Professional Documents
Culture Documents
LL.B. (Hons.) (Semester VI) Examination, 2014-15: (Old Course 2009-10 Syllabus) (7 Papers System) Paper
Uploaded by
rohitOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
LL.B. (Hons.) (Semester VI) Examination, 2014-15: (Old Course 2009-10 Syllabus) (7 Papers System) Paper
Uploaded by
rohitCopyright:
Available Formats
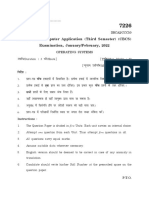
L/Sem VI/140(Old) Printed Pages : 4 Roll No.....................
L/Sem VI/140(Old)
(b) Cyber obscenity
lkbcj v’yhyrk LL.B. (Hons.) (Semester VI)
(c) Electronic Evidence
Examination, 2014-15
Law
bySDVªkfud lk{;
(Old Course 2009-10 Syllabus)
(d) Indian computer Emergency Team. (7 Papers System)
Hkkjrh; dEI;wVj vkikr ekspu nyA Paper : 36(a)
Information Technology Law
Time : Three Hours Full Marks : 80
(Write your Roll No. at the top immediately on the
receipt of this question paper)
Note: Answer any five questions. All questions
carry equal marks.
fdUgha ik¡p iz'uksa ds mRrj nhft,A lHkh iz'uksa ds
vad leku gaSA
1. Discuss the origin, objects and scope of the
Information Technology Act, 2000.
lwpuk izkS|ksfxdh vf/kfu;e 2000 ds mn~Hko] mn~ns';
,oa {ks= dh foospuk dhft,A
2. Discuss the concept of e-governance with
reference to the Information Technology Act,
2000.
4 500 P.T.O.
L/Sem VI/140(Old) L/Sem VI/140(Old)
lwpuk izk|
S ksfxdh vf/kfu;e] 2000 ds lUnHkZ esa bySDVªkfud 6. What do you understand by intermediary ?
'kklu ds fl)kUr dh foospuk dhft,A De scribe its liability in the light of the
Information Technology Act, 2000.
3. Define the term e-contract. Explain the
statutory provisions related to e-contract as e/;orhZ ls vki D;k le>rs gSa \ lwpuk izkS|ksfxdh
given under the Information Technology Act,
2000. vf/kfu;e] 2000 ds vkyksd esa blds mRrjnkf;Ro dk
bZ&lafonk dks ifjHkkf"kr dhft,A bZ&lafonk ls lEcfU/kr o.kZu dhft,A
lkafof/kd izko/kkuksa dks Li"V dhft, tSlk fd lwpuk
izkS|ksfxdh vf/kfu;e] 2000 esa of.kZr gSA 7. Discuss the efforts made at national and
international levels to curb the menace of
4. W h a t d o y o u u n d e r s t a n d b y C y b e r
Contravention ? Elaborate the process of cyber terrorism.
adjudication by referring to the relevant
lkbcj vkradckn ds mUewyu djus gsrq jk"Vªh; ,oa
provisions under the Information Technology
Act, 2000. vUrjkZ"Vªh; Lrj ij mBk;s x;s dneksa dh foospuk
lkbcj mYya?ku ls vki D;k le>rs gSa \ lwpuk dhft,A
iz k S | ks f xdh vf/kfu;e] 2000 ds vUrxZ r lq l a x r
izko/kkuksa dk mYys[k djrs gq, bldh U;k;fu.kZ;u izfØ;k 8. W r i t e s h o r t n o t e s o n a n y t w o o f t h e
dh O;k[;k dhft,A following :
5. Explain the functions and powers of the fuEufyf[kr esa ls fdUgha nks ij laf{kIr fVIif.k;k¡
Controllere of Certifying Authorities under the
fyf[k, %
Information Technology Act, 2000.
lwpuk izkS|ksfxdh vf/kfu;e] 2000 ds vUrxZr izek.kdrkZ (a) Digital Signature
izkf/kdkfj;ksa ds fu;a=d ds dk;ksZa ,oa 'kfDr;ksa dh O;k[;k vadh; fpUgd
dhft,A
2 3 P.T.O.
