EXECUTIVE PROTECTION
ARTURO A BRINGAS MBA,CSP,CSMS,CST
�Introduction
2
You were notified one late night that a key executive in your company was kidnapped and ransom has been demanded.
WHAT ARE YOU GOING TO DO? ARE YOU PREPARED TO RESPOND?
3
More than 20 years ago, kidnapping, extortion and terrorism occur mostly in other countries. In the 90s, incidence of kidnapping, extortion and terrorism occurred with alarming frequency. Threats on executives then escalated from Very Serious to Extremely Serious
4
� Terrorism take many forms such as rioting, arson and bombing In recent years, the new and more personal brand of terrorism was kidnapping. It has become so frightening and so effective form of terrorism from the point of view of terrorists Individuals who wield power - financial or political are the attractive targets for
extremists, kidnappers and extortionists
5
�What experts say on Kidnapping?
Frequency - 1 kidnapping every two weeks worldwide A high number of kidnappings occur in the Philippines Vast bulk of kidnappings is in Latin America and lately, South Africa
(Ref: Kroll)
� Kidnapping has become an INDUSTRY. The only industry that posted phenomenal growth during the Asian currency crisis in 1997 P300M paid
�Kidnapping as an Industry
Recruitment and Training Research on Target Victims Resources Planning of Operations Snatching of Victim Hiding of Victim Ransom Negotiation
8
�Kidnapping as an Industry
Ransom Collection Sanitation / Clean Up Operation Investment or Money Laundering Neutralization of Obstacles and Cultivation of Support Legal Aspects
9
�Favorite Targets of KFRGs
Rich Chinese-Filipinos Filipino Businessmen Foreigners/expatriates Dependents of affluent families Wives of rich businessmen Top executives of big companies
10
�Worldwide Profile
1997 The Philippines was the 4th kidnap capital of the world with 500 cases or more. Colombia was 1st with 4,000 Mexico was 2nd with 1,400 Brazil was 3rd with 800. 2002 2003 South Africa the new kidnap capital of the world with 3,071 kidnappings and 4,210 abductions
11
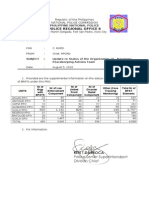
�Latest in our Country
Recurring security problem In 2008, there were 58 incidents with 103 victims or 5 cases & 8 victims / month 31 businessmen, 31 ordinary citizens, 17 children/students, 13 professionals, 6 teachers and 5 NGO workers were kidnapped Most notable was the kidnap of a TV news network by ASG in Sulu
12
�Latest in our Country
In 2008 also, 5 victims were killed Ransom demands ranged from P100,000 to P30M Actual payments were between P20,000 and P3M Victims were held in captivity on an average of 5 to 15 days
13
�Philippine Profile
Foreign Nationals kidnapped: 6 Indians 3 Chinese 2 Koreans 2 Canadians All were released after ransom was paid.
Kidnap Spots :
ARMM NCR Central Luzon Calabarzon 27 12 5 4
Rest of Mindanao Zamboanga Peninsula Western Visayas
4
4 2
14
�Where Victims are Snatched?
In place of business or work On the Street In Shopping Malls In Schools At Home
15
�New Tactics Employed
Ransom money is paid elsewhere Pre-kidnap threat is employed and ransom paid in advance Use of sophisticated equipment Have enough funding to cover cost of operation
16
�ATTITUDE TOWARDS KIDNAPPING The world-wide trend of violence foretells a threat that many businessmen choose not to recognize the seriousness of the threat. Many corporations, leery of exposing their vulnerabilities to the public, have suppressed reports of successful kidnappings.
17
�ATTITUDE TOWARDS KIDNAPPING The world-wide trend of violence foretells a threat that many businessmen choose not to recognize the seriousness of the threat. Many corporations, leery of exposing their vulnerabilities to the public, have suppressed reports of successful kidnappings.
18
�Response to Kidnapping Hazards
1. Many Security Directors focused on executive protection awareness and services. This aspect of security is often different from the normal corporate security procedures. This is a necessary element in a complete protection of assets strategy. 2. An Executive protection specialist is hired 3. Corporate security personnel are sent for training.
