Professional Documents
Culture Documents
Pranay Report
Uploaded by
balaji xeroxCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Pranay Report
Uploaded by
balaji xeroxCopyright:
Available Formats
Optimal Jamming Attack
ABSTRACT
An optimal jamming attack involves strategically disrupting communication
channels to maximize the impact on the target system while minimizing the
resources expended by the attacker. This form of cyber warfare aims to exploit
vulnerabilities in wireless networks, rendering them dysfunctional or
significantly impairing their performance. The attacker seeks to identify the
most efficient frequency bands or communication protocols to disrupt, aiming
for a balance between achieving the desired impact and evading detection.
Optimal jamming attacks pose significant challenges for defenders, as they
require sophisticated countermeasures to detect and mitigate the interference,
highlighting the ongoing cat-and-mouse game in the realm of cybersecurity.
The proliferation of wireless communication systems has led to an increased
vulnerability to adversarial actions, with jamming attacks being a prominent
threat. Optimal jamming attacks refer to strategic interference aimed at
disrupting the communication between legitimate parties in a manner that
maximizes the attacker's objectives while minimizing resource expenditure.
This abstract provides an overview of the concept of optimal jamming attacks,
exploring their strategic aspects, potential impacts on communication systems,
and countermeasures.
Department of Information Science and Engineering,
PDA College of Engineering, Kalaburagi Page 1
Optimal Jamming Attack
INTRODUCTION
An optimal jamming attack refers to the deliberate interference with wireless
communication systems in a strategic and efficient manner. The goal is to
disrupt or disable the targeted communication channels while minimizing
resource usage. This type of attack aims to exploit vulnerabilities in the
communication protocols or wireless networks, often requiring careful analysis
and optimization to achieve maximum impact with minimal energy expenditure.
Optimal jamming attacks can be a concern in various domains, including
military communications, IoT networks, and other wireless
communication systems.
Optimal jamming attacks leverage a deep understanding of communication
protocols, system architectures, and channel characteristics to exploit
weaknesses in the targeted network. This strategic approach sets them apart
from traditional jamming methods, requiring the attacker to make dynamic
decisions based on evolving conditions. As a result, optimal jamming attacks
pose a formidable challenge to the robustness of wireless communication
systems, prompting researchers and practitioners to delve into the intricacies of
this threat to develop effective countermeasures.
Department of Information Science and Engineering,
PDA College of Engineering, Kalaburagi Page 2
Optimal Jamming Attack
WORKING OF OPTIMAL JAMMING
1. Understanding the Communication System:
- The attacker first needs a good understanding of the target communication
system, including the modulation schemes, frequency bands, and other relevant
parameters.
2. Signal Analysis:
- The attacker analyzes the signals used in the communication system. This
includes understanding the modulation and coding schemes employed by the
system.
3. Jamming Strategy:
- Based on the analysis, the attacker devises a jamming strategy to interfere
with the communication system. This may involve transmitting jamming signals
in specific frequency bands, patterns, or using certain modulation schemes.
4. Optimization:
- The term "optimal" implies that the attacker seeks to optimize the
effectiveness of the jamming signals. This optimization involves finding the
best parameters for the jamming signals, such as power levels, frequencies, and
timing, to achieve the desired impact on the communication system.
5. Adaptability:
- In some cases, optimal jamming attacks may involve adaptive techniques
where the attacker adjusts the jamming parameters dynamically based on
changes in the communication system's behavior. This adaptability allows the
attacker to maintain effectiveness despite countermeasures taken by the target.
Department of Information Science and Engineering,
PDA College of Engineering, Kalaburagi Page 3
Optimal Jamming Attack
6. Avoiding Detection:
- To maximize the impact and duration of the attack, the attacker may also
employ techniques to avoid detection by the target's defenses. This could
include using spread spectrum techniques, frequency hopping, or other methods
to make it challenging for the target to identify and mitigate the jamming
signals.
7. Impact on Communication System:
- The ultimate goal is to disrupt the targeted communication system. The
impact can range from causing temporary disruptions to rendering the
communication system completely unusable, depending on the attacker's
objectives.
Department of Information Science and Engineering,
PDA College of Engineering, Kalaburagi Page 4
Optimal Jamming Attack
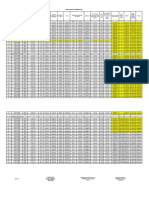
ARCHITECTURE
Department of Information Science and Engineering,
PDA College of Engineering, Kalaburagi Page 5
Optimal Jamming Attack
1. Monitor the Network Communication:
- In this step, the communication network is continuously monitored for any
unusual patterns, disruptions, or anomalies. This can involve the use of intrusion
detection systems, traffic analysis, and other monitoring tools to identify
potential signs of jamming or interference.