You might also like
- The Computer Book: From the Abacus to Artificial Intelligence, 250 Milestones in the History of Computer ScienceFrom EverandThe Computer Book: From the Abacus to Artificial Intelligence, 250 Milestones in the History of Computer ScienceNo ratings yet
- Jan 2022Document12 pagesJan 2022Abhi SinghNo ratings yet
- Master of Library and Information Science Semester-III (C.B.C.S.) Examination Legal Information System Elective 3T5-IIDocument3 pagesMaster of Library and Information Science Semester-III (C.B.C.S.) Examination Legal Information System Elective 3T5-IIPrashik UndirwadeNo ratings yet
- Question Bank Cyber Law Students'Document12 pagesQuestion Bank Cyber Law Students'spoken.21211457No ratings yet
- CKSF D Leink DK Vfèkdkj: Ikb&LajpukDocument10 pagesCKSF D Leink DK Vfèkdkj: Ikb&LajpukAbhinav KumarNo ratings yet
- Funsz'K %: Printed Pages-3) 1pgdca1Document3 pagesFunsz'K %: Printed Pages-3) 1pgdca1Dali ashdevaNo ratings yet
- Unit - I Introduction:-InternetDocument13 pagesUnit - I Introduction:-InternetMmNo ratings yet
- Advanced Programming in C On Linux December 2005Document3 pagesAdvanced Programming in C On Linux December 2005pankaj dadhichNo ratings yet
- F"K (KK Funs"Kky ) JK'V H Jkt/Kkuh (Ks Fnyyh VH KL Iz"U I L D (KK Lkekftd Fokku DKSM 087Document7 pagesF"K (KK Funs"Kky ) JK'V H Jkt/Kkuh (Ks Fnyyh VH KL Iz"U I L D (KK Lkekftd Fokku DKSM 087Viswapriyaa KrishnanNo ratings yet
- July 2021Document11 pagesJuly 2021Abhi SinghNo ratings yet
- B.Ed. First Semester (C.B.S.) Examination 104: Educational Technology and Computer Assisted Instruction (Compulsory)Document3 pagesB.Ed. First Semester (C.B.S.) Examination 104: Educational Technology and Computer Assisted Instruction (Compulsory)VarunNo ratings yet
- What Is A Network? The Internet Society Sri Lanka Chapter: WWW - Isoc.lk/ President@isoc - LKDocument5 pagesWhat Is A Network? The Internet Society Sri Lanka Chapter: WWW - Isoc.lk/ President@isoc - LKTharushka DinujayaNo ratings yet
- Computer Basic FundamentalDocument58 pagesComputer Basic Fundamentalchandan kumarNo ratings yet
- Bcom 6 Sem Bi Fundamentals of Insurance 2 12403 2020 PDFDocument3 pagesBcom 6 Sem Bi Fundamentals of Insurance 2 12403 2020 PDFDeepak KumarNo ratings yet
- NEW - Information Technology Hindi & English Notes1Document26 pagesNEW - Information Technology Hindi & English Notes1SANKALP SINGH100% (1)
- First NotesDocument3 pagesFirst NotesManish SharmaNo ratings yet
- Class Note 1Document12 pagesClass Note 1rajiv alexNo ratings yet
- Bachelor'S Degree in Library and Information Science (Blis) Term-End Examination December, 2020Document4 pagesBachelor'S Degree in Library and Information Science (Blis) Term-End Examination December, 2020MohitNo ratings yet
- ComputerOperatorGrade A PDFDocument3 pagesComputerOperatorGrade A PDFRiteshNo ratings yet
- Master of Library and Information Science Semester-III (CBCS) Examination Ict Applications in Libraries and Information Centres Core-3T3Document3 pagesMaster of Library and Information Science Semester-III (CBCS) Examination Ict Applications in Libraries and Information Centres Core-3T3Prashik UndirwadeNo ratings yet
