Professional Documents
Culture Documents
Assignment 2 Due Date 26-12-22
Uploaded by
Muhammad TalhaOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Assignment 2 Due Date 26-12-22
Uploaded by
Muhammad TalhaCopyright:
Available Formats
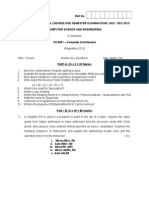
Assignment 2 19-12-22
Computer Networks
Due date 26-12-22 (Late submission marks will be calculated from 50% of total points)
Points 30
Find these problems there and solve with help of book and internet. It is further
recommended that do these excercise by yourself.
Chapter 10.7.3 Problems (B A Forozan) Exercises
P10-3. Exclusive-OR (XOR) is one of the most used operations in the calculation of
codewords. Apply the exclusive-OR operation on the following pairs of patterns.
Interpret the results.
a. (10001) ⊕ (10001) b. (11100) ⊕ (00000) c. (10011) ⊕ (11111)
P10-4. In Table 10.1, the sender sends dataword 10. A 3-bit burst error corrupts the
codeword. Can the receiver detect the error? Defend your answer.
P10-5. Using the code in Table 10.2, what is the data word if each of the following
codewords is received?
a. 01011 b. 11111 c. 00000 d. 11011
P10-6. What is the Hamming distance for each of the following code words?
a. d (10000, 00000) b. d (10101, 10000)
c. d (00000, 11111) d. d (00000, 00000)
P10-6 Assuming even parity, find the parity bit for each of the following data
units.
a. 1001011 b. 0001100 c. 1000000 d. 1110111
P10-7 Assuming odd parity, find the parity bit for each of the following data
units.
a. 1001011 b. 0001100 c. 1000000 d. 1110111
P10-8 A simple parity-check bit, which is normally added at the end of the word (changing a 7-
bit ASCII character to a byte), cannot detect even numbers of errors. For example, two, four, six,
or eight errors cannot be detected in this way. A better solution is to organize the characters in a
table and create row
and column parities. Kindly Explain Two Dimensional Parity Check with examples clearly
make table and add redundant bit with Red pen in rows and columns
Chapter 11.6.2 Questions, 11.6.4 Problems (B A Forozan) Exercices
Q11-2. Explain why flags are needed when we use variable-size frames.
Q11-3. Assume a new character-oriented protocol is using the 16-bit Unicode as the character
set. What should the size of the flag be in this protocol?
Q11-4. Compare and contrast byte-oriented and bit-oriented protocols.
Q11-5. Compare and contrast byte-stuffing and bit-stuffing.
Q11-6. In a byte-oriented protocol, should we first unstuff the extra bytes and then remove the
flags or reverse the process?
Q11-7. In a bit-oriented protocol, should we first unstuff the extra bits and then remove the flags
or reverse the process?
NETWORK LAYER
a. Elaborate in Detail Classless IP Addressing, why we use Classless addressing though we
have Class full addressing. Give example of Classless addressing to justify your answer.
You may Give IP of Classless network to further clarify your example.
b. Comparison of Classful Vs Classless Addressing
You might also like
- Tutorial 1 QuestionsDocument2 pagesTutorial 1 Questionsyoyolamlyy0511No ratings yet
- Handout Nivel ReteaDocument14 pagesHandout Nivel ReteaAlexz AleeNo ratings yet
- Data and Computer CommunicationsDocument31 pagesData and Computer CommunicationsDipanker SarkerNo ratings yet
- qpEE6301 DIGLOGICCIRCUITSDocument9 pagesqpEE6301 DIGLOGICCIRCUITSsyedabdulaleem003No ratings yet
- CN Assignment 1Document2 pagesCN Assignment 1KrishanuNayakNo ratings yet
- Parity CheckDocument41 pagesParity CheckAmit DhullNo ratings yet
- Abc DOCUUCOD1109902Document4 pagesAbc DOCUUCOD1109902santoshchapaneriNo ratings yet
- CIS 5100 Homework Assignment #2: Fall 2020, Dr. Song Xing Due On Monday, Oct 5Document6 pagesCIS 5100 Homework Assignment #2: Fall 2020, Dr. Song Xing Due On Monday, Oct 5Oliver BaileyNo ratings yet
- CS211 ExamDocument10 pagesCS211 ExamTetzNo ratings yet
- Hw5 ReportDocument4 pagesHw5 ReportMadhan ReddyNo ratings yet
- Practice Problems 1Document34 pagesPractice Problems 1akbisoi1No ratings yet