2. Is Jamming Detected:
- The monitoring system analyzes the network data to determine if there are
indications of jamming. This can include identifying sudden increases in noise,
changes in signal strength, or disruptions in communication patterns that may be
indicative of a jamming attack.
3. Find Concerned Node:
- Once jamming is detected, the system attempts to identify the specific nodes
or devices that are being affected by the jamming signals. This involves
pinpointing the areas of the network that are experiencing disruptions.
4. Apply Localization Algorithm:
- A localization algorithm is employed to determine the physical location of
the jamming source or sources. This algorithm may use techniques such as
triangulation, signal strength analysis, or time-of-arrival measurements to
estimate the location of the jammer.
5. Locate and Block Jammer:
- With the information obtained from the localization algorithm, the system
takes measures to physically locate the jamming device or devices. Once
located, countermeasures are deployed to block or neutralize the jamming
signals. This can involve disabling the jamming device or adjusting network
settings to mitigate the impact.
6. Continue with Actual Transmission without Any Jamming Attack:
- After successfully blocking the jamming signals and neutralizing the threat,
the network communication system can resume normal operation. This involves
ensuring that the affected nodes or devices can continue their intended
transmissions without further interference.
Department of Information Science and Engineering,
PDA College of Engineering, Kalaburagi Page 6
Optimal Jamming Attack
Department of Information Science and Engineering,
PDA College of Engineering, Kalaburagi Page 7
Optimal Jamming Attack
ADVANTAGES
1. Disruption of Communication:
Jamming attacks can disrupt communication systems, causing confusion,
hindering coordination, and potentially impeding the ability of a targeted entity
to respond effectively.
2. Security Bypass:
Jamming can be used as a means to disrupt security measures that rely on
communication, potentially creating vulnerabilities in the targeted system.
3.Economic Impact:
Disrupting communication in critical sectors such as finance, transportation, or
healthcare could have economic consequences, affecting businesses, services,
and overall infrastructure.
4. Espionage and Information Theft:
Jamming attacks may be used to create distractions or disrupt communication
channels, allowing malicious actors to exploit the chaos and carry out other
activities, such as information theft or espionage.
5. Denial of Service (DoS):
Jamming attacks can be part of a broader strategy to execute denial-of-service
attacks, rendering systems or services unavailable to legitimate users.
6. Versatility:
Optimal jamming attacks can be tailored to exploit specific vulnerabilities in
communication protocols, making them versatile for targeting various systems.
7. Low Resource Requirement:
In some cases, optimal jamming attacks may achieve significant disruption
with relatively low resource requirements, making them attractive for
adversaries with limited resources.
Department of Information Science and Engineering,
PDA College of Engineering, Kalaburagi Page 8
Optimal Jamming Attack
8.Defensive measures against jamming attacks:
Understanding how these attacks work can help you develop strategies to
protect your systems and communications.
9.The importance of cybersecurity:
In today's digital world, protecting our data and systems is crucial. I can share
information about different cybersecurity threats and best practices for staying
safe online.
10.The ethical implications of technology:
Technology can be used for both good and bad purposes. I can discuss the
importance of using technology ethically and responsibly.
Department of Information Science and Engineering,
PDA College of Engineering, Kalaburagi Page 9
Optimal Jamming Attack
DISADVANTAGES
1. Disruption of Critical Services:
Jamming attacks can disrupt essential communication services such as
emergency services, air traffic control, and healthcare systems. This can lead to
delayed responses to emergencies, potentially resulting in loss of life or
property.
2. Economic Impact:
Disruption of communication in critical sectors can have severe economic
consequences. For example, interruptions in financial communication systems
can impact stock markets and financial transactions, leading to financial losses.
3. Security Risks:
Jamming attacks may create vulnerabilities in security systems that rely on
communication, potentially allowing unauthorized access, data breaches, or
other security incidents.
4. Loss of Productivity:
Businesses and organizations heavily depend on communication systems for
day-to-day operations. Jamming attacks can disrupt these systems, leading to a
loss of productivity and revenue.
5. Public Safety Concerns:
Jamming attacks in public spaces or during large events can create panic and
confusion, raising public safety concerns. For instance, disrupting
communication in crowded areas may impede the ability to manage and respond
to potential security threats.
6. Military Implications:
In military contexts, jamming attacks can disrupt command and control
communications, compromising the effectiveness of military operations and
posing a threat to national security.
Department of Information Science and Engineering,
PDA College of Engineering, Kalaburagi Page 10
Optimal Jamming Attack
7. Legal Consequences:
Engaging in jamming attacks is illegal in many jurisdictions. Perpetrators may
face legal action, including fines and imprisonment, if caught and prosecuted.
8. Reputation Damage:
Organizations and individuals responsible for jamming attacks risk significant
damage to their reputation. Being associated with disruptive and malicious
activities can result in loss of trust and credibility.
