Professional Documents
Culture Documents
CCN Test
Uploaded by
vipulkondekar0 ratings0% found this document useful (0 votes)
69 views1 pageQuestion Paper For mid test
Original Title
CCN TEST
Copyright
© Attribution Non-Commercial (BY-NC)
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentQuestion Paper For mid test
Copyright:
Attribution Non-Commercial (BY-NC)
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
69 views1 pageCCN Test
Uploaded by
vipulkondekarQuestion Paper For mid test
Copyright:
Attribution Non-Commercial (BY-NC)
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 1
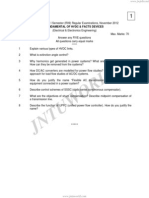
Walchand Institute of Technology, Solapur.
Department of Electronics and Telecommunication.
Mid-Test
-----------------------------------------------------------------------------------------------------------
Class :B.E. Max. Marks :50
Subject:C.C.N. Day and Date :
-----------------------------------------------------------------------------------------------------------
Q1 Solve any four questions.(4x5=20 marks)
1. Explain different network topologies and discuss their advantages and
disadvantages.
2. Give different mode transition commands and explain the mode transition in
HDLC using.
3. Explain the function of each layer in OSI standard interface.
4. Give the relationship between them using Shannon’s theorem and Nyquist
theorem. Define Bandwidth and data rate.
5. Explain modem with the help of block schematic. What is null modem?
6. What is Pure ALOHA and Slotted ALOHA. Discuss throughput versus offered
traffic for ALOHA system?
Q2 Solve any two from the following questions.(10 marks each)
1. How error control can be done using Hamming code for single bit error and burst
error. A Hamming code generated as 10110010011 is received as 10110010111 at
receiver then explains how error correction is done by hamming code?
2. What do you mean by guided transmission media and unguided transmission
media? Discuss two examples of each transmission media.
3 What are electrical, mechanical, functional and procedural specifications of
EIA234D standard interface? Draw commonly implemented circuit in standard
full duplex configuration using this standard.
-------------------------------------------------------------------------------------------------------
Teacher-Mr. Vipul Kondekar
https://sites.google.com/site/vipulwitextc/
You might also like
- Electronic Systems: Study Topics in Physics Book 8From EverandElectronic Systems: Study Topics in Physics Book 8Rating: 5 out of 5 stars5/5 (1)
- Time: 1 Hrs Electronics-I Marks: 25: Iv Unit Test Examination 2011-2012Document28 pagesTime: 1 Hrs Electronics-I Marks: 25: Iv Unit Test Examination 2011-2012Kiran Kumar0% (1)
- WAN TECHNOLOGY FRAME-RELAY: An Expert's Handbook of Navigating Frame Relay NetworksFrom EverandWAN TECHNOLOGY FRAME-RELAY: An Expert's Handbook of Navigating Frame Relay NetworksNo ratings yet
- DCN Prelims Sem V 2015Document2 pagesDCN Prelims Sem V 2015FARSHAIKH1No ratings yet
- SQL ServerDocument162 pagesSQL Serversangeeta pNo ratings yet
- Analog Electronics Lesson PlanDocument51 pagesAnalog Electronics Lesson PlanAnonymous FKMfvCbNo ratings yet
- PLCC Job Aids 21.1.14Document42 pagesPLCC Job Aids 21.1.14svk1974No ratings yet
- Redundancy Test of Power Supply Module: Test Description: To Check The Redundancy of The Power Supply Module by Making One Operative andDocument1 pageRedundancy Test of Power Supply Module: Test Description: To Check The Redundancy of The Power Supply Module by Making One Operative andSasiKumar PetchiappanNo ratings yet
- III Semester Ece Revised@lbrceDocument14 pagesIII Semester Ece Revised@lbrceTsapparapu Ravi TejaNo ratings yet
- SY Slips Sem2Document4 pagesSY Slips Sem2prashantsheetalNo ratings yet
- Ay20 21 - R18e1 Sem 1 - Mid 2 - Ece Et 31072021Document2 pagesAy20 21 - R18e1 Sem 1 - Mid 2 - Ece Et 31072021BalajiNo ratings yet