19
�Response to Kidnapping Hazards
3. An Executive Protection Program is prepared and implemented to equip the target executive, family and support personnel with the tools (security countermeasures) to minimize exposure to dangerous situations. 4. Most companies get bodyguards because that is the traditional approach. However, these companies dont know that PREVENTION is much more important and effective.
20
�Traditional Approach of Using Bodyguards
Advantages? Disadvantages?
21
�Analysis of the Traditional vs Modern Approach to Executive Protection
1. Bodyguard is an old-fashioned name New professional name: Protection Specialist 2. Bodyguard will work for less Protection Specialist is more expensive 3. Bodyguard use more brawn not brains Brains not brawn 4. Samurai were bodyguards Wears a suit not kimono 5. 5th Oldest Profession Graduate of a Protection School
22
�Kidnapping - A Classic Art of Terrorism
Kidnappers know that FEAR is their best weapon because: Terror breeds terror and with terror comes destruction of the human spirit and determination to oppose the sources of terror. Terrorists exploit this to ensure compliance to their demands.
23
�Kidnapping Categories POLITICAL CRIMINAL PASSION
24
�POLITICAL KIDNAPPING
Victim is normally not harmed Kidnappers aim for greater propaganda impact (Patricia Hearst Case1974)
Unintentional harm occurs due to an accident, sometimes when victim resisted Intentional harm cannot be ruled out
25
�CRIMINAL KIDNAPPING
Usually motivated by personal gain Traditional demand for ransom Harm is inevitable as victim is of no value after ransom is paid
26
�PASSION KIDNAPPING:
Jilted or Jealous Lover Will exact vengeance and kidnap a person at the spur of the moment
Victim may be harmed Kidnapper may end up killing himself
Psychologically imbalance
27
�Psychology of Abduction
28
�The Victim It cant happen to me Attitude:
Too confident person who thinks:
Harm will fall on others but not to him Everyone holds him in high regard and no one would want to attack him Will aggressively resist any effort to protect himself May take unnecessary risks to demonstrate he is not vulnerable.
29
�Nothing can be done about it Attitude:
A Fatalist who feels: An event will occur regardless of what is done to prevent it Useless to interfere with fate Normal to happen
30
�It will reflect on my reputation Attitude:
Extremely conscious on image (False Bravery) Will not do anything that might indicate: 1. lack of bravery 2. indecisiveness 3. poor leadership Cannot accept advice or suggestion from others in lesser position
31
�Indecisiveness on Protection:
Distrustful on protection offered to him
Fluctuation between agreement and disagreement with protective measures Demonstrates constant change in attitude toward security
32
�THE KIDNAPPER
Uses the element of SURPRISE to sow confusion and frighten everyone Careful and patient planner Devote a great amount of time, effort and resources Learn more on intended victim thru close observation over a period of time. Aim to know where victim is most vulnerable.
33
�STATISTICS ON HOSTAGE TAKING
87% - Probability of actually seizing hostage 79% - chance all the terrorists would escape punishment or death 40% - chance that all or some demands would be met 29% - chance of full compliance with such demands 83% - chance of success where safe passage or exit for the themselves was the sole demand 67% - all or virtually all the terrorists would still escape alive by going underground, safe passage in lieu of their original demands, or surrendering to a sympathetic government 100% - major publicity gain (Source CIA)
34
�Prevention Oriented Planning
Creating an awareness of potential threats is the most important in the success of an Executive Protection Program. Executive Protection Specialists must recognize and overcome the reluctance of executives. A TOTAL EXECUTIVE PROTECTION PLAN must be prepared for the target executive, family and support personnel to reduce the chance of becoming victims
35
�COVERAGE OF AN EXECUTIVE PROTECTION PROGRAM prevention planning kidnap attempt hostage survival vehicle security defensive driving bomb threat contingency duress code
36
�COVERAGE OF AN EXECUTIVE PROTECTION PROGRAM
crisis management current dossiers psychology and probability of abduction pros and cons of escape attempts risk factors involved development of strategies to cope with the problem
37
�The Executive Protection Program
Not all are Primary Targets Must have a contingency program for all Establish Basic Protection Procedures Plan for Crisis Management Identify who is in charge of the program Identify who makes what decisions Provision for ransom demands Test and evaluate the above BEFORE and NOT AFTER an incident
38
�Responsibility
The Executive Protection Specialist is in charge of the planning, development and execution of the program The present trend now is the setting up of a Crisis Response Team backed up by a working committee composed by: COO or representative Security Chief Treasury Chief Negotiator PR man
39
1. 2. 3. 4. 5.