9. Collateral Damage:
Jamming attacks may not be precise and can affect unintended targets. Innocent
individuals and organizations may experience disruptions and negative
consequences due to the indiscriminate nature of such attacks.
10.Escalation of Conflict:
In certain situations, jamming attacks can contribute to an escalation of tensions
between parties involved, potentially leading to a broader conflict.
Department of Information Science and Engineering,
PDA College of Engineering, Kalaburagi Page 11
Optimal Jamming Attack
APPLICATIONS
1. Research in Cyberwarfare:
Explore the theoretical frameworks and ethical considerations around jamming
attacks in the context of cyberwarfare, emphasizing the potential for disruption
and escalation of conflict.
2. Industrial Espionage:
Discuss the hypothetical use of jamming attacks to disrupt communications and
steal sensitive information in industrial settings, highlighting the economic and
security implications.
3. Electronic Countermeasures:
Analyze the strategies employed in developing electronic countermeasures
against jamming attacks, focusing on the technical challenges and limitations of
such defensive systems.
4. Wireless Network Security:
Examine the vulnerabilities of wireless networks to jamming attacks and
explore mitigation techniques such as frequency hopping, spread spectrum
communication, and jamming detection algorithms.
5. Regulatory Frameworks:
Discuss the need for international regulations and collaborative efforts to
prevent the development and deployment of malicious jamming technologies.
6. Privacy Implications:
Explore the potential of jamming attacks to be used for surveillance and privacy
violations, raising questions about the ethical implications of such technologies.
Department of Information Science and Engineering,
PDA College of Engineering, Kalaburagi Page 12
Optimal Jamming Attack
7. Public Safety Concerns:
Discuss the risks posed by jamming attacks to public safety, such as disruption
of emergency communications and navigation systems, emphasizing the need
for responsible development and deployment of such technologies.
8.International Cooperation:
Discuss the need for international cooperation and information sharing to
combat the development and deployment of malicious jamming technologies,
emphasizing the importance of collaborative efforts in cybersecurity.
9.Education and Awareness:
Explore the importance of educating the public and policymakers about the
potential dangers of jamming attacks and promoting responsible use of
technology.
10.Emerging Technologies:
Analyze the vulnerabilities of emerging technologies, such as autonomous
vehicles and drones, to jamming attacks and discuss potential mitigation
strategies.
Department of Information Science and Engineering,
PDA College of Engineering, Kalaburagi Page 13
Optimal Jamming Attack
CONCLUSION
Optimal jamming attacks, while presenting theoretical challenges in the field of
communication security, raise serious ethical and practical concerns. Their
potential to disrupt critical infrastructure, compromise personal safety, and even
escalate conflict makes their responsible development and application
paramount. Instead of delving into specific attack details, it's crucial to focus on
understanding the vulnerabilities such attacks exploit, exploring robust
defensive measures, and fostering international collaboration to ensure
technology serves as a force for good. By prioritizing ethical research and
promoting responsible use, we can navigate the complex landscape of jamming
technology and build a safer, more secure digital future for all.
Department of Information Science and Engineering,
PDA College of Engineering, Kalaburagi Page 14
Optimal Jamming Attack
REFERENCES
1] P. Kyasanur and N. Vaidya, “Selfish MAC layer misbehavior in wireless
networks,” IEEE Trans. Mobile Computing,, vol. 4, no. 5, Sept./Oct. 2020.
[2] S. Radosavac, I. Koutsopoulos and J.S. Baras, “A framework for MAC
protocol misbehavior detection in wireless networks,” in Proc. ACM Workshop
on Wireless Security (WiSe), 2022.
[3] R. Negi and A. Perrig, “Jamming analysis of MAC protocols,” Carnegie
Mellon Technical Memo, 2022.
[4] R. Mallik, R. Scholtz, and G. Papavassilopoulos, “Analysis of an on-off
jamming situation as a dynamic game,” IEEE Trans. Commun., vol. 48, no. 8,
pp. 1360-1373, Aug. 2020.
[5] J. Jung, V. Paxson, A.W. Berger and H. Balakrishnan, “Fast portscan
detection using sequential hypothesis testing,” in Proc. IEEE Symposium on
Security and Privacy, 2018.
[6] V. Coskun, E. Cayirci, A. Levi, and S. Sancak, “Quarantine region scheme to
mitigate spam attacks in wireless-sensor networks”, IEEE Trans. on Mobile
Computing, vol. 5, no. 8, pp. 1074-1086, August 2021.
[7] A. D. Wood and J. A. Stankovic, “Denial of service in sensor networks,”
IEEE Computer, vol. 35, no. 10, pp. 54-62, 2022.
[8] Y. W. Law, L. van Hoesel, J. Doumen, P. Hartel and P. Havinga, “ Energy
efficient link-layer jamming attacks against wireless sensor network MAC
protocols,” in Proc. ACM Security Sensor Ad-hoc Networks (SASN), 2005. [9]
G. Lin and G. Noubir, “On link-layer denial of service in data wireless LANs,”
Journal on Wireless Comm. and Mob. Computing, August 2020.
