Professional Documents
Culture Documents
System Information and Technology Weekly Assignment: Chapter 8 Summary Securing Information Systems (Aileen Irmina P. 19/440371/EK/22297)
Uploaded by
Aileen Irmina Putri0 ratings0% found this document useful (0 votes)
19 views3 pagesOriginal Title
SIT chapter 8
Copyright
© © All Rights Reserved
Available Formats
DOCX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
19 views3 pagesSystem Information and Technology Weekly Assignment: Chapter 8 Summary Securing Information Systems (Aileen Irmina P. 19/440371/EK/22297)
Uploaded by
Aileen Irmina PutriCopyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
You are on page 1of 3
System Information and Technology
Weekly Assignment: Chapter 8 Summary
Securing Information Systems
(Aileen Irmina P. 19/440371/EK/22297)
Security is policies, procedures, and technical measures used to prevent
unauthorized access, alteration, theft, or physical damage to information systems. Controls
is methods, policies, and organizational procedures that ensure the safety of the
organization’s assets, the accuracy and reliability of its records, and operational adherence
to management standards. Systems may vulnerable because accessibility of networks,
hardware problems, software problems, disasters, use of networks or outside of firm’s
control, loss and theft of portable devices.
Internet vulnerabilities is depend on how much the networks open to anyone. size of
the internet means abuses can have wide impact. Vulnerability has also increased from
widespread use of e-mail, instant messaging, and peer-to-peer (P2P) file-sharing program.
Wireless security challenges is depends on how vigilant we are, because radio
frequency bands is easy to scan. Wi-Fi transmission technology was designed to make it
easy for stations to find and hear one another with SSIDs (the service set identifiers). It used
to identify access points, broadcast multiple times, can be identified by sniffer programs,
and war driving (eavesdroppers drive by buildings or park outside and try to intercept
wireless networks traffic).
Types of malware (malicious software):
Computer virus: rogue software program that attaches itself to other
software programs or data files to be executed, usually without user
knowledge or permission.
Worms: independent programs that copy themselves from one computer to
other computers over a network
Trojan horse: software program that appears to be benign but then does
something other than expected.
SQL injection attacks: hackers submit data to Web forms that exploits site’s
unprotected software and sends rogue SQL query to database
Spyware: small programs that install themselves surreptitious on computers
to monitor user web-surfing activity and serve up advertising
Keyloggers: record every keystroke made on a computer to steal serial
numbers for software
Hacker is an individual who intends to gain unauthorized access to computer system.
Their activity include: system intrusion, system damage, cyber-vandalism (intentional
disruption, defacement, destruction of Web site or corporate information).
Spoofing is misrepresenting oneself by using fake e-mail addresses or masquerading
as someone else. This may also involve redirecting a web link to an address different from
the intended one. Sniffer is a type of eavesdropping program that monitors information
traveling over a network.
Denial-of-service (DoS) attack is when hackers flood a network server or web server
with many thousands of false communications or requests for services to crash the network.
Distributed denial-of-service (DDoS) attack uses numerous computers to inundate and
overwhelm the network from numerous launch points. Botnet is place used to organize PCs
infected with malicious software.
Computer crime define as any violations of criminal law that involve a knowledge of
computer technology for their perpetration, investigation, or prosecution. Computer may be
the target of crime or may be the instrument of crime.
Identity theft is a crime in which a imposter obtains key pieces of personal
information (security numbers, driver’s licence numbers, or credit card numbers). Phishing
is setting up fake Web sites or sending e-mail messages that look like legitimate businesses
to ask users for confidential personal data. Evil twins is wireless networks that pretend to
offer trustworthy Wi-Fi connections to the Internet. Pharming redirects users to a bogus
web page, even when the individual types the correct web page address into his or her
browser.
Click fraud occurs when an individual or computer program fraudulently clicks an
online ad without any intention of learning more about the advertiser or making a purchase.
Cyberwarfare is state-sponsored activity designed to cripple and defeat another state or
nation by penetrating its computers or networks to cause damage and disruption.
Internal threats – employees is security threats from inside an organization because
of sloppy security procedures and social engineering (tricking employees to reveal
passwords, etc). software vulnerability is commercial software contains flaws that create
security vulnerabilities.
Legal and regulatory requirements for electronic records management: HIPAA,
Gramm-Leach-Bliley Act, Sarbanes-Oxley Act. Electronics evidence and computer forensics is
scientific collection, examination, authentication, preservation, and analysis of data from
computer storage media for use as evidence in court law.