- Practice Problems - 1: Department of Electrical EngineeringDocument2 pagesPractice Problems - 1: Department of Electrical EngineeringMalay Kumar MohantaNo ratings yet
- Practice Problems 12Document32 pagesPractice Problems 12suduku007No ratings yet
- UMN EE2301 Final ExamDocument10 pagesUMN EE2301 Final ExamchrisNo ratings yet
- Exam #1 For Computer Networks SOLUTIONSDocument4 pagesExam #1 For Computer Networks SOLUTIONS87bbNo ratings yet
- Datalink LayerDocument23 pagesDatalink LayerSushama PatilNo ratings yet
- WEEK-3 - CSC340 Homework 2Document3 pagesWEEK-3 - CSC340 Homework 2Daniel sNo ratings yet
- Digital Logic Design: Lecture # 10 University of TehranDocument22 pagesDigital Logic Design: Lecture # 10 University of Tehranbilalc15No ratings yet
- Your Name:: Final ExamDocument9 pagesYour Name:: Final ExamDaniel EcheverriaNo ratings yet
- MST Latest 2025Document8 pagesMST Latest 2025bndianonymousNo ratings yet
- Mob Net 2011 Exam SolutionDocument13 pagesMob Net 2011 Exam Solutionمحيي الدين الكميشىNo ratings yet
- T103-Revision For MTA-2017Document25 pagesT103-Revision For MTA-2017Abdullah SamianNo ratings yet
- 3213 Final Winter2008 SolutionsDocument17 pages3213 Final Winter2008 SolutionsMohammedMikhaelYahyaNo ratings yet
- Practice Exam Computer ArchitectureDocument15 pagesPractice Exam Computer ArchitectureMuhammad UsmanNo ratings yet
- Electronics For Computing QuestionsDocument30 pagesElectronics For Computing QuestionsKaka MwenyaNo ratings yet
- 40 OutDocument80 pages40 Outciuciu.denis.2023No ratings yet
- Workshop Week 4 PDFDocument4 pagesWorkshop Week 4 PDFStevenRNo ratings yet
- Final Exam Solution - Test Paper Final Exam Solution - Test PaperDocument15 pagesFinal Exam Solution - Test Paper Final Exam Solution - Test Paperciuciu.denis.2023No ratings yet
- Final Exam Solution - Test Paper Final Exam Solution - Test PaperDocument82 pagesFinal Exam Solution - Test Paper Final Exam Solution - Test Paperciuciu.denis.2023No ratings yet
- Fault Tolerance ExamDocument14 pagesFault Tolerance Examahmadhassan306No ratings yet
- Digital Logic DesignDocument126 pagesDigital Logic Designmt21215015 Navdeep GuptaNo ratings yet
- DigitalDocument2 pagesDigitalVikrant SahuNo ratings yet
- 604524007Document6 pages604524007Hung LeoNo ratings yet
- Final Old SolDocument8 pagesFinal Old SolPDF PDFNo ratings yet
- Subject Code/ Title: Ee6301 Digital Logic Circuits Year/ Sem/Branch: Ii/ Iii/ EeeDocument16 pagesSubject Code/ Title: Ee6301 Digital Logic Circuits Year/ Sem/Branch: Ii/ Iii/ EeePavithra ManiNo ratings yet
- Introductory Overview: 2009 Texas Instruments, All Rights ReservedDocument35 pagesIntroductory Overview: 2009 Texas Instruments, All Rights ReservedMustafa KhairallahNo ratings yet
- Xyz DOCUUCOD678Document3 pagesXyz DOCUUCOD678santoshchapaneriNo ratings yet
- Error Detection CorrectionDocument22 pagesError Detection CorrectionJagdish BhanushaliNo ratings yet
- Digital PDFDocument15 pagesDigital PDFthumatimadhusudhanNo ratings yet
- Data Networks Summer 2007 Midterm ExamDocument10 pagesData Networks Summer 2007 Midterm ExamKerem CelikNo ratings yet
- Assignment#1 SolutionDocument4 pagesAssignment#1 SolutioneidmohdNo ratings yet
- 2-Bit Multiplier M B A: Don't Worry About This Question Because This Particular Method Was Not Presented in ClassDocument8 pages2-Bit Multiplier M B A: Don't Worry About This Question Because This Particular Method Was Not Presented in ClassMarlon BoucaudNo ratings yet
- Ch-1 1Document29 pagesCh-1 1A_b_qNo ratings yet
- Convolution Codes: 1.0 PrologueDocument26 pagesConvolution Codes: 1.0 PrologueKulwant NagiNo ratings yet
- 9A04306 Digital Logic DesignDocument4 pages9A04306 Digital Logic DesignsivabharathamurthyNo ratings yet
- DG Iqs FullDocument126 pagesDG Iqs FullShyamala Venkataramani100% (2)
- Midterm Ic s16 SolutionDocument10 pagesMidterm Ic s16 SolutionLogan BushNo ratings yet
- Error Detection CorrectionDocument49 pagesError Detection Correctionsiddhanta69No ratings yet
- Ca 13Document3 pagesCa 13krishnasankar95No ratings yet