[10] M. Cagalj, S. Capkun, J.-P. Hubaux, “Wormhole-based anti-jamming
techniques in sensor networks,” IEEE Trans. on Mobile Computing, vol. 6, no.
1, pp. 100-114, Jan. 2019.
Department of Information Science and Engineering,
PDA College of Engineering, Kalaburagi Page 15
You might also like
- Cyber-Physical Attacks: A Growing Invisible ThreatFrom EverandCyber-Physical Attacks: A Growing Invisible ThreatRating: 4.5 out of 5 stars4.5/5 (3)
- Attack Prevention TechniquesDocument9 pagesAttack Prevention TechniquesLavanya AlagNo ratings yet
- How to Defeat Advanced Malware: New Tools for Protection and ForensicsFrom EverandHow to Defeat Advanced Malware: New Tools for Protection and ForensicsNo ratings yet
- Jamming and Network Restoration On Multi Channel Wireless Sensor NetworksDocument5 pagesJamming and Network Restoration On Multi Channel Wireless Sensor NetworksRakeshconclaveNo ratings yet
- Literature SurveyDocument3 pagesLiterature SurveyAshok KumarNo ratings yet
- International Journal of Engineering Research and Development (IJERD)Document7 pagesInternational Journal of Engineering Research and Development (IJERD)IJERDNo ratings yet
- Assignment 2Document8 pagesAssignment 2bobjbobNo ratings yet
- Cybersecurity Attacks: Detection and Mitigation: A Guide For PsapsDocument11 pagesCybersecurity Attacks: Detection and Mitigation: A Guide For PsapsepraetorianNo ratings yet
- Design and Implementation of A Network Security Model For Cooperative NetworkDocument11 pagesDesign and Implementation of A Network Security Model For Cooperative NetworkJitendra Yadav100% (1)
- Intrusion Detection Against Denial of Service Attacks in Manet EnvironmentDocument8 pagesIntrusion Detection Against Denial of Service Attacks in Manet EnvironmentInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Quest 01Document10 pagesQuest 01Muhammad Ibrahim MarwatNo ratings yet
- Am 03402220229Document8 pagesAm 03402220229International Journal of computational Engineering research (IJCER)No ratings yet
- Ubiccjournalvolume2no3 5 67Document9 pagesUbiccjournalvolume2no3 5 67Ubiquitous Computing and Communication JournalNo ratings yet
- Distributed and Intelligent Platform of Intrusion Detection at Two LevelsDocument8 pagesDistributed and Intelligent Platform of Intrusion Detection at Two LevelsBasavaraj KagalkarNo ratings yet
- Explore Signaling Security Network - White Paper - EricssonDocument8 pagesExplore Signaling Security Network - White Paper - EricssonYanis BouabdallahNo ratings yet
- Literature Survey by M.arunprabu (Mitigation of Control Channel Jamming)Document8 pagesLiterature Survey by M.arunprabu (Mitigation of Control Channel Jamming)arunprabu123No ratings yet
- MANET Study: Security Threats and Counter MeasureDocument12 pagesMANET Study: Security Threats and Counter MeasureInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- An Efficient Leader Election Mechanism For Intrusion Detection in MANETDocument6 pagesAn Efficient Leader Election Mechanism For Intrusion Detection in MANETJournal of Computer ApplicationsNo ratings yet
- The Next Generation Cognitive Security O PDFDocument22 pagesThe Next Generation Cognitive Security O PDFNurgiantoNo ratings yet
- Presetation Report ON Network Security: Submitted To:-Submitted By: - Ms. Amba Ramneek Kaur Faculty, MRIU FET/CS(s) /2092Document19 pagesPresetation Report ON Network Security: Submitted To:-Submitted By: - Ms. Amba Ramneek Kaur Faculty, MRIU FET/CS(s) /2092Tushar ChandhokNo ratings yet
- Research ProjectDocument8 pagesResearch ProjectAlvin ChiengNo ratings yet
- Q1: Different Types of Security Attacks Along With Prevention Techniques?Document21 pagesQ1: Different Types of Security Attacks Along With Prevention Techniques?Varun KumarNo ratings yet
- Design and Implementation of A Network Security Model For Cooperative Network PDFDocument11 pagesDesign and Implementation of A Network Security Model For Cooperative Network PDFSpad ParnianNo ratings yet
- Design and Implementation of A Network Security Model For Cooperative Network PDFDocument11 pagesDesign and Implementation of A Network Security Model For Cooperative Network PDFyassin alkulaiNo ratings yet
