Professional Documents
Culture Documents
Module-01 CN Search Creators Hanumanthu
Uploaded by
daliodsouza222222Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Module-01 CN Search Creators Hanumanthu
Uploaded by
daliodsouza222222Copyright:
Available Formats
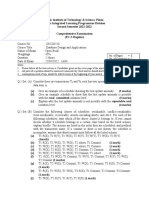
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
Course: Computer Networks
Course Code: 21CS52
Module-01
Introduction to Networks | Physical Layer
Syllabus
Chapter-01: Introduction to networks: Network hardware, Network software, Reference
models,
Chapter-02: Physical Layer: Guided transmission media, Wireless transmission
Chapter-01
Introduction to networks
• “A computer network is a group of computers linked to each other that enables the
computer to communicate with another computer and share their resources, data, and
applications... “
• The aim of the computer network is the sharing of resources among various devices.
• In the case of computer network technology, there are several types of networks that vary
from simple to complex level.
Search Creators... Page 1
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
Major components of a computer network are
NIC (National interface card)
• NIC is a device that helps the computer to communicate with another device.
• The network interface card contains the hardware addresses, the data-link layer protocol
uses this address to identify the system on the network so that it transfers the data to the
correct destination.
There are two types of NIC: wireless NIC and wired NIC.
• Wireless NIC: All the modern laptops use the wireless NIC. In Wireless NIC, a connection
is made using the antenna that employs the radio wave technology.
• Wired NIC: Cables use the wired NIC to transfer the data over the medium.
Hub
• Hub is a central device that splits the network connection into multiple devices. When
computer requests for information from a computer, it sends the request to the Hub. Hub
distributes this request to all the interconnected computers.
Switches
• Switch is a networking device that groups all the devices over the network to transfer the
data to another device.
• A switch is better than Hub as it does not broadcast the message over the network, i.e., it
sends the message to the device for which it belongs to.
• Therefore, we can say that switch sends the message directly from source to the destination.
Search Creators... Page 2
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
Cables and connectors
Cable is a transmission media that transmits the communication signals. There are three types of
cables:
• Twisted pair cable: It is a high-speed cable that transmits the data over 1Gbps or more.
• Coaxial cable: Coaxial cable resembles like a TV installation cable. Coaxial cable is more
expensive than twisted pair cable, but it provides the high data transmission speed.
• Fibre optic cable: Fibre optic cable is a high-speed cable that transmits the data using light
beams. It provides high data transmission speed as compared to other cables. It is more
expensive as compared to other cables, so it is installed at the government level.
Router
• Router is a device that connects the LAN to the internet.
• The router is mainly used to connect the distinct networks or connect the internet to
multiple computers.
Modem
• Modem connects the computer to the internet over the existing telephone line. A modem
is not integrated with the computer motherboard.
• A modem is a separate part on the PC slot found on the motherboard.
Uses Of Computer Network
• Resource sharing Server-Client model
• Communication medium
• E-commerce
Search Creators... Page 3
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
Network Hardware
• A computer network can be categorized by their size.
A computer network is mainly of four types:
1. LAN (Local Area Network)
2. PAN (Personal Area Network)
3. MAN (Metropolitan Area Network)
4. WAN (Wide Area Network)
LAN (Local Area Network)
• Local Area Network is a group of computers connected to each other in a small area such
as building, office.
• LAN is used for connecting two or more personal computers through a communication
medium such as twisted pair, coaxial cable, etc.
• It is less costly as it is built with inexpensive hardware such as hubs, network adapters, and
ethernet cables.
• The data is transferred at an extremely faster rate in Local Area Network.
• Local Area Network provides higher security.
Search Creators... Page 4
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
PAN (Personal Area Network)
• Personal Area Network is a network arranged within an individual person, typically
within a range of 10 meters.
• Personal Area Network is used for connecting the computer devices of personal use
is known as Personal Area Network.
• Thomas Zimmerman was the first research scientist to bring the idea of the Personal
Area Network.
• Personal Area Network covers an area of 30 feet.
• Personal computer devices that are used to develop the personal area network are
the laptop, mobile phones, media player and play stations.
Search Creators... Page 5
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
Examples Of Personal Area Network:
• Body Area Network: Body Area Network is a network that moves with a person. For
example, a mobile network moves with a person. Suppose a person establishes a network
connection and then creates a connection with another device to share the information.
• Offline Network: An offline network can be created inside the home, so it is also known
as a home network. A home network is designed to integrate the devices such as printers,
computer, television but they are not connected to the internet.
• Small Home Office: It is used to connect a variety of devices to the internet and to a
corporate network using a VPN.
MAN (Metropolitan Area Network)
• A metropolitan area network is a network that covers a larger geographic area by
interconnecting a different LAN to form a larger network.
• Government agencies use MAN to connect to the citizens and private industries.
• In MAN, various LANs are connected to each other through a telephone exchange line.
• The most widely used protocols in MAN are RS-232, Frame Relay, ATM, ISDN, OC-3,
ADSL, etc.
Search Creators... Page 6
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
• It has a higher range than Local Area Network (LAN).
Uses Of Metropolitan Area Network:
• MAN is used in communication between the banks in a city.
• It can be used in an Airline Reservation.
• It can be used in a college within a city.
• It can also be used for communication in the military.
WAN (Wide Area Network)
• A Wide Area Network is a network that extends over a large geographical area such as
states or countries.
• A Wide Area Network is quite bigger network than the LAN.
• A Wide Area Network is not limited to a single location, but it spans over a large
geographical area through a telephone line, fibre optic cable or satellite links.
• The internet is one of the biggest WAN in the world.
• A Wide Area Network is widely used in the field of Business, government, and education.
Search Creators... Page 7
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
Examples Of Wide Area Network:
• Mobile Broadband: A 4G network is widely used across a region or country.
• Last mile: A telecom company is used to provide the internet services to the customers in
hundreds of cities by connecting their home with fiber.
• Private network: A bank provides a private network that connects the 44 offices. This
network is made by using the telephone leased line provided by the telecom company.