- Guideline Student Credit CardDocument13 pagesGuideline Student Credit CardSaurabh KumarNo ratings yet
- Trade Mark and DesignDocument2 pagesTrade Mark and DesignNikhil MishraNo ratings yet
- 8 - Social Science - Level - 2 - MorningDocument8 pages8 - Social Science - Level - 2 - MorningrajatNo ratings yet
- Final 13-4-2023 Akhbaarsaar - Final - Copy - InddDocument15 pagesFinal 13-4-2023 Akhbaarsaar - Final - Copy - InddRaj GuptaNo ratings yet
- III Year Hons - CCEDocument4 pagesIII Year Hons - CCEngfn gncNo ratings yet
- Interpretation of Statutes 2018-19Document5 pagesInterpretation of Statutes 2018-19GauravNo ratings yet
- Paper 7188Document3 pagesPaper 7188IJARSCT JournalNo ratings yet
- Coordinator (DDE) 490-1-10313220POL21C5ResearchMethodologyISelfLearningMaterialDocument178 pagesCoordinator (DDE) 490-1-10313220POL21C5ResearchMethodologyISelfLearningMaterialchoudhary.bhavna0746No ratings yet
- Administrative LawDocument32 pagesAdministrative Lawcbaarun6162No ratings yet
- 229 Data Entry OperationDocument8 pages229 Data Entry OperationVinoth RockerNo ratings yet
- Class 9th Computer Hindi Medium BookDocument221 pagesClass 9th Computer Hindi Medium BookAnkit laptop0% (1)
- Computer FundamentalDocument22 pagesComputer FundamentalNAVEEN BHARTINo ratings yet
- Computer Fundamental - FinalDocument22 pagesComputer Fundamental - FinalNAVEEN BHARTINo ratings yet
- Sudesh Data Card Level NWDocument58 pagesSudesh Data Card Level NWSonu SinghNo ratings yet
- Bca Paper 4Document4 pagesBca Paper 4Vipul YadavNo ratings yet
- Advertisement PDFDocument7 pagesAdvertisement PDFGourang SahuNo ratings yet
- Networking and Internet The IntroducationDocument20 pagesNetworking and Internet The IntroducationarpitNo ratings yet
- Business StudiesDocument4 pagesBusiness StudiesAbhinavNo ratings yet
- LL.B 4th InternalDocument11 pagesLL.B 4th InternalNaincy KesharwaniNo ratings yet
- Lkeku Vè U& (Iz'Ui K&) : 641, First Floor, Mukherjee Nagar, Delhi-09 Contact-87501 87501Document3 pagesLkeku Vè U& (Iz'Ui K&) : 641, First Floor, Mukherjee Nagar, Delhi-09 Contact-87501 87501PrathameshNo ratings yet
- BALLB 5th Sem 2021 LAW OF CRIMES-IIDocument2 pagesBALLB 5th Sem 2021 LAW OF CRIMES-IIYASHWANT DEWANGANNo ratings yet
- Ir>J Esa Vwvh Ifrr;K¡: (Kam ^D* Μ Li'Kz&2 (Xn~; (Kam)Document5 pagesIr>J Esa Vwvh Ifrr;K¡: (Kam ^D* Μ Li'Kz&2 (Xn~; (Kam)Ansh KharcheNo ratings yet
- 1st QP CJ - 2018 PDFDocument4 pages1st QP CJ - 2018 PDFParas IndNo ratings yet
- Computer Networks With Windows NTDocument3 pagesComputer Networks With Windows NTMmNo ratings yet
- Press Release 22 23 Dated 28 02 2024Document2 pagesPress Release 22 23 Dated 28 02 2024ALOK VERMANo ratings yet
- Computer HardwareDocument42 pagesComputer HardwareRAHUL NISHADNo ratings yet
- 1 - Hindi OK 11Document4 pages1 - Hindi OK 11जगत नयनNo ratings yet
- Fundamental Hindi Notes of McuDocument85 pagesFundamental Hindi Notes of Mcubright_2790% (1)
- Handbook On Predictive Maintenance Through Network of Data Loggers Ver2 PDFDocument96 pagesHandbook On Predictive Maintenance Through Network of Data Loggers Ver2 PDFamarsingh choudharyNo ratings yet