- Network SecurityDocument53 pagesNetwork SecuritytsayeedctgNo ratings yet
- Order 3Document14 pagesOrder 3Chris MwangiNo ratings yet
- Energy Efficient & Low Power Consuming Data Aggregation Method For Intrusion Detection in MANETDocument9 pagesEnergy Efficient & Low Power Consuming Data Aggregation Method For Intrusion Detection in MANETInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Adaptive Distributed Mechanism Against Flooding Network Attacks Based On Machine LearningDocument11 pagesAdaptive Distributed Mechanism Against Flooding Network Attacks Based On Machine LearningKevin MondragonNo ratings yet
- Intrusion Detection Techniques in Mobile NetworksDocument8 pagesIntrusion Detection Techniques in Mobile NetworksInternational Organization of Scientific Research (IOSR)No ratings yet
- Strategic Honeypot Game Model For Distributed Denial of Service Attacks in The Smart Grid PDFDocument9 pagesStrategic Honeypot Game Model For Distributed Denial of Service Attacks in The Smart Grid PDFYudha Ananda PratamaNo ratings yet
- IEP RevoU Sept23 NEXT - RezaMalikiAkbar - IoTCyberSecDocument35 pagesIEP RevoU Sept23 NEXT - RezaMalikiAkbar - IoTCyberSechasna.nafirNo ratings yet
- Intrusion Detection System by Layered Approach and Hidden Markov ModelDocument8 pagesIntrusion Detection System by Layered Approach and Hidden Markov ModelArnav GudduNo ratings yet
- Study of Active Network Intrusion Detection SystemDocument6 pagesStudy of Active Network Intrusion Detection SystemInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- FIT3031 Tutorial 1 Sample Solution Introduction To Information & Network SecurityDocument5 pagesFIT3031 Tutorial 1 Sample Solution Introduction To Information & Network SecurityMozenkei100% (1)
- Security in Optical NetworksDocument21 pagesSecurity in Optical NetworksDivonikaNo ratings yet
- Designing A Multi-Layered Security Algorithms For Network Intrusion Detection Systems On Virtual Machines in The Cloud ComputingDocument9 pagesDesigning A Multi-Layered Security Algorithms For Network Intrusion Detection Systems On Virtual Machines in The Cloud ComputingIOSRJEN : hard copy, certificates, Call for Papers 2013, publishing of journalNo ratings yet
- Mns 5gDocument7 pagesMns 5gfemiNo ratings yet
- Intrusion Detection Systems: 2.2 DescriptionDocument10 pagesIntrusion Detection Systems: 2.2 DescriptionneehajosephNo ratings yet
- Existing System:: Data Analysis For Network Cyber-Security Focuses On Monitoring and AnalyzingDocument3 pagesExisting System:: Data Analysis For Network Cyber-Security Focuses On Monitoring and AnalyzingKeerthik ReddyNo ratings yet
- A Survey of Intrusion Detection Techniques in Computer NetworkDocument3 pagesA Survey of Intrusion Detection Techniques in Computer NetworkEditor IJRITCCNo ratings yet
- Research Article: Network Traffic Anomaly Detection Based On ML-ESN For Power Metering SystemDocument21 pagesResearch Article: Network Traffic Anomaly Detection Based On ML-ESN For Power Metering Systemmichael dapoNo ratings yet
- Detecting Wormhole Attack in Wireless Network Coding System Using Dawn & ETXDocument6 pagesDetecting Wormhole Attack in Wireless Network Coding System Using Dawn & ETXIJSTENo ratings yet
- Welcome To International Journal of Engineering Research and Development (IJERD)Document7 pagesWelcome To International Journal of Engineering Research and Development (IJERD)IJERDNo ratings yet
- The Discovery of Jamming Attackers in Wireless Sensor NetworksDocument9 pagesThe Discovery of Jamming Attackers in Wireless Sensor NetworksAparupa DasguptaNo ratings yet
- 14 1474953582 - 27-09-2016 PDFDocument3 pages14 1474953582 - 27-09-2016 PDFEditor IJRITCCNo ratings yet
- Valnurabiloity AssessmentDocument5 pagesValnurabiloity AssessmentBlessing ShenjeNo ratings yet
- 14 Ways To Evade Botnet Malware Attacks On Your Computers (Recovered)Document7 pages14 Ways To Evade Botnet Malware Attacks On Your Computers (Recovered)nanaNo ratings yet
- Network Security - Attacks and Defense Mechanism by Designing An Intelligent Firewall AgentDocument14 pagesNetwork Security - Attacks and Defense Mechanism by Designing An Intelligent Firewall AgentAdekogbe damilareNo ratings yet
