Professional Documents
Culture Documents
4 Cryptography
Uploaded by
omarnader160 ratings0% found this document useful (0 votes)
4 views1 pageCryptography deals with protecting and preserving information. It involves encryption to manipulate and protect information, and cryptanalysis to uncover secrets that others try to hide. The main goals of cryptography nowadays are confidentiality, integrity, authentication, non-repudiation, and key distribution. Cryptography uses encryption to convert plain text into cipher text and decryption to convert cipher text back into plain text.
Original Description:
Original Title
4-Cryptography
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCryptography deals with protecting and preserving information. It involves encryption to manipulate and protect information, and cryptanalysis to uncover secrets that others try to hide. The main goals of cryptography nowadays are confidentiality, integrity, authentication, non-repudiation, and key distribution. Cryptography uses encryption to convert plain text into cipher text and decryption to convert cipher text back into plain text.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
4 views1 page4 Cryptography
Uploaded by
omarnader16Cryptography deals with protecting and preserving information. It involves encryption to manipulate and protect information, and cryptanalysis to uncover secrets that others try to hide. The main goals of cryptography nowadays are confidentiality, integrity, authentication, non-repudiation, and key distribution. Cryptography uses encryption to convert plain text into cipher text and decryption to convert cipher text back into plain text.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 1
Cryptography deals with protection and
preservation of information in all its forms.
In cryptography field, encryption gets the
Early Applications and most attention for manipulating and
Examples protecting information
deals with unlocking or uncovering the
cryptanalysis secrets that others try so hard to hide
or obscure
اللي جي ده حصة تاريخ فمعلش استحمل شويه
The intricate patterns and glyphs used in
Egyptian hieroglyphics
الرموز المعقده المستخدمه في الهيلغروفيه المصريه
The ancient Egyptians were probably using
the system not so much to withhold secrets
but because they wanted a special writing
system to commune with their gods and
eternity.
لم يكونوا يستخدموه لحفظ األسرار بقدر ما كانوا يستخدموه في
التواصل مع الهتهم
It is believed that only members of the royal
family and the religious orders could fully
understand how to read and write the system
History of Cryptography and comprehend it fully.
the writing system became more complex;
eventually the public and those who could
write the language either passed away or
turned their interests to other endeavors, and
the ability to decipher the symbols was lost
for a time.
نظام الكتابه كان معقد فاللي كانوا بيعرفوا يكتبوا يا إما ماتوا أو
حولوا اهتمامتهم لشيء اخر
The Rosetta stone حجر رشيدwas the key that
allowed modern civilization to
understand a language that was
nearly lost
it took over 20 years of concerted effort to
reveal the language to the world once again.
One of the most widely used applications of
cryptography is in the safeguarding of
communications between two parties
wanting to share information.
من أهم الحاجات اللي بنستخدم فيها التشفير هي إننا نحافظ علي
التواصل بين طرفيين عشان يكون امن ومحدش يطلع علي الرسائل
In today’s world, not only must information
be kept secret, but provisions to detect
unwelcome or unwanted modifications are
Tracing the Evolution just as important.
في العصر الحالي مش بهتم بس بعدم قدرة طرف تاني علي قرايتها
بل برده باهتم بانه ميقدرش يعدلها
Is the body of knowledge relating to
in the first few generations of its existence,
cryptography concerned only with
the answer was yes, but that has changed
protecting information?
لو بنتكلم في األول فاالجابة اه لكن دلوقتي الموضوع اتغير
هل المعرفه بالتشفير مهتمه بس بالحمايه بتاعت البيانات؟
It is the primary goal that encryption seeks
to achieve.
Confidentiality Encryption is done to keep secret
information from disclosure, away from
prying eyes.
الغرض األساسي للتشفيرأصال هو أن المعلومات تبقي بعيده عن
أعين المتطفلين
Cryptography can detect changes in
Integrity information and thus prove its integrity or
original unmodified state.
Cryptography allows a person, object,
or party to be identified with a high
degree
Goals cryptography nowadays of confidence.
Authentication
seek to achieve Authentication is an essential component of
a secure system because it allows
software and other things to be positively
identified.