- Faculty of Engineering Mid Exam Fall 2015Document3 pagesFaculty of Engineering Mid Exam Fall 2015Mohamad El-MasryNo ratings yet
- Range Rover Diagnostics - 22!5!2016Document18 pagesRange Rover Diagnostics - 22!5!2016Charles MooreNo ratings yet
- CCNA 3 Final ExamDocument25 pagesCCNA 3 Final ExamAhmed FaroukNo ratings yet
- Current-Source DC-DC ConverterDocument53 pagesCurrent-Source DC-DC ConverterpepenitoNo ratings yet
- Engineering Physics - I LabDocument1 pageEngineering Physics - I LabIrfanNo ratings yet
- Lab Manual j01Document7 pagesLab Manual j01SyedaNo ratings yet
- PLC QuestionsDocument2 pagesPLC QuestionsSreejithRaveendran100% (1)
- Network AnalysisDocument3 pagesNetwork AnalysisDeva Raju TNo ratings yet
- Resonant Gate Drive Techniques For Power MosfetsDocument85 pagesResonant Gate Drive Techniques For Power MosfetsEnzo Karol VelásquezNo ratings yet
- Transmission Line Theory: Microwave EngineeringDocument8 pagesTransmission Line Theory: Microwave EngineeringDai Thang TranNo ratings yet
- Curriculum Circuits LabDocument1 pageCurriculum Circuits LabKarthik ThirumalaNo ratings yet
- Power Supply and Special CircuitsDocument18 pagesPower Supply and Special CircuitsManoj Kumar RathNo ratings yet
- M.Tech. Programme: Electronics and Communication - Microwave and TV Engineering Curriculum and Scheme of ExaminationsDocument9 pagesM.Tech. Programme: Electronics and Communication - Microwave and TV Engineering Curriculum and Scheme of ExaminationsGoosajaNo ratings yet
- Assignment 2Document1 pageAssignment 2AnandNo ratings yet
- Kalim 1Document12 pagesKalim 1mdwasim6123No ratings yet
- Lab 03 Transmission Line Analysis On Simulink 14032021 102443amDocument6 pagesLab 03 Transmission Line Analysis On Simulink 14032021 102443amArkam AliNo ratings yet
- Ccna R&SDocument77 pagesCcna R&SarunNo ratings yet
- Variables Dynamical SystemDocument12 pagesVariables Dynamical SystemTitok TitokNo ratings yet
- Assignment 6 MechDocument1 pageAssignment 6 Mechحماد رندNo ratings yet
- Integrated Circuits and Applications: CO1 CO2 CO3 CO4 CO5Document72 pagesIntegrated Circuits and Applications: CO1 CO2 CO3 CO4 CO5Chinsdazz KumarNo ratings yet
- Eurec 606Document2 pagesEurec 606haziqhazriNo ratings yet
- Cw1 (Part1) BriefDocument3 pagesCw1 (Part1) Briefoussama sadkiNo ratings yet
- Fundamental of HVDC FACTS DevicesDocument4 pagesFundamental of HVDC FACTS Devicessreenivasroyal80% (1)
- PE III-paper, Mid Term-IIDocument1 pagePE III-paper, Mid Term-IIhodeegits9526No ratings yet
- M06 Troubl. AC - DCDocument111 pagesM06 Troubl. AC - DCbilisummaaNo ratings yet
- AnaKosThesisFinal SEgment RoutingDocument110 pagesAnaKosThesisFinal SEgment RoutingAizaz HussainNo ratings yet
- An Akos Thesis FinalDocument110 pagesAn Akos Thesis Finalmohammed meladNo ratings yet
- Question Bank For Mid-2 r13 (Vlsi) .Document6 pagesQuestion Bank For Mid-2 r13 (Vlsi) .rppvchNo ratings yet
- GVS - DALI Gateway, 1 - 2-Fold - UM - V1.2 - 20210525 - ENDocument52 pagesGVS - DALI Gateway, 1 - 2-Fold - UM - V1.2 - 20210525 - ENmellNo ratings yet
- Course Objectives: Student Will Be Able ToDocument1 pageCourse Objectives: Student Will Be Able ToNaushad SheikNo ratings yet
- MP 2012-13 Mid Test Paper FinalDocument2 pagesMP 2012-13 Mid Test Paper FinalVipul KondekarNo ratings yet
- 4188 856 PDFDocument186 pages4188 856 PDFshahbazalam4a550% (2)
- PDQDocument9 pagesPDQkavita4123No ratings yet
- EMI Important QuestionsDocument2 pagesEMI Important Questionsanishkurmi66No ratings yet
- Assignment 5 Sub Transmission Lines and Non Technical Distribution Substations Design FactorsDocument1 pageAssignment 5 Sub Transmission Lines and Non Technical Distribution Substations Design FactorsMohammad Haseeb ButtNo ratings yet
- BizTalk Server MCQDocument10 pagesBizTalk Server MCQvijay kumarNo ratings yet
- TssDocument2 pagesTssvinu0410No ratings yet
- Lakireddy Bali Reddy College of Engineering (Document9 pagesLakireddy Bali Reddy College of Engineering (raman yarramilliNo ratings yet