- Risks and Threats To Storage Area Networks: Free Pass To The RSA ConferenceDocument3 pagesRisks and Threats To Storage Area Networks: Free Pass To The RSA ConferenceSrinivas GollanapalliNo ratings yet
- Selfish Jammer Detection in Multiple P2P Communication NetworksDocument7 pagesSelfish Jammer Detection in Multiple P2P Communication Networksmindworkz proNo ratings yet
- Unit - Iv 4.0: Computer NetworksDocument21 pagesUnit - Iv 4.0: Computer NetworksJit AggNo ratings yet
- NCTOC Top 5 Security Operations Center (SOC) Principles: 1) Establish A Defendable PerimeterDocument2 pagesNCTOC Top 5 Security Operations Center (SOC) Principles: 1) Establish A Defendable PerimeterBhabesh KumarNo ratings yet
- Security in Building Automation Systems: Wolfgang Granzer, Fritz Praus, and Wolfgang Kastner, Member, IEEEDocument9 pagesSecurity in Building Automation Systems: Wolfgang Granzer, Fritz Praus, and Wolfgang Kastner, Member, IEEEIqbal KosanostraNo ratings yet
- Securing Networks An in Depth Guide To FirewallsDocument11 pagesSecuring Networks An in Depth Guide To Firewallsmohokkgp396No ratings yet
- A Survey On Anomaly Detection Methods For Ad Hoc NetworksDocument9 pagesA Survey On Anomaly Detection Methods For Ad Hoc NetworksUsman TariqNo ratings yet
- Dept. of Information Science and Technology: A Paper OnDocument11 pagesDept. of Information Science and Technology: A Paper OnroseNo ratings yet
- New Modeling Technique For Detecting, Analyzing, and Mitigating Multi AttacksDocument8 pagesNew Modeling Technique For Detecting, Analyzing, and Mitigating Multi AttackserpublicationNo ratings yet
- 06 Designand Implementationofa Network Security Modelfor Cooperative NetworkDocument12 pages06 Designand Implementationofa Network Security Modelfor Cooperative NetworkMicrowork BitcoinNo ratings yet
- Pp-I Com N SecDocument11 pagesPp-I Com N SecGawrav BaishyaNo ratings yet
- Intrusion Detection Techniques: A State-of-Art: International Journal of Mobile Communications March 2016Document4 pagesIntrusion Detection Techniques: A State-of-Art: International Journal of Mobile Communications March 2016skamelNo ratings yet
- Anil 2Document29 pagesAnil 2balaji xeroxNo ratings yet
- Remote Monitoring & Control of Industrial Parameters Using EWSDocument16 pagesRemote Monitoring & Control of Industrial Parameters Using EWSbalaji xeroxNo ratings yet
- Report 11Document19 pagesReport 11balaji xeroxNo ratings yet
- Hotel Report 3Document17 pagesHotel Report 3balaji xeroxNo ratings yet
- 20 July English TestDocument4 pages20 July English Testbalaji xeroxNo ratings yet
- Santoshi Patil Pattan 11Document60 pagesSantoshi Patil Pattan 11balaji xeroxNo ratings yet
- Thesis Sewage Water TreatmentDocument31 pagesThesis Sewage Water Treatmentbalaji xeroxNo ratings yet
- Rahman Seminar 12Document17 pagesRahman Seminar 12balaji xeroxNo ratings yet
- Thesis Sewage Water TreatmentDocument31 pagesThesis Sewage Water Treatmentbalaji xeroxNo ratings yet
- Physiochemical Charecterization and Evaluation of PHDocument6 pagesPhysiochemical Charecterization and Evaluation of PHbalaji xeroxNo ratings yet
- A in Police Custody SaysDocument5 pagesA in Police Custody Saysbalaji xeroxNo ratings yet
- II Module EITDocument32 pagesII Module EITbalaji xeroxNo ratings yet
- Buda Variation5-5-23Document48 pagesBuda Variation5-5-23balaji xeroxNo ratings yet
- Presentation 1Document4 pagesPresentation 1balaji xeroxNo ratings yet
- Jyoti FDocument21 pagesJyoti Fbalaji xeroxNo ratings yet
- H.K.E Society's Poojya Doddappa Appa College of Engineering KALABURAGI - 585102Document4 pagesH.K.E Society's Poojya Doddappa Appa College of Engineering KALABURAGI - 585102balaji xeroxNo ratings yet
- English 1st LessonDocument16 pagesEnglish 1st Lessonbalaji xeroxNo ratings yet
- Vaishnavi (3vy20ba092) Cover PageDocument1 pageVaishnavi (3vy20ba092) Cover Pagebalaji xeroxNo ratings yet
- English 2nd LessonDocument19 pagesEnglish 2nd Lessonbalaji xeroxNo ratings yet
- English 1st LessonDocument16 pagesEnglish 1st Lessonbalaji xeroxNo ratings yet
- English 2nd LessonDocument19 pagesEnglish 2nd Lessonbalaji xeroxNo ratings yet