Internetwork
• An internetwork is defined as two or more computer network LANs or WAN or computer
network segments are connected using devices, and they are configured by a local
addressing scheme. This process is known as internetworking.
• An interconnection between public, private, commercial, industrial, or government
computer networks can also be defined as internetworking.
• An internetworking uses the internet protocol.
• The reference model used for internetworking is Open System Interconnection (OSI).
Search Creators... Page 8
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
NETWORK SOFTWARE
Protocol Hierarchies
• To reduce their design complexity, most networks are organized as a stack of layers or
levels, each one built upon the one below it.
• The number of layers, the name of each layer, the contents of each layer, and the function
of each layer differ from network to network.
• The purpose of each layer is to offer certain services to the higher layers while shielding
those layers from the details of how the offered services are actually implemented.
• When layer n on one machine carries on a conversation with layer n on another machine,
the rules and conventions used in this conversation are collectively known as the layer n
protocol.
• Basically, a protocol is an agreement between the communicating parties on how
communication is to proceed.
• A five-layer network is illustrated in Fig
• the entities comprising the corresponding layers on different machines are called peers.
• The peers may be software processes, hardware devices, or even human being.
Search Creators... Page 9
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
• Below layer 1 is the physical medium through which actual communication occurs.
• virtual communication is shown by dotted lines and physical communication by solid
lines.
• Between each pair of adjacent layers is an interface.
• A set of layers and protocols is called a network architecture.
• A list of the protocols used by a certain system, one protocol per layer, is called a
protocol stack.
Search Creators... Page 10
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
• In this example, M is split into two parts, M 1 and M 2 , that will be transmitted
separately.
• Layer 3 decides which of the outgoing lines to use and passes the packets to layer 2.
• Layer 2 adds to each piece not only a header but also a trailer, and gives the resulting
unit to layer 1 for physical transmission.
Search Creators... Page 11
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
Design Issues for the Layers
Reliability
• Network channels and components may be unreliable, resulting in loss of bits while data
transfer.
Scalability
• Networks are continuously evolving. The sizes are continually increasing leading to
congestion.
Addressing
• At a particular time, innumerable messages are being transferred between large numbers
of computers.
Error Control
• Unreliable channels introduce a number of errors in the data streams that are
communicated.
Flow Control
• If the rate at which data is produced by the sender is higher than the rate at which data is
received by the receiver, there are chances of overflowing the receiver.
• So, a proper flow control mechanism needs to be implemented.
Search Creators... Page 12
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
Resource Allocation
• Computer networks provide services in the form of network resources to the end users.
• The main design issue is to allocate and deallocate resources to processes.
• The allocation/deallocation should occur so that minimal interference among the hosts
occurs and there is optimal usage of the resources.
Statistical Multiplexing
• It is not feasible to allocate a dedicated path for each message while it is being transferred
from the source to the destination.
• So, the data channel needs to be multiplexed, so as to allocate a fraction of the bandwidth
or time to each host.
Routing
• There may be multiple paths from the source to the destination. Routing involves choosing
an optimal path among all possible paths, in terms of cost and time.
• There are several routing algorithms that are used in network systems.
Security
• A major factor of data communication is to defend it against threats like eavesdropping
and surreptitious alteration of messages.
• So, there should be adequate mechanisms to prevent unauthorized access to data through
authentication and cryptography.
Search Creators... Page 13
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
Connection-Oriented Versus Connectionless Service
Search Creators... Page 14
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
Service Primitives
• A service is formally specified by a set of primitives (operations) available to user
processes to access the service.
The Relationship of Services to Protocols
• A protocol, in contrast, is a set of rules governing the format and meaning of the packets,
or messages that are exchanged by the peer entities within a layer.
• Entities use protocols to implement their service definitions.
Search Creators... Page 15
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
REFERENCE MODELS
The OSI Reference Model
• The model is called the ISO OSI (Open Systems Interconnection) Reference Model
because it deals with connecting open system that is, systems that are open for
communication with other systems.
• OSI stands for Open System Interconnection is a reference model that describes how
information from a software application in one computer moves through a physical
medium to the software application in another computer.
• OSI consists of seven layers, and each layer performs a particular network function.
• OSI model was developed by the International Organization for Standardization (ISO) in
1984, and it is now considered as an architectural model for the inter-computer
communications.
Search Creators... Page 16
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
7 Layers of OSI Model
There are the seven OSI layers. Each layer has different functions. A list of seven layers are
given below
1. Physical Layer
2. Data-Link Layer
3. Network Layer
4. Transport Layer
5. Session Layer
6. Presentation Layer
7. Application Layer
Search Creators... Page 17
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
1. Physical layer
• The physical layer is concerned with transmitting raw bits over a communication channel.
The main functionality of the physical layer is to transmit the individual bits from one node
to another node.
• It is the lowest layer of the OSI model.
• It establishes, maintains and deactivates the physical connection.
• It specifies the mechanical, electrical and procedural network interface specifications.
2. The Data Link Layer
• This layer is responsible for the error-free transfer of data frames.
• It defines the format of the data on the network.
• It provides a reliable and efficient communication between two or more devices.
• It is mainly responsible for the unique identification of each device that resides on a local
network.
3. The Network Layer
• It is a layer 3 that manages device addressing, tracks the location of devices on the
network.
• It determines the best path to move data from source to the destination based on the
network conditions, the priority of service, and other factors.
• The Data link layer is responsible for routing and forwarding the packets.
• Routers are the layer 3 devices, they are specified in this layer and used to provide the
routing services within an internetwork.
• The protocols used to route the network traffic are known as Network layer protocols.
Examples of protocols are IP and Ipv6.
Search Creators... Page 18
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
4. The Transport Layer
• The Transport layer is a Layer 4 ensures that messages are transmitted in the order in
which they are sent and there is no duplication of data.
• The main responsibility of the transport layer is to transfer the data completely.
• It receives the data from the upper layer and converts them into smaller units known as
segments.
• This layer can be termed as an end-to-end layer as it provides a point-to-point
connection between source and destination to deliver the data reliably.