Information systems controls are both manual-automated controls and general-
application controls. Types of general controls: software, hardware, computer operations,
data security, implementation, and administrative controls. Risk assessment determines
level of risk to firm if specific activity or process is not properly controlled. Security policy
ranks information risks, identifies acceptable security goals, and identifies mechanism for
achieving these goals. Disaster recovery planning devises plans for restoration of disrupted
services. Business continuity planning focuses on restoring business operations after
disaster. Information systems audit examines the firm’s overall security environment as well
as controls governing individual information systems.
Identify management software automates keeping track of all users and privileges.
Authentication refers to the ability to know that a person is who he or she claims to be.
Smart card is a device about the size of a credit card that contains a chip formatted with
access permission and other data. Biometric authentications uses systems that read and
interpret individual human traits (fingerprints, irises, and voices) to grant or deny access.
Two-factor authentication increases security by validating users through a multistep
process.
Firewall prevent unauthorized users from accessing private networks. Intrusion
detection systems feature full-time monitoring tools placed at the most vulnerable point to
detect and deter intruders continually.
Wired Equivalent Privacy (WEP) security can provide some security for Wi-Fi.
Encryption transforming text/data into cipher text that can’t be read by unintended
recipients. Ensuring system availability by online transaction processing, fault-tolerant
computer systems. Controlling network traffic using deep packet inspection (DPI). Security
issues: security in the cloud, securing mobile platforms.
You might also like
- CEH: Certified Ethical Hacker v11 : Exam Cram Notes - First Edition - 2021From EverandCEH: Certified Ethical Hacker v11 : Exam Cram Notes - First Edition - 2021No ratings yet
- 0 - Security and Control in Information System 12-13Document26 pages0 - Security and Control in Information System 12-13Amneet KaurNo ratings yet
- Security: Challenges/Threats To Is SecurityDocument16 pagesSecurity: Challenges/Threats To Is SecuritysarvemNo ratings yet
- Ethical and Security IssuesDocument6 pagesEthical and Security IssuesPaulina BossNo ratings yet
- NSE1 Key Cybersecurity Terms-ENDocument6 pagesNSE1 Key Cybersecurity Terms-ENitachi uchihaNo ratings yet
- Privacy Unit1Document6 pagesPrivacy Unit1SwetankNo ratings yet
- NSE 1 Key Cybersecurity TermsDocument6 pagesNSE 1 Key Cybersecurity TermsJuan Pablo CordobaNo ratings yet
- Summary Chapter 8 Securing Informatin SystemDocument6 pagesSummary Chapter 8 Securing Informatin SystemTasha NurafifahNo ratings yet
- Reflection Chap 07Document3 pagesReflection Chap 07Fizza JunaidNo ratings yet
- Unit IDocument101 pagesUnit IYogita TiwariNo ratings yet
- Information Security: BY: Dr. Shailja TripathiDocument55 pagesInformation Security: BY: Dr. Shailja Tripathisaket kumarNo ratings yet
- Cyber Security CEHDocument5 pagesCyber Security CEHSridhar PNo ratings yet
- System Design and Analysis - Information Security and Cyber CrimeDocument29 pagesSystem Design and Analysis - Information Security and Cyber CrimeMilon MahatoNo ratings yet
- For Final YearDocument13 pagesFor Final YearnishpriyasudhagarNo ratings yet
- Big Data Visualization PowerPoint Templates (Autosaved)Document80 pagesBig Data Visualization PowerPoint Templates (Autosaved)Malek SbNo ratings yet
- Big Data Visualization PowerPoint TemplatesDocument94 pagesBig Data Visualization PowerPoint TemplatesMalek SbNo ratings yet
- Cse - 1Document25 pagesCse - 1santhosh n prabhuNo ratings yet
