Professional Documents
Culture Documents
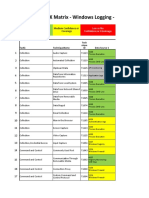
ATTCK Matrix For Enterprise
ATTCK Matrix For Enterprise
Uploaded by
Nuryadin Usman Abdurrahim AsSampiti IIOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
ATTCK Matrix For Enterprise
ATTCK Matrix For Enterprise
Uploaded by
Nuryadin Usman Abdurrahim AsSampiti IICopyright:
Available Formats
ATT&CK Matrix for Enterprise
ID: TA0040 Impact ID: TA0043 Reconnaissance
T1529 - System Shutdown/Reboot T1531 - Account Access Removal T1594 - Search Victim-Owned Websites T1595 - Active Scanning
T1489 - Service Stop T1485 - Data Destruction T1593 - Search Open Websites/Domains Scanning IP Blocks
T1496 - Resource Hijacking T1486 - Data Encrypted for Impact Social Media Vulnerability Scanning
T1498 - Network Denial of Service T1565 - Data Manipulation Search Engines Wordlist Scanning
Direct Network Flood Stored Data Manipulation Code Repositories T1592 - Gather Victim Host Information
Reflection Amplification Transmitted Data Manipulation T1596 - Search Open Technical Databases Hardware
13 Techniques
T1490 - Inhibit System Recovery Runtime Data Manipulation DNS/Passive DNS Software
T1495 - Firmware Corruption T1491 - Defacement WHOIS Firmware
The adversary is trying to manipulate,
interrupt, or destroy your systems and data. Internal Defacement Digital Certificates Client Configurations 10 Techniques
External Defacement CDNs T1589 - Gather Victim Identity Information
The adversary is trying to
T1561 - Disk Wipe Scan Databases Credentials
gather information they
Disk Content Wipe T1597 - Search Closed Sources Email Addresses
can use to plan future
Disk Structure Wipe Threat Intel Vendors Employee Names operations.
T1499 - Endpoint Denial of Service Purchase Technical Data T1590 - Gather Victim Network Information
OS Exhaustion Flood T1598 - Phishing for Information Domain Properties
Service Exhaustion Flood Spearphishing Service DNS
Application Exhaustion Flood Spearphishing Attachment Network Trust Dependencies
Application or System Exploitation Spearphishing Link Network Topology
IP Addresses
ID: TA0010 Exfiltration Network Security Appliances
T1537 - Transfer Data to Cloud Account T1020 - Automated Exfiltration T1591 - Gather Victim Org Information
T1029 - Scheduled Transfer Traffic Duplication Determine Physical Locations
9 Techniques T1567 - Exfiltration Over Web Service T1030 - Data Transfer Size Limits Business Relationships
Exfiltration to Code Repository T1048 - Exfiltration Over Alternative Protocol Identify Business Tempo
The adversary is trying to steal data. Identify Roles
Exfiltration to Cloud Storage Exfiltration Over Symmetric Encrypted Non-C2 Protocol
T1052 - Exfiltration Over Physical Medium Exfiltration Over Asymmetric Encrypted Non-C2 Protocol
Exfiltration over USB Exfiltration Over Unencrypted Non-C2 Protocol
ID: TA0042 Resource Development
T1041 - Exfiltration Over C2 Channel T1608 - Stage Capabilities T1583 - Acquire Infrastructure
T1011 - Exfiltration Over Other Network Medium Upload Malware Domains
Exfiltration Over Bluetooth Upload Tool DNS Server
Install Digital Certificate Virtual Private Server
ID: TA0011 Command and Control Drive-by Target Server
Dead Drop Resolver T1071 - Application Layer Protocol Link Target Botnet
Bidirectional Communication T1102 - Web Service Web Protocols SEO Poisoning Web Services
One-Way Communication File Transfer Protocols T1588 - Obtain Capabilities Serverless
T1205 - Traffic Signaling Mail Protocols Malware T1586 - Compromise Accounts
Port Knocking DNS Tool Social Media Accounts 7 Techniques
Socket Filters T1092 - Communication Through Removable Media Code Signing Certificates Email Accounts
T1219 - Remote Access Software Digital Certificates Cloud Accounts The adversary is trying to establish resources they can
T1132 - Data Encoding
use to support operations.
