1 = 0. This
19, 9 (Sept. 1976), 517-521.
2. Ehrlich, G. Algorithm 466, Four combinatorial algorithms. implies that for a given search time allotment, the a - f l
Comm. ACM, 16, II (Nov. 1973), 690-691. pruning allows the search depth to be increased by a
3. Ehrlich, G. Loopless algorithms for generating permutations,
combinations and other combinatorial configurations. J. ,4 CM, 20,
factor = 4/3 over that of an exhaustive minimax search.
(1973), 500-513. Moreover, since the quantity (~n/1 - ~,~)d has been
4. Ives, F.M. Permutation enumeration: Four new permutation identified as an absolute lower bound for the average
algorithms. Comm. ACM, 19, 2 (Feb. 1976), 68-72. complexity of all game searching algorithms, the equality
5. Reingold, E.M., Nievergelt, J., and Deo, N. Combinatorial
Algorithms: Theory and Practice. Prentice-Hall, New Jersey, 1977. ;JC~_~(n) = ~,,/1 - ~n now renders a-fl asymptotically
optimal
C R Categories and Subject Descriptors: 1.2.8 [Artifi-
cial Intelligence]: Problem Solving, Control Methods
and Search--graph and tree search strategies, heuristic
methods; F.2.2 [Analysis of Algorithms and Problem
Complexity]: Nonnumerical Algorithms and P r o b l e m s - -
complexity of proof procedures, sorting and searching;
G.2.2 [Discrete Mathematics]: G r a p h Theory--graph
algorithms, trees
General Term: Algorithms
Additional Key Words and Phrases: alpha-beta
search, game searching, games, minimax algorithms,
branch and bound search, average case analysis
This work was supported in part by the National Science Foun-
dation Grants MCS 78-07468 and MCS 78-18924
An early versionof this paper was presented at the 8th International
Conference on Automata Languages and Algorithms, Acre, Israel, July
3-17, 1981.
* Former editor of Programming Techniques and Data Structures,
of which Ellis Horowitz is the current editor.
Author's Present Address: Judea Pearl, Cognitive Systems Labo-
ratory, Departments of Computer Science and Engineering Systems,
University of California, Los Angeles, Los Angeles, CA 90024.
Permission to copy without fee all or part of this material is
granted provided that the copies are not made or distributed for direct
commercial advantage, the ACM copyright notice and the title of the
publication and its date appear, and notice is given that copying is by
permission of the Association for Computing Machinery. To copy
otherwise, or to republish, requires a fee and/or specific permission.
© 1982 ACM 0001-0782/82/0800-0559 $00.75.
559 Communications August 1982
of Volume 25
the ACM Number 8
You might also like
- Optimization in Engineering DesignDocument13 pagesOptimization in Engineering DesignCoNo ratings yet
- ConvexHull PreparataHong77 PDFDocument7 pagesConvexHull PreparataHong77 PDFarun_kejariwalNo ratings yet
- p424 KowalskiDocument13 pagesp424 KowalskiMaya Ria AgustinNo ratings yet
- Brent Kung Prefix AdderDocument5 pagesBrent Kung Prefix AdderSanary RebelsNo ratings yet
- Rethinking Modular Multi-Exponentiation AlgorithmsDocument15 pagesRethinking Modular Multi-Exponentiation Algorithmsfsd fsdfdsNo ratings yet
- Convex Hulls of Finite Sets of Points in Two and Three DimensionsDocument7 pagesConvex Hulls of Finite Sets of Points in Two and Three DimensionsAnonymous UjdVtuTtqNo ratings yet
- J. Parallel Distrib. Comput.: Oleksandr Kalentev Abha Rai Stefan Kemnitz Ralf SchneiderDocument6 pagesJ. Parallel Distrib. Comput.: Oleksandr Kalentev Abha Rai Stefan Kemnitz Ralf Schneiderakash menonNo ratings yet
- L Stability of Large Scale SystemsDocument4 pagesL Stability of Large Scale SystemsBinhMinh NguyenNo ratings yet
- Nagrath 1982Document1 pageNagrath 1982Manikya SharmaNo ratings yet