- Gazette NotificationDocument2 pagesGazette NotificationSinius InfracomNo ratings yet
- Patent LawsDocument2 pagesPatent LawsNikhil MishraNo ratings yet
- MCM 503MCM 106Document6 pagesMCM 503MCM 106jiahanjiahan1234567No ratings yet
- Internet Hindi Medium Locked ssc45Document97 pagesInternet Hindi Medium Locked ssc45api-356931346No ratings yet
- Computer McqsDocument13 pagesComputer McqsAnkit JhariyaNo ratings yet
- DCA Fundamental All UnitsDocument68 pagesDCA Fundamental All UnitsJitendra Kasotia78% (9)
- Workshop 2Document16 pagesWorkshop 2Santosh BharadNo ratings yet
- Overview of Cyber LawDocument26 pagesOverview of Cyber LawDigant DeoNo ratings yet
- Economics11 ADocument6 pagesEconomics11 Akpawar460063No ratings yet
- Data Structure December 2005Document3 pagesData Structure December 2005pankaj dadhichNo ratings yet
- Iec University: School of LawDocument11 pagesIec University: School of LawrohitNo ratings yet
- Judicial Process Term PaperDocument9 pagesJudicial Process Term PaperrohitNo ratings yet
- Iec University: School of LawDocument21 pagesIec University: School of LawrohitNo ratings yet
- Pcs J Entrance Examinations Subject TableDocument3 pagesPcs J Entrance Examinations Subject TablerohitNo ratings yet
- Iec University: School of LawDocument11 pagesIec University: School of LawrohitNo ratings yet
- LL.B. (Hons.) (Semester IV) Examination, 2014-15: PaperDocument2 pagesLL.B. (Hons.) (Semester IV) Examination, 2014-15: PaperrohitNo ratings yet
- Th. (.Iaq, F (NR QRRDocument21 pagesTh. (.Iaq, F (NR QRRrohitNo ratings yet
- Aditya Copyright LawDocument16 pagesAditya Copyright LawrohitNo ratings yet
- Assignment Competition LawDocument21 pagesAssignment Competition LawrohitNo ratings yet
- RJS Trans To HindiDocument6 pagesRJS Trans To HindirohitNo ratings yet
- Bibliography: Internet SourcesDocument5 pagesBibliography: Internet SourcesrohitNo ratings yet
- LL.B. (Hons.) (Semester II) Examination, 2014-15: Paper: LBH-124Document2 pagesLL.B. (Hons.) (Semester II) Examination, 2014-15: Paper: LBH-124rohitNo ratings yet
- Overview of Trademark Laws in IndiaDocument35 pagesOverview of Trademark Laws in IndiarohitNo ratings yet
- RJS 2018Document16 pagesRJS 2018rohitNo ratings yet
- Aditya Competition LawDocument21 pagesAditya Competition LawrohitNo ratings yet
- Rohit Muslim The Secondary Sources 3Document3 pagesRohit Muslim The Secondary Sources 3rohitNo ratings yet
- Envr FNLDocument17 pagesEnvr FNLrohitNo ratings yet
- Assignment Competition LawDocument21 pagesAssignment Competition LawrohitNo ratings yet
- 8th Semester SyllabusDocument5 pages8th Semester SyllabusrohitNo ratings yet
- Env. Law 1Document14 pagesEnv. Law 1rohitNo ratings yet
- Shakshi Copyright AssignmentDocument18 pagesShakshi Copyright AssignmentrohitNo ratings yet
- Ijma: Unanimous Decisions of The JuristsDocument4 pagesIjma: Unanimous Decisions of The JuristsrohitNo ratings yet
- Adi Land LawDocument8 pagesAdi Land LawrohitNo ratings yet
- Doctrine of Competence-CompetenceDocument18 pagesDoctrine of Competence-CompetencerohitNo ratings yet
- Labour Law Project 11Document22 pagesLabour Law Project 11rohitNo ratings yet
