Professional Documents
Culture Documents
Cisco Cloud Infrastructure Security Breach
Uploaded by
Jaja HollaOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Cisco Cloud Infrastructure Security Breach
Uploaded by
Jaja HollaCopyright:
Available Formats
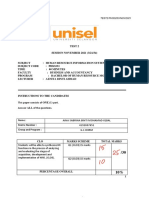
FACULTY OF BUSINESS AND ACCOUNTANCY
CODE AND COURSE NAME PHS 3233 HUMAN RESOURCES INFORMATION SYSTEM
LECTURER’S NAME MADAM AZNITA BT AHMAD
STUDENT’S NAME NUR IZZATUL NAJWA BINTI NORZI AZWA
STUDENT MATRIC NO.
4192009631
PROGRAMME BACHELOR OF HUMAN RESOURCES MANAGEMENT
EXAMINATION DATE 17/3/2022
This final examination measures the student's ability for the following outcomes:
QUESTION NO. 1ST EXAMINER 2ND EXAMINER EXAMINER’S ENDORSEMENT:
(MARKS) (MARKS)
Please tick (√) in the appropriate space.
I have checked the answers on each page.
I have calculated all marks correctly.
TOTAL
First Examiner Second Examiner
Name : Name :
Date : Date :
Signature : Signature :
FACULTY OF BUSINESS AND ACCOUNTANCY/ NOVEMBER 2021
STUDENT DECLARATION FORM
FINAL EXAM
SEMESTER NOVEMBER 2021 (32134)
To validate the examination and to protect the integrity of the examination process,
UNISEL students are required to complete this Student Declaration Form and to submit
together with the answer script or assignment for online, take home, or project based
examination.
I hereby declare and verify that:
/ the work done is my own unaided work.
/ I follow the procedure of the final examination/assignment/project.
/ I appropriately acknowledge any part of a work that is not my own.
/ I do not falsify or misrepresent authorship, evidence, data, findings, or conclusions
/ I do not allow other students to copy or use my work unless required by my task.
/ I do not use or submit the work of other student unless a task requires this.
/ I do not use or submit the work of others such as family members and friends.
/ I do not submit the same piece of work for assessment in more than one subject.
/ I hereby declare that I have read and understood the rules for undertaking the final
online examination/take-home examination/project. I certify that this declaration is true
and correct. I understand that if this declaration is found to be untrue or incorrect, I may
be subject to penalties in accordance with the University’s rules and regulations.
Student Name : Nur Izzatul Najwa Binti Norzi Azwa
Student Matric : 4192009631
Program : Bachelor Of Human Resource
Management
Course Name : HUMAN RESOURCES INFORMATION
SYSTEM
Course Code : PHS 3233
FACULTY OF BUSINESS AND ACCOUNTANCY/ NOVEMBER 2021
ANSWERS:
Section A Q1)a):
Company Profile
i. Basic information
Basic information is one of the part of company profile components. Basic information in
this company profile needs information is related to the staff company name, company
resgistration number, Phone, Fax, Email, Websites URL, Contact Person Name,
Addreses, and so on. As an example:
Name: Suka HQ
Staff number: A56091
Identification NO: 920605-06-5246
Gender: Female
Race: Malay
Birth Date: 5 January 2000
Religion: Islam
Marital Status: Single
ii. Financial information
Financial information is one of the part on office central it is related to the staff financial
information conducting the EPF number, SOCSO, Income tax number, ZAKAT, Tabung
Haji, and so on.
Staff Profile
i. Basic information
Name: Suka HQ
Staff number: A56091
FACULTY OF BUSINESS AND ACCOUNTANCY/ NOVEMBER 2021
Identification NO: 920605-06-5246
Gender: Female
Race: Malay
Birth Date: 5 January 2000
Religion: Islam
Marital Status: Single
ii. Education
Education Name: Master in Bussiness Administration
Education Description: Oxford University
Year: 2
iii. Experience
Company name: XIXILI SDN BHD
Description:Assistant Sales Manager
Start Date:1 Dec 2016
End date: 1 June 2017
b)items in a payroll group:
Items included in payroll group is Satff NO, Staff Name, Classifcation, Department,
Designation, Report To, and Date Joined Duration.