T1090 - Proxy Standard Encoding Exploits T1584 - Compromise Infrastructure
16 Techniques Internal Proxy Vulnerabilities Domains
Non-Standard Encoding
External Proxy T1001 - Data Obfuscation T1585 - Establish Accounts DNS Server
The adversary is trying to communicate with
compromised systems to control them. Multi-hop Proxy Junk Data Social Media Accounts Virtual Private Server
Domain Fronting Steganography Email Accounts Server
T1572 - Protocol Tunneling Protocol Impersonation Cloud Accounts Botnet
T1571 - Non-Standard Port T1568 - Dynamic Resolution Web Services
T1095 - Non-Application Layer Protocol Fast Flux DNS Serverless
T1104 - Multi-Stage Channels Domain Generation Algorithms T1587 - Develop Capabilities
DNS Calculation Malware
T1573 - Encrypted Channel Code Signing Certificates
Symmetric Cryptography Digital Certificates
Asymmetric Cryptography Exploits
T1008 - Fallback Channels
T1105 - Ingress Tool Transfer
ID: TA0001 Initial Access
T1078 - Valid Accounts T1189 - Drive-by Compromise
ID: TA0009 Collection Default Accounts T1190 - Exploit Public-Facing Application
T1125 - Video Capture T1557 - Adversary-in-the-Middle Domain Accounts T1133 - External Remote Services
9 Techniques
T1113 - Screen Capture LLMNR/NBT-NS Poisoning and SMB Relay Local Accounts T1200 - Hardware Additions
T1056 - Input Capture ARP Cache Poisoning Cloud Accounts T1566 - Phishing The adversary is trying to get into your network.
Keylogging DHCP Spoofing T1199 - Trusted Relationship Spearphishing Attachment
GUI Input Capture T1560 - Archive Collected Data T1195 - Supply Chain Compromise Spearphishing Link
Web Portal Capture Archive via Utility Compromise Software Dependencies and Development Tools Spearphishing via Service
Credential API Hooking Archive via Library Compromise Software Supply Chain
17 Techniques Compromise Hardware Supply Chain
T1114 - Email Collection Archive via Custom Method
Local Email Collection T1123 - Audio Capture T1091 - Replication Through Removable Media
The adversary is trying to gather data of interest to
their goal. Remote Email Collection T1119 - Automated Collection
Email Forwarding Rule T1185 - Browser Session Hijacking
ID: TA0002 Execution
T1074 - Data Staged T1115 - Clipboard Data T1047 - Windows Management Instrumentation T1059 - Command and Scripting Interpreter
Local Data Staging T1530 - Data from Cloud Storage T1204 - User Execution PowerShell
Remote Data Staging T1602 - Data from Configuration Repository Malicious Link AppleScript
T1025 - Data from Removable Media SNMP (MIB Dump) Malicious File Windows Command Shell
T1039 - Data from Network Shared Drive Network Device Configuration Dump Malicious Image Unix Shell
T1005 - Data from Local System T1213 - Data from Information Repositories T1569 - System Services Visual Basic
Confluence Launchctl Python
Sharepoint Service Execution JavaScript
Code Repositories T1072 - Software Deployment Tools Network Device CLI
13 Techniques
T1129 - Shared Modules T1609 - Container Administration Command
ID: TA0008 Lateral Movement T1648 - Serverless Execution T1610 - Deploy Container The adversary is trying to run malicious code.
T1550 - Use Alternate Authentication Material T1210 - Exploitation of Remote Services T1203 - Exploitation for Client Execution
Application Access Token T1534 - Internal Spearphishing T1559 - Inter-Process Communication
Pass the Hash T1570 - Lateral Tool Transfer Component Object Model
Pass the Ticket T1563 - Remote Service Session Hijacking Dynamic Data Exchange
9 Techniques
Web Session Cookie SSH Hijacking XPC Services
The adversary is trying to move through your T1080 - Taint Shared Content RDP Hijacking T1106 - Native API
environment.