�Key Elements of a Successful Executive Protection Program
Salesmanship sell the need and the program Public Relations promote your resource persons from law enforcement and private security. The more validity they have, the more valid your plan will be Presentation The look of a good program Is it neat? Colorful? Professional? Follow through is essential Update the program at least once a year; count on the executives families as allies. 40
�Round the Clock Executive Protection
Executive Terrorism has been experienced many times over by almost every country. Private organizations and public agencies worked in top speed to define the risk, assess vulnerability, and develop strategies that are both preventive and responsive. Companies not primary targets should also have a program for contingency.
41
�Weaknesses in the Executive Protection Program
42
�Case Study: The Aldo Moro Kidnapping
On March 16, 1978, Aldo Moro was kidnapped from his car in a Rome street near his home and took only a few seconds. 3 policemen, the bodyguard and driver were killed. Before it happened, his escorts drove too close to the VIP and they used the same route everyday. His driver was a long time employee. Different police units handled security and since veterans shy from being assigned in Moros security, fresh graduates with no special training and using substandard weapons were assigned. To top it all, security situation in Italy was worse as there were 78 kidnappings in 1977 and more than doubled in 1978.
43
�Weaknesses Noted - The DONTs
in Executive Protection
Failure to Coordinate Plans 2 police organizations were involved but did not seriously discussed and coordinated their efforts Lack of Professionalism Personnel have no special training and not properly selected; over-familiarity
44
�Weaknesses Noted - The DONTs
in Executive Protection
Failed to Follow Good Security Procedures Escort vehicle stayed too close; substandard firearms Failure to Assess the Risk - ignored the occurrence of a lot kidnapping incidents Conspicuous Target VIP car is easily identified and subject clearly seen inside Failed to Change Routine Used the same route everyday Poor intelligence Car plate used by kidnappers was a returned diplomatic plate
45
�Case Studies
Assassination of Yitzhak Rabin Why was his killing not prevented? "There was a colossal failure of the General Security Service (GSS) which led to Rabin's assassination. They had many tips and many leads about the killer's intention to murder the prime minister and they ignored them. Failed Attempt PCC President Nemesio Prudente Why did the killers failed?
46
�The 24 Hour Protection Cycle
Protection plans for company executives, can be effective if simple, tested deterrents are established and carefully followed. Need not be extremely costly, although use of bodyguards, armored cars and clandestine rather than open meetings cannot be ruled out in some instances Should not interrupt the lifestyle. To the contrary, plans that greatly disrupt the established lifestyles will not be accepted.
47
�The 24 Hour Protection Cycle
Plans must be detailed, tested and revised as daily routine changes to ensure that the effectiveness of the plan does not deteriorate. Protection programs must start with an economical, workable and effective physical security program to secure the facilities used by the executive
48
�Phase I - En route to the office, country club, or other locations routinely visited Use of Route Driver as bodyguard Advance Party, Close In and Back Up Security Weapons Communications Vehicle type and profile
Evasive Actions
Support along the route and destination
49
�Phase II - Inside the Facility Housing the Executive Offices Access control is established Surveillance, Alarm and Access Control Systems should be considered including use of panic buttons Board Room Check (against bugs) Custodial Staff Screening Passage Check no obstruction, for emergency exit / escape Building Check for structural durability
50
�Phase III - Precaution During Lunch Within the building, no need for additional security measures Outside the building - private club or restaurant apply Phase I and VII to a certain degree. Apply Phase I (or V) when returning to office.