C (i)
Pay Dates
Employees who are paid monthly are paid on the last working day of the month, except
in December, when pay day is shifted to accommodate the Christmas holiday. Here, you'll
find a list of pay dates for December.
FACULTY OF BUSINESS AND ACCOUNTANCY/ NOVEMBER 2021
Dates of Payroll Deadlines
Information must be provided by the deadlines listed in the notices. Pay period
transactions will not be executed until the next pay period, and departments should inform
their personnel of this fact. Because of the early paydays in December and other public
or bank holidays, several deadlines are sooner than in the rest of the year. The deadlines
are subject to change, so please check the website often to see if anything has been
changed.
c)ii)
FACULTY OF BUSINESS AND ACCOUNTANCY/ NOVEMBER 2021
d) i. Employee Provident Fund (EPF) - contribute 11 percent of your monthly salary to the
EPF, and your employer will contribute an additional 12 percent or 13 percent. The
government has the authority to alter the statutory contribution rate for EPF savings.
However, either the employer or the company, or both, may contribute at a higher rate
than the statutory rate.
ii. Social Security Organization (SOCSO) - The Social Security Organization (SOCSO)
provides social security protection to employees through social insurance, which includes
medical and cash benefits, the provision of artificial aids, and rehabilitation to alleviate
suffering and provide financial guarantees and protection to the family.
iv. Malaysian Inland Revenue Board (LHDN) - The LHDN is one of the Ministry of
Finance's primary revenue collection agencies. The LHDN was established in accordance
with the Inland Revenue Board of Malaysia Act 1995 in order to grant it greater autonomy,
particularly in financial and personnel management, and to improve the quality and
effectiveness of tax administration.
B. SECTION (Q1)
a.
Analyze security breaches that occurred in relation to intentional threats against Cisco
cloud infrastructure perpetrated by a former Cisco employee.
The following are the security breaches that have occurred in relation to intentional threats
against Cisco cloud infrastructure perpetrated by a former Cisco employee:
• A former Cisco employee gained unauthorised access to the company's cloud
infrastructure by exploiting his knowledge of Cisco's security mechanisms and exploiting
their flaws in order to gain access to the cloud infrastructure and deploy his code.
• He distributed malicious code that deleted 456 virtual machines associated with Cisco's
WebEx Teams application.
• There was no use of two-factor authentication or other access management techniques
to protect sensitive resources, making it simple for the former Cisco employee to gain
access.
• As a result, 16,000 WebEx users were unable to access their accounts for two weeks.
• Cisco had to spend approximately $1.4 million in employee time auditing and repairing
their infrastructure.
FACULTY OF BUSINESS AND ACCOUNTANCY/ NOVEMBER 2021
SECTION B Q1(B)
To prevent unauthorised access, the HR department should be more proactive about
company data security. Human resources departments have always been associated with
people's success and development, but they are now more actively involved in
cybersecurity and data protection. With the rise in cyber-attacks and data breaches, HR
can no longer afford to ignore this responsibility. HR professionals are already familiar
with all of the sensitive information that organisations keep on their employees, such as
salary history, performance reviews, benefit plans, and so on. However, because of this
level of openness, HR professionals are a potential target for criminal hackers.
To avoid this, HR departments can take a proactive approach to data security by providing
ongoing training and education. HR professionals, for example, can pursue qualifications
that will help them become HR specialists. HR professionals with such credentials are
better prepared to deal with the complexities of cybersecurity and data protection. By
understanding how security breaches can disrupt business operations, HR personnel will
be able to intervene when necessary and resolve issues before they become more
serious issues. To stay current in the industry, these individuals should continue their
education by attending seminars or webinars on emerging trends. This way, you can keep
your finger on the pulse of cybersecurity best practises at all times. This entails being
aware of any new threats that must be addressed. Furthermore, by regularly updating
employees' knowledge of best practises for safeguarding sensitive information – such as
phishing scams, password security protocols, and more – HR professionals can help
prevent harmful incidents in the workplace.