- 2Document2 pages2balaji xeroxNo ratings yet
- Robot Garbage Collector Using Wireless CommunicationDocument15 pagesRobot Garbage Collector Using Wireless Communicationbalaji xeroxNo ratings yet
- H.K.E Society's Poojya Doddappa Appa College of Engineering KALABURAGI - 585102Document22 pagesH.K.E Society's Poojya Doddappa Appa College of Engineering KALABURAGI - 585102balaji xeroxNo ratings yet
- Robot Garbage Collector Using Wireless CommunicationDocument15 pagesRobot Garbage Collector Using Wireless Communicationbalaji xeroxNo ratings yet
- 3Document1 page3balaji xeroxNo ratings yet
- A Seminar On "Industrial Internship" BY Ashish Biradar (3PD20EPE02) Under The Guidance of Dr. M.S. AspalliDocument27 pagesA Seminar On "Industrial Internship" BY Ashish Biradar (3PD20EPE02) Under The Guidance of Dr. M.S. Aspallibalaji xeroxNo ratings yet
- Document Traffic SignalDocument32 pagesDocument Traffic Signalbalaji xeroxNo ratings yet
- Pampapathi Diposit Scheme of Suko BankDocument56 pagesPampapathi Diposit Scheme of Suko Bankbalaji xeroxNo ratings yet
- Hydrographic Data Branch, Nautical Charting Division Hydrography Department Last Update: 26 February 2016Document8 pagesHydrographic Data Branch, Nautical Charting Division Hydrography Department Last Update: 26 February 2016Jerry LansanganNo ratings yet
- Installscript GtavcDocument23 pagesInstallscript Gtavcalex_4you69No ratings yet
- LPH75-MC470-P Datasheet 20221014Document4 pagesLPH75-MC470-P Datasheet 20221014purchasingNo ratings yet
- Confirm Napolcom SlipDocument2 pagesConfirm Napolcom SlipMarkjason castilloNo ratings yet
- Ark Embarked On Their VoyageDocument25 pagesArk Embarked On Their VoyageChris Cider ThompsonNo ratings yet
- A. Steps in Queuing AnalysisDocument10 pagesA. Steps in Queuing AnalysisstudentoneNo ratings yet
- Creating New Portal Display RulesDocument14 pagesCreating New Portal Display RulesAnonymous Yw2XhfXvNo ratings yet
- DP and PPDS Without SNPDocument14 pagesDP and PPDS Without SNPJagannadh BirakayalaNo ratings yet
- Solved Objective Finalterm Mega Paper by Syeda 2Document65 pagesSolved Objective Finalterm Mega Paper by Syeda 2Irshad Ullah BaigNo ratings yet
- Information Technology For ExcelDocument6 pagesInformation Technology For ExcelMark HayesNo ratings yet
- Chapter 24 MiscellaneousSystemsDocument17 pagesChapter 24 MiscellaneousSystemsMark Evan SalutinNo ratings yet
- Datasheet AMX Navigate 2021 JB05588USDocument13 pagesDatasheet AMX Navigate 2021 JB05588USmanoellocoNo ratings yet
- Forecasting With EntropyDocument19 pagesForecasting With EntropyKuntal DasNo ratings yet
- Dual WAN With Pfsense - TutorialDocument20 pagesDual WAN With Pfsense - TutorialcuvsaranNo ratings yet
- Health & Safety Procedural Manual Procedure For Internal Audits MNE/OHS/P04Document3 pagesHealth & Safety Procedural Manual Procedure For Internal Audits MNE/OHS/P04Richu PaliNo ratings yet
- CCTV Fdas Sprinkler Biometrics Access Control Web Development PabxDocument2 pagesCCTV Fdas Sprinkler Biometrics Access Control Web Development PabxKris Larine Orillo-DavisNo ratings yet
- Dcit 26 ReviewerDocument8 pagesDcit 26 ReviewerHunter KurusakiNo ratings yet
- FP-5500 Data Sheet Rev E-AlteraDocument1 pageFP-5500 Data Sheet Rev E-Alteravasece4537577No ratings yet
- CS50 PSET5 Images and FormatsDocument87 pagesCS50 PSET5 Images and FormatsX Hai HoangNo ratings yet
- Ip Telephony Voi P SystemDocument22 pagesIp Telephony Voi P SystemFreeman JacksonNo ratings yet
- Conceptos Financieros Crown PDFDocument4 pagesConceptos Financieros Crown PDFRodrigo Martinez CordobaNo ratings yet
- TR400 Tachometer ES400 Rev F 111813Document2 pagesTR400 Tachometer ES400 Rev F 111813Juan GalvesNo ratings yet
- Travel Request Form: Traveller InformationDocument1 pageTravel Request Form: Traveller InformationMohammad Nabil AbdullahNo ratings yet
- Vdocuments - MX - How To Properly Use pk3dsDocument10 pagesVdocuments - MX - How To Properly Use pk3dsDhan Dhan DhanNo ratings yet
- Verilog Dice GameDocument6 pagesVerilog Dice GameVishnu Sharma50% (2)
- Facility Location With Clustering AlgorithmDocument50 pagesFacility Location With Clustering AlgorithmDĩnh TràNo ratings yet