51
�Phase IV - In the Business Office Follow Phase II again throughout the working day: Access Control Surveillance and Alarm System Board Room Check Custodial Staff Screening Passage Check Building Check
52
�Phase V - En route Home Follow Phase I again: Use of Route Driver as bodyguard Advance Party, Close In and Back Up Security Weapons Communications Vehicle type and profile Evasive Actions Support along the route and destination
53
�Phase VI - Protection of the Executives Residence Conduct complete physical security survey to establish appropriate security measures. Protection should be realistic and not interfere with normal activities of the family. Educate the family & household staff on basic security, safety and emergency procedures including telephone security and access control. Apply Security or Defense-In-Depth (a 3layered barrier system)
54
�Security or Defense-In-Depth
55
�Presence of friendly installations in the perimeter like: police station military base LGU installations public frequented places private security forces barangay tanods friendly neighborhood religious institutions
56
�Protection of the residence include human, structural, animal, electronic, man-made or natural barriers
57
�2nd Layer of security Install fences or walls Gates should remain locked when not in use Install controlled protective lighting Install CCTV system Use trained dogs; geese, chickens, birds, etc Hire uniformed armed guard/s or caretaker Use video intercoms to id visitors.
58
�The inside of the residence is protected by walls, windows, doors, cameras, alarms, secret passages and a strong room.
59
�Phase VII - Social Functions Apply Phase I whenever a car is used Apply Phase III if function is in a private club or public frequented place Avoid using reserved tables and change table location frequently The bodyguard should remain either near the entrance or seated in the dining area at an adjoining table. For sports activities, the routine should be changed. Activities should be low-keyed. On speaking engagement, public announcement should be made after the address and not before.
60
�Phase VIII - Stockholders Meetings Protection is dictated by current climate and type of business Make prior coordination with venue officials and support services Have executive arrive just before meeting starts Consider using alternative entrance Implement access control Employ covert personnel
61
� Coordinate with local authorities for situation update, crowd control, area security and deterrence aspect Use surveillance cameras Record by video and still photos the entire proceedings Sweep the venue for bugs and bombs Get list of venue personnel who will serve in the meeting Establish media room far from public view Change geographical location of the meetings to places where protesters cannot get support.
62
�Phase IX - Corporate Travel By Air 1. Secure aircraft, if owned. Degree of protection is the same as that in the business office 2. Secure aircraft 24 hours a day until departure. 3. Use caution. Always search the aircraft immediately prior to flights. 4. Establish access control and review pilots chart 5. Double check luggage 6. If using commercial aircraft, dont announce travel schedule; use other 63 names in reservation
�7. Escort executives to the passenger screening point in airport 8. If situation dictates, use combination of corporate and commercial aircraft for travel 9. Use 2 or 3 planes for large groups. Never place all your eggs in one basket.
By Land - advance party is sent or arrange for pick up, use pre-planned route. Billet Security - accredit the place, get assurance of confidentiality, make prior coordination
64
�Phase X - Vacation The toughest protection assignment and protection dependent on number of travellers, mode of travel and location. Consider the following: Low Profile - Publicity be done after the travel, not before Avoid trouble areas Use sound judgment Do not announce Arrange for mail pick up, lawn clearing newspapers and bills delivery, divert phone calls, etc
65
�Phase XI - Protection of the Executives Family Protect the children
1. 2. 3. 4. going to and from and at school use different routes discuss protection plan with the kids consider discontinuance of school if attack is probable or possible
Examine wifes social activity brief her on various precautions she should constantly exercise Train the family and household staff Keep personal data of each member of the family
66
�11 Phase Protection Cycle
Phase I 0800H-0845H enroute to office Phase II 0845H-1230H inside protected area or building Phase III 1230H-1400H lunch Phase IV 1400H-1800H inside protected area or building Phase V 1800H-1845H enroute home Phase VI 1845H-2000H inside protected residence Phase VII Social functions Phase VIII Stockholders meetings Phase IX Corporate travel Phase X Vacations Phase XI Protection of the executives family 67
�Sample Executive Protection Awareness Course
Introduction to Terrorism Crisis Management Hostage Survival Observation and Description Individual Protective Measures Home Security Measures Safe Havens Firearms Training Defensive and Evasive Driving Surveillance and Counter-Surveillance Explosive Devices
68
��Thank you