Second, HR departments can be proactive by auditing the data collection and storage
process. For example, a company that has out-of-date security protocols in place to
protect sensitive information such as employee salaries or benefit plans is a prime target
for criminal hackers In that case, it is time to update these procedures in order to remain
compliant with new federal government regulations regarding how organisations must
store this PII (personally identifiable information). When hiring third-party vendors who
will have access to PII on the organization's employees and other sensitive business
intelligence, HR professionals should be especially cautious. This includes thoroughly
vetting potential service providers before bringing them into your network, ensuring they
have a solid track record of protecting information and adhering to federal regulations.
This is significant because there have been numerous instances where employees of
FACULTY OF BUSINESS AND ACCOUNTANCY/ NOVEMBER 2021
third-party vendors have violated privacy policies, putting the organisation at risk of fines
or worse if their system is hacked and sensitive data is stolenHR professionals should
also collaborate closely with their IT department to ensure that data security measures
are implemented consistently. For example, ensuring that software upgrades are
completed on time so that cyber criminals are unable to exploit existing vulnerabilities or
weaknesses in a system.
Maintain the integrity of your firewall rules as well. A firewall is a network security device
that monitors both incoming and outgoing network traffic and allows or denies data
packets based on a set of security rules. It is possible to optimise the firewall rule base to
ensure that it runs smoothly and without interruptions. Make sure you don't have any rules
that are duplicated, incorrect, or shadowed. Again, having a regular schedule for
upgrades and efficiency checks is recommended.
Control user access and firewall changes as well. HR should be strict about user
permissions and only allow authorised users you trust to change the firewall rules. Also,
have a procedure in place for firewall changes. It should include a list of the desired
adjustments, an estimation of the risk of policy changes, and basic information about who
implemented the changes, when they were implemented, and why, as well as a record of
the results.
Employees are the most effective line of defence against data breaches. HR
professionals should be proactive in educating employees about the importance of
protecting sensitive information and adhering to legislation. This entails collaborating
closely with IT, auditing security measures within an organisation, and thoroughly
screening third-party vendors before allowing them access to your network.
SECTION B Q1(C)
In terms of technical controls, the best practises of prevention techniques that Cisco
should implement in order to secure customer data are, first and foremost, auditing the
network and checking security controls. Maintaining a secure environment necessitates
knowledge. The IT organisation must conduct a network audit to gain an accurate picture
of a given enterprise's security posture. IT professionals can use auditing to identify
potential vulnerabilities that need to be fixed, find unused or unnecessary applications
running in the background that can be removed, determine the strength of the firewall and
the currency of its settings, measure the state of networked servers, gear, software, and
applications, confirm the overall efficacy of the security infrastructure, and judge.
Second, put in place and communicate a security governance structure. Compliance does
not always imply security, but it can provide important guidance on how to mitigate risks.
Regulatory bodies such as the International Organization for Standardization and the
FACULTY OF BUSINESS AND ACCOUNTANCY/ NOVEMBER 2021
Payment Card Industry Security Standards Council emphasise the importance of
establishing a structure that specifies who is responsible for managing security and
responding to cybersecurity incidents. IT organisations must define the roles and
responsibilities of individuals in managing risks and responding to incidents. Periodic risk
assessments can assist organisations in prioritising vulnerability remediation and
minimising downtime.
Furthermore, review and communicate security policies. To ensure a strong security
posture, a pragmatic and valid security policy is required. Organizations frequently fail to
review policies to ensure that they address current business operational requirements
and security conditions. Unfortunately, enterprises frequently fail to communicate these
policies to both IT staff and, where applicable, end users. Organizations such as the
SANS Institute publish reference documents that IT professionals can use to reexamine
and update policies, such as having a formal directive on implementing and executing
changes.
After that, educate end users. Raising end-user awareness is critical in an era when
phishing attacks are a preferred method of many cyberattacks. In a 2017 Dell survey of
corporate employees, more than 75% said they would willingly share confidential data
under certain conditions. End users are vulnerable to certain types of attacks that look
like normal communications. And, as cybercriminals become more adept at using email
and other forms of communication to closely mimic professional interactions, the
likelihood of a staff member succumbing to the threat grows. End-user education should
be an ongoing process that is an intrinsic part of a company's culture to keep employees
informed about the evolving threat environment and associated corporate security
policies.
