Professional Documents
Culture Documents
Danzalan Jeremy - Activity 1 (Mid)
Uploaded by
Rej Agustin0 ratings0% found this document useful (0 votes)
8 views2 pagesOriginal Title
Danzalan Jeremy - Activity 1 (mid)
Copyright
© © All Rights Reserved
Available Formats
DOCX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
8 views2 pagesDanzalan Jeremy - Activity 1 (Mid)
Uploaded by
Rej AgustinCopyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
You are on page 1of 2
Subject/Course
Platform Technologies
Name:Jeremy Dazanlan
Program/Course:PT101 BSIT -2A
Guide Question/s
1. Go to a process and set its priority to “high”. Take screenshot.
Example
2. What Level of threads is better? Why?
User - Level Thread
User-level threads are implemented by users and the kernel is
unaware of the existence of these threads. It treats them as if
they were single-threaded processes. User-level threads are small
and much faster than kernel-level threads. They are represented
by a program counter (PC), stack, registers, and a small process
control block. Additionally, there is no kernel involvement in
synchronization for user-level threads.
Advantages of user-level threads
Some of the benefits of user-level threads are
User-level threads are easier and faster to create than kernel-
level threads. They can also be managed more easily.
User-level threads can run on any operating system.
Thread switching in user-level threads does not require kernel-
mode privileges.
Disadvantages of user-level threads
Some of the disadvantages of user-level threads are that
multithreaded applications in user-level threads cannot take
advantage of multiprocessing. The whole process is blocked when a
user-level thread performs a blocking operation.
3. What is the best mode for data communication? Why?
Full-Duplex is the data transfer mode where data can flow in both
directions at the same time. It is bidirectional in nature. It is
a two-way communication where both stations can send and receive
data at the same time.
The full duplex mode has double the bandwidth of half duplex. The
channel capacity is split between the two communication
directions. This mode is used when full-duplex communication is
required.
the benefits of using a full-duplex transmission method
Two-way communication can be carried out in both directions at
the same time.
It is the fastest way of communication between devices.
the disadvantages of using a half-duplex transmission mode
The capacity of the communication channel is divided into two
parts. Also, there is no dedicated path for data transfer. It is
misusing the channel bandwidth because there are two separate
paths for two communicating devices.
Covered under Copyright Law of the 2 | Page
Philippines
All Rights Reserved @ OLSHCO
You might also like
- Multicore Software Development Techniques: Applications, Tips, and TricksFrom EverandMulticore Software Development Techniques: Applications, Tips, and TricksRating: 2.5 out of 5 stars2.5/5 (2)
- Advantages of Thread Over ProcessDocument4 pagesAdvantages of Thread Over ProcessSakshiNo ratings yet
- Unit 3 Process and Thread Kernel Data StructureDocument3 pagesUnit 3 Process and Thread Kernel Data StructureRishabh MalikNo ratings yet
- Mohamed Abdelrahman Anwar - 20011634 - Sheet 4Document15 pagesMohamed Abdelrahman Anwar - 20011634 - Sheet 4mohamed abdalrahmanNo ratings yet
- DCC ProjectDocument17 pagesDCC ProjectLucky JamnikNo ratings yet
- Threads and Its Types in Operating SystemDocument10 pagesThreads and Its Types in Operating SystemFranck divinfranckNo ratings yet
- Os Lec 5 ThreadDocument10 pagesOs Lec 5 Threadfihava5658No ratings yet