T1072 - Software Deployment Tools T1021 - Remote Services T1053 - Scheduled Task/Job
T1091 - Replication Through Removable Media Remote Desktop Protocol At
SMB/Windows Admin Shares Cron
Distributed Component Object Model Scheduled Task
SSH Systemd Timers
VNC Container Orchestration Job
Windows Remote Management
ID: TA0003 Persistence
ID: TA0007 Discovery T1078 - Valid Accounts T1098 - Account Manipulation
T1497 - Virtualization/Sandbox Evasion T1087 - Account Discovery Default Accounts Additional Cloud Credentials
System Checks Local Account Domain Accounts Additional Email Delegate Permissions
User Activity Based Checks Domain Account Local Accounts Additional Cloud Roles
Time Based Evasion Email Account Cloud Accounts SSH Authorized Keys
T1124 - System Time Discovery Cloud Account T1205 - Traffic Signaling Device Registration
T1007 - System Service Discovery T1010 - Application Window Discovery Port Knocking T1197 - BITS Jobs
T1033 - System Owner/User Discovery T1217 - Browser Bookmark Discovery Socket Filters T1547 - Boot or Logon Autostart Execution
T1049 - System Network Connections Discovery T1580 - Cloud Infrastructure Discovery T1505 - Server Software Component Registry Run Keys / Startup Folder
T1016 - System Network Configuration Discovery T1538 - Cloud Service Dashboard SQL Stored Procedures Authentication Package
30 Techniques Transport Agent Time Providers
Internet Connection Discovery T1526 - Cloud Service Discovery
T1614 - System Location Discovery T1619 - Cloud Storage Object Discovery Web Shell Winlogon Helper DLL
The adversary is trying to figure out your
System Language Discovery T1613 - Container and Resource Discovery IIS Components Security Support Provider
environment.
T1082 - System Information Discovery T1622 - Debugger Evasion Terminal Services DLL Kernel Modules and Extensions
T1518 - Software Discovery T1482 - Domain Trust Discovery T1053 - Scheduled Task/Job Re-opened Applications
Security Software Discovery T1083 - File and Directory Discovery At LSASS Driver
T1018 - Remote System Discovery T1615 - Group Policy Discovery Cron Shortcut Modification
T1012 - Query Registry T1046 - Network Service Discovery Scheduled Task Port Monitors
T1057 - Process Discovery T1135 - Network Share Discovery Systemd Timers Print Processors
T1069 - Permission Groups Discovery T1040 - Network Sniffing Container Orchestration Job XDG Autostart Entries
Local Groups T1542 - Pre-OS Boot Active Setup
Domain Groups System Firmware Login Items
Cloud Groups Component Firmware T1037 - Boot or Logon Initialization Scripts
T1120 - Peripheral Device Discovery Bootkit Logon Script (Windows)
T1201 - Password Policy Discovery TFTP Boot Login Hook
ROMMONkit Network Logon Script 19 Techniques
ID: TA0004 Privilege Escalation T1137 - Office Application Startup RC Scripts
Office Template Macros Startup Items The adversary is trying to maintain
T1078 - Valid Accounts T1548 - Abuse Elevation Control Mechanism
their foothold.
Office Test T1176 - Browser Extensions
Default Accounts Setuid and Setgid
Outlook Forms T1554 - Compromise Client Software Binary
Domain Accounts Bypass User Account Control
Outlook Home Page T1136 - Create Account
Local Accounts Sudo and Sudo Caching
Outlook Rules Local Account
Cloud Accounts Elevated Execution with Prompt
Add-ins Domain Account
T1053 - Scheduled Task/Job T1134 - Access Token Manipulation
T1556 - Modify Authentication Process Cloud Account
At Token Impersonation/Theft
Domain Controller Authentication T1543 - Create or Modify System Process
Cron Create Process with Token
Password Filter DLL Launch Agent
Scheduled Task Make and Impersonate Token
Pluggable Authentication Modules Systemd Service
Systemd Timers Parent PID Spoofing
Network Device Authentication Windows Service
Container Orchestration Job SID-History Injection
Reversible Encryption Launch Daemon
T1055 - Process Injection T1547 - Boot or Logon Autostart Execution
Multi-Factor Authentication T1546 - Event Triggered Execution
Dynamic-link Library Injection Registry Run Keys / Startup Folder
Hybrid Identity Change Default File Association
Portable Executable Injection Authentication Package
T1525 - Implant Internal Image Screensaver
Thread Execution Hijacking Time Providers
T1574 - Hijack Execution Flow Windows Management Instrumentation Event Subscription
Asynchronous Procedure Call Winlogon Helper DLL
DLL Search Order Hijacking Unix Shell Configuration Modification
Thread Local Storage Security Support Provider