The ability to provide positive identification
of the source or originator of an
Nonrepudiation - عدم التنصل event is an important part of security
باختصار بيخليني أقدر أعرف مين عمل ايه عشان بعدين ميقدرش
يتنصل ويقول إنه معملش
One of the most valuable components of a
cryptosystem is the key, which is the
Key Distribution specific secret combination or code used
in a cryptographic function.
Plain text is the original message.
Plain Text/Clear Text it is the usable information.
It has not been altered
Cipher text is the opposite of plain text
it is a message or other data that has
Cipher Text been
transformed into a different format using a
mechanism known as an algorithm.
It is also something that can be reversed
using an algorithm and a key
بمعني إني لو معايا األلجوريزم والمفتاح أقدر أرجعها تاني ل
Cryptography How Does It Work?
plain text
transform clear text into cipher text.
Algorithms a formula that includes discrete steps that
describe how the encryption and decryption
process is to be performed in a given
instance.
A key is a discrete piece of information,
usually random in nature, that determines
the result or output of a given cryptographic
operation.
Keys It can be thought of in the same way a key in
the physical world is, as a special item used
to open or unlock something—in this case, a
piece of information.
هو شبه المفتاح في العالم الحقيقي زي ما األول بيستخدم في فتح
حاجه معينه ده هو الطريقه لفهم جزء من المعلومات عن طريق
تحويله مع األلجوريزم منcipher text to plain text
The Same key is used for both encryption
and decryption and must be kept secret
Preserving confidentiality
Increased speed over many non-
symmetric systems
symmetric algorithms are great at all of the
symmetric
following (advatages):
Ensuring simplicity (relatively speaking,
of course)
Providing authenticity
Key management issues
Symmetric algorithms have drawbacks in
these areas:
Lack of nonrepudiation features
عدم وجود ميزات عدم التنصل
The concept of public key cryptography
was intended to overcome the key
management problems inherent in
symmetric systems.
Types of cryptography
In this system, each user who is enrolled
receives a pair of keys called the public
key and the private key.
Each person’s public key is published,
whereas the private key is kept secret.
How it works
By creating the keys this way, the need
for a shared symmetric key is eliminated.
This option also secures the
communication against eavesdropping
التنصتor betrayal.الخيانة
asymmetric (aka public-key cryptography)
this system of generating keys provides
a means of nonrepudiation that is not
possible with symmetric systems.
Since anything encrypted with the
private key can be reversed only with the
corresponding public key and only one
Digital Signature person holds the private key, then the
identity of the encrypting party can be
assured
Hashing can be considered a type of one-
way encryption.
it is a process that creates a scrambled
output that cannot be reversed.
The process outputs is a hash value, or
message digest. (ex: Passwords storage)
Designed to be a one-way process, hashing
is commonly used to validate the integrity of
information.
بيحافظ علي البيانات بإنها ال يتم تعديلها أو التالعب بيها
hashing شخص عمل ملف كاتب فيه حاجات وعمله: مثال
عشان اللي استلم الملف يتأكد إن الملف ما اتعدلش المفروض
Understanding Hashing يتبعتله مع الملف الhashing function and hashing
value
Hashing function هو المفروض يطبق ال
لو طلعتله نفس الHashing value
اللي مبعوته ده معناها الملف لم يتم التعديل عليه وكده يبقي تمام لو
طلعت حاجه مغايره هيبقي معناها إن في حد لعب في الملف
A hash function generates a fixed-length
value that is always the same length no
matter how large or small the data entering
the process or algorithm is.
The fixed-length value is unique for every
different input that enters the process. It is
because of this unique property and its
behavior that hashes are used to detect the
changes that can happen
in data of any type.
Cryptographic systems are all vulnerable to
what is known as a brute-force attack.
In brute-force attack, every possible
combination of characters is tried in an
attempt to uncover a valid key.