- Operating Systems Services: Program ExecutionDocument11 pagesOperating Systems Services: Program ExecutionKömäil MäzhárNo ratings yet
- Distributed Unit 2Document16 pagesDistributed Unit 2mj099159No ratings yet
- OS Module2.1 ThreadsDocument43 pagesOS Module2.1 ThreadsDavidNo ratings yet
- O.S - Theory Assignment 02Document7 pagesO.S - Theory Assignment 02Haadi KhanNo ratings yet
- Unit2 (Os) R20Document52 pagesUnit2 (Os) R20necn cse-b 2nd-yearNo ratings yet
- ProcessDocument33 pagesProcessSrijan singhNo ratings yet
- Lecture 3Document24 pagesLecture 3Pratik PatelNo ratings yet
- Nust College of Eme Nismah SaleemDocument4 pagesNust College of Eme Nismah SaleemNismah MuneebNo ratings yet
- Pass Assignment 1Document27 pagesPass Assignment 1Athl S33% (3)
- Performance Analysis of N-Computing Device Under Various Load ConditionsDocument7 pagesPerformance Analysis of N-Computing Device Under Various Load ConditionsInternational Organization of Scientific Research (IOSR)No ratings yet
- LO2 Determine Uer NeedsDocument17 pagesLO2 Determine Uer Needsbiruk mollaNo ratings yet
- ThreadDocument29 pagesThreadsumitbhadane22No ratings yet
- Computer NetworkDocument13 pagesComputer NetworkParidhi GaurNo ratings yet
- Questions To Practice For Cse323 Quiz 1Document4 pagesQuestions To Practice For Cse323 Quiz 1errormaruf4No ratings yet
- Processes: Distributed Systems Principles and ParadigmsDocument78 pagesProcesses: Distributed Systems Principles and ParadigmsZain HamzaNo ratings yet
- Thread (Operating System)Document17 pagesThread (Operating System)hashimkainatNo ratings yet
- Adv OsDocument12 pagesAdv Osshaik muheen saidaNo ratings yet
- Assignment Os: Saqib Javed 11912Document8 pagesAssignment Os: Saqib Javed 11912Saqib JavedNo ratings yet
- Chapter 4 - Processes and ThreadsDocument2 pagesChapter 4 - Processes and ThreadsAbdirahin AbdirahimNo ratings yet
- Ds/Unit 1 Truba College of Science & Tech., BhopalDocument9 pagesDs/Unit 1 Truba College of Science & Tech., BhopalKuldeep PalNo ratings yet
- What Is Interprocess Communication?Document39 pagesWhat Is Interprocess Communication?sumitbhadane22No ratings yet
- Chapter 3-ProcessesDocument23 pagesChapter 3-ProcessesGebreigziabher M. AbNo ratings yet
- SENG 307 Patterns2 UpdatedDocument32 pagesSENG 307 Patterns2 UpdatedNonny ElewekeNo ratings yet
- What Is Thread?Document8 pagesWhat Is Thread?Linda BrownNo ratings yet
- Stevenson College - Graded Unit-1Document53 pagesStevenson College - Graded Unit-1karagenski0% (1)
- DCS-Tutorial 2 (Answer)Document3 pagesDCS-Tutorial 2 (Answer)Siau HuiNo ratings yet
- OSYfDocument12 pagesOSYfMaruti PatilNo ratings yet
- Chapter 3Document25 pagesChapter 3yomiftamiru21No ratings yet
- Process and Thread: Group CDocument31 pagesProcess and Thread: Group CChit TarNo ratings yet
- 2 Assignment No 2 Chap 4 03042021 020349amDocument3 pages2 Assignment No 2 Chap 4 03042021 020349amatifNo ratings yet
- Threads: Basic Theory and Libraries: Unit of Resource OwnershipDocument33 pagesThreads: Basic Theory and Libraries: Unit of Resource OwnershipSudheera PalihakkaraNo ratings yet
- OS MOD - 2 NotesDocument44 pagesOS MOD - 2 NotesSHALINI KGNo ratings yet
- Lecture 1 Introduction To Distributed Systems - 034922Document6 pagesLecture 1 Introduction To Distributed Systems - 034922leonardkigen100No ratings yet
- Scheduler Activations:: Effective Kernel Support For The User-Level Management of ParallelismDocument19 pagesScheduler Activations:: Effective Kernel Support For The User-Level Management of ParallelismsushmsnNo ratings yet
- CN Unit-1 Imp QA'sDocument29 pagesCN Unit-1 Imp QA'shajirasabuhiNo ratings yet
- Unit 1Document14 pagesUnit 1Amruta ShingoteNo ratings yet