5. The Session Layer
• It is a layer 3 in the OSI model.
• The Session layer is used to establish, maintain and synchronizes the interaction
between communicating devices.
6. The Presentation Layer
• A Presentation layer is mainly concerned with the syntax and semantics of the
information exchanged between the two systems.
• It acts as a data translator for a network.
• This layer is a part of the operating system that converts the data from one presentation
format to another format.
• The Presentation layer is also known as the syntax layer.
7. The Application Layer
• An application layer serves as a window for users and application processes to access
network service.
• It handles issues such as network transparency, resource allocation, etc.
• An application layer is not an application, but it performs the application layer
functions.
• This layer provides the network services to the end-users.
Search Creators... Page 19
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
The TCP/IP Reference Model
• The TCP/IP model was developed prior to the OSI model.
• The TCP/IP model is not exactly similar to the OSI model.
• The TCP/IP model consists of five layers: the application layer, transport layer, network
layer, data link layer and physical layer.
• The first four layers provide physical standards, network interface, internetworking, and
transport functions that correspond to the first four layers of the OSI model and these four
layers are represented in TCP/IP model by a single layer called the application layer.
• TCP/IP is a hierarchical protocol made up of interactive modules, and each of them
provides specific functionality.
The Link Layer
• The lowest layer in the model, the link layer describes what links such as serial lines and
classic Ethernet must do to meet the needs of this connectionless internet layer.
• It is not really a layer at all, in the normal sense of the term, but rather an interface between
hosts and transmission links.
Search Creators... Page 20
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
Internet Layer
• An internet layer is the second layer of the TCP/IP model.
• An internet layer is also known as the network layer.
• The main responsibility of the internet layer is to send the packets from any network,
and they arrive at the destination irrespective of the route they take.
Transport Layer
The transport layer is responsible for the reliability, flow control, and correction of data which is
being sent over the network.
The two protocols used in the transport layer are User Datagram protocol and Transmission control
protocol.
User Datagram Protocol (UDP)
• It provides connectionless service and end-to-end delivery of transmission.
• It is an unreliable protocol as it discovers the errors but not specify the error.
• User Datagram Protocol discovers the error, and ICMP protocol reports the error to the
sender that user datagram has been damaged.
UDP consists of the following fields:
• Source port address: The source port address is the address of the application program
that has created the message.
• Destination port address: The destination port address is the address of the application
program that receives the message.
• Total length: It defines the total number of bytes of the user datagram in bytes.
• Checksum: The checksum is a 16-bit field used in error detection.
Search Creators... Page 21
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
• UDP does not specify which packet is lost. UDP contains only checksum; it does not
contain any ID of a data segment.
Transmission Control Protocol (TCP)
• It provides a full transport layer services to applications.
• It creates a virtual circuit between the sender and receiver, and it is active for the duration
of the transmission.
• TCP is a reliable protocol as it detects the error and retransmits the damaged frames.
Therefore, it ensures all the segments must be received and acknowledged before the
transmission is considered to be completed and a virtual circuit is discarded.
• At the sending end, TCP divides the whole message into smaller units known as segment,
and each segment contains a sequence number which is required for reordering the frames
to form an original message.
• At the receiving end, TCP collects all the segments and reorders them based on sequence
numbers.
Application Layer
• An application layer is the topmost layer in the TCP/IP model.
• It is responsible for handling high-level protocols, issues of representation.
• This layer allows the user to interact with the application.
• When one application layer protocol wants to communicate with another application layer,
it forwards its data to the transport layer.
• There is an ambiguity occurs in the application layer. Every application cannot be placed
inside the application layer except those who interact with the communication system. For
example: text editor cannot be considered in application layer while web browser using
HTTP protocol to interact with the network where HTTP protocol is an application layer
protocol.
Search Creators... Page 22
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
A Comparison of the OSI and TCP/IP Reference Models
Search Creators... Page 23
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
A Critique of the OSI Model and Protocols
1. Bad timing.
2. Bad technology.
3. Bad implementations.
4. Bad politics.
1. Bad Timing
• it is essential that the standards be written in the trough in between the two
‘‘elephants.’’
• they are written too late, so many companies may have already made major
investments in different ways of doing things that the standards are effectively
ignored.
Search Creators... Page 24
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
2. Bad technology.
• The second reason that OSI never caught on is that both the model and the protocols
are flawed.
• The choice of seven layers was more political than technical, and two of the layers
(session and presentation) are nearly empty, whereas two other ones (data link and
network) are overfull.
3. Bad Implementations
• In contrast, one of the first implementations of TCP/IP was part of Berkeley UNIX
and was quite good (not to mention, free).
• People began using it quickly, which led to a large user community, which led to
improvements, which led to an even larger community.
4. Bad Politics
• OSI, on the other hand, was widely thought to be the creature of the European
telecommunication ministries, the European Community, and later the U.S.
Government.
A Critique of the TCP/IP Reference Model
• The TCP/IP model and protocols have their problems too.
• First, the model does not clearly distinguish the concepts of services, interfaces, and
protocols good software engineering practice requires differentiating between the
specification and the implementation, something that OSI does very carefully, but
TCP/IP does not.
• Consequently, the TCP/IP model is not much of a guide for designing new networks
using new technologies.
• Second, the TCP/IP model is not at all general and is poorly suited to describing any
protocol stack other than TCP/IP.
• Trying to use the TCP/IP model to describe Bluetooth, for example, is completely
impossible.
Search Creators... Page 25
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
Chapter-02
Physical Layer
• The physical layer is the first and lowest layer from the bottom of the 7-layered OSI
model and delivers security to hardware.
• This layer is in charge of data transmission over the physical medium. It is the most
complex layer in the OSI model.
• The physical layer converts the data frame received from the data link layer into bits, i.e.,
in terms of ones and zeros.
• It maintains the data quality by implementing the required protocols on different network
modes and maintaining the bit rate through data transfer using a wired or wireless
medium.
THE THEORETICAL BASIS FOR DATA COMMUNICATION
• Information can be transmitted on wires by varying some physical property such as
voltage or current.
