Professional Documents
Culture Documents
Unit 6 Managing A Successful Computing Project
Uploaded by
Lakshan KingOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Unit 6 Managing A Successful Computing Project
Uploaded by
Lakshan KingCopyright:
Available Formats
Higher Nationals
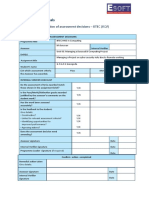
Internal verification of assessment decisions – BTEC (RQF)
INTERNAL VERIFICATION – ASSESSMENT DECISIONS
Programme title BTEC Higher National Diploma in Computing
Assessor Internal Verifier
Unit 6 Managing a Successful Computing Project
Unit(s)
Vulnerability Assessment – Management Information System (MIS) Project
Assignment title
Raman Lakshan
Student’s name
List which assessment Pass Merit Distinction
criteria the Assessor has
awarded.
INTERNAL VERIFIER CHECKLIST
Do the assessment criteria awarded match
those shown in the assignment brief? Y/N
Is the Pass/Merit/Distinction grade awarded
justified by the assessor’s comments on the Y/N
student work?
Has the work been assessed
Y/N
accurately?
Is the feedback to the student:
Give details:
• Constructive?
Y/N
• Linked to relevant assessment
criteria? Y/N
• Identifying opportunities for
improved performance? Y/N
• Agreeing actions? Y/N
Does the assessment decision need
Y/N
amending?
Assessor signature Date
Internal Verifier signature Date
Programme Leader signature(if
Date
required)
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 1
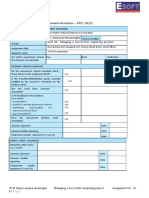
Confirm action completed
Remedial action taken
Give details:
Assessor signature Date
Internal Verifier
Date
signature
Programme Leader
Date
signature (if required)
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 2
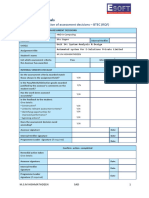
Higher Nationals - Summative Assignment Feedback Form
Student Name/ID
Unit Title Unit 6 Managing a Successful Computing Project
Assignment Number 1 Assessor
Date Received 1st
Submission Date
submission
Date Received 2nd
Re-submission Date
submission
Assessor Feedback:
LO1. Establish project aims, objectives and timeframes based on the chosen theme
Pass, Merit & Distinction P1 P2 P3 M1
Descripts
LO2. Conduct small-scale research, information gathering and data collection to generate knowledge
to support the project
Pass, Merit & Distinction P4 M2 D1
Descripts
LO3. Present the project and communicate appropriate recommendations based on meaningful conclusions
drawn from the evidence findings and/or analysis.
Pass, Merit & Distinction P5 P6 M3
Descripts
LO4. Reflect on the value gained from conducting the project and its usefulness to support sustainable
organisational performance
Pass, Merit & Distinction P7 M4 D2
Descripts
Grade: Assessor Signature: Date:
Resubmission Feedback:
Grade: Assessor Signature: Date:
Internal Verifier’s Comments:
Signature & Date:
* Please note that grade decisions are provisional. They are only confirmed once internal and external moderation has taken place and grades decisions have
been agreed at the assessment board.
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 3
Pearson
Higher Nationals in
Computing
Unit 6: Managing a Successful Computing Project
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 4
General Guidelines
1. A Cover page or title page – You should always attach a title page to your assignment. Use previous page as
your cover sheet and be sure to fill the details correctly.
2. This entire brief should be attached in first before you start answering.
3. All the assignments should prepare using word processing software.
4. All the assignments should print in A4 sized paper, and make sure to only use one side printing.
5. Allow 1” margin on each side of the paper. But on the left side you will need to leave room for binging.
Word Processing Rules
1. Use a font type that will make easy for your examiner to read. The font size should be 12 point, and should be
in the style of Time New Roman.
2. Use 1.5 line word-processing. Left justify all paragraphs.
3. Ensure that all headings are consistent in terms of size and font style.
4. Use footer function on the word processor to insert Your Name, Subject, Assignment No, and Page Number
on each page. This is useful if individual sheets become detached for any reason.
5. Use word processing application spell check and grammar check function to help edit your assignment.
Important Points:
1. Check carefully the hand in date and the instructions given with the assignment. Late submissions will not be
accepted.
2. Ensure that you give yourself enough time to complete the assignment by the due date.
3. Don’t leave things such as printing to the last minute – excuses of this nature will not be accepted for failure
to hand in the work on time.
4. You must take responsibility for managing your own time effectively.
5. If you are unable to hand in your assignment on time and have valid reasons such as illness, you may apply (in
writing) for an extension.
6. Failure to achieve at least a PASS grade will result in a REFERRAL grade being given.
7. Non-submission of work without valid reasons will lead to an automatic REFERRAL. You will then be asked to
complete an alternative assignment.
8. Take great care that if you use other people’s work or ideas in your assignment, you properly reference them,
using the HARVARD referencing system, in you text and any bibliography, otherwise you may be guilty of
plagiarism.
9. If you are caught plagiarising you could have your grade reduced to A REFERRAL or at worst you could be
excluded from the course.
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 5
Student Declaration
I hereby, declare that I know what plagiarism entails, namely to use another’s work and to present it as my own
without attributing the sources in the correct way. I further understand what it means to copy another’s work.
1. I know that plagiarism is a punishable offence because it constitutes theft.
2. I understand the plagiarism and copying policy of the Edexcel UK.
3. I know what the consequences will be if I plagiaries or copy another’s work in any of the assignments for this
program.
4. I declare therefore that all work presented by me for every aspects of my program, will be my own, and where
I have made use of another’s work, I will attribute the source in the correct way.
5. I acknowledge that the attachment of this document signed or not, constitutes a binding agreement between
myself and Edexcel UK.
6. I understand that my assignment will not be considered as submitted if this document is not attached to the
attached.
Ramanlakshan1995@gmail.com
Student’s Signature: Date: 31.12.2020
(Provide E-mail ID) (Provide Submission Date)
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 6
Assignment Brief
Student Name /ID Number NEG/A - 014710
Unit Number and Title Unit 6: Managing a Successful Computing Project
Academic Year 2017/2018
Unit Tutor
Assignment Title Vulnerability Assessment - Management Information System Project
Issue Date
Submission Date
IV Name & Date
Submission Format:
The submission is in the form of an individual written report. This should be written in a concise, formal
business style using single spacing and font size 12. You are required to make use of headings, paragraphs
and subsections as appropriate, and all work must be supported with research and referenced using the
Harvard referencing system. Please also provide an end list of references using the Harvard referencing
system.
Unit Learning Outcomes:
LO1 Establish project aims, objectives and timeframes based on the chosen theme.
LO2 Conduct small-scale research, information gathering and data collection to generate knowledge to
support the project.
LO3 Present the project and communicate appropriate recommendations based on meaningful
conclusions drawn from the evidence findings and/or analysis.
LO4 Reflect on the value gained from conducting the project and its usefulness to support sustainable
organizational performance.
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 7
Assignment Brief and Guidance:
Vulnerability Assessment - Management Information System (MIS) Project
Management Information Systems (MIS) plays a very important role in today’s organizations; it creates
an impact on the organization’s functions, performance and productivity. A Management Information
System (MIS) ensures that an appropriate data is collected from the various sources, processed and send
further to all the needy destinations. A system is expected to fulfill the information needs of an individual,
a group of individuals, management functionaries, managers and top management to improve efficiency
and productivity.
On contrary, any system can be compromised with vulnerability issues. This is mostly in area of
confidentiality, integrity and availability (security triangle).
You’re advised to provide solutions for improvements for a selected Management Information System’s in
a selected organization in the area of how to improve aspects of confidentiality, integrity and availability
(security triangle) through a vulnerability study assessment.
You should investigate the causes and impacts of vulnerabilities within computing systems and explore the
solutions to the problems presented in order to make recommendations to improve their security for
Management Information System. The expected solution of the project is a vulnerability assessment and
action plan which includes, issues of varying severity.
In general, the vulnerability assessment may focus on a test of security infrastructure devices, network
servers, operational systems (including Windows and Linux), physical security of buildings, and wireless
internet security. You have to mainly focus on how can vulnerabilities in an existing system be identified
and counteracted.
Discover unknown entry points both physical and electronic – that is threat to the overall
confidentiality, integrity, and availability of network data and resources.
Problem can be discovered in the areas of installing, configuring, and maintaining servers and
infrastructure equipment as well as practices of different department managers and staff tend to have
different ways of managing their IT.
Recommendations for standardization of upcoming infrastructure installations, configurations, and
maintenance.
Educate and increase user awareness on what they could change to improve their security situation
in order to build confidence of using the Management Information System
An action plan to keep their environment secure.
Your role as a student researcher means that you are not trying to perform a specific solution to any
vulnerability problem case. You have to make expert recommendations on how to tighten security
controls, based on a proven assessment methodology, that are in the best interest of the specific project of
Management Information System which may eliminate unnecessary entry points that would greatly reduce
the threat. Introducing of a set of policies and procedures for the entire Management Information System
help eliminate threats through network entry points and infrastructure. The vulnerability trends and
recurring issues that needed careful attention. The project span 03 months in order to provide an accurate
snapshot of their current security posture.
The benefit of the project is that it provides a greater awareness among the entire staff about how any
vulnerability or weakness in any functional area affects the overall security posture of the Management
Information System at large. You are required to provide a full report on vulnerabilities you found and
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 8
how you educate the Management Information System staff on what they could change to improve their
security situation with an action plan to keep their environment secure.
TASK – 01
1.1 Describe aims and objectives for vulnerability assessment project which you’re introducing. Your
explanation should include a brief introduction about the company, the MIS and other relevant
information to the assessment project.
1.2 Produce a comprehensive project management plan, The plan should include milestone schedule
and project schedule for monitoring and completing the aims and objectives of the project that
includes cost, scope, time, quality, communication, risk and resources management.
1.3 Produce a work breakdown structure and a Gantt Chart to provide timeframes and stages for
completion.
TASK – 02
2.1 Explain qualitative and quantitative research methods appropriate for meeting project aims and
objectives which you produced as vulnerability assessment project.
2.2 Evaluate the project’s management process and appropriate research methodologies applied, the
accuracy and reliability of different research methods applied for the small scale research
TASK – 03
3.1 Analyze research data using appropriate tools and techniques.
3.2 Describe appropriate recommendations as a result of research and data analysis to draw valid and
meaningful conclusions.
3.3 Evaluate the selection of appropriate tools and techniques for accuracy and authenticity to support
and justify recommendations.
TASK – 04
4.1. Provide a reflection on the value of undertaking the research to meet stated objectives with your
own learning and performance which includes a discussion of the project outcomes, its usefulness
to support sustainability of the given organization and its’ performance, the decision-making
process and changes or developments of the initial project management plan to support
justification of recommendations and learning during the project.
4.2. Evaluate the value of the project management process and use of quality research to meet stated
objectives and support own learning and performance
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 9
Grading Rubric
Grading Criteria Achieved Feedback
LO1 Establish project aims, objectives and timeframes based on
the chosen theme
P1 Devise project aims and objectives for a chosen scenario.
P2 Produce a project management plan that covers aspects of
cost, scope, time, quality, communication, risk and resources.
P3 Produce a work breakdown structure and a Gantt Chart to
provide timeframes and stages for completion.
M1 Produce a comprehensive project management plan, milestone
schedule and project schedule for monitoring and completing the
aims and objectives of the project.
LO2 Conduct small-scale research, information gathering and data
collection to generate knowledge to support the project
P4 Carry out small-scale research by applying qualitative and
quantitative research methods appropriate for meeting project
aims and objectives.
M2 Evaluate the accuracy and reliability of different research
methods applied.
D1 Critically evaluate the project management process and
appropriate research methodologies applied.
LO3 Present the project and communicate appropriate
recommendations based on meaningful conclusions drawn from
the evidence findings and/or analysis
P5 Analyse research and data using appropriate
tools and techniques.
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 10
P6 Communicate appropriate recommendations as a
result of research and data analysis to draw valid and meaningful
conclusions.
M3 Evaluate the selection of appropriate tools and techniques for
accuracy and authenticity to support and justify recommendations.
LO4 Reflect on the value gained from conducting the project and
its usefulness to support sustainable organisational performance
P7 Reflect on the value of undertaking the research to meet
stated objectives and own learning and performance.
M4 Evaluate the value of the project management process and use
of quality research to meet stated objectives and support own
learning and performance.
D2 Critically evaluate and reflect on the project outcomes, the
decision making process and changes or developments of the initial
project management plan to support justification of
recommendations and learning during the project.
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 11
Pearson
Higher Nationals in
Computing
Unit 6: Managing a Successful Computing Project
By
Raman Lakshan
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 12
Acknowledgement
In the accomplishment of the project successfully, I would like to express my thanks to the
people who have helped me most throughout my project. I am grateful to my lecturer Mrs.
Dilini Kumanayake and Miss. Ann Roshanie for nonstop support for the project. Their
assistance and insightful comments, and who willingly shared their expertise with me.
Especially I would like to thanks all Akshaya food city management to given the opportunity
to study their system.
Last but not the least I would like to thank my dearest friends and classmates who have helped
me a lot and made this possible to complete my project with all accurate information.
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 13
Table of Contents
Acknowledgement ................................................................................................................... 13
Table of Figures ....................................................................................................................... 17
Reference of tables. .................................................................................................................. 18
TASK – 01 ............................................................................................................................... 19
1.1 Describe vulnerability assessment project aims and objectives with a brief introduction
of company profile, the MIS and other relevant information to the assessment project. .... 19
1.1.1 Vulnerability assessment......................................................................................... 19
1.1.2 Importance of Vulnerability-assessment. ................................................................ 20
1.1.3 Project aims and objectives. .................................................................................... 20
1.1.4 The other key aims and objectives of vulnerability assessment project. ................ 20
1.1.5 Introduction of Akshaya Food City. ....................................................................... 21
1.1.6 Management Information System (MIS) ................................................................ 21
1.1.7 Other relevant information to the assessment project. ............................................ 22
1.2 Produce a comprehensive project management plan, milestone schedule and
project schedule for monitoring and completing the aims and objectives of the
project that includes cost, scope, time, quality, communication, risk and resources
management. ........................................................................................................................ 23
1.2.1 Introduction to Project Management Plan. ............................................................. 23
1.2.2 Project Scope Definition. ........................................................................................ 24
1.2.3 Project Aims and Objectives. .................................................................................. 24
1.2.4 Project schedule and milestones. ............................................................................ 25
1.2.5 Project Cost Management. ...................................................................................... 26
1.2.6 Project Communications Management. .................................................................. 26
1.2.7 Project Resource Management. ............................................................................... 27
1.2.8 Introduction to Risk Management........................................................................... 27
1.2.9 Risk Management Process. ..................................................................................... 28
1.2.10 Quality Management. ............................................................................................ 29
1.2.11 Time Management. ............................................................................................... 30
1.3 Produce a work breakdown structure and a Gantt chart to provide timeframes and
stages for completion. .......................................................................................................... 31
1.3.1 Work breakdown structure (WBS) ......................................................................... 31
1.3.2 Gantt chart ............................................................................................................... 32
Task - 02................................................................................................................................... 33
2.1 Explain qualitative and quantitative research methods appropriate for meeting project
aims and objectives which you produced as vulnerability assessment project. ................... 33
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 14
2.1.1 Introduction to qualitative research methods. ......................................................... 33
2.1.2 Introduction to quantitative research methods. ....................................................... 35
2.1.3 The research techniques that has been used for this research inside of qualitative
and quantitative research methods. .................................................................................. 38
2.2 Evaluate the project’s management process and appropriate research methodologies
applied, the accuracy and reliability of different research methods applied for the small
scale research. ...................................................................................................................... 42
2.2.1 Project Management Process. ................................................................................. 42
2.2.2 Accuracy and reliability of different research methods applied. ............................ 44
Task - 03................................................................................................................................... 45
3.1 Analyze research data using appropriate tools and techniques. ..................................... 45
3.1.1 Data analysis. .......................................................................................................... 45
3.1.2 Qualitative Analysis ................................................................................................ 46
3.1.3 Quantitative Analysis. ............................................................................................. 47
3.1.4 Data analysis from the interview. ........................................................................... 48
3.1.5 Data analysis from the questionnaires form. ........................................................... 50
3.2 Describe appropriate recommendations as a result of research and data analysis to draw
valid and meaningful conclusions. ....................................................................................... 52
3.2.1 Recommendation for vulnerability spotted in interview. ........................................ 52
3.2.2 Recommendation for vulnerability spotted in questionnaire. ................................. 53
3.3 Evaluate the selection of appropriate tools and techniques for accuracy and authenticity
to support and justify recommendations. ............................................................................. 54
3.3.1 Qualitative Analysis tools and techniques. ............................................................. 54
3.3.2 Quantitative Analysis tools and techniques. ........................................................... 55
3.3.3 Conclusion. ............................................................................................................. 55
Task - 04................................................................................................................................... 56
4.1 Provide a reflection on the value of undertaking the research to meet stated objectives
with your own learning and performance which includes a discussion of the project
outcomes, its usefulness to support sustainability of the given organization and its’
performance, the decision-making process and changes or developments of the initial
project management plan to support justification of recommendations and learning during
the project............................................................................................................................. 56
4.1.1 The value of undertaking the research to meet stated objectives and own learning
and performance in this research. .................................................................................... 56
4.1.2 Critically evaluate and reflect on the project outcomes, the decision-making
process and changes or developments of the initial project management plan to support
justification of recommendations and learning during the project. ................................. 57
4.2 Evaluate the value of the project management process and use of quality research to
meet stated objectives and support own learning and performance. ................................... 58
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 15
4.2.1 Value of project management process. ................................................................... 58
4.2.2 Use of quality research. ........................................................................................... 59
4.2.3 Own learning and performance by undertaking the research. ................................ 59
References. ............................................................................................................................... 61
Content References. ............................................................................................................. 61
Figure References. ............................................................................................................... 63
Gantt chart. ............................................................................................................................... 64
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 16
Table of Figures
Figure 1 Vulnerability-assessment-steps .............................................................................. 19
Figure 2 Risk Management Process ..................................................................................... 27
Figure 3 Risk Probability & Impact ..................................................................................... 28
Figure 4 Work Breakdown Structure .................................................................................. 31
Figure 5 Gantt chart .............................................................................................................. 32
Figure 6 Advantage and disadvantage of interview ............................................................ 39
Figure 7 Advantages and disadvantages of questionnaires ................................................ 40
Figure 8 Questionnaire Form................................................................................................ 41
Figure 9 Project Management Process ................................................................................. 42
Figure 10 Data Analysis tools ................................................................................................ 46
Figure 11 Vulnerability rate of interview data .................................................................... 49
Figure 12 Vulnerability rate of questionnaires ................................................................... 51
Figure 13 Assignment Gantt chart ....................................................................................... 64
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 17
Reference of tables.
Table 1 Project Schedule & Milestone ................................................................................. 25
Table 2 Estimated Budget ..................................................................................................... 26
Table 3 Project Communication Plan .................................................................................. 26
Table 4 data analysis of interview ........................................................................................ 49
Table 5 data analysis of questionnaires................................................................................ 50
Table 6 Actual cost ................................................................................................................. 60
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 18
TASK – 01
1.1 Describe vulnerability assessment project aims and objectives with a
brief introduction of company profile, the MIS and other relevant
information to the assessment project.
1.1.1 Vulnerability assessment.
Vulnerability assessment it is a security analysis that has the goal of identifying all the
potential vulnerabilities of systems and applications. Highly qualified personnel, in a second
moment, integrate and verify the results through manual activities. The testing process utilized
to distinguish and assign severity levels to as numerous security defects as possible in a given
timeframe. This process may include computerized and manual methods with shifting degrees
of thoroughness and an emphasis on comprehensive coverage. These activities have the
purpose of refining the research highlighting eventual errors during the process. A
vulnerability assessment Using a risk-based approach, vulnerability assessments sometime can
target distinctive layers of technology, the foremost common being the network, host and
application-layer assessments.
(vulnerability-assessment, 2020)
Figure 1 Vulnerability-assessment-steps
Source: (Vulnerability-assessment-steps, 2020)
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 19
1.1.2 Importance of Vulnerability-assessment.
Having anti-virus protection and being up thus far with all the newest system patches is
sometimes solely the primary step towards a truly secure network. Security is often overlooked
at the human level. For instance, network equipment may be deployed with default passwords,
with needless services running on the main server while default user accounts remain open.
Devices that are connected to the network also can be an attack vector; routers, switches,
printers are can be potential back doors for the hackers. Vulnerability assessments assist you
sanitize your network setting and cut back the attack surface to the bare minimum required to
successfully grow your business.
(Importance of Vulnerability assessment, 2020)
1.1.3 Project aims and objectives.
The impact of security vulnerability may enable an attacker to compromise the
availability, confidentiality or integrity of an organization. The main objective of this
vulnerability assessment project is to examine the multi dimensions of vulnerabilities in a
management Information System from the standpoint of a student researcher. Additionally
investigate the causes and impacts of vulnerabilities within computing systems and explore the
solutions the issues conferred in order to create recommendations to improve its security for
management information system.
(Vulnerability Analysis, 2020)
1.1.4 The other key aims and objectives of vulnerability assessment project.
Research about the different kind of Vulnerability and their impact in an
organization. To assess vulnerabilities, first should get a well knowledge about the
process of the select project area.
Recognizing the issues which can be discovered in the areas of installing,
configuring, and maintaining service and infrastructure equipment.
Recognizing the issues which can be occur during the practice of different Apartment
managers and staff tend to have different ways of managing it
Recommend solution for identifying issues through a document that list what steps
must be taken in order to mitigate Vulnerabilities and to secure informational
assets.
(Vulnerability Analysis, 2020)
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 20
1.1.5 Introduction of Akshaya Food City.
Akshaya Food City is a local e-supermarket where customers can shop for all their grocery,
beverages and household needs online and they provide doorstep delivery service to their
customers. What started small, with a single discount store and the simple idea of selling more
for less, has grown into one of the largest retailer in srilanka.
This is the only super market in kotahena area, satisfying consumers with whole sale prices for
all items, even on a single purchase. This Company located at Akshaya Food City, 284, Georg
R De Silva Mawatha, Colombo, Sri Lanka.
1.1.6 Management Information System (MIS)
An organized approach of the study of the information requirements of an organization's
management at each level in creating tactical, strategic and operational decisions. In the
management information system, modern and computerized systems continuously gather the
relevant data, each from within and outside of an organization. This data is then will be
integrated, processed and stored in a centralized database where it is always upgraded and made
accessible to all the authorized user of that organization.
Characteristics of Management Information System (MIS)
Management Information System (MIS) is mainly designed to take care of the needs of
the managers in the organization.
Management Information System (MIS) helps in integrating the information which are
created by different departments of the organization.
Management Information System (MIS) helps in spotting a suitable mechanism for
storage of data.
Management Information System (MIS) helps in establishing mechanisms to remove
redundancies in data.
(profile, 2020)
[Left Space Intentionally]
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 21
1.1.7 Other relevant information to the assessment project.
CIA Triangle.
Confidentiality, integrity and availability, also known as the CIA triad, is a security model
which created to guide information security policies within an organization. The three elements
of the CIA triangle are considered the three most crucial components of security.
Confidentiality: Confidentiality is the security principle that controls access to
information. It is designed to ensure the wrong people cannot gain access to sensitive
information like bank account statements, personal information, credit card numbers,
trade secrets, government documents while ensuring the right people can access it.
Integrity: The second component of the triad, integrity assures the sensitive data is
trustworthy and accurate. Trustworthiness, consistency, and accuracy of data should be
maintained over its life cycle. Sensitive data should not be altered in transit, and security
measures, such as file permissions and user access controls, should be taken to make
sure that it can't be changed by unauthorized users. In addition, backups or redundancy
plans should be planned and implemented to restore any affected data in case of an
integrity failure or security breach in order to restore data back to its correct state.
Availability: Availability is that the guarantee of reliable and constant access to your
sensitive data by only authorized people. It is best guaranteed by properly maintaining
all software and hardware necessary to make sure the availability of sensitive data. It’s
also vital to keep up with the system upgrades. Providing adequate communication
throughput and preventing bottleneck helps as well.
(Bashay, 2020)
[Left Space Intentionally]
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 22
1.2 Produce a comprehensive project management plan, milestone
schedule and project schedule for monitoring and completing the aims
and objectives of the project that includes cost, scope, time, quality,
communication, risk and resources management.
1.2.1 Introduction to Project Management Plan.
A project management plan is a formal document which defines how the project is going to be
carried out. It outlines the goals, scope, timeline, deliverables and budget of a project, and this
are essential to keeping a project on track so fundamentally, a project plan should tell
stakeholders what needs to get done, how it will get done, and when it will get done.
The main elements of a Project Management Plan:
Executive Summary: A brief description of the contents of the report.
Project Scope & Deliverables: An overview of the boundaries of the project, and an
outline of how the project will be broken down into measurable deliverables.
Project Schedule: A high-level read of project tasks and milestones (Gantt charts are
handy for this).
Project Resources: The budget, personnel, and other resources required to meet project
goals.
Risk and Issue Management Plan: A list of factors that would derail the project and a
plan for how the problems will be identified, addressed, and controlled.
Communication Management Plan: A plan for how team and stakeholder
communication will be handled over the course of the project.
(Project Management Plan, 2020)
[Left Space Intentionally]
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 23
1.2.2 Project Scope Definition.
Akshaya Food City is consist of three main system which are Accounts management system,
Stock management system, Order management system. Among them I have chosen Order
management system to do a vulnerability assessment. In Order management system customer
registration, customer order management, delivery management would be happen.
Project deliverables:
To identify vulnerabilities that might related with the Order management system.
To investigate the possible causes and impacts of security issues.
To suggest measures to overcome vulnerability issues in the Order management system.
To make recommendations to improve its security issues in the Order management
system.
1.2.3 Project Aims and Objectives.
The Project Aim and objective is to assess vulnerabilities of Order management system in
Akshaya Food City and make recommendations to improve its security of system resources
and client information.
[Left Space Intentionally]
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 24
1.2.4 Project schedule and milestones.
Project Schedule
Milestone Start Date End Date Status
1.Initiation 18/10/2020 27/10/2020 Completed
1.1 Define process for gathering 18/10/2020 20/10/2020 Completed
requirements
1.2 Analyze the requirements 21/10/2020 23/10/2020 Completed
1.3 Project statement 24/10/2020 26/10/2020 Completed
development
1.4 Project statement approval 27/10/2020 27/10/2020 Completed
2. Planning 28/10/2020 10/11/2020 Completed
2.1 Project plan development 28/10/2020 06/11/2020 Completed
2.2 Work breakdown structure 07/11/2020 09/11/2020 Completed
2.3 Gantt Chart 10/11/2020 10/11/2020 Completed
3. Execution 11/11/2020 22/11/2020 Completed
3.1 Analyzing Vulnerabilities 11/11/2020 16/11/2020 Completed
3.2 Implement Vulnerability 17/11/2020 19/11/2020 Completed
Assessment tool
3.3 Characterize impacts of 20/11/2020 22/11/2020 Completed
Vulnerabilities
4. Closure 23/11/2020 07/12/2020 Completed
4.1 Project Analysis 23/11/2020 30/11/2020 Completed
4.2 Project Report 01/12/2020 07/12/2020 Completed
Table 1 Project Schedule & Milestone
Source: Author’s work
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 25
1.2.5 Project Cost Management.
Cost management is the process of estimating, controlling, and allocating the costs of the
project. It permit a business to anticipate coming expenses in order to decrease the possibility
of it going over the budget.
Cost Details Cost Total Cost
Travelling Charges 700.00
Call Charges 200.00
Internet Charges 750.00
Printout Charges 150.00
Stationeries Charges 800.00
Total Cost 2,600.00
Table 2 Estimated Budget
Source: Author’s work
1.2.6 Project Communications Management.
A project management communication plan pinpoint how the important information can be
communicated to stakeholders through the whole project.
Deliverable Info Recipient Delivery Schedule Who is
(What) (Who) Method (When) Responsible
(How) (Owner)
Project Company Manager Meeting As needed Project Manager
Information Company Owner Conference call
Project Analysis Company Manager Meeting Every Project Manager
Company Staff Phone calls Weekdays
Company Customers
Project Review Company Manger Meeting Last day Project Manager
Company Staff
Table 3 Project Communication Plan
Source: Author’s work.
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 26
1.2.7 Project Resource Management.
Project Resource management is an aspect of the project management process that plans,
organizes, manages, and measures people's work. Its purpose is to plan, allocate and schedule
the company's resources as efficiently as possible.
Resource Management Plan: Is a tool which project managers use to gain the instruction on
how should a project resources managed, allocated, categorized and released.
1.2.8 Introduction to Risk Management.
Project risk management is the method of identifying, analyzing and then responding to any
risk that appear over the life cycle of a project to assist the project to stay on track and meet its
goal. A risk is whatever that could probably impact the project’s performance, budget or
timeline and in a project management context, if risk become realities, then they become
classified as “issues” that need to be addressed.
So the plan outlines a strategy to spot, analyze, track and reduce risks throughout the project
lifecycle. Identifying and managing risk will increase the possibility of a successful project
completion by reducing uncertainty related to the project.
(Ray and Ray, 2020)
Figure 2 Risk Management Process
Source: (risk-management-process, 2020)
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 27
1.2.9 Risk Management Process.
Risk identification
This is the first step of risk management process. As you do go through this step, you will
determining threats which could potentially affect to the company or its system.
Risk Analysis
This is the step that access the identified risk and during this step, you will assess the probability
and fallout of each risk to determine which factor should be focus first. Factors such as potential
financial loss to the organization, time lost, and severity of impact all play a part in accurately
analyzing each risk.
Figure 3 Risk Probability & Impact
Source: (risk-analysis, 2020)
Risk Evaluation
In this step you can evaluate or designate the risk by deciding the risk magnitude, which was a
fusion of consequence and likelihood. You can take decisions about whether it is serious
enough to warrant treatment or is the risk acceptable.
Risk Treatment
This is the forth step of risk management process and it is also known as Risk Response
Planning. In this step you evaluate your highest ranked risks and set forth a plan to modify or
treat these risks to attain acceptable risk levels.
[Left Space Intentionally]
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 28
Risk Monitor and Review
This is the last step of risk management process and in this step where you can take the Project
Risk Register and use it to monitor, track and review risks. This step will guarantee that the
specified management plans and action stays relevant and updated.
(Development, 2020)
1.2.10 Quality Management.
The mechanism by which quality is handled and maintained within a project is project quality
management. Although the meaning may suggest that "quality means "perfection," it is
generally all about maintaining continuity of quality in a project in this situation. Nevertheless,
what is specifically meant by "quality" is linked to what the client or stakeholder wants from
the project, and may therefore vary on a per-project basis.
Project quality management contains three main processes:
Quality management planning: This includes defining the project and product quality
specifications and expectations. The purpose of quality control of the project should be openly
communicated with all stakeholders and appropriate roles should be allocated to those
responsible.
Quality assurance: Which requires auditing the quality criteria and outcomes of quality
management to ensure that adequate quality standards are used. If expectations are not met or
targets are not met, appropriate steps and corrective measures should be taken to address these
problems.
Quality control: This requires tracking and documenting the outcomes of quality operations
in order to measure performance and suggest the appropriate improvements.
(Project Quality Management, 2020)
[Left Space Intentionally]
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 29
1.2.11 Time Management.
Time Management is the art of organizing, arranging and scheduling activities in a way that
optimizes the highest level of productivity and success for an individual or perhaps a team.
Time management is of critical importance, especially in the context of project management.
One of the main reason for the failure of projects is the lack of control of project time or in
other words, non-compliance with the project schedule. The signs of projects failing due to
scheduling issues are that goals are not being reached, completion deadlines are delayed, and
a project that slips its schedule eventually results.
The Processes of Time Management:
Define activities: Identifies the necessary collection of activities and the "Activity List"
is the chief performance.
Sequence Activities: Understand the logical connection between the activities listed
and bring them out. The Schedule Network Diagram is the most significant
performance of this method.
Estimate Activity Resources: Estimate and document the type and amount of
resources needed for each of the specified activities. Action resource specifications and
resource breakdown structure are the key outputs of this approach.
Estimate Activity Durations: This is the method of estimating the time units required
for each activity, depending on the scope of activities. Activity Duration Estimates are
the principal result of this process.
Develop Schedule: The schedule is developed taking into account the outputs of all
previous processes and reaching an optimal combination of dependencies, resources
and durations with a realistic schedule.
Control Schedule: This is the method of monitoring scheduled project status with
respect to planned Schedule. Some of the most important parameters of project
performance are determined, such as variance and schedule performance index.
(What is Time Management?, 2020)
[Left Space Intentionally]
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 30
1.3 Produce a work breakdown structure and a Gantt chart to provide
timeframes and stages for completion.
1.3.1 Work breakdown structure (WBS)
Figure 4 Work Breakdown Structure
Source: Author’s work
[Left Space Intentionally]
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 31
1.3.2 Gantt chart
Figure 5 Gantt chart
Source: Author’s work
[Left Space Intentionally]
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 32
Task - 02
2.1 Explain qualitative and quantitative research methods appropriate for
meeting project aims and objectives which you produced as vulnerability
assessment project.
2.1.1 Introduction to qualitative research methods.
Qualitative research involves gathering and examine of non-numerical data such has audio,
video, or text to acknowledge opinions, experiences, or concepts. This can be used to collect
in-depth awareness into an issue or create new research ideas.
Qualitative research is often used in the social sciences and humanities, in subjects such as
education, history, health sciences, education, sociology, anthropology and etc.
Qualitative research methods.
In qualitative research method every research approaches of it involves usage of one or more
data gathering methods. These are some of the most popular qualitative methods:
Observations: This is a method where researchers record what they have encountered,
seen or heard in a detailed field notes.
Interviews: This is considered has the most popular qualitative research method where
researchers personally ask a person questions in one-on-one conversations.
Focus groups: This method also consider has most popular in qualitative research
method where researchers ask questions and creating discussion among a limited group
of people.
Surveys: This is a method where researchers distribute questionnaires with open-ended
questions.
Secondary research: This method used to gathering existing data in such a form of
video or audio recordings, images, texts etc.
[Left Space Intentionally]
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 33
Advantages of qualitative research.
Flexibility: The analysis process and data collection can be convert as into new ideas,
questioning can be adapted in real-time to the nature and quality of information being
accumulated.
Meaningful insights: Detailed descriptions of people’s feelings, perceptions and
experiences will be a key to use in improving designing or testing of the products or the
systems.
Creation of new ideas: Open-ended feedback mean that the researchers can detect
opportunities or problems that they wouldn’t have thought of otherwise.
Disadvantages of qualitative research.
Unreliability: The real-world setting frequently set the qualitative research has
inconstant because of uncontrolled factors which are affects the data.
Subjectivity: Because of researcher's primary role in interpreting and analyzing the
data, replication of qualitative research cannot be done. The researcher will decides
what was important and what was unrelated in data analysis, therefore interpretations
of a same data can vary greatly.
Limited generalizability: In order to obtain accurate details about particular contexts,
small samples are also used. Despite rigorous analysis procedures, it is difficult to draw
generalizable conclusions despite stringent research methods, since the data may be
biased and unrepresentative of the larger population.
Labor-intensive: While it is possible to use software to manage and document vast
amounts of text, data analysis also needs to be manually checked or carried out.
(Base and research, 2020)
[Left Space Intentionally]
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 34
2.1.2 Introduction to quantitative research methods.
Quantitative research involves gathering, analyzing and interpreting numerical data. By
collecting numerical data and conducting computational, mathematical, or statistical
techniques, quantitative research is characterized as a systematic investigation of phenomena.
Quantitative research uses sampling techniques to gather data from current and prospective
customers and send out online surveys, online surveys, questionnaires, etc. the findings of
which can be expressed in numerical form.
Mainly there are two quantitative research methods and the have mentioned below.
Primary quantitative research methods
Secondary quantitative research methods
1. Primary quantitative research methods.
This is the most widely used method in market researches. The main feature of this method is
the researcher does not depend on the data which are collected on previously. Updated data
would be used in primary quantitative methods. As long the process flow, primary quantitative
research architecture can be divided into three more distinctive tracks Techniques and Types
of Studies, Data collection methodologies, Data analysis techniques. Few primary quantitative
methods have mentioned below.
Survey Research: In survey research a set of questions would be asked from the
respondents regarding to research. This research method can be done as online surveys,
online polls, paper questioners, web-intercept surveys and etc.
Correlational research: This method is conducted to create a link between two
closely-knit entities and how one affects the other and what changes are ultimately
observed. In order to provide value to naturally occurring relationships, this research
method is carried out and a minimum of two separate groups are needed to effectively
perform this quantitative research method.
Causal-comparative research: This method also known has quasi-experimental
research and this research mostly depends on the comparison factor. Researchers use
this technique to finish the cause-effect equation in between two or more variables,
where one variable depends on the independent variable of the other.
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 35
2. Secondary quantitative research methods.
In this method, researches use already collected data like the government resources, internet,
research reports, libraries, etc. Sometimes these data could be outdated. To increase the overall
efficiency of research, these current data are summarized and collated. Some methods of this
type have been listed below.
Data on the internet: With any information under any topic are available on the
internet this method has become increasingly easy to perform. Data is accessible online
on most research subjects, which helps to improve the validity of primary quantitative
data as well as show the importance of previously collected data.
Non-government and Government sources: It is also possible to perform secondary
quantitative research with the aid of non-government and government sources that deal
with market research studies. This knowledge is extremely accurate and in-depth, and
can thus be used to improve the validity of the design of quantitative research.
Sources of commercial information: Local newspapers, newspapers, magazines,
radio and television stations provide a great source to refer data for secondary
quantitative research. First-hand in-depth information on economic trends, the political
agenda, demographic segmentation, market analysis, and related topics is available
from these commercial information sources.
Advantages of quantitative research.
Testing and checking can be achieved: Careful experimental design and the ability
for others to reproduce both the test and the findings are required for quantitative
testing. This makes the knowledge you are gathering more credible and less open to
contention.
Straightforward review: The type of results will tell you which statistical measures
are suitable to use when you gather quantitative data. As a result, it is easy to interpret
the data and present those results and less open to error and subjectivity.
Prestige: Since many people don't understand the mathematics involved, research
involving complicated statistics and data analysis is considered useful and impressive.
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 36
Disadvantages of quantitative research.
False reliance on statistics: In its pursuit of specific statistical relationships,
quantitative analysis can be constrained, which can lead to researchers missing wider
themes and relationships. You run the risk of overlooking surprising or large-scale data
that can help your company by concentrating solely on numbers.
Difficulty in setting up a model for analysis: You need to carefully establish a
hypothesis and set up a model for gathering and evaluating data when you perform
quantitative research. All the findings can be invalidated by any mistakes in the set-up,
bias on the part of mistakes in execution or the researcher.
It may be deceptive: Many people believe that it is more reliable or scientific than
observational, qualitative analysis, since quantitative research is focused on statistics.
Both sorts of analysis, however can be arbitrary and deceptive.
(Quantitative Research, 2020)
[Left Space Intentionally]
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 37
2.1.3 The research techniques that has been used for this research inside of qualitative
and quantitative research methods.
I have used both qualitative and qualitative and quantitative research methods to do this
research. On qualitative research method I used individual interview it is used to gain an
understanding of underlying reasons, opinions, and motivations. On quantitative research
method I used questionnaires which produce either numerical data or data that can be put into
categories for example yes or no answers.
1. Interviews
A discussion in which someone tries to get data from another person is an interview. The term
"interview" in common parlance refers to a one-on-one discussion between an interviewee and
an interviewer. The interviewer may take a formal or informal approach, either encouraging
the interviewee to talk openly about a particular issue or asking pre-determined specific
questions. It is often difficult to pay attention to the non-verbal elements of communication and
to recall everything.
Reasons for using interviews in this research:
Interviews can be helpful as a follow-up to some survey respondents.
Interview can be helpful to discover how people think and feel about a subject and why
they hold those views.
Interview can be helpful to address some sensitive topics which in a focus group people
may feel uncomfortable addressing.
Interview can be helpful to deepen knowledge and clarify statistical evidence.
Interview can be helpful to add a human perspective to impersonal data.
[Left Space Intentionally]
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 38
Figure 6 Advantage and disadvantage of interview
Source: (advantage & disadvantage of interview, 2020)
Some Interview questions which has been asked from company manager for this
research.
1. Does the organization have a backup server?
2. Does the antivirus software has been installed in data processing servers?
3. Does the stock handling processed on system every day?
4. Do you use fingerprint readers to Keep track of the attendance and time of your
employees?
5. Do you get notified when a new order has been placed on the system?
6. Does a customer get notified if products on the system are out of stock?
7. Can the system show all the details of orders and the payments of customers?
8. Do this system provide a feedback option for the customers to give a feedback after
they receive their products?
[Left Space Intentionally]
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 39
2. Questionnaires
A questionnaire is a study tool consisting of a set of questions for the goal of collecting
respondent data. Face to face, by telephone, machine or post, they may be carried out.
Questionnaires offer a relatively inexpensive, fast and effective way for a large sample of
individuals to collect large quantities of information. Data can be obtained reasonably easily
because when the questionnaires have been completed, the researcher does not need to be
present. This is beneficial for large populations where it would be inconvenient for interviews.
Reasons for using questionnaires in this research:
Questionnaires can be helpful to find the needs, aspirations, opinions, interests and
desires of users.
Questionnaires are relatively easy and straightforward to evaluate.
Questionnaires are helpful to find user satisfaction with services and collection.
Questionnaires are helpful to gather information on a large sample of data at relatively
low cost.
Questionnaires are simple and fast to complete for the respondent.
Figure 7 Advantages and disadvantages of questionnaires
Source: (Advantages & disadvantages of questionnaires, 2020)
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 40
Questionnaires form that has been used for this research.
Figure 8 Questionnaire Form
Source: Author’s work
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 41
2.2 Evaluate the project’s management process and appropriate research
methodologies applied, the accuracy and reliability of different research
methods applied for the small scale research.
2.2.1 Project Management Process.
One of the essential phases of any project is project management. This is due to the fact that
the central mechanism that binds all other project activities and processes together is project
management.
There are plenty when it comes to the tasks of project management. However it is possible to
categorize these several project management practices into five main processes.
Figure 9 Project Management Process
Source: (Project Management Process, 2020)
Initiating: The proposal is conceptualized during this phase and feasibility is decided.
Some tasks that should be carried out during this phase, according to the SME Toolkit,
include defining the project objective; defining the scope of the project; identifying the
project manager and key stakeholders; identifying possible risks; and creating an
approximate budget and timetable.
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 42
Planning: First from ideation to completion, the project manager will create a blueprint
to direct the whole project. This blueprint will map the scope of the project; the
resources needed to produce the deliverables; the expected time and financial
commitments; the communication strategy to ensure that stakeholders are kept up-to-
date and involved; the implementation plan; and the continued maintenance proposal.
Executing: The project manager will perform the procurement needed for the project
at this stage, as well as staff the team. In addition, the team members would carried out
their own assignments within the given deadline for each activity in order to achieve
the defined targets.
Monitoring and control: In this phase, Project managers will assess the progress of
each task closely to ensure the proper execution of the project. Documentation such as
data collection and verbal and written status reports can usually be used to assess that.
If a change is needed, it will happen at this point.
Closing: The group of closing processes takes place once the project deliverables have
been generated and checked and accepted by the stakeholders. All documentation will
be archived and a final project report will be produced during this process.
(What Are Project Management Processes?, 2020)
[Left Space Intentionally]
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 43
2.2.2 Accuracy and reliability of different research methods applied.
In doing good research, data accuracy and reliability are very important concerns since
incomplete and unreliable data leads to spurious or incorrect conclusions. Two separate
analysis methods has been used to carry out this research in order to achieve project aim and
objectives. There are qualitative research methods and quantitative research methods.
The qualitative research method is carried out by generating ideas through in-depth research
that helps to create an observational and interpretative view of the human and social sciences.
This type of data is process-oriented and is not observable. To gain an understanding of the
underlying causes and motives, qualitative research is conducted to discover prevalent patterns
in thoughts and samples. It is non-statistical data analysis which focuses on organizations,
individuals, in-depth interviews, community conversations to understand the opinions of
people. It helped a lot to achieve the aims and objectives of this project.
Similarly, quantitative research approaches have often been used to measure data and
generalize outcomes from a survey to populations of interest, often followed by qualitative
research to discuss some further findings. Typically, a significant number of cases reflecting
the population of concern are included. Its results are descriptive and conclusive. With the aid
of questionnaire, the data is obtained by asking various project-related questions by the phone.
Conclusions
Since, different research methods applied in a systematic way in this project like interviews are
done to face to face and some group discussions also been executed. Likewise, lots of peoples
are involved in questionnaire research method. And the results are almost all positive, verifying
that the research techniques used to find people's opinions on this Order management system
are accurate and reliable for the project to proceed.
[Left Space Intentionally]
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 44
Task - 03
3.1 Analyze research data using appropriate tools and techniques.
3.1.1 Data analysis.
In simple terms, Data analysis is the method of gathering and arranging data to draw valuable
conclusions from it. To extract knowledge from the data, the data analysis process uses
analytical and logical reasoning.
The main aim of Data Analysis is to derive valuable data from the data and to make decisions
based on the analysis of the data. There are two main methods of Data Analysis used in this
research:
Qualitative Analysis
Quantitative Analysis
Data Analysis Techniques
Depending on the topic at hand, the form of data, and the amount of data obtained, there are
various methods for data analysis. In order to turn facts and figures into decision-making
criteria, each focuses on strategies for taking on new data, mining knowledge, and digging into
information.
Accordingly, the different techniques of data analysis can be categorized as techniques based
on:
Mathematics and Statistics.
Artificial Intelligence and Machine Learning.
Visualization and Graphs.
Data Analysis Tools.
Data analysis tools can help the users to manipulate and process data, analyze the relationships
and correlations between data sets, and also help on greater insights into their customers,
business, and industry. Here are some example tools for Data Analysis: Excel, Tableau, Power
BI, Fine Report, R & Python.
(What is Data Analysis?, 2020)
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 45
Figure 10 Data Analysis tools
Source: (data-analysis-tools, 2020)
3.1.2 Qualitative Analysis
Qualitative Analysis mainly give an answers to questions such as ‘why,’ ‘what’ or ‘how’. With
the help quantitative methods such as interview transcripts, attitude scaling, standard results,
and more, each of these questions is answered.
Qualitative analysis can be split into five main categories:
Content analysis: This refers to the method of categorizing verbal or behavioral data
to arrange, summarize and identify the data.
Narrative analysis: This approach includes reformulating the stories presented by the
participants, taking into account the context of each case and the various perspectives
of each participant.
Discourse analysis: An approach of analysis of naturally occurring expression and all
forms of written text.
Framework analysis: This is a more detailed methodology consisting of many steps,
such as familiarization, the recognition of a thematic structure, coding, graphics,
mapping and interpretation.
Grounded theory: To formulate a concept, this process of qualitative data analysis
begins with an analysis of a single event. Then, to see if they relate to the concept,
additional cases are investigated.
(Qualitative Data Analysis, 2020)
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 46
3.1.3 Quantitative Analysis.
Quantitative analysis is focused on statistically and numerically representing and analyzing
objects. The goal of quantitative analysis is to analyze the data obtained by numerical variables
and statistics for the phenomenon. The estimation of frequencies of variables and variations
between variables can be used in quantitative data analysis. In general, a quantitative approach
is associated with seeking evidence to validate theories that you have developed in the earlier
stages of the research phase. Descriptive statistics and inferential statistics are the two most
widely used quantitative data analysis techniques.
A list of widely used descriptive statistics is presented below:
Mean: The numerical average of a value range.
Median: The midpoint of a number value range.
Mode: The most common value among a set of values.
Percentage: used as a percentage of the whole to express a collection of scores or
values.
Frequency: The amount of times it finds a value.
Range: The highest value in a set of values, and the lowest value.
(Bhatia and Bhatia, 2020)
[Left Space Intentionally]
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 47
3.1.4 Data analysis from the interview.
The response for the interview with the company manager has shown in the below table:
Questions Response from company manager Vulnerability Risk
or not
1. Does the organization have a backup server? No, we don’t have a backup server. Vulnerability High
2. Does the antivirus software has been installed in data There is no antivirus software has been installed on data Vulnerability High
processing servers? processing server.
3. Does the stock handling processed on system every No, stock handling processes only done once a week. Vulnerability High
day?
4. Do you use fingerprint readers to Keep track of the No, the attendance is marked in a book. Vulnerability Medium
attendance and time of your employees?
5. Do you get notified when a new order has been placed Yes, the new order will be notified to my mail for every Not Low
on the system? order that made on system. Vulnerability
6. Does a customer get notified if products on the system Yes, customer will get an alert when the items are out of Not Low
are out of stock? stock. Vulnerability
7. Can the system show all the details of orders and the This system comes with full detailed report of the orders Not Low
payments of customers? and payment so yes I can check every details of it. Vulnerability
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 48
8. Do this system provide a feedback option for the Yes, after every product is delivered customers can Not Low
customers to give a feedback after they receive their provide there feedback in our system which we analyze Vulnerability
products? to improve our service.
Table 4 data analysis of interview
Source: Author’s work
Pie chart analyze for interview questions vulnerability rate:
Figure 11 Vulnerability rate of interview data
Source: Author’s work
This pie chart represent the vulnerability rate for data analysis of interview response from the company manager and blue represent the percentage
of vulnerability rate so according to the response gained from interview there is fifty percentage vulnerability noticed from this analysis.
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 49
3.1.5 Data analysis from the questionnaires form.
The response of questionnaire form about client security risk assessment has been taken from
10 staffs and it has been shown in the below table:
Question Number of users Number of users Is the overall response Risk
No answered ‘Yes’ answered ‘No’ considered has a
vulnerability or not
1 10 0 No Low
2 2 8 Yes High
3 0 10 Yes High
4 4 6 Yes Medium
5 5 5 Yes Medium
6 10 0 No Low
7 0 10 Yes High
Table 5 data analysis of questionnaires
Source: Author’s work
[Left Space Intentionally]
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 50
Bar chart analyze for questionnaire vulnerability rate:
Figure 12 Vulnerability rate of questionnaires
Source: Author’s work
The above chart represent the security vulnerability rate of data analysis on questionnaire
response gained from staffs of akshaya food city. In this chart the horizontal line represent
vulnerability rate and the vertical line represent the question numbers so according to the
response there is no vulnerability spotted in question 1 and question 6 because of that there is
no any vulnerability rate showing on question 1 and question 6 but other questions are spotted
vulnerability and question 3 and question 7 showing high rate of vulnerability.
[Left Space Intentionally]
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 51
3.2 Describe appropriate recommendations as a result of research and data
analysis to draw valid and meaningful conclusions.
3.2.1 Recommendation for vulnerability spotted in interview.
As per the response form collected from interview question one to four considered has
vulnerabilities. Recommendation to fix those vulnerabilities given below:
According to question one this company don’t have a backup server and it’s a main
vulnerability risk considering all this company system relied on one server so in case
of server failures every process of this company will get shutdown until the server
respond back. This can lead to data losses and customers won’t be able to place any
orders so I highly recommend to set a backup server to resolve this vulnerability risk.
According to question two this company data processing server running without a
antivirus software is another main vulnerability risk considering if the server get
affected with virus its can lead to data lose, time lose and its can cost the company to
clear the virus from server so its highly recommended to install original antivirus guards
on the data processing server.
According to question there this company is not processing the stocks on system every
day. This is a vulnerability risk because considering there are more than fifteen new
orders per day if the stock is not handled every day it can lead to data storing error on
day end process and customers could order the products which are not in stock it can
lead to customer dissatisfaction on product delivery. Therefore I highly recommend to
process the stock handing every day to resolve this vulnerability risk.
According to question four not having a fingerprint reader to keep the track of
attendance will lead to vulnerability risk because the need to classify individuals is
especially important in the workplace, as it is often related to staff attendance, security,
and payroll in the workplace. So I highly recommend to have a fingerprint reader so
they can quickly identify employees and verify and keep the track of everything clearly.
[Left Space Intentionally]
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 52
3.2.2 Recommendation for vulnerability spotted in questionnaire.
As per the response form collected from questionnaire question two, three, four, five and seven
considered has vulnerabilities. Recommendation to fix those vulnerabilities given below:
According to question two there are eight staffs who are not taking backup on regular
schedule and it’s a vulnerability risk considering accidents like deleting important files,
Damages to a hard drive and Power failures often occur when you least expect them
and when one happens it can lead to data loss so it is best to be prepared by backing up
the computer according to the regular schedule it can prevent the data loss.
According to question three not having a disaster recovery plan is a huge vulnerability
risk because disaster can strike via many routes. One of the most common is IT security
breaches and hacking attempts: this can lead to anything from the disclosure of
personally identifiable data to the irreversible loss of customer data so I highly
recommend to implement a disaster recovery plan to the data processing facilities to
avoid these issue and it’s also help this company on the elimination of unnecessary
hardware and reduce the risk of human error.
According to question four there are six staff not using VPN when accessing the
companies system it’s a vulnerability risk because a VPN can allow staffs to share files
securely and keep the data secure and encrypted and away from the prying eyes of
hackers while working remotely. So I highly recommend that every staffs should use
VPN to access the company system.
According to question five there are five computers runs without an antivirus guard and
it’s a vulnerability risk because if the computer get affected with virus its can lead to
data lose so it’s highly recommended to install original antivirus guards on all the
computer on this company.
According to question seven not performing a vulnerability scan regularly on network
is a huge vulnerability risk because there's a chance of a hacker taking advantage of
some new vulnerability any time a device connects to the Internet. So I highly
recommend to do the vulnerability scan regularly on network to prevent hacking and
regular vulnerability scan also will help on analysis and reporting of potential security
issues on a network and an external scan can simulate how hackers would try to gain
access to this company network.
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 53
3.3 Evaluate the selection of appropriate tools and techniques for accuracy
and authenticity to support and justify recommendations.
3.3.1 Qualitative Analysis tools and techniques.
Qualitative research is something which is hard to predict, it requires lot of cognitive
analysis. Qualitative Research is also used to uncover trends in thought and opinions,
and dive deeper into the problem. Qualitative data collection methods vary using
unstructured or semi-structured techniques.
Qualitative data is best processed manually by the tool. Categories data according to themes.
The purpose of a research project is after all, to provide answers to the research questions and
to achieve the research goals.
In below there are some software tools mentioned:
NVivo: This software used for both qualitative and mixed-methods analysis. Is
particularly used for analysis of free audio, text, image, and video data from focus
groups, interviews, social media, journal articles and polls.
Text Analysis: A method for the identification of themes in texts and was developed
for use in research on ethnography and discourse. The researcher can also analyze
coded content, extract it, and save it.
QDA Miner: This is a program for qualitative analysis that lets you handle documents
and carry out basic tasks for qualitative analysis.
(Qualitative Data Analysis tools, 2020)
[Left Space Intentionally]
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 54
3.3.2 Quantitative Analysis tools and techniques.
For a broad range of applications and industries, quantitative data collection and analysis tools
are described as a set of charts, maps, and diagrams designed to collect, analyze, and present
data. Various systems and methodologies, from production and quality assurance to research
groups and data collection agencies, have been developed for use in almost every sector.
Although we need to understand what to do with the information and how to interpret the data,
statistical analysis software will make this process as smooth and as easy as possible. There are
a wide number of methods available for statistical data analysis, and there are some of them
listed below:
Microsoft Excel: Although not a cutting-edge statistical analysis solution, MS Excel
provides a broad range of data visualization and basic statistics tools. Summary metrics
and customizable graphics and figures are easy to produce, making it a functional tool
for those who want to see the basics of their data.
Spss: A statistical general purpose package commonly used for editing, evaluating and
presenting numerical data in academic science.
R: Free statistical computing and graphics program environment. It compiles and runs
on a wide range of UNIX, Windows and MacOS platforms. R is extremely extensible
and offers a wide range of statistical and graphical techniques.
(Quantitative Data Analysis tools, 2020)
3.3.3 Conclusion.
According to the analysis tools and techniques that have been mentioned above I recommend
Microsoft Excel has an analysis solution because excel is real easy to use, the easiest to learn
and the interface also so simple to use. The summary metrics and customizable graphics and
figures are easy to produce on Microsoft Excel and many of the Microsoft Excel add-ons are
open source. It’s also very easy to create workbooks that hook up to Access and SQL databases
and refresh this data to create an up to date data analysis in Microsoft Excel. So the Microsoft
Excel can be a perfect solution to provide an accurate data analysis.
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 55
Task - 04
4.1 Provide a reflection on the value of undertaking the research to meet
stated objectives with your own learning and performance which includes a
discussion of the project outcomes, its usefulness to support sustainability
of the given organization and its’ performance, the decision-making
process and changes or developments of the initial project management
plan to support justification of recommendations and learning during the
project.
4.1.1 The value of undertaking the research to meet stated objectives and own learning
and performance in this research.
The Research objectives were, To Investigate possible vulnerabilities within the Order
management system of akshaya food city and to investigate the causes and impacts of
vulnerabilities and to recommend measures to overcome vulnerability issues in the system.
In reflecting on the research carried out, the project management plan provides the methods
and ways from starting to end process. It is a crucial method and requires the understanding or
knowledge to gain the experience in the specific field and with the help of qualitative and
quantitative research methods all the project objectives were fulfilled successfully and the
Gantt chart and WBS helped to monitor and manage the time duration within the project
timeframe until the aims and objectives being accomplished.
The observations of this research are very significant for akshaya food city as there have not
been any vulnerability assessment done in similar capacity. To identify the loop holes and
drawbacks of the existing system, this research contributed positively and this research helped
to identify vulnerabilities of this system and bad practices of staffs while using a company
system and Then, based on their vulnerabilities, the project manager was able to provide
solutions for the vulnerabilities that been found and reduce the risks that akshaya food city will
face in the future.
[Left Space Intentionally]
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 56
Conclusion
From the above research, it can be concluded that akshaya food city was able to identify their
system’s vulnerabilities and they have got a clear idea to fix the vulnerabilities that has been
found and by resolving those vulnerabilities this research will be help them to increase their
company productivity.
4.1.2 Critically evaluate and reflect on the project outcomes, the decision-making process
and changes or developments of the initial project management plan to support
justification of recommendations and learning during the project.
Project outcomes, the decision-making process and changes or developments of the initial
project management plan can lead to the creation of deep and appropriate recommendations,
as well as to learning during the project, in line with the project management process. One of
the important factors helped me to achieve the goals of this project is the planning factor. In
other words, in order to accomplish the goals and objectives, it allows me to make a clear route
to follow the results of the projects and comprehensive plan seems to assist me to explain what
needs to be done first to save time and effort to help accomplish the project.
The decision-making of the project management process tends to form the justification of the
project's recommendations and learning and it also helps to overcome project planning issues
because, at first, the project struggled to find the results of the questionnaire in the correct way
the decision-making process help to overcome this issue.
The changes or developments of the initial project management plan will allows the conductor
of this research to strengthen the weakness of the analysis to fulfill the project requirements
and aims to help achieve the high results or outcomes and efficiency of the project.
In addition, I found after the fulfillment of this project that because of good time management,
I am able to conduct and accomplish a consistent research project better and more efficiently.
In a certain period of time, it gave me the ability to outline a complete content for my project
and it empowers me to stop spending too much time on a chapter to concentrate on crucial
sections of the project.
[Left Space Intentionally]
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 57
4.2 Evaluate the value of the project management process and use of
quality research to meet stated objectives and support own learning and
performance.
4.2.1 Value of project management process.
The project management process is unique and close to this project. It assigns team members
to work, helps to establish good working relationships, and increases the project's success by
effectively allocating the work to team members. After that, it also helps the team members to
operate in the same way to quickly accomplish the goal. Furthermore, the project manager
sufficiently supports the project team in order to make success simpler.
The Importance of project management process.
Project planning: Without careful project planning, a project can quickly get off track
before it has even begun. Organizations so often overestimate how fast they can
produce deliverables, underestimate costs, or both which leads to failure of project so
project planning would help to overcome this issues.
Clear focus and objectives: To success a project there should be one or more clear
objectives otherwise an unclear focus can lead to slippage of scope, missed deadlines,
and over expense.
Strategic alignment: Aligning projects with business strategy is one of the most
critical factors for using project management process.
Managed process: Project management is a constructive process that aims to assist the
right people at the right time to perform the right tasks. it can help to break down a
project into more manageable pieces.
Quality control: An essential component of project management process is quality
control. All requirements for time and budget could be met by your project, but if the
quality criteria are not met, the project would be considered a failure.
(Why Is Project Management Important?, 2020)
[Left Space Intentionally]
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 58
4.2.2 Use of quality research.
A good quality research will provide evidence that is ethical, robust, stands up to scrutiny and
can be used to guide decision making and should adhere to standards of transparency,
professionalism, accountability and auditability.
Use of a high quality research will ensure,
Outcomes, interventions, and feedback that are meaningful and useful to your research.
To provide detailed description of the methods and statistics used in the research.
To use a relevant research methodology to collect data.
To ensure there are no any unnecessary costs are incurred.
To finish the research on the given time frame.
(Centre, 2020)
4.2.3 Own learning and performance by undertaking the research.
While doing this project, I have learned some qualities that are useful for project management.
This experience, as I worked to accomplish goals and objectives of this project, further
strengthened my abilities. Some of them are referred below.
Self-work and Co-operation
The talents within me were identifiable and I have improved my Co-operation skill by helping
each other’s when face difficult situation through the event this experience most helped to
success of this project.
Communication skill
Communication skill is building block to all co-operation skills. I have strengthened my
communication skills in this project and I have been able to apply them in this project to make
it succeed. I have been able to learn how to interact perfectly with others through my
experience.
Problem solving skill
I always curious about solving such problems and even though my skill on problems solving
is good by doing this project I have improved it more and there is still space to improve this
skill more.
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 59
Working with others
One of the skills I have learned is to interact with other people. Working with various
individuals is challenging, but I learned how to communicate with them by doing this project.
The experience helped most to make this project a success. I didn't have any background like
that before this assessment. But after this evaluation, I will improve my abilities to work with
others.
Written report
The report is a standard way of presenting information and a particular purpose-related
recommendation or conclusion. As well-developed report writing skills are important in many
professional contexts, reports are also used as an evaluation task so by doing this project I have
improve my report written skill.
Cost Management
Cost management permit a business to anticipate coming expenses in order to decrease the
possibility of it going over the budget. By doing this project I have learn the mistake I made on
cost management plan and it help me to improve my skill on estimating the cost. In beginning
I estimated two thousand six hundred rupees has the budget for this project but in the end of
the project the actual cost was three thousand rupees I have spent four hundred more than the
estimated budget which implies that we estimate everything in the planning, but sometimes
some estimates might vary from the plan.
Cost Details Estimated Cost Actual Cost
Travelling Charges 700.00 850.00
Call Charges 200.00 250.00
Internet Charges 750.00 750.00
Printout Charges 150.00 250.00
Stationeries Charges 800.00 900.00
Total Cost 2600.00 3000.00
Table 6 Actual cost
Source: Author’s work
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 60
References.
Content References.
Base, K. and research, A., 2020. Qualitative Research Methods & Examples. [online]
Scribbr. Available at: <https://www.scribbr.com/methodology/qualitative-research/>
[Accessed 15 December 2020].
Bashay, F., 2020. What Is The CIA. [online] Difenda.com. Available at:
<https://www.difenda.com/blog/what-is-the-cia-triangle-and-why-is-it-important-for-
cybersecurity-management> [Accessed 12 December 2020].
Bhatia, M. and Bhatia, M., 2020. Quantitative Data Analysis Methods. [online] Atlan |
Humans of Data. Available at: <https://humansofdata.atlan.com/2018/09/qualitative-
quantitative-data-analysis-methods/> [Accessed 21 December 2020].
Centre, S., 2020. What Is Good Quality Research?. [online] Saferinternet.org.uk.
Available at: <https://www.saferinternet.org.uk/research/what-good-quality-research>
[Accessed 30 December 2020].
Development, C., 2020. Risk Management Process. [online] Continuing Professional
Development. Available at: <https://continuingprofessionaldevelopment.org/risk-
management-steps-in-risk-management-process/> [Accessed 14 December 2020].
Globalknowledge.com. 2020. Project Quality Management. [online] Available at:
<https://www.globalknowledge.com/us-en/resources/resource-library/articles/what-is-
project-quality-management/> [Accessed 17 December 2020].
Hackr.io. 2020. What Is Data Analysis?. [online] Available at:
<https://hackr.io/blog/what-is-data-analysis-methods-techniques-tools> [Accessed 20
December 2020].
Lucidchart.com. 2020. Why Is Project Management Important?. [online] Available at:
<https://www.lucidchart.com/blog/why-is-project-management-important> [Accessed
30 December 2020].
PAT RESEARCH: B2B Reviews, Buying Guides & Best Practices. 2020. Qualitative
Data Analysis Tools. [online] Available at:
<https://www.predictiveanalyticstoday.com/top-qualitative-data-analysis-software/>
[Accessed 20 December 2020].
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 61
profile, V., 2020. Management Information System (MIS). [online] A-
smude.blogspot.com. Available at: <https://a-
smude.blogspot.com/2012/04/management-information-system-mis.html> [Accessed
9 December 2020].
Project-Management.com. 2020. What Is Time Management?. [online] Available at:
<https://project-management.com/what-is-time-management/> [Accessed 17
December 2020].
QuestionPro. 2020. Quantitative Research. [online] Available at:
<https://www.questionpro.com/blog/quantitative-research/> [Accessed 15 December
2020].
Ray, S. and Ray, S., 2020. The Risk Management. [online] ProjectManager.com.
Available at: <https://www.projectmanager.com/blog/risk-management-process-
steps> [Accessed 13 December 2020].
Research-Methodology. 2020. Qualitative Data Analysis. [online] Available at:
<https://research-methodology.net/research-methods/data-analysis/qualitative-data-
analysis/> [Accessed 20 December 2020].
Research-Methodology. 2020. Quantitative Data Analysis Tools. [online] Available at:
<https://research-methodology.net/research-methods/data-analysis/quantitative-data-
analysis/> [Accessed 21 December 2020].
Sciencedirect.com. 2020. Vulnerability Analysis. [online] Available at:
<https://www.sciencedirect.com/topics/economics-econometrics-and-
finance/vulnerability-analysis> [Accessed 9 December 2020].
Silentbreach.com. 2020. Importance Of Vulnerability Assessment. [online] Available
at: <https://silentbreach.com/vulnerability-assessment.php> [Accessed 9 December
2020].
Swascan.com. 2020. Vulnerability-Assessment. [online] Available at:
<https://www.swascan.com/swascan-vulnerability-assessment/> [Accessed 9
December 2020].
Venngage. 2020. Project Management Plan. [online] Available at:
<https://venngage.com/blog/project-management-plan/> [Accessed 13 December
2020].
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 62
Wrike.com. 2020. What Are Project Management Processes?. [online] Available at:
<https://www.wrike.com/project-management-guide/faq/what-are-project-
management-processes/> [Accessed 17 December 2020].
Figure References.
Invensislearning.com. 2020. Risk-Management-Process. [online] Available at:
<https://www.invensislearning.com/blog/wp-content/uploads/2020/07/5-steps-of-risk-
management-process.jpg> [Accessed 13 December 2020].
Jisc.ac.uk. 2020. Risk-Analysis. [online] Available at:
<https://www.jisc.ac.uk/sites/default/files/risk-values-equal-scale.png> [Accessed 13
December 2020].
Manageengine.com. 2020. Vulnerability-Assessment-Steps. [online] Available at:
<https://www.manageengine.com/vulnerability-management/images/vulnerability-
assessment-steps.jpg> [Accessed 9 December 2020].
Methods.sagepub.com. 2020. Advantage & Disadvantage Of Interview. [online]
Available at: <https://methods.sagepub.com/images/virtual/essentials-of-marketing-
research/9781412991308-p176-1.jpg> [Accessed 16 December 2020].
Slideplayer.com. 2020. Advantages & Disadvantages Of Questionnaires. [online]
Available at:
<https://slideplayer.com/slide/12534614/75/images/22/Advantages+and+disadvantage
s+of+self+completion+questionnaires.jpg> [Accessed 16 December 2020].
Smartsheet.com. 2020. Project Management Process. [online] Available at:
<https://www.smartsheet.com/sites/default/files/styles/900px/public/2020-10/IC-Five-
Phases-of-Project-Management.png?itok=hjc2LnZR> [Accessed 17 December 2020].
Storage.unitedwebnetwork.com. 2020. Data-Analysis-Tools. [online] Available at:
<https://storage.unitedwebnetwork.com/files/282/fd95125f9558cd6412a26510406232
1f.png> [Accessed 21 December 2020].
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 63
Gantt chart.
Figure 13 Assignment Gantt chart
Source: Author’s work
RAMAN LAKSHAN / Unit: 06 – Managing a Successful Computing Project / Assignment No: 01 64
You might also like
- SAP SD by Manoj Tony Latest PDFDocument15 pagesSAP SD by Manoj Tony Latest PDFPavan TodkarNo ratings yet
- ABC Assignment PDFDocument64 pagesABC Assignment PDFRaishaNo ratings yet
- Arthur Meidan (Auth.) - Marketing Financial Services-Macmillan Education UK (1996) PDFDocument343 pagesArthur Meidan (Auth.) - Marketing Financial Services-Macmillan Education UK (1996) PDFUmesh Karn100% (1)
- A 019730 1647416384898 137822 W.M.supun Anjana Business InteligentDocument138 pagesA 019730 1647416384898 137822 W.M.supun Anjana Business InteligentDishan SanjayaNo ratings yet
- SDLCDocument79 pagesSDLCRaman TamangNo ratings yet
- A 019730 1636101756198 114163 W.M.supun Anjana Jayasinghe Unit 11 - Maths For Computing - Reworded - 2021Document63 pagesA 019730 1636101756198 114163 W.M.supun Anjana Jayasinghe Unit 11 - Maths For Computing - Reworded - 2021Dishan SanjayaNo ratings yet
- MSCP AssignmentDocument55 pagesMSCP AssignmentSadeep SanchanaNo ratings yet
- 10 Unit 13 CRP Proposal 2020 2021 IOTDocument27 pages10 Unit 13 CRP Proposal 2020 2021 IOTROSHEN ANTHONYNo ratings yet
- Knowledge Management PDFDocument252 pagesKnowledge Management PDFKasiraman RamanujamNo ratings yet
- A-065211-1606734174791-53830-Unit 10 Web Design and Development - KavinDocument115 pagesA-065211-1606734174791-53830-Unit 10 Web Design and Development - KavinRehan RatnaweeraNo ratings yet
- Adv ProgrammingDocument93 pagesAdv Programmingshahzad sultanNo ratings yet
- MSCP NewDocument37 pagesMSCP NewHasantha IndrajithNo ratings yet
- 1447-1628760497056-Unit 6 MSCP - 2021 and 22 RW AnjaliDocument106 pages1447-1628760497056-Unit 6 MSCP - 2021 and 22 RW AnjaliThanaraj KaveenNo ratings yet
- Software Development Life Cycle ASM1Document39 pagesSoftware Development Life Cycle ASM1alexNo ratings yet
- A-019730-1635326717126-114203-W.M.supun Anjana Jayasinghe-Unit 6 Managing A Successful Research Project Reviewed - Reworded - 2021Document67 pagesA-019730-1635326717126-114203-W.M.supun Anjana Jayasinghe-Unit 6 Managing A Successful Research Project Reviewed - Reworded - 2021Dishan SanjayaNo ratings yet
- COLA-070071 - Unit 10 Web Design and DevelopmentDocument104 pagesCOLA-070071 - Unit 10 Web Design and DevelopmentChanaka SandaruwanNo ratings yet
- APTA Procurement HandbookDocument29 pagesAPTA Procurement Handbookahong100No ratings yet
- Unit 6 Managing A Successful Research Project)Document15 pagesUnit 6 Managing A Successful Research Project)CULPRIT BOY0% (1)
- Unit 14 - Business IntelligenceDocument14 pagesUnit 14 - Business IntelligenceIshara EroshiNo ratings yet
- Cogoport Private Limited Offer Letter - Rishu KumarDocument4 pagesCogoport Private Limited Offer Letter - Rishu KumarRishu GuptaNo ratings yet
- Programming AssignmentDocument110 pagesProgramming AssignmentShrawan ShrawNo ratings yet
- A-011814-1612368830998-72379-Lahiru Viraj - ME24716 - 799-1601899513739-Unit 18 - Discrete MathematicsDocument89 pagesA-011814-1612368830998-72379-Lahiru Viraj - ME24716 - 799-1601899513739-Unit 18 - Discrete MathematicsLahiru VirajNo ratings yet
- A-014114-1608747919893-65801-Crp - Neg - A - 014114Document84 pagesA-014114-1608747919893-65801-Crp - Neg - A - 014114AngeloNo ratings yet
- A-008550-1624862702015-80342-BIIII-converted (44445)Document69 pagesA-008550-1624862702015-80342-BIIII-converted (44445)Hansi RanasingheNo ratings yet
- 3467 HND 10 Hajanya Kalaruban Database Devolopment Management SystemDocument90 pages3467 HND 10 Hajanya Kalaruban Database Devolopment Management Systemronica100% (1)
- Financial Ratio AnalysisDocument4 pagesFinancial Ratio AnalysisJennineNo ratings yet
- Internal Verification of Assessment Decisions - BTEC (RQF) : Higher NationalsDocument27 pagesInternal Verification of Assessment Decisions - BTEC (RQF) : Higher NationalsSusira MednisNo ratings yet
- Netting Topical EssayDocument60 pagesNetting Topical EssayAli100% (2)
- Assignment 2 Môn SDLCDocument28 pagesAssignment 2 Môn SDLCHuynh Nhat Nam (FGW HCM)No ratings yet
- Computing - Research - Project MadanDocument30 pagesComputing - Research - Project MadanMadan KhattriNo ratings yet
- A-019730-1659516307423-163428-W.M.supun Anjana Jayasinghe Advanced Programming - Reworded - 2021Document115 pagesA-019730-1659516307423-163428-W.M.supun Anjana Jayasinghe Advanced Programming - Reworded - 2021Dishan SanjayaNo ratings yet
- KANA-013536 P.V.Godrick Naveen (MSCP Assignment)Document56 pagesKANA-013536 P.V.Godrick Naveen (MSCP Assignment)Rajesh PrabhakarNo ratings yet
- SIP Report Reference 2 PDFDocument69 pagesSIP Report Reference 2 PDFJayshree NaiduNo ratings yet
- MSCP Pasi NewDocument38 pagesMSCP Pasi NewHimsara vihanNo ratings yet
- 1448-1628760651890-Unit 13 - CRP - Report - 2021 - 2022 RWDocument35 pages1448-1628760651890-Unit 13 - CRP - Report - 2021 - 2022 RWThushan LakshithaNo ratings yet
- 2582-1664429268190-Unit 6 MSCP - 2021 and 22 Digital TransformationDocument16 pages2582-1664429268190-Unit 6 MSCP - 2021 and 22 Digital Transformationishan bomaluwage0% (1)
- Unit 6 Managing A Successful Research ProjectDocument14 pagesUnit 6 Managing A Successful Research Projectmhmd100% (1)
- Jalina MSCP AssignmentDocument49 pagesJalina MSCP Assignmentchamidu hansajithNo ratings yet
- Internal Verification of Assessment Decisions - Btec (RQF) : Jghigher NationalsDocument32 pagesInternal Verification of Assessment Decisions - Btec (RQF) : Jghigher NationalsSusira MednisNo ratings yet
- 4272-1687314071266-Unit 6 - Chapter 01Document37 pages4272-1687314071266-Unit 6 - Chapter 01Dulanja OmeshNo ratings yet
- Internal Verification of Assessment Decisions - BTEC (RQF) : Higher NationalsDocument57 pagesInternal Verification of Assessment Decisions - BTEC (RQF) : Higher NationalsAngeloNo ratings yet
- SecurityDocument41 pagesSecurityMaster GamerNo ratings yet
- Computing Research Project QuestionDocument7 pagesComputing Research Project QuestionkarkiakNo ratings yet
- Unit 03 Professional PracticeDocument82 pagesUnit 03 Professional Practicemohammed shalmanNo ratings yet
- Internal Verification of Assessment Decisions - BTEC (RQF) : Higher NationalsDocument39 pagesInternal Verification of Assessment Decisions - BTEC (RQF) : Higher NationalsHansi RanasingheNo ratings yet
- CRP 13Document98 pagesCRP 13Abinaya AbishanNo ratings yet
- PM Assingment - FinalDocument44 pagesPM Assingment - FinalIsuru Avantha WickramasingheNo ratings yet
- E133118-1663061373597-191178-Work Related Learning ReportDocument55 pagesE133118-1663061373597-191178-Work Related Learning Reportimad zayan (bumblebee ..)No ratings yet
- E122930-1661079507113-195599-54-1547092378635-Unit 34 SAD - Assignment 2018.11.13Document133 pagesE122930-1661079507113-195599-54-1547092378635-Unit 34 SAD - Assignment 2018.11.13tharindu roshanaNo ratings yet
- Unit 10 Web Design and Development Reworded 2021 Bhanuka PereraDocument105 pagesUnit 10 Web Design and Development Reworded 2021 Bhanuka PereraThejanu BandaraNo ratings yet
- Unit 34 - System AnalysisDocument72 pagesUnit 34 - System Analysistharindu roshanaNo ratings yet
- E168429-1664557821200-193283-Thirukkumaran 00139198 Unit 02 Networking-Reworded 2Document78 pagesE168429-1664557821200-193283-Thirukkumaran 00139198 Unit 02 Networking-Reworded 2Gopahan HamsavarthanNo ratings yet
- Internal Verification of Assessment Decisions - BTEC (RQF) : Higher NationalsDocument60 pagesInternal Verification of Assessment Decisions - BTEC (RQF) : Higher NationalsAngeloNo ratings yet
- Dad Assignment - EsoftDocument11 pagesDad Assignment - Esoftsheran2333% (3)
- Unit - 05 - Security AssignmentDocument96 pagesUnit - 05 - Security AssignmentsachinNo ratings yet
- Higher Nationals in Computing: Unit 2: Web Design and Development Assignment 2Document59 pagesHigher Nationals in Computing: Unit 2: Web Design and Development Assignment 2Tấn Nghĩa LêNo ratings yet
- Assignment Brief BTEC Level 4-5 HNC/HND Diploma (QCF) : To Be Filled by The StudentDocument42 pagesAssignment Brief BTEC Level 4-5 HNC/HND Diploma (QCF) : To Be Filled by The StudentronicaNo ratings yet
- BSE - MohammedDocument56 pagesBSE - MohammedronicaNo ratings yet
- Managing Successful Computing Project AssignmentDocument49 pagesManaging Successful Computing Project AssignmentRajesh PrabhakarNo ratings yet
- AssDocument15 pagesAssOntime Bestwriters50% (2)
- Discrete Mathematics HasithaDocument57 pagesDiscrete Mathematics HasithaHasitha JayasekaraNo ratings yet
- Col e 004653 MSCP Com079Document41 pagesCol e 004653 MSCP Com079AliNo ratings yet
- 788-1601897459456-Unit 05 - Security - 2020Document14 pages788-1601897459456-Unit 05 - Security - 2020Career and EducationNo ratings yet
- Business Intelligance Pradeep SirDocument5 pagesBusiness Intelligance Pradeep SirRohim Acharya100% (1)
- 789-1601897728690-Unit 6 Managing A Successful Computing Research Project - 2020Document14 pages789-1601897728690-Unit 6 Managing A Successful Computing Research Project - 2020Kevin JeromNo ratings yet
- 1447-1628760497056-Unit 6 MSCP - 2021 and 22 RWDocument16 pages1447-1628760497056-Unit 6 MSCP - 2021 and 22 RWMadara PereraNo ratings yet
- Sample MSCPDocument55 pagesSample MSCPHasantha IndrajithNo ratings yet
- MSCP Ready21Document47 pagesMSCP Ready21Yohan Tharish WarnakulasooriyaNo ratings yet
- Bca Iii Year Syllabus - SaadDocument2 pagesBca Iii Year Syllabus - SaadShubhamNo ratings yet
- Effect of Branding and MarketingDocument5 pagesEffect of Branding and Marketing20E3532 SIVABALAN CNo ratings yet
- SmartPlant Spoolgen Plus White Paper March 2012 PDFDocument40 pagesSmartPlant Spoolgen Plus White Paper March 2012 PDFrkarthikmtmrNo ratings yet
- Tanjung Manis HowDocument7 pagesTanjung Manis Howramen28No ratings yet
- Trade and Payment Documents - NepalDocument38 pagesTrade and Payment Documents - NepalNarayanPrajapati100% (1)
- Working Capital ManagmentDocument4 pagesWorking Capital ManagmentKundan kumarNo ratings yet
- Yes IT LabsDocument6 pagesYes IT LabsYash VarshneyNo ratings yet
- CORPORATIONDocument54 pagesCORPORATIONThu ThảoNo ratings yet
- Advanced Analysis and Appraisal of PerformanceDocument12 pagesAdvanced Analysis and Appraisal of PerformanceGreghvon MatolNo ratings yet
- Presentation On FSMDocument23 pagesPresentation On FSMMakiNo ratings yet
- Aeb SM CH11 1Document15 pagesAeb SM CH11 1Crytal AbubakarNo ratings yet
- Maintainance Contract FormatDocument3 pagesMaintainance Contract Formatnauaf101No ratings yet
- Technopreneurship - EthicsDocument10 pagesTechnopreneurship - EthicsCamilogs100% (1)
- Infosys Working CapitalDocument30 pagesInfosys Working CapitalSonali JoshiNo ratings yet
- ÷ M÷M÷÷M ÷ M MMM ÷÷MMMMMMMMMMMMMMMMMMMMMMM MM M÷ MDocument5 pages÷ M÷M÷÷M ÷ M MMM ÷÷MMMMMMMMMMMMMMMMMMMMMMM MM M÷ MAhmed JavedNo ratings yet
- Lease and Project Finance Exam 2022 S2Document4 pagesLease and Project Finance Exam 2022 S2bonaventure chipetaNo ratings yet
- BI Insurance CompaniesDocument19 pagesBI Insurance CompaniesArmel SergesNo ratings yet
- University of ZimbabweDocument14 pagesUniversity of ZimbabweZvikomborero Lisah KamupiraNo ratings yet
- Nestle Corporate StrategyDocument6 pagesNestle Corporate Strategyayema kashifNo ratings yet
- MultimediaDocument55 pagesMultimediaRAVI TalawarNo ratings yet
- Manajemen RisikoDocument67 pagesManajemen RisikoBustanus SalatinNo ratings yet
- Chapter 13 SOCFDocument18 pagesChapter 13 SOCFHà NguyễnNo ratings yet