Professional Documents
Culture Documents
Dashboard
Uploaded by
shreeshOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Dashboard
Uploaded by
shreeshCopyright:
Available Formats
0%
10%
20%
30%
40%
50%
60%
80%
90%
100%
70%
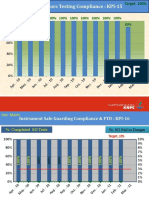
Information Security Policies
Organisation of information security
Human resources security
Halkyn Consulting Ltd
Asset management
www.halkynconsulting.co.uk
Access control
Cryptography
Physical and environmental security
Operations security
Communications security
System acquisition, development and…
Compliance Status - By Section
Supplier relationships
Information security incident management
Information security aspects of business…
Compliance
A.5 A.6 A.7 A.8 A.9 A.10 A.11 A.12 A.13 A.14 A.15 A.16 A.17 A.18
0%
10%
20%
30%
40%
50%
60%
70%
80%
90%
100%
Management direction for information security
Internal Organisation
Mobile devices and teleworking
Prior to employment
During employment
Termination and change of employment
Responibility for assets
Information classification
ISO27001:2013 Assessment Status
Media handling
Business requirements for access control
User access management
User responsibilities
System and application access control
Crypographic controls
Secure areas
Equipment
Operational procedures and responsibilities
Protection from malware
Backup
Logging and monitoring
Control of operational software
Technical vulnerability management
Information systems audit considerations
Network security management
Information transfer
Compliance Status - By Control
Security requirements of information systems
Security in development and support processes
Test data
Information security in supplier relationships
Supplier service delivery management
Management of infosec incidents &…
Information security continuity
Redundancies
Compliance with legal and contractual…
Information security reviews
info@halkynconsulting.co.uk
06-10-2023
You might also like
- ISO27001 2013 ComplianceChecklist UnprotectedDocument22 pagesISO27001 2013 ComplianceChecklist Unprotectedcuentacompartida988No ratings yet
- Security Value Map™: Next Generation Firewall (NGFW)Document1 pageSecurity Value Map™: Next Generation Firewall (NGFW)Xavi MilanNo ratings yet
- Jakarta Property Watch h2 2023 Market Update and 2024 Property Projections For ParticipantDocument65 pagesJakarta Property Watch h2 2023 Market Update and 2024 Property Projections For ParticipantAdri KhosasihNo ratings yet
- MDR Building Work Latest 31.may.2018Document9 pagesMDR Building Work Latest 31.may.2018Revan OlenNo ratings yet
- ISO27001:2013 Assessment StatusDocument23 pagesISO27001:2013 Assessment StatusAhmad YaseenNo ratings yet
- 13a Fy 22 Asylum Grant Rates by CourtDocument1 page13a Fy 22 Asylum Grant Rates by CourtJdf FdcvNo ratings yet
- Security Value Map™: Next Generation Firewall (NGFW)Document1 pageSecurity Value Map™: Next Generation Firewall (NGFW)Wagner MarlonNo ratings yet
- MDR (MK) - Bukit Asam Convention Hall JakabaringDocument6 pagesMDR (MK) - Bukit Asam Convention Hall JakabaringAdianto Rahman100% (3)
- DoradoVista Hydro Newsletter Profile PDFDocument1 pageDoradoVista Hydro Newsletter Profile PDFyared sitotawNo ratings yet
- Resources LoadingDocument2 pagesResources Loadingtotok.madriantolubisNo ratings yet
- Format Lap Dinding Uci BPPDocument1 pageFormat Lap Dinding Uci BPPChiyo NimNo ratings yet
- Curva S - E.P - N°1 - AvanceDocument1 pageCurva S - E.P - N°1 - AvanceMauricio Alonso Escalona ArayaNo ratings yet
- Pareto Analysis: Cumulative Percentage Cutoff: 80%Document4 pagesPareto Analysis: Cumulative Percentage Cutoff: 80%Nandha KumarNo ratings yet
- Difc22 Fintech Week Event ReportDocument46 pagesDifc22 Fintech Week Event ReportemergingtechsummitksaNo ratings yet
- Performance ContractDocument6 pagesPerformance Contractkapunza mbevyaNo ratings yet
- Data Economy Financial ServicesDocument1 pageData Economy Financial ServicescoloradoresourcesNo ratings yet