- Lecture 6, OS PDFDocument7 pagesLecture 6, OS PDFMaria Akter LuthfaNo ratings yet
- CH 4 (Threads)Document8 pagesCH 4 (Threads)Muhammad ImranNo ratings yet
- Computer NetworkDocument32 pagesComputer NetworkTony StarkNo ratings yet
- XII - Computer Networks - DifferentWaysofSendingDataOnNW - SwitchingTechniquesDocument17 pagesXII - Computer Networks - DifferentWaysofSendingDataOnNW - SwitchingTechniquesLakshya NayakNo ratings yet
- OS Unit 2Document6 pagesOS Unit 2Study WorkNo ratings yet
- CN Experiment 2Document6 pagesCN Experiment 2rudraNo ratings yet
- It Is The ThreadDocument17 pagesIt Is The Threadbhageshnarnawareg1No ratings yet
- CNS Long AnswersDocument42 pagesCNS Long AnswersRagnar LothbrokeNo ratings yet
- Computer Networks and Their AttributesDocument34 pagesComputer Networks and Their AttributesOxman BhattiNo ratings yet
- 2nd Data Communication NetworkDocument5 pages2nd Data Communication NetworkIan Michael LacsonNo ratings yet
- Networking AssignmentDocument15 pagesNetworking AssignmentabcdNo ratings yet
- Computer Network AssignDocument6 pagesComputer Network AssignMasood MughalNo ratings yet
- ThreadsDocument24 pagesThreadsAjay Kumar RNo ratings yet
- Unit-Ii 2ND PartDocument7 pagesUnit-Ii 2ND PartRABIN SINGHANo ratings yet
- Operating System Lect12Document34 pagesOperating System Lect12gogochor5No ratings yet
- DCCN SolutionDocument11 pagesDCCN SolutionghostproxgamingNo ratings yet
- Threads Class 2 Module 2Document6 pagesThreads Class 2 Module 2Bobby chNo ratings yet
- REVIEWERDocument20 pagesREVIEWERRej AgustinNo ratings yet
- Rad Danzalan Jeremy ADocument1 pageRad Danzalan Jeremy ARej AgustinNo ratings yet
- Activity 2 (Finals)Document2 pagesActivity 2 (Finals)Rej AgustinNo ratings yet
- GE9Document2 pagesGE9Rej AgustinNo ratings yet
- Reviewer in Ge10Document13 pagesReviewer in Ge10Rej AgustinNo ratings yet
- Action-Plan TemplateDocument5 pagesAction-Plan TemplateRej AgustinNo ratings yet
- Church HistoryDocument4 pagesChurch HistoryRej AgustinNo ratings yet
- Danzalan Jeremy A PrototypingDocument1 pageDanzalan Jeremy A PrototypingRej AgustinNo ratings yet
- Carl Second VaticanDocument2 pagesCarl Second VaticanRej AgustinNo ratings yet
- Carl Church HistoryDocument3 pagesCarl Church HistoryRej AgustinNo ratings yet
- GE8 PrintDocument8 pagesGE8 PrintRej AgustinNo ratings yet
- Notes On Ecclessiology CourseDocument208 pagesNotes On Ecclessiology CourseRej AgustinNo ratings yet
- Second Vatican CouncilDocument2 pagesSecond Vatican CouncilRej AgustinNo ratings yet
- Jewel DanzalanDocument9 pagesJewel DanzalanRej AgustinNo ratings yet
- Danzalan Jeremy - PT101 MidtermExamDocument4 pagesDanzalan Jeremy - PT101 MidtermExamRej AgustinNo ratings yet
- Module 10 - English For ITDocument50 pagesModule 10 - English For ITRej AgustinNo ratings yet
- First PageDocument4 pagesFirst PageRej AgustinNo ratings yet
- A Case Study of Marcopper Mining DisasterDocument6 pagesA Case Study of Marcopper Mining DisasterRej AgustinNo ratings yet
- Incremental Development ModelDocument12 pagesIncremental Development ModelRej AgustinNo ratings yet
- Labasan Melchor Christian Jr. Activity 2 MidDocument4 pagesLabasan Melchor Christian Jr. Activity 2 MidRej AgustinNo ratings yet
- Midterm Reviewer in Ge8Document24 pagesMidterm Reviewer in Ge8Rej AgustinNo ratings yet
- Cisco CSS 11000 Series OverviewDocument4 pagesCisco CSS 11000 Series OverviewGerryNo ratings yet
- MapReduce ExampleDocument76 pagesMapReduce ExampleYoonMin NamNo ratings yet
- Software EngineerDocument2 pagesSoftware Engineerapi-78307656No ratings yet
- Dos Command1Document5 pagesDos Command1Vinoth MechNo ratings yet