• By representing the value of this voltage or current as a single-valued function of time,
f(t), we can model the behaviour of the signal and analyze it mathematically.
Fourier Analysis
where f = 1/T is the fundamental frequency, an and bn are the sine and cosine amplitudes of the
nth harmonics (terms), and c is a constant. Such a decomposition is called a Fourier series.
Search Creators... Page 26
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
Bandwidth-Limited Signals
• The width of the frequency range transmitted without being strongly attenuated is called
the bandwidth.
• Signals that run from 0 up to a maximum frequency are called baseband signals.
• Signals that are shifted to occupy a higher range of frequencies, as is the case for all
wireless transmissions, are called passband signals.
Search Creators... Page 27
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
The Maximum Data Rate of a Channel
• Data rate refers to the speed of data transfer through a channel.
• It is generally computed in bits per second (bps).
• Higher data rates are expressed as Kbps ("Kilo" bits per second, i.e.1000 bps), Mbps
("Mega" bits per second, i.e.1000 Kbps), Gbps ("Giga" bits per second, i.e. 1000 Mbps)
and Tbps ("Tera" bits per second, i.e. 1000 Gbps).
One of the main objectives of data communications is to increase the data rate.
There are three factors that determine the data rate of a channel:
1. Bandwidth of the channel
2. Number of levels of signals that are used
3. Noise present in the channel
Data rate can be calculated using two theoretical formulae:
1. Nyquist Bit Rate – for noiseless channel
2. Shannon’s Capacity – for noisy channel
Nyquist Bit Rate
Nyquist bit rate was developed by Henry Nyquist who proved that the transmission capacity of
even a perfect channel with no noise has a maximum limit.
Search Creators... Page 28
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
The theoretical formula for the maximum bit rate is:
maximum bit rate = 2 × Bandwidth × log2V
Here, maximum bit rate is calculated in bps
Bandwidth is the bandwidth of the channel
V is the number of discrete levels in the signal
For example, if there is a noiseless channel with a bandwidth of 4 KHz that is transmitting a
signal with 4 discrete levels, then the maximum bit rate will be computed as, maximum bit rate
= 2 × 4000 × log24 = 16,000 bps = 16 kbps
Shannon's Capacity
Claude Shannon extended Nyquist's work for actual channels that are subject to noise.
Signal-to-Noise Ratio, SNR = Average Signal Power/Average Noise Power
Since SNR is the ratio of two powers that varies over a very large range, it is often expressed in
decibels, called SNRdb and calculated as: SNRdb = 10log10SNR.
Shannon's Capacity gives the theoretical maximum data rate or capacity of a noisy channel. It is
expressed as:
Capacity = Bandwidth × log2(1+SNR)
Here, Capacity is the maximum data rate of the channel in bps
Bandwidth is the bandwidth of the channel
SNR is the signal – to – noise ratio
For example, if the bandwidth of a noisy channel is 4 KHz, and the signal to noise ratio is 100,
then the maximum bit rate can be computed as:
Capacity = 4000 × log2(1+100) = 26,633 bps = 26.63 kbps
Search Creators... Page 29
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
GUIDED TRANSMISSION MEDIA
Media are roughly grouped into guided media, such as copper wire and fiber optics, and
unguided media, such as terrestrial wireless, satellite, and lasers through the air.
Magnetic Media
• One of the most convenient ways to transfer data from one computer to another, even
before the birth of networking, was to save it on some storage media and transfer physical
from one station to another.
• Though it may seem old-fashion way in today’s world of high-speed internet, but when
the size of data is huge, the magnetic media comes into play.
• For example, a bank has to handle and transfer huge data of its customer, which stores a
backup of it at some geographically far-away place for security reasons and to keep it
from uncertain calamities.
Twisted Pairs
• Twisted pair is a physical media made up of a pair of cables twisted with each other. A
twisted pair cable is cheap as compared to other transmission media.
• Installation of the twisted pair cable is easy, and it is a lightweight cable. The frequency
range for twisted pair cable is from 0 to 3.5KHz.
• A twisted pair consists of two insulated copper wires arranged in a regular spiral pattern.
Search Creators... Page 30
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
Unshielded Twisted Pair:
An unshielded twisted pair is widely used in telecommunication. Following are the
categories of the unshielded twisted pair cable:
Category 1: Category 1 is used for telephone lines that have low-speed data.
Category 2: It can support upto 4Mbps.
Category 3: It can support upto 16Mbps.
Category 4: It can support upto 20Mbps. Therefore, it can be used for long-distance
communication.
Category 5: It can support upto 200Mbps.
Advantages Of Unshielded Twisted Pair:
• It is cheap.
• Installation of the unshielded twisted pair is easy.
• It can be used for high-speed LAN.
Disadvantage:
• This cable can only be used for shorter distances because of attenuation.
Shielded Twisted Pair
A shielded twisted pair is a cable that contains the mesh surrounding the wire that allows the
higher transmission rate.
Characteristics Of Shielded Twisted Pair:
• The cost of the shielded twisted pair cable is not very high and not very low.
• An installation of STP is easy.
• It has higher capacity as compared to unshielded twisted pair cable.
• It has a higher attenuation.
• It is shielded that provides the higher data transmission rate.
Search Creators... Page 31
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
Disadvantages
• It is more expensive as compared to UTP and coaxial cable.
• It has a higher attenuation rate.
Coaxial Cable
• Coaxial cable is very commonly used transmission media, for example, TV wire is
usually a coaxial cable.
• The name of the cable is coaxial as it contains two conductors parallel to each other.
• It has a higher frequency as compared to Twisted pair cable.
• The inner conductor of the coaxial cable is made up of copper, and the outer conductor is
made up of copper mesh. The middle core is made up of non-conductive cover that
separates the inner conductor from the outer conductor.
• The middle core is responsible for the data transferring whereas the copper mesh prevents
from the EMI (Electromagnetic interference).
Coaxial cable is of two types:
• Baseband transmission: It is defined as the process of transmitting a single signal at high
speed.
• Broadband transmission: It is defined as the process of transmitting multiple signals
simultaneously.