DLL Side-Loading Trap
Ptrace System Calls Kernel Modules and Extensions
Dylib Hijacking LC_LOAD_DYLIB Addition
Proc Memory Re-opened Applications
Executable Installer File Permissions Weakness Netsh Helper DLL
Extra Window Memory Injection LSASS Driver
Dynamic Linker Hijacking Accessibility Features
Process Doppelgänging Shortcut Modification
Path Interception by PATH Environment Variable AppCert DLLs
VDSO Hijacking Port Monitors
Path Interception by Search Order Hijacking AppInit DLLs
ListPlanting Print Processors
Path Interception by Unquoted Path Application Shimming
T1574 - Hijack Execution Flow XDG Autostart Entries
Services File Permissions Weakness Image File Execution Options Injection
13 Techniques DLL Search Order Hijacking Active Setup
Services Registry Permissions Weakness PowerShell Profile
DLL Side-Loading Login Items
The adversary is trying to gain higher-level permissions. COR_PROFILER Emond
Dylib Hijacking T1037 - Boot or Logon Initialization Scripts
KernelCallbackTable Component Object Model Hijacking
Executable Installer File Permissions Weakness Logon Script (Windows)
Installer Packages
Hijacking Login Hook
T1133 - External Remote Services
Path Interception by PATH Environment Variable Network Logon Script
Path Interception by Search Order Hijacking RC Scripts
ID: TA0005 Defense Evasion
Path Interception by Unquoted Path Startup Items
Services File Permissions Weakness T1543 - Create or Modify System Process T1220 - XSL Script Processing T1548 - Abuse Elevation Control Mechanism
Services Registry Permissions Weakness Launch Agent T1600 - Weaken Encryption Setuid and Setgid
COR_PROFILER Systemd Service Reduce Key Space Bypass User Account Control
KernelCallbackTable Windows Service Disable Crypto Hardware Sudo and Sudo Caching
T1068 - Exploitation for Privilege Escalation Launch Daemon T1497 - Virtualization/Sandbox Evasion Elevated Execution with Prompt
T1546 - Event Triggered Execution T1484 - Domain Policy Modification System Checks T1202 - Indirect Command Execution
Change Default File Association Group Policy Modification User Activity Based Checks T1564 - Hide Artifacts
Screensaver Domain Trust Modification Time Based Evasion Hidden Files and Directories
Windows Management Instrumentation Event Subscription T1611 - Escape to Host T1078 - Valid Accounts Hidden Users
Unix Shell Configuration Modification Default Accounts Hidden Window
Trap Domain Accounts NTFS File Attributes
LC_LOAD_DYLIB Addition Local Accounts Hidden File System
Netsh Helper DLL Cloud Accounts Run Virtual Instance
Accessibility Features T1550 - Use Alternate Authentication Material VBA Stomping
AppCert DLLs Application Access Token Email Hiding Rules
AppInit DLLs Pass the Hash Resource Forking
Application Shimming Pass the Ticket Process Argument Spoofing
Image File Execution Options Injection Web Session Cookie T1134 - Access Token Manipulation
PowerShell Profile T1535 - Unused/Unsupported Cloud Regions Token Impersonation/Theft
Emond T1127 - Trusted Developer Utilities Proxy Execution Create Process with Token
Component Object Model Hijacking MSBuild Make and Impersonate Token
Installer Packages T1205 - Traffic Signaling Parent PID Spoofing
Port Knocking SID-History Injection
Socket Filters T1036 - Masquerading
@hackinarticles
T1221 - Template Injection Invalid Code Signature
T1216 - System Script Proxy Execution Right-to-Left Override
https://github.com/Ignitetechnologies
PubPrn Rename System Utilities
T1218 - System Binary Proxy Execution Masquerade Task or Service
https://in.linkedin.com/company/hackingarticles
Compiled HTML File Match Legitimate Name or Location
Control Panel Space after Filename
CMSTP Double File Extension
InstallUtil T1197 - BITS Jobs
Mshta T1612 - Build Image on Host
Msiexec T1622 - Debugger Evasion
Odbcconf T1140 - Deobfuscate/Decode Files or Information
Regsvcs/Regasm T1610 - Deploy Container
Regsvr32 T1006 - Direct Volume Access
Rundll32 T1484 - Domain Policy Modification
Verclsid Group Policy Modification
Mavinject Domain Trust Modification
MMC T1480 - Execution Guardrails
T1553 - Subvert Trust Controls Environmental Keying
Gatekeeper Bypass T1211 - Exploitation for Defense Evasion
Code Signing T1222 - File and Directory Permissions Modification
42 Techniques
SIP and Trust Provider Hijacking Windows File and Directory Permissions Modification
Install Root Certificate Linux and Mac File and Directory Permissions Modification The adversary is trying to avoid being detected.