- Construciton PDFDocument1 pageConstruciton PDFElangkohNo ratings yet
- Curva S Loteo 25-03-24Document1 pageCurva S Loteo 25-03-24cjaraNo ratings yet
- ISO27001:2013 Assessment Status: Compliance Status - by SectionDocument21 pagesISO27001:2013 Assessment Status: Compliance Status - by SectionLakshya SadanaNo ratings yet
- Testing & Commisioning: Progress S-CurveDocument1 pageTesting & Commisioning: Progress S-CurveElangkohNo ratings yet
- EEN Audit Format Sample GuideDocument2 pagesEEN Audit Format Sample GuideDuane SchumacherNo ratings yet
- Comparing PM Certifications: Which Is Best For You?: by Stacy Goff, Ceo of Projectexperts UsaDocument9 pagesComparing PM Certifications: Which Is Best For You?: by Stacy Goff, Ceo of Projectexperts UsaDenis ValleNo ratings yet
- ISO27001 2013 ComplianceChecklistDocument21 pagesISO27001 2013 ComplianceChecklistDavid67% (3)
- Growth Policy Study: Draft Report 4/23/09: Appendix D - Sustainability Indicators (Resolution 16-376 F11) Mary DolanDocument13 pagesGrowth Policy Study: Draft Report 4/23/09: Appendix D - Sustainability Indicators (Resolution 16-376 F11) Mary DolanM-NCPPCNo ratings yet
- LED Driver IC Report - Abstract and Table of ContentsDocument7 pagesLED Driver IC Report - Abstract and Table of Contentsies837No ratings yet
- Dashboards Gauge Bullet HistoricalDocument1 pageDashboards Gauge Bullet HistoricalEriel Ramos-PizarroNo ratings yet
- ISO27001:2013 Assessment Status: Compliance Status - by SectionDocument19 pagesISO27001:2013 Assessment Status: Compliance Status - by SectionShraddha GawandNo ratings yet
- Growth Policy Study:: Appendix D - Sustainability Indicators (Resolution 16-376 F11) Mary DolanDocument16 pagesGrowth Policy Study:: Appendix D - Sustainability Indicators (Resolution 16-376 F11) Mary DolanM-NCPPCNo ratings yet
- Growth Policy StudyDocument16 pagesGrowth Policy StudyM-NCPPCNo ratings yet
- TimelineDocument28 pagesTimelinePavethraNo ratings yet
- Jeison Anillo: Technology in Logistics ManagementDocument2 pagesJeison Anillo: Technology in Logistics ManagementGinna BaronNo ratings yet
- Ukoug Original Software r12 Survey InfographicDocument1 pageUkoug Original Software r12 Survey InfographicChandra S JNo ratings yet
- Sample Overview ReportDocument1 pageSample Overview ReportNatsumamaNo ratings yet
- Curva S Presurizadora 25-03-24Document1 pageCurva S Presurizadora 25-03-24cjaraNo ratings yet
- 19DE0087 ECQ CorrectionDocument1 page19DE0087 ECQ CorrectionDerf Jayson AdanteNo ratings yet
- JunioDocument21 pagesJunioNELLY EVELYN CHURA QUISPENo ratings yet
- JulioDocument21 pagesJulioNELLY EVELYN CHURA QUISPENo ratings yet
- Wcms 546862-1Document12 pagesWcms 546862-1Marvin M. CandaNo ratings yet
- NTVQF Report - Upload PDFDocument206 pagesNTVQF Report - Upload PDFOsint TechNo ratings yet
- Online Advertising: Internet Trends 2019Document8 pagesOnline Advertising: Internet Trends 2019zizozeNo ratings yet
- Panel de Control de Curvas S..Document3 pagesPanel de Control de Curvas S..Xtian Martinez EscobedoNo ratings yet
- Axis BankDocument19 pagesAxis Bankathul jobyNo ratings yet
- Data 1Document8 pagesData 1Rohit RajNo ratings yet
- P and U-ChartDocument5 pagesP and U-ChartSeda ErsoyNo ratings yet
- Prueba de ColoresDocument1 pagePrueba de ColoresRICHARD GUERRANo ratings yet
- Proof Quality TestDocument1 pageProof Quality TestIvo KaraneshevNo ratings yet
- ITEP Business Sample Score Report UPWMAY2017Document3 pagesITEP Business Sample Score Report UPWMAY2017pelin100% (1)
- Dashboards Gauge Bullet Historical v2Document3 pagesDashboards Gauge Bullet Historical v2Eriel Ramos-PizarroNo ratings yet
- HSE Dashboard For Single SiteDocument2 pagesHSE Dashboard For Single SiteAngel Rivera CrespoNo ratings yet
- CS Alternative Energy YieldCosDocument32 pagesCS Alternative Energy YieldCosJonathan ChuahNo ratings yet
- Brit March DraftDocument2 pagesBrit March DraftzdwawdsfghhNo ratings yet
- Anfrek Tapak MenjanganDocument1 pageAnfrek Tapak MenjanganAkademik HimasdaNo ratings yet