Search Creators... Page 32
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
Advantages Of Coaxial cable:
• The data can be transmitted at high speed.
• It has better shielding as compared to twisted pair cable.
• It provides higher bandwidth.
Disadvantages Of Coaxial cable:
• It is more expensive as compared to twisted pair cable.
• If any fault occurs in the cable causes the failure in the entire network.
Power Lines
• Power line communications (PLC) allows data communications over conductors that are
simultaneously used for transmission of electrical power.
• PLCs work by adding a modulated carrier signal, formed by superimposing data signal
over low frequency power signal. Electrical signals transmit at 50 – 60 Hz, while the data
signals transmit in the order of MHz.
• PLCs are also known as power line carrier, power line digital subscriber line (PDSL), or
power line networking (PLN).
Search Creators... Page 33
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
Fibre Optic
• Fibre optic cable is a cable that uses electrical signals for communication.
• Fibre optic is a cable that holds the optical fibres coated in plastic that are used to send
the data by pulses of light.
• The plastic coating protects the optical fibres from heat, cold, electromagnetic
interference from other types of wiring.
• Fibre optics provide faster data transmission than copper wires.
Basic elements of Fibre optic cable:
• Core: The optical fibre consists of a narrow strand of glass or plastic known as a core. A
core is a light transmission area of the fibre. The more the area of the core, the more light
will be transmitted into the fibre.
• Cladding: The concentric layer of glass is known as cladding. The main functionality of
the cladding is to provide the lower refractive index at the core interface as to cause the
reflection within the core so that the light waves are transmitted through the fibre.
• Jacket: The protective coating consisting of plastic is known as a jacket. The main
purpose of a jacket is to preserve the fibre strength, absorb shock and extra fibre
protection.
Search Creators... Page 34
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
Fiber Cables
• Fiber optic cables are similar to coax, except without the braid.
• Figure shows a single fiber viewed from the side.
• At the center is the glass core through which the light propagates. In multimode fibers,
the core is typically 50 microns in diameter, about the thickness of a human hair.
• In single-mode fibers, the core is 8 to 10 microns.
Search Creators... Page 35
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
Comparison of Fiber Optics and Copper Wire
Search Creators... Page 36
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
WIRELESS TRANSMISSION
The Electromagnetic Spectrum
• The electromagnetic spectrum is the entire range of electromagnetic radiation according
to the wavelength or frequencies.
• It has a range of frequencies from 1Hz to Hz. The waves in order of increasing
frequencies are radio waves, microwaves, infrared rays, visible light, UV rays, X-rays
and gamma rays.
• Among these range, the frequencies between Hz to Hz are used for communication.
• A second form of spread spectrum, direct sequence spread spectrum, uses a code
sequence to spread the data signal over a wider frequency band.
• These signals can be given different codes, a method called CDMA (Code Division
Multiple Access)
Search Creators... Page 37
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
• A third method of communication with a wider band is UWB (Ultra-WideBand)
communication. UWB sends a series of rapid pulses, varying their positions to
communicate information.
• The rapid transitions lead to a signal that is spread thinly over a very wide frequency
band.
• UWB is defined as signals that have a bandwidth of at least 500 MHz or at least 20% of
the center frequency of their frequency band.
Radio Transmission
• In the electromagnetic spectrum, all omnidirectional waves in the frequencies 3KHz to
1GHz are called radio waves.
• They are widely used for communications since they are easy to generate, can travel long
distances and can penetrate buildings.
• Radio waves have omnidirectional antennas, i.e. antennas that can send signals in all
directions.
• The properties of radios waves vary according to their frequencies. However, radio waves
at all frequencies are prone to interference from electrical equipments like motors etc.
Low and Medium Frequency Radio Waves
• Low and medium frequency radio waves can pass through obstacles and have ground
propagation. However, the power diminishes rapidly depending upon the distance from
the source. This attenuation in power is called the path loss. AM radio uses LF and MF
bands.
Search Creators... Page 38
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
High Frequency Radio Waves
• High frequency radio waves travel in straight lines and have sky propagation. However,
they are affected by interferences and are affected by rains. The military communicates in
the HF and VHF bands. They are also used for long distance broadcasting and FM radio.
Microwave Transmission
• In the electromagnetic spectrum, waves within the frequencies 1GHz to 300GHz are called
microwaves.
• Microwaves travel in straight lines, and so the transmitter and receiver stations should be
accurately aligned to each other.
• Microwave propagation is line – of – sight propagation. So, towers hoisting the stations
should be placed so that the curvature of the earth or any other obstacle does not interfere
with the communication.
• Since it is unidirectional, it allows multiple receivers in a row to receive the signals without
interference.
• Microwaves do not pass through buildings. So, indoor receivers cannot be used effectively.
• Microwaves are often refracted by the atmospheric layers. The refracted rays take longer
time to reach the destination than the direct rays. This causes out of phase transmission,
called multipath fading.
Search Creators... Page 39
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
The Politics of the Electromagnetic Spectrum
• To prevent total chaos, there are national and international agreements about who gets
to use which frequencies.
• Since everyone wants a higher data rate, everyone wants more spectrum.
Infrared Transmission
• The electromagnetic waves having frequencies from 300 GHz to 400 THz (wavelengths
from 1mm to 770 nm) are referred to as infrared (IR) waves. IR uses line-of-sight
propagation.
• Infrared light is a transmission channel whose features are necessarily different from those
of the radio frequencies. A fundamental property of infrared light is that it cannot penetrate
the walls. This represents that it can easily include it within a room.
• Another advantage of infrared communication is massive bandwidth which is available for
use, but has not been exploited to its full extent.
Search Creators... Page 40
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
Light Transmission
Electromagnetic waves within the frequency range of 400 THz – 790 THz are detected by the
human eye. Light transmission is line of sight propagation and is blocked by obstacles.
Laser Signals
• Optical signalling can be obtained by laser signals. For example, the LANs in two buildings
can be connected by installing laser signalling system on the rooftops.
• Laser rays are unidirectional. So, both the transmitter and the receiver need perfectly
aligned photo-emitter and photo-detector.