- Ame Relay LabDocument6 pagesAme Relay LabasegunloluNo ratings yet
- The Innovators SummaryDocument4 pagesThe Innovators SummaryTony AstroNo ratings yet
- Module 3-Lesson 4Document6 pagesModule 3-Lesson 4Kel LumawanNo ratings yet
- Easy Mikrotik HotSpot SetupDocument5 pagesEasy Mikrotik HotSpot SetupBoy EloadNo ratings yet
- Hacking Network Protocols: Complete Guide about Hacking, Scripting and Security of Computer Systems and Networks.From EverandHacking Network Protocols: Complete Guide about Hacking, Scripting and Security of Computer Systems and Networks.Rating: 5 out of 5 stars5/5 (2)
- Set Up Your Own IPsec VPN, OpenVPN and WireGuard Server: Build Your Own VPNFrom EverandSet Up Your Own IPsec VPN, OpenVPN and WireGuard Server: Build Your Own VPNRating: 5 out of 5 stars5/5 (1)
- Concise Guide to OTN optical transport networksFrom EverandConcise Guide to OTN optical transport networksRating: 4 out of 5 stars4/5 (2)
- Evaluation of Some Websites that Offer Virtual Phone Numbers for SMS Reception and Websites to Obtain Virtual Debit/Credit Cards for Online Accounts VerificationsFrom EverandEvaluation of Some Websites that Offer Virtual Phone Numbers for SMS Reception and Websites to Obtain Virtual Debit/Credit Cards for Online Accounts VerificationsRating: 5 out of 5 stars5/5 (1)
- Microsoft Azure Infrastructure Services for Architects: Designing Cloud SolutionsFrom EverandMicrosoft Azure Infrastructure Services for Architects: Designing Cloud SolutionsNo ratings yet
- AWS Certified Cloud Practitioner Study Guide: CLF-C01 ExamFrom EverandAWS Certified Cloud Practitioner Study Guide: CLF-C01 ExamRating: 5 out of 5 stars5/5 (1)
- The Compete Ccna 200-301 Study Guide: Network Engineering EditionFrom EverandThe Compete Ccna 200-301 Study Guide: Network Engineering EditionRating: 5 out of 5 stars5/5 (4)
- PHP BLUEPRINT: An Essential Beginners Guide to Learn the Realms of PHP From A-ZFrom EverandPHP BLUEPRINT: An Essential Beginners Guide to Learn the Realms of PHP From A-ZNo ratings yet
- Alcatel-Lucent Service Routing Architect (SRA) Self-Study Guide: Preparing for the BGP, VPRN and Multicast ExamsFrom EverandAlcatel-Lucent Service Routing Architect (SRA) Self-Study Guide: Preparing for the BGP, VPRN and Multicast ExamsNo ratings yet
- Designing and Building Security Operations CenterFrom EverandDesigning and Building Security Operations CenterRating: 3 out of 5 stars3/5 (3)
- Computer Systems and Networking Guide: A Complete Guide to the Basic Concepts in Computer Systems, Networking, IP Subnetting and Network SecurityFrom EverandComputer Systems and Networking Guide: A Complete Guide to the Basic Concepts in Computer Systems, Networking, IP Subnetting and Network SecurityRating: 4.5 out of 5 stars4.5/5 (13)
- Mastering Linux Security and Hardening - Second Edition: Protect your Linux systems from intruders, malware attacks, and other cyber threats, 2nd EditionFrom EverandMastering Linux Security and Hardening - Second Edition: Protect your Linux systems from intruders, malware attacks, and other cyber threats, 2nd EditionNo ratings yet
- Software-Defined Networks: A Systems ApproachFrom EverandSoftware-Defined Networks: A Systems ApproachRating: 5 out of 5 stars5/5 (1)
- AWS Certified Solutions Architect Study Guide: Associate SAA-C02 ExamFrom EverandAWS Certified Solutions Architect Study Guide: Associate SAA-C02 ExamNo ratings yet
- FTTx Networks: Technology Implementation and OperationFrom EverandFTTx Networks: Technology Implementation and OperationRating: 5 out of 5 stars5/5 (1)
- Computer Networking: The Complete Guide to Understanding Wireless Technology, Network Security, Computer Architecture and Communications Systems (Including Cisco, CCNA and CCENT)From EverandComputer Networking: The Complete Guide to Understanding Wireless Technology, Network Security, Computer Architecture and Communications Systems (Including Cisco, CCNA and CCENT)No ratings yet
- ITIL 4: Digital and IT strategy: Reference and study guideFrom EverandITIL 4: Digital and IT strategy: Reference and study guideRating: 5 out of 5 stars5/5 (1)