- ECE 190: Introduction To Computing Systems: Mid-Term Exam 2006-2007Document10 pagesECE 190: Introduction To Computing Systems: Mid-Term Exam 2006-2007Ace NhatNo ratings yet
- Integer Optimization and its Computation in Emergency ManagementFrom EverandInteger Optimization and its Computation in Emergency ManagementNo ratings yet
- Task-Software Engineering-ICT On Sustainable SE DevelopmentDocument1 pageTask-Software Engineering-ICT On Sustainable SE DevelopmentMuhammad TalhaNo ratings yet
- Assignment no.1-BESE-27CDocument1 pageAssignment no.1-BESE-27CMuhammad TalhaNo ratings yet
- EE 353 Computer Networks-Fall 2022Document81 pagesEE 353 Computer Networks-Fall 2022Muhammad TalhaNo ratings yet
- CS-250 Data StructuresDocument67 pagesCS-250 Data StructuresMuhammad TalhaNo ratings yet
- Basics of TDMA, FDMA and CDMA PDFDocument3 pagesBasics of TDMA, FDMA and CDMA PDFManas DasNo ratings yet
- IGS-6329 Series - LDocument14 pagesIGS-6329 Series - Lmayraelisa.salgadoNo ratings yet
- AutomatizaciónDocument91 pagesAutomatizaciónJohnatan RojasNo ratings yet
- Configuring Cisco 4G LTE Wireless WAN EHWICDocument40 pagesConfiguring Cisco 4G LTE Wireless WAN EHWICindore bhopalNo ratings yet
- Meraki SDWAN Exercise SMBDocument7 pagesMeraki SDWAN Exercise SMBNUR BALQIS BINTI IZHARNo ratings yet
- Passive Optical Network (PON) ReDocument94 pagesPassive Optical Network (PON) Reamanda05700No ratings yet
- Check Point Appliances BrochureDocument20 pagesCheck Point Appliances BrochureRafael ReisNo ratings yet
- Arduino Ethernet Shield TutorialDocument15 pagesArduino Ethernet Shield TutorialAnis TrihandayaniNo ratings yet
- DCN Unit-4 SaqDocument5 pagesDCN Unit-4 Saqsravan kumarNo ratings yet
- GSM TimerDocument2 pagesGSM Timerthana.p4596No ratings yet
- 8AL91007USAF Ed01en SIP ExtractDocument250 pages8AL91007USAF Ed01en SIP ExtractAurelian CretuNo ratings yet
- RDMA Verb ProgrammingDocument18 pagesRDMA Verb ProgrammingAlok PrasadNo ratings yet
- Presidency University Bangalore Network Programming Lab Comscpbtech624922 Comsc Btech Sem 6 Div 2Document7 pagesPresidency University Bangalore Network Programming Lab Comscpbtech624922 Comsc Btech Sem 6 Div 2Hithai ShreeNo ratings yet
- ALFA AIP-W525H User GuideDocument69 pagesALFA AIP-W525H User Guidehassan329100% (1)
- 12.1 - Configure Ip Bts (GSM) Via Cme Gui 1Document42 pages12.1 - Configure Ip Bts (GSM) Via Cme Gui 1Sabina SerbanNo ratings yet
- Wireless Security by Sandeep Kumar SharmaDocument40 pagesWireless Security by Sandeep Kumar SharmasandeepNo ratings yet
- Chapter ThreeDocument73 pagesChapter ThreeAbenezer BedluNo ratings yet
- ConfidentialDocument28 pagesConfidentialwirelesssoulNo ratings yet
- Tamilrockers Latest LinksDocument26 pagesTamilrockers Latest LinksRamkumarNo ratings yet
- GifiDocument15 pagesGifiakankshareddy dappilliNo ratings yet
- FIREBOX M290 & M390: Enterprise-Grade Security For Small To Midsize BusinessesDocument2 pagesFIREBOX M290 & M390: Enterprise-Grade Security For Small To Midsize BusinessesGonzalo AyalaNo ratings yet
- Introduction To WLAN TestingDocument42 pagesIntroduction To WLAN TestingGabriel SilvaNo ratings yet
- Cisco CCNA 200-125 Exam Dumps Latest - New Questions & AnswersDocument136 pagesCisco CCNA 200-125 Exam Dumps Latest - New Questions & Answersergu vfuko fghuiNo ratings yet
- Lacoste R., Edgeworth B. - CCNP Enterprise Advanced Routing ENARSI 300-410 Official Cert Guide (2020) PDFDocument1,883 pagesLacoste R., Edgeworth B. - CCNP Enterprise Advanced Routing ENARSI 300-410 Official Cert Guide (2020) PDFSrishti Baliyan65% (26)
- Base Band Transmision 2020-21Document60 pagesBase Band Transmision 2020-21rahul guptaNo ratings yet
- 7210 Sas Service-Access-Switch Amt PDFDocument7 pages7210 Sas Service-Access-Switch Amt PDFHector Obando VNo ratings yet
- DCC MicroprojectDocument10 pagesDCC Microprojectkunal more88% (16)
- DRIVES-FT-CC-004 - Altivar Process ATV6x0 Update - 250116 - Rev 2Document32 pagesDRIVES-FT-CC-004 - Altivar Process ATV6x0 Update - 250116 - Rev 2Edwin RamírezNo ratings yet
- VANETfinalDocument47 pagesVANETfinalMeenakshi MuthuramanNo ratings yet