Visual Light Communication
• A more used variant of light transmission is visual light communication (VLC). VLC refers
to data communication using visible spectrum of the light.
• It is part of optical wireless communication, which refers to data communication using
infrared, visible and ultraviolet lights.
• VLC uses florescent lamps or LEDs to generate optical signals. The signals are received
by photodiodes.
Application
• Communication using light signals is safe for eyes and cost effective. Also, it does not
require any license for usage.
• So, it is increasingly being used for ubiquitous computing and IoT systems.
Search Creators... Page 41
21CS52 | COMPUTER NETWORKS | SEARCH CREATORS.
Search Creators... Page 42
You might also like
- 1 1Document35 pages1 1tafadzwa sidNo ratings yet
- Basic Networking: Introduction To Computing Unit 5Document25 pagesBasic Networking: Introduction To Computing Unit 5AbdulRehman AamirNo ratings yet
- IntroductionDocument48 pagesIntroductionRanjan DwivediNo ratings yet
- NETWORK DESIGNDocument37 pagesNETWORK DESIGNjackstone saitotiNo ratings yet
- Chapter 3 Introdaction of NetworkDocument50 pagesChapter 3 Introdaction of NetworkFiliphos EyoelNo ratings yet
- Lesson 1 - Introduction To Network DesignDocument37 pagesLesson 1 - Introduction To Network Designvictor.wachira2022No ratings yet
- Networking Components and ModelsDocument40 pagesNetworking Components and ModelsGOHIL AJAYKUMAR SHANKARBHAINo ratings yet
- revesionDocument31 pagesrevesionbiruk mollaNo ratings yet
- Understanding Network Fundamentals - 1Document42 pagesUnderstanding Network Fundamentals - 1huge502No ratings yet
- Introduction To CN-2Document88 pagesIntroduction To CN-2Jkiu MeluiNo ratings yet
- Wa0008Document20 pagesWa0008pr1746702No ratings yet
- Computer Communication Network: M.T.Hasan Department of Electronics and TelecommunicationDocument271 pagesComputer Communication Network: M.T.Hasan Department of Electronics and TelecommunicationRAJESHNo ratings yet
- 6tirupati Computer Communication NetworkDocument72 pages6tirupati Computer Communication Networkmohitnajkani786No ratings yet
- 02 Introduction To Computer Networking TechnologyDocument25 pages02 Introduction To Computer Networking TechnologyEthiopian CodeNo ratings yet
- Lesson - 1: Introduction To Computer Networks and Data CommunicationsDocument40 pagesLesson - 1: Introduction To Computer Networks and Data CommunicationsMaccryNo ratings yet
- Module5Document6 pagesModule5Diestro Lyka Mae L.No ratings yet
- LESSON 1-Networking ConceptsDocument50 pagesLESSON 1-Networking ConceptsKirtiNo ratings yet
- Classifications of NetworksDocument24 pagesClassifications of NetworksLyka LinezoNo ratings yet
- CS-106 Introduction to IT: Network TypesDocument72 pagesCS-106 Introduction to IT: Network TypesAbdullah ShahzadNo ratings yet
- Introduction to Computer Network UnitDocument409 pagesIntroduction to Computer Network UnitKarina Rathore100% (1)
- Types of Computer Networks ExplainedDocument28 pagesTypes of Computer Networks ExplainedSyed MuneebNo ratings yet
- Chapter 2 - NetworkingDocument12 pagesChapter 2 - NetworkingkaushikarubasingheNo ratings yet
- ITE I Networking FundamentalsDocument64 pagesITE I Networking Fundamentalsapi-3722006No ratings yet
- Chapter 1 2022Document160 pagesChapter 1 2022adityadas.657No ratings yet
- Computer NetworksDocument99 pagesComputer Networksanju chauhanNo ratings yet
- CC Unit1 PPTDocument156 pagesCC Unit1 PPTdio rastongiNo ratings yet
- UNIT 3 Notes For Students - 2Document49 pagesUNIT 3 Notes For Students - 2deepesh_gaonkarNo ratings yet
- Unit 2: Telecommunication and Networks: Telecommunications MediaDocument45 pagesUnit 2: Telecommunication and Networks: Telecommunications MediaDivyam DiviNo ratings yet
- LO 01 Introduction To Computer Networking EditedDocument63 pagesLO 01 Introduction To Computer Networking EditedIsrael EyasuNo ratings yet
- Set Up Computer NetworksDocument11 pagesSet Up Computer NetworksNoelyn GarciaNo ratings yet
- CN IntroductionDocument73 pagesCN Introductionpatela1No ratings yet
- Lecture 7 23-24Document29 pagesLecture 7 23-24Bekzat SagyndykovNo ratings yet
- Basic Networking Concepts Explained: LANs, WANs, the Internet, Network Addressing & MoreDocument35 pagesBasic Networking Concepts Explained: LANs, WANs, the Internet, Network Addressing & MoreJanice BrownNo ratings yet
- Computer NetworksDocument23 pagesComputer Networkszorara533No ratings yet
- Computer Communication Unit 1Document103 pagesComputer Communication Unit 1SHASHANK .KOMMINENI (RA2111030010233)No ratings yet
- Network: M. Haikal Karana Sitepu, ST, M.Eng, PH.DDocument28 pagesNetwork: M. Haikal Karana Sitepu, ST, M.Eng, PH.DmentariNo ratings yet
- COMPUTER NETWORK PROJECT REPORTDocument15 pagesCOMPUTER NETWORK PROJECT REPORTImranNo ratings yet
- Computer Communications Course OverviewDocument137 pagesComputer Communications Course OverviewSai Rohit PaturiNo ratings yet
- Chapter 1 Data Communications and Computer NetworksDocument28 pagesChapter 1 Data Communications and Computer NetworkstesfuNo ratings yet
- CHAPTER 2 Network BasicsDocument50 pagesCHAPTER 2 Network BasicsAbel GulilatNo ratings yet