- Distributed Dynamic Programming: Thar Appl.. Vol. 6, Pp. 213-222. 1978. Oprimization. New York: Van NostrandDocument7 pagesDistributed Dynamic Programming: Thar Appl.. Vol. 6, Pp. 213-222. 1978. Oprimization. New York: Van Nostrandarun_kejariwalNo ratings yet
- A Comprehensive StudyDocument11 pagesA Comprehensive StudyGerardo OlveraNo ratings yet
- Machine Learning Approach For Computing Optical Properties of A Photonic Crystal FiberDocument12 pagesMachine Learning Approach For Computing Optical Properties of A Photonic Crystal FiberfaisalbanNo ratings yet
- QTree Represent CACM82Document6 pagesQTree Represent CACM82Satyajeet ParidaNo ratings yet
- A Survey of Work On Multiple Valued LogiDocument5 pagesA Survey of Work On Multiple Valued Logichibballi.ec21No ratings yet
- X,, - S-A-Az2,: F (.rl.x2..rg..rq)Document7 pagesX,, - S-A-Az2,: F (.rl.x2..rg..rq)uptcalc2007No ratings yet
- An Efficient Algorithm For The Evaluation of Convolution IntegralsDocument22 pagesAn Efficient Algorithm For The Evaluation of Convolution IntegralsCarlangasPardoNo ratings yet
- A Sparse Matrix Approach To Reverse Mode AutomaticDocument10 pagesA Sparse Matrix Approach To Reverse Mode Automaticgorot1No ratings yet
- IEEE TRANSACTIONS ON COMPUTERS, VOL. C-22, NO. 8, AUGUST 1973Document8 pagesIEEE TRANSACTIONS ON COMPUTERS, VOL. C-22, NO. 8, AUGUST 1973Tamer CakiciNo ratings yet
- An Efficient Exact Model For The Cell Formation Problem Bychkov2018Document9 pagesAn Efficient Exact Model For The Cell Formation Problem Bychkov2018khemakhem MohamedAliNo ratings yet
- ClusterDocument5 pagesClusterceti7No ratings yet
- K. J. Somaiya College of Engineering, Mumbai-77Document7 pagesK. J. Somaiya College of Engineering, Mumbai-77ARNAB DENo ratings yet
- Ogunnaike Ray 1979Document15 pagesOgunnaike Ray 1979John Walter Ticona QuispeNo ratings yet
- TR (Zak) : Xo+z,' Z + ZDocument5 pagesTR (Zak) : Xo+z,' Z + ZSara WigginsNo ratings yet
- A Global-Local Optimization Method For Problems in Structural DynamicsDocument10 pagesA Global-Local Optimization Method For Problems in Structural DynamicsxtrenNo ratings yet
- Numerical Tools in Structural Optimization - Iass Iacm 2008Document4 pagesNumerical Tools in Structural Optimization - Iass Iacm 2008juancarrionmonsalveNo ratings yet
- Interleave-Division Multiple Access in High Rate ApplicationsDocument4 pagesInterleave-Division Multiple Access in High Rate ApplicationsRoopali AgarwalNo ratings yet
- IFS Matlab Generator A Computer Tool For Displaying IFS FractalsDocument11 pagesIFS Matlab Generator A Computer Tool For Displaying IFS FractalsDorys MorgadoNo ratings yet
- 1 Projection Pursuit Regression and Neural Networks 6Document44 pages1 Projection Pursuit Regression and Neural Networks 6sridharmirNo ratings yet
- Computational Physics SyllabusDocument3 pagesComputational Physics SyllabusAbhishek SharmaNo ratings yet
- Transfer Function Method of Calculating Cooling Loads Heat Extra 1973Document1 pageTransfer Function Method of Calculating Cooling Loads Heat Extra 1973Gavriel CarvalhoNo ratings yet
- Evolution of Continuous-Time Modeling and SimulationDocument10 pagesEvolution of Continuous-Time Modeling and SimulationFrancesco_Giun_36No ratings yet
- Tai - Pereira - An Approximate Formula For Calculating The Directivity of An AntennaDocument2 pagesTai - Pereira - An Approximate Formula For Calculating The Directivity of An Antennasanjeevsoni64No ratings yet
- Design and Analysis of Algorithms Laboratory (15Csl47)Document12 pagesDesign and Analysis of Algorithms Laboratory (15Csl47)Raj vamsi Srigakulam100% (1)