Finally, stay informed. One overarching requirement for establishing best practises in
network security is to treat the discipline as an ongoing effort. This includes staying up to
date on changes in the threat environment. As a result, security personnel and IT
professionals must understand how cyberattackers are changing their tactics. They must
also stay current on advances in threat detection and mitigation. The goal should be to
apply lessons learned from previous incidents to limit the negative consequences of future
events.
Q2)a) ANSWERS
Problems that Cempakasari Sdn Bhd are experiencing is:
-Head count reports are frequently late and inaccurate
FACULTY OF BUSINESS AND ACCOUNTANCY/ NOVEMBER 2021
- Daily attendance records for personnel from various offices and locations
throughout Malaysia is time-consuming and late submissions. Reports received
from 10 separate offices, and not user-friendly for upper administration.
-The recruiting procedure is extremely slow, takes three months from the date of
the advertisement for new staff to begin working.
-Leave administration is time-consuming, and the employees who seek information
often become frustrated. Managers were found to be tardy in making
decisions or granting leave requests.
-The payroll procedure, centralized at the corporate headquarters, takes
lengthy time, placing a load on the HR personnel and resulting high rate of
human error computations of salaries. Salary information, which is intended
to be private, discreet, and managed, was occasionally discovered on the table of
human resources personnel.
Solutions that can be implemented to the issues that faced by Cempakasari Sdn Bhd
is,they can used:
1. Recruiting Modules
This is because the Cempakasari Sdn Bhd have an issue is The recruiting procedure is
extremely slow, takes three months from the date of the advertisement for new staff to
begin working. When the HRMS module have a recruiting modules it can make it easy to
the HR department. This is because the recruiting system can help in the providence of
requisition and vacancy, create a vacancy, assign recruitement vacancy, applicant quick
entry and final step is Mass update of the applicant. With this modules, Cepakasari can
reduce the time of recruitementofeach applicant.
2. Payroll module
The challenges that Cempakasari faces on centralised at the corporate headquarters take
a long time, putting a strain on HR personnel and resulting in a high rate of human error
in salary computations. The payroll module has the potential to solve the organization's
problem. The HR clerk only needs to enter the on-payroll profile in the payroll system,
FACULTY OF BUSINESS AND ACCOUNTANCY/ NOVEMBER 2021
which includes the basic salary, overtime, payroll group, bank information, EPF
information, SOCSO information, LHDN information, and Zakat information. When the
salary date arrives, the HR clerk simply clicks on process payroll and indicates which
month and when the date should be cut off. For example, if the salary is paid on January
27, 2022, the cut-off date must be January 26, 2022. It is very simple when the payroll
module is used in the part of HRMS
3. Attendance management and leave management module
The issue that Cempakasari SDN BHD is facing is that maintaining daily attendance
records for personnel from various offices and locations throughout Malaysia is time-
consuming, and late submissions are common. Additionally, leave administration is time-
consuming, and employees who seek information frequently become frustrated, which
can reduce errors. This is due to the fact that the system is automatically updated once