باختصار المشكله إن كل التكنيكات دي متقدرش توقف الbtute-
Issues with Cryptography force attack
You might also like
- C++20 STL Cookbook - Leverage The Latest Features of The STL To Solve Real-World ProblemsDocument450 pagesC++20 STL Cookbook - Leverage The Latest Features of The STL To Solve Real-World ProblemsPramod BhatNo ratings yet
- Unit 19 - Assignment Brief 1 - Huynh Nhat Nam-Môn DATA AND ALGORITHMSDocument27 pagesUnit 19 - Assignment Brief 1 - Huynh Nhat Nam-Môn DATA AND ALGORITHMSHuynh Nhat Nam (FGW HCM)100% (1)
- Image Steganography: B. Yellamma K. Kanaka Durga Iii Ece Iii EceDocument11 pagesImage Steganography: B. Yellamma K. Kanaka Durga Iii Ece Iii EceSrushith RepakulaNo ratings yet
- Cs201 Grand QuizDocument8 pagesCs201 Grand Quiznew historyNo ratings yet
- Cipher Methods FinalDocument21 pagesCipher Methods FinalE.J. PelayoNo ratings yet
- Introduction To Cryptography: Marcus K. G. AdomeyDocument52 pagesIntroduction To Cryptography: Marcus K. G. Adomeysaurabh sirohiNo ratings yet
- Espionage 120131090711 Phpapp02Document19 pagesEspionage 120131090711 Phpapp02Anonymous GvUjV5GtirNo ratings yet
- Steganography: (A New Technique To Hide Information Within Image File)Document35 pagesSteganography: (A New Technique To Hide Information Within Image File)Präshäñt Kälē PätîlNo ratings yet
- Cryptology for Beginners #1 Guide for Security, Encryption, Crypto, Algorithms and PythonFrom EverandCryptology for Beginners #1 Guide for Security, Encryption, Crypto, Algorithms and PythonNo ratings yet
- The Whisper Network: You SettleDocument12 pagesThe Whisper Network: You SettleJay VeeNo ratings yet
- Introduction To SteganographyDocument24 pagesIntroduction To Steganographydukerex100% (1)
- Cryptography: Presented byDocument11 pagesCryptography: Presented byapi-19799369No ratings yet
- Cryptography and Network Security: Dr. R.K.MugelanDocument52 pagesCryptography and Network Security: Dr. R.K.Mugelanbabloo veluvoluNo ratings yet
- Week 1Document37 pagesWeek 1Nina SyNo ratings yet
- Unit - 1: Cryptography & Network SecurityDocument236 pagesUnit - 1: Cryptography & Network SecuritycrayonNo ratings yet
- Major Doc Fine1Document75 pagesMajor Doc Fine1Anil SagarNo ratings yet
- SecurityDocument5 pagesSecuritymai elsayedNo ratings yet
- Secure E-Commerce: Understanding The Public Key Cryptography Jigsaw PuzzleDocument9 pagesSecure E-Commerce: Understanding The Public Key Cryptography Jigsaw PuzzlesbNo ratings yet
- Ethics Lect4 CryptographyDocument15 pagesEthics Lect4 Cryptographyomarnader16No ratings yet
- Cryptography TutorialDocument12 pagesCryptography TutorialamarkalsyNo ratings yet
- Ellenziliak 2017Document2 pagesEllenziliak 2017Jorge VegaNo ratings yet
- Secret Writing and Is Thus The Art of Hiding Messages InsideDocument44 pagesSecret Writing and Is Thus The Art of Hiding Messages InsideDebasish Sahoo100% (6)
- CSEIT1831159Document7 pagesCSEIT1831159Hasain AhmedNo ratings yet
- A Brief History of CryptographyDocument2 pagesA Brief History of Cryptographycmilleret74No ratings yet
- Paper Presentation On Network Security & Cryptography: Aditya Engineering CollegeDocument6 pagesPaper Presentation On Network Security & Cryptography: Aditya Engineering CollegeSujit SeelaNo ratings yet
- SETR 03: CryptographyDocument11 pagesSETR 03: CryptographyHoover InstitutionNo ratings yet
- Overview of Cryptography: SSRN Electronic Journal January 2011Document10 pagesOverview of Cryptography: SSRN Electronic Journal January 2011EbubeNo ratings yet
- A Cypherpunk'S Manifesto: Eric HughesDocument12 pagesA Cypherpunk'S Manifesto: Eric Hughesdeni fortranNo ratings yet