- Introduction To Socket ProgrammingDocument20 pagesIntroduction To Socket ProgrammingSundariNo ratings yet
- Microsensor I2cDocument4 pagesMicrosensor I2cVuk AntonicNo ratings yet
- Gateway Zx4800-02 OobeDocument11 pagesGateway Zx4800-02 OobeJohnNO69No ratings yet
- Ascenlink: Wan Link Load BalancingDocument3 pagesAscenlink: Wan Link Load BalancingGustavo SantosNo ratings yet
- U Face 800Document2 pagesU Face 800akhtarNo ratings yet
- Sony Kdl-40-52nx803 CH Az1hDocument47 pagesSony Kdl-40-52nx803 CH Az1hIsmael CosgayaNo ratings yet
- It2353 Web Technology Question Bank Unit I: 40. HTML Is Case Sensitive or Not?Document4 pagesIt2353 Web Technology Question Bank Unit I: 40. HTML Is Case Sensitive or Not?Baran Mahamood MNo ratings yet
- Digital Input Module SM 321 DI 16 X DC 24 V High Speed (6ES7321-1BH10-0AA0)Document3 pagesDigital Input Module SM 321 DI 16 X DC 24 V High Speed (6ES7321-1BH10-0AA0)Fabio CavalheiroNo ratings yet
- 05-TL - SS002 - E01 - 0 ZXSDR B8200 TL200 Principle and Hardware Structure Training Manual-48Document48 pages05-TL - SS002 - E01 - 0 ZXSDR B8200 TL200 Principle and Hardware Structure Training Manual-48a2227 jglNo ratings yet
- Rigol 2016 Full Product CatalogDocument52 pagesRigol 2016 Full Product Cataloghindukusc80No ratings yet
- Hands-On Ethical Hacking and Network Defense: Linux Operating System VulnerabilitiesDocument40 pagesHands-On Ethical Hacking and Network Defense: Linux Operating System VulnerabilitiesAhsan HabibNo ratings yet
- Focom Manual enDocument43 pagesFocom Manual enIulianCiobanuNo ratings yet
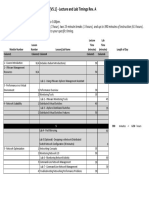
- Vmware Vsphere: Optimize and Scale (V5.1) - Lecture and Lab Timings Rev. ADocument1 pageVmware Vsphere: Optimize and Scale (V5.1) - Lecture and Lab Timings Rev. Au9yNo ratings yet
- Namespaces Cgroups Conatiners PDFDocument74 pagesNamespaces Cgroups Conatiners PDFSoumana Abdou AmadouNo ratings yet
- ETI Unit 2 MCQDocument25 pagesETI Unit 2 MCQPooja AbhangNo ratings yet
- SAU User Guide (Nastar Service Component) (V600R014 - 04) (PDF) - enDocument277 pagesSAU User Guide (Nastar Service Component) (V600R014 - 04) (PDF) - enmike0147230No ratings yet
- 454u6 - Elective I - Grid ComputingDocument20 pages454u6 - Elective I - Grid ComputingArjun Reddy100% (1)
- Kip 800 Series BrochureDocument12 pagesKip 800 Series BrochurekgiyerNo ratings yet
- Nokia MHA ParametersDocument38 pagesNokia MHA ParametersRockyNo ratings yet
- CCNA Exploration 2 - FINAL Exam Answers (C) Version 4.0Document10 pagesCCNA Exploration 2 - FINAL Exam Answers (C) Version 4.0fun kollaNo ratings yet
- Modul-5 Panduan Design FTTH 2014 VER 1.1Document75 pagesModul-5 Panduan Design FTTH 2014 VER 1.1Ivan FernaldyNo ratings yet
- Netflow Endpoint - 192.168.100.12: Last Hour IngressDocument3 pagesNetflow Endpoint - 192.168.100.12: Last Hour IngressclaudingaNo ratings yet
- Password Recovery Dor Cisco 1941Document10 pagesPassword Recovery Dor Cisco 1941Chris BuenaventuraNo ratings yet
- Tangowithdjango2 PDFDocument267 pagesTangowithdjango2 PDFAntonio Carlos Ortiz71% (7)
- Project 3a Hacking Web Apps With Command Injections and Patching ThemDocument3 pagesProject 3a Hacking Web Apps With Command Injections and Patching Themmaylinpatydakin0% (1)
- PongoSAG 191101Document242 pagesPongoSAG 191101ElvÏs ElvÏsNo ratings yet
- iPhone Unlocked for the Non-Tech Savvy: Color Images & Illustrated Instructions to Simplify the Smartphone Use for Beginners & Seniors [COLOR EDITION]From EverandiPhone Unlocked for the Non-Tech Savvy: Color Images & Illustrated Instructions to Simplify the Smartphone Use for Beginners & Seniors [COLOR EDITION]Rating: 5 out of 5 stars5/5 (3)
