Professional Documents
Culture Documents
Enterprise Resource Planning1
Uploaded by
Muhammed AjmalCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Enterprise Resource Planning1
Uploaded by
Muhammed AjmalCopyright:
Available Formats
Enterprise Resource Planning System Project Report
1. PROFILE OF THE PROBLEM
STAS, Pathanamthitta Page | 1
Enterprise Resource Planning System Project Report
1.1ABOUT THE PROJECT
ERP stands for Enterprise Resource Planning.
Accounting software needs access to information in each area of organization and market
research through manufacturing, distribution and sales.
Financial solution must provide the management with information that can be leveraged
for strategic decisions, in order to achieve comprehensive advantage.
This section provides an overview of the financial solutions in most the ERP packages.
In today’s business enterprise, user need to know that your financial decisions are based
on today’s data, not numbers from records closed a month ago, or even a week ago.
The Finance modules of the most ERP systems provide financial functionality and
analysis support to thousands of businesses in many countries across the globe.
These ERP systems include not only financial application components, but also Human
resources, Purchase, Stock and Sales.
There are a FIVE main module in this ERP system.
1) Human Resource :-
a. Maintain Employee Attendance
b. Approve / Reject Employee Leaves
c. Maintain Employee Records
d. Generate Employee Payslip
2) Account :-
a. Customer Payment
b. Vendor Payment
c. Cash Register
3) Purchase :-
a. Request for Quotation
b. Create Purchase Order
c. Purchase Invoice / Bill
STAS, Pathanamthitta Page | 2
Enterprise Resource Planning System Project Report
d. Give Feedback
4) Store :-
a. Inward Material Detail
b. Maintain Stock
c. Outward Material Detail
d. Waste / Return Material Detail
5) Sales :-
a. Create Sales Quotation
b. Sales Order
c. Sales Invoice / Bill
d. Customer Feed
STAS, Pathanamthitta Page | 3
Enterprise Resource Planning System Project Report
2. SYSTEM STUDY
STAS, Pathanamthitta Page | 4
Enterprise Resource Planning System Project Report
2.1 INTRODUCTION
System Study is a general term that refers to an orderly, structured
process for identifying and solving problems. We call system Study process lifecycle
methodology, since it relates to four significant phases in the lifecycle of all business
information system. The system is studied to the minute details and analyzed. Analysis
implies the process of breaking something into parts so that the whole may be understood.
The definition of the system analysis includes not only the process of analysis but also that of
synthesis, which implies the process of putting together to form a new whole.
All activities associated with each life cycle phase must be performed, managed and
documented. Hence, we define system analysis as the performance, management,
documentation of the activities related to the life cycle phases of a computer-based business
system. In the study phase a detailed study of the project is made and clear picture of the
project is in mind. In the design phase the designing of the input, output and table designs are
made. Development phase is where the physical designing of the input-output screens and
coding of the system is done. System implementation actually implements the system by
making necessary testing.
2.2 EXISTING SYSTEM
No centralize system
Centralized database is not there by which you can access.
Not User Friendly
The existing system is not user friendly because the retrieval of data is
very slow and data is not maintained efficiently.
Difficulty in report generating
We require more calculations to generate the report so it is generated at the
end of the session.
Manual control
All calculations to generate report is done manually so there is greater
chance of errors.
STAS, Pathanamthitta Page | 5
Enterprise Resource Planning System Project Report
Lots of paperwork
Existing system requires lot of paper work. Loss of even a single
Register/record led to difficult situation because all the papers are needed
to generate the reports.
Time consuming
Every work is done manually so we cannot generate report in the middle
of the session or as per the requirement because it is very time consuming.
2.3 PROPOSED SYSTEM
The fundamental advantage of ERP is that it saves time and expense.
Decisions can be made more quickly and with fewer errors.
Data becomes visible across the organization.
They eliminate the need to synchronize changes between multiple systems.
Reduced requirement of manpower.
Increased customer satisfaction.
Enables global outreach.
Quick searching option.
Eliminate unnecessary paperwork.
STAS, Pathanamthitta Page | 6
Enterprise Resource Planning System Project Report
3. PROBLEM ANALYSIS
STAS, Pathanamthitta Page | 7
Enterprise Resource Planning System Project Report
3.1 SYSTEM DEFENITION
The project Enterprise Resource Planning System is developed
using C#.Net. The new user can register and only the registered user can go further. The
administrator can control all the operations in the website. He can also modify and upload
data to the website. The registered user can see all information about the products, searching
and viewing product details. The website is designed in such a way that the future plans of
expansion can be implementing easily without affecting the existing features. The website
and its operations should be safe and unauthorized access should not be allowed. The user is
able to view the product details only if he is logged in and active user.
3.2 FEASIBILITY ANALYSIS
A feasibility study is a test of system proposal according to its
workability, impact on the organization, ability to meet user needs, and effective use of
resources. The objective of feasibility study is acquiring a sense of the scope of the system.
The feasibility of a project can be ascertained in terms of technical
factors, economic factors, or both. A feasibility study is documented with a report showing
all the ramifications of the project. It is very important to evaluate the feasibility study and
risk analysis is related in many ways. If the project study is great, the feasibility of producing
quality software is reduced.
The key factors considered during the feasibility study are:
1. Economic Feasibility
2. Behavioral Feasibility
3. Technical Feasibility
4. Operational Feasibility
5. Legal Feasibility
STAS, Pathanamthitta Page | 8
Enterprise Resource Planning System Project Report
3.2.1 ECONOMIC FEASIBILITY
Economic analysis is the most commonly used method for evaluating
effectiveness of a system. Cost-benefit analysis is the most important assessment of economic
justification of the project. Cost –benefit analysis delineates the cost for project development
and weighs them against tangible and intangible benefits of a system. This type of analysis
varies with the characteristics of the system to be developed, the relative site of the project,
and the expected return on investment. Benefits of a new system are always determined
relative to the existing mode of operation.
Economic feasibility deals about the economic impact faced by the
organization to implement the new system. Not only cost of hardware, software etc. is
considered but also the form of reduced costs. The project, installed certainly be beneficial
since there will be a reduction in manual wok, increase in speed of work. The analysis raises
financial and economic questions during the preliminary investigation to estimate the
following:
The cost to conduct a full systems investigation.
The cost of hardware and software for the class of application of the project being
considered.
To be judged feasible, a proposal for the specific project must pass all these tests, otherwise it
is not considered as a feasible project. I gathered the details regarding the financial aspects
incorporated in the system to make it cost efficient.
3.2.2 BEHAVIORAL FEASIBILITY
Proposed projects are beneficial only if they can be turned into
information systems that will meet the operating requirements of the organization. This test
of feasibility asks if the system will work when it is developed satisfies all the operational
conditions. It was the most difficult task for me, but met efficiently.
As this package is found to be feasible technically, economically and
functionally, the system is judged feasible. Viewing the collected information,
STAS, Pathanamthitta Page | 9
Enterprise Resource Planning System Project Report
recommendation and justification, conclusions is made of the proposed system. Hence
decision is taken to go on with the project.
3.2.3 TECHNICAL FEASIBILITY
There are a number of technical issues, which are generally raised during
the feasibility stage of the investigation. A study of function, performance and constraints
gave me the ability to achieve acceptable system. The software required for this system is:
VISUAL STUDIO 2017
SQL SERVER 2019
3.2.4 OPERATIONAL FEASIBILITY
Suppose for a moment that technical and economic resources are both
judged adequate. The systems analyst must still consider the operational feasibility of the
requested project. Operational feasibility is dependent on human resources available for the
project and involves projecting whether the system will operate and be used once it is
installed. If users are virtually wed to the present system, see no problems with it, and
generally are not involved in requesting a new system, resistance to implementing the new
system will be strong. Chances for it ever becoming operational are low.
3.2.5 LEGAL FEASIBILITY
A determination of any infringement, violation, or liability that could
result from development of the system. Legal feasibility encompasses a broad range of
concerns that include contracts, liability, infringement, and myriad other traps frequently
unknown to technical staff.
STAS, Pathanamthitta Page | 10
Enterprise Resource Planning System Project Report
3.3 PROJECT PLAN
Planning is very important in every aspect of development work. Good
managers carefully monitor developments at various phases. Improper planning leads to
failure of the project. Software project pan can be viewed as the following:
1. within the organization: How the project is to be implemented? What are various
constraints? What is market strategy?
2. With respect to the customer: Weekly or timely meetings with the customer with
presentations on status reports. Customer feedback is also taken and further modifications
and developments are done. Project milestones and deliverables are also presented to the
customer. For a successful project the following steps can be followed:
Selection of project: Includes identifying project’s aims and objectives, understanding
requirements and specification, methods of analysis, design and implementation, testing
techniques and documentation.
Project milestones and deliverables.
Project estimates: including cost, time, size of code and duration.
Resource allocation: including hardware, software, previous relevant project
information and digital library.
Risk management: including risk avoidance, risk detection, risk control and risk
recovery.
Scheduling techniques: including work breakdown structure, activity graph, critical
path method, Gantt chart and Program Evaluation Review Technique.
People: including staff recruitment, team management and customer interaction.
Quality control and standard.
STAS, Pathanamthitta Page | 11
Enterprise Resource Planning System Project Report
Fig: Gantt chart
STAS, Pathanamthitta Page | 12
Enterprise Resource Planning System Project Report
4. REQUIREMENT ENGINEERING
STAS, Pathanamthitta Page | 13
Enterprise Resource Planning System Project Report
4.1 INTRODUCTION
Requirement analysis involves studying the current system to find out how
it works and where improvements could be made. A clear idea about the existing system is a
must for making improvements where it is required. Proper planning and collection of data
serves the purpose. The popularity of this document is to describe all the requirements for the
popularity of the website for Enterprise Resource Planning System. This website gives all the
information for a person. In our busy life, we cannot go to each department or offices. This
problem will manage this site. It will help to avoid in correction and missing data.
4.2 SPECIFIC REQUIREMENTS
HARDWARE REQUIREMENTS:
CPU - 1.8 GHz or faster processor
HARD DISK SPACE - Minimum 160GB
RAM - 2GB or more
WEB SERVER - IIS
CODING LANGUAGE - C#.Net
FRONT END - Microsoft Visual Studio .Net 2017
BACK END - SQL Server 2019
OPERATING SYSTEM - Windows (Any Version)
SOFTWARE REQUIREMENTS:
Introduction to .NET
When .NET was announced in late 1999, Microsoft positioned the technology as a platform
for building and consuming Extensible Markup Language (XML) Web services. XML Web
STAS, Pathanamthitta Page | 14
Enterprise Resource Planning System Project Report
services allow any type of application, be it a Windows- or browser-based application
running on any type of computer system, to consume data from any type of server over the
Internet. The reason this idea is so great is the way in which the XML messages are
transferred: over established standard protocols that exist today. Using protocols such as
SOAP, HTTP, and SMTP, XML Web services make it possible to expose data over the wire
with little or no modifications to your existing code.
Figure 1.1 presents a high-level overview of the .NET Framework and how XML
Web services are positioned.
Stateless XML Web services Modal
Since the initial announcement of the .NET Framework, it's taken on many new and
different meanings to different people. To a developer, .NET means a great environment for
creating robust distributed applications. To an IT manager, .NET means simpler deployment
of applications to end users, tighter security, and simpler management. To a CTO or CIO,
STAS, Pathanamthitta Page | 15
Enterprise Resource Planning System Project Report
.NET means happier developers using state-of-the-art development technologies and a
smaller bottom line. To understand why all these statements are true, you need to get a grip
on what the .NET Framework consists of, and how it's truly a revolutionary step forward for
application architecture, development, and deployment.
.NET Framework
Now that you are familiar with the major goals of the .NET Framework, let's briefly
examine its architecture. As you can see in Figure 1-2, the .NET Framework sits on top of the
operating system, which can be a few different flavors of Windows and consists of a number
of components .NET is essentially a system application that runs on Windows.
Conceptually, the CLR and the JVM are similar in that they are both runtime infrastructures
that abstract the underlying platform differences. However, while the JVM officially supports
only the Java language, the CLR supports any language that can be represented in its
Common Intermediate Language (CIL). The JVM executes bytecode, so it can, in principle,
support many languages, too. Unlike Java's bytecode, though, CIL is never interpreted.
Another conceptual difference between the two infrastructures is that Java code runs on any
platform with a JVM, whereas .NET code runs only on platforms that support the CLR. In
April, 2003, the International Organization for Standardization and the International Electro
technical Committee (ISO/IEC) recognized a functional subset of the CLR, known as the
Common Language Interface (CLI), as an international standard. This development, initiated
by Microsoft and developed by ECMA International, a European standards organization,
STAS, Pathanamthitta Page | 16
Enterprise Resource Planning System Project Report
opens the way for third parties to implement their own versions of the CLR on other
platforms, such as Linux or Mac OS X. For information on third-party and open source
projects working to implement the ISO/IEC CLI and C# specifications
The layer on top of the CLR is a set of framework base classes. This set of classes is
similar to the set of classes found in STL, MFC, ATL, or Java. These classes support
rudimentary input and output functionality, string manipulation, security management,
network communications, thread management, text management, reflection functionality,
collections functionality, as well as other functions.
On top of the framework base classes is a set of classes that extend the base classes to
support data management and XML manipulation. These classes, called ADO.NET, support
persistent data management—data that is stored on backend databases. Alongside the data
classes, the .NET Framework supports a number of classes to let you manipulate XML data
and perform XML searching and XML translations.
Classes in three different technologies (including web services, Web Forms, and
Windows Forms) extend the framework base classes and the data and XML classes. Web
services include a number of classes that support the development of lightweight distributed
components, which work even in the face of firewalls and NAT software. These components
support plug-and-play across the Internet, because web services employ standard HTTP and
SOAP.
Web Forms, the key technology behind ASP.NET, include a number of classes that
allow you to rapidly develop web Graphical User Interface (GUI) applications. If you're
currently developing web applications with Visual Interdev, you can think of Web Forms as a
facility that allows you to develop web GUIs using the same drag-and-drop approach as if
you were developing the GUIs in Visual Basic. Simply drag-and-drop controls onto your
Web Form, double-click on a control, and write the code to respond to the associated event.
Windows Forms support a set of classes that allow you to develop native Windows
GUI applications. You can think of these classes collectively as a much better version of the
MFC in C++ because they support easier and more powerful GUI development and provide a
common, consistent interface that can be used in all languages.
STAS, Pathanamthitta Page | 17
Enterprise Resource Planning System Project Report
The Common Language Runtime
At the heart of the .NET Framework is the common language runtime. The common language
runtime is responsible for providing the execution environment that code written in a .NET
language runs under. The common language runtime can be compared to the Visual Basic 6
runtime, except that the common language runtime is designed to handle all .NET languages,
not just one, as the Visual Basic 6 runtime did for Visual Basic 6. The following list describes
some of the benefits the common language runtime gives you:
Automatic memory management
Cross-language debugging
Cross-language exception handling
Full support for component versioning
Access to legacy COM components
XCOPY deployment
Robust security model
You might expect all those features, but this has never been possible using Microsoft
development tools. Figure 1.3 shows where the common language runtime fits into the .NET
Framework.
The common language runtime and the .NET Framework
STAS, Pathanamthitta Page | 18
Enterprise Resource Planning System Project Report
Note
Code written using a .NET language is known as managed code. Code that uses
anything but the common language runtime is known as unmanaged code. The common
language runtime provides a managed execution environment for .NET code, whereas the
individual runtimes of non-.NET languages provide an unmanaged execution environment.
Inside the Common Language Runtime
The common language runtime enables code running in its execution environment to have
features such as security, versioning, memory management and exception handling because
of the way .NET code actually executes. When you compiled Visual Basic 6 forms
applications, you had the ability to compile down to native node or p-code. Figure 1.4 should
refresh your memory of what the Visual Basic 6 options dialog looked It.
When you compile your applications in .NET, you aren't creating anything in native
code. When you compile in .NET, you're converting your code—no matter what .NET
language you're using—into an assembly made up of an intermediate language called
Microsoft Intermediate Language (MSIL or just IL, for short). The IL contains all the
information about your application, including methods, properties, events, types, exceptions,
STAS, Pathanamthitta Page | 19
Enterprise Resource Planning System Project Report
security objects, and so on, and it also includes metadata about what types in your code can
or cannot be exposed to other applications. This was called a type library in Visual Basic 6 or
an IDL (interface definition language) file in C++. In .NET, it's simply the metadata that the
IL contains about your assembly.
Note
The file format for the IL is known as PE (portable executable) format, which is a
standard format for processor-specific execution.
When a user or another component executes your code, a process occurs called just-
in-time (JIT) compilation, and it's at this point that the IL is converted into the specific
machine language of the processor it's executing on. This makes it very easy to port a .NET
application to any type of operating system on any type of processor because the IL is simply
waiting to be consumed by a JIT compiler.
Note
The first time an assembly is called in .NET, the JIT process occurs. Subsequent calls
don't re-JIT the IL; the previously JITted IL remains in cache and is used over and over
again. when you learn about Application Center Test, you also see how the warm-up time of
the JIT process can affect application performance.
Understanding the process of compilation in .NET is very important because it makes
clear how features such as cross-language debugging and exception handling are possible.
You're not actually compiling to any machine-specific code—you're simply compiling down
to an intermediate language that's the same for all .NET languages. The IL produced by J#
.NET and C# looks just like the IL created by the Visual Basic .NET compiler. These
instructions are the same, only how you type them in Visual Studio .NET is different, and the
power of the common language runtime is apparent.
When the IL code is JIT ted into machine-specific language, it does so on an as-needed
basis. If your assembly is 10MB and the user is only using a fraction of that 10MB, only the
required IL and its dependencies are compiled to machine language. This makes for a very
efficient execution process. But during this execution, how does the common language
STAS, Pathanamthitta Page | 20
Enterprise Resource Planning System Project Report
runtime make sure that the IL is correct? Because the compiler for each language creates its
own IL, there must be a process that makes sure what's compiling won't corrupt the system.
The process that validates the IL is known as verification. Figure 1.5 demonstrates the
process the IL goes through before the code actually executes.
Figure 1.5. The JIT process and verification.
When code is JIT compiled, the common language runtime checks to make sure that the IL is
correct. The rules that the common language runtime uses for verification are set forth in the
Common Language Specification (CLS) and the Common Type System (CTS).
The .NET Framework Class Library
The second most important piece of the .NET Framework is the .NET Framework class
library (FCL). As you've seen, the common language runtime handles the dirty work of
actually running the code you write. But to write the code, you need a foundation of available
STAS, Pathanamthitta Page | 21
Enterprise Resource Planning System Project Report
classes to access the resources of the operating system, database server, or file server. The
FCL is made up of a hierarchy of namespaces that expose classes, structures, interfaces,
enumerations, and delegates that give you access to these resources.
The namespaces are logically defined by functionality. For example, the System.Data
namespace contains all the functionality available to accessing databases. This namespace is
further broken down into System.Data.SqlClient, which exposes functionality specific to
SQL Server, and System.Data.OleDb, which exposes specific functionality for accessing
OLEDB data sources. The bounds of a namespace aren't necessarily defined by specific
assemblies within the FCL; rather, they're focused on functionality and logical grouping. In
total, there are more than 20,000 classes in the FCL, all logically grouped in a hierarchical
manner. Figure 1.8 shows where the FCL fits into the .NET Framework and the logical
grouping of namespace. The .NET Framework class library.
To use an FCL class in your application, you use the Imports statement in Visual
Basic .NET or the using statement in C#. When you reference a namespace in Visual
Basic .NET or C#, you also get the convenience of auto-complete and auto-list members
when you access the objects' types using Visual Studio .NET. This makes it very easy to
determine what types are available for each class in the namespace you're using. As you'll see
over the next several weeks, it's very easy to start coding in Visual Studio .NET.
To understand how the common language runtime manages code execution, you must
examine the structure of a .NET application. The primary unit of a .NET application is the
assembly. An assembly is a self-describing collection of code, resources, and metadata. The
assembly manifest contains information about what is contained within the assembly. The
assembly manifest provides:
Identity information, such as the assembly’s name and version number
A list of all types exposed by the assembly
A list of other assemblies required by the assembly
A list of code access security instructions, including permissions required by the
assembly and permissions to be denied the assembly
STAS, Pathanamthitta Page | 22
Enterprise Resource Planning System Project Report
Each assembly has one and only one assembly manifest, and it contains all the description
information for the assembly. However, the assembly manifest can be contained in its own
file or within one of the assembly’s modules.
An assembly contains one or more modules. A module contains the code that makes up
your application or library, and it contains metadata that describes that code. When you
compile a project into an assembly, your code is converted from high-level code to IL.
Because all managed code is first converted to IL code, applications written in different
languages can easily interact. For example, one developer might write an application in
Visual C# that accesses a DLL in Visual Basic .NET. Both resources will be converted to IL
modules before being executed, thus avoiding any language-incompatibility issues.
Each module also contains a number of types. Types are templates that describe a set of
data encapsulation and functionality. There are two kinds of types: reference types (classes)
and value types (structures). These types are discussed in greater detail in Lesson 2 of this
chapter. Each type is described to the common language runtime in the assembly manifest. A
type can contain fields, properties, and methods, each of which should be related to a
common functionality. For example, you might have a class that represents a bank account. It
contains fields, properties, and methods related to the functions needed to implement a bank
account. A field represents storage of a particular type of data. One field might store the name
of an account holder, for example. Properties are similar to fields, but properties usually
provide some kind of validation when data is set or retrieved. You might have a property that
represents an account balance. When an attempt is made to change the value, the property can
check to see if the attempted change is greater than a predetermined limit. If the value is
greater than the limit, the property does not allow the change. Methods represent behavior,
such as actions taken on data stored within the class or changes to the user interface.
Continuing with the bank account example, you might have a Transfer method that transfers
a balance from a checking account to a savings account, or an Alert method that warns users
when their balances fall below a predetermined level.
Compilation and Execution of a .NET Application
STAS, Pathanamthitta Page | 23
Enterprise Resource Planning System Project Report
When you compile a .NET application, it is not compiled to binary machine code; rather,
it is converted to IL. This is the form that your deployed application takes—one or more
assemblies consisting of executable files and DLL files in IL form. At least one of these
assemblies will contain an executable file that has been designated as the entry point for the
application.
When execution of your program begins, the first assembly is loaded into memory. At
this point, the common language runtime examines the assembly manifest and determines the
requirements to run the program. It examines security permissions requested by the assembly
and compares them with the system’s security policy. If the system’s security policy does not
allow the requested permissions, the application will not run. If the application passes the
system’s security policy, the common ¬language runtime executes the code. It creates a
process for the application to run in and begins application execution. When execution starts,
the first bit of code that needs to be executed is loaded into memory and compiled into native
binary code from IL by the common language runtime’s Just-In-Time (JIT) compiler. Once
compiled, the code is executed and stored in memory as native code. Thus, each portion of
code is compiled only once when an application executes. Whenever program execution
branches to code that has not yet run, the JIT compiler compiles it ahead of execution and
stores it in memory as binary code. This way, application performance is maximized because
only the parts of a program that are executed are compiled.
The .NET Framework base class library contains the base classes that provide many of the
services and objects you need when writing your applications. The class library is organized
into namespaces. A namespace is a logical grouping of types that perform related functions.
For example, the System.Windows.Forms namespace contains all the types that make up
Windows forms and the controls used in those forms.
Namespaces are logical groupings of related classes. The namespaces in the .NET
base class library are organized hierarchically. The root of the .NET Framework is the
System namespace. Other namespaces can be accessed with the period operator. A typical
namespace construction appears as follows:
STAS, Pathanamthitta Page | 24
Enterprise Resource Planning System Project Report
System
System.Data
System. Data. SQLClient
The first example refers to the System namespace. The second refers to the
System.Data namespace. The third example refers to the System.Data.SQLClient namespace.
Table 1.1 introduces some of the more commonly used .NET base class namespaces.
Table 1-1. Representative .NET Namespaces
Namespace Description
System This namespace is the root for many of the low-level types
required by the .NET Framework. It is the root for primitive
data types as well, and it is the root for all the other
namespaces in the .NET base class library.
System.Collections This namespace contains classes that represent a variety of
different container types, such as ArrayList, SortedList,
Queue, and Stack. You also can find abstract classes, such
as CollectionBase, which are useful for implementing your
own collection functionality.
System.ComponentModel This namespace contains classes involved in component
creation and containment, such as attributes, type
converters, and license providers.
System.Data This namespace contains classes required for database
access and manipulations, as well as additional namespaces
used for data access.
System.Data.Common This namespace contains a set of classes that are shared by
the .NET managed data providers.
System.Data.OleDb This namespace contains classes that make up the managed
data provider for OLE DB data access.
System.Data.SQLClient This namespace contains classes that are optimized for
interacting with Microsoft SQL Server.
System.Drawing This namespace exposes GDI+ functionality and provides
classes that facilitate graphics rendering.
System.IO In this namespace, you will find types for handling file
system I/O.
System.Math This namespace is home to common mathematics functions
STAS, Pathanamthitta Page | 25
Enterprise Resource Planning System Project Report
such as extracting roots and trigonometry.
System.Reflection This namespace provides support for obtaining information
and dynamic creation of types at runtime.
System.Security This namespace is home to types dealing with permissions,
cryptography, and code access security.
System.Threading This namespace contains classes that facilitate the
implementation of multithreaded applications.
System.Windows.Forms This namespace contains types involved in creating standard
Windows applications. Classes that represent forms and
controls reside here as well.
The namespace names are self-descriptive by design. Straightforward names make the .NET
Framework easy to use and allow you to rapidly familiarize yourself with its contents.
Introduction to Object-Oriented Programming
Programming in the .NET Framework environment is done with objects. Objects are
programmatic constructs that represent packages of related data and functionality. Objects are
self-contained and expose specific functionality to the rest of the application environment
without detailing the inner workings of the object itself. Objects are created from a template
called a class. The .NET base class library provides a set of classes from which you can
create objects in your applications. You also can use the Microsoft Visual Studio
programming environment to create your own classes. This lesson introduces you to the
concepts associated with object-oriented programming.
Objects, Members, and Abstraction
An object is a programmatic construct that represents something. In the real world,
objects are cars, bicycles, laptop computers, and so on. Each of these items exposes specific
functionality and has specific properties. In your application, an object might be a form, a
control such as a button, a database connection, or any of a number of other constructs. Each
object is a complete functional unit, and contains all of the data and exposes all of the
functionality required to fulfill its purpose. The ability of programmatic objects to represent
real-world objects is called abstraction.
STAS, Pathanamthitta Page | 26
Enterprise Resource Planning System Project Report
Classes Are Templates for Objects
Classes were discussed in Chapter 1 and represent user-defined reference types. Classes
can be thought of as blueprints for objects: they define all of the members of an object, define
the behavior of an object, and set initial values for data when appropriate. When a class is
instantiated, an in-memory instance of that class is created. This instance is called an object.
To review, a class is instantiated using the New (new) keyword as follows:
Visual Basic .NET
' Declares a variable of the Widget type
Dim myWidget As Widget
' Instantiates a new Widget object and assigns it to the myWidget
' variable
myWidget = New Widget()
When an instance of a class is created, a copy of the instance data defined by that
class is created in memory and assigned to the reference variable. Individual instances of a
class are independent of one another and represent separate programmatic constructs. There
is generally no limit to how many copies of a single class can be instantiated at any time. To
use a real-world analogy, if a car is an object, the plans for the car are the class. The plans can
be used to make any number of cars, and changes to a single car do not, for the most part,
affect any other cars.
Objects and Members
Objects are composed of members. Members are properties, fields, methods, and events,
and they represent the data and functionality that comprise the object. Fields and properties
represent data members of an object. Methods are actions the object can perform, and events
are notifications an object receives from or sends to other objects when activity happens in
the application.
To continue with the real-world example of a car, consider that a Car object has fields
and properties, such as Color, Make, Model, Age, GasLevel, and so on. These are the data
that describe the state of the object. A Car object might also expose several methods, such as
STAS, Pathanamthitta Page | 27
Enterprise Resource Planning System Project Report
Accelerate, ShiftGears, or Turn. The methods represent behaviors the object can execute.
And events represent notifications. For example, a Car object might receive an
EngineOverheating event from its Engine object, or it might raise a Crash event when
interacting with a Tree object.
Object Models
Simple objects might consist of only a few properties, methods, and perhaps an event or
two. More complex objects might require numerous properties and methods and possibly
even subordinate objects. Objects can contain and expose other objects as members. For
example, the TextBox control exposes a Font property, which consists of a Font object.
Similarly, every instance of the Form class contains and exposes a Controls collection that
comprises all of the controls contained by the form. The object model defines the hierarchy of
contained objects that form the structure of an object.
An object model is a hierarchical organization of subordinate objects contained and
exposed within a main object. To illustrate, let’s revisit the example of a car as an object. A
car is a single object, but it also consists of subordinate objects. A Car object might contain
an Engine object, four Wheel objects, a Transmission object, and so on. The composition of
these subordinate objects directly affects how the Car object functions as a whole. For
example, if the Cylinders property of the Engine subordinate object is equal to 4, the Car will
behave differently than a Car whose Engine has a Cylinders property value of 8. Contained
objects can have subordinate objects of their own. For example, the contained Engine object
might contain several SparkPlug objects.
Encapsulation
Encapsulation is the concept that implementation of an object is independent of its
interface. Put another way, an application interacts with an object through its interface, which
consists of its public properties and methods. As long as this interface remains constant, the
application can continue to interact with the component, even if implementation of the
interface was completely rewritten between versions.
STAS, Pathanamthitta Page | 28
Enterprise Resource Planning System Project Report
Objects should only interact with other objects through their public methods and
properties. Thus, objects should contain all of the data they require, as well as all of the
functionality that works with that data. The internal data of an object should never be exposed
in the interface; thus, fields rarely should be Public (public).
Returning to the Car example. If a Car object interacts with a Driver object, the Car
interface might consist of a GoForward method, a GoBackward method, and a Stop method.
This is all the information that the Driver needs to interact with the Car. The Car might
contain an Engine object, for example, but the Driver doesn’t need to know about the Engine
object—all the Driver cares about is that the methods can be called and that they return the
appropriate values. Thus, if one Engine object is exchanged for another, it makes no
difference to the Driver as long as the interface continues to function correctly.
Polymorphism
Polymorphism is the ability of different classes to provide different implementations of
the same public interfaces. In other words, polymorphism allows methods and properties of
an object to be called without regard for the particular implementation of those members. For
example, a Driver object can interact with a Car object through the Car public interface. If
another object, such as a Truck object or a SportsCar object, exposes the same public
interface, the Driver object can interact with them without regard to the specific
implementation of that interface. There are two principal ways through which polymorphism
can be provided: interface polymorphism and inheritance polymorphism.
Interface Polymorphism
An interface is a contract for behavior. Essentially, it defines the members a class should
implement, but states nothing at all about the details of that implementation. An object can
implement many different interfaces, and many diverse classes can implement the same
interface. All objects implementing the same interface are capable of interacting with other
objects through that interface. For example, the Car object in the previous examples might
implement the IDrivable interface (by convention, interfaces usually begin with I), which
specifies the GoForward, GoBackward, and Halt methods.
STAS, Pathanamthitta Page | 29
Enterprise Resource Planning System Project Report
Other classes, such as Truck, Forklift, or Boat might implement this interface and thus are
able to interact with the Driver object. The Driver object is unaware of which interface
implementation it is interacting with; it is only aware of the interface itself. Interface
polymorphism is discussed in detail in Lesson 3.
Inheritance Polymorphism
Inheritance allows you to incorporate the functionality of a previously defined class into a
new class and implement different members as needed. A class that inherits another class is
said to derive from that class, or to inherit from that class. A class can directly inherit from
only one class, which is called the base class. The new class has the same members as the
base class, and additional members can be added as needed. Additionally, the implementation
of base members can be changed in the new class by overriding the base class
implementation. Inherited classes retain all the characteristics of the base class and can
interact with other objects as though they were instances of the base class. For example, if the
Car class is the base class, a derived class might be SportsCar. The SportsCar class might be
the base class for another derived class, the ConvertibleSportsCar. Each newly derived class
might implement additional members, but the functionality defined in the original Car class is
retained. Inheritance polymorphism
FEATURES OF SQL-SERVER 2005
The OLAP Services feature available in SQL Server version 7.0 is now called SQL
Server 2005 Analysis Services. The term OLAP Services has been replaced with the term
Analysis Services. Analysis Services also includes a new data mining component. The
Repository component available in SQL Server version 7.0 is now called Microsoft SQL
Server 2005 Meta Data Services. References to the component now use the term Meta Data
Services. The term repository is used only in reference to the repository engine within Meta
Data Service
SQL-SERVER database consists of six type of objects,
They are,
1. TABLE
2. QUERY
STAS, Pathanamthitta Page | 30
Enterprise Resource Planning System Project Report
3. FORM
4. REPORT
5. MACRO
TABLE
A database is a collection of data about a specific topic.
VIEWS OF TABLE
We can work with a table in two types,
1. Design View
2. Datasheet View
Design View
To build or modify the structure of a table we work in the table design view. We can
specify what kind of data will be hold.
Datasheet View
To add, edit or analyses the data itself we work in tables datasheet view mode.
QUERY
A query is a question that has to be asked the data. Access gathers data that answers
the question from one or more table. The data that make up the answer is either dataset (if
you edit it) or a snapshot (it cannot be edited).Each time we run query, we get latest
information in the dataset. Access either displays the dataset or snapshot for us to view or
perform an action on it, such as deleting or updating.
FORMS
A form is used to view and edit information in the database record by record. A form
displays only the information we want to see in the way we want to see it. Forms use the
familiar controls such as textboxes and checkboxes. This makes viewing and entering data
easy.
STAS, Pathanamthitta Page | 31
Enterprise Resource Planning System Project Report
Views of Form:
We can work with forms in several primarily there are two views,
They are,
1. Design View
2. Form View
Design View
To build or modify the structure of a form, we work in forms design view. We can add
control to the form that are bound to fields in a table or query, includes textboxes, option
buttons, graphs and pictures.
Form View
The form view which display the whole design of the form.
REPORT
A report is used to vies and print information from the database. The report can ground
records into many levels and compute totals and average by checking values from many
records at once. Also the report is attractive and distinctive because we have control over the
size and appearance of it.
MACRO
A macro is a set of actions. Each action in macros does something. Such as opening a form or
printing a report .We write macros to automate the common tasks the work easy and save the
time.
MODULE
Modules are units of code written in access basic language. We can write and use
module to automate and customize the database in very sophisticated ways.It is a personal
computer based RDBMS. This provides most of the features available in the high-end
RDBMS products like Oracle, Sybase, and Ingress etc.
STAS, Pathanamthitta Page | 32
Enterprise Resource Planning System Project Report
STAS, Pathanamthitta Page | 33
Enterprise Resource Planning System Project Report
5. MODELING
5.1 INTRODUCTION
We create models to obtain a better understanding of the actual entity to be
built. The model focuses on what the system must do and not on how it does it. The second
and third operational analysis principles require that we build modules of function and
behavior. The written word is a wonderful vehicle for communication, but it isn't
necessarily the best way to represent the requirements for computer software. Analysis
modeling uses a combination of text and diagrammatic forms to depict requirements for
data, function, and behavior in a way that is relatively easy to understand, and more
important, straightforward to review for correctness, completeness and consistency. This
section presents resources for conventional and object-oriented analysis (OOA) methods as
well as resources for UML. Analysis modeling is an extremely robust subject.
5.2 GENERAL DESCRIPTION
STAS, Pathanamthitta Page | 34
Enterprise Resource Planning System Project Report
Requirement Modelling approaches are
1. Scenario-Based modeling
o Use Case Diagram
2. Data modeling
o ER Diagram
3. Class based modeling
o Class diagrams
4. Behavioral modeling
o State Diagram
5.2.1 Scenario-Based modeling
Scenario based modeling represents requirements from the point of
view of various system ‘actors’. Requirement modeling begins with the creation of
scenarios in the form of use case diagrams.
o Use Case Diagram
Use cases help to determine the functionality and features of the
software from user’s perspective. A use case describes how a user interacts with the system
by defining the steps required to accomplish a specific goal. Variations in the sequence of
steps describe various scenarios. In the diagram the stick figure represents an actor that is
associated with one category of user. In the use-case diagram the use cases are displayed as
ovals.
The actors are connected by lines to the use cases that they carry out. The use
cases are placed in a rectangle but the actors are not .This rectangle is a visual remainder of
the system boundaries and that the actors are outside the system.
STAS, Pathanamthitta Page | 35
Enterprise Resource Planning System Project Report
USE CASE FOR ADMIN
REGISTER EMPLOYEES
REGISTER VENDORS
REGISTER CUSTOMER
CREATE ID & PASSWORD
FOR EMPLOYEES
ADMIN
SYSTEM MAINTAINANCE
LEAVE APPLICATION
STAS, Pathanamthitta Page | 36
Enterprise Resource Planning System Project Report
USE CASE FOR HUMAN RESOURCE MANAGER / EMPLOYEE
MAINTAIN MONTHLY
EMPLOYEES ATTENDANCE
APPROVE / REJECT
EMPLOYEES LEAVE
MAINTAIN MONTHLY
EMPLOYEES RECORDS
CREATE EMPLOYEES
HR MANAGER / EMPLOYEE
PAY SLIP
LEAVE APPLICATION
USE CASE FOR ACCOUNT MANAGER / EMPLOYEE
CUSTOMER PAYMENTS
VENDOR PAYMENTS
EMPLOYEES SALARY
ACCOUNT
MANAGER / EMPLOYEE
LEAVE APPLICATION
STAS, Pathanamthitta Page | 37
Enterprise Resource Planning System Project Report
USE CASE FOR PURCHASE MANAGER / EMPLOYEE
PURCHASE ORDER
PURCHASE INVOICE / BILL
PURCHASE ENTRY
PURCHASE COMMENTS
MANAGER / EMPLOYEE
LEAVE APPLICATION
USE CASE FOR STORE MANAGER / EMPLOYEE
INWARD MATERIAL DETAIL
MAINTAIN STOCK
OUTWARD MATERIAL DETAIL
WASTE / RETURN
STORE MATERIAL DETAIL
MANAGER / EMPLOYEE
LEAVE APPLICATION
STAS, Pathanamthitta Page | 38
Enterprise Resource Planning System Project Report
USE CASE FOR SALES MANAGER / EMPLOYEE
SALES ORDER
SALES INVOICE / BILL
SALES ENTRY
COMMENTS
SALES
MANAGER / EMPLOYEE
LEAVE APPLICATION
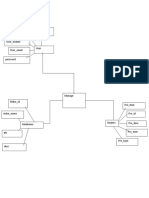
5.2.3 Data Modeling
If software requirements include the need to create, extend, or
interface with a database, the software team may choose to create a data model as part of
overall requirements modeling. It defines all data objects that are processed within the
system, the relationship between the data objects, and other information that is pertinent to
the relationships. The entity –relationship diagram (ERD) addresses these issues and
represents all data objects that are entered, stored, transformed, and produced within an
application. Data modeling tools provide a software engineer with the ability to represent data
object, their characteristics, and their relationships. Used primarily for large database
applications and other information systems projects, data modeling tools provide an
automated means for creating comprehensive entity relation diagrams, data object
dictionaries, and related models.
An E-R diagram may also indicate the cardinality of a
relationship. Cardinality is the number of instances of one entity that can, or must, be
STAS, Pathanamthitta Page | 39
Enterprise Resource Planning System Project Report
associated with each instance of another entity. In general, we may speak of one-to-one, one-
to-many, or many-to-many relationships.
Rectangle which represents entity sets.
Diamond which represents relationship sets.
Ellipse which represents attributes.
Lines which link attributes to entity sets and entity sets to
relationship sets.
STAS, Pathanamthitta Page | 40
Enterprise Resource Planning System Project Report
username desig_id half_day
emp_name email_id emp_id
absent_day sales_qty
emp_id received_qty
gender emp_atte_id
scrape_qty
item_name
password contact_no item_name
ATTENDANCE
received_quantity
SiH
b_acc_no DETAILS bill_no STOCK
present_day item_id
bank_name billed_amount sales_date
HUMAN month_year
INWARD sales_bill_no so_no
dob address
RESOURCE po_id
item_name item_id
leave_app_id pur_date OUTWARD
LEAVE
pur_id
leave_status
STORE sales_qty
emp_id sales_amount
reason
WASTE /
leave_from_date leave_app_date RETURN scrape_no
eave_to_date
scrape_date
scrape_qty
rec_id
item_id
Bill_no rec_date
cust_id sales_date
rec_amount
rec_mode sales_bill_no
cheque_dd_no so_no
RECEIPT
vend_id ENTRY
bill_no
bank_name
PAYMENT
MAINTAIN
ACCOUNT
DPARTMENT
ONLINE ERP ENTRY sales_qty
so_date
so_no
ENTRY
pay_amount
ACCOUNT SYSTEM sales_amount cust_id
pay_id so_qty
salary_mode
pay_mode
cheque_dd_no EMPLOYEE ORDER
gross_amount
SALARY salary_id
pay_date
SALES tax_amount
cheque_no item_id net_amount
price
salary_date emp_id
salary_amount
month_year sales_date price
address
INVOICE sales_bill_no
cust_name
bill_no bill_amount
item_id so_no
po_id cust_id
sales_qty
ENTRY address amount
pur_date
item_name
item_units
PURCHASE
pur_id contact_no
received_qty
ADMIN emp_id
desig_id
pur_id
username
po_date
po_id pur_date VENDOR EMPLOYEE
req_date REGISTRATION REGISTRATION password
INVOICE bill_no bank_name
vend_id emp_name
item_name
ORDER net_amount vend_name CUSTOMER
req_qty vend_id
_id vend_name b_acc_no gender
received_qty REGISTRATION
address email_id
price tax_amount
billed_amount dob
gross_amount
cust_id cust_name
STAS, Pathanamthitta Page | 41
Enterprise Resource Planning System Project Report
6. DESIGN
6.1 INTRODUCTION
STAS, Pathanamthitta Page | 42
Enterprise Resource Planning System Project Report
Design for Web apps encompasses technical and non-technical activities
that include: establishing the look and feel of the Web app, creating the aesthetic layout of the
user interface, defining the overall architectural structure, developing the content and
functionality that reside within the architecture, and planning the navigation that occurs
within the Web app.
Design allows you to create a model that can be assessed for quality and
improved before content and code are generated, tests are conducted, and end users become
involved in large numbers. Design is the place where Web app quality is established.
In general, the following design objectives must be kept in mind;
Practicality of the System
Efficiency of the System
Minimized cost of the System
Flexibility of the System
Security of the System
The system design involves first logical design and then physical
construction of the system. The logical design describes structure and characteristics of
features, like the outputs, inputs, databases and procedures. The physical construction which
follows the logical design produces actual program software files and the working system.
System design sits at the technical kernel of the software engineering and is applied
regardless of the software process model that is used. Beginning once software requirements
have been analyzed and specified, software design is the first technical activity that is used to
build and verify the software. Each activity (designing, coding and testing) transforms
information in a manner that ultimately results in validated computer software.
STAS, Pathanamthitta Page | 43
Enterprise Resource Planning System Project Report
6.2 USER INTERFACE DESIGN
The interface describes how the software communicates with itself. The
user interface is the link between the users and the employers. A well-designed user interface
makes it very easy for users to learn software. The user interface portion of software is
responsible for all interaction with the user. Development of good user interface usually takes a
significant portion of the total system development effort. GUI can be defined as a program
interface that takes advantages of the computer’s graphic capabilities to make the program
easier to use.
The Enterprise Resource Planning System is a web based one. Web
application use client/server architecture. The web application resides on a server and responds to
request from multiple clients over the Internet on the client side, a browser, such as Internet
Explorer, Netscape Navigator, hosts the Web application. The application’s user interface takes
the form of HTML pages that are interpreted and displayed by the client’s browser. On the server
side, the Web application runs under Microsoft Internet Information Services (IIS). IIS manages
the application, passes requests from clients to the application, and returns the application’s
response to the client.
6.3 CONTENT DESIGN
Content design focuses on two different design tasks, each addressed by
individuals with different skill test sets. First, a design representation for content objects and
the mechanisms required to establish their relationship to one another is developed. In
addition, the information within a specific content object is created. The latter task may be
conducted by copywriters, graphic designers, and others who generate the content to be used
within a Web app.
In the Enterprise Resource Planning System admin has the total control
to the website. Admin will manage all registration and report generation. Admin can control
every student who has attend the examination. Students can select different subject. Each
subject has multiple examinations.
STAS, Pathanamthitta Page | 44
Enterprise Resource Planning System Project Report
6.4 ARCHITECTURAL DESIGN
It is tied to the goals established for a web App, the content to be
presented, the user who will visit and the navigation philosophy that has been established. As
an architectural designer, you must identify content architecture and WebApp Architecture.
Content architecture focuses on the manner in which content objects are structured for
presentation and navigation. WebApp Architecture addresses the manner in which the
application is structured to manage user interaction, handle internal processing tasks, effect
navigation and present content. Architectural design - creates a blueprint for the design with
the necessary specifications for the hardware, software, people and data resources. In this
project n-Tier architecture is used for development. It can use objects for handling business
rules and data access. It has multiple servers handling business services.
6.5 NAVIGATION DESIGN
Once the WebApp Architecture has been established and the component of
the architecture has been identified, you must define navigation path way that enable users to
access WebApp content and functions. To accomplish this, you should
(1) Identify the semantics of navigation for different users of the site.
(2) Define the mechanics of achieving the navigation.
The main pages used in the system are,
7.6 COMPONENT LEVEL DESIGN
Modern Webapp deliver increasingly sophisticated processing functions
that,
(1) Perform localized processing to generate content and navigation capability in a dynamic
fashion,
STAS, Pathanamthitta Page | 45
Enterprise Resource Planning System Project Report
(2) Provide computation or data processing capability that is appropriate for the Webapp’s
business domain,
(3) Provide sophisticated database query and access,
(4) Establish data interface with external cooperate system.
6.7 DATABASE DESIGN
The most important aspect of building an application is the
design of database. The data they store must be organized according to the user requirement.
A well-designed database is essential for the good performance of the system. A database
table known as a relation provides information related to specific entity.
The basic functions involved in a database system related to the information required by the
user are:
Defining the data
Input the data
Locating the data
Communicating the data
Database Name: erp
* Primary Key
Table Name: cust_details
FIELD NAME DATA SIZE CONSTRAINTS DESCRIPTION
cust_id INT PRIMARY KEY Customer ID
cust_name VARCHAR 30 Customer Name
address VARCHAR 110 Address
contact_no VARCHAR 12 Contact Number
Table Name: desig_master
FIELD NAME DATA SIZE CONSTRAINTS DESCRIPTION
desig_id INT PRIMARY KEY Designation ID
dept_id INT Department ID
desig_name VARCHAR 30 Designation
Name
basic_salary FLOAT Basic Salary
STAS, Pathanamthitta Page | 46
Enterprise Resource Planning System Project Report
Table Name: emp_atte
FIELD NAME DATA SIZE CONSTRAINTS DESCRIPTION
emp_atte_id INT PRIMARY KEY Customer ID
emp_id INT Customer Name
month_year DATE Address
present_day INT Contact Number
Table Name: emp_detail
FIELD NAME DATA SIZE CONSTRAINTS DESCRIPTION
emp_id INT PRIMARY KEY Employee ID
desig_id INT Designation ID
username VARCHAR 40 Username
password VARCHAR 60 Password
emp_name VARCHAR 30 Employee Name
gender VARCHAR 10 Gender
dob DATE DOB
address VARCHAR 110 Address
contact_no VARCHAR 12 Contact Number
email_id VARCHAR 40 Email ID
bank_name VARCHAR 110 Bank Name
b_acc_no VARCHAR 20 Bank Account
Number
Table Name: item_master
FIELD NAME DATA SIZE CONSTRAINTS DESCRIPTION
item_id INT PRIMARY KEY Item ID
item_name VARCHAR 40 Item Name
item_units INT Number of units
Table Name:leave_application
FIELD NAME DATA SIZE CONSTRAINTS DESCRIPTION
leave_app_id INT PRIMARY KEY Leave
Application ID
leave_app_date DATE Leave
Application Date
STAS, Pathanamthitta Page | 47
Enterprise Resource Planning System Project Report
emp_id INT Employee ID
leave_from_date DATE Leave From
Date
leave_to_date DATE Leave To Date
reason VARCHAR 110 Reason
leave_status VARCHAR 20 Leave Status
Table Name: payment_entry
FIELD NAME DATA SIZE CONSTRAINTS DESCRIPTION
pay_id INT PRIMARY KEY Payment ID
pay_date DATE Payment Date
vend_date DATE Vendor Date
bill_no INT Bill Number
pay_amount FLOAT Payment
Amount
pay_mode VARCHAR 30 Payment Mode
bank_name VARCHAR 40 Bank Name
cheque_dd_no VARCHAR 20 Cheque DD
Number
Table Name: purchase_entry
FIELD NAME DATA SIZE CONSTRAINTS DESCRIPTION
pur_id INT PRIMARY KEY Purchase ID
po_date DATE Purchase Date
req_date DATE Request Date
vend_date DATE Vendor Date
item_id INT Item ID
req_qty INT Request
Quantity
price FLOAT Price
gross_amount FLOAT Gross Amount
tax_amount FLOAT Tax Amount
STAS, Pathanamthitta Page | 48
Enterprise Resource Planning System Project Report
net_amount FLOAT Net Amount
Table Name: purchase_order
FIELD NAME DATA SIZE CONSTRAINTS DESCRIPTION
po_id INT PRIMARY KEY Purchase Order
ID
po_date DATE Purchase Date
req_date DATE Request Date
vend_date DATE Vendor Date
item_id INT Item ID
req_qty INT Request
Quantity
price FLOAT Price
gross_amount FLOAT Gross Amount
tax_amount FLOAT Tax Amount
net_amount FLOAT Net Amount
Table Name: recipt_entry
FIELD NAME DATA SIZE CONSTRAINTS DESCRIPTION
cust_id INT PRIMARY KEY Customer ID
cust_name VARCHAR 30 Customer Name
address VARCHAR 110 Address
contact_no VARCHAR 12 Contact Number
Table Name: cust_details
FIELD NAME DATA SIZE CONSTRAINTS DESCRIPTION
rec_id INT PRIMARY KEY Recipt ID
rec_date DATE Recipt Date
cust_id INT Customer ID
bill_no INT Bill Number
rec_amount FLOAT Recipt Amount
rec_mode VARCHAR 30 Receipt Mode
bank_name VARCHAR 40 Bank Name
STAS, Pathanamthitta Page | 49
Enterprise Resource Planning System Project Report
cheque_dd_no VARCHAR 20 Cheque Number
Table Name: salary_entry
FIELD NAME DATA SIZE CONSTRAINTS DESCRIPTION
salary_id INT PRIMARY KEY Salary ID
salary_date DATE Salary Date
emp_id INT Employee ID
month_year DATE Month & Year
salary_amount FLOAT Salary Amount
salary_mode VARCHAR 30 Salary Mode
bank_name VARCHAR 40 Bank Name
cheque_no VARCHAR 20 Cheque Number
Table Name: sales_entry
FIELD NAME DATA SIZE CONSTRAINTS DESCRIPTION
sales_bill_no INT Sales Bill
Number
sales_date DATE Sales Date
so_no INT Sales Number
item_id INT Item ID
sales_qty INT Sales Quantity
sales_amount FLOAT Sales Amount
Table Name: sales_order
FIELD NAME DATA SIZE CONSTRAINTS DESCRIPTION
so_no INT Sales Order
Number
so_date DATE Sales Order Date
cust_id INT Customer ID
item_id INT Item ID
so_qty INT Sales Order
Quantity
price FLOAT Price
gross_amount FLOAT Gross Amount
tax_amount FLOAT Tax Amount
net_amount FLOAT Net Amount
STAS, Pathanamthitta Page | 50
Enterprise Resource Planning System Project Report
6.8. DIAGRAMS
6.8.1 Data flow Diagram (DFD)
The data flow diagram (DFD) is one of the most important tools used
by system analysts. Data flow diagrams are made up of a number of symbols, which
represent system components. Most data flow modeling methods use four kinds of symbols.
These symbols are used to represent four kinds of system components. Possesses, data stores,
data flows and external entities are the components. Circles in DFD represent a process. Data
flow is represented by a thin line in DFD and square or rectangle represents external entities.
Unlike detailed flow chart, data flow diagrams do not
supply detailed description of the modules but graphically describes a system’s data and how
the data interact with the system.
Symbols used in DFD are:
Square, this defines source or destination of data
Arrow, which shows data flow
Circle, which represents a process that transforms
incoming data into outgoing flow
Open rectangle, which shows a data store
STAS, Pathanamthitta Page | 51
Enterprise Resource Planning System Project Report
Level-0
STAS, Pathanamthitta Page | 52
Enterprise Resource Planning System Project Report
STAS, Pathanamthitta Page | 53
Enterprise Resource Planning System Project Report
Level-1
LEVEL 1 FOR ADMIN
LOGIN
CHECK
1.0
ADMIN LOGIN
RETRIEVE
emp_detail
STATUS
ENTER
REGISTRATION
DETAIL
2.0
USER ID
REGISTRATION
AND
PASSWORD
HUMAN
SOURCE
SYSTEM
MAINTAIN 3.0 UPDATE
REPORT
MAINTAIN HUMAN department
RESOURCE _master
RETRIEVE
DEPARTMENT
ACCOUNT
SYSTEM
MAINTAIN
REPORT
4.0 UPDATE
PURCHASE
MAINTAIN department
SYSTEM ACCOUNT
RETRIEVE
_master
MAINTAIN DEPARTMENT
REPORT
STORE
SYSTEM 5.0
MAINTAIN UPDATE
MAINTAIN department
REPORT PURCHASE RETRIEVE _master
DEPARTMENT
SALES
SYSTEM
MAINTAIN
REPORT 6.0
UPDATE
MAINTAIN department
STORE _master
RETRIEVE
LEAVE DEPARTMENT
REQUEST
LEAVE
STATUS
7.0 UPDATE
LOGOUT MAINTAIN department
SALES RETRIEVE _master
DEPARTMENT
STATUS
INSERT
8.0 leave_
LEAVE application
STATUS
APPLICATION
9.0
LOGOUT
STAS, Pathanamthitta Page | 54
Enterprise Resource Planning System Project Report
Level – 2
Registration LEVEL 2 FOR REGISTRATION
ENTER
EMPLOYEE DETAIL INSERT
2.1
REGISTRATION EMPLOYEE
RETRIEVE
emp_detail
SUCCESSFULLY REGISTRATION
REGISTATION
ENTER
VENDOR 2.2 INSERT
DETAIL
VENDOR emp_detail
SUCCESSFULLY
REGISTRATION RETRIEVE
REGISTRATION
ENTER
CUSTOMER 2.2 INSERT
DETAIL
CUSTOMER emp_detail
SUCCESSFULLY REGISTRATION RETRIEVE
REGISTRATION
STAS, Pathanamthitta Page | 55
Enterprise Resource Planning System Project Report
Level – 2 LEVEL 2 FOR HUMAN RESOURCE MANAGER
HR Manager
SIGN IN REQUEST ID
3.1
HR MANAGER LOGIN
LOGIN
RETRIEVE ID
emp_detail
ENTER 3.2 INSERT
ATTENDANCE MAINTAIN
EMPLOYEE emp_atte
STATUS RETRIEVE
ATTENDANCE
UPDATE
EMPLOYEE
LEAVES
3.3
UPDATE
APPROVE/
STATUS leave_
REJECT
EMPLOYEE RETRIEVE
application
LEAVES
UPDATE
RECORD
STATUS
3.4 UPDATE
MAINTAIN
MONTHLY EMPLOYEE
emp_detail
RECORDS RETRIEVE
RECORDS
PAY
DETAIL
LEAVE
REQUEST 3.5 INSERT
GENERATE
LEAVE
EMPLOYEE
emp_atte
STATUS
RETRIEVE
PAY SLIP
LOGOUT
STATUS
INSERT
3.6 leave_
LEAVE application
APPLICATION RETRIEVE
3.7
LOGOUT
STAS, Pathanamthitta Page | 56
Enterprise Resource Planning System Project Report
Level – 2
Account Manager LEVEL 2 FOR ACCOUNT MANAGER
ACCOUNT SIGN IN
4.1
REQUEST ID
emp_detail
MANAGER LOGIN LOGIN RETRIEVE ID
ENTER
CUSTOMER
PAYMENT UPDATE
4.2
DETAIL receipt_entry
CUSTOMER
RETRIEVE
RECEIPT
PAYMENTS
ENTER
VENDOR
PAYMENT
DETAIL UPDATE
4.3
payment_entry
RECEIPT VENDOR RETRIEVE
PAYMENTS
ENTER
EMPLOYEE
SALARY
DETAIL
RECEIPT
4.4
UPDATE salary_entry
EMPLOYEE RETRIEVE
LEAVE SALARY
REQUEST
LEAVE
STATUS
4.5 INSERT
leave_
LOGOUT
LEAVE application
RETRIEVE
STATUS APPLICATION
4.6
LOGOUT
STAS, Pathanamthitta Page | 57
Enterprise Resource Planning System Project Report
Level – 2
Purchase Manager LEVEL 2 FOR PURCHASE MANAGER
PURCHASE SIGN IN
5.1
REQUEST ID
emp_detail
MANAGER LOGIN LOGIN RETRIEVE ID
GIVE
ORDER
5.2 UPDATE
purchase_
PURCHASE
RETRIEVE order
STATUS
ORDER
INVOICE
DETAIL
5.3 UPDATE
INVOICE purchase_
PURCHASE
entry
INVOICE / BILL RETRIEVE
LEAVE
REQUEST
LEAVE
STATUS
5.4 UPDATE
leave_
LEAVE
application
APPLICATION RETRIEVE
COMMENTS
LOGOUT
STATUS 5.5
COMMENTS
5.6
LOGOUT
STAS, Pathanamthitta Page | 58
Enterprise Resource Planning System Project Report
Level – 2
Purchase Manager LEVEL 2 FOR STORE MANAGER
STORE SIGN IN
6.1
REQUEST ID
emp_detail
MANAGER LOGIN LOGIN RETRIEVE ID
REQUEST
FOR
PURCHSE
6.2 REQUEST
MATERIAL purchase_
DETAIL INWARD
entry
MATERIAL RETRIEVE
STATUS DETAIL
CHECK
STOCK
REQUEST
INWARD STOCK
STATUS 6.3
RETRIVE INWARD MATERIAL DETAIL
MAINTAIN RETRIVE OUTWARD MATERIAL DETAIL
REQUEST STOCK
REQUEST
FOR SALES OUTWARD STOCK
MATERIAL
DETAIL
STATUS
6.4 REQUEST
ENTER
WASTE OUTWARD sales_entry
MATERIAL MATERIAL RETRIEVE
DETAIL
DETAIL
FINAL
STOCK
REQUEST
LEAVE
6.5 UPDATE
LEAVE WASTE / RETURN scrape_entry
STATUS MATERIAL RETRIEVE
DETAIL
LOGOUT
LEAVE
STATUS
6.6 INSERT
leave_
LEAVE application
RETRIEVE
APPLICATION
6.7
LOGOUT
STAS, Pathanamthitta Page | 59
Enterprise Resource Planning System Project Report
Level – 2
Sales Manager LEVEL 2 FOR SALES MANAGER
SALES SIGN IN
7.1
REQUEST ID
emp_detail
MANAGER LOGIN LOGIN RETRIEVE ID
GIVE
ORDER
7.2 UPDATE
sales_
SALES
RETRIEVE order
STATUS
ORDER
INVOICE
DETAIL
7.3 UPDATE
INVOICE
SALES sales_ entry
INVOICE / BILL RETRIEVE
LEAVE
REQUEST
LEAVE
STATUS
7.4 UPDATE
leave_
LEAVE
application
APPLICATION RETRIEVE
COMMENTS
LOGOUT
STATUS 7.5
COMMENTS
7.6
LOGOUT
STAS, Pathanamthitta Page | 60
Enterprise Resource Planning System Project Report
7. CODING
STAS, Pathanamthitta Page | 61
Enterprise Resource Planning System Project Report
7.1 INTRODUCTION
The coding step is a process that transforms design into a programming
language. It translates a detail design representation of software into a programming language
realization. The translation process continues when a compiler accepts source code as input
and produces machine-dependent object code as output. Quality is an important goal during
coding. The quality of source code can be improved by the use of structured coding
techniques; good coding style and readable, consistent code format. During coding, some
coding standards are to be followed. This has two purposes; reducing the chance of making it
easier for some time to modify the code later on. Coding phase affects both testing and
maintenance profoundly. The Enterprise Resource Planning System uses PHP as the
programming language for coding.
STAS, Pathanamthitta Page | 62
Enterprise Resource Planning System Project Report
8. TESTING
8.1 INTRODUCTION
STAS, Pathanamthitta Page | 63
Enterprise Resource Planning System Project Report
The purpose of system testing is to identify and correct errors in the candidate
system. Testing is an important element of the software quality assurance and represents the
ultimate review of specification, design and coding. The increasing visibility of the software
as a system element and the costs associated with a software failure are motivated forces for
well planned, through testing.
Software testing is a critical element of software quality assurance and
represents the ultimate quality review of specifications, design and code generation. Once the
source code has been generated, the program should be executed before the customer gets it
with the specific intend of fining and removing all errors, test must be designed using
disciplined techniques. Testing techniques provides the systematic guidance for designing
tests. To uncover the errors in the program behavior function and performance the following
steps to be done:
Execute the integral logic of the software components.
Execute the input and output domains of the program to uncover errors
During testing the system is used experimentally to ensure that the software
does not fail, i.e., it will run according to the specification and in the way the user expects.
Preparation of test data plays n vital role in the system testing. Different set of test data are
generated and the system under study is tested using that data. While testing using test data
errors are again uncovered and corrected using different testing techniques.
System testing was conducted in order to detect errors and for comparing then
the final system with the requirement specification report. That is, whether the system meets
requirements. During testing the software was executed with a set of test cases and the output
of the program for the test cases was evaluated to determine if the program is performing as it
was expected to.
Testing presents, an interesting challenge for the software engineer attends to
hold software from an abstract concept to an acceptable implementation. In testing engineer
creates a series of test cases that o c c u r s w h e n e r r o r s a r e uncovered. Testing is the
process of executing a program for finding errors. A good test is one that has high probability
of finding an uncovered error
STAS, Pathanamthitta Page | 64
Enterprise Resource Planning System Project Report
The turn error is used to refer the difference between the actual output of the
software and the correct output. Fault is a condition that causes the software to fail to perform
its required function. Software reliability is defined as the required function.
Software reliability is defined as the probability that the software will not
undergo failure for a specified time under specified condition. Failure is the inability of a
system or a component to perform a required function according to its specification.
Different levels of testing were employed for software to make an error free, fault free and
reliable. Basically, in software testing four type of testing methods are adopted.
8.2 CONTENT TESTING
Content testing checks that users can easily understand all items that appear on
a site and, importantly, that they are able to correctly interpret the information they read.
Accordingly, it identifies any problem areas that may require simplification or rewriting. The
overall purpose of testing a content concept is to figure out what content strategy you should
follow throughout the project. This system was tested for successful acceptance and was
found to be working properly.
Content should be logical and easy to understand. Check for spelling errors.
Use of dark colors annoys users and should not be used in site theme. Enterprise Resource
Planning System follows some standards that are used for web page and content building.
These are common accepted standards like mentioned above about annoying colors, fonts,
frames, etc. Content should be meaningful. All the anchor text links should be working
properly. Images should be placed properly with proper sizes. These are some basic standards
that are followed in Enterprise Resource Planning System
8.3 USER INTERFACE TESTING
STAS, Pathanamthitta Page | 65
Enterprise Resource Planning System Project Report
This tests the whole end to end scenario (which simulates
exactly what the user would be doing). This (for the most part) goes through all the mouse
clicks and keyboard presses the user goes through to get an action done. If we extend the
previous example this would be invoking the same action except that this time instead of
using any test hooks it would be using the keyboard shortcut and instead verify the actual
displayed results on the application. User Interface testing is a process to test Enterprise
Resource Planning System user interface and to detect if application is functionally correct.
User Interface testing involves carrying set of tasks and comparing the result of same with the
expected output and ability to repeat same set of tasks multiple times with different data input
and same level of accuracy. User Interface Testing includes how the Enterprise Resource
Planning System handles keyboard and mouse events, how different GUI components like
menu bars, toolbars, dialogs, buttons, edit fields, list controls, images etc. reacts to user input
and whether or not it performs in the desired manner. Implementing User Interface testing for
your application early in the software development cycle speeds up development, improves
quality and reduces risks towards the end of the cycle. User Interface Testing can be
performed both manually with a human tester or could be performed automatically with use
of a software program.
8.4 COMPONENT LEVEL TESTING
Component level testing similar to unit testing but with a higher level of
integration. The big difference here is that the testing is done in the context of the application
instead of just directly testing the method in question. While testing at the component level
you would have the application open and the document displayed but you would be testing
the method and evaluating its result.(without taking into account the shortcut or what get
displayed on the application afterwards). In Enterprise Resource Planning System, the system
consists of several modules. All modules are tested and were found to be working properly.
8.5 NAVIGATION TESTING
STAS, Pathanamthitta Page | 66
Enterprise Resource Planning System Project Report
Navigation testing confirms that all internal and external links of Enterprise
Resource Planning System are working properly. There is no any broken link or orphan
page in application. Once the first layers of the Software have been examined, it is time to
perform simple tests to probe the quality of the global Software navigation. Good Software
will provide consistent, well-executed navigation and should provide alternative navigation
schemes, such as Software maps, indexes, and search engines. First, look to make sure that
placement of navigation is consistent from page to page. Subtle shifting may occur, so try
browsing the site extremely fast and notice whether the menu items bounce or jump position
slightly from page to page. Even this minor variation can break the perceived stability of a
site. Next, look to see how robust the navigation is and whether multiple forms of Software
navigation are supported. Numerous navigation execution questions should be asked during
this phase. The current location clearly indicated with labels or link path indicators. The
Software has text links at the bottoms of pages. Alternative text used for graphical navigation
buttons. The Software requires excessive scrolling.
8.6 CONFIGURATION TESTING
The process of testing a system with each of the configuration of software and
hardware that are supported. Configuration testing is another variation on traditional
performance testing. Rather than testing for performance from the perspective of load you are
testing the effects of configuration changes in the application landscape on application
performance and behavior. Enterprise Resource Planning System was tested for successful
acceptance and was found to be working properly.
8.7 SECUTITY TESTING
STAS, Pathanamthitta Page | 67
Enterprise Resource Planning System Project Report
Security testing is the process to determine that an information system protects
data and maintain functionality as intended. During security testing, the tester plays roles of
the individual who desires to penetrate the system. The tester may attempt to acquire
passwords through external clerical means; may attack the system with custom software
designed to breakdown any defenses that have been constructed; may overwhelm the system,
thereby denying service to others; may cause system errors, hoping to find the key to system
entry.
Enterprise Resource Planning System was tested for successful acceptance
i.e., she/he have to enter username or password to enter to the system. If the username and
password is not correct the message invalid username or password is displayed. So
unauthorized user cannot access the system.
8.8 PERFORMANCE TESTING
Performance testing is designed to test the run time performance of software
within the context of an integrated system. Performance testing occurs throughout all steps in
the testing process. Even at the unit level, performance of individual module may be assessed
as white box tests are conducted, it is not until all system elements are fully integrated that
true performance of a system can be ascertained. This system was tested for successful
acceptance and was found to be working properly.
8.9 TEST CASES
A test case is a document that describes an input, action or event and an
expected response, to determine if a feature of an application is working correctly. A test case
should contain particulars such as test case identifier, test case name, test conditions, input
data requirements steps, and expected results.
STAS, Pathanamthitta Page | 68
Enterprise Resource Planning System Project Report
Test cases
Project Title : ENTERPRISE RESOURCE PLANNING SYSTEM
Software Tool :
Test objective : To check whether the entered User name and Password are valid or invalid.
Test data : User name = admin and password = admin
Step Steps Data Expected results Actual
no: results
1 Enter User name and User name = Should display warning Login
press LOGIN Button admin message box "Please Enter failed
Password"
2 Enter Password and Password = Should display warning Login
press LOGIN Button admin message box "Please Enter failed
User name “
3 Enter User name and User = admin Should display warning Login
Password and press and Password = message box "Invalid User failed
LOGIN Button XYZ name or Password"
4 Enter User name and User = XYZ and Should display warning Login
Password and press Password = message box "Invalid User failed
LOGIN Button admin name or Password"
5 Enter User name and User = xyz and Should display warning Login
Password and press Password = xyz message box "Invalid User failed
LOGIN Button name or Password"
6 Enter User name and User = “ ” and Should display warning Login
Password and press Password = “ ” message box "Please Enter failed
LOGIN Button User name and Password“
7 Enter User name and User = admin Should navigate to admin Login
Password and press and password home page made
LOGIN Button =admin
STAS, Pathanamthitta Page | 69
Enterprise Resource Planning System Project Report
9. IMPLEMENTATION
9.1 IMPLEMENTATION OF THE PROJECT
The implementation is the final stage and it is an important phase. It
involves the individual programming; system testing, user training and the operational
running of developed proposed system that constitutes the application subsystems. One major
STAS, Pathanamthitta Page | 70
Enterprise Resource Planning System Project Report
task of preparing for implementation is education of users, which should really have been
taken place much earlier in the project when they were being involved in the investigation
and the design.
The implementation phase of the software development is concerned with
translating design specifications into source code. The user tests the developed system and
changes are made according to their needs. Our system has been successfully implemented.
Before implementation several tests have been conducted to ensure that no errors are
encounter during the operation. The implementation phase ends with an evaluation of the
system after placing it into operation for a period of time. Implementation is the third phase
of the system process. In order to achieve the objectives and the expected performance the
system has been developed in a highly interactive and user-friendly manner.
9.2 POST-IMPLEMENTATION AND SOFTWARE MAINTENANCE
Maintenance involves the software industry captive, typing up system
resources. It means restoring something to its original condition. Maintenance involves a
wide range of activities including correcting, coding, and design errors, updating
documentation and test data, and upgrading user support. Maintenance was done after the
success implementation. Maintenance is continued till the product is reengineered or
deployed to another platform. Maintenance is also done based on fixing the problems
reported, changing the interface with other software or hardware enhancing the software.
STAS, Pathanamthitta Page | 71
Enterprise Resource Planning System Project Report
10. PROJECT LEGACY
10.1 CURRENT STATUS OF THE PROJECT
STAS, Pathanamthitta Page | 72
Enterprise Resource Planning System Project Report
The project Enterprise Resource Planning System computerizes all the
manual activities in the existing site. As the technology grows, we must adopt the advantages
of the technologies to our organization.
The project titled Enterprise Resource Planning System has been done
successfully and satisfies all the requirements specified. This system helps in providing live
data to the authorities and help in decision making without wastage of time.
This website provides a user-friendly approach towards the system. This
system has been well developed and when implemented, is bound to satisfy all of the
requirements. Painstaking efforts have been taken to make the system impeccable and
upgradeable. There is a hope that this website will be utilized to its maximum and will do a
good job in the long run. With blessings of God, the exertions are hoped to bear fruit.
The program for carrying out various activities have been run and
successfully tested to ensure that the website developed meets the needs satisfactorily. Any
users can process this system without any experience in any software products. The newly
developed system consumes less processing time and all the details are updated and
processed immediately. Modules are designed to be highly flexible so that any failure
requirements can be easily added to the modules without facing many problems.
10.2 REMAINING AREAS OF CONCERN
The existing system is a manual one. Though the proposed system tries to
overcome the limitations of the existing system, we cannot say that the proposed system is
fully developed. So, the proposed system is developed with an insight that further
modifications can be applied.
Evolution in technology will give the customer more sophisticated
service. The Enterprise Resource Planning System will give a small part of its actual
working. Introducing the distributed database concept can make further extension to this
system. Module related to the functions of Product Dealers will add in future. Trial test may
conduct in future.
STAS, Pathanamthitta Page | 73
Enterprise Resource Planning System Project Report
11. SOURCE CODE
STAS, Pathanamthitta Page | 74
Enterprise Resource Planning System Project Report
Login.aspx.cs
using System;
using System.Configuration;
using System.Data;
using System.Linq;
using System.Web;
using System.Web.Security;
using System.Web.UI;
using System.Web.UI.HtmlControls;
using System.Web.UI.WebControls;
using System.Web.UI.WebControls.WebParts;
using System.Xml.Linq;
using System.Data.SqlClient;
public partial class _Default : System.Web.UI.Page
{
SqlConnection conn=new SqlConnection("Data
Source=.\\SQLEXPRESS;AttachDbFilename=|DataDirectory|\\erp.mdf;Integrated
Security=True;User Instance=True");
string qry,str,substr;
protected void Page_Load(object sender, EventArgs e)
{
if (!IsPostBack)
{
Session["emp_id"] = "";
Session["desig_id"] = "";
Session["username"] = "";
Session["emp_name"] = "";
Session["email_id"] = "";
Session["user_type"] = "";
STAS, Pathanamthitta Page | 75
Enterprise Resource Planning System Project Report
ImageButton1.Attributes.Add("onmouseover", "this.src='buttons/submit1.png'");
ImageButton1.Attributes.Add("onmouseout", "this.src='buttons/submit.png'");
ImageButton2.Attributes.Add("onmouseover", "this.src='buttons/reset1.png'");
ImageButton2.Attributes.Add("onmouseout", "this.src='buttons/reset.png'");
}
}
protected void ImageButton1_Click(object sender, ImageClickEventArgs e)
{
str = txtuser.Text;
substr = str.Substring(0, 2);
qry = "select * from emp_detail where username='" + txtuser.Text + "' AND
password='" + txtpass.Text + "'";
conn.Open();
SqlCommand cmd = new SqlCommand(qry, conn);
SqlDataReader dr = cmd.ExecuteReader();
if (dr.Read() == true)
{
Session["emp_id"] = dr.GetValue(0).ToString();
Session["desig_id"] = dr.GetValue(1).ToString();
Session["username"] = dr.GetValue(2).ToString();
Session["emp_name"] = dr.GetValue(4).ToString();
Session["email_id"] = dr.GetValue(9).ToString();
Session["user_type"] = substr;
if (substr == "ad")
{
Response.Redirect("adminhome.aspx");
}
else if (substr == "hr")
{
Response.Redirect("hrhome.aspx");
}
STAS, Pathanamthitta Page | 76
Enterprise Resource Planning System Project Report
else if (substr == "ac")
{
Response.Redirect("achome.aspx");
}
else if (substr == "pu")
{
Response.Redirect("puhome.aspx");
}
else if (substr == "st")
{
Response.Redirect("sthome.aspx");
}
else if (substr == "sa")
{
Response.Redirect("sahome.aspx");
}
}
else
{
error.Text = "Invalid ID or Password";
}
dr.Close();
conn.Close();
}
protected void ImageButton2_Click(object sender, ImageClickEventArgs e)
{
txtuser.Text = "";
txtpass.Text = "";
}
}
STAS, Pathanamthitta Page | 77
Enterprise Resource Planning System Project Report
Employee_pslip.aspx
<%@ Page Language="C#" MasterPageFile="~/AfterLogin.master"
AutoEventWireup="true" CodeFile="emp_pslip.aspx.cs" Inherits="emp_pslip" Title="Online
ERP System" %>
<asp:Content ID="Content1" ContentPlaceHolderID="head" Runat="Server">
</asp:Content>
<asp:Content ID="Content2" ContentPlaceHolderID="ContentPlaceHolder1"
Runat="Server">
<div id="content">
<div class="post">
<br />
<asp:ImageButton ID="ibgenerate" Height="40" Width="90"
ImageUrl="~/buttons/generate.png" runat="server"
onclick="ibgenerate_Click" />
<br />
<br />
<asp:GridView ID="empslip123" runat="server" AutoGenerateColumns="False"
BackColor="#DEBA84" BorderColor="#DEBA84" BorderStyle="None"
BorderWidth="1px"
CellPadding="3" CellSpacing="2" DataKeyNames="emp_atte_id"
onselectedindexchanged="empslip123_SelectedIndexChanged">
<RowStyle BackColor="#FFF7E7" ForeColor="#8C4510" />
<Columns>
<asp:CommandField ShowSelectButton="True" />
<asp:BoundField DataField="emp_atte_id" HeaderText="Attendance ID"
ReadOnly="True" SortExpression="emp_atte_id" />
STAS, Pathanamthitta Page | 78
Enterprise Resource Planning System Project Report
<asp:BoundField DataField="emp_id" HeaderText="Emp ID"
SortExpression="emp_id" />
<asp:BoundField DataField="month_year" HeaderText="Month-Year"
SortExpression="month_year" />
<asp:BoundField DataField="present_day" HeaderText="Present Day"
SortExpression="present_day" />
<asp:BoundField DataField="absent_day" HeaderText="Absent Day"
SortExpression="absent_day" />
<asp:BoundField DataField="half_day" HeaderText="Half Day"
SortExpression="half_day" />
</Columns>
<FooterStyle BackColor="#F7DFB5" ForeColor="#8C4510" />
<PagerStyle ForeColor="#8C4510" HorizontalAlign="Center" />
<SelectedRowStyle BackColor="#738A9C" Font-Bold="True" ForeColor="White" />
<HeaderStyle BackColor="#A55129" Font-Bold="True" ForeColor="White" />
</asp:GridView>
<asp:SqlDataSource ID="SqlDataSource1" runat="server"
ConnectionString="<%$ ConnectionStrings:ConnectionString %>"
SelectCommand="SELECT * FROM [emp_atte]"></asp:SqlDataSource>
</div>
</div>
</asp:Content>
STAS, Pathanamthitta Page | 79
Enterprise Resource Planning System Project Report
Customer_rec.aspx
<%@ Page Language="C#" MasterPageFile="~/AfterLogin.master"
AutoEventWireup="true" CodeFile="cust_record.aspx.cs" Inherits="cust_record"
Title="Online ERP System" %>
<%@ Register Assembly="AjaxControlToolkit" Namespace="AjaxControlToolkit"
TagPrefix="asp" %>
<asp:Content ID="Content1" ContentPlaceHolderID="head" Runat="Server">
</asp:Content>
<asp:Content ID="Content2" ContentPlaceHolderID="ContentPlaceHolder1"
Runat="Server">
<asp:ToolkitScriptManager ID="custrecord" runat="server">
</asp:ToolkitScriptManager>
<div id="content">
<div class="post">
<h2 class="title"><a href="#">Customer
Records</a></h2>
<hr />
<table>
<tr>
<td> <asp:Label ID="Label2" runat="server" Text="Customer ID"></asp:Label>
</td>
<td>:</td>
<td> <asp:TextBox ID="txtcust_id" ReadOnly="true"
runat="server"></asp:TextBox> </td>
</tr>
<tr>
<td> <asp:Label ID="name" runat="server" Text="Name"></asp:Label> </td>
<td>:</td>
<td>
<asp:TextBox ID="txtname" runat="server"></asp:TextBox>
STAS, Pathanamthitta Page | 80
Enterprise Resource Planning System Project Report
<asp:RequiredFieldValidator ID="name123" runat="server"
ControlToValidate="txtname" Display="None" ErrorMessage="Enter
Name"></asp:RequiredFieldValidator>
<asp:ValidatorCalloutExtender ID="ValidatorCalloutExtender6"
TargetControlID="name123" runat="server">
</asp:ValidatorCalloutExtender>
<asp:RegularExpressionValidator ID="name1234" runat="server"
ValidationExpression="^[a-zA-Z\s]+$" Display="None" ControlToValidate="txtname"
ErrorMessage="Enter Valid Name"></asp:RegularExpressionValidator>
<asp:ValidatorCalloutExtender ID="ValidatorCalloutExtender7"
TargetControlID="name1234" runat="server">
</asp:ValidatorCalloutExtender>
</td>
</tr>
<tr>
<td> <asp:Label ID="lbladdress" runat="server" Text="Address"></asp:Label>
</td>
<td>:</td>
<td>
<asp:TextBox ID="txtaddress" runat="server"
TextMode="MultiLine"></asp:TextBox>
<asp:RequiredFieldValidator ID="address123" ControlToValidate="txtaddress"
Display="None" runat="server" ErrorMessage="Enter
Address"></asp:RequiredFieldValidator>
<asp:ValidatorCalloutExtender ID="ValidatorCalloutExtender9"
TargetControlID="address123" runat="server">
</asp:ValidatorCalloutExtender>
</td>
</tr>
<tr>
<td> <asp:Label ID="lblcont" runat="server" Text="Contact
Number"></asp:Label> </td>
STAS, Pathanamthitta Page | 81
Enterprise Resource Planning System Project Report
<td>:</td>
<td>
<asp:TextBox ID="txtcont" MaxLength="10" runat="server"></asp:TextBox>
<asp:RequiredFieldValidator ID="cont123" ControlToValidate="txtcont"
Display="None" runat="server" ErrorMessage="Enter Contact
Number"></asp:RequiredFieldValidator>
<asp:ValidatorCalloutExtender ID="ValidatorCalloutExtender10"
TargetControlID="cont123" runat="server">
</asp:ValidatorCalloutExtender>
<asp:RegularExpressionValidator ID="cont1234" ControlToValidate="txtcont"
Display="None" runat="server" ErrorMessage="Enter Valid Contact Number"
ValidationExpression="^[0-9]{10}$"></asp:RegularExpressionValidator>
<asp:ValidatorCalloutExtender ID="ValidatorCalloutExtender11"
TargetControlID="cont1234" runat="server">
</asp:ValidatorCalloutExtender>
</td>
</tr>
</table>
<br />
<br />
<asp:ImageButton ID="btnmodify" Height="40" Width="90"
ImageUrl="~/buttons/modify.png"
onmouseover="this.src='buttons/modify1.png';"
onmouseout="this.src='buttons/modify.png';" runat="server"
onclick="btnmodify_Click"
/>
&n
bsp;
<asp:ImageButton ID="btndelete" Height="40" Width="90"
ImageUrl="~/buttons/delete.png"
onmouseover="this.src='buttons/delete1.png';"
STAS, Pathanamthitta Page | 82
Enterprise Resource Planning System Project Report
onmouseout="this.src='buttons/delete.png';" runat="server"
onclick="btndelete_Click" OnClientClick="return confirm('Are you sure want to Delete?')"/>
<br />
<table>
<tr>
<td align="left">
<asp:TextBox ID="txtsearch" runat="server"></asp:TextBox>
</td>
<td>
<asp:ImageButton ID="btnsearch" Height="40" Width="90"
ImageUrl="~/buttons/search.png"
onmouseover="this.src='buttons/search1.png';"
onmouseout="this.src='buttons/search.png';" runat="server"
onclick="btnsearch_Click1" CausesValidation="False"/>
</td>
</tr>
</table>
<br />
<asp:GridView ID="cust_grid" runat="server" BackColor="#DEBA84"
BorderColor="#DEBA84" BorderStyle="None" BorderWidth="1px" CellPadding="3"
onselectedindexchanged="cust_grid_SelectedIndexChanged" CellSpacing="2"
AutoGenerateColumns="False" DataKeyNames="cust_id" >
<RowStyle BackColor="#FFF7E7" ForeColor="#8C4510" />
<Columns>
<asp:CommandField ShowSelectButton="True" />
<asp:BoundField DataField="cust_id" HeaderText="Cust ID" ReadOnly="True"
SortExpression="cust_id" />
<asp:BoundField DataField="cust_name" HeaderText="Cust Name"
SortExpression="cust_name" />
<asp:BoundField DataField="address" HeaderText="Address"
STAS, Pathanamthitta Page | 83
Enterprise Resource Planning System Project Report
SortExpression="address" />
<asp:BoundField DataField="contact_no" HeaderText="Contact No"
SortExpression="contact_no" />
</Columns>
<FooterStyle BackColor="#F7DFB5" ForeColor="#8C4510" />
<PagerStyle ForeColor="#8C4510" HorizontalAlign="Center" />
<SelectedRowStyle BackColor="#738A9C" Font-Bold="True" ForeColor="White" />
<HeaderStyle BackColor="#A55129" Font-Bold="True" ForeColor="White" />
</asp:GridView>
<asp:SqlDataSource ID="SqlDataSource1"
runat="server"
ConnectionString="<%$ ConnectionStrings:ConnectionString %>"
SelectCommand="SELECT * FROM [cust_detail]"></asp:SqlDataSource>
</div>
</div>
</asp:Content>
STAS, Pathanamthitta Page | 84
Enterprise Resource Planning System Project Report
12. LIMITATION AND FUTURE ENHANCEMENT
STAS, Pathanamthitta Page | 85
Enterprise Resource Planning System Project Report
12. 1 LIMITATION:-
A firewall is always required on System server to protect from network attacks.
Overall User acceptance is a huge concern and driving factor for the success of the
implementation.
After System establishment switching costs are very high.
Without the proper support and dedication of the Top Management, This can’t be
a productive outcome.
If proper training is not given to the end users, they can cause blunders.
Managers cannot create custom reports or queries without the help of the
Programmer; hence all such requirements need to be specified from the beginning.
12.2 FUTURE ENHANCEMENT:-
Addition of a Decision Support System using AI.
Integration of the accounts module
Future of the ERP application mostly depends on the small and medium scale
companies.
STAS, Pathanamthitta Page | 86
Enterprise Resource Planning System Project Report
13. CONCLUSION
STAS, Pathanamthitta Page | 87
Enterprise Resource Planning System Project Report
Conclusion
Use of our system eliminates the tedious task of filling paperwork thus making the
business process more manageable and efficient all while reducing the time overhead &
increasing customer satisfaction.
Our system allows our clients to make informed & timely decisions thus giving them a
competitive edge over their counterparts.
STAS, Pathanamthitta Page | 88
Enterprise Resource Planning System Project Report
14. APPENDIX
STAS, Pathanamthitta Page | 89
Enterprise Resource Planning System Project Report
SCREEN LAYOUT
Login Page
Home Page
STAS, Pathanamthitta Page | 90
Enterprise Resource Planning System Project Report
Vender and Item Insertion
STAS, Pathanamthitta Page | 91
Enterprise Resource Planning System Project Report
Vender Update and Item Update
STAS, Pathanamthitta Page | 92
Enterprise Resource Planning System Project Report
Delete Vender and Item Delete
STAS, Pathanamthitta Page | 93
Enterprise Resource Planning System Project Report
Item Search and Vender Search
STAS, Pathanamthitta Page | 94
Enterprise Resource Planning System Project Report
Viewing Venders and Items
STAS, Pathanamthitta Page | 95
Enterprise Resource Planning System Project Report
STAS, Pathanamthitta Page | 96
Enterprise Resource Planning System Project Report
Purchase Order Creation
Invoice
STAS, Pathanamthitta Page | 97
Enterprise Resource Planning System Project Report
15. BIBILOGRAPHY
STAS, Pathanamthitta Page | 98
Enterprise Resource Planning System Project Report
Web References:
www.google.co.in
www.webbasederp.com
www.dolibarr.com
www.globerp.com
www.openerp.com
www.w3schools.com
www.wikipedia.com
www.aspnet.com
www.cooltext.com
www.grsites.com
STAS, Pathanamthitta Page | 99
You might also like
- Manage Medical Shop Inventory & SalesDocument85 pagesManage Medical Shop Inventory & SalesMuhammed AjmalNo ratings yet
- Profile of The Problem: Online Entrance Question and Result Project ReportDocument62 pagesProfile of The Problem: Online Entrance Question and Result Project ReportMuhammed AjmalNo ratings yet
- 1.1 Development of Employee Performance Management - An OverviewDocument57 pages1.1 Development of Employee Performance Management - An OverviewJothi ManiNo ratings yet
- Online Job PortalDocument84 pagesOnline Job PortalMuhammed Ajmal86% (7)
- Courier Project ReportDocument99 pagesCourier Project ReportArchie Srivastava100% (3)
- In The Existing System The Transactions Are Done Only Manually But inDocument53 pagesIn The Existing System The Transactions Are Done Only Manually But inSatendraSinghNo ratings yet
- Profile of The Problem: Online Certificate Printing Project ReportDocument57 pagesProfile of The Problem: Online Certificate Printing Project ReportMuhammed AjmalNo ratings yet
- A Project Report Submitted in Partial Fulfillment ofDocument14 pagesA Project Report Submitted in Partial Fulfillment ofAnchal Midha100% (1)
- Banking System AbstractDocument14 pagesBanking System AbstractAdesh Kumar Yadav100% (3)
- Employee Details in CPPDocument48 pagesEmployee Details in CPPTarun PatelNo ratings yet
- In The Existing System The Transactions Are Done Only Manually But inDocument53 pagesIn The Existing System The Transactions Are Done Only Manually But inRajesh Kumar MeenaNo ratings yet
- Online Event Management System Using PHPDocument4 pagesOnline Event Management System Using PHPLogaNathanNo ratings yet
- Banking Soft project tracks banking transactionsDocument40 pagesBanking Soft project tracks banking transactionsPaari Malhotra100% (1)
- Synopsis Job PortalDocument16 pagesSynopsis Job PortalAbhishek SrivastavaNo ratings yet
- Customer Account Management SystemDocument57 pagesCustomer Account Management SystemMegha SahuNo ratings yet
- Product Master Maintenance SystemDocument50 pagesProduct Master Maintenance Systembrinda100% (1)
- Retail Bill Management SystemDocument77 pagesRetail Bill Management SystemssigoldNo ratings yet
- Furniture Management System: BachelorDocument66 pagesFurniture Management System: BachelorjissmathewNo ratings yet
- Feasibility StudyDocument16 pagesFeasibility StudyMarianne Balita AtienzaNo ratings yet
- Bank AtmDocument4 pagesBank Atmsharatgupta0% (2)
- Banking System (Synopsis)Document9 pagesBanking System (Synopsis)Princ SinghNo ratings yet
- Project Report SummaryDocument41 pagesProject Report SummarySarlaJaiswalNo ratings yet
- Study Unit 10: F.3. Technology-Enabled Finance TransformationDocument20 pagesStudy Unit 10: F.3. Technology-Enabled Finance TransformationNhi Trần ThảoNo ratings yet
- Information System Development MethodologiesDocument10 pagesInformation System Development Methodologiessseba1900No ratings yet
- Banking System ProjectDocument13 pagesBanking System ProjectParamjit SinghNo ratings yet
- Online Learning PortalDocument158 pagesOnline Learning Portalaccord12340% (5)
- Computerized Self Supporting ProgramDocument87 pagesComputerized Self Supporting ProgramSatendraSinghNo ratings yet
- Profile of The Problem: Online Entrance Question and Result Project ReportDocument64 pagesProfile of The Problem: Online Entrance Question and Result Project ReportMuhammed AjmalNo ratings yet
- Banking System Account Opening InterestDocument18 pagesBanking System Account Opening InterestSourav BrahmaNo ratings yet
- Online Sales and Service Management SystemDocument39 pagesOnline Sales and Service Management SystemSayeeda Anjum0% (1)
- Airlines Resevation System FinalDocument97 pagesAirlines Resevation System FinalDheeraj Singh0% (1)
- Document VBDocument75 pagesDocument VBManoj Kumar SahuNo ratings yet
- Online Job Portal Java Project DocumentDocument92 pagesOnline Job Portal Java Project DocumentMamatha RYNo ratings yet
- SDLC Notes Systems Analyst RoleDocument9 pagesSDLC Notes Systems Analyst RoleRavinder K SinglaNo ratings yet
- Managing Organizational Change with Information SystemsDocument10 pagesManaging Organizational Change with Information Systemsermiyas tesfayeNo ratings yet
- Methodology of WPS Office 1Document13 pagesMethodology of WPS Office 1Monica BabuNo ratings yet
- Production Planning and Control System SynopsisDocument6 pagesProduction Planning and Control System Synopsisgvani3333No ratings yet
- Bank ManagementDocument71 pagesBank ManagementMubariz ShaikhNo ratings yet
- Budget Management System (SSP) "Document100 pagesBudget Management System (SSP) "SatendraSinghNo ratings yet
- Inventory Management SystemDocument28 pagesInventory Management SystemSairaj More100% (1)
- Vegan Spoon (Project File)Document142 pagesVegan Spoon (Project File)jatin khandelwalNo ratings yet
- Objective and Scope of The Project: Page - 1Document84 pagesObjective and Scope of The Project: Page - 1jassi nishadNo ratings yet
- G.H.Raisoni Institute of Business Management: Academic Year-2022-2023Document39 pagesG.H.Raisoni Institute of Business Management: Academic Year-2022-2023Bhavesh PawarNo ratings yet
- Alternative SolutionsDocument7 pagesAlternative Solutionsravi9981No ratings yet
- Ankit Singh GymDocument27 pagesAnkit Singh GymMayank jainNo ratings yet
- Business Management SystemDocument209 pagesBusiness Management SystemAnand VishwakarmaNo ratings yet
- Project Caretaker ManagementDocument68 pagesProject Caretaker ManagementChandramathi M100% (2)
- Online Courier Service SystemDocument84 pagesOnline Courier Service SystemRadheshyam Nayak100% (1)
- Summary of Theory CH 13 - Week 12Document5 pagesSummary of Theory CH 13 - Week 12Salsa ArdilaNo ratings yet
- SDLC Online Notice BoardDocument24 pagesSDLC Online Notice Boardawneesh tiwariNo ratings yet
- Banking Software AbstractionDocument3 pagesBanking Software AbstractionEng Denis Christopher MkingaNo ratings yet
- Study of Billing SystemsDocument14 pagesStudy of Billing SystemsPrarthana P WNo ratings yet
- A Report On Gym Management SystemDocument20 pagesA Report On Gym Management Systemdron upadhyayNo ratings yet
- Store Management System SRS Chapter SummaryDocument65 pagesStore Management System SRS Chapter SummaryAkshay GuptaNo ratings yet
- Employee Survey Feedback SystemDocument32 pagesEmployee Survey Feedback SystemAbhijeet NigoskarNo ratings yet
- Cost Estimation in Agile Software Development: Utilizing Functional Size Measurement MethodsFrom EverandCost Estimation in Agile Software Development: Utilizing Functional Size Measurement MethodsNo ratings yet
- Zero To Mastery In Cybersecurity- Become Zero To Hero In Cybersecurity, This Cybersecurity Book Covers A-Z Cybersecurity Concepts, 2022 Latest EditionFrom EverandZero To Mastery In Cybersecurity- Become Zero To Hero In Cybersecurity, This Cybersecurity Book Covers A-Z Cybersecurity Concepts, 2022 Latest EditionNo ratings yet
- Software Testing Interview Questions You'll Most Likely Be AskedFrom EverandSoftware Testing Interview Questions You'll Most Likely Be AskedNo ratings yet
- Enterprise Resource Planning1Document99 pagesEnterprise Resource Planning1Muhammed AjmalNo ratings yet
- Enterprise Resource Planning1Document99 pagesEnterprise Resource Planning1Muhammed AjmalNo ratings yet
- Covid-19 Hospital Management SystemDocument74 pagesCovid-19 Hospital Management SystemMuhammed Ajmal67% (3)
- ERP Program: User ManualDocument29 pagesERP Program: User ManualMuhammed AjmalNo ratings yet
- Human Resource Management SystemDocument1 pageHuman Resource Management SystemMuhammed AjmalNo ratings yet
- HRMS system with C# & SQL ServerDocument41 pagesHRMS system with C# & SQL ServerMuhammed AjmalNo ratings yet
- Customer Relationship ManagementDocument1 pageCustomer Relationship ManagementMuhammed AjmalNo ratings yet
- Profile of The Problem: Online ID Card Management System Project ReportDocument64 pagesProfile of The Problem: Online ID Card Management System Project ReportMuhammed Ajmal100% (1)
- Enterprise Resource Planning1Document99 pagesEnterprise Resource Planning1Muhammed AjmalNo ratings yet
- Enterprise Resource Planning1Document99 pagesEnterprise Resource Planning1Muhammed AjmalNo ratings yet
- Profile of The Problem: College Student Portal Project ReportDocument63 pagesProfile of The Problem: College Student Portal Project ReportMuhammed AjmalNo ratings yet
- Profile of The Problem: Online Entrance Question and Result Project ReportDocument64 pagesProfile of The Problem: Online Entrance Question and Result Project ReportMuhammed AjmalNo ratings yet
- Profile of The Problem: Online Certificate Printing Project ReportDocument57 pagesProfile of The Problem: Online Certificate Printing Project ReportMuhammed AjmalNo ratings yet
- 1.3.1 Hardware SpecificationDocument5 pages1.3.1 Hardware Specificationsuriya extazeeNo ratings yet
- 2 Net Framework Overview 120201085125 Phpapp01Document48 pages2 Net Framework Overview 120201085125 Phpapp01Partho BoraNo ratings yet
- C# ProgrammingDocument175 pagesC# ProgrammingrickletNo ratings yet
- Code Execution ProcessDocument6 pagesCode Execution ProcessPrasanth JayaprakashNo ratings yet
- Unit01-Getting Started With .NET Framework 4.0Document40 pagesUnit01-Getting Started With .NET Framework 4.0mgsumaNo ratings yet
- Introduction To The Microsoft .NET FrameworkDocument18 pagesIntroduction To The Microsoft .NET Frameworkpandu165No ratings yet
- Final DocumentDocument60 pagesFinal DocumentRitul RaiNo ratings yet
- DotNet SQL Interview QuestionsDocument167 pagesDotNet SQL Interview QuestionsDuccati ZiNo ratings yet
- Singularity - Rethinking The Software StackDocument13 pagesSingularity - Rethinking The Software StackComputer GuruNo ratings yet
- C Sharp Notes (2006) - SJBITDocument2 pagesC Sharp Notes (2006) - SJBITrajesh_amcNo ratings yet
- Software Platform".: Common Language Runtime (CLR)Document4 pagesSoftware Platform".: Common Language Runtime (CLR)Himawan_Budi_L_7947No ratings yet
- ASP Net Question PaperDocument122 pagesASP Net Question Paperbhrantav0% (1)
- Am Rts Step 3 CIL Standard CBA: Autonomous Maintenance PillarDocument19 pagesAm Rts Step 3 CIL Standard CBA: Autonomous Maintenance PillarAsanka Chathuranga100% (1)
- NOTESDocument22 pagesNOTEShamsa20201No ratings yet
- Object Oriented ProgrammingDocument72 pagesObject Oriented Programmingpraptiitm100% (1)
- Memory Footprints of Programs on Different Platforms and LanguagesDocument26 pagesMemory Footprints of Programs on Different Platforms and Languagesrohto1945No ratings yet
- Unit 1 - Topic 1 VB - Net Framework, Architectre and ComponentsDocument12 pagesUnit 1 - Topic 1 VB - Net Framework, Architectre and ComponentsVandana DulaniNo ratings yet
- Comparison of C Sharp and Visual BasicDocument10 pagesComparison of C Sharp and Visual Basicsanchi.varmaNo ratings yet
- Answer in ShortDocument87 pagesAnswer in Shortapi-19920737No ratings yet
- VTU ISE7sem Syllabus C#Document1 pageVTU ISE7sem Syllabus C#ashwinchavanNo ratings yet
- Ax2012 Enus Deviv 02 PDFDocument50 pagesAx2012 Enus Deviv 02 PDFBachtiar YanuariNo ratings yet
- C NET Material PDFDocument548 pagesC NET Material PDFBhagyasri Annam JaldawarNo ratings yet
- Visual Programming Lecture 01Document63 pagesVisual Programming Lecture 01Shabila GulzarNo ratings yet
- CSharp TutorialDocument181 pagesCSharp TutorialKartheek VvsNo ratings yet
- DaxDocument16 pagesDaxInfant RoseNo ratings yet
- DotNet FrameworkDocument60 pagesDotNet Frameworkd4anmol86% (7)
- QuestionsDocument410 pagesQuestionsKamlesh KumarNo ratings yet
- C#basicsDocument314 pagesC#basicskotiramaNo ratings yet
- TOC Previous Next: Here Here Here HereDocument6 pagesTOC Previous Next: Here Here Here Hereessiben ngangueNo ratings yet
- OSWE NOTES BASIC BY JOASDocument233 pagesOSWE NOTES BASIC BY JOASjjjabriyel jabriNo ratings yet