Mark-of-the-Web Bypass T1574 - Hijack Execution Flow
Code Signing Policy Modification DLL Search Order Hijacking
T1014 - Rootkit DLL Side-Loading
T1207 - Rogue Domain Controller Dylib Hijacking
T1620 - Reflective Code Loading Executable Installer File Permissions Weakness
T1055 - Process Injection Dynamic Linker Hijacking
Dynamic-link Library Injection Path Interception by PATH Environment Variable
Portable Executable Injection Path Interception by Search Order Hijacking
Thread Execution Hijacking Path Interception by Unquoted Path
Asynchronous Procedure Call Services File Permissions Weakness
Thread Local Storage Services Registry Permissions Weakness
Ptrace System Calls COR_PROFILER
Proc Memory KernelCallbackTable
Extra Window Memory Injection T1562 - Impair Defenses
Process Hollowing Disable or Modify Tools
Process Doppelgänging Disable Windows Event Logging
VDSO Hijacking Impair Command History Logging
ListPlanting Disable or Modify System Firewall
T1542 - Pre-OS Boot Indicator Blocking
System Firmware Disable or Modify Cloud Firewall
Component Firmware Disable Cloud Logs
Bootkit Safe Mode Boot
ROMMONkit Downgrade Attack
TFTP Boot T1070 - Indicator Removal
T1647 - Plist File Modification Clear Windows Event Logs
T1027 - Obfuscated Files or Information Clear Linux or Mac System Logs
Binary Padding Clear Command History
Software Packing File Deletion
Steganography Network Share Connection Removal
Compile After Delivery Timestomp
Indicator Removal from Tools Clear Network Connection History and Configurations
HTML Smuggling Clear Mailbox Data
Dynamic API Resolution Clear Persistence
Stripped Payloads T1556 - Modify Authentication Process
Embedded Payloads Domain Controller Authentication
T1599 - Network Boundary Bridging Password Filter DLL
Network Address Translation Traversal Pluggable Authentication Modules
T1601 - Modify System Image Network Device Authentication
Patch System Image Reversible Encryption
Downgrade System Image Multi-Factor Authentication
Hybrid Identity
T1578 - Modify Cloud Compute Infrastructure
Create Snapshot
Create Cloud Instance
Delete Cloud Instance
Revert Cloud Instance
T1112 - Modify Registry
ID: TA0006 Credential Access
Credentials In Files T1557 - Adversary-in-the-Middle
Credentials in Registry LLMNR/NBT-NS Poisoning and SMB Relay
Bash History ARP Cache Poisoning
Private Keys T1552 - Unsecured Credentials
DHCP Spoofing
Cloud Instance Metadata API
T1110 - Brute Force
Group Policy Preferences
Password Guessing
Container API
Password Cracking
T1539 - Steal Web Session Cookie
Password Spraying
T1558 - Steal or Forge Kerberos Tickets
Credential Stuffing
Golden Ticket
T1555 - Credentials from Password Stores
Silver Ticket
Keychain
Kerberoasting
Securityd Memory
AS-REP Roasting
Credentials from Web Browsers
T1649 - Steal or Forge Authentication Certificates
Windows Credential Manager
T1528 - Steal Application Access Token 17 Techniques
Password Managers
T1003 - OS Credential Dumping
T1212 - Exploitation for Credential Access
LSASS Memory The adversary is trying to steal account names and
T1187 - Forced Authentication passwords.
Security Account Manager
T1606 - Forge Web Credentials
NTDS
Web Cookies
LSA Secrets
SAML Tokens
Cached Domain Credentials
T1056 - Input Capture
DCSync
Keylogging
Proc Filesystem
GUI Input Capture
/etc/passwd and /etc/shadow
Web Portal Capture
T1040 - Network Sniffing
Credential API Hooking
T1621 - Multi-Factor Authentication Request Generation
T1556 - Modify Authentication Process
Domain Controller Authentication
Password Filter DLL
Pluggable Authentication Modules
Network Device Authentication
Reversible Encryption
Multi-Factor Authentication
Hybrid Identity