- Computersecurity 181224070259Document24 pagesComputersecurity 181224070259syedaalishanoor97No ratings yet
- Securing Information Systems: COM 2KA3Document34 pagesSecuring Information Systems: COM 2KA3RyanNo ratings yet
- Module 1Document16 pagesModule 1Shubham SarkarNo ratings yet
- Why Are Information Systems Vulnerable To Destruction, Error, and Abuse ?Document4 pagesWhy Are Information Systems Vulnerable To Destruction, Error, and Abuse ?Urvashi SharmaNo ratings yet
- Cybersecurity PrologueDocument44 pagesCybersecurity PrologueRaj Prabhu RajendranNo ratings yet
- Securing Information SystemsDocument19 pagesSecuring Information SystemsArbab AshrafNo ratings yet
- Ca3 SuggestionsDocument5 pagesCa3 Suggestionsabhijitmandal27068No ratings yet
- Modlue 4: Cybersecurity Awareness: ObjectivesDocument9 pagesModlue 4: Cybersecurity Awareness: ObjectivesJulie RamosNo ratings yet
- Malware and Its TypesDocument5 pagesMalware and Its TypestinashejohnnesonganoNo ratings yet
- Introduction To CybersecurityDocument47 pagesIntroduction To CybersecurityMalek SbNo ratings yet
- COM 426 COMPUT4R SECURITY COURSE NOTEpdfDocument18 pagesCOM 426 COMPUT4R SECURITY COURSE NOTEpdfAhmed SaliuNo ratings yet
- Adware: Adware (Or Advertising Software) Is The Term Used For Various Pop-UpDocument9 pagesAdware: Adware (Or Advertising Software) Is The Term Used For Various Pop-UpG.SowmyaNo ratings yet
- Session13&14 Computing&SecuringISDocument53 pagesSession13&14 Computing&SecuringISSreyas SudarsanNo ratings yet
- Com SciDocument7 pagesCom SciLeinah RamosNo ratings yet
- Chapter 2 Security Threats and CyberattacksDocument9 pagesChapter 2 Security Threats and CyberattacksPaz BarcebalNo ratings yet
- Chapter 5. Cybersecurity and Risk Management TechnologyDocument30 pagesChapter 5. Cybersecurity and Risk Management Technologyarmando.lykajovel.dllNo ratings yet
- Cybersecurity TermsDocument3 pagesCybersecurity TermsMark AminNo ratings yet
- Managing Information Resources and Security: Unintentional ThreatsDocument10 pagesManaging Information Resources and Security: Unintentional Threatsmansi sainiNo ratings yet
- Chapter 8 - Sajorda, KennethDocument22 pagesChapter 8 - Sajorda, KennethlumpasginopaulNo ratings yet
- Siberseguridad Todo Copiado Aqui 2020Document29 pagesSiberseguridad Todo Copiado Aqui 2020vladi reyNo ratings yet
- Cyber Security IntroductionDocument20 pagesCyber Security IntroductionjilikajithendarNo ratings yet
- Cyber Threats and SecurityDocument17 pagesCyber Threats and Securityno OneNo ratings yet
- Unit Internet SecurityDocument29 pagesUnit Internet Securitykapinga0609No ratings yet
- Blue Owl, Member of The Ready Rangers Liberation FrontDocument28 pagesBlue Owl, Member of The Ready Rangers Liberation Frontkousalya06No ratings yet
- Cyber Security MaterialDocument20 pagesCyber Security Materialagentvikram74No ratings yet
- A Literature Survey On Network Attacks and Prevention: AbstractDocument7 pagesA Literature Survey On Network Attacks and Prevention: Abstractmani DILLSNo ratings yet
- Day 3: Introduction To Cyber SecurityDocument18 pagesDay 3: Introduction To Cyber SecurityAdedinewNo ratings yet
- ReportDocument4 pagesReportendurthiabhilashNo ratings yet
- Social, Economic, Ethical and Legal Implications of ComputersDocument11 pagesSocial, Economic, Ethical and Legal Implications of ComputersNitro stormNo ratings yet
- 2.5.1 Information System SecurityDocument32 pages2.5.1 Information System SecurityRishika SinghNo ratings yet
- Review On Malware, Types, and Its AnalysisDocument7 pagesReview On Malware, Types, and Its AnalysisIJRASETPublicationsNo ratings yet
- It ReportDocument20 pagesIt Reportcristine rose celestialNo ratings yet
- Session 1 Cyber Security - Oct 23 2021Document33 pagesSession 1 Cyber Security - Oct 23 2021u9830120786No ratings yet