- Materi Direktur Webinar Jetset TB (130520) FINALDocument6 pagesMateri Direktur Webinar Jetset TB (130520) FINALhariyanti hariNo ratings yet
- Why People Don't "Follow" ProceduresDocument19 pagesWhy People Don't "Follow" ProceduresDedy ChemistNo ratings yet
- Youtube Sample Insight PDFDocument7 pagesYoutube Sample Insight PDFNazifa KamalyNo ratings yet
- Pareto Chart On Decrease in SalesDocument2 pagesPareto Chart On Decrease in SalesMary KarmacharyaNo ratings yet
- Calculating Returns of A StockDocument4 pagesCalculating Returns of A StockShoummo RubaiyatNo ratings yet
- Real Time S & OP With APCC: Chandra Pandey - Director Supply ChainDocument43 pagesReal Time S & OP With APCC: Chandra Pandey - Director Supply ChainSanjeev ThakurNo ratings yet
- Economic DataWatch - EmploymentDocument6 pagesEconomic DataWatch - EmploymentandrewbloggerNo ratings yet
- D15 HIPAA Final Standard For Data Security in Plain EnglishDocument27 pagesD15 HIPAA Final Standard For Data Security in Plain Englishg478w34No ratings yet
- Canidium, A Leading Consultancy in Sales Process and Sales Performance Management, Is Officially SOC 2 Type 1 CertifiedDocument2 pagesCanidium, A Leading Consultancy in Sales Process and Sales Performance Management, Is Officially SOC 2 Type 1 CertifiedPR.comNo ratings yet
- ISO IEC 27005-2022-FineDocument70 pagesISO IEC 27005-2022-FineMinh Ttn100% (1)
- Chapter 1Document19 pagesChapter 1Garima MaharjanNo ratings yet
- Cissp NotesDocument83 pagesCissp NotesRobert Mota HawksNo ratings yet
- Security PDFDocument516 pagesSecurity PDFGeorge PhillasNo ratings yet
- Network Security: Henric Johnson Blekinge Institute of Technology, Sweden WWW - Its.bth - Se/staff/hjo/ Henric - Johnson@bth - SeDocument14 pagesNetwork Security: Henric Johnson Blekinge Institute of Technology, Sweden WWW - Its.bth - Se/staff/hjo/ Henric - Johnson@bth - SeRishika ChowdaryNo ratings yet
- Enterprise Standards For Information SecurityDocument5 pagesEnterprise Standards For Information SecurityAnonymouse CTFNo ratings yet
- Requirements Engineering: Foundation For Software Quality: Eric Knauss Michael GoedickeDocument304 pagesRequirements Engineering: Foundation For Software Quality: Eric Knauss Michael GoedickeBenhar Masahod BLM-VLOGNo ratings yet
- Autonomous Security Guard RobotDocument90 pagesAutonomous Security Guard Robotkeyurvachhani102No ratings yet
- CIA Triad (Confidentiality, Integrity and Availability)Document2 pagesCIA Triad (Confidentiality, Integrity and Availability)Misbah javedNo ratings yet
- Saas Public Cloud ServicesDocument8 pagesSaas Public Cloud ServicesjohnsonplouisNo ratings yet
- Term Paper Kamishetti Sharan 12107927 CSE423Document5 pagesTerm Paper Kamishetti Sharan 12107927 CSE423Kamishetti SharanNo ratings yet
- Classification Policy WorksheetDocument4 pagesClassification Policy WorksheetRadhikaNo ratings yet
- Security & Compliance Quick Reference GuideDocument27 pagesSecurity & Compliance Quick Reference GuideporongNo ratings yet
- Cyber Security Exam 2022Document20 pagesCyber Security Exam 2022Manjur AlamNo ratings yet
- Kirkuk Institute For Computer Science Information Security: Fourth StageDocument6 pagesKirkuk Institute For Computer Science Information Security: Fourth StageFarhad SalihNo ratings yet
- Chapter 2-6 Review QuestionsDocument176 pagesChapter 2-6 Review Questionsidk100% (5)
- 5 Ethical HackingDocument37 pages5 Ethical HackingNilaa RaghunathanNo ratings yet
- Lab3 - Information Systems Security Policy FWDocument5 pagesLab3 - Information Systems Security Policy FWS Teja Svi0% (2)
- Digital Identity Management: Enabling Innovation and Trust in The Internet EconomyDocument183 pagesDigital Identity Management: Enabling Innovation and Trust in The Internet EconomyErnane Luis PaixãoNo ratings yet
- Latest Research Papers On Database SecurityDocument4 pagesLatest Research Papers On Database Securityijsgpibkf100% (1)
- Chat ServerDocument14 pagesChat ServerKeshav KhannaNo ratings yet
