Professional Documents
Culture Documents
Introduction To Cybersecurity and Networking: Equipment and Resources Cost/Unit
Uploaded by
J SajatovicOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Introduction To Cybersecurity and Networking: Equipment and Resources Cost/Unit
Uploaded by
J SajatovicCopyright:
Available Formats
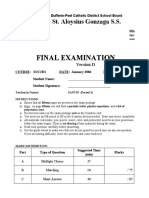
Introduction to Cybersecurity and Networking
Overview This is a full-year course for students in 10th grade and above. It is designed to foster interest in
Information Technology and networking careers. Through hands-on projects, students learn to install
and administer operating systems, to have computers communicate with each other and to detect
and repair vulnerabilities in systems and networks. This course also covers connections of
computing and society, including ethics, security and privacy in on-line communication. Students
taking this course will be expected to take the CompTIA ETF+ and CompTIA A+ certification exams.
Objectives To have students understand the fundamentals of computers, including system
management, hardware configuration, software installation, troubleshooting of operating
system issues and resolution of problems with common applications.
To introduce students to basic cybersecurity concepts.
To prepare students to successfully take the CompTIA ETF+ and CompTIA A+ certification
exams by the end of the course.
To help students prepare for the CompTIA Network+ certification exam, which may require
some further study after completing this course.
To prepare students for more advanced cybersecurity, digital forensics courses and
networking courses.
Assessment Formative assessment includes worksheets, several practice activities and quizzes for each lesson.
Summative assessment includes a test and a project for each unit, and a final exam.
Course Essentials
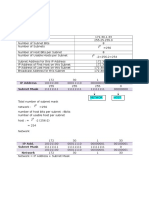
Equipment and Resources Cost/Unit
Classroom set of computers $0 if you already have some, $500-600 per computer if you need to
purchase them.
Network switch, cables and USB keys. About $50-$100 for everything.
Set of spare used computers Cost may vary, depending on whether they can be donated to the school,
bought at surplus stores or otherwise collected from retired inventory.
Budget for the whole set should not go over $500.
Set of Raspberry Pi computer kits Approximately $750 for 10 kits each including a raspberry Pi, RGB LED-
strip, breadboard, MOSFETs, power jack, power supply and jumper wires.
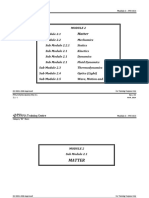
Course Outline
Unit 1: Operating Systems Installing Linux in real and virtual hardware, managing and using Linux,
automating routine tasks. Other operating systems, managing and using
Windows, troubleshooting common issues
Unit 2: Hardware and software Installing and configuring hardware components, device drivers, interfacing
configuration with electronic circuits, sensors and actuators. Raspberry Pi binary clock.
Unit 3: Cybersecurity Authentication, access controls, vulnerabilities, attacks, defenses, secure
fundamentals software design, secure communication, encryption protocols, human-in-the-
loop vulnerabilities, social engineering
Unit 4: Networking OSI network model, Network protocols, wireless and wired networks, network
management, analysis of network traffic, techniques for defending networks,
ethics of online communication
Unit 5: Cryptology Theoretical foundations, bitwise operations, encoding systems, cryptanalysis
of classical cyphers, modern crypto, practical uses: https, block chain, drm,
UEFI
Unit 6: Malware and digital Malicious software, types of malware, functionality, analysis, defense. Legal
forensics issues: evidence acquisition and preservation, digital forensic analysis, storage
forensics, live forensics, memory analysis, reporting findings
You might also like
- IT EssentialsDocument1 pageIT EssentialsAyyodya LuchmiahNo ratings yet
- Flyer Courses - IT EssentialsDocument1 pageFlyer Courses - IT EssentialsAyyodya LuchmiahNo ratings yet
- High-Performance Embedded Computing: Applications in Cyber-Physical Systems and Mobile ComputingFrom EverandHigh-Performance Embedded Computing: Applications in Cyber-Physical Systems and Mobile ComputingNo ratings yet
- Course Outline SCS4110Document3 pagesCourse Outline SCS4110n02019697mNo ratings yet
- Configuring IPCop Firewalls: Closing Borders with Open SourceFrom EverandConfiguring IPCop Firewalls: Closing Borders with Open SourceNo ratings yet
- IT Essentials 1 2 Syllabus Rev Spring 2018Document10 pagesIT Essentials 1 2 Syllabus Rev Spring 2018Dimas Tejo GumilangNo ratings yet
- It Essentials 6.0: PC Hardware and Software (Comptia A+)Document7 pagesIt Essentials 6.0: PC Hardware and Software (Comptia A+)Akibo Tunde Williamson DaviesNo ratings yet
- Raspberry Pi IoT Projects: Prototyping Experiments for MakersFrom EverandRaspberry Pi IoT Projects: Prototyping Experiments for MakersNo ratings yet
- The CompTIA Network+ & Security+ Certification: 2 in 1 Book- Simplified Study Guide Eighth Edition (Exam N10-008) | The Complete Exam Prep with Practice Tests and Insider Tips & Tricks | Achieve a 98% Pass Rate on Your First Attempt!From EverandThe CompTIA Network+ & Security+ Certification: 2 in 1 Book- Simplified Study Guide Eighth Edition (Exam N10-008) | The Complete Exam Prep with Practice Tests and Insider Tips & Tricks | Achieve a 98% Pass Rate on Your First Attempt!No ratings yet
- Defending IoT Infrastructures with the Raspberry Pi: Monitoring and Detecting Nefarious Behavior in Real TimeFrom EverandDefending IoT Infrastructures with the Raspberry Pi: Monitoring and Detecting Nefarious Behavior in Real TimeNo ratings yet
- Cyber SecurityDocument3 pagesCyber Securitysweta.jethava24460No ratings yet
- Computer Networking: Beginners Guide to Network Security & Network Troubleshooting FundamentalsFrom EverandComputer Networking: Beginners Guide to Network Security & Network Troubleshooting FundamentalsNo ratings yet
- Nguyen Tien TungDocument2 pagesNguyen Tien Tungviti_93No ratings yet
- Kali Linux Wireless Penetration Testing EssentialsFrom EverandKali Linux Wireless Penetration Testing EssentialsRating: 5 out of 5 stars5/5 (2)
- Module 3 - IASDocument14 pagesModule 3 - IASKirito ZachariasNo ratings yet
- Cse320 At2Document12 pagesCse320 At2Barnny StinsonNo ratings yet
- CSE Flex Syllabus 1Document15 pagesCSE Flex Syllabus 1Zachary CurtisNo ratings yet
- T.Y B.Tech - Open Elective - 2021Document13 pagesT.Y B.Tech - Open Elective - 2021markeloff d'souzaNo ratings yet
- Infrastructure TracksDocument8 pagesInfrastructure Tracksabdlwhapahmed12No ratings yet
- CSE Live SyllabusDocument18 pagesCSE Live SyllabusAkbar ShakoorNo ratings yet
- Get ConnectedDocument3 pagesGet ConnectedNawaraj Bhandari0% (1)
- C++ Networking 101: Unlocking Sockets, Protocols, VPNs, and Asynchronous I/O with 75+ sample programsFrom EverandC++ Networking 101: Unlocking Sockets, Protocols, VPNs, and Asynchronous I/O with 75+ sample programsNo ratings yet
- Hacking with Kali Linux: A Step by Step Guide to Learn the Basics of Linux Penetration. What A Beginner Needs to Know About Wireless Networks Hacking and Systems Security. Tools Explanation IncludedFrom EverandHacking with Kali Linux: A Step by Step Guide to Learn the Basics of Linux Penetration. What A Beginner Needs to Know About Wireless Networks Hacking and Systems Security. Tools Explanation IncludedNo ratings yet
- Editable Computer Network ManualDocument168 pagesEditable Computer Network ManualPRABHAKAR MORENo ratings yet
- HW MSC m01 f21cnDocument2 pagesHW MSC m01 f21cnphilipyapNo ratings yet
- Ethical Hacking CourseDocument17 pagesEthical Hacking CoursegiansantosmendoncaNo ratings yet
- 7 Bonus ClassesDocument7 pages7 Bonus ClassesDev ZakNo ratings yet
- Cyber Security: Professional Diploma inDocument5 pagesCyber Security: Professional Diploma inAnshpreet SinghNo ratings yet
- Saint Felicity College: College Vision College MissionDocument12 pagesSaint Felicity College: College Vision College MissionUpper Bicutan National High SchoolNo ratings yet
- CBSE Class 10 Computer Applications Syllabus 2019 2020Document7 pagesCBSE Class 10 Computer Applications Syllabus 2019 2020lavish shakyaNo ratings yet
- Computer Networks: MCA-E14: Cryptography & Network SecurityDocument3 pagesComputer Networks: MCA-E14: Cryptography & Network Securitysonali_raisonigroupNo ratings yet
- Assignement # 1 Project ProposalDocument6 pagesAssignement # 1 Project ProposalephertNo ratings yet
- UVA 126638 en US 1118 3 PDFDocument4 pagesUVA 126638 en US 1118 3 PDFKarim MatNo ratings yet
- Applied Cyber Security and the Smart Grid: Implementing Security Controls into the Modern Power InfrastructureFrom EverandApplied Cyber Security and the Smart Grid: Implementing Security Controls into the Modern Power InfrastructureRating: 5 out of 5 stars5/5 (1)
- Python for Cybersecurity Cookbook: 80+ practical recipes for detecting, defending, and responding to Cyber threats (English Edition)From EverandPython for Cybersecurity Cookbook: 80+ practical recipes for detecting, defending, and responding to Cyber threats (English Edition)No ratings yet
- IIT Jammu Times Offers Post Graduate Diploma in Cyber Security - BrochureDocument22 pagesIIT Jammu Times Offers Post Graduate Diploma in Cyber Security - BrochureKhushal OzaNo ratings yet
- Edu 311 8x DatasheetDocument1 pageEdu 311 8x DatasheetPrince Mishra0% (1)
- TECH3701 Security June 2005Document2 pagesTECH3701 Security June 2005conor1990No ratings yet
- KWL TableDocument2 pagesKWL TableDaisaq HadyaNo ratings yet
- EdU 110 8.0Document1 pageEdU 110 8.0asdf2012No ratings yet
- CSD4003 Network-And-System-Security LP 1.0 6 CSD4003Document3 pagesCSD4003 Network-And-System-Security LP 1.0 6 CSD4003VibhuNo ratings yet
- Computer Networking: Beginners Guide to Network Fundamentals, Protocols & Enterprise Network InfrastructureFrom EverandComputer Networking: Beginners Guide to Network Fundamentals, Protocols & Enterprise Network InfrastructureNo ratings yet
- Unit2 NetworkingDocument8 pagesUnit2 Networkingr.elmasri2No ratings yet
- Ieee Research Papers On Network Security PDFDocument8 pagesIeee Research Papers On Network Security PDFefdvje8d100% (1)
- Software SystemDocument15 pagesSoftware SystemkanikaNo ratings yet
- AppendixDocument4 pagesAppendixDiana KhandratianiNo ratings yet
- Resume Faisal ShaikhDocument1 pageResume Faisal Shaikhapi-491240191No ratings yet
- Week 1Document106 pagesWeek 1Thasleem ReyasNo ratings yet
- Tybsc Annexure-II Structure/ Pattern of Syllabus Must Be As FollowsDocument10 pagesTybsc Annexure-II Structure/ Pattern of Syllabus Must Be As FollowsVipul KaushikNo ratings yet
- Master of Science: in Computer SecurityDocument3 pagesMaster of Science: in Computer SecurityPaddy WonderNo ratings yet
- CompTIA Network+Document3 pagesCompTIA Network+homsom100% (1)
- Eleventh Hour Network+: Exam N10-004 Study GuideFrom EverandEleventh Hour Network+: Exam N10-004 Study GuideRating: 5 out of 5 stars5/5 (1)
- Competency Based Learning Material: Maintaining Computer System and NetworksDocument35 pagesCompetency Based Learning Material: Maintaining Computer System and NetworksVictor Dagohoy DumaguitNo ratings yet
- Ch32 Applying Stains and FinishesDocument14 pagesCh32 Applying Stains and FinishesJ SajatovicNo ratings yet
- Name Data FilesDocument1 pageName Data FilesJ SajatovicNo ratings yet
- CreditsDocument1 pageCreditsJ SajatovicNo ratings yet
- Ch16 Gluing and ClampingDocument12 pagesCh16 Gluing and ClampingJ SajatovicNo ratings yet
- Ch15 FastenersDocument12 pagesCh15 FastenersJ SajatovicNo ratings yet
- List Data FilesDocument2 pagesList Data FilesJ SajatovicNo ratings yet
- AssignmentDocument1 pageAssignmentJ SajatovicNo ratings yet
- VEXcode VR ActivitiesDocument6 pagesVEXcode VR ActivitiesJ SajatovicNo ratings yet
- Hard Arch QsDocument12 pagesHard Arch QsJ SajatovicNo ratings yet
- Ics 3 UcourseoutlineDocument6 pagesIcs 3 UcourseoutlineJ SajatovicNo ratings yet
- Handout #2Document1 pageHandout #2J SajatovicNo ratings yet
- Handout #1Document1 pageHandout #1J SajatovicNo ratings yet
- Exam (Jan 2006) (Letter)Document15 pagesExam (Jan 2006) (Letter)J SajatovicNo ratings yet
- Python Guide - Micro - BitDocument28 pagesPython Guide - Micro - BitJ SajatovicNo ratings yet
- Outline of Course of Study - Tdj2o - Part 1 - Fall 2021Document16 pagesOutline of Course of Study - Tdj2o - Part 1 - Fall 2021J SajatovicNo ratings yet
- Outline of Course of Study: Faculty of Engineering Secondary School Department of EngineeringDocument14 pagesOutline of Course of Study: Faculty of Engineering Secondary School Department of EngineeringJ SajatovicNo ratings yet
- 9 12 Unit1 Digitallife102Document10 pages9 12 Unit1 Digitallife102J SajatovicNo ratings yet
- Lesson Lesson Lesson Lesson Plan Plan Plan Plan:::: Your Your Your Your Digital Digital Digital Digital Footprint Footprint Footprint FootprintDocument4 pagesLesson Lesson Lesson Lesson Plan Plan Plan Plan:::: Your Your Your Your Digital Digital Digital Digital Footprint Footprint Footprint FootprintJ SajatovicNo ratings yet
- Outline of Course of Study - Tdj2o - Summer 2021 0Document16 pagesOutline of Course of Study - Tdj2o - Summer 2021 0J SajatovicNo ratings yet
- Symbaloo Manual 2014Document9 pagesSymbaloo Manual 2014J SajatovicNo ratings yet
- SYMBALOO PAGES & OTHER SITES - BrinkerrDocument2 pagesSYMBALOO PAGES & OTHER SITES - BrinkerrJ SajatovicNo ratings yet
- Sym Ball Oo ExistDocument1 pageSym Ball Oo ExistJ SajatovicNo ratings yet
- How To Use A Raspberry Pi 4 As A Minecraft Java Server - Scott Hanselman's BlogDocument3 pagesHow To Use A Raspberry Pi 4 As A Minecraft Java Server - Scott Hanselman's BlogJ SajatovicNo ratings yet
- Formative Assessment in The Computer Science Classroom - Raspberry PiDocument10 pagesFormative Assessment in The Computer Science Classroom - Raspberry PiJ SajatovicNo ratings yet
- Computer Science Principles Performance Tasks - Computer Science 2Document2 pagesComputer Science Principles Performance Tasks - Computer Science 2J SajatovicNo ratings yet
- AP Performance Tasks Teacher GuideDocument4 pagesAP Performance Tasks Teacher GuideJ SajatovicNo ratings yet
- PR Ctice Performace Tasks TierDocument1 pagePR Ctice Performace Tasks TierJ SajatovicNo ratings yet
- Performance Task Explore - Supporting Report of Computer ArtifactDocument4 pagesPerformance Task Explore - Supporting Report of Computer ArtifactJ SajatovicNo ratings yet
- PerfomacetaskDocument3 pagesPerfomacetaskJ SajatovicNo ratings yet
- PythonDocument1 pagePythonJ SajatovicNo ratings yet
- Three Way Conference Template 2019Document4 pagesThree Way Conference Template 2019api-313701922No ratings yet
- Bacterial ClassificationDocument2 pagesBacterial ClassificationAndrew JavierNo ratings yet
- Labour Productivity ChartDocument635 pagesLabour Productivity ChartFrederick AgliamNo ratings yet
- Properties in Shear: (Eg. Ssy 0.5sy)Document34 pagesProperties in Shear: (Eg. Ssy 0.5sy)Yusuf SahinNo ratings yet
- Miestamo Wagner-Nagy 08Document15 pagesMiestamo Wagner-Nagy 08AdjepoleNo ratings yet
- Altronic V Service Manual (FORM AV SM)Document15 pagesAltronic V Service Manual (FORM AV SM)francis_mouille_iiNo ratings yet
- Welding Symbols & Weld PreparationsDocument54 pagesWelding Symbols & Weld PreparationsAmirtha Thiyagaraajan AlagesanNo ratings yet
- Chapter Seven: GS Ohlins Installation, Adjustment Tips & TricksDocument29 pagesChapter Seven: GS Ohlins Installation, Adjustment Tips & TricksWhattonNo ratings yet
- LUXEN SERIES 5 182 144cells 530-550w MONOFACIALDocument2 pagesLUXEN SERIES 5 182 144cells 530-550w MONOFACIALOscar DuduNo ratings yet
- MATLAB Modeling of SPT and Grain Size Data in Producing Soil-ProfileDocument5 pagesMATLAB Modeling of SPT and Grain Size Data in Producing Soil-Profileicv.xaviNo ratings yet
- JCrenshaw ImplementingCRCsDocument17 pagesJCrenshaw ImplementingCRCsspyeagleNo ratings yet
- Fdot Modifications To LRFD Specifications For Structural Supports For Highway Signs, Luminaires and Traffic Signals (Lrfdlts-1)Document26 pagesFdot Modifications To LRFD Specifications For Structural Supports For Highway Signs, Luminaires and Traffic Signals (Lrfdlts-1)kayshephNo ratings yet
- Pengaruh Customer Experience Terhadap Kepuasan Pelanggan Dan Loyalitas Pelanggan Survei Pada Pelanggan KFC Kawi MalangDocument6 pagesPengaruh Customer Experience Terhadap Kepuasan Pelanggan Dan Loyalitas Pelanggan Survei Pada Pelanggan KFC Kawi MalangSatria WijayaNo ratings yet
- Assigment Sheet Tast 2 Aina MardianaDocument10 pagesAssigment Sheet Tast 2 Aina MardianaAina MardianaNo ratings yet
- Why Might Some People Regard Science As The Supreme Form of All KnowledgeDocument4 pagesWhy Might Some People Regard Science As The Supreme Form of All KnowledgexxxsyedxxNo ratings yet
- Сравнит. лингвистикаDocument22 pagesСравнит. лингвистикаАнастасия ДобровольскаяNo ratings yet
- Lista Ejercicios 3 PPEDocument25 pagesLista Ejercicios 3 PPEKarla HermorNo ratings yet
- InfiniBand WikipediaDocument2 pagesInfiniBand WikipediaYoussef BoukhdimiNo ratings yet
- L28-32H GenSet TierII PDFDocument824 pagesL28-32H GenSet TierII PDFHelder Pinto100% (1)
- PIA B2 - Module 2 (PHYSICS) SubModule 2.1 (Matter) Final1Document17 pagesPIA B2 - Module 2 (PHYSICS) SubModule 2.1 (Matter) Final1samarrana1234679No ratings yet
- Srinivasan Engineering College, Perambalur: Part B Unit IDocument2 pagesSrinivasan Engineering College, Perambalur: Part B Unit IPrabhat SinghNo ratings yet
- Topic 9 - Transport in Animals: Blood and Lymph VesselsDocument15 pagesTopic 9 - Transport in Animals: Blood and Lymph Vesselsgytfnhj.comNo ratings yet
- Aviation Service ManualDocument28 pagesAviation Service ManualArmo MoralesNo ratings yet
- Workbook Theory Grade Six SampleDocument4 pagesWorkbook Theory Grade Six SampleRobert TseNo ratings yet
- M2-Exam 2Document13 pagesM2-Exam 2youngturtlevibesNo ratings yet
- Kanban Scheduling SystemsDocument8 pagesKanban Scheduling SystemsharsurajNo ratings yet
- Applied Dynamics PDFDocument862 pagesApplied Dynamics PDFLeonardo Mereles100% (1)
- Department of Mechanical Engineering Question Bank Subject Name: Heat & Mass Transfer Unit - I Conduction Part - ADocument3 pagesDepartment of Mechanical Engineering Question Bank Subject Name: Heat & Mass Transfer Unit - I Conduction Part - AkarthikNo ratings yet
- Lte OptimizationDocument323 pagesLte Optimizationkumar100% (2)
- Review Article: Biomedical Applications of Shape Memory AlloysDocument16 pagesReview Article: Biomedical Applications of Shape Memory AlloysAntonela-Georgiana MateiNo ratings yet