- On-The-Fly Garbage CollectionDocument11 pagesOn-The-Fly Garbage CollectionRyan CookNo ratings yet
- K-Means Clustering Method For The Analysis of Log DataDocument3 pagesK-Means Clustering Method For The Analysis of Log DataidescitationNo ratings yet
- Tackling Component Interoperability in Quantum Chemistry SoftwareDocument10 pagesTackling Component Interoperability in Quantum Chemistry SoftwareElectro_LiteNo ratings yet
- 5th International Congress on Multi-Physics SimulationsDocument10 pages5th International Congress on Multi-Physics SimulationsoguierNo ratings yet
- Koch 1986Document5 pagesKoch 1986Sidinei RibisckiNo ratings yet
- I Jsa It 04132012Document4 pagesI Jsa It 04132012WARSE JournalsNo ratings yet
- 2018 A Comparative Study of Different Curve Fitting Algorithms in ANNDocument5 pages2018 A Comparative Study of Different Curve Fitting Algorithms in ANNEhtesham AshrafNo ratings yet
- Diaz 1999Document14 pagesDiaz 1999Abdur RashidNo ratings yet
- Boomer AMGDocument23 pagesBoomer AMGKeerthana Chandrasekar JeyanthiNo ratings yet
- WH TransformDocument5 pagesWH Transformyugandhar_yadamNo ratings yet
- Modelling The Runtime of The Gaussian Computational Chemistry Application and Assessing The Impacts of Microarchitectural VariationsDocument11 pagesModelling The Runtime of The Gaussian Computational Chemistry Application and Assessing The Impacts of Microarchitectural Variationselias antonio bello leonNo ratings yet
- Notebook OR 2015Document74 pagesNotebook OR 2015DonitaNo ratings yet
- s14 CompletareDocument14 pagess14 CompletareLaura NicoletaNo ratings yet
- Genetic Programming Within Civil EngineeringDocument6 pagesGenetic Programming Within Civil EngineeringJagadeesh SundaramNo ratings yet
- Fast Scaling in The Residue Number SystemDocument5 pagesFast Scaling in The Residue Number SystemswarnasureshtrNo ratings yet
- Machine Learning Journal Article Summarizes CN2 Induction AlgorithmDocument29 pagesMachine Learning Journal Article Summarizes CN2 Induction AlgorithmPratik DevkotaNo ratings yet
- Comparative Analysis of KL and SA Partitioning Algorithms Implemented On VLSI Circuit PartitioningDocument7 pagesComparative Analysis of KL and SA Partitioning Algorithms Implemented On VLSI Circuit Partitioningwww.irjes.comNo ratings yet
- Document 3Document16 pagesDocument 3Su BoccardNo ratings yet
- Symbolic Analysis of Electronic Circuits Based On A Tree Enumeration TechniqueDocument7 pagesSymbolic Analysis of Electronic Circuits Based On A Tree Enumeration TechniqueVinayakNo ratings yet
- Fast Approximate Energy Minimization Via Graph CutsDocument18 pagesFast Approximate Energy Minimization Via Graph Cutskarnati87No ratings yet
- Decoupling of Fluid and Thermo Elastic Simulations On Machine - 2017 - ProcediaDocument6 pagesDecoupling of Fluid and Thermo Elastic Simulations On Machine - 2017 - ProcediaDEEPESH KUMARNo ratings yet
- Michael P. Ekstrom (Auth.) - Digital Image Processing Techniques (1984, Academic Press) PDFDocument379 pagesMichael P. Ekstrom (Auth.) - Digital Image Processing Techniques (1984, Academic Press) PDFApolinar TabañeraNo ratings yet
- Computational Geometry Methods and Applications - ChenDocument227 pagesComputational Geometry Methods and Applications - ChenAlejandro JimenezNo ratings yet
- Introduction To Fem - The Electrical PerspectiveDocument18 pagesIntroduction To Fem - The Electrical Perspectivebhairavthakkar1975No ratings yet
- C EssentialsDocument45 pagesC EssentialssuchitraprasannaNo ratings yet
- Unix Text ProcessingDocument680 pagesUnix Text Processingapi-3701136No ratings yet
- Unix ToolsDocument94 pagesUnix Toolsapi-3701136No ratings yet