- Security PoliciesDocument18 pagesSecurity PoliciesMichele VasconcellosNo ratings yet
- Sistem Perakaunan Berkomputer Standard Untuk Kerajaan Negeri (Speks) Information Security PoliciesDocument30 pagesSistem Perakaunan Berkomputer Standard Untuk Kerajaan Negeri (Speks) Information Security Policieshafis82No ratings yet
- An Assesment of Cyber Security Challenge in ArushaDocument98 pagesAn Assesment of Cyber Security Challenge in ArushaIsmail SettendaNo ratings yet
- Acceptable Use PolicyDocument8 pagesAcceptable Use PolicySammy ColeNo ratings yet
- How To Conduct A Risk AssessmentDocument23 pagesHow To Conduct A Risk Assessmentdurgasainath100% (1)
- Pecb Iso 38500 It Governance Manager Exam Preparation GuideDocument10 pagesPecb Iso 38500 It Governance Manager Exam Preparation GuideqassamiNo ratings yet
- SCP 11Document33 pagesSCP 11greenostrichNo ratings yet
- ChatGPT Side Hustles 2024 - Unlock the Digital Goldmine and Get AI Working for You Fast with More Than 85 Side Hustle Ideas to Boost Passive Income, Create New Cash Flow, and Get Ahead of the CurveFrom EverandChatGPT Side Hustles 2024 - Unlock the Digital Goldmine and Get AI Working for You Fast with More Than 85 Side Hustle Ideas to Boost Passive Income, Create New Cash Flow, and Get Ahead of the CurveNo ratings yet
- Microsoft Project 2019 For DummiesFrom EverandMicrosoft Project 2019 For DummiesRating: 5 out of 5 stars5/5 (1)
- ChatGPT Millionaire 2024 - Bot-Driven Side Hustles, Prompt Engineering Shortcut Secrets, and Automated Income Streams that Print Money While You Sleep. The Ultimate Beginner’s Guide for AI BusinessFrom EverandChatGPT Millionaire 2024 - Bot-Driven Side Hustles, Prompt Engineering Shortcut Secrets, and Automated Income Streams that Print Money While You Sleep. The Ultimate Beginner’s Guide for AI BusinessNo ratings yet
- Creating Online Courses with ChatGPT | A Step-by-Step Guide with Prompt TemplatesFrom EverandCreating Online Courses with ChatGPT | A Step-by-Step Guide with Prompt TemplatesRating: 4 out of 5 stars4/5 (4)
- Product Operations: How successful companies build better products at scaleFrom EverandProduct Operations: How successful companies build better products at scaleNo ratings yet
- Python for Beginners: A Crash Course Guide to Learn Python in 1 WeekFrom EverandPython for Beginners: A Crash Course Guide to Learn Python in 1 WeekRating: 4.5 out of 5 stars4.5/5 (7)
- Fundamentals of Data Engineering: Plan and Build Robust Data SystemsFrom EverandFundamentals of Data Engineering: Plan and Build Robust Data SystemsRating: 5 out of 5 stars5/5 (1)
- Excel for Beginners 2023: A Step-by-Step and Quick Reference Guide to Master the Fundamentals, Formulas, Functions, & Charts in Excel with Practical Examples | A Complete Excel Shortcuts Cheat SheetFrom EverandExcel for Beginners 2023: A Step-by-Step and Quick Reference Guide to Master the Fundamentals, Formulas, Functions, & Charts in Excel with Practical Examples | A Complete Excel Shortcuts Cheat SheetNo ratings yet
- Managing Humans: Biting and Humorous Tales of a Software Engineering ManagerFrom EverandManaging Humans: Biting and Humorous Tales of a Software Engineering ManagerRating: 4 out of 5 stars4/5 (90)
- Designing Data-Intensive Applications: The Big Ideas Behind Reliable, Scalable, and Maintainable SystemsFrom EverandDesigning Data-Intensive Applications: The Big Ideas Behind Reliable, Scalable, and Maintainable SystemsRating: 5 out of 5 stars5/5 (6)
- Excel Dynamic Arrays Straight to the Point 2nd EditionFrom EverandExcel Dynamic Arrays Straight to the Point 2nd EditionRating: 5 out of 5 stars5/5 (1)
- The Complete Business Process Handbook: Body of Knowledge from Process Modeling to BPM, Volume 1From EverandThe Complete Business Process Handbook: Body of Knowledge from Process Modeling to BPM, Volume 1Rating: 4.5 out of 5 stars4.5/5 (7)