- Cybersecurity Group 3 Bsa2bDocument45 pagesCybersecurity Group 3 Bsa2bCj AntonioNo ratings yet
- Faculty of Engineering, Sciences & Technology Cryptography and Data Security Assignment Instructor: Ali Ahmad SiddiquiDocument11 pagesFaculty of Engineering, Sciences & Technology Cryptography and Data Security Assignment Instructor: Ali Ahmad SiddiquiUsama AshrafNo ratings yet
- Cyber Security Seminar ReportDocument19 pagesCyber Security Seminar ReportNoobToProytNo ratings yet
- LO1 Asset and Security Threat Week 02Document40 pagesLO1 Asset and Security Threat Week 02kaung kyaw zaNo ratings yet
- Q1 Common Types of Cybersecurity Attacks: 1. MalwareDocument32 pagesQ1 Common Types of Cybersecurity Attacks: 1. MalwareKhateeb AhmadNo ratings yet
- The Set School Computer Class Vii Chapter:Cyber SecurityDocument9 pagesThe Set School Computer Class Vii Chapter:Cyber SecurityAisha Anwar100% (1)
- Introduction To Network SecurityDocument17 pagesIntroduction To Network SecurityAlaiza Moraleda Lopez RomanNo ratings yet
- Why Is Computer Security Important?Document9 pagesWhy Is Computer Security Important?nuhamin desalegnNo ratings yet
- IT NS 1 - Chapter 1b Types of Attacks and DetectionDocument6 pagesIT NS 1 - Chapter 1b Types of Attacks and DetectionGALAPON FRANCISNo ratings yet
- INDIVIDUAL BY StanleyDocument4 pagesINDIVIDUAL BY Stanleyphenomenal 4spNo ratings yet
- Chapter 8 Weekly SummaryDocument2 pagesChapter 8 Weekly SummaryAileen Irmina PutriNo ratings yet
- Joyce2016 PDFDocument13 pagesJoyce2016 PDFAffan ArrizqiNo ratings yet
- Quiz Week 3 - Aileen (440371)Document1 pageQuiz Week 3 - Aileen (440371)Aileen Irmina PutriNo ratings yet
- Chapter 7 Weekly SummaryDocument2 pagesChapter 7 Weekly SummaryAileen Irmina PutriNo ratings yet
- Chapter 1 Weekly Summary AileenDocument2 pagesChapter 1 Weekly Summary AileenAileen Irmina PutriNo ratings yet
- Chapter 6 Weekly SummaryDocument1 pageChapter 6 Weekly SummaryAileen Irmina PutriNo ratings yet
- ILC Week 4 Aileen Irmina P 19:440371:EK:22297Document2 pagesILC Week 4 Aileen Irmina P 19:440371:EK:22297Aileen Irmina PutriNo ratings yet
- SectorUpdate 14JAN19 PDFDocument39 pagesSectorUpdate 14JAN19 PDFAileen Irmina PutriNo ratings yet
- Management Test 3 Aileen Irmina PDocument2 pagesManagement Test 3 Aileen Irmina PAileen Irmina PutriNo ratings yet
- ILC Week 5Document1 pageILC Week 5Aileen Irmina PutriNo ratings yet
- SIT Week 2 Aileen Irmina P. 19.440371.EK.22297Document1 pageSIT Week 2 Aileen Irmina P. 19.440371.EK.22297Aileen Irmina PutriNo ratings yet
- Ux Tdxrt1d6.enDocument22 pagesUx Tdxrt1d6.enAileen Irmina PutriNo ratings yet
- SIT Chapter 3Document1 pageSIT Chapter 3Aileen Irmina PutriNo ratings yet
- SIT Chapter 3Document1 pageSIT Chapter 3Aileen Irmina PutriNo ratings yet
- SIT Week 2 Aileen Irmina P. 19.440371.EK.22297Document1 pageSIT Week 2 Aileen Irmina P. 19.440371.EK.22297Aileen Irmina PutriNo ratings yet
- Security Issues in E CommerceDocument107 pagesSecurity Issues in E CommerceHarish NagNo ratings yet
- Cs707 Current Past Viva Solved Questions1Document4 pagesCs707 Current Past Viva Solved Questions1Zahid Gulzar100% (1)
- Cryptography: Meeting 11Document11 pagesCryptography: Meeting 11Epul PublisherNo ratings yet
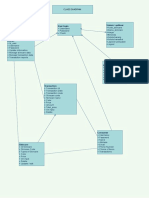
- User Login Sistem / Aplikasi: Class DiagramDocument1 pageUser Login Sistem / Aplikasi: Class Diagramhanifahh alfitri salsabilaNo ratings yet
- Wa0000.Document13 pagesWa0000.talhahussainmangiNo ratings yet
- PT0-101 NetworkArmyDocument84 pagesPT0-101 NetworkArmyMohammad Malek KhataeiNo ratings yet
- Class Diagram Dan Sequence DiagramDocument7 pagesClass Diagram Dan Sequence DiagramJarfa StuffNo ratings yet
- PGP E-Mail SecurityDocument43 pagesPGP E-Mail SecuritySana SaiyedNo ratings yet