the clerk has indicated the employee's attendance and leave. They simply enter the data
into the module, and the result is calculated automatically; the clerk does not need to
calculate manually because the system is built automatically
Q2)b) Precise factors that should be considered while selecting the most suitable vendor
for the Cempakasari SDN BHD is this organization need to use the need analysis metrics
factors. This analysis willhelp the organization to becomemore systematics which it is
using the need analysis stages included process of Need analysis planning,Observation,
Exploration, Evaluation and Reporting. Cempakasari need to used this factor because it
is important to giving benefits in aspect of :
• Automate Process
• Ensure 100 percent accuracy
• Save time, increase effiecient and accelerate growth of the organization
FACULTY OF BUSINESS AND ACCOUNTANCY/ NOVEMBER 2021
You might also like
- The Not Yet Exploited Goldmine of OSINT OpportunitDocument23 pagesThe Not Yet Exploited Goldmine of OSINT Opportunitxaranix916No ratings yet
- International Human Resource Management 6th EditionDocument364 pagesInternational Human Resource Management 6th EditionJaja Holla100% (1)
- EwaptDocument33 pagesEwaptBertrand Lorente YanezNo ratings yet
- CEH Practical NotesDocument42 pagesCEH Practical NotesSundeel Bin Haleem100% (7)
- General Studies Tamil by Tata Mcgraw HillDocument1 pageGeneral Studies Tamil by Tata Mcgraw HillmuruganandamNo ratings yet
- Detailed Teaching Syllabus (DTS) and Instructor Guide (Ig'S)Document15 pagesDetailed Teaching Syllabus (DTS) and Instructor Guide (Ig'S)Charo GironellaNo ratings yet
- Types of CYBER SECURITY Threats: ©shabinDocument13 pagesTypes of CYBER SECURITY Threats: ©shabinShabin JerinNo ratings yet
- FINAL EXAM HrisDocument11 pagesFINAL EXAM HrisJaja HollaNo ratings yet
- Payroll Records and Security ProceduresDocument19 pagesPayroll Records and Security ProceduresNiomi Golrai100% (1)
- ICTNWK502 Task 2 Answer Part ADocument19 pagesICTNWK502 Task 2 Answer Part AKouser SultanaNo ratings yet
- MBS 539 - Accounting For ManagersDocument21 pagesMBS 539 - Accounting For ManagersSenior Assistant Secretary EducationNo ratings yet
- HRM-2022 P S SanjanaDocument16 pagesHRM-2022 P S SanjanaSanjanaNo ratings yet
- Assignment 3RAIDocument8 pagesAssignment 3RAIHussin Al-AsafNo ratings yet
- 01.06 - Preparing For Employment WorksheetDocument3 pages01.06 - Preparing For Employment Worksheetanshi christinaNo ratings yet
- Andres - Paez - BSBXCS402 - Attempt 1Document28 pagesAndres - Paez - BSBXCS402 - Attempt 1Andres PaezNo ratings yet
- Mirza Zaid HRMDocument5 pagesMirza Zaid HRMZaid BaigNo ratings yet
- RS BSBINM601 MadhavPrasadGhimire Task4Document17 pagesRS BSBINM601 MadhavPrasadGhimire Task4Lok SewaNo ratings yet
- DocxDocument48 pagesDocxMaria TahreemNo ratings yet
- CIPD Assignment Cover PageDocument10 pagesCIPD Assignment Cover PageHussin Al-AsafNo ratings yet
- Summative Assessment - Developing Skills For Business LeadershipDocument27 pagesSummative Assessment - Developing Skills For Business Leadershipriannemarie12No ratings yet
- MIP Report Anupama (2SD17MBA06) PDFDocument19 pagesMIP Report Anupama (2SD17MBA06) PDFSangamesh BagaliNo ratings yet
- Executive Reg LetterDocument8 pagesExecutive Reg LetterDibyaranjan SahooNo ratings yet
- WINTER 2024 247 Drake Centre TR 11:30 AM - 12:45 AM: IDM 2020 & SECTION A02 (3 CH) Introduction To Business AnalyticsDocument11 pagesWINTER 2024 247 Drake Centre TR 11:30 AM - 12:45 AM: IDM 2020 & SECTION A02 (3 CH) Introduction To Business Analyticstaylerlynn19No ratings yet