- Report Computer NetworkingDocument45 pagesReport Computer NetworkingTayab AbdelrhimNo ratings yet
- Chapter 01 Computer Networks and The InternetDocument90 pagesChapter 01 Computer Networks and The Internetgaucon12007No ratings yet
- Live Crash Course Computer - Awareness - 4Document31 pagesLive Crash Course Computer - Awareness - 4Gaming MasterNo ratings yet
- Introduction of Computer CommunicationDocument19 pagesIntroduction of Computer CommunicationMazhar HussainNo ratings yet
- Class-1 (Seema Kujur)Document38 pagesClass-1 (Seema Kujur)Seema KujurNo ratings yet
- Computer Network: PropertiesDocument4 pagesComputer Network: Propertiesanup_verma71No ratings yet
- Lesson 7 Introduction To NetworksDocument20 pagesLesson 7 Introduction To NetworksEdwinNo ratings yet
- Ch 09 Introduction to Computer NetworksDocument21 pagesCh 09 Introduction to Computer NetworksRomitNo ratings yet
- LMT - 1 - Introduction To Networks and Networking ConceptsDocument53 pagesLMT - 1 - Introduction To Networks and Networking Conceptslakshay187No ratings yet
- Chapter 6 Communication TechnologiesDocument21 pagesChapter 6 Communication TechnologiesTsepiso MohaleNo ratings yet
- a1.2.0.0 INTRODUCTION TO COMPUTER NETWORKINGDocument33 pagesa1.2.0.0 INTRODUCTION TO COMPUTER NETWORKINGLawrence FosterNo ratings yet
- Chapter 1 Data Comm Ethio-ItalyDocument44 pagesChapter 1 Data Comm Ethio-ItalyrtyiookNo ratings yet
- An Assigenment On:-: 1. Basic of Networking 2. Introduction To Network Types 3. Internet and IntranetDocument8 pagesAn Assigenment On:-: 1. Basic of Networking 2. Introduction To Network Types 3. Internet and Intranetvipin singhNo ratings yet
- LAN and WAN types of networksDocument18 pagesLAN and WAN types of networksPing ArcenalNo ratings yet
- Computer Networks: Types of Networks: Network ArchitecturesDocument65 pagesComputer Networks: Types of Networks: Network ArchitecturesAyush MishraNo ratings yet
- Unit IvDocument12 pagesUnit IvsumipriyaaNo ratings yet
- CN - Unit 1Document196 pagesCN - Unit 1deekshitha ReddyNo ratings yet
- GCC Unit 1Document83 pagesGCC Unit 1Bhargava TipirisettyNo ratings yet
- EL 303 SP 21 CCN LEC1 IntroductionDocument68 pagesEL 303 SP 21 CCN LEC1 IntroductionBilal Ahmed MemonNo ratings yet
- Brochure AplusDocument36 pagesBrochure AplusTsuroerusuNo ratings yet
- Amf Aut T3658Document20 pagesAmf Aut T3658郭植誠No ratings yet
- CHap3 Data Acquisition Systems (DAQ)Document38 pagesCHap3 Data Acquisition Systems (DAQ)eyoule abdiNo ratings yet
- Itc Week 6Document59 pagesItc Week 6fanniNo ratings yet
- Semester - I (Ay 2020 - 21) Online Test McqsDocument30 pagesSemester - I (Ay 2020 - 21) Online Test McqsRaj JoshiNo ratings yet
- CH 08Document33 pagesCH 08Yasser SabriNo ratings yet
- Unit Unit: Installation and Configuration of Operating SystemDocument17 pagesUnit Unit: Installation and Configuration of Operating Systemanshuman singhNo ratings yet
- MQTT vs. HTTP For IoTDocument18 pagesMQTT vs. HTTP For IoTMohsinNo ratings yet
- Creating A Connection String and Working With SQL Server LocalDB - Microsoft DocsDocument4 pagesCreating A Connection String and Working With SQL Server LocalDB - Microsoft DocsPedro AriasNo ratings yet
- EWARM DevelopmentGuide - ENUDocument672 pagesEWARM DevelopmentGuide - ENUPABLO IVAN TELLO SANDOVALNo ratings yet
- SQL Codes for Filtering and Querying DataDocument23 pagesSQL Codes for Filtering and Querying Dataanderson nascimento dos santosNo ratings yet
- Java Books Some ExampleDocument4 pagesJava Books Some ExampleDasarathi RathaNo ratings yet
- Computer Ports GuideDocument17 pagesComputer Ports GuideJoannah Claire AlforqueNo ratings yet
- Guide For LC-2, LM-2, MTX-L, SCG-1and Multi-Sensor SupportDocument2 pagesGuide For LC-2, LM-2, MTX-L, SCG-1and Multi-Sensor SupportmartinNo ratings yet
- Paper 3 MadhuDocument3 pagesPaper 3 MadhuD2D Study materialNo ratings yet
- Lab ExerciseDocument4 pagesLab ExerciseJeyaan జేయాన్No ratings yet
- Cc1 Module 3 Data Representation and Number SystemDocument7 pagesCc1 Module 3 Data Representation and Number SystemjanlixalmendralNo ratings yet
- Chef LabDocument3 pagesChef LabSuraj JPNo ratings yet
- Solution Manual For C How To Program 7 e 7th Edition Paul Deitel Harvey DeitelDocument24 pagesSolution Manual For C How To Program 7 e 7th Edition Paul Deitel Harvey DeitelMariaHendrickswdkjp100% (81)
- IoT Based A Smart Home Automation System Using Packet TracerDocument7 pagesIoT Based A Smart Home Automation System Using Packet TracerIJRASETPublicationsNo ratings yet
- SAP TcodesDocument4 pagesSAP TcodesGasser EltananiNo ratings yet
- Mazak Matrix Automatic NC Backup ProcedureDocument6 pagesMazak Matrix Automatic NC Backup ProcedureTensaiga100% (2)
- Windows Network Services Internals: Jean-Baptiste MarchandDocument316 pagesWindows Network Services Internals: Jean-Baptiste MarchandAbdelwahab GhasmiNo ratings yet
- Turkish Journal of Computer and Mathematics Education Vol.12 No.14 (2021), 1372 - 1382 Research ArticleDocument11 pagesTurkish Journal of Computer and Mathematics Education Vol.12 No.14 (2021), 1372 - 1382 Research Articlekushal00001No ratings yet