- CSC-308 M4 StudentsDocument29 pagesCSC-308 M4 Studentsjonnel talañaNo ratings yet
- Cryptographic Services To Enforce Secure Messaging and Data StorageDocument4 pagesCryptographic Services To Enforce Secure Messaging and Data StorageInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Chapter 2 - Elementary CryptographyDocument91 pagesChapter 2 - Elementary Cryptographypraveenembd1No ratings yet
- SohaiDocument16 pagesSohaiJHON ANDREI SEMANo ratings yet
- Purple Pink Trendy Cyber Y2K Creative PresentationDocument9 pagesPurple Pink Trendy Cyber Y2K Creative Presentationmathiasguaman12No ratings yet
- Cryptography: Essay 15Document36 pagesCryptography: Essay 15Dhairav PatelNo ratings yet
- Fubswrorjb: Teri Schmidt Matt Rose K-12 OutreachDocument13 pagesFubswrorjb: Teri Schmidt Matt Rose K-12 Outreachraji rajeshNo ratings yet
- Secure Data Communication and Cryptography Based On DNA Based Message EncodingDocument6 pagesSecure Data Communication and Cryptography Based On DNA Based Message EncodingHaroonRashidNo ratings yet
- Cryptography Comes From Greek Word Kryptos, MeaningDocument33 pagesCryptography Comes From Greek Word Kryptos, Meaningraunakbajoria75% (8)
- Cryptography: Hiding The WordDocument18 pagesCryptography: Hiding The WordNiharika BundelaNo ratings yet
- Cse CryptographyDocument19 pagesCse Cryptographytejas it do d he got f foods manchiNo ratings yet
- Secure Data Transfer Over The Internet Using Image CryptosteganographyDocument8 pagesSecure Data Transfer Over The Internet Using Image CryptosteganographyTrịnh Văn ThoạiNo ratings yet
- IS AssignmentDocument24 pagesIS Assignmentyuvanpgr-wm20No ratings yet
- The Basics of Cryptography: Encryption and DecryptionDocument5 pagesThe Basics of Cryptography: Encryption and DecryptionAngelyn BlanquiscoNo ratings yet
- Cryptography Term PaperDocument4 pagesCryptography Term PaperAngelica AngelesNo ratings yet
- Multilevel Cryptography Technique Using Graceful CodesDocument5 pagesMultilevel Cryptography Technique Using Graceful CodesAnthony LiangNo ratings yet
- CryptologyDocument5 pagesCryptologywejtyNo ratings yet
- LESSON 6 - CryptographyDocument12 pagesLESSON 6 - CryptographyKIBENo ratings yet
- Chapter Four Security Techniques Origin of CryptographyDocument33 pagesChapter Four Security Techniques Origin of CryptographyGetnete degemuNo ratings yet
- Assignment Css 4Document5 pagesAssignment Css 4mordche.dayvianNo ratings yet
- Cryptography and Network SecurityDocument24 pagesCryptography and Network SecurityRyan SarmientoNo ratings yet
- Securing Information: Cryptography and SteganographyDocument5 pagesSecuring Information: Cryptography and SteganographyNull PointerNo ratings yet
- 1.1 What Is Steganography?Document2 pages1.1 What Is Steganography?Shalki NareshNo ratings yet
- A Survey On Various Cryptography TechniquesDocument7 pagesA Survey On Various Cryptography TechniquesDNo ratings yet
- Cse CryptographyDocument19 pagesCse CryptographyunknownNo ratings yet
- ch02 ElementaryEncryption 2fDocument83 pagesch02 ElementaryEncryption 2fpraveenembd1No ratings yet
- Data Hiding Using Video Steganography - A SurveyDocument8 pagesData Hiding Using Video Steganography - A SurveySwetha AmmukuttyNo ratings yet
- Stego LRDocument8 pagesStego LRSimdie OnuoraNo ratings yet
- EncryptionstDocument41 pagesEncryptionstSamer SamaraNo ratings yet
- Cryptography & Information SecurityDocument7 pagesCryptography & Information SecurityragunathrevNo ratings yet
- Module 5 CryptographyDocument14 pagesModule 5 CryptographyCIELICA BURCANo ratings yet
- Cryptography ReportDocument16 pagesCryptography ReportGRACENo ratings yet
- What Does It Mean For A Language Model To Preserve Privacy?: Hannah Brown Katherine Lee Fatemehsadat MireshghallahDocument13 pagesWhat Does It Mean For A Language Model To Preserve Privacy?: Hannah Brown Katherine Lee Fatemehsadat Mireshghallahsunshinenicole11No ratings yet
- Ethics Lect1 IntroductionDocument11 pagesEthics Lect1 Introductionomarnader16No ratings yet
- Ethics Lect5 MalwareDocument18 pagesEthics Lect5 Malwareomarnader16No ratings yet
- Ethics Lect4 CryptographyDocument15 pagesEthics Lect4 Cryptographyomarnader16No ratings yet
- NW Lec 6Document28 pagesNW Lec 6omarnader16No ratings yet
- COMP600 Spring Lab#2Document7 pagesCOMP600 Spring Lab#2jassica sahiNo ratings yet
- CHAZELLEDocument20 pagesCHAZELLETomiro YisajorNo ratings yet
- Rida MumtazDocument26 pagesRida Mumtazsatyam sharmaNo ratings yet
- Solutions For QAHO1002110Document3 pagesSolutions For QAHO1002110Mark LucasNo ratings yet
- Incremental Compilation in The Vcs EnvironmentDocument6 pagesIncremental Compilation in The Vcs EnvironmentKeyur MahantNo ratings yet
- Rust Cheat SheetDocument80 pagesRust Cheat SheetSean FlanderhijnNo ratings yet
- ENDORSEMENT LETTER Ojt 2022Document2 pagesENDORSEMENT LETTER Ojt 2022Jam MaribojocNo ratings yet
- Iteraivos 2020-IDocument49 pagesIteraivos 2020-Iluis diazNo ratings yet
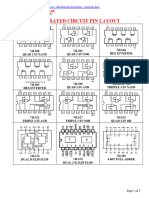
- IcpinoutDocument3 pagesIcpinouthakyNo ratings yet
- History: History of Compiler ConstructionDocument4 pagesHistory: History of Compiler ConstructionShyamSunderDadhichNo ratings yet
- Access 2 ExcelDocument4 pagesAccess 2 ExcelPanji Ryan WidhiNo ratings yet
- "Page Replacement Algorithms": - A-28 Manasi Dhote A-32 Akshat Gandhi A-63 Dhruv MistryDocument18 pages"Page Replacement Algorithms": - A-28 Manasi Dhote A-32 Akshat Gandhi A-63 Dhruv MistryManasiNo ratings yet
- Algorithm-Complexity ReviewerDocument6 pagesAlgorithm-Complexity ReviewerJonathan BregenteNo ratings yet
- Cse Programming For Problem Solving Lecture NotesDocument185 pagesCse Programming For Problem Solving Lecture NotesTAMMISETTY VIJAY KUMARNo ratings yet
- Data Structures and Algorithms CodeDocument4 pagesData Structures and Algorithms CodePavan KoutharapuNo ratings yet
- 15ECSC701 - 576 - KLE47-15Ecsc701-set1 Cse PaperDocument5 pages15ECSC701 - 576 - KLE47-15Ecsc701-set1 Cse PaperAniket AmbekarNo ratings yet
- Mix0 Bimodal No No No No Lru 8coreDocument12 pagesMix0 Bimodal No No No No Lru 8coreimcpNo ratings yet
- Infix To Postfix ConversionDocument3 pagesInfix To Postfix ConversionsaravananaecNo ratings yet
- In-Place Sorting and Not-In-Place SortingDocument23 pagesIn-Place Sorting and Not-In-Place SortingLeary John TambagahanNo ratings yet
- Computer Science - Bits and BytesDocument19 pagesComputer Science - Bits and Byteswhois glaNo ratings yet
- Compiler DesignDocument4 pagesCompiler DesignSanidhya JadaunNo ratings yet
- Design and Implementation of A Centralized University Result Processing and TranscriptSystem Case Study of University of IbadanDocument13 pagesDesign and Implementation of A Centralized University Result Processing and TranscriptSystem Case Study of University of Ibadanchisom aneneNo ratings yet
- TXTBK - C++ - Intermediate Gems - 4.7Document275 pagesTXTBK - C++ - Intermediate Gems - 4.7NedelcuNo ratings yet
- DMS Question Bank (Cse It Aids)Document11 pagesDMS Question Bank (Cse It Aids)S AdilakshmiNo ratings yet
- DSA SyllabusDocument4 pagesDSA SyllabusKasani Tirumala tejaNo ratings yet
- DMS - Imp Questions - VTU ExamDocument10 pagesDMS - Imp Questions - VTU ExamAnser PashaNo ratings yet
- C-Robot Simulator: Program StructureDocument17 pagesC-Robot Simulator: Program StructureAyessa Karyl GanirNo ratings yet