- B170219B BBMN3213 HrmfinalexamDocument16 pagesB170219B BBMN3213 HrmfinalexamLIM JEI XEE BACC18B-1No ratings yet
- Executive Reg LetterDocument8 pagesExecutive Reg Letterbackupsanthosh21 dataNo ratings yet
- Sip ReportDocument40 pagesSip Reportavinashkumar.mba22No ratings yet
- Information Systems in Business Course OutlineDocument15 pagesInformation Systems in Business Course Outlinemounica_veraNo ratings yet
- Assignment 1 Front Sheet: Qualification BTEC Level 5 HND Diploma in Computing Unit Number and TitleDocument78 pagesAssignment 1 Front Sheet: Qualification BTEC Level 5 HND Diploma in Computing Unit Number and TitleCong CongNo ratings yet
- Bin900 01 AssignmentDocument21 pagesBin900 01 Assignmentanon_168023518No ratings yet
- BSBITU301 - Assessment 1 - Knowledge QuestionDocument4 pagesBSBITU301 - Assessment 1 - Knowledge QuestionAashish thapa100% (1)
- Student Details:: Assessment Coversheet-Individual (VET)Document9 pagesStudent Details:: Assessment Coversheet-Individual (VET)Diana Pulido33% (3)
- Intial Pages For M.com ProjectsDocument54 pagesIntial Pages For M.com ProjectsInamul HaqueNo ratings yet
- RS BSBINM601 MadhavPrasadGhimire Task2Document34 pagesRS BSBINM601 MadhavPrasadGhimire Task2Lok Sewa100% (1)
- Melroy Pukailara Black BookDocument58 pagesMelroy Pukailara Black BookVinit RautNo ratings yet
- Queensland International Business Academy AssessmentDocument11 pagesQueensland International Business Academy AssessmentsammyNo ratings yet
- Individual AssignmentDocument15 pagesIndividual Assignmentsharifah nadiah munirahNo ratings yet
- 487-Asm1-Nguyen Do Thanh UyenDocument44 pages487-Asm1-Nguyen Do Thanh UyenBảo NhưNo ratings yet
- Field Project MGNM729Document44 pagesField Project MGNM729sahil gakkharNo ratings yet
- Assessment: Queensland International Business AcademyDocument13 pagesAssessment: Queensland International Business AcademysammyNo ratings yet
- Ensure workplace safety assessmentDocument8 pagesEnsure workplace safety assessmentgagidonNo ratings yet
- Andres Paez ICTICT618 T2022 Attempt1Document59 pagesAndres Paez ICTICT618 T2022 Attempt1Andres PaezNo ratings yet
- Assessment BSBINN601 2 of 3 QIBA V2Document15 pagesAssessment BSBINN601 2 of 3 QIBA V2sammyNo ratings yet
- Career Interest Report - 202002581Document10 pagesCareer Interest Report - 202002581api-585895578No ratings yet
- Assignment On Email & Memo: Submitted To: Mr. Sayedul KarimDocument3 pagesAssignment On Email & Memo: Submitted To: Mr. Sayedul KarimTASLIMA BEGUMNo ratings yet
- 491 - Assignment 2 Frontsheet FixDocument13 pages491 - Assignment 2 Frontsheet FixMuoi VanNo ratings yet
- Adekunle Benjamin Siwes Report On DSTVDocument11 pagesAdekunle Benjamin Siwes Report On DSTVBello OlalekanNo ratings yet
- Executive Reg LetterDocument6 pagesExecutive Reg LetterTANMAYA GUPTANo ratings yet
- Assessment BSBINN601 3 of 3 QIBA V2Document21 pagesAssessment BSBINN601 3 of 3 QIBA V2sammyNo ratings yet
- Mbs 535 Assign 2 Man A 33903419Document24 pagesMbs 535 Assign 2 Man A 33903419Senior Assistant Secretary EducationNo ratings yet
- BSBWOR301 AE Professional[2]Document13 pagesBSBWOR301 AE Professional[2]sc20600226No ratings yet
- 20230329185029PM 1893858855 10834313 110798271 - CLT294619Document8 pages20230329185029PM 1893858855 10834313 110798271 - CLT294619Pritam DasNo ratings yet
- Supervising Administrative Officer - CESAR E. A. VIRATA SCHOOL OF BUSINESS - UPSB-SADOF-567-2004Document3 pagesSupervising Administrative Officer - CESAR E. A. VIRATA SCHOOL OF BUSINESS - UPSB-SADOF-567-2004EA MendozaNo ratings yet
- Executive Reg LetterDocument8 pagesExecutive Reg LetterNitin DhaterwalNo ratings yet