- 140512-140703-Object Oriented Analysis Design and UmlDocument2 pages140512-140703-Object Oriented Analysis Design and UmlMahadeva HerbalsNo ratings yet
- Csi ZG518 Ec-3r Second Sem 2021-2022Document8 pagesCsi ZG518 Ec-3r Second Sem 2021-2022anishjiNo ratings yet
- Multithreaded Architectures: Lecture 5: Performance ConsiderationsDocument49 pagesMultithreaded Architectures: Lecture 5: Performance ConsiderationsYAAKOV SOLOMONNo ratings yet
- PIC Microcontrollers: BRANCH, CALL, AND TIME DELAY LOOPDocument31 pagesPIC Microcontrollers: BRANCH, CALL, AND TIME DELAY LOOPBernard Maacaron100% (1)
- Azure Active Directory - Grant Service Principal Access To Application in Other Tenant - Stack OverflowDocument4 pagesAzure Active Directory - Grant Service Principal Access To Application in Other Tenant - Stack OverflowybNo ratings yet
- Arduino Nano Datasheet 2Document5 pagesArduino Nano Datasheet 2Samrul YoNo ratings yet
- Computer Systems and Networking Guide: A Complete Guide to the Basic Concepts in Computer Systems, Networking, IP Subnetting and Network SecurityFrom EverandComputer Systems and Networking Guide: A Complete Guide to the Basic Concepts in Computer Systems, Networking, IP Subnetting and Network SecurityRating: 4.5 out of 5 stars4.5/5 (13)
- Microsoft Azure Infrastructure Services for Architects: Designing Cloud SolutionsFrom EverandMicrosoft Azure Infrastructure Services for Architects: Designing Cloud SolutionsNo ratings yet
- ITIL 4: Digital and IT strategy: Reference and study guideFrom EverandITIL 4: Digital and IT strategy: Reference and study guideRating: 5 out of 5 stars5/5 (1)
- Evaluation of Some Websites that Offer Virtual Phone Numbers for SMS Reception and Websites to Obtain Virtual Debit/Credit Cards for Online Accounts VerificationsFrom EverandEvaluation of Some Websites that Offer Virtual Phone Numbers for SMS Reception and Websites to Obtain Virtual Debit/Credit Cards for Online Accounts VerificationsRating: 5 out of 5 stars5/5 (1)
- AWS Certified Cloud Practitioner Study Guide: CLF-C01 ExamFrom EverandAWS Certified Cloud Practitioner Study Guide: CLF-C01 ExamRating: 5 out of 5 stars5/5 (1)
- The Compete Ccna 200-301 Study Guide: Network Engineering EditionFrom EverandThe Compete Ccna 200-301 Study Guide: Network Engineering EditionRating: 5 out of 5 stars5/5 (4)
- AWS Certified Solutions Architect Study Guide: Associate SAA-C02 ExamFrom EverandAWS Certified Solutions Architect Study Guide: Associate SAA-C02 ExamNo ratings yet
- FTTx Networks: Technology Implementation and OperationFrom EverandFTTx Networks: Technology Implementation and OperationRating: 5 out of 5 stars5/5 (1)
- Practical TCP/IP and Ethernet Networking for IndustryFrom EverandPractical TCP/IP and Ethernet Networking for IndustryRating: 4 out of 5 stars4/5 (2)
- Introduction to Cyber-Warfare: A Multidisciplinary ApproachFrom EverandIntroduction to Cyber-Warfare: A Multidisciplinary ApproachRating: 4.5 out of 5 stars4.5/5 (3)
- Computer Networking: The Complete Beginner's Guide to Learning the Basics of Network Security, Computer Architecture, Wireless Technology and Communications Systems (Including Cisco, CCENT, and CCNA)From EverandComputer Networking: The Complete Beginner's Guide to Learning the Basics of Network Security, Computer Architecture, Wireless Technology and Communications Systems (Including Cisco, CCENT, and CCNA)Rating: 4 out of 5 stars4/5 (4)
- CCNA: 3 in 1- Beginner's Guide+ Tips on Taking the Exam+ Simple and Effective Strategies to Learn About CCNA (Cisco Certified Network Associate) Routing And Switching CertificationFrom EverandCCNA: 3 in 1- Beginner's Guide+ Tips on Taking the Exam+ Simple and Effective Strategies to Learn About CCNA (Cisco Certified Network Associate) Routing And Switching CertificationNo ratings yet
- Hacking Network Protocols: Complete Guide about Hacking, Scripting and Security of Computer Systems and Networks.From EverandHacking Network Protocols: Complete Guide about Hacking, Scripting and Security of Computer Systems and Networks.Rating: 5 out of 5 stars5/5 (2)
- The CompTIA Network+ Computing Technology Industry Association Certification N10-008 Study Guide: Hi-Tech Edition: Proven Methods to Pass the Exam with Confidence - Practice Test with AnswersFrom EverandThe CompTIA Network+ Computing Technology Industry Association Certification N10-008 Study Guide: Hi-Tech Edition: Proven Methods to Pass the Exam with Confidence - Practice Test with AnswersNo ratings yet
- Amazon Web Services (AWS) Interview Questions and AnswersFrom EverandAmazon Web Services (AWS) Interview Questions and AnswersRating: 4.5 out of 5 stars4.5/5 (3)
- The Ultimate Kali Linux Book - Second Edition: Perform advanced penetration testing using Nmap, Metasploit, Aircrack-ng, and EmpireFrom EverandThe Ultimate Kali Linux Book - Second Edition: Perform advanced penetration testing using Nmap, Metasploit, Aircrack-ng, and EmpireNo ratings yet
- Open Radio Access Network (O-RAN) Systems Architecture and DesignFrom EverandOpen Radio Access Network (O-RAN) Systems Architecture and DesignNo ratings yet