- Assignment #1 - Themro II - Spring 2024Document3 pagesAssignment #1 - Themro II - Spring 2024Mai DweikatNo ratings yet
- John D. Lenk - Handbook of Practical Solid-State Troubleshooting (1971, Prentice Hall) - Libgen - LiDocument328 pagesJohn D. Lenk - Handbook of Practical Solid-State Troubleshooting (1971, Prentice Hall) - Libgen - Lianalog changeNo ratings yet
- Mid Term PDFDocument2 pagesMid Term PDFIshfaq AhmadNo ratings yet
- Pe Cep A3Document3 pagesPe Cep A3M Hassan BashirNo ratings yet
- Low Cost Narrow Band Network AnalyserDocument29 pagesLow Cost Narrow Band Network AnalyserAmeer JahaanNo ratings yet
- Final SCADA SpecificationDocument66 pagesFinal SCADA SpecificationPavan100% (1)
- LessonPlanCS A&dDocument2 pagesLessonPlanCS A&dneczuberbashaNo ratings yet
- Reversible Gate Mapping Into QCA Explicit Cells Packed With Single LayerDocument9 pagesReversible Gate Mapping Into QCA Explicit Cells Packed With Single LayermishraneeNo ratings yet
- Exp - 8Document4 pagesExp - 8Md KaziNo ratings yet
- 2017-18 M.sc. Electronics Part-IDocument14 pages2017-18 M.sc. Electronics Part-Isonawaneulhas292No ratings yet
- Department of Electrical EngineeringDocument1 pageDepartment of Electrical EngineeringsangeetadineshNo ratings yet
- PPT5 - Network Layer IP Addressing-IIDocument20 pagesPPT5 - Network Layer IP Addressing-IIvipulkondekarNo ratings yet
- PPT4 - Network Layer Subnetting and SupernettingDocument19 pagesPPT4 - Network Layer Subnetting and Supernettingvipulkondekar100% (1)
- PPT3 - Network Layer IP Addressing-IDocument12 pagesPPT3 - Network Layer IP Addressing-IvipulkondekarNo ratings yet
- Ass6 Data AnalyticsDocument2 pagesAss6 Data AnalyticsvipulkondekarNo ratings yet
- Assignment Unit 5: Regression and ClassificationDocument1 pageAssignment Unit 5: Regression and ClassificationvipulkondekarNo ratings yet
- PPT1 - Data Link Layer HDLC Protocol-Part IDocument15 pagesPPT1 - Data Link Layer HDLC Protocol-Part IvipulkondekarNo ratings yet
- PPT2 - Data Link Layer HDLC Protocol-Part IIDocument13 pagesPPT2 - Data Link Layer HDLC Protocol-Part IIvipulkondekarNo ratings yet
- DA Institute Level TestDocument1 pageDA Institute Level TestvipulkondekarNo ratings yet
- Program For Matrix Keyboard Interfacing: Objective: Requirements: TheoryDocument3 pagesProgram For Matrix Keyboard Interfacing: Objective: Requirements: TheoryvipulkondekarNo ratings yet
- LCD Interfacing PIC16F877aDocument5 pagesLCD Interfacing PIC16F877avipulkondekar100% (1)
- Revised Courses Jan-April 2019Document1 pageRevised Courses Jan-April 2019vipulkondekarNo ratings yet
- 8.program For Internal ADC of PIC: ObjectiveDocument4 pages8.program For Internal ADC of PIC: ObjectivevipulkondekarNo ratings yet
- PWM Speed & Direction Control of DC Motor: ObjectiveDocument6 pagesPWM Speed & Direction Control of DC Motor: Objectivevipulkondekar100% (1)
- Solapur University, SolapurDocument32 pagesSolapur University, SolapurvipulkondekarNo ratings yet
- Exam Registration Form For September 2017 Exams: Basic DetailsDocument2 pagesExam Registration Form For September 2017 Exams: Basic DetailsvipulkondekarNo ratings yet
- NPTL Scholarship 2017 - Return FormatDocument10 pagesNPTL Scholarship 2017 - Return FormatvipulkondekarNo ratings yet
- Lab Manual: Electronics and Telecommunication EngineeringDocument1 pageLab Manual: Electronics and Telecommunication EngineeringvipulkondekarNo ratings yet
- BBC QPDocument1 pageBBC QPvipulkondekarNo ratings yet
- My TTDocument1 pageMy TTvipulkondekarNo ratings yet
- 8051 ProgramsDocument2 pages8051 ProgramsvipulkondekarNo ratings yet
- Bar GraphsDocument2 pagesBar GraphsvipulkondekarNo ratings yet
- Round 2Document1 pageRound 2vipulkondekarNo ratings yet
- Electronics LabDocument0 pagesElectronics LabvipulkondekarNo ratings yet
- Evaluation of Some Websites that Offer Virtual Phone Numbers for SMS Reception and Websites to Obtain Virtual Debit/Credit Cards for Online Accounts VerificationsFrom EverandEvaluation of Some Websites that Offer Virtual Phone Numbers for SMS Reception and Websites to Obtain Virtual Debit/Credit Cards for Online Accounts VerificationsRating: 5 out of 5 stars5/5 (1)