- Incident Detection and Response To Suspicious Root Access PlaybookDocument10 pagesIncident Detection and Response To Suspicious Root Access PlaybookirokoNo ratings yet
- Advanced Whiteboard Hacking - Aka Hands-On Threat Modelling: Training Course 30 & 31 of OctoberDocument6 pagesAdvanced Whiteboard Hacking - Aka Hands-On Threat Modelling: Training Course 30 & 31 of OctoberJustin SuthNo ratings yet
- 10 - System Acquisition Development and Maintenance Security Standard v10Document17 pages10 - System Acquisition Development and Maintenance Security Standard v10gemchis dawoNo ratings yet
- PKI - Thesis - Gheller SamuelDocument204 pagesPKI - Thesis - Gheller SamuelSylvain MARETNo ratings yet
- University of Cyprus Department of Computer ScienceDocument23 pagesUniversity of Cyprus Department of Computer SciencestrokenfilledNo ratings yet
- Stream CipherDocument16 pagesStream CipherSanjeev KumarNo ratings yet
- End-User Security Training: Beginners Guide To Keeping Your Information and Computer Safe Kelly Handerhan, InstructorDocument9 pagesEnd-User Security Training: Beginners Guide To Keeping Your Information and Computer Safe Kelly Handerhan, InstructorBan Le VanNo ratings yet
- Cyber Security: Threats, Vulnerabilities and Countermeasures - A Perspective On The State of Affairs in MauritiusDocument15 pagesCyber Security: Threats, Vulnerabilities and Countermeasures - A Perspective On The State of Affairs in MauritiusliezelleannNo ratings yet
- Implementation of Aes and Rsa Algorithm On Hardware PlatformDocument5 pagesImplementation of Aes and Rsa Algorithm On Hardware PlatformHanin TANo ratings yet
- Cyber Security CountermeasuresDocument8 pagesCyber Security CountermeasuresVeena’s AbroadfiaNo ratings yet
- Reset Gmail PasswordDocument7 pagesReset Gmail Passwordaustin roiNo ratings yet
- Risk Treatment Plan: GDPR AssessmentDocument8 pagesRisk Treatment Plan: GDPR AssessmentpanosplhNo ratings yet
- DB - Updateuser - MongoDB ManualDocument13 pagesDB - Updateuser - MongoDB ManualIng Jesus A MtzNo ratings yet
- User Dan Password PoliteknikDocument8 pagesUser Dan Password PoliteknikDaen'k KoerNo ratings yet
- 100 Security BooksDocument2 pages100 Security BooksdinekNo ratings yet
- Windows AuthenticationDocument16 pagesWindows AuthenticationBharti SharmaNo ratings yet
- Graduation Certificate DigitalDocument6 pagesGraduation Certificate DigitalGuilherme CarvalhoNo ratings yet
- Message Authentication CodesDocument46 pagesMessage Authentication CodesSoumak PoddarNo ratings yet
- Blahut CryptographyDocument608 pagesBlahut Cryptographygxsteph100% (2)
- Self Defending NetworksDocument10 pagesSelf Defending NetworksIJRASETPublicationsNo ratings yet
- @somaliliabrary - Barashada Hacking Ka Termux Ee Android IosDocument36 pages@somaliliabrary - Barashada Hacking Ka Termux Ee Android Ioslako karo75% (4)
- 2.4G Basic Network Settings: Enable WLANDocument1 page2.4G Basic Network Settings: Enable WLANHydei CaincayNo ratings yet
- ChatGPT Money Machine 2024 - The Ultimate Chatbot Cheat Sheet to Go From Clueless Noob to Prompt Prodigy Fast! Complete AI Beginner’s Course to Catch the GPT Gold Rush Before It Leaves You BehindFrom EverandChatGPT Money Machine 2024 - The Ultimate Chatbot Cheat Sheet to Go From Clueless Noob to Prompt Prodigy Fast! Complete AI Beginner’s Course to Catch the GPT Gold Rush Before It Leaves You BehindNo ratings yet
- Defensive Cyber Mastery: Expert Strategies for Unbeatable Personal and Business SecurityFrom EverandDefensive Cyber Mastery: Expert Strategies for Unbeatable Personal and Business SecurityRating: 5 out of 5 stars5/5 (1)
- ChatGPT Side Hustles 2024 - Unlock the Digital Goldmine and Get AI Working for You Fast with More Than 85 Side Hustle Ideas to Boost Passive Income, Create New Cash Flow, and Get Ahead of the CurveFrom EverandChatGPT Side Hustles 2024 - Unlock the Digital Goldmine and Get AI Working for You Fast with More Than 85 Side Hustle Ideas to Boost Passive Income, Create New Cash Flow, and Get Ahead of the CurveNo ratings yet