- Andres Paez ICTICT618 T2022 Attempt1Document57 pagesAndres Paez ICTICT618 T2022 Attempt1Andres PaezNo ratings yet
- Act303 Principles of Auditing Assignment - s121Document10 pagesAct303 Principles of Auditing Assignment - s121Sujan SilwalNo ratings yet
- Mohamed Abdi KilasDocument5 pagesMohamed Abdi KilasKilas YareNo ratings yet
- Group Assignment (20%) : Any Question Related To Group Assignment Should Be Directed To Lead LecturerDocument7 pagesGroup Assignment (20%) : Any Question Related To Group Assignment Should Be Directed To Lead LecturerEsther Lueh100% (1)
- ICSI registration for Executive ProgrammeDocument8 pagesICSI registration for Executive ProgrammeParth KachhiyaNo ratings yet
- 7407_Unit 06 - Assignment 2 frontsheetDocument50 pages7407_Unit 06 - Assignment 2 frontsheetBui Thi Hoai (BTEC HN)No ratings yet
- Er Shadab Safety CV 3Document24 pagesEr Shadab Safety CV 3Ksa KsaNo ratings yet
- Career Portfolio Worksheet HandoutDocument11 pagesCareer Portfolio Worksheet Handoutapi-317304401No ratings yet
- Authentication Record For School-Assessed CourseworkDocument5 pagesAuthentication Record For School-Assessed Courseworkf675ztsf100% (1)
- 410841615-BSBHRM501-docx (1) Important YamkantaDocument33 pages410841615-BSBHRM501-docx (1) Important Yamkantanirajan parajuliNo ratings yet
- New Era University Internship EvaluationDocument11 pagesNew Era University Internship EvaluationErine DelfinNo ratings yet
- Arid Agriculture University, Rawalpindi: Final Exam / Spring 2021 (Paper Duration 12 Hours) To Be Filled by The TeacherDocument7 pagesArid Agriculture University, Rawalpindi: Final Exam / Spring 2021 (Paper Duration 12 Hours) To Be Filled by The TeacherMohammad AliNo ratings yet
- Examination Slip HrisDocument1 pageExamination Slip HrisJaja HollaNo ratings yet
- Test2 Aina Sabrina Binti Mohamad Iqbal 4192007651Document5 pagesTest2 Aina Sabrina Binti Mohamad Iqbal 4192007651Jaja HollaNo ratings yet
- Office Centarl Assignment Mohammad Rahmat 4192008411 Nurshazrina Shiela 4192007521Document60 pagesOffice Centarl Assignment Mohammad Rahmat 4192008411 Nurshazrina Shiela 4192007521Jaja HollaNo ratings yet
- Office Central Fashion ValleyDocument38 pagesOffice Central Fashion ValleyJaja HollaNo ratings yet
- Nur Izzatul Najwa: Human ResourcesDocument2 pagesNur Izzatul Najwa: Human ResourcesJaja HollaNo ratings yet
- Quality Improvement Project for Education InstitutionsDocument7 pagesQuality Improvement Project for Education InstitutionsJaja HollaNo ratings yet
- Assignment Group 1Document17 pagesAssignment Group 1Jaja HollaNo ratings yet
- Spss Result WordDocument24 pagesSpss Result WordJaja HollaNo ratings yet
- PBS Mandarin Test 1.2 for Sem August 2021Document2 pagesPBS Mandarin Test 1.2 for Sem August 2021Jaja HollaNo ratings yet
- Fba Li Report Duty FormDocument1 pageFba Li Report Duty FormJaja HollaNo ratings yet
- Swot - Strategic ManagementDocument6 pagesSwot - Strategic ManagementJaja HollaNo ratings yet
- SPACE Matrix of Microsoft CorpDocument2 pagesSPACE Matrix of Microsoft CorpJaja HollaNo ratings yet
- PBS Mandarin Test 1.2 for Sem August 2021Document2 pagesPBS Mandarin Test 1.2 for Sem August 2021Jaja HollaNo ratings yet
- Assingment 2 g5 Microsoft NewDocument38 pagesAssingment 2 g5 Microsoft NewJaja HollaNo ratings yet
- GROUP PROJECT ASSIGNMENT IHRM SETB - EditedDocument2 pagesGROUP PROJECT ASSIGNMENT IHRM SETB - EditedJaja HollaNo ratings yet
- Final Year Project Sem 8 JajaDocument5 pagesFinal Year Project Sem 8 JajaJaja HollaNo ratings yet
- Jaja FYP Questionaire CorrectionsDocument4 pagesJaja FYP Questionaire CorrectionsJaja HollaNo ratings yet