- iPhone 14 Guide for Seniors: Unlocking Seamless Simplicity for the Golden Generation with Step-by-Step ScreenshotsFrom EverandiPhone 14 Guide for Seniors: Unlocking Seamless Simplicity for the Golden Generation with Step-by-Step ScreenshotsRating: 5 out of 5 stars5/5 (3)
- RHCSA Red Hat Enterprise Linux 9: Training and Exam Preparation Guide (EX200), Third EditionFrom EverandRHCSA Red Hat Enterprise Linux 9: Training and Exam Preparation Guide (EX200), Third EditionNo ratings yet
- Kali Linux - An Ethical Hacker's Cookbook - Second Edition: Practical recipes that combine strategies, attacks, and tools for advanced penetration testing, 2nd EditionFrom EverandKali Linux - An Ethical Hacker's Cookbook - Second Edition: Practical recipes that combine strategies, attacks, and tools for advanced penetration testing, 2nd EditionRating: 5 out of 5 stars5/5 (1)
- Linux For Beginners: The Comprehensive Guide To Learning Linux Operating System And Mastering Linux Command Line Like A ProFrom EverandLinux For Beginners: The Comprehensive Guide To Learning Linux Operating System And Mastering Linux Command Line Like A ProNo ratings yet
- Hacking : The Ultimate Comprehensive Step-By-Step Guide to the Basics of Ethical HackingFrom EverandHacking : The Ultimate Comprehensive Step-By-Step Guide to the Basics of Ethical HackingRating: 5 out of 5 stars5/5 (3)
- Mastering Swift 5 - Fifth Edition: Deep dive into the latest edition of the Swift programming language, 5th EditionFrom EverandMastering Swift 5 - Fifth Edition: Deep dive into the latest edition of the Swift programming language, 5th EditionNo ratings yet
- Linux: A Comprehensive Guide to Linux Operating System and Command LineFrom EverandLinux: A Comprehensive Guide to Linux Operating System and Command LineNo ratings yet
- Excel : The Ultimate Comprehensive Step-By-Step Guide to the Basics of Excel Programming: 1From EverandExcel : The Ultimate Comprehensive Step-By-Step Guide to the Basics of Excel Programming: 1Rating: 4.5 out of 5 stars4.5/5 (3)
- Mastering Linux Security and Hardening - Second Edition: Protect your Linux systems from intruders, malware attacks, and other cyber threats, 2nd EditionFrom EverandMastering Linux Security and Hardening - Second Edition: Protect your Linux systems from intruders, malware attacks, and other cyber threats, 2nd EditionNo ratings yet
- React.js for A Beginners Guide : From Basics to Advanced - A Comprehensive Guide to Effortless Web Development for Beginners, Intermediates, and ExpertsFrom EverandReact.js for A Beginners Guide : From Basics to Advanced - A Comprehensive Guide to Effortless Web Development for Beginners, Intermediates, and ExpertsNo ratings yet
- Azure DevOps Engineer: Exam AZ-400: Azure DevOps Engineer: Exam AZ-400 Designing and Implementing Microsoft DevOps SolutionsFrom EverandAzure DevOps Engineer: Exam AZ-400: Azure DevOps Engineer: Exam AZ-400 Designing and Implementing Microsoft DevOps SolutionsNo ratings yet
- Hello Swift!: iOS app programming for kids and other beginnersFrom EverandHello Swift!: iOS app programming for kids and other beginnersNo ratings yet
- RHCSA Exam Pass: Red Hat Certified System Administrator Study GuideFrom EverandRHCSA Exam Pass: Red Hat Certified System Administrator Study GuideNo ratings yet














































































































![iPhone Unlocked for the Non-Tech Savvy: Color Images & Illustrated Instructions to Simplify the Smartphone Use for Beginners & Seniors [COLOR EDITION]](https://imgv2-2-f.scribdassets.com/img/audiobook_square_badge/728318688/198x198/f3385cbfef/1715193157?v=1)