- Algorithms to Live By: The Computer Science of Human DecisionsFrom EverandAlgorithms to Live By: The Computer Science of Human DecisionsRating: 4.5 out of 5 stars4.5/5 (722)
- AI Superpowers: China, Silicon Valley, and the New World OrderFrom EverandAI Superpowers: China, Silicon Valley, and the New World OrderRating: 4.5 out of 5 stars4.5/5 (398)
- Cyber War: The Next Threat to National Security and What to Do About ItFrom EverandCyber War: The Next Threat to National Security and What to Do About ItRating: 3.5 out of 5 stars3.5/5 (66)
- Chaos Monkeys: Obscene Fortune and Random Failure in Silicon ValleyFrom EverandChaos Monkeys: Obscene Fortune and Random Failure in Silicon ValleyRating: 3.5 out of 5 stars3.5/5 (111)
- Generative AI: The Insights You Need from Harvard Business ReviewFrom EverandGenerative AI: The Insights You Need from Harvard Business ReviewRating: 4.5 out of 5 stars4.5/5 (2)
- Digital Gold: Bitcoin and the Inside Story of the Misfits and Millionaires Trying to Reinvent MoneyFrom EverandDigital Gold: Bitcoin and the Inside Story of the Misfits and Millionaires Trying to Reinvent MoneyRating: 4 out of 5 stars4/5 (51)
- Scary Smart: The Future of Artificial Intelligence and How You Can Save Our WorldFrom EverandScary Smart: The Future of Artificial Intelligence and How You Can Save Our WorldRating: 4.5 out of 5 stars4.5/5 (55)
- The Infinite Machine: How an Army of Crypto-Hackers Is Building the Next Internet with EthereumFrom EverandThe Infinite Machine: How an Army of Crypto-Hackers Is Building the Next Internet with EthereumRating: 3 out of 5 stars3/5 (12)
- ChatGPT Millionaire 2024 - Bot-Driven Side Hustles, Prompt Engineering Shortcut Secrets, and Automated Income Streams that Print Money While You Sleep. The Ultimate Beginner’s Guide for AI BusinessFrom EverandChatGPT Millionaire 2024 - Bot-Driven Side Hustles, Prompt Engineering Shortcut Secrets, and Automated Income Streams that Print Money While You Sleep. The Ultimate Beginner’s Guide for AI BusinessNo ratings yet
- The Things We Make: The Unknown History of Invention from Cathedrals to Soda CansFrom EverandThe Things We Make: The Unknown History of Invention from Cathedrals to Soda CansNo ratings yet
- The Intel Trinity: How Robert Noyce, Gordon Moore, and Andy Grove Built the World's Most Important CompanyFrom EverandThe Intel Trinity: How Robert Noyce, Gordon Moore, and Andy Grove Built the World's Most Important CompanyNo ratings yet
- Mini Farming: Self-Sufficiency on 1/4 AcreFrom EverandMini Farming: Self-Sufficiency on 1/4 AcreRating: 4 out of 5 stars4/5 (76)
- Reality+: Virtual Worlds and the Problems of PhilosophyFrom EverandReality+: Virtual Worlds and the Problems of PhilosophyRating: 4 out of 5 stars4/5 (24)
- The Master Algorithm: How the Quest for the Ultimate Learning Machine Will Remake Our WorldFrom EverandThe Master Algorithm: How the Quest for the Ultimate Learning Machine Will Remake Our WorldRating: 4.5 out of 5 stars4.5/5 (107)
- Chip War: The Quest to Dominate the World's Most Critical TechnologyFrom EverandChip War: The Quest to Dominate the World's Most Critical TechnologyRating: 4.5 out of 5 stars4.5/5 (227)
- The Internet Con: How to Seize the Means of ComputationFrom EverandThe Internet Con: How to Seize the Means of ComputationRating: 5 out of 5 stars5/5 (6)
- The Simulated Multiverse: An MIT Computer Scientist Explores Parallel Universes, The Simulation Hypothesis, Quantum Computing and the Mandela EffectFrom EverandThe Simulated Multiverse: An MIT Computer Scientist Explores Parallel Universes, The Simulation Hypothesis, Quantum Computing and the Mandela EffectRating: 4.5 out of 5 stars4.5/5 (20)