- A Tutorial On Pointers and Arrays in CDocument53 pagesA Tutorial On Pointers and Arrays in Cnaveen karthikeyan100% (10)
- Build 11gR2 RAC to RAC Physical Standby DataGuardDocument9 pagesBuild 11gR2 RAC to RAC Physical Standby DataGuardpravin2projectsNo ratings yet
- LogcatDocument25 pagesLogcatequiseedson15No ratings yet
- 0478 s19 Ms 13Document12 pages0478 s19 Ms 13Me RandomNo ratings yet
- 12 CS Worksheet - FunctionDocument5 pages12 CS Worksheet - Functionmukesh lanna100% (1)
- Deep Blue Delay ManualDocument32 pagesDeep Blue Delay Manualeleazar campoNo ratings yet
- ETPMDocument11 pagesETPMsamiie30No ratings yet
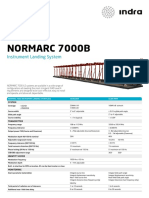
- Normarc Data SheetsDocument18 pagesNormarc Data SheetsReza RezaeiNo ratings yet
- M.sc. Computer Science Syllabus - 2021-2022 OnwardsDocument66 pagesM.sc. Computer Science Syllabus - 2021-2022 OnwardsSanthiya SanthiyaNo ratings yet
- Fundamental File Structure Concepts & Managing Files of RecordsDocument18 pagesFundamental File Structure Concepts & Managing Files of RecordsVenkat SNo ratings yet
- Software Engineering Lecture 5 Requirement EngineeringDocument35 pagesSoftware Engineering Lecture 5 Requirement Engineeringحماد شھزادNo ratings yet
- MT6070/8070/6100/8100 I Series: Installation InstructionDocument2 pagesMT6070/8070/6100/8100 I Series: Installation InstructionLuis Alberto PalaciosNo ratings yet
- LXC 6110E MANUAL - CompressedDocument46 pagesLXC 6110E MANUAL - CompressedLuis Gonzalez100% (2)
- Midterm Examination NET 1 Lec and LabDocument5 pagesMidterm Examination NET 1 Lec and LabCj AntonioNo ratings yet
- Acceptance of Delivery: It Project Descriptions & ScopeDocument8 pagesAcceptance of Delivery: It Project Descriptions & ScopeAhmed ElhartyNo ratings yet
- PHP With Mysql Material-1Document63 pagesPHP With Mysql Material-1Vijay DhamaNo ratings yet
- Training Manual 2 PDFDocument46 pagesTraining Manual 2 PDFjrusalen1100% (1)
- Designing A SASE Architecture by NetskopeDocument66 pagesDesigning A SASE Architecture by NetskopeFrank TafurNo ratings yet
- How To Install The Xerox Printer For Windows: If Your Computer Is in Active DirectoryDocument14 pagesHow To Install The Xerox Printer For Windows: If Your Computer Is in Active DirectoryRadhakrishnan IyerNo ratings yet
- Error Sync 1459757003592Document3 pagesError Sync 1459757003592Nyi Lay NaingNo ratings yet
- Epic Story / Req ID Steps Test DataDocument4 pagesEpic Story / Req ID Steps Test DatazsdxcfgNo ratings yet
- Nav2013 Enus Csintro 10Document18 pagesNav2013 Enus Csintro 10Cesar Alexander Gutierez RuedaNo ratings yet
- Electrical Engineering Past Papers: NESCOM/ NDC / Career 1737 Past Paper (AM Electronics)Document12 pagesElectrical Engineering Past Papers: NESCOM/ NDC / Career 1737 Past Paper (AM Electronics)NadeemAhmad0% (1)
- AUTOSAR Handbook for Embedded System ProfessionalsDocument93 pagesAUTOSAR Handbook for Embedded System Professionalschandrakanthats100% (2)
- Computer QuizDocument31 pagesComputer QuizYOGESH CHHAGANRAO MULEYNo ratings yet
- Programming API Overview and Concepts: System IDocument588 pagesProgramming API Overview and Concepts: System IJoseph MarreirosNo ratings yet
- Lecture 1 FloatingPointNumberSystemsDocument46 pagesLecture 1 FloatingPointNumberSystemsSaksham SharmaNo ratings yet
- Troubleshooting ProfibusDocument5 pagesTroubleshooting Profibussteam100deg8229No ratings yet
- Alienware 15 Review GuideDocument8 pagesAlienware 15 Review Guideatom tuxNo ratings yet
- Wireless Networking Lab ReportDocument13 pagesWireless Networking Lab ReportfathiwestNo ratings yet
- Implement Organization-Wide Policy for New ClinicDocument8 pagesImplement Organization-Wide Policy for New ClinicVo Minh Khanh (K14 HCM)100% (1)