Professional Documents
Culture Documents
Cissp-Exam-Outline Guidelines
Cissp-Exam-Outline Guidelines
Uploaded by
aloksingh1980Original Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Cissp-Exam-Outline Guidelines
Cissp-Exam-Outline Guidelines
Uploaded by
aloksingh1980Copyright:
Available Formats
Certification Exam Outline
About CISSP
e Certifie In ormation S tem Securit Pro e ional CISSP i t e mo t lo all reco ni e certification
in t e in ormation ecurit mar et CISSP ali ate an in ormation ecurit ro e ional ee tec nical
an mana erial no le e an ex erience to e ecti el e i n en ineer an mana e t e o erall ecurit
o ture o an or ani ation
e roa ectrum o to ic inclu e in t e CISSP Common o o no le e C en ure it rele anc
acro all i ci line in t e fiel o in ormation ecurit Succe ul can i ate are com etent in t e ollo in
omain
• Securit an i ana ement
• et Securit
• Securit En ineerin
• Communication an et or Securit
• I entit an cce ana ement
• Securit e ment an e tin
• Securit O eration
• So t are e elo ment Securit
Experience Requirements
Can i ate mu t a e a minimum o ear cumulati e ai ull time or ex erience in or more o t e
omain o t e ISC C Can i ate ma recei e a ear ex erience ai er it a ear colle e e ree
or re ional e ui alent or a itional cre ential rom t e ISC a ro e li t t u re uirin ear o irect
ull time ro e ional ecurit or ex erience in or more o t e omain o t e CISSP C
can i ate t at oe n t a e t e re uire ex erience to ecome a CISSP ma ecome an ociate o ISC
ucce ull a in t e CISSP examination e ociate o ISC ill t en a e ear to earn t e
ear re uire ex erience
Accreditation
CISSP a t e fir t cre ential in t e fiel o in ormation ecurit to meet t e trin ent re uirement o SI
ISO IEC Stan ar
Job Task Analysis (JTA)
ISC a an o li ation to it mem er i to maintain t e rele anc o t e CISSP Con ucte at re ular
inter al t e o a nal i i a met o ical an critical roce o eterminin t e ta t at are
er orme ecurit ro e ional o are en a e in t e ro e ion efine t e CISSP e re ult o
t e are u e to u ate t e examination i roce en ure t at can i ate are te te on t e to ic
area rele ant to t e role an re on i ilitie o to a racticin in ormation ecurit ro e ional
CISSP Certification Exam Outline 2
CISSP Examination Information
Length of exam our
Number of questions
Question format ulti le c oice an a ance inno ati e ue tion
Passing grade out o oint
Exam availability En li renc erman ra ilian Portu ue e S ani
a ane e Sim lifie C ine e orean i uall im aire
Testing center Pear on E e tin Center
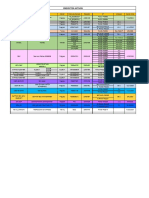
CISSP Examination Weights
Domains Weight
Securit an i ana ement
et Securit
Securit En ineerin
Communication an et or Securit
I entit an cce ana ement
Securit e ment an e tin
Securit O eration
So t are e elo ment Securit
Total: 100%
CISSP Certification Exam Outline 3
Domain 1:
Security and Risk Management
1.1 Understand and apply concepts of confidentiality, integrity and availability
1.2 Apply security governance principles through:
» li nment o ecurit unction to trate oal » Securit role an re on i ilitie
mi ion an o ecti e e u ine ca e » Control rame or
u et an re ource
» ue care
» Or ani ational roce e e ac ui ition
i e titure o ernance committee » ue ili ence
1.3 Compliance
» e i lati e an re ulator com liance
» Pri ac re uirement com liance
1.4 Understand legal and regulatory issues that pertain to information security in a global
context
» Com uter crime » ran or er ata o
» icen in an intellectual ro ert e » Pri ac
co ri t tra emar i ital ri t mana ement » ata reac e
» Im ort ex ort control
1.5 Understand professional ethics
» Exerci e ISC Co e o Pro e ional Et ic
» Su ort or ani ation co e o et ic
1.6 Develop and implement documented security policy, standards, procedures, and
guidelines
1.7 Understand business continuity requirements
» e elo an ocument ro ect co e an lan
» Con uct u ine im act anal i
CISSP Certification Exam Outline 4
1.8 Contribute to personnel security policies
» Em lo ment can i ate creenin e re erence » en or con ultant an contractor control
c ec e ucation erification » Com liance
» Em lo ment a reement an olicie » Pri ac
» Em lo ment termination roce e
1.9 Understand and apply risk management concepts
» I enti t reat an ulnera ilitie » Control a e ment
» i a e ment anal i ualitati e uantitati e » onitorin an mea urement
ri » et aluation
» i a i nment acce tance e tem » e ortin
aut ori ation
» Continuou im ro ement
» Countermea ure election
» i rame or
» Im lementation
» e o control re enti e etecti e
correcti e etc
1.10 Understand and apply threat modeling
» I enti in t reat e a er arie contractor » Per ormin re uction anal i
em lo ee tru te artner » ec nolo ie an roce e to reme iate t reat
» eterminin an ia rammin otential attac e o t are arc itecture an o eration
e ocial en ineerin oofin
1.11 Integrate security risk considerations into acquisition strategy and practice
» ar are o t are an er ice » inimum ecurit re uirement
» ir art a e ment an monitorin e on » Ser ice le el re uirement
ite a e ment ocument exc an e an re ie
roce olic re ie
1.12 Establish and manage information security education, training, and awareness
» ro riate le el o a arene trainin an e ucation re uire it in or ani ation
» Perio ic re ie or content rele anc
CISSP Certification Exam Outline 5
Domain 2:
Asset Security
2.1 Classify information and supporting assets (e.g., sensitivity, criticality)
2.2 Determine and maintain ownership (e.g., data owners, system owners, business/mission
owners)
2.3 Protect privacy
» ata o ner » ata remanence
» ata roce er » Collection limitation
2.4 Ensure appropriate retention (e.g., media, hardware, personnel)
2.5 Determine data security controls (e.g., data at rest, data in transit)
» a eline » Stan ar election
» Sco in an tailorin » Cr to ra
2.6 Establish handling requirements (markings, labels, storage, destruction of sensitive
information)
CISSP Certification Exam Outline 6
Domain 3:
Security Engineering
3.1 Implement and manage engineering processes using secure design principles
3.2 Understand the fundamental concepts of security models (e.g., Confidentiality,
Integrity, and Multi-level Models)
3.3 Select controls and countermeasures based upon systems security evaluation models
3.4 Understand security capabilities of information systems (e.g., memory protection,
virtualization, trusted platform module, interfaces, fault tolerance)
3.5 Assess and mitigate the vulnerabilities of security architectures, designs, and solution
elements
» Client a e e a let local cac e » i tri ute tem e clou com utin ri
com utin eer to eer
» Ser er a e e ata o control
» Cr to ra ic tem
» ata a e ecurit e in erence a re ation
ata minin ata anal tic are ou in » In u trial control tem e SC
» ar e cale arallel ata tem
3.6 Assess and mitigate vulnerabilities in web-based systems (e.g., XML, OWASP)
3.7 Assess and mitigate vulnerabilities in mobile systems
3.8 Assess and mitigate vulnerabilities in embedded devices and cyber-physical systems (e.g.,
network-enabled devices, Internet of things (loT))
3.9 Apply cryptography
» Cr to ra ic li e c cle e cr to ra ic » i ital i nature
limitation al orit m rotocol o ernance » i ital ri t mana ement
» Cr to ra ic t e e mmetric a mmetric » on re u iation
elli tic cur e
» Inte rit a in an altin
» Pu lic e In ra tructure P I
» et o o cr tanal tic attac e rute orce
» e mana ement ractice ci er text onl no n laintext
CISSP Certification Exam Outline 7
3.10 Apply secure principles to site and facility design
3.11 Design and implement physical security
» irin clo et » ata center ecurit
» Ser er room » tilitie an C con i eration
» e ia tora e acilitie » ater i ue e lea a e oo in
» E i ence tora e » ire re ention etection an u re ion
» e tricte an or area ecurit e o eration
center
CISSP Certification Exam Outline 8
Domain 4:
Communication and Network Security
4.1 Apply secure design principles to network architecture (e.g., IP & non-IP protocols,
segmentation)
» OSI an CP IP mo el » So t are efine net or
» IP net or in » irele net or
» Im lication o multila er rotocol e P » Cr to ra u e to maintain communication
ecurit
» Con er e rotocol e CoE P S oIP
iSCSI
4.2 Secure network components
» O eration o ar are e mo em itc e » En oint ecurit
router irele acce oint mo ile e ice » Content i tri ution net or
» ran mi ion me ia e ire irele fi er » P ical e ice
» et or acce control e ice e
fire all roxie
4.3 Design and establish secure communication channels
» oice » ata communication e S SS
» ultime ia colla oration e remote meetin » irtuali e net or e S irtual S ue t
tec nolo in tant me a in o eratin tem ort i olation
» emote acce e P creen cra er irtual
a lication e to telecommutin
4.4 Prevent or mitigate network attacks
CISSP Certification Exam Outline 9
Domain 5:
Identity and Access Management
5.1 Control physical and logical access to assets
» In ormation
» S tem
» e ice
» acilitie
5.2 Manage identification and authentication of people and devices
» I entit mana ement im lementation e SSO » Se ion mana ement e timeout
P creen a er
» Sin le multi actor aut entication e actor » e i tration an roofin o i entit
tren t error » e erate i entit mana ement e S
» ccounta ilit » Cre ential mana ement tem
5.3 Integrate identity as a service (e.g., cloud identity)
5.4 Integrate third-party identity services (e.g., on-premise)
5.5 Implement and manage authorization mechanisms
» ole a e cce Control C met o
» ule a e acce control met o
» an ator cce Control C
» i cretionar cce Control C
5.6 Prevent or mitigate access control attacks
5.7 Manage the identity and access provisioning lifecycle (e.g., provisioning, review)
CISSP Certification Exam Outline 10
Domain 6:
Security Assessment and Testing
6.1 Design and validate assessment and test strategies
6.2 Conduct security control testing
» ulnera ilit a e ment » i u e ca e te tin
» Penetration te tin » e t co era e anal i
» o re ie » Inter ace te tin e PI I ical
» S nt etic tran action
» Co e re ie an te tin e manual namic
tatic u
6.3 Collect security process data (e.g., management and operational controls)
» ccount mana ement e e calation » ac u erification ata
re ocation » rainin an a arene
» ana ement re ie » i a ter reco er an u ine continuit
» e er ormance an ri in icator
6.4 Analyze and report test outputs (e.g., automated, manual)
6.5 Conduct or facilitate internal and third party audits
CISSP Certification Exam Outline 11
Domain 7:
Security Operations
7.1 Understand and support investigations
» E i ence collection an an lin e c ain o » In e ti ati e tec ni ue e root cau e anal i
cu to inter ie in inci ent an lin
» e ortin an ocumentin » i ital oren ic e me ia net or o t are
an em e e e ice
7.2 Understand requirements for investigation types
» O erational » e ulator
» Criminal » Electronic i co er e i co er
» Ci il
7.3 Conduct logging and monitoring activities
» Intru ion etection an re ention » E re monitorin e ata lo re ention
te ano ra atermar in
» Securit in ormation an e ent mana ement
» Continuou monitorin
7.4 Secure the provisioning of resources
» et in entor e ar are o t are » Clou a et e er ice tora e
net or
» Confi uration mana ement
» lication e or loa or ri ate clou
» P ical a et
e er ice o t are a a er ice
» irtual a et e o t are efine net or
irtual S ue t o eratin tem
7.5 Understand and apply foundational security operations concepts
» ee to no lea t ri ile e e entitlement » o rotation
a re ation tran iti e tru t » In ormation li ec cle
» Se aration o utie an re on i ilitie » Ser ice le el a reement
» onitor ecial ri ile e e o erator
a mini trator
7.6 Employ resource protection techniques
» e ia mana ement
» ar are an o t are a et mana ement
CISSP Certification Exam Outline 12
7.7 Conduct incident management
» etection » eco er
» e on e » eme iation
» iti ation » e on learne
» e ortin
7.8 Operate and maintain preventative measures
» ire all » San oxin
» Intru ion etection an re ention tem » one ot one net
» iteli tin lac li tin » nti mal are
» ir art ecurit er ice
7.9 Implement and support patch and vulnerability management
7.10 Participate in and understand change management processes (e.g., versioning, baselining,
security impact analysis)
7.11 Implement recovery strategies
» ac u tora e trate ie e o ite tora e » ulti le roce in ite e o erationall
electronic aultin ta e rotation re un ant tem
» eco er ite trate ie » S tem re ilience i a aila ilit ualit o
er ice an ault tolerance
7.12 Implement disaster recovery processes
» e on e » e ment
» Per onnel » e toration
» Communication » rainin an a arene
7.13 Test disaster recovery plans
» ea t rou » Parallel
» al t rou » ull interru tion
» Simulation
7.14 Participate in business continuity planning and exercises
7.15 Implement and manage physical security
» Perimeter e acce control an monitorin
» Internal ecurit e e cort re uirement i itor control e an loc
7.16 Participate in addressing personnel safety concerns (e.g., duress, travel, monitoring)
CISSP Certification Exam Outline 13
Domain 8:
Software Development Security
8.1 Understand and apply security in the software development lifecycle
» e elo ment met o olo ie e ile » O eration an maintenance
ater all » C an e mana ement
» aturit mo el » Inte rate ro uct team e e O
8.2 Enforce security controls in development environments
» Securit o t e o t are en ironment » Confi uration mana ement a an a ect o
ecure co in
» Securit ea ne e an ulnera ilitie at
t e ource co e le el e u er o er o » Securit o co e re o itorie
e calation o ri ile e in ut out ut ali ation » Securit o a lication ro rammin inter ace
8.3 Assess the effectiveness of software security
» u itin an lo in o c an e
» i anal i an miti ation
» cce tance te tin
8.4 Assess security impact of acquired software
CISSP Certification Exam Outline 14
Additional Examination Information
Supplementary References
Can i ate are encoura e to u lement t eir e ucation an ex erience re ie in
rele ant re ource t at ertain to t e C an i enti in area o tu t at ma nee
a itional attention
ie t e ull li t o u lementar re erence at i c or ci c re erence
Examination Policies and Procedures
ISC recommen t at CISSP can i ate re ie exam olicie an roce ure rior to
re i terin or t e examination ea t e com re en i e rea o n o t i im ortant
in ormation at i c or exam olicie roce ure
Legal Info
or an ue tion relate to ISC le al olicie lea e contact t e ISC e al
e artment at le al i c or
Any Questions?
ISC Can i ate Ser ice
Par Place l Suite
Clear ater
ISC merica
el
Email in o i c or
ISC ia Pacific
el
Email i c a ia i c or
ISC E E
el
Email in o emea i c or
CISSP Certification Exam Outline 15
You might also like
- ABB Robotics Operational, Programming, and Maintenance TrainingDocument264 pagesABB Robotics Operational, Programming, and Maintenance TrainingagungNo ratings yet
- Discussion Forum Unit 3Document2 pagesDiscussion Forum Unit 3Safwan al ubaied0% (1)
- SD IM004 - Health Safety Policy Procedures CBSA V1.0 (ID 162249)Document7 pagesSD IM004 - Health Safety Policy Procedures CBSA V1.0 (ID 162249)Varun JamesNo ratings yet
- SMS PresentationDocument53 pagesSMS PresentationbarbarbiroUNo ratings yet
- CISSP - 1 Information Security & Risk ManagementDocument60 pagesCISSP - 1 Information Security & Risk ManagementlebenikosNo ratings yet
- CisspDocument16 pagesCisspRyan GlasgowNo ratings yet
- ExpeditionaryWarfareStud Small00center10 3831126Document33 pagesExpeditionaryWarfareStud Small00center10 3831126Tré AngeliNo ratings yet
- Safety Management System: An Introduction ToDocument65 pagesSafety Management System: An Introduction TojorgeNo ratings yet
- Behavior Based Safety BBSDocument67 pagesBehavior Based Safety BBSAkhilesh Kumar Singh100% (1)
- Safety Management System Structure: What Is A SMS?Document8 pagesSafety Management System Structure: What Is A SMS?Sayed AbbasNo ratings yet
- Information Systems Security OfficerDocument19 pagesInformation Systems Security OfficermabesninaNo ratings yet
- CISSP Exam Outline-V1115Document16 pagesCISSP Exam Outline-V1115AsadMalikNo ratings yet
- CISSP Exam Outline English April 2021 PDFDocument16 pagesCISSP Exam Outline English April 2021 PDFKevin MonkamNo ratings yet
- 4 Safety ManagementDocument52 pages4 Safety Managementvimalk017No ratings yet
- Behavior Based SafetyDocument57 pagesBehavior Based SafetyMohamed Elberry100% (1)
- Safety Culture in Aircraft Maintenance SectorDocument8 pagesSafety Culture in Aircraft Maintenance SectorElkhweldiNo ratings yet
- CEP2010 Heat TransferDocument8 pagesCEP2010 Heat TransferamsukdNo ratings yet
- Duties of Safety OfficerDocument5 pagesDuties of Safety Officerjio4g1941No ratings yet
- Building a Corporate Culture of Security: Strategies for Strengthening Organizational ResiliencyFrom EverandBuilding a Corporate Culture of Security: Strategies for Strengthening Organizational ResiliencyNo ratings yet
- Process Safety Performance Indicators and PSM AuditingDocument4 pagesProcess Safety Performance Indicators and PSM AuditingHuyen Trang LeNo ratings yet
- Risk Assessment For Personnel SecurityDocument42 pagesRisk Assessment For Personnel SecurityAKANo ratings yet
- Understanding Process Safety ManagementDocument8 pagesUnderstanding Process Safety ManagementIffatNo ratings yet
- 5 Top Questions Asked During AccreditationDocument72 pages5 Top Questions Asked During AccreditationRohan PawarNo ratings yet
- Hfsafety 1 SEM 22-23: Click To Add Text Click To Add TextDocument70 pagesHfsafety 1 SEM 22-23: Click To Add Text Click To Add TextAdrienne CoNo ratings yet
- ISO27001 2013 ComplianceChecklistDocument46 pagesISO27001 2013 ComplianceChecklistMassimo Carnelli100% (5)
- Vince GalottiDocument21 pagesVince GalottiDaffa HauzaanNo ratings yet
- Creating A More Effective Safety CultureDocument5 pagesCreating A More Effective Safety Culturekelvin0007No ratings yet
- SafetyDocument21 pagesSafetyAmir HussainNo ratings yet
- BBS by - Bureau-VertasDocument53 pagesBBS by - Bureau-VertasAnupam ShuklaNo ratings yet
- Ponemon Report The Economics of Security Operations CentersDocument32 pagesPonemon Report The Economics of Security Operations CentersIvan BetancourtNo ratings yet
- 3 How To Use The CSF Profile For CVEDocument21 pages3 How To Use The CSF Profile For CVEFerry AstikaNo ratings yet
- Lezione Argiolu - Master Roma3!3!12-2010 - Test Di Application SecurityDocument26 pagesLezione Argiolu - Master Roma3!3!12-2010 - Test Di Application SecurityWB_YeatsNo ratings yet
- Disasters Related To BBSDocument38 pagesDisasters Related To BBSVikram TNo ratings yet
- Bbs Preventive ToolsDocument6 pagesBbs Preventive ToolsEmmanuelNo ratings yet
- Safety and Efficiency An ICAO Perspective: Aviation Safety, Security & The Environment: The Way ForwardDocument21 pagesSafety and Efficiency An ICAO Perspective: Aviation Safety, Security & The Environment: The Way ForwardabdulmannanadsNo ratings yet
- (Slides Note) 05 ISFT Security Policies, Standards and Compliance VE - MHHDocument69 pages(Slides Note) 05 ISFT Security Policies, Standards and Compliance VE - MHHFaZe MoHANo ratings yet
- 1 Information Security Incidents Iso Iec 27002 m1 SlidesDocument23 pages1 Information Security Incidents Iso Iec 27002 m1 SlidesRavi Kumar GaliNo ratings yet
- 2021 11 11 All in One Day Mandatory Training 443656Document2 pages2021 11 11 All in One Day Mandatory Training 443656George Ricky HawkinsNo ratings yet
- Behaviour Based SafetyDocument104 pagesBehaviour Based SafetyKouroufia Diaby Gassamma100% (1)
- CH17 CompSec4eDocument29 pagesCH17 CompSec4ejffdNo ratings yet
- SAE6788 Harsimran Preet SITXWHS003 Implement and Monitor Work Health and Safety Practices PDFDocument67 pagesSAE6788 Harsimran Preet SITXWHS003 Implement and Monitor Work Health and Safety Practices PDFsunita dhamijaNo ratings yet
- Health & Safety: Implementation ofDocument14 pagesHealth & Safety: Implementation ofharikeshmn09No ratings yet
- Safety Management System & Crew Resource Management: For Training Purposes OnlyDocument14 pagesSafety Management System & Crew Resource Management: For Training Purposes OnlyAldrin DayritNo ratings yet
- Management of Human Elements - R1Document37 pagesManagement of Human Elements - R1Lyes OuabdesselamNo ratings yet
- Advanced Safety ManagementDocument2 pagesAdvanced Safety ManagementziyadeliNo ratings yet
- Intelie Ebook Dra 2022Document15 pagesIntelie Ebook Dra 2022Mariana BoninaNo ratings yet
- Ms. Andres - PHC Case StudyDocument48 pagesMs. Andres - PHC Case StudyJBLMGH EMPLOYEESCLINICNo ratings yet
- KPMG Survey On Data Protection PracticesDocument24 pagesKPMG Survey On Data Protection PracticeskissvineetNo ratings yet
- CISSP - 1 Information Security & Risk ManagementDocument60 pagesCISSP - 1 Information Security & Risk Managementjonty509No ratings yet
- 04-Fisher Effective Information Security GovernanceDocument23 pages04-Fisher Effective Information Security GovernanceSalil MittalNo ratings yet
- ARCON Protecting Data Survey Report 2017 PDFDocument20 pagesARCON Protecting Data Survey Report 2017 PDFPrasad KshirsagarNo ratings yet
- Safety & Health Management - The Basics: Introduction To The Seven Elements of EffectiveDocument86 pagesSafety & Health Management - The Basics: Introduction To The Seven Elements of Effectivesiva_aelNo ratings yet
- Supervisor & Managers Safety Responsibilities at Site: SECL HSE Overseas Support TeamDocument53 pagesSupervisor & Managers Safety Responsibilities at Site: SECL HSE Overseas Support TeamrubelNo ratings yet
- caatمدى إستجابة أنظمة الرقابة الداخلية لمخرجات إدارة المخاطر في ظل سلوك الإدارة العليا - دراسة ميدانية للشركة الوطنية للتأميناتDocument18 pagescaatمدى إستجابة أنظمة الرقابة الداخلية لمخرجات إدارة المخاطر في ظل سلوك الإدارة العليا - دراسة ميدانية للشركة الوطنية للتأميناتnadaamr1234nadaNo ratings yet
- Wrong Storage Practices Improperly Maintained Tools Lack of IlluminationDocument5 pagesWrong Storage Practices Improperly Maintained Tools Lack of IlluminationRajat HiraNo ratings yet
- 008 PSMDocument21 pages008 PSMniels.cauwenberghNo ratings yet
- Looking For Higher Standards: Behavioural Safety - Improving PerformanceDocument16 pagesLooking For Higher Standards: Behavioural Safety - Improving PerformanceHelp Tubestar Crew100% (1)
- Intro To Safety ManagementDocument2 pagesIntro To Safety ManagementFatima CellonaNo ratings yet
- Security Orchestration Use CasesDocument33 pagesSecurity Orchestration Use CasesCatalin Apostol100% (3)
- Uk The Security Operations Maturity Model Quick Reference Guide For Defence BrochureDocument7 pagesUk The Security Operations Maturity Model Quick Reference Guide For Defence BrochureFlávio RibeiroNo ratings yet
- Safety Culture and Safety ManagementDocument24 pagesSafety Culture and Safety Managementandrej.sukoraNo ratings yet
- Presentation ISMS ISO IEC 27001 2022Document150 pagesPresentation ISMS ISO IEC 27001 2022Denis OuNo ratings yet
- Cyber Insurance - Author Mansi ThaparDocument3 pagesCyber Insurance - Author Mansi Thaparaloksingh1980No ratings yet
- Drawn Date Description Rev: V1.0 First Release 2013-06-03Document4 pagesDrawn Date Description Rev: V1.0 First Release 2013-06-03aloksingh1980No ratings yet
- Gwen Bettwy - Think Like A Manager TipsDocument1 pageGwen Bettwy - Think Like A Manager Tipsaloksingh1980No ratings yet
- 1Y0-341 Citrix ADC Advanced Topics: Security, Management and OptimizationDocument19 pages1Y0-341 Citrix ADC Advanced Topics: Security, Management and Optimizationaloksingh1980No ratings yet
- Environment Monitoring System Using Low Cost Sensors: March 2020Document6 pagesEnvironment Monitoring System Using Low Cost Sensors: March 2020aloksingh1980No ratings yet
- Konftel 300IP AG Rev 5A - ENGDocument66 pagesKonftel 300IP AG Rev 5A - ENGaloksingh1980No ratings yet
- 2021 07 Margoni Kretschmer-2Document70 pages2021 07 Margoni Kretschmer-2bart boogaertsNo ratings yet
- Generator Type Eco 3-1Sn/4: Electrical CharacteristicsDocument5 pagesGenerator Type Eco 3-1Sn/4: Electrical CharacteristicsFaridh AmroullohNo ratings yet
- Hydrogen Energy TechnologiesDocument9 pagesHydrogen Energy Technologieschkald1No ratings yet
- Analysis and Design of Multistoryed G+5 Pre Engineered BuildingDocument6 pagesAnalysis and Design of Multistoryed G+5 Pre Engineered Buildingpankaj645924No ratings yet
- SP GTU Study Material E-Notes All-Units 15102019051954AMDocument100 pagesSP GTU Study Material E-Notes All-Units 15102019051954AMDixit Chotaliya100% (1)
- The Synthetic Agenda - The Distorted Heart of The New World OrderDocument10 pagesThe Synthetic Agenda - The Distorted Heart of The New World OrderWillie Johnson100% (1)
- Microfluidics Lecture 1Document4 pagesMicrofluidics Lecture 1Tseng Yen JungNo ratings yet
- (Web Tech) Week 7Document17 pages(Web Tech) Week 7Mr ProductNo ratings yet
- Java-Advanced-Stacks-and-Queues-LabDocument5 pagesJava-Advanced-Stacks-and-Queues-LabJudith NelsonNo ratings yet
- Equpment StatusDocument11 pagesEqupment StatusSantosh Kumar PathakNo ratings yet
- COMP 500 Lab 2 Submission TemplateDocument3 pagesCOMP 500 Lab 2 Submission TemplateNishant YadavNo ratings yet
- Unit 4 - Week 3 - Conditional Executions and Loops, Data Management With SequencesDocument8 pagesUnit 4 - Week 3 - Conditional Executions and Loops, Data Management With SequencesxlntyogeshNo ratings yet
- My Easter ConfessionDocument3 pagesMy Easter ConfessionDENNIS LUKAAYA100% (1)
- An International Social Inclusion Index With Application in - 2022 - Decision AnDocument15 pagesAn International Social Inclusion Index With Application in - 2022 - Decision AnVikash KumarNo ratings yet
- Gir 3000 ManualDocument44 pagesGir 3000 Manualxxzeizxx6No ratings yet
- Sapio WhitepaperDocument6 pagesSapio WhitepaperBluesunset1No ratings yet
- HL 40 InsulationDocument2 pagesHL 40 InsulationSky MoonNo ratings yet
- Proyectos ActivosDocument1 pageProyectos ActivosAlejandra GloriaNo ratings yet
- Electro-Hydraulic Turbine Controller: Lets Share Knowledge OnDocument45 pagesElectro-Hydraulic Turbine Controller: Lets Share Knowledge OnNishant Chaudhary100% (1)
- Sample Ale ExamDocument37 pagesSample Ale ExamMarian Lim100% (1)
- Motorola MCC 5500 Dispatch Console Basic IP Network Set-Up Manual 6871004P79-B (April 2008)Document80 pagesMotorola MCC 5500 Dispatch Console Basic IP Network Set-Up Manual 6871004P79-B (April 2008)aurtizNo ratings yet
- Book 1Document9 pagesBook 1Prince NsikanNo ratings yet
- 14 Steps For Being An Outstanding Master of CeremoniesDocument2 pages14 Steps For Being An Outstanding Master of CeremoniesChandrashekar KupperiNo ratings yet
- Advanced Troubleshooting and Update - Edition 15 DT00XTE278Document483 pagesAdvanced Troubleshooting and Update - Edition 15 DT00XTE278sidney SantiagoNo ratings yet
- Network Management: A Note On The Use of These PPT SlidesDocument12 pagesNetwork Management: A Note On The Use of These PPT SlidesDaya MendozaNo ratings yet
- Resume Electrical Engineer FaizDocument2 pagesResume Electrical Engineer FaizFaizFzNo ratings yet
- Readiness of ICT Students On Work Immersion Program of Paharang Integrated SchoolDocument6 pagesReadiness of ICT Students On Work Immersion Program of Paharang Integrated SchoolInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- HPT 50 & 55 Series: Operating Instructions Spare Parts List Service ManualDocument25 pagesHPT 50 & 55 Series: Operating Instructions Spare Parts List Service ManualGustavo HerreraNo ratings yet