- Chapter 3: Methodology 3.1 An OverviewDocument4 pagesChapter 3: Methodology 3.1 An OverviewJaja HollaNo ratings yet
- Detection of Phishing Emails WDocument10 pagesDetection of Phishing Emails WJohnNo ratings yet
- Threats and Attacks: CSE 4471: Information Security Instructor: Adam C. Champion, PH.DDocument26 pagesThreats and Attacks: CSE 4471: Information Security Instructor: Adam C. Champion, PH.Dswapnil RawatNo ratings yet
- The Stuxnet Worm and Options For RemediationDocument22 pagesThe Stuxnet Worm and Options For RemediationFábio Carvalho FurtadoNo ratings yet
- Ultramar Cibersecurity 30-05-23Document7 pagesUltramar Cibersecurity 30-05-23Luis MontecinosNo ratings yet
- Pse Palo AltoDocument26 pagesPse Palo AltoJose Rodas Alayo0% (1)
- Active Defense: Marcus Ranum's View vs. Dmitri Alperovitch's ViewDocument11 pagesActive Defense: Marcus Ranum's View vs. Dmitri Alperovitch's ViewSufiyan GhoriNo ratings yet
- 02-Network Security ProtocolsDocument30 pages02-Network Security ProtocolsNaveen AkalankaNo ratings yet
- View Tips and Tricks How To Create Keyboard Shortcut On Kali LinuxDocument4 pagesView Tips and Tricks How To Create Keyboard Shortcut On Kali Linuxajish808No ratings yet
- ESSAYDocument3 pagesESSAYNick del RosarioNo ratings yet
- اهم اسكربتات الميكروتكDocument13 pagesاهم اسكربتات الميكروتكWalid OsamaNo ratings yet
- Cracking Wifi WPA - WPA2 Passwords Using Reaver-WPS - BlackMORE OpsDocument11 pagesCracking Wifi WPA - WPA2 Passwords Using Reaver-WPS - BlackMORE OpsRichard DouglasNo ratings yet
- CEHv9 Labs Module 10 Session HijackingDocument55 pagesCEHv9 Labs Module 10 Session Hijackingwilburroberts20034852No ratings yet
- Public-Key Cryptography and Message AuthenticationDocument28 pagesPublic-Key Cryptography and Message Authenticationishita chakrabortyNo ratings yet
- Course Instructor: Ngollo T. Kishegena Coursecode: Course Name: System Administration & Security TypeofworkDocument8 pagesCourse Instructor: Ngollo T. Kishegena Coursecode: Course Name: System Administration & Security Typeofworkmahmoud janNo ratings yet
- Borivau 11, Poladia Pandey Loan Ms. Hemshree: Racpc PMDocument5 pagesBorivau 11, Poladia Pandey Loan Ms. Hemshree: Racpc PMRikhil NairNo ratings yet
- Module-1: Section-3 Appendix: AnnexureDocument2 pagesModule-1: Section-3 Appendix: AnnexureT shaaNo ratings yet
- SANGFOR - WANO - v9.5.3 - Associate - 05 - IPSEC VPN Multiline and Certificate Based AuthDocument33 pagesSANGFOR - WANO - v9.5.3 - Associate - 05 - IPSEC VPN Multiline and Certificate Based Authwendy yohanesNo ratings yet
- VSFTPDDocument3 pagesVSFTPDyassineNo ratings yet
- White-Paper - Living in A Quantum-Safe WorldDocument4 pagesWhite-Paper - Living in A Quantum-Safe WorldSanti IndarjaniNo ratings yet
- Biometric SecurityDocument495 pagesBiometric SecurityPlay100% (1)
- Part 2Document6 pagesPart 2LewisNo ratings yet
- Auditing OS and Networks for Security RisksDocument8 pagesAuditing OS and Networks for Security RisksJanine Joy OrpillaNo ratings yet
- CyberSense For Dell PowerProtect Cyber Recovery 1656644381Document12 pagesCyberSense For Dell PowerProtect Cyber Recovery 1656644381Marcelo MafraNo ratings yet
- The Cyber Security ObjectivesDocument6 pagesThe Cyber Security Objectiveshabib saleemNo ratings yet
- What Is Phishing, and How Not To Get CaughtDocument11 pagesWhat Is Phishing, and How Not To Get Caughtdanieljones0094No ratings yet

















































![BSBWOR301 AE Professional[2]](https://imgv2-2-f.scribdassets.com/img/document/723839452/149x198/9b8f9ccc17/1713332788?v=1)