- Good Governance ProjectDocument38 pagesGood Governance ProjectrohitNo ratings yet
- R.A 10821Document11 pagesR.A 10821Riza Gaquit100% (1)
- Strenghtening Civil Society - Phase TwoDocument10 pagesStrenghtening Civil Society - Phase TwoAsose TuNo ratings yet
- Case Note - MALLIKARJUN KODAGALI CASEDocument6 pagesCase Note - MALLIKARJUN KODAGALI CASEAISHANI PATTANAIKNo ratings yet
- Yao v. CADocument1 pageYao v. CAAKNo ratings yet
- Mbushuu Alias Dominic Mnyaroje and Another VDocument4 pagesMbushuu Alias Dominic Mnyaroje and Another VNovatus ShayoNo ratings yet
- Salient Feature Agrarian ReformsDocument13 pagesSalient Feature Agrarian ReformsJimmy YauNo ratings yet
- Case of Berdzenishvili and Others v. RussiaDocument45 pagesCase of Berdzenishvili and Others v. RussiaANo ratings yet
- 1956 ConstitutionDocument23 pages1956 ConstitutionSaqib TanveerNo ratings yet
- Nuisance Art. 694: Other ClassificationDocument7 pagesNuisance Art. 694: Other ClassificationCarla Mae MartinezNo ratings yet
- XXXVVVDocument3 pagesXXXVVVRabindranath TagoreNo ratings yet
- Hillsborough County Board of County Commissioners EMERGENCY MANAGEMENT ORDINANCEDocument22 pagesHillsborough County Board of County Commissioners EMERGENCY MANAGEMENT ORDINANCEABC Action NewsNo ratings yet
- Vda de Barrera V Heirs of Legaspi DigestDocument4 pagesVda de Barrera V Heirs of Legaspi DigestIvan Montealegre ConchasNo ratings yet
- Shan Foods (Timeline, Competitive Advantage, Exports)Document3 pagesShan Foods (Timeline, Competitive Advantage, Exports)SYED HARIS HASHMI0% (1)
- Pilapil vs. Ibay-SomeraDocument8 pagesPilapil vs. Ibay-SomeraFrance De LunaNo ratings yet
- Larranaga vs. CADocument1 pageLarranaga vs. CALeNo ratings yet
- Group Assignment 01Document6 pagesGroup Assignment 01Yathu MathuNo ratings yet
- Civil Service Reform in VietnamDocument4 pagesCivil Service Reform in VietnamphanvanquyetNo ratings yet
- Unit 4: Disast Er Risk Reduction An D ManagementDocument13 pagesUnit 4: Disast Er Risk Reduction An D ManagementMelanie GirayNo ratings yet
- Makoti Khawula: Makoti Sibongile Khawula (Born 7 December 1954) Is A SouthDocument3 pagesMakoti Khawula: Makoti Sibongile Khawula (Born 7 December 1954) Is A SouthmisterpNo ratings yet
- Communist Manifesto Sparknotes PDFDocument2 pagesCommunist Manifesto Sparknotes PDFMichaelNo ratings yet
- An Overview of The Public Relations Function PDFDocument200 pagesAn Overview of The Public Relations Function PDFMiluska GarateNo ratings yet
- Aggravating Circumstances ReportDocument19 pagesAggravating Circumstances ReportApril Yang100% (3)
- Pepsi Lipton Number WorkDocument16 pagesPepsi Lipton Number WorkSachin KamraNo ratings yet
- In Re Petition Martin NGDocument2 pagesIn Re Petition Martin NGshirlyn cuyongNo ratings yet
- CensorshipDocument22 pagesCensorshipRoma GillNo ratings yet
- Cabral vs. CADocument2 pagesCabral vs. CANicole SantoallaNo ratings yet
- P L D 1994 Supreme Court 31Document3 pagesP L D 1994 Supreme Court 31Fareeha RajaNo ratings yet
- People V ArrojadoDocument7 pagesPeople V ArrojadoKris Anne TuralloNo ratings yet
- 6 Different Types of Press ReleasesDocument1 page6 Different Types of Press ReleasesJesse JhangraNo ratings yet