- Hacking: A Beginners Guide To Your First Computer Hack; Learn To Crack A Wireless Network, Basic Security Penetration Made Easy and Step By Step Kali LinuxFrom EverandHacking: A Beginners Guide To Your First Computer Hack; Learn To Crack A Wireless Network, Basic Security Penetration Made Easy and Step By Step Kali LinuxRating: 4.5 out of 5 stars4.5/5 (67)
- Microsoft Certified Azure Fundamentals Study Guide: Exam AZ-900From EverandMicrosoft Certified Azure Fundamentals Study Guide: Exam AZ-900No ratings yet
- AWS Certified Solutions Architect Study Guide: Associate SAA-C02 ExamFrom EverandAWS Certified Solutions Architect Study Guide: Associate SAA-C02 ExamNo ratings yet
- The Compete Ccna 200-301 Study Guide: Network Engineering EditionFrom EverandThe Compete Ccna 200-301 Study Guide: Network Engineering EditionRating: 5 out of 5 stars5/5 (4)
- Cybersecurity: A Simple Beginner’s Guide to Cybersecurity, Computer Networks and Protecting Oneself from Hacking in the Form of Phishing, Malware, Ransomware, and Social EngineeringFrom EverandCybersecurity: A Simple Beginner’s Guide to Cybersecurity, Computer Networks and Protecting Oneself from Hacking in the Form of Phishing, Malware, Ransomware, and Social EngineeringRating: 5 out of 5 stars5/5 (40)
- Microsoft Azure Infrastructure Services for Architects: Designing Cloud SolutionsFrom EverandMicrosoft Azure Infrastructure Services for Architects: Designing Cloud SolutionsNo ratings yet
- Networking Fundamentals: Develop the networking skills required to pass the Microsoft MTA Networking Fundamentals Exam 98-366From EverandNetworking Fundamentals: Develop the networking skills required to pass the Microsoft MTA Networking Fundamentals Exam 98-366No ratings yet
- Set Up Your Own IPsec VPN, OpenVPN and WireGuard Server: Build Your Own VPNFrom EverandSet Up Your Own IPsec VPN, OpenVPN and WireGuard Server: Build Your Own VPNRating: 5 out of 5 stars5/5 (1)
- Azure Networking: Command Line Mastery From Beginner To ArchitectFrom EverandAzure Networking: Command Line Mastery From Beginner To ArchitectNo ratings yet
- Cybersecurity: The Beginner's Guide: A comprehensive guide to getting started in cybersecurityFrom EverandCybersecurity: The Beginner's Guide: A comprehensive guide to getting started in cybersecurityRating: 5 out of 5 stars5/5 (2)
- ITIL 4 : Drive Stakeholder Value: Reference and study guideFrom EverandITIL 4 : Drive Stakeholder Value: Reference and study guideNo ratings yet
- ITIL® 4 Create, Deliver and Support (CDS): Your companion to the ITIL 4 Managing Professional CDS certificationFrom EverandITIL® 4 Create, Deliver and Support (CDS): Your companion to the ITIL 4 Managing Professional CDS certificationRating: 5 out of 5 stars5/5 (2)
- Mastering Linux Security and Hardening - Second Edition: Protect your Linux systems from intruders, malware attacks, and other cyber threats, 2nd EditionFrom EverandMastering Linux Security and Hardening - Second Edition: Protect your Linux systems from intruders, malware attacks, and other cyber threats, 2nd EditionNo ratings yet
- Alcatel-Lucent Service Routing Architect (SRA) Self-Study Guide: Preparing for the BGP, VPRN and Multicast ExamsFrom EverandAlcatel-Lucent Service Routing Architect (SRA) Self-Study Guide: Preparing for the BGP, VPRN and Multicast ExamsNo ratings yet
- Concise Guide to OTN optical transport networksFrom EverandConcise Guide to OTN optical transport networksRating: 4 out of 5 stars4/5 (2)
- Open Radio Access Network (O-RAN) Systems Architecture and DesignFrom EverandOpen Radio Access Network (O-RAN) Systems Architecture and DesignNo ratings yet
- AWS Certified Cloud Practitioner Study Guide: CLF-C01 ExamFrom EverandAWS Certified Cloud Practitioner Study Guide: CLF-C01 ExamRating: 5 out of 5 stars5/5 (1)