- Microsoft Excel Guide for Success: Transform Your Work with Microsoft Excel, Unleash Formulas, Functions, and Charts to Optimize Tasks and Surpass Expectations [II EDITION]From EverandMicrosoft Excel Guide for Success: Transform Your Work with Microsoft Excel, Unleash Formulas, Functions, and Charts to Optimize Tasks and Surpass Expectations [II EDITION]Rating: 5 out of 5 stars5/5 (2)
- Microsoft OneNote Guide to Success: Learn In A Guided Way How To Take Digital Notes To Optimize Your Understanding, Tasks, And Projects, Surprising Your Colleagues And ClientsFrom EverandMicrosoft OneNote Guide to Success: Learn In A Guided Way How To Take Digital Notes To Optimize Your Understanding, Tasks, And Projects, Surprising Your Colleagues And ClientsRating: 5 out of 5 stars5/5 (2)
- Microsoft Teams Guide for Success: Mastering Communication, Collaboration, and Virtual Meetings with Colleagues & ClientsFrom EverandMicrosoft Teams Guide for Success: Mastering Communication, Collaboration, and Virtual Meetings with Colleagues & ClientsRating: 5 out of 5 stars5/5 (2)
- The Non-Technical Founder: How a 16-Year Old Built a Six Figure Software Company Without Writing Any CodeFrom EverandThe Non-Technical Founder: How a 16-Year Old Built a Six Figure Software Company Without Writing Any CodeRating: 4 out of 5 stars4/5 (1)
- Design and Build Modern Datacentres, A to Z practical guideFrom EverandDesign and Build Modern Datacentres, A to Z practical guideRating: 3 out of 5 stars3/5 (2)
- Microsoft Word Guide for Success: From Basics to Brilliance in Achieving Faster and Smarter Results [II EDITION]From EverandMicrosoft Word Guide for Success: From Basics to Brilliance in Achieving Faster and Smarter Results [II EDITION]Rating: 5 out of 5 stars5/5 (2)
- Microsoft PowerPoint Guide for Success: Learn in a Guided Way to Create, Edit & Format Your Presentations Documents to Visual Explain Your Projects & Surprise Your Bosses And Colleagues | Big Four Consulting Firms MethodFrom EverandMicrosoft PowerPoint Guide for Success: Learn in a Guided Way to Create, Edit & Format Your Presentations Documents to Visual Explain Your Projects & Surprise Your Bosses And Colleagues | Big Four Consulting Firms MethodRating: 5 out of 5 stars5/5 (2)
- Learn Power BI: A beginner's guide to developing interactive business intelligence solutions using Microsoft Power BIFrom EverandLearn Power BI: A beginner's guide to developing interactive business intelligence solutions using Microsoft Power BIRating: 5 out of 5 stars5/5 (1)
- Microsoft Outlook Guide to Success: Learn Smart Email Practices and Calendar Management for a Smooth Workflow [II EDITION]From EverandMicrosoft Outlook Guide to Success: Learn Smart Email Practices and Calendar Management for a Smooth Workflow [II EDITION]Rating: 5 out of 5 stars5/5 (2)
- Change Management for Beginners: Understanding Change Processes and Actively Shaping ThemFrom EverandChange Management for Beginners: Understanding Change Processes and Actively Shaping ThemRating: 4.5 out of 5 stars4.5/5 (3)
- Optimizing DAX: Improving DAX performance in Microsoft Power BI and Analysis ServicesFrom EverandOptimizing DAX: Improving DAX performance in Microsoft Power BI and Analysis ServicesNo ratings yet


































































































![Microsoft Excel Guide for Success: Transform Your Work with Microsoft Excel, Unleash Formulas, Functions, and Charts to Optimize Tasks and Surpass Expectations [II EDITION]](https://imgv2-1-f.scribdassets.com/img/audiobook_square_badge/728318885/198x198/86d097382f/1714821849?v=1)



![Microsoft Word Guide for Success: From Basics to Brilliance in Achieving Faster and Smarter Results [II EDITION]](https://imgv2-2-f.scribdassets.com/img/audiobook_square_badge/728320756/198x198/6f19793d5e/1714821714?v=1)




![Microsoft Outlook Guide to Success: Learn Smart Email Practices and Calendar Management for a Smooth Workflow [II EDITION]](https://imgv2-1-f.scribdassets.com/img/audiobook_square_badge/728320983/198x198/d544db3174/1714821660?v=1)