T1111 - Multi-Factor Authentication Interception
You might also like
- SM-0006900 - G Pulse 120H Service Manual 27dec2018Document636 pagesSM-0006900 - G Pulse 120H Service Manual 27dec2018MacKiiz ซี้แหงแก๋100% (4)
- Atlas Copco Xas 90 Parts ManualDocument2 pagesAtlas Copco Xas 90 Parts ManualJose Carmona33% (9)
- Pdfmergerfreecom Reinforced Concrete Limit State Design A K Jain 9788185240794Document2 pagesPdfmergerfreecom Reinforced Concrete Limit State Design A K Jain 9788185240794Sailesh BudhathokiNo ratings yet
- Finacle Desktop Configuration For 10 2 1Document60 pagesFinacle Desktop Configuration For 10 2 1nidhinvg8950% (4)
- Mobile Attack Cheat Sheet 1708115239Document1 pageMobile Attack Cheat Sheet 1708115239Joash MacentonNo ratings yet
- Network MatrixDocument1 pageNetwork MatrixrakivanatanNo ratings yet
- Containers MatrixDocument1 pageContainers MatrixNuryadin Usman Abdurrahim AsSampiti IINo ratings yet
- iOS AttackDocument1 pageiOS AttackrakivanatanNo ratings yet
- Cloud MatrixDocument1 pageCloud MatrixrakivanatanNo ratings yet
- Credential AccessDocument1 pageCredential AccessNuryadin Usman Abdurrahim AsSampiti IINo ratings yet
- Defense EvasionDocument1 pageDefense EvasionrakivanatanNo ratings yet
- Peter O & Alessandra Di Carlo - Lessons From The Frontlines - Ransomware Attacks, New Techniques and Old TricksDocument23 pagesPeter O & Alessandra Di Carlo - Lessons From The Frontlines - Ransomware Attacks, New Techniques and Old TricksFranklin CordeiroNo ratings yet
- Windows ATT&CK - Logging Cheat Sheet - Ver - Sept - 2018Document15 pagesWindows ATT&CK - Logging Cheat Sheet - Ver - Sept - 2018Ike ChenNo ratings yet
- Windows Log-Md Att&Ck Cheat Sheet - Win 7 - Win 2012: DefinitionsDocument17 pagesWindows Log-Md Att&Ck Cheat Sheet - Win 7 - Win 2012: DefinitionsJWilhNo ratings yet
- Conti (s0575)Document5 pagesConti (s0575)anup.tilekar.86No ratings yet
- Mitre Att&ck v9Document22 pagesMitre Att&ck v9Fabiano DiscacciatiNo ratings yet
- APT39 AnswersDocument4 pagesAPT39 Answersimane sadaniNo ratings yet
- How To Use Splunk For Automated Regulatory Compliance PDFDocument74 pagesHow To Use Splunk For Automated Regulatory Compliance PDFDennis DubeNo ratings yet
- Windows MatrixDocument1 pageWindows MatrixfolalikNo ratings yet
- Training Manual Section 2Document12 pagesTraining Manual Section 2ilai276494No ratings yet
- Mitre Overview 2021-01-16Document5 pagesMitre Overview 2021-01-16iaas labsNo ratings yet
- CybersecurityDocument42 pagesCybersecurityKurangeswararao chNo ratings yet
- Tmi para Fls Motor Flash-CatDocument28 pagesTmi para Fls Motor Flash-Catyadira saezNo ratings yet
- Joint-CISA-FBI-NSA CSA AA21-291A BlackMatter RansomwareDocument7 pagesJoint-CISA-FBI-NSA CSA AA21-291A BlackMatter RansomwareyejacafoNo ratings yet
- Technical Marketing Information (TMI) : Shane GillesDocument28 pagesTechnical Marketing Information (TMI) : Shane GillesJopeth YoussefNo ratings yet
- MITRE ATT&CK Wheel of FortuneDocument122 pagesMITRE ATT&CK Wheel of FortuneMilin ShahNo ratings yet
- Brksec 3455Document87 pagesBrksec 3455falconNo ratings yet
- Technical Marketing Information (TMI) : Shane GillesDocument28 pagesTechnical Marketing Information (TMI) : Shane Gillesdon cargaNo ratings yet
- Mitre ATT&CK Top TecnicasDocument4 pagesMitre ATT&CK Top TecnicasInfonet MundoNo ratings yet
- Kyocera KM 1820 KM1820 - SSG - ENG User Manual To The A4287ff3 171c 4657 8f7f E2b6efa8a9d3Document35 pagesKyocera KM 1820 KM1820 - SSG - ENG User Manual To The A4287ff3 171c 4657 8f7f E2b6efa8a9d3Gaspar BalderramaNo ratings yet
- NCSC MAR Infamous ChiselDocument35 pagesNCSC MAR Infamous Chiselamojm1No ratings yet
- DME IQ Intelligent Cloud O&M Platform Quick Deployment Guide (Connecting Storage Using DME IQ Client)Document2 pagesDME IQ Intelligent Cloud O&M Platform Quick Deployment Guide (Connecting Storage Using DME IQ Client)Mpho MpyaNo ratings yet
- User Interface Connection ProceduresDocument72 pagesUser Interface Connection Proceduresalek nowalNo ratings yet
- CSA - TTPs of Indicted APT40 Actors Associated With China MSS Hainan State Security DepartmentDocument14 pagesCSA - TTPs of Indicted APT40 Actors Associated With China MSS Hainan State Security Departmentmalikjavaid093No ratings yet
- Mitre ATT@CK Matrix - Windows Logging - Basic: High Confidence or Covereage Medium Confidence or CoverageDocument27 pagesMitre ATT@CK Matrix - Windows Logging - Basic: High Confidence or Covereage Medium Confidence or CoverageTuba ŞengünNo ratings yet
- NSA Sharkseer PDFDocument12 pagesNSA Sharkseer PDFJuan100% (1)
- DNS Pres ITS BP 2016-12Document10 pagesDNS Pres ITS BP 2016-12JaarnoNo ratings yet
- Effectively Enhancing Our Soc With Sysmon Powershell Logging and Machine Learning To Detect and Respond To Todays Threats PDFDocument43 pagesEffectively Enhancing Our Soc With Sysmon Powershell Logging and Machine Learning To Detect and Respond To Todays Threats PDFHamza IdrisNo ratings yet
- NENA 03-502 Trunking For PriDocument26 pagesNENA 03-502 Trunking For PrisysbenderNo ratings yet
- DigiSAFE Data Diode & FCS (2018-06-27)Document15 pagesDigiSAFE Data Diode & FCS (2018-06-27)Tuan MANo ratings yet
- TCN TRDP2 I CNC 003 01 TCNOpen PresentationDocument8 pagesTCN TRDP2 I CNC 003 01 TCNOpen PresentationBojan SubasicNo ratings yet
- What Is Smart Card - 2010!09!20Document31 pagesWhat Is Smart Card - 2010!09!20OttohungNo ratings yet
- Etwork: Penetration TestingDocument19 pagesEtwork: Penetration Testingesmail ahmedNo ratings yet
- Chapter 9 & 10: Is Controls For System Reliabilities: - Confidentiality, Privacy, Processing Integrity & AvaiabilityDocument7 pagesChapter 9 & 10: Is Controls For System Reliabilities: - Confidentiality, Privacy, Processing Integrity & AvaiabilityNik Nur Azmina AzharNo ratings yet
- Cisco Firepower and Radware Technical OverviewDocument14 pagesCisco Firepower and Radware Technical OverviewAlfredo Claros100% (1)
- PKWARE - Overview - AK - Ian's NotesDocument11 pagesPKWARE - Overview - AK - Ian's NotesChai QixuanNo ratings yet
- DLP PresentationDocument59 pagesDLP PresentationnagarjunaNo ratings yet
- TEMENOS Data Migration Services - Synopsis - 10 Oct 2011 - V1 - 10102011Document28 pagesTEMENOS Data Migration Services - Synopsis - 10 Oct 2011 - V1 - 10102011MrMochtar100% (2)
- Temenos Data Migration (TDM) ServicesDocument9 pagesTemenos Data Migration (TDM) Servicesthunder.ajay100% (2)
- Lecture 05 and 06Document48 pagesLecture 05 and 06Syed BadshahNo ratings yet
- Relational Data Base Management For On-Line Transaction ProcessingDocument22 pagesRelational Data Base Management For On-Line Transaction ProcessingKrishna SgNo ratings yet
- Rajalakshmi Engineering CollegeDocument3 pagesRajalakshmi Engineering Collegecadburys_ajayNo ratings yet
- Data Analytics Module OutlineDocument1 pageData Analytics Module OutlineSathia ShekarNo ratings yet
- d2 4PM 643 HollingsworthDocument23 pagesd2 4PM 643 HollingsworthcesrdanielgarciaramirezNo ratings yet
- Cloudera Big Data Architecture DiagramDocument3 pagesCloudera Big Data Architecture DiagramSteven Christian HalimNo ratings yet
- Systemblueprint DownloadDocument2 pagesSystemblueprint DownloadpendejitusNo ratings yet
- Making Mitre Att&Ck Framework New Hunting Standard: January 2020 SentineloneDocument14 pagesMaking Mitre Att&Ck Framework New Hunting Standard: January 2020 SentineloneShreekanth MuraliNo ratings yet
- Security Analytics Architecture For APT: Dale Long, Sr. Technology Consultant, RSA SecurityDocument33 pagesSecurity Analytics Architecture For APT: Dale Long, Sr. Technology Consultant, RSA SecurityDodo winyNo ratings yet
- Account Security ChecklistDocument15 pagesAccount Security ChecklistRyalapeta Venu YadavNo ratings yet
- CDR Tcs BSNL Pune 23 June 2007Document90 pagesCDR Tcs BSNL Pune 23 June 2007rebba89No ratings yet
- DNS AM-Trap-Whitepaperv2.2Document4 pagesDNS AM-Trap-Whitepaperv2.2Pooja GuptaNo ratings yet
- 4 Collecting Volatile DataDocument55 pages4 Collecting Volatile DataRoheet BhatnagarNo ratings yet
- BITE202P-Digital Logic & Microprocessor Lab: Assessment 1: Combinational Logic CircuitsDocument2 pagesBITE202P-Digital Logic & Microprocessor Lab: Assessment 1: Combinational Logic CircuitsDeveshNo ratings yet
- SMS NOTES 1st UNIT 8th SemDocument30 pagesSMS NOTES 1st UNIT 8th Semgvarun_1989100% (1)
- Spark English FAQDocument2 pagesSpark English FAQKushal DeshmukhNo ratings yet
- Acer v223hq Ver.001 LCD MonitorDocument69 pagesAcer v223hq Ver.001 LCD MonitorDarko ZeravicaNo ratings yet
- Otto Servo Calibration GuideDocument16 pagesOtto Servo Calibration Guideporsche6911No ratings yet
- Dual Display PID Temperature Controllers: TCN SeriesDocument6 pagesDual Display PID Temperature Controllers: TCN SeriesDinho AcioliNo ratings yet
- LTE Throughput Troubleshooting GuidlelineDocument15 pagesLTE Throughput Troubleshooting GuidlelineTourchianNo ratings yet
- 2-Search Your DataDocument52 pages2-Search Your DatasoniarpbNo ratings yet
- Validation Based ProtocolDocument7 pagesValidation Based ProtocolTerimaaNo ratings yet
- Chapter 3 ForecastingDocument87 pagesChapter 3 ForecastingTabassum BushraNo ratings yet
- (CI) 1106653 Na 10026292 PT INDONESIA LOYAL ART 00043202Document7 pages(CI) 1106653 Na 10026292 PT INDONESIA LOYAL ART 00043202VonggeNo ratings yet
- Syllabus Content:: Input, Output and Storage DevicesDocument32 pagesSyllabus Content:: Input, Output and Storage Devicesapi-470106119No ratings yet
- Akarsh SynopsisDocument18 pagesAkarsh SynopsisDheeraj singhNo ratings yet
- Tinyhawk III PLUS-RTF Manual EnglishDocument50 pagesTinyhawk III PLUS-RTF Manual EnglishIan SadockNo ratings yet
- Test Construction With IRTDocument11 pagesTest Construction With IRTYogananda CSNo ratings yet
- Harsh2 ResumeDocument1 pageHarsh2 Resumeankit ojhaNo ratings yet
- Pic 16 C 505Document85 pagesPic 16 C 505Joel LopezNo ratings yet
- IBM Presentación Data CentersDocument14 pagesIBM Presentación Data CentersDaniel AguilarNo ratings yet
- Advanced ElectricalDocument242 pagesAdvanced ElectricalCharles SiameNo ratings yet
- MMV1205SDocument4 pagesMMV1205SmuhammedasifNo ratings yet
- CHAPTER 1: Introduction To Discrete-Time Control Systems Digital Control SystemsDocument6 pagesCHAPTER 1: Introduction To Discrete-Time Control Systems Digital Control SystemsIzzat AzmanNo ratings yet
- E Vaccination System Using AiDocument17 pagesE Vaccination System Using AiBRO.V͙A͙M͙S͙I͙ Ƥeͥ†eͣrͫ꧂No ratings yet
- LackeyCCG - Tutorial - Plugin Creation - How To Make A PlugininfoDocument6 pagesLackeyCCG - Tutorial - Plugin Creation - How To Make A Plugininfodekijom963No ratings yet
- Practise: 1. Write A Query To Display All Customers From Mexico As FollowsDocument6 pagesPractise: 1. Write A Query To Display All Customers From Mexico As FollowsTran Ngoc Hong Quan (K16HL)No ratings yet
- Release Notes Nfnic-4.0.0.87Document2 pagesRelease Notes Nfnic-4.0.0.87Nilesh AjgaonkarNo ratings yet
- Data Structures - GeeksforGeeksDocument22 pagesData Structures - GeeksforGeeksJohn PrestonNo ratings yet