Professional Documents
Culture Documents
NUSING INFORMATICS NETIQUETTE GUIDELINES
Uploaded by
werismy daddy0 ratings0% found this document useful (0 votes)
6 views5 pages1) The document discusses guidelines for proper netiquette or etiquette for online communication and social media use.
2) It provides tips for polite, considerate, and professional online behavior such as being concise, using proper grammar and capitalization, and maintaining a respectful tone.
3) The document emphasizes thinking before posting, avoiding all-caps text, and considering how messages might be perceived if seen out of context or shared publicly.
Original Description:
Original Title
INFORMATICS_04
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this Document1) The document discusses guidelines for proper netiquette or etiquette for online communication and social media use.
2) It provides tips for polite, considerate, and professional online behavior such as being concise, using proper grammar and capitalization, and maintaining a respectful tone.
3) The document emphasizes thinking before posting, avoiding all-caps text, and considering how messages might be perceived if seen out of context or shared publicly.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
6 views5 pagesNUSING INFORMATICS NETIQUETTE GUIDELINES
Uploaded by
werismy daddy1) The document discusses guidelines for proper netiquette or etiquette for online communication and social media use.
2) It provides tips for polite, considerate, and professional online behavior such as being concise, using proper grammar and capitalization, and maintaining a respectful tone.
3) The document emphasizes thinking before posting, avoiding all-caps text, and considering how messages might be perceived if seen out of context or shared publicly.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 5
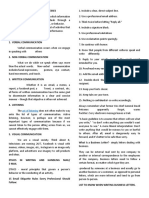
NUSING INFORMATICS 04
Professor: Sir Joshua Coronel
Source: PDF
The best way to make decisions
OUTLINE especially to us nurses, is
objective.
I. Netiquette
3. Think before you reply!!! Do not write
anything online if you would not say the
NETIQUETTE same think to the recipient face-to-face.
Be professional about what you write to
others (E-mail can be forwarded, and
CODE of INTERNET because the many people have ended up having the
internet is a NETWORK and message forwarded to the person being
ETIQUETTE is a CODE gossiped about).
Comparable to appropriate manners in a 4. As a general rule, focus on one subject or
professional or academic setting topic per e-mail message. Keep your
Only used for formal means and online message brief and specific (a maximum
communication guideline is one or two e-mail screens
worth.
Use of NETIQUETTE: For applications in the general
Proper netiquette discourages people future, this rule is mostly applied.
from flooding another person’s e-mail Do not make an application that is
inbox with spam mail or forwarded three (3) or more pages long; an
messages or misusing social network application letter mostly consists
sites by posting personal information of the following: introduce
unrelated to the online course. yourself, educational attainments,
In addition, especially in an online class, and qualifications.
netiquette includes using standard fonts Whenmessaging, one should keep
and font sizes that are a readable size only one topic per chat bubble for
formal chats
Netiquette Guidelines 5. Make the visual layout of your message
pleasing for the recipient. It should be
1. Always be polite and considerate of
easy to read, watch your spacing, lower
others. Never send or keep anything that
and upper-case usage, indentation,
you would mind seeing broadcasted on
spelling, and etc.
the Evening News.
The most important thing to look
Think before you communicate
out for in your messages are the
in social media.
lower and upper cases, since it is
2. Do not send mail or reply to mail when
a general idea that only using
you are “flaming”, in order words angry,
upper case in a conversation
tired, upset, or irritable. Cool off first.
usually means that one has strong
Wait until you calm down or can speak to
emotional antonations in their
the person directly.
message, i.e. one may be angry.
Control your emotions.
Indentations are also important,
because the format nowadays for
writing letters have no more
special indentation at the
beginning, and the sentences start
at the left most side of the page.
Correct spelling is also a must,
especiallywhen it comes to a
formal message as it could cause
confusion within the message.
Observing appropriate spacing
from each word in a message is a
given, if spacing becomes an
issue, one must inform the
receiver of such issue. This is Character Definition
important as to not cause
confusion such as:
“thisisanexampleofinappropriates
pacing”.
6. Do not capitalize an entire message like
this: “IT MEANS YOU ARE
SHOUTING IN E-MAIL LAND!!!”.
Use a combination of upper and lower-
case characters, just as you would if you
were writing a pen and paper letter or
memo.
7. Always begin an e-mail message with a
descriptive Subject Heading in five Don’t forget
words or less. An appropriate subject line Before you post “THINK”
allows recipients to organize their e-mail
messages using keywords or subject T- is it True?
headings. H – is it Helpful?
Follow instructions on how to
construct your subject line if the I – is it Inspiring?
recipient has given a specific
N – is it Necessary?
format as this makes it easier for the
recipient to receive and read your K – is it Kind?
e-mails. Generally, a subject with
all uppercase is likely for urgent Core rule of NETIQUETTE
matters, as such it is used in that Remember the human:
way, although one should not
always use uppercase always as it is in cyber, there are real people out there.
strictly for urgent uses.
Adhere to the same standards of behavior online
8. Express emotions gracefully. Use
that you follow in real life:
“Smileys” to add an indication of your
emotional intent. Don’t ever use this in be ethical. Breaking the law is bad
formal setting/Document netiquette.
You are breaking the law when you
plagiarize.
Know where you are in cyberspace: Our digital footprints are monetized by
organizations with which we have no
Netiquette varies from domain to domain
relationship and which we can’t control.
Observe then participate.
Few internet users realize how intimate
Respect other people’s time and bandwidth: their digital footprints are or how
commonly the resulting data is shared by
It’s your responsibility to ensure that the third parties
time they spend reading your post isn’t One online security company has
wasted. identified more than 200 Third-party
You are not the center of cyberspace. Advertisers and 630 Tracking
Don’t waste other people’s time. Think Technologies collecting individual data
twice before you hit the send or publish on the web. e.g., facebook, twitter,
key. google.
Make yourself look good online: They are tracking your visits to any web
page with a like, tweet or plus one button
Know what you’re talking about and whether or not you click on that button.
make sense. Every site you visit gives them more
Do not swear! information to store and commercialize.
there’s an implicit bargain there but
Share expert knowledge: who’s getting the best of it?
Sharing your knowledge is fun! Other reasons why digital footprint matters
Help keep flame wars under control: 1. Protecting your Reputation
Strong and heated arguments must be it’s appropriate to every audience
operated. all time. Digital footprints can be
taken out of context and
Respect other people’s privacy: misinterpreted.
reputation is a social interpersonal
Self-explanatory.
judgement tempered by forgiveness
Don’t abuse your power and forgetfulness. You can’t rely on
the internet.
Be forgiving of other people’s mistakes 2. Maintaining your ability to decide where
Think twice before reacting. and how your personal information is
shared
Digital Footprints everyone has information that
they only want to share in
“Out of sight, Out of mind”. It’s hard to
specific contexts
manage something you’ve never seen.
It’s not uncommon for people to say “I you may share medical
have nothing to hide, so why should I information with family but not
care about my digital footprints”. necessarily your boss in some
countries it may be important
The simplest reason: The digital
that your religious beliefs are
footprints reveal a lot about you. They
known only to a few
build up into a detailed picture of your
likes and habits and that information has there are probably substances
commercial value. which you’re comfortable
sharing personal information
with organizations through the credit limit had been lowered
internet but wouldn’t want that from about eleven thousand to
same data spread around four thousand the credit card
Today’s tracking mechanisms, company explained that other
most internet users don’t have customers who use their card at
the control to prevent that kind of establishments where you
spread. There is no easy way on recently shopped have a poor
the internet to say no to most repayment history based on
forms of tracking and certainly similar kinds of data and
no way to say you can share this inference financial services
but not that company could steer you to
Commercial Tracking aside, credit card offers with higher
there’s also a law enforcement interest rates and lower credit
aspect Microsoft, google, twitter, limits an insurer could deny you
Facebook and yahoo have all coverage or charge you more for
released user data governments it based on your digital footprint.
on demand and there is growing 4. Preserving your freedom
concern about the number of maintaining your freedom your
apps that leak user’s personal digital footprints can also affect
data your freedom to express yourself
Online services can greatly and in some places even your
reduce subscriber’s ability to liberty and well-being.
control their own information. many governments routinely
3. Preventing Financial loss track social media sites instant
Identity theft is a global issue as messaging services and chat
digital foot prints are aggregated rooms and some may arrest
into larger databases. Digital people for political statements
thieves can obtain data about made in these venues.
tremendous numbers of people Surveillance software may be
facilitating identity related crime used to intercept
User authentication systems add communications to and from
detail to these databases for human rights activists and this
example: has resulted in cases of arrest and
“What was your first pet’s torture. Recently, some mobile
name?” which we might already phone users in kiev received a
have disclosed in some other text message saying dear
context without thinking about it subscriber you have been
registered as a participant in a
When such an aggregation of mass riot based on the location of
data is hacked it’s all the easier their handsets not necessarily on
for criminals to impersonate whether they were there or what
others for financial gain or other they were doing law
purposes, even other people’s enforcement action based on this
digital footprint can affect your kind of inference comes with a
credit worthiness. high risk of air and injustice
Example: one returning There are softer forms of
honeymooner found that his freedom too. You may find your
freedom to access information, http://www.internetsociety.org/footprint.
limited based on assumptions
Click on : “how can I manage my digital
about where you are
footprint?”.
Using data from your digital
footprints that may or may not be Explore the other links on that page for
reliable. Imagine for a moment background information and practical tips.
that based on your online
activities your reputation was Digital footprint can be controlled on
tarnished your intimate details IOS
were broadcast to the world you
were defrauded or even that you Professor: Sir Joshua Coronel
were arrested and jailed any one Source: PPT
of those outcomes could be
devastating but the more of our
lives we conduct online the more
exposed we are to these kinds of
risk how do people feel about
that
Research in India found that 40
% said they shop online using
unsecured wi-fi networks and
about 20% share passwords with
others
On the other hand, in a
Malaysian survey 86% said they
are concerned that mobile apps
might be collecting personal
information without their
permission and more than half
(>50%) of those with concerns
state that they limit their use of
apps.
Among readers of the wall street
journal 60% expressed concern
about the loss of online privacy
and the figure is almost 70%
percent for US consumers as a
whole.
People's perception of the risks clearly varies
greatly but we think it's vital to understand how
your digital footprints relate to your privacy and
safety and what you can do about it. For tutorials
and suggestions about how to manage your digital
footprint visit
You might also like
- emails@work: How to write effective business emailsFrom Everandemails@work: How to write effective business emailsRating: 1 out of 5 stars1/5 (1)
- Computer 10 Quarter 1 Lesson 2Document17 pagesComputer 10 Quarter 1 Lesson 2Ella MendozaNo ratings yet
- E-mail In An Instant: 60 Ways to Communicate With Style and ImpactFrom EverandE-mail In An Instant: 60 Ways to Communicate With Style and ImpactRating: 5 out of 5 stars5/5 (3)
- Week 5 - Lesson 4 - NetiquetteDocument4 pagesWeek 5 - Lesson 4 - Netiquettealleah joy sabuyanNo ratings yet
- Module 4 NSTPDocument4 pagesModule 4 NSTPCarlo & LynNo ratings yet
- Ch.3 - Electronic Messages and Digital MediaDocument22 pagesCh.3 - Electronic Messages and Digital MediasitizulaikahjamilNo ratings yet
- Email Etiquette: Quick Reference GuideDocument3 pagesEmail Etiquette: Quick Reference GuideSefa TseghaNo ratings yet
- Email EtiquetteDocument3 pagesEmail EtiquetteArshad Ansari100% (1)
- 99 Email Security and Productivity TipsDocument7 pages99 Email Security and Productivity TipsUgur Onder BozkurtNo ratings yet
- NETIQUETTESDocument27 pagesNETIQUETTESEdrizNo ratings yet
- EFEKTA-GE-B2.3 U2 Manners and EtiquetteDocument12 pagesEFEKTA-GE-B2.3 U2 Manners and EtiquetteTamara DavidsonNo ratings yet
- MIDTERM - Nursing InformaticsDocument13 pagesMIDTERM - Nursing InformaticsReya Mae OrcajadaNo ratings yet
- Netiquette DefinitionDocument1 pageNetiquette DefinitionArlett PachecoNo ratings yet
- Professional CommunicationDocument6 pagesProfessional CommunicationMhayalene DiamanteNo ratings yet
- 6 Cs OF WRITING A PROFESSIONAL EMAILDocument2 pages6 Cs OF WRITING A PROFESSIONAL EMAILNguyễn Đức AnhNo ratings yet
- Why Have Email RulesDocument7 pagesWhy Have Email RulesChiranjivi NainiNo ratings yet
- Netiquette 2 PDFDocument11 pagesNetiquette 2 PDFErickson BarrientosNo ratings yet
- Email EtiquetteDocument19 pagesEmail Etiquettegrovermehak116No ratings yet
- Abid CSDocument11 pagesAbid CSEA AbidNo ratings yet
- 취업영어 5WDocument19 pages취업영어 5W김도비No ratings yet
- 华时代读写第二册Unit 3 CourtesyDocument176 pages华时代读写第二册Unit 3 CourtesyGabriellezhuNo ratings yet
- Quick Guide To Professional Communication in Customer SupportDocument11 pagesQuick Guide To Professional Communication in Customer SupportSergio MonsalveNo ratings yet
- How to Write Effective EmailsDocument3 pagesHow to Write Effective EmailsSana MazharNo ratings yet
- English Unlimited B2 Worksheet - 01ADocument2 pagesEnglish Unlimited B2 Worksheet - 01AOh ErnaNo ratings yet
- Tool Kit E-MailsDocument14 pagesTool Kit E-MailsKanchana RandallNo ratings yet
- Soft Skills: Communicating With E-Mail and MemosDocument34 pagesSoft Skills: Communicating With E-Mail and MemosriyaNo ratings yet
- E-Mail Writing Ettiquettes 146Document22 pagesE-Mail Writing Ettiquettes 146Manu Deep YaduvanshiNo ratings yet
- 4 Tone, Readabilityand NetiquetteDocument11 pages4 Tone, Readabilityand Netiquetteimnik89No ratings yet
- Module 3_ Digital Literacy & Social MediaDocument47 pagesModule 3_ Digital Literacy & Social MediaAnuNo ratings yet
- Writing A Formal EmailDocument7 pagesWriting A Formal EmailMilette CaliwanNo ratings yet
- Writing Email & EtiquettesDocument63 pagesWriting Email & EtiquettesHMNoorHaqOpu100% (1)
- Adobe Scan 09-Aug-2023Document14 pagesAdobe Scan 09-Aug-2023james17stevensNo ratings yet
- Definitions of Netiquettes: 1) Longman Dictionary of Contemporary EnglishDocument11 pagesDefinitions of Netiquettes: 1) Longman Dictionary of Contemporary EnglishAbdul Samad NasirNo ratings yet
- Learning Module 1 Course Packet 1-5Document125 pagesLearning Module 1 Course Packet 1-5august basaNo ratings yet
- All You Want To Know About E-Mails (I)Document19 pagesAll You Want To Know About E-Mails (I)Hrithik SharmaNo ratings yet
- 2nd Prelim Module 1Document36 pages2nd Prelim Module 1madel guarinNo ratings yet
- Learning Guide Module: English 4 - Page 1 of 10Document10 pagesLearning Guide Module: English 4 - Page 1 of 10jvvuvuuv lopezNo ratings yet
- NCM210 MidtermDocument15 pagesNCM210 MidtermJasmine Angeli ObilloNo ratings yet
- 12 Do's and Don'ts For Effective E-Mail Communication: Overarching ConsiderationDocument2 pages12 Do's and Don'ts For Effective E-Mail Communication: Overarching ConsiderationAnna MalaiNo ratings yet
- Email Etiquette 101: Before You Click "Send" Email ChecklistDocument12 pagesEmail Etiquette 101: Before You Click "Send" Email Checklistneah55No ratings yet
- E-Mail Writing Ettiquettes 146Document22 pagesE-Mail Writing Ettiquettes 146AnanthaNo ratings yet
- Communication Skills and ProcessesDocument3 pagesCommunication Skills and ProcessesRICHELLE CASTAÑEDANo ratings yet
- Lesson 4 - NetiquetteDocument26 pagesLesson 4 - NetiquetteAll Of MeNo ratings yet
- Six Rules For Effective Emails - SkillsYouNeedDocument4 pagesSix Rules For Effective Emails - SkillsYouNeedSalman AzeemNo ratings yet
- 10 Tips For Effective Email WritingDocument1 page10 Tips For Effective Email Writingafreddy9639No ratings yet
- 10 Best Practices Online CommunicationDocument2 pages10 Best Practices Online CommunicationyourhunkieNo ratings yet
- MODULE 2-2.2 Technology Enabled CommunicationDocument25 pagesMODULE 2-2.2 Technology Enabled CommunicationmanthanjaniNo ratings yet
- Nine Tips for Effective Written CommunicationDocument2 pagesNine Tips for Effective Written CommunicationAyush GuptaNo ratings yet
- COMM 205 Final Exam ReviewDocument13 pagesCOMM 205 Final Exam ReviewMoises Hernandez100% (1)
- Essential Rules of NetiquetteDocument2 pagesEssential Rules of NetiquetteChaitali ChoudhuryNo ratings yet
- Writing Effective Emails: GE 5: Purposive Communication Sem 1, 2021-2022Document15 pagesWriting Effective Emails: GE 5: Purposive Communication Sem 1, 2021-2022Glyn Magbanua100% (2)
- Module 2Document6 pagesModule 2Niña Erica PaladoNo ratings yet
- 7 Essential Rules of Netiquette: Online CommunicationDocument2 pages7 Essential Rules of Netiquette: Online Communicationvikas_2No ratings yet
- Communication Through Letters: The Five Cs of Effective Written CommunicationDocument25 pagesCommunication Through Letters: The Five Cs of Effective Written CommunicationRashid KaryadNo ratings yet
- Business Report Writing - CHAPTER 6Document5 pagesBusiness Report Writing - CHAPTER 6juliana c.No ratings yet
- Writing Effective E-mailsDocument51 pagesWriting Effective E-mailsAnna DerNo ratings yet
- Top 10 Email Etiquette Tips for Effective CommunicationDocument8 pagesTop 10 Email Etiquette Tips for Effective CommunicationsheenlaNo ratings yet
- TopicDocument18 pagesTopicDestrofan GamingNo ratings yet
- Ngec 0423 Online Course Module 2nd Sem Ay 2020 2021Document64 pagesNgec 0423 Online Course Module 2nd Sem Ay 2020 2021Aina HaravataNo ratings yet
- Business English - Writing Workplace1Document45 pagesBusiness English - Writing Workplace1Raghad MJKNo ratings yet
- DR Rot ReviewerDocument41 pagesDR Rot Reviewerwerismy daddyNo ratings yet
- Aa 06Document10 pagesAa 06werismy daddyNo ratings yet
- NCP Knowledge DeficitDocument2 pagesNCP Knowledge Deficitangeleigh viernesNo ratings yet
- Baby Olivia IsDocument1 pageBaby Olivia Iswerismy daddyNo ratings yet
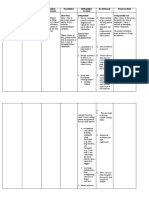
- Nursing Care PlansDocument4 pagesNursing Care Planswerismy daddyNo ratings yet
- National Service Training Program: Drug AND Substance Abuse Prevention and ControlDocument3 pagesNational Service Training Program: Drug AND Substance Abuse Prevention and Controlwerismy daddyNo ratings yet
- Information Needed (Modified) Title: Date: Art Movement/Style: Medium: PriceDocument2 pagesInformation Needed (Modified) Title: Date: Art Movement/Style: Medium: Pricewerismy daddyNo ratings yet
- Integrated Management of Childhood Illness PDFDocument79 pagesIntegrated Management of Childhood Illness PDFheyyymeeeNo ratings yet
- 1 - Intellectual Revolution ActivityDocument11 pages1 - Intellectual Revolution Activitywerismy daddyNo ratings yet
- Data Privacy Act 2012Document26 pagesData Privacy Act 2012Budoy WashupapiNo ratings yet
- Nursing Care Plan AutismDocument3 pagesNursing Care Plan Autismangeliejoy_110976% (29)
- A1 - Project Overview & Basic Rules-V2Document24 pagesA1 - Project Overview & Basic Rules-V2werismy daddyNo ratings yet
- Molar Pregnancy-Case ReportDocument2 pagesMolar Pregnancy-Case Reportwerismy daddyNo ratings yet
- RD ChecklistDocument14 pagesRD Checklistwerismy daddyNo ratings yet
- Brown Retro Aesthetic Minimalists Inspiration Vintage Moodboard Photo CollageDocument1 pageBrown Retro Aesthetic Minimalists Inspiration Vintage Moodboard Photo Collagewerismy daddyNo ratings yet
- Virtual Tour of Selected Maternity HospitalsDocument1 pageVirtual Tour of Selected Maternity Hospitalswerismy daddyNo ratings yet
- Urgent Cesarean Delivery for 38-Week Pregnant Woman with Cord ProlapseDocument2 pagesUrgent Cesarean Delivery for 38-Week Pregnant Woman with Cord Prolapsewerismy daddyNo ratings yet
- Integrated Management of Childhood Illness 1Document37 pagesIntegrated Management of Childhood Illness 1werismy daddyNo ratings yet
- National Service Training Program: Core ValuesDocument3 pagesNational Service Training Program: Core Valueswerismy daddyNo ratings yet
- High Risk Newborn: Problems Related To Maturity Preterm NewbornDocument36 pagesHigh Risk Newborn: Problems Related To Maturity Preterm Newbornwerismy daddyNo ratings yet
- High Risk Newborn CareDocument5 pagesHigh Risk Newborn Carewerismy daddyNo ratings yet
- Environmental Situation and ProtectionDocument1 pageEnvironmental Situation and Protectionwerismy daddyNo ratings yet
- HR NB InfantDocument18 pagesHR NB Infantwerismy daddyNo ratings yet
- Nusing Informatics: Course OutlineDocument10 pagesNusing Informatics: Course Outlinewerismy daddyNo ratings yet
- High Risk NotesDocument36 pagesHigh Risk Noteswerismy daddyNo ratings yet
- Pediatric Assessment: Monday, 24 January 2022 4:45 PMDocument11 pagesPediatric Assessment: Monday, 24 January 2022 4:45 PMwerismy daddyNo ratings yet
- Application of Heat and Cold Therapies ChecklistDocument19 pagesApplication of Heat and Cold Therapies ChecklistRoger ViloNo ratings yet
- Case 2Document4 pagesCase 2werismy daddyNo ratings yet
- Branding More NotesDocument194 pagesBranding More NotesandiswaNo ratings yet
- Major 7 (Calculus With Analytic Geometry)Document17 pagesMajor 7 (Calculus With Analytic Geometry)Leroy A. FloresNo ratings yet
- Activity 5, Educ 322Document4 pagesActivity 5, Educ 322Mae Jireka Sapico PautNo ratings yet
- English - Communication in Professional LifeDocument39 pagesEnglish - Communication in Professional Lifesuhaneekaushal8No ratings yet
- NETIQUETTE / Internet Etiquette or Network Etiquette / Are Guidelines For Courteous Communication in The Online EnvironmentDocument2 pagesNETIQUETTE / Internet Etiquette or Network Etiquette / Are Guidelines For Courteous Communication in The Online Environmentmarjorie tagaoNo ratings yet
- Educ 11Document4 pagesEduc 11Abren Manalo100% (2)
- Texas Christian University Students Will Create Own Drag Personas, Perform in 'Queer Art of Drag' CourseDocument28 pagesTexas Christian University Students Will Create Own Drag Personas, Perform in 'Queer Art of Drag' CourseCampus ReformNo ratings yet
- Netiquette: Networking EtiquetteDocument27 pagesNetiquette: Networking EtiquetteTrainer IntstuNo ratings yet
- Lesson 4 Cyber EthicsDocument44 pagesLesson 4 Cyber EthicsGina May DaulNo ratings yet
- Photo 50B Spring 2020 Syllabus CompleteDocument14 pagesPhoto 50B Spring 2020 Syllabus CompleteClyde LanierNo ratings yet
- Unit 10: Communication A. PhoneticsDocument14 pagesUnit 10: Communication A. PhoneticsDiệu Nguyễn100% (1)
- President Ramon Magsaysay State University: Telefax: 047-8111683/email Address: Prmsu - Edu.phDocument22 pagesPresident Ramon Magsaysay State University: Telefax: 047-8111683/email Address: Prmsu - Edu.phShienallaine QuilabNo ratings yet
- Grade 12 ONLINE SAFETY AND RULES OF NETIQUETTEDocument13 pagesGrade 12 ONLINE SAFETY AND RULES OF NETIQUETTELeslie PerezNo ratings yet
- Dance 3 SyllabusDocument12 pagesDance 3 SyllabusSally MistyNo ratings yet
- MIL - Module 5 - Lesson 1 and 2-FINALDocument19 pagesMIL - Module 5 - Lesson 1 and 2-FINALRANIE MAY V. PIÑERONo ratings yet
- NetiquetteDocument3 pagesNetiquetteOnin C. OpeñaNo ratings yet
- Netiquette DefinitionDocument1 pageNetiquette DefinitionArlett PachecoNo ratings yet
- Syllabus MPH 6005 Environmental HealthDocument22 pagesSyllabus MPH 6005 Environmental Healthkon blazeNo ratings yet
- 10 Rules of NetiquetteDocument4 pages10 Rules of NetiquettenettextsNo ratings yet
- CRT Learning Module: Course Code Course Title No. of Hours Module TitleDocument11 pagesCRT Learning Module: Course Code Course Title No. of Hours Module TitleEiszel CadacioNo ratings yet
- Legal, Ethical, and Societal Issues in MediaDocument40 pagesLegal, Ethical, and Societal Issues in Medialorraine barrogaNo ratings yet
- LC-2&3-Legal Ethical and Societal Issues in Media and InformationDocument35 pagesLC-2&3-Legal Ethical and Societal Issues in Media and InformationRowena TattaoNo ratings yet
- Roles of The Internet and The WWW in EducationDocument9 pagesRoles of The Internet and The WWW in EducationPearly LucesNo ratings yet
- Work EtiquetteDocument10 pagesWork EtiquetteZeusKimNo ratings yet
- TOPIC 3 - Digital Citizenship and NetiquetteDocument23 pagesTOPIC 3 - Digital Citizenship and NetiquetteMarie CunananNo ratings yet
- BREM Syllabus Cohort 2Document8 pagesBREM Syllabus Cohort 2heymuraliNo ratings yet
- Student Netiquette: BACC 107 September 3, 2020Document26 pagesStudent Netiquette: BACC 107 September 3, 2020Rhealyn Joyce CabatbatNo ratings yet
- Netiquette Guidelines For Online Communication (Soc Sci 111)Document4 pagesNetiquette Guidelines For Online Communication (Soc Sci 111)Sargeant OxfordNo ratings yet
- Business Writing Essentials for Effective CommunicationDocument30 pagesBusiness Writing Essentials for Effective CommunicationHassaan Bin KhalidNo ratings yet
- Lesson 2Document3 pagesLesson 2Kiean CupinNo ratings yet
- Defensive Cyber Mastery: Expert Strategies for Unbeatable Personal and Business SecurityFrom EverandDefensive Cyber Mastery: Expert Strategies for Unbeatable Personal and Business SecurityRating: 5 out of 5 stars5/5 (1)
- The Digital Marketing Handbook: A Step-By-Step Guide to Creating Websites That SellFrom EverandThe Digital Marketing Handbook: A Step-By-Step Guide to Creating Websites That SellRating: 5 out of 5 stars5/5 (6)
- The Wires of War: Technology and the Global Struggle for PowerFrom EverandThe Wires of War: Technology and the Global Struggle for PowerRating: 4 out of 5 stars4/5 (34)
- Python for Beginners: The 1 Day Crash Course For Python Programming In The Real WorldFrom EverandPython for Beginners: The 1 Day Crash Course For Python Programming In The Real WorldNo ratings yet
- So You Want to Start a Podcast: Finding Your Voice, Telling Your Story, and Building a Community that Will ListenFrom EverandSo You Want to Start a Podcast: Finding Your Voice, Telling Your Story, and Building a Community that Will ListenRating: 4.5 out of 5 stars4.5/5 (35)
- The Internet Con: How to Seize the Means of ComputationFrom EverandThe Internet Con: How to Seize the Means of ComputationRating: 5 out of 5 stars5/5 (6)
- How to Be Fine: What We Learned by Living by the Rules of 50 Self-Help BooksFrom EverandHow to Be Fine: What We Learned by Living by the Rules of 50 Self-Help BooksRating: 4.5 out of 5 stars4.5/5 (48)
- Ultimate Guide to LinkedIn for Business: Access more than 500 million people in 10 minutesFrom EverandUltimate Guide to LinkedIn for Business: Access more than 500 million people in 10 minutesRating: 5 out of 5 stars5/5 (5)
- Content Rules: How to Create Killer Blogs, Podcasts, Videos, Ebooks, Webinars (and More) That Engage Customers and Ignite Your BusinessFrom EverandContent Rules: How to Create Killer Blogs, Podcasts, Videos, Ebooks, Webinars (and More) That Engage Customers and Ignite Your BusinessRating: 4.5 out of 5 stars4.5/5 (42)
- How to Do Nothing: Resisting the Attention EconomyFrom EverandHow to Do Nothing: Resisting the Attention EconomyRating: 4 out of 5 stars4/5 (421)
- Social Media Marketing 2024, 2025: Build Your Business, Skyrocket in Passive Income, Stop Working a 9-5 Lifestyle, True Online Working from HomeFrom EverandSocial Media Marketing 2024, 2025: Build Your Business, Skyrocket in Passive Income, Stop Working a 9-5 Lifestyle, True Online Working from HomeNo ratings yet
- Nine Algorithms That Changed the Future: The Ingenious Ideas That Drive Today's ComputersFrom EverandNine Algorithms That Changed the Future: The Ingenious Ideas That Drive Today's ComputersRating: 5 out of 5 stars5/5 (7)
- TikTok Algorithms 2024 $15,000/Month Guide To Escape Your Job And Build an Successful Social Media Marketing Business From Home Using Your Personal Account, Branding, SEO, InfluencerFrom EverandTikTok Algorithms 2024 $15,000/Month Guide To Escape Your Job And Build an Successful Social Media Marketing Business From Home Using Your Personal Account, Branding, SEO, InfluencerRating: 4 out of 5 stars4/5 (4)
- Ultimate Guide to YouTube for BusinessFrom EverandUltimate Guide to YouTube for BusinessRating: 5 out of 5 stars5/5 (1)
- More Porn - Faster!: 50 Tips & Tools for Faster and More Efficient Porn BrowsingFrom EverandMore Porn - Faster!: 50 Tips & Tools for Faster and More Efficient Porn BrowsingRating: 3.5 out of 5 stars3.5/5 (23)
- HTML5 and CSS3 Masterclass: In-depth Web Design Training with Geolocation, the HTML5 Canvas, 2D and 3D CSS Transformations, Flexbox, CSS Grid, and More (English Edition)From EverandHTML5 and CSS3 Masterclass: In-depth Web Design Training with Geolocation, the HTML5 Canvas, 2D and 3D CSS Transformations, Flexbox, CSS Grid, and More (English Edition)No ratings yet
- SEO 2021: Learn search engine optimization with smart internet marketing strategiesFrom EverandSEO 2021: Learn search engine optimization with smart internet marketing strategiesRating: 5 out of 5 stars5/5 (6)
- The $1,000,000 Web Designer Guide: A Practical Guide for Wealth and Freedom as an Online FreelancerFrom EverandThe $1,000,000 Web Designer Guide: A Practical Guide for Wealth and Freedom as an Online FreelancerRating: 4.5 out of 5 stars4.5/5 (22)
- Monitored: Business and Surveillance in a Time of Big DataFrom EverandMonitored: Business and Surveillance in a Time of Big DataRating: 4 out of 5 stars4/5 (1)
- The Designer’s Guide to Figma: Master Prototyping, Collaboration, Handoff, and WorkflowFrom EverandThe Designer’s Guide to Figma: Master Prototyping, Collaboration, Handoff